►
From YouTube: Securing EcmaScript, presentation to Node Security
Description
Presentation to Node Security group
https://github.com/nodejs/security-wg/issues/376#issuecomment-415567888
Identical to https://www.youtube.com/watch?v=lgAnL1swyns&index=23&list=PLKr-mvz8uvUgybLg53lgXSeLOp4BiwvB2&t=0s but with corrected visuals
A
I
want
to
speak
today
on
my
thoughts
about
securing
atmospheric.
This
is
something
that
I've
been
working
on
for
a
very
long
time
now,
starting
with
the
comm
project
and
and
my
contribution
design
of
Eggman
script.
Five
and
I
from
interacting
with
Bradley
I've
come
to
understand
a
lot
of
the
relevance
of
what
I've
said
for
a
lot
of
the
issues
facing
node
right
now.
So
this
is,
in
the
other
view
of
the
talk
I'm
going
to
start
by
explaining
the
focus
problem
that
I
want
to
orient.
A
This
talk
around
and
I
want
to
stress
that
there
are
many
security
problems
and
different
security
problems
will
call
for
different
mechanisms
and
altogether
I,
very
much
believe
in
defense-in-depth
that
we
have
to
fight
on
all
fronts.
Security
is
hard,
and
when
there
is
a
well
motivated
problem,
then
we
should
figure
out
what
we
need
to
do
for
that
problem
and
if
we
can
build
mechanisms
that
solve
other
problems
as
well,
great,
so
I'm
going
to
focus
on
least
Authority
libraries.
A
There
are
a
variety
of
vulnerabilities
that
we've
seen
that
come
from
the
fact
that
people
build
applications
and
websites
that
happens
at
both
the
browser
and
server
and
on
mixed
browsers
and
servers
like
electron
from
the
fact
that
that
anytime,
you
build
something.
You
probably
linked
in
lots
of
code,
lots
of
library,
code
from
third
parties
that
you
don't
vet
and
often
that
code
comes
along
with
other
code
and
sometimes
that
code
misbehaves.
A
So
there's
been
some
significant
concern
about
electron
to
the
point
that
Brendan
reports
that
Windows
10
store
was
considering
banning
all
electron
based
apps,
including
slack
and
signal.
So
that's
you
know
quite
a
severe
reaction,
indicating
that
the
problem
is
quite
severe
and
the
problem
is
driven
by
the
fact
that
in
our
current
systems,
when
a
bunch
of
code
is
loaded
and
linked
together,
it's
all
completely
vulnerable
to
each
other.
A
That
that
every
bit
of
that
code
runs
with
all
of
the
authority
of
the
application
or
in
the
server
side
of
its
user
and
on
the
browser
side
of
get
all
the
app.
The
authority
given
to
the
web
page
as
a
whole
and
Brandon
refers
here
to
Pola,
which
is
the
principle
of
least
Authority,
which
is
the
the
most
important
first
principle
to
turn
to
at
all
granularities,
including
the
library
granularity
that
I'm
focusing
on
today,
and
that
principle
is
the
principle
that
one
should
give
a
component
again
a
component
at
any.
A
Once
you
give
a
component
only
the
least
authority
that
that
component
needs
to
do
it's
legit
legitimate
job
and
then
that
component
still
might
misbehave,
but
the
limit
on
the
damage
that
it
can
do
if
it
misbehaves
is
limited
by
the
authority.
It's
been
that's
been
placed
at
risk
through
its
misbehavior.
A
There's
also
the
Princeton
No
Boundaries
series
that
documents
rather
massive
they're,
looking
they're
looking
at
browser
properties,
but
what
they're
identifying
as
a
form
of
vulnerability
applies
equally
to
server
side
apps
and
to
mixed
browsers
and
servers.
What
they're
documenting
is
that
people
link
in
third-party
scripts
all
the
time
without
understanding
the
vulnerability
they're
creating,
for
example,
Walgreens
by
a
virtue
of
third-party
scripts.
A
It
was
using
on
its
website,
patient
prescription
information
was
being
leaked
to
those
third-party
scripts
and
the
websites
from
which
the
third-party
scripts
came
in
clearly
blatant
violation
of
HIPAA
like
likewise
in
Princeton
zone
information
security
course.
They
found
that
they
were
linking
in
libraries
that
caused
exfiltration
of
grading
assignments,
student
names,
emails
grades
and
instructor
comments
to
the
source
of
those
third-party
scripts
and
that's
in
violation
of
something
called
FERPA.
So
this
is
a
pervasive
problem.
A
Sometimes
you
will
hear
the
security
perspective
that
well
any
code.
You
link
into
your
website
or
link
into
your
server
any
kind
library
that
you've
decided
to
load
is
they
use?
You
will
often
hear
the
phrase
trusted
code
and
the
implication
is
that
you
should
only
use
third-party
libraries
that
you
fully
vetted
that
you're
completely
certain
is
secure
or
that,
where
you're
willing
to
risk
all
of
your
users
security
on-
and
this
is
rather
ridiculous
advice.
A
The
the
purpose
of
this
advice,
I
think,
will
only
be
understood
as
advice
whose
purpose
is
to
shed
liability
rather
than
protect
users.
It's
very
much
like
when
the
car
industry
was
saying
things
like:
oh
you're,
Pinto
bro.
It
blew
up.
Well,
it's
your
fault
because
you
had
a
collision.
You
shouldn't
have
had
a
collision.
It
was
operator
error.
A
We
need
to
understand
what
realistic
behavior
is
for
use
of
the
programming
language.
Cars
became
more
forgiving
of
realistic
behavior
over
time.
It
doesn't
mean
people
don't
crash,
it
doesn't
mean
people
don't
get
hurt,
but
they
became
more
forgiving
of
realistic
behavior.
It
was
much
easier
to
drive
a
car
safely
and
was
much
easier
to
survive.
Many
accidents
and
our
industry
needs
to
make
that
map
change
as
well.
We
should
take
responsibility
for
the
more
responsibility,
so
the
realistic
behavior
that
our
programmers
engage
in
and
what's
necessary
to
help
them
help
their
users
be
safe.
A
So
when
we
talk
about
destructive
interference
when
the
destructive
interference
of
concern
is
accidental,
we
call
those
bugs
and
that's
the
domain
of
software
engineering
and
much
of
computer
science
has
been
concerned
with
that
how
to
how
to
gain
the
benefits
of
cooperative
composition
with
with,
while
limiting
the
damage
from
accidental
interference
and
when
the.
When
the
interference
is
intentional.
We
call
those
attacks
and
those
are
studied
by
computer
security.
But
my
message
and
and
my
work
is
all
premise
on
the
idea
that
I
don't
much
care
whether
the
interference
is
accidental
or
intentional.
A
A
It's
often
using
mechanisms
that
are,
in
fact
quite
similar
to
make
it
as
you
find
in
good
security
architecture
and
the
progress
of
computer
science.
Both
software
engineering
and
security
can
be
seen
as
the
progress
of
the
discovery
of
modularity
and
abstraction
mechanisms,
lifting
the
crate
off
her.
A
A
Organizations
can
only
build
engineering
artifacts,
whose
communication
structure
the
mirrors,
the
communication
structure
of
the
organization
well
JavaScript
started
as
a
language
only
for
scripting
web
browsers,
but
it
was
split
between
two
standards
organizations
ACMA,
which
had
responsibility
for
the
language
in
w3c,
which
had
responsibility
for
the
hosts
api,
the
API
for
interacting
with
web
pages
and
communicating
or
the
met
etc.
And
the
result
was
that
JavaScript
has
an
almost
perfect
division.
A
Look
up
object,
bounty
names
that
are
outside
the
name
standardized
by
the
JavaScript
standard
in
the
browser
like
document
and
window,
an
xhr
on
the
node
all
of
the
node
API,
that
all
access
to
the
external
world
starts
with
that
global
scope.
Lookup
and
therefore,
if
you
can
intervene
in
that
global
scope,
lookup,
you
can
virtualize
all
access
to
the
equivalent
of
system
mode
and
you
can
do
the
equivalent
of
building
virtual
machine
monitors
and
operating
systems.
A
Furthermore,
the
JavaScript
primordial,
which
are
the
objects
that
exist
before
code
starts
running,
have
essentially
no
hidden
state,
meaning
that
the
prop
all
of
all
of
their
mutability,
all
of
their
abilities
to
to
enable
internal
side
effects
are
all
in
properties.
So,
if
you
freeze
all
of
those
properties,
there
is
no
mutability
left.
A
B
B
A
The
other
that's
so,
if
I'm,
making
use
of
both
of
these
facts,
the
first
one
is
the
ability
to
intercept
any
attempt
by
JavaScript
to
access
host
objects
so
that
you
can
virtualize
the
house.
You
can
virtualize
and
deny
by
use
of
the
intervention
on
global
scope,
lookup,
and
so
that
takes
that's
what
I'm,
using
for
corruption
for
dealing
with
corruption
and
attack
via
access
to
host
objects
and
then,
additionally,
for
among
the
JavaScript
objects
themselves
that
are
Co
loaded
into
the
same
realm.
A
A
Welcome
and
by
the
way,
please
do
continue
to
interrupt
as
things
are
unclear
and
for
questions
or
or
comments.
I
do
want
to
get
through
the
presentation
before
extended
discussion,
you
can
feel
free
to
interrupt
and
if
I
feel
like
a
point,
this
is
something
I
want
to
postpone.
I'll
just
take
responsibility
for
postponing
it.
A
Also,
let
me
mention
the
two
asterisks
here:
it's
an
almost
perfect
separation
among
the
JavaScript
are
more
reals.
Today
there
are
two
exceptions
to
this.
One
is
access
to
the
current
time,
via
date,
dot
now
or
the
date
constructor,
both
with
no
arguments
and
that's
being
able
to
read
external
effects
from
the
outside
world.
A
It's
still
not
an
ability
to
communicate
and
the
other
one
is
math
dot
random,
which
doesn't
have
anything
to
do
with
external
effects
at
all,
but
by
virtue
of
being
statically
acts
the
primordial
if
there
is
a
bad
random
number
generator
or
something
anything
less
than
a
cryptographically,
strong
wind
lever,
generator
that
creates
a
communications
channel
between
object
where
an
object
subgraphs
that
should
have
not
been
able
to
communicate.
So
those
are
both
minor
exceptions,
but
those
are
both
exceptions.
A
A
So,
starting
with
the
design
of
atmosphere
5
when
I
got
involved,
it
was
at
that
point
the
extra
3.1
revolt
against
es
4,
which
then
became
es
5,
but
starting
with
the
S
5,
we
have
been
consistently
shaping
Equis
script,
going
forward
to
be
able
to
support
the
kind
of
security
I'm
explaining
today
to
support
object,
capability
security,
both
at
coarse
grain
and
the
fine
grain,
and
a
lot
of
the
elements
that
we've
gotten
into
acting
script.
To
support
our
security
goals.
A
These
three
goals
that
they're
transparent
by
the
fault-
that,
if
the
membrane
isn't
doing
something
to
change,
behavior,
it's
as
if
it
isn't
there
that
it
forms
an
impenetrable
boundary
that
is
as
new
references
across
the
membrane,
they're,
wrapped
or
unwrapped
to
preserve
the
boundary
between
the
great
subgraphs
and
that
it
supports
a
purposeful
distortions
which
are
the
reason
you
introduced
membrane.
If
they're
only
transparent,
they
might
as
well
not
have
been
there
so
revoking
access,
creating
subjective
views
or
policies
that
protect
delicate
internals.
A
This
is
actually
where
the
membrane
of
a
metaphor
came
from,
which
is
a
cell
membrane,
protects
the
delicate
internals
of
a
cell
friendly
rather
chaotic
world
outside
the
cell,
and
the
Firefox
internal
security
architecture
is
actually
built
out
of
exactly
this.
They
started
off
with
their
own
ad-hoc
membranes
in
C++
that
were
larger
than
a
principle.
A
A
As
long
as
the
later
code
is
not
translated,
there
are
certain
objects
among
the
primordial
is
that
it
can
just
reach
by
syntax
a
object.
Literal
evaluates
directly
to
an
object
that
inherits
from
the
original
object:
dot
prototype
function,
little
devalue,
sorry
inherit
to
the
original
function,
prototype
and
even
if
even
no
matter
what
we
do
to
the
namespace,
the
binding
to
those
objects
and
sides
are
not
something
we
can
intervene.
A
The
global
object,
of
course,
has
properties
that
refer
into
this
group
of
primordial
x'
and
are
essentially
the
roots
for
navigating
among
the
primordial
x',
and
there
is
a
special
relationship
between
a
certain
set
of
primordial
x'
in
the
global
object.
Those
particular
primordial
I'm
going
to
call
the
evaluators,
so
the
eval
function
and
the
function
constructor
both
evaluate
code,
where
the
global
the
properties
of
the
global
object,
are
also
at
the
end
of
the
scope
chain
of
the
scope
in
which
they
evaluate
cutter.
A
A
However,
as
anyone
who's
actually
tried
to
make
use
of
this
particular
feature
for
isolation,
for
whatever
purpose
has
found,
is
that
that
has
an
isolation
mechanism
really
conflicts
with
the
usability
of
JavaScript
through
a
phenomena
that
I
call
the
identity,
discontinuity
and
my
own
experience
with
that
is
they
didn't
think
this
continuity,
even
for
very
knowledgeable
experts
who
hid
it
again
and
again
is
when
you
try
to
do
cross
run
programming.
It
keeps
catching
there's
just
a
much
harder
problem
than
you
can
anticipate.
A
So
the
identity
discontinuity
is,
for
example,
that
if
Alice
in
one
realm
in
around
a
evaluates
an
array
literal,
it
inherits
from
her
array
prototype
and
then,
if,
through
cross
realm
interaction,
Bob
in
ronbie
obtains
a
reference
to
that
array
and
asks
is
it
instance
of
Ray?
The
answer
will
be
no
and.
A
And
the
thing
that
really
makes
this
identity
discontinuity
so
hazardous
is
not
so
much
the
instance
of
test.
That's
the
that's
the
obvious
one
is
that
when
you
then
follow
pointers,
starting
from
the
object
from
the
surprising
realm,
you
find
yourself
traversing
the
primordial
z--
of
the
wrong
realm.
Does
this
cross
realm
accidental
leakage
that
just
keeps
happening
so
we'd
like
to
bring
about
useful
isolation,
but
without
making
our
users
have
to
face
this
very
difficult
problem
of
the
identity?
Discontinuity
mark.
B
A
So
cross-origin
is
fine
for
the
seperation
between
pages.
It
is
completely
unrealistic
for
the
issue
of
LinkedIn
libraries,
the
8,000
websites
that
the
Princeton
No
Boundaries
series
found
were
vulnerable
to
libraries
that
they
LinkedIn
that
they're,
using
as
libraries
that
use
the
opportunity
of
being
LinkedIn
as
just
a
component
of
the
website.
The
excellent
right
there
yeah
anybody
who's
tried
to
do
it
to
use
code
between
be
over
postmessage
between
different
origin
frames
in
the
browser
knows
that
it's
a
very
awkward
interaction.
You
don't
try
to
do
that
with
your
own
libraries.
B
So
some
minions
work
I
think
it's
calling
hey
I
can
look
it
up,
but
it's
James
McGinnis,
but
basically
like
we.
We
have.
We
have
ways
of
transforming
libraries
that
are
intertwined
into
extracting
them,
to
separate,
realms
and
doing
message
passing
between
them
and,
if
they're
not
doing
that,
that
they're
doing
like
something
that's
very
much
intertwined
that
it
might
not
be
isolated
anyway,
to
the
point
where
I'm
not
sure
what
you're
actually
getting
interrupt
for
a
second.
A
B
We
were
suddenly
comparing
the
web's
model,
two
nodes
model.
We
don't
have
this
kind
of
multi
realm
iframe
situation
in
node
people
are
just
requiring
other
modules
and
loading
them
into
the
same
realm
and
very
old
versions
of
node.
We
tried
the
multi
context,
approach
kind
of
what
you're
talking
about,
and
there
were
problems
with
it.
So
I'd
be
curious
on
how
you
suggest
we
solve
kind
of
the
identity,
discontinuity
that
we
saw
way
back
when
that
mark
also
touched
on,
and
also
the
problems
of
changing
programming
models
entirely
for
these
things,
yeah.
A
But
but
if
there's,
if
there's
work
on
trying
to
do
this
in
the
browser
other
than
the
common
legwork,
I'd
certainly
be
interested
in
hearing
about
so
Kay's,
do
you
send
me
the
link?
Let
me
ask,
based
on
the
comic
experience,
let
me
ask
what
sort
of
the
crucial
question
from
that
work,
which
is,
does
this
so
to
speak,
transparent.
B
A
A
So
now
I'm
going
to
explain
the
mechanism
that
we're
now
introducing
into
the
JavaScript
standard
to
help
leverage
the
elements,
the
security
elements
of
JavaScript
that
I
just
mentioned
in
order
to
make
it
very
pleasant
to
address
the
library
issue
and
the
realms
API
proposal
is
a
statement
as
a
proposal
before
the
committee.
The
realms
shim
is
a
shim
that
we've
drawn
me
engineered
with
Salesforce,
it's
a
shim
of
the
approximately
other
proposal.
A
A
So
there's
a
new
global
object
named
realm:
it
has
a
static
method
called
make
root
realm.
So
if
an
Alice
in
one
realm
says
make
rude
realm
at
that
point,
she
is
creating
a
new
root
ground.
The
new
root
realm
is
a
realm
that
has
its
own
fresh
set
of
prime
Oracle's,
so
between
Alice
and
Bob.
Here
there
is
the
same
old
identity,
discontinuity,
but
we're
going
to
so
we
have
to
deal
with
the
identity.
Discontinuity
during
the
good
strap
we're
going
to
try
to
use
the
boots
fast.
A
So
when
Ellis
says
make
root
realm,
she
also
gets
as
a
result
a
instance
of
the
realm
object.
The
root
won't
be
shown
as
the
lowercase
root
realm
object
that
has
a
access
to
property
in
global
that
points
at
new
realms
global
has
evaluate
method
for
evaluating
code
in
the
scope
of
the
of
Bob's
global
and
the
root
realm
object
is
Alice's
object
for
manipulating
new
room.
Ro
Madre
is
itself
an
object
in
Alice's
realm.
A
And
a
difference
between
what
the
realms
shim
accomplishes
and
what
the
browser
gives
you
with
same-origin
iframes,
a
node
gives
you
with
VM.
Create
context
is
that
this
new
root
realm
is
born
with
no
host
objects
that
are
implicitly
granted
that
it's
up
to
Alice
to
populate
Bob's
global
with
those
additional
objects
that
Alice
wants
Bob
to
see
and
anything
that's
not
explicitly
granted
by
Alice
is
completely
absent
from
Bob's
realm.
A
So
what
this
is
doing
is,
are,
you
know,
go
let's
go
back
to
the
analogy
of
a
virtual
machine,
monitor
all
of
the
access
to
the
host
environment.
That
JavaScript
program
C,
is
by
lookup
of
names
on
the
global
scone,
the
global
object.
So
if
Alice
populates
Bob's
global
object,
then
no
matter
what
the
underlying
platform
host
is
Alice
is
acting
as
a
virtual
host
for
box.
You
can
create
for
Bob.
She
can
emulate
any
host
environment.
She
wants
or
invent
new
ones.
A
Bob
also
has
a
realm
class
in
his
prime
Orioles
and
if
Bob
invokes
realm
dot
make
compartment,
a
compartment
is
also
a
kind
of
realm,
but
it's
unlike
a
root
realm.
It's
incredibly
lightweight
Bob's
Bob's
compartment
shares
almost
all
of
the
primordial
of
the
root
realm
that
created
the
compartment.
That's
the
the
defining
difference
of
the
compartment.
A
The
only
objects
that
need
to
be
created,
they're
visible,
that
that
characterize
the
compartment
is
there's
a
object
created
as
a
as
a
member
of
the
root
of
Bob's
root
realm,
which
is
the
object
representing
the
Caroll
compartment.
The
Caroll
compartment
has
its
own
global
and
it
has
its
own
function.
Constructor
and
eval
function
that
evaluates
code
in
a
scope
that
terminates
in
that
compartment,
global
scope
and
other
than
those
objects.
A
Everything
else
comes
from
the
root
realm
that
that
compartment
is
created
in
and
then,
if
Alice
does
a
deep
freeze
on
the
Bob
realm,
and
let
me
apologize
for
the
name
deep
freeze.
We
will
probably
be
renaming
it
to
something
less
prone
to
misunderstanding,
but
what
deep
freeze
does
is
it
essentially
freezes
the
primordial
of
the
bob
root
realm?
A
It
freezes
it
does
not
freeze
all
of
the
objects
that
are
not
part
of
the
primordial
graph,
but
it
freezes
all
the
primordial
and
because
of
the
property
that
I
that
I'm
earlier,
that
there's
no
hidden
state
the
result.
Leaving
aside
the
two,
the
two
exceptions
of
date
and
math.random,
the
result
is
that
the
primordial
that
are
that
the
Carroll
compartment
is
sharing,
has
no
mutable
state
left
and
has
no
access
to
the
outside
world.
A
And
the
result
is
that
many
compartments,
the
compartments,
are
featherweight
protection
domains.
Many
many
compartments
can
be
created
within
eNOS
context
and
there's
no
identity,
discontinuity
among
them.
An
array
created
we
won't
buy
one.
Its
incidence
of
array
is
checked
by
the
other.
It's
even
the
case
that
all
of
the
different
function,
constructors
share
the
same
function,
prototype
so
even
different
functions
from
these
different
compartments
evaluating
in
the
scope
of
different
Global's
they're,
still
all
passed
each
other's
instance
of
test.
Oh.
A
Is
only
these
transitively
immutable
objects
with
their
implicitly
sharing?
Is
these
graphs
are
born
fully
isolated
from
each
other?
They
can
only
interact
or
become
further
connected
according
to
the
decisions
of
the
objects
that
have
a
foot
in
both
which
initially
are
the
objects
that
are
in
the
position
of
having
created
them,
so
that
topological
constraint
makes
that
the
ideal
position
to
stand
to
express
the
security
policies
by
which
these
things
interact.
A
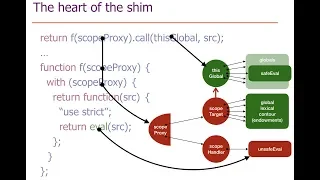
Al
any
attempt
by
to
look
up
a
global
variable
goes
through
the
scope
proxy,
which
is
then
able
to
intercept
the
scope
lookup
and
thereby
prevent
access
to
the
genuine
global
scope
that
was
created
by
the
underlying
browser
or
no
primitive
the
and
by
completely
insulating
all
this
mechanism.
From
the
genuine
global,
we
can
create
environments
that
have
the
global
of
our
own
design.
A
A
A
The
I
should
also
mention
these
numbers
were
put
together
in
a
hurry
to
be
able
to
report
them
by
the
last
second
script.
Meeting
they're,
not
I,
don't
know
if
more
up-to-date
numbers
are
done,
but
we're
in
regular
we're
collaboration
with
jf,
and
we
haven't
heard
of
an
attempt
to
revisit
the
measurement
exercise
I
I
can
I
can
find
out
for
you
what
was
actually
measured.
I
don't
have
that
available
immediately
John.
Is
it
spreadsheet?
There
was
a
spreadsheet
to
Jeff
I
shared
with
me,
but
I
think
names
that
were
measured
as.
A
The
override
mistake
is
that
if
you
know
I'll
just
talk
it
through
with
regard
to
want
to
the
to
the
most
egregious
example,
if
you,
if
you
naively,
freeze,
object
that
prototype,
then
you've
made
the
to
string
property
object,
dot,
prototype
dot
to
string
into
a
non
configurable
non
writable
data
property.
If
other
code
then
engages
in
the
very
normal
coding
pattern
that
much
old
code
in
fact
engages
in
with
no
problem,
let's
say:
defining
a
function,
a
constructor
function
using
the
pre
class
pattern.
They
define
a
construction,
constructor
function
named
point.
A
A
A
A
What
would
have
been
the
behavior
if
we
had
convinced
the
committee
to
repair
the
override
mistake,
meaning
that
if
you
tried
to
mutate
it
on
the
object
itself,
it
still
throws
because
the
property
is
not
mutable
on
the
object
itself.
But
if
you
try
to
mutate
it
on
another
object
that
inherits
from
that
object.
The
center
notices
that
and
emulates
the
assignment
using
defined
property.
The
emulation
of
the
assignment
is
not
the
bottleneck,
that's
not
the
it's,
not
the
pain
point
with
regard
to
performance.
A
The
pain
point
with
regard
to
performance
is
that
reading
the
property
now
has
to
go
through
a
getter
and
for
property
for
in
particular,
object
that
prototyped
up
to
string
it's
read
sufficiently
often
and
the
jits
are
are,
for
whatever
reason
not
sufficiently
aggressive
at
optimizing.
The
code
path
going
through
the
getter
that
the
difference
between
looking
up
the
getter
value
versus
looking
up
the
property
value
is
painful
and
those
are
that
and
that
pain
is
not
reflected
in
these
numbers.
I
will
get
you
numbers
that
reflect
that.
A
B
Thanks
thanks
for
that,
there's
also
like
more
than
two
string
or
like
we're,
seeing
like
a
lot
more
monkey-patching
of
these
primordial
x'
that
I
think
you'd
have
to
do
is
very
similar
thing.
Now.
That's
I'm,
curious
I'm
gone
like
even
like
what
these
units
are,
but,
like
I
guess
like
we
could
talk
offline
so.
A
A
The
no
op
policy
would
be
direct
access.
You
can
Alice's
is
in
a
position
to
give
direct
access.
If
it's
intermediated
through,
let's
say
a
function,
that's
just
a
front
ending
function
that
forwards
everything
to
the
underlying
function.
We
could
measure
that
it
shouldn't
be
any
different
than
any
other
cases
of
forwarding
function,
so,
whatever
the
overhead
isn't
going
through
an
extra
function,
so
it
shouldn't
be
any
mystery
there,
but
yeah.
A
We
can
measure
that
and
with
regard
to
this
also,
you
know
we
do
know
that
there
used
to
be
a
penalty
for
interacting
with
frozen
objects,
in
particular
in
v8.
Simply
interact
with
frozen
objects,
for
many
different
objects
would
put
you
on
the
slow
path.
That's
been
corrected
across
B,
a
and
all
engines.
The
override
mistake
issue
still
has
a
real
penalty,
but
other
than
that,
there's
no
penalty
for
being
for
interacting
with
frozen
objects.
A
So
this
is
essentially
the
realms
shim
API,
the
you
know
the
API
that
we
that
were
able
to
shin
with
hard
security
properties
and
a
very,
very
small
TCB,
a
very
small
trusted
computing
base.
Less
than
seven
hundred
lines
of
code
now
and
the
constraint
with
regard
to
our
security
goals
is
that
any
person
that's
introduced
to
the
overall
picture
is
introduced
cannot
be
introduced
for
the
sake
of
security
that
we,
because
any
parser
is
going
to
be,
is
going
to
blow
up
the
overall
code
size
by
a
lot
any
user
level.
A
Parser
parts
are
written
in
JavaScript,
so
we
want
the
security
of
our
system
not
to
depend
on
the
parser.
So
this
is
a
parser
aside.
This
is
what
what
from
realms
we
can
securely
emulate,
with
no
rewriting
and
to
emulate
module
loader,
that's
part
of
the
overall
realm
API.
It's
not
something!
We
can
securely
do
in
a
shame
with
that
rewriting
because
we
don't
currently
have
any
way,
as
in
a
general
host,
independent
JavaScript
way,
to
intercept
loading
behavior,
of
course,
for
nodes.
A
Is
that
we're
using
untrusted,
parsers
and
rewriters
to
realize
what,
like,
roll-up
and
ESM
to
rewrite
code
expressed
in
terms
of
modules
into
code
expressed
more
in
terms
of
node
modules,
with
Rakolta
with
requiring
exports
that
then
become
strings,
that
we
can
evaluate
whose
global
scope
look
up
to
require
and
export
itself
or
ones.
We
can
intervene
on.
B
Suppose
we
have
more
than
just
at
most
script
and
we
actually
have
say
say
buffers
or
we
have
FS
or
something
like
that,
that
we'd
like
to
expose
to
one
of
these
realms
and
within
a
realm.
I
call
one
of
these
functions,
which
will
end
up
calling
it
insane
in
binding
code
and
the
binding
code
will
call
my
callback
with
an
object.
What
happens
so.
A
A
Provides
adequate
material
that,
whatever
security
policy
you
want
with
regard
to
that,
we
should
exist
not
for
any
security
policy,
but
for
many
plausible
security
policies,
we're
trying
to
provide
the
mechanism
that
enables
a
large
number
of
policies
to
be
expressed
with
common
mechanisms.
I
went
back
to
this
slide
here,
where
there
is
multiple
coexisting
compartments.
A
That
was
then
the
compartment
that
ran
the
code
for
expressing
the
policy
for
attenuating
the
SF
module
into
virtual
FS
modules
that
were
then
used
to
see
the
other
compartments,
and
by
doing
it
in
that,
in
this
way,
you
can
give
these
other
compartments
differential
access,
and
you
can
deny
the
FS
module
to
those
compartments
that
have
no
need
for
the
FS
module.
This
is
actually
the
perfect
segue
to
the
rest
of
the
talk,
which
is
many
libraries,
don't
need
the
FS
module.
B
A
B
Know
I
have
an
attenuated
version
of
FS
that
ultimately
cause
it's
real
FS,
which
calls
into
binding
code
that
creates
an
object
that
I
then
like
hacks,
you
further
like
what
the
mechanism
described
so
hard
doesn't
seem
like.
It
would
help
me
with
making
sure
that
that's
not
the
true
object
that
I
can't
mess
with.
A
B
A
Okay,
now
Alice
makes
the
route
realm
here
and
the
route
realm.
Let's
say
she
does
not
give
the
route
access
to
to
that
F
s,
object
and
the
reason
she
doesn't
do
it
to
the
root
realm.
Has
all
the
compartments
created
in
the
root
realm
shared
the
root
realm
and
share
access
to
the
global
of
the
so
going
forward.
So
this
is
the
node
host
objects
and
in
this
case,
Alice
does
not
put
the
genuine
FS
object
into
the
into
this
global.
A
A
The
global
of
the
new
compartment
Carol
and,
let's
say
Alice-
puts
the
genuine
FS
object
on
this
global
and
then
having
an
event
or
in
either
order
doesn't
matter
whether
alice
freezes
Bob
before
or
afterwards,
because
this
new
stuff
is
on
present
by
freezing
the
rid
realm
and
then
starting
from
this
picture.
What
Alice
does
is
she
loads
all
the
rest?
A
She
she
makes
all
of
the
rest
of
her
application
following
the
bootstrap
happen
inside
the
Carol
realm
and
the
reason
she
moves
all
the
rest
of
her
application
logic
into
the
Carol
realm
is
so
that
there's
no
identity,
discontinuity
between
the
pieces
of
the
Alice
application.
So
the
only
thing
that
remains
to
execute
in
the
initial
realm
is
the
code
that
picks
out
the
global
authority.
The
the
dangerous
global
host
objects
picks
out
which
things
should
be
loaded
and
what
module
loading
policy
to
use
to,
determine
which
module
should
get.
A
What
and
then
sets
up
the
Carol
situation
so
that
everything
else
that
gets
loaded,
that's
part
of
the
application,
gets
isolated
and
constrained
by
those
policies
and
all
the
rest
of
the
application
gets
started
from
there.
And
let's
say
that
each
of
these
compartments
now
represents
the
a
different
loaded
module
of
the
Alice
application
started
from
that
situation,
and
it
was
the
loading,
the
policy
that
at
and
the
logic
of
that
initial
code
executing
a
compartment
Carol
that
further
divided
the
FS
Authority.
A
So
so
the
the
Alice
application,
the
the
I'm
going
to
say,
trusted
the
trusted
part
of
the
Alice
application
when
I
and
now
I'll
be
very
specific.
What
I
mean
by
trusted
is
the
the
code
of
the
Alice
application
that
the
Alice
author
decided
that
that
it
was
okay
for
all
of
the
Alice
application
to
be
vulnerable
to
that
vulnerability
decision
applied
only
to
the
code
running
in
the
Carol
compartment
and
that
code
used
these
mechanisms
largely
through
parameterizing,
a
module
loader.
B
Is
added
similar
question,
which
is
like
I,
just
like,
like
I
guess,
walking
through
a
concrete
thing
of
like
exposing
refil
right
like
like
I'm,
not
concerned
about
rewriting
the
path
to
be
a
virtual
path,
or
anything
like
that?
I
guess,
I'm
more
concerned
that
this
function
ultimately
will
be
implemented
in
C++
and
that
will
be
binding
code.
That
creates
the
object
response.
You
can
buffer
that
you're
giving
me
and
then.
A
A
A
hard
thing
to
inter
mediate,
in
fact,
is
where
most
of
our
security
bugs
were
more,
but
it
was
still
a
user
level
library
in
the
sense
that
it
was
built
on
SES
and
then
the
users,
then
the
normal
users
then
never
expressed
policy
with
the
underlying
Dom
node
other
than
by
handing
it
to
our
safe
library
for
manipulating
and
virtualizing
Dom
access
same
thing.
The
same
I
expect
the
same
pattern
to
emerge
on
note.
A
Let
me
also
pick
up
on
another
thing.
You
said,
which
is
from
the
experience
with
e,
where
we
were
bringing
native
filesystems,
treating
them
with
the
same
kind
of
policy
decomposition.
Is
that
one
very
common
thing
is
that
other
modules
don't
need
access
to
the
final
system.
They
need
access
to
particular
fire
and
the
natural
thing
there
is
to
create
an
object
that
doesn't
represent
the
final
system.
A
It
just
represents
access
to
a
file
and
now
access
to
the
ability
to
read
the
file
or
to
put
another
way,
read-only
access
to
the
file
or
append
only
access
to
the
file
or
revocable
access
to
the
file
then
becomes
then
further
becomes
very
easy
to
express
attenuators,
and
we
in
fact
found
ourselves
expressing
all
of
those
attenuators
very
simply
in
E
and
I
expect
the
same
kind
of
leverage
for
wrapping
denote
API
with
libraries
of
well-constructed
attenuators.
So.
B
B
A
A
The
I
mean
just
the
Dom
API
is,
is
properly
blamed
for
being
one
of
the
worst
API
is
that
human
beings
have
ever
designed,
and
nevertheless,
we
ultimately
did
succeed
by
creating
a
library
for
attenuating
Dominic
P
I
that
critical
web
properties
then
dependent
on
and
Salesforce,
has
now
reconstructed
a
similar
intervention
and
on
reconstructed
from
scratch
on
similar
ideas.
That's
also
part
of
what
they're
building
on
top
of
the
new
realms.
A
Okay,
so
going
forward
okay,
so
so,
with
those
elements
in
mind,
here's
a
key
observation
about
the
about
existing
libraries,
which
is
a
tremendous
number
of
existing
libraries,
are
what
we
would
call
transformational
in
the
sense
of
what
job
is
that
they're
doing.
There
are
libraries
that
are
given
inputs
compute
for
a
while
and
produce
outputs,
where
the
library
itself
has
no
need
for
access
to
IO.
It
hasn't
a
need
for
access
to
the
user.
A
It
has
no
need
for
access
to
the
network,
it
has
no
need
for
access
to
non
terminus,
'm
or
to
be
able
to
measure
duration
now.
Obviously
many
other
libraries
do
need
those
things,
but
there's
an
opportunity
here
with
regard
to
the
overall
vetting
burden
and
the
the
issue
of
defense-in-depth,
the
principle
of
least
Authority
is
we
can
recognize
that
for
a
very
large
number
of
the
libraries
that
we're
using
the
least
authority
that
they
need
does
not
include
access
to
the
file
system,
it
doesn't
mean
the
one
very
nice
contrast
is
baked.
A
Arithmetic
is
transformational,
but
access
to
the
current
date
is
not,
and
you
find
that
you've
reflected
very
much
in
the
analogy.
We're
making
about
what
you
can
do
and
user
mode
versus
system
a
properly
designed
processor
can't
find
out
what
the
current
time
is.
Computation
user
mode
computation
can't
find
that
with
the
current
time
is
other
than
by
making
a
system
call,
but
it
can
do
all
the
data
rithmetic
it
likes
and-
and
one
particular
interesting
observation
is
that
for
transformational,
libraries
that
are
denied
all
of
these
things,
including
any
source
of
non
determinism.
A
They
don't
have
adequate
material
from
which
to
build
something
that
they
can
use
to.
Measure
duration,
there's
wonderful
paper,
fantastic
timers
and
where
to
find
them,
saying
that,
even
if
you
deny
all
of
the
explicit
timers
in
the
browser,
there's
plenty
of
impressive
things
you
can.
You
can
use
in
order
to
measure
duration,
and
then
you
can
use
those
to
read
side
channels
and
that's
like
meltdown
inspector
and
a
zillion
other
side
channels
that
that
browsers
have
and
I
suspect
node
has
as
well
on.
A
A
That's
that
that
are
rooted
in
the
full
grounds
proposal
and
there's
Mike's
angles:
a
proposal
for
module
keys,
which
are
basically
a
very
modular
mechanism
for
modules
to
interact
with
each
other
where
they
can
whitelist,
which
other
modules
they
wish
to
grab
things
to,
as
well
as
light
weight,
which
other
modules
they're
willing
to
believe.
With
regard
to
the
veracity
of
what
kind
of
information
wonderful
example
is
when
you're
forming
a
safe
HTML
by
appending
strings
that
are
allegedly
HTML
that
were
constructed
in
a
in
a
safe
manner.
A
Mike
Samuel
has
a
a
shim
for
shimming
the
module
keys
thing
in
which
of
these
things
should
move
into
the
platform
in
which
of
things
should
remain
user
level.
Libraries
is
to
be
figured
out
as
we
go
on,
but
the
overall
surfaced
presented,
the
normal
user
I
think
is
one
in
which
this
kind
of
per
module
distinction
of
authority
and
veracity
is
something
we
want
to
express.
A
So
in
conclusion,
I
want
to
go
philosophically
large
again.
In
conclusion,
over
the
last
few
decades,
civilization
has
made
a
transition
where
it
now
rests
on
the
infrastructure
that
our
industry
has
made
and
node
is
no
small
part
of
that
story.
It's
a
significant
player
with
regard
to
that,
overall,
vulnerability
of
civilization
to
the
infrastructure
created
by
our
industry
and
the
overall
insecurity
of
the
overall
computational
infrastructure
really
puts
our
civilization
at
risk.
A
Your
if
your
read
realistic
assessments
of
how
much
damage
and
all-out
cyber
work
can
do
it's
really
quite
frightening
and
as
a
security,
professional
I
consider
those
usually
to
be
under
estimating
the
degree
of
damage
and
the
result,
and
my
conclusion
from
that
once
again
is
defense
in
depth.
We
have
to
fight
this
on
all
fronts
and
to
the
degree
to
which
we
can
reduce
risks
at
any
level
of
abstraction.
We
can
amplify
the
benefits
that
we
can
obtain
safely
at
that
level
of
abstraction.
A
A
What's
what
you're
given
in
that
playground
are
the
things
that
transformational
libraries
will
expect
to
have,
but
nothing
else
except
that
you're
also
given
a
callback
that
we've
seeded
in
that
environment
with
to
a
really
egregious
side-channel
one
who
that
that,
when
you
call
it,
it
takes
an
amount
of
time,
that's
really
egregiously
dependent
on
what
the
secret
is
that
it
doesn't
want
to
reveal
such
that.
If
you
have
date,
dot
now
enabled
notice
the
query
string
at
the
end
of
the
URL.
B
B
A
Sorry
I,
when
I
was
at
Google.
Most
recently,
I
was
in
the
wasm
team.
I
know
a
lot
about
lazon
for
a
lot
of
these
transformational.
Libraries
written
in
JavaScript
part
of
what
makes
them
usable
by
other
code
written
in
JavaScript,
is
that
they're
all
within
the
view
of
one
garbage,
collector,
there's
wasm
right
now
is
a
plat
address.
A
B
B
A
A
A
So
when,
when
a
depends
on
B
to
a
B,
might
just
be
one
thing,
because
it's
represented
by
one
thing:
they
import,
but
B
internally
uses
a
whole
bunch
of
other
things.
That
a
is
unaware
of.
So
all
of
those
other
things
coming
along
for
the
ride
that,
as
far
as
a
is
concerned,
internal
parts
of
a
a
should
be
in
the
position
of
first
of
all,
a
only
I'm,
sorry
I
did
I
say
a.
A
A
You
Carol
through
Joe
is
just
internal
mechanism
within
Bob,
so
Alice
might
already
had
given
Bob
limited
authority,
but
that
limited
Authority
for
this
scenario
has
to
in
you
know
what
at
Bob's
least
Authority
includes
all
of
the
authority
he
needs
to.
In
turn,
pass
onto
his
own
internal
modules,
even
if
at
the
Bob
as
module
doesn't
need
a
particular
authority.
A
If
bob
has
as
carol
is
an
internal
component
and
Carol
needs
the
authority,
then
Bob
as
a
creative
component
needs
the
authority
Bob's
manifest
should
describe
it
and
Alice
should
provide
something
that
at
least
appears
to
be
that
authority
is
API
compatible
of
the
authority.
Once
again,
Alice
can
still
attenuate,
because
as
long
as
Bob
can't
pal
or
Bob
is
compatible
with
the
attenuation
but
Bob
in
turn,
I.
Basically,
every
level
of
composition
there's
yet
another
key
CB
there's
yet
another
trusted
computing
base.
A
B
So
I
building
clean
slate
systems
I
think
we
can
do
it.
What
I'm,
like
afraid
of,
is
that
I,
don't
I
think,
like
you
end
up
requiring
a
lot
more
authority
than
you
might
think.
At
first
I
like
like,
take
take
a
wrapper
around
the
database
module
all
right,
like
let's
say
a
wrap
around
go
like
three,
which
needs
to
write
to
disk.
Whether
or
not
this
thing
currently
is
running
on
behalf
of
Alice
or
Bob.
Let's
say
they're
users.
B
It
might
need
one
motor
to
be
able
to
write
in
one
part
of
a
database
or
another
or
like,
let's
say,
file
system
right,
so,
like
I,
don't
think
like
if
we
were
to
make
a
per
module
policy
decision
we'd
be
making
the
decision
that
you
get
to
do
whatever
the
hell
you
want
and
I
think
like
its.
It
becomes
really
hard
to
to
do
anything
about
that.
Okay,.
A
So
initially
I
expect
that
many
people
will
do
exactly
that,
and
it
very
much
reminds
me
of
the
original
Android
installation.
Experience
is
Android
up
front,
asked
for
all
the
permissions
and
provided
no
explanation
of
what
why
it
needed
anyone
permission
and
in
any
case
the
normal
user
never
would
have
paid
any
attention
to
that
anyway.
So
what
happened?
A
Well,
the
part
that's
not
analogous
about
the
new
Android
policy
is:
is
that
for
many
permissions
it
waits
until
it
needs
it
before
it
asks.
But
the
part
that
is
analogous
is
that,
because
of
that
restructuring
of
the
interaction
when
a
users
saw
a
request
that
seemed
completely
bizarre
and
unjustified
by
their
sense
of
what
they
were
doing.
A
He
has
this
wonderful
notion
of
the
stubborn
minority,
where
a
stubborn
minority
in
who
who
have
a
particular
requirement
where
the
requirement
is
otherwise
meeting
the
requirement
is
otherwise
not
too
costly
by
the
producer
and
meeting
the
requirement
does
not
harm
the
other
consumers,
who
don't
care
about
the
requirement
that
often
the
iterative
interaction
over
time
is
that
the
producers
satisfy
the
requirement
of
the
stubborn
Minari
in
the
example
is
look
at
how
many
foods
are
labeled,
halal
or
kosher.
I
commend
this.
A
Now
I
want
to
come
back
to,
though
the
concession
you
made
at
the
beginning,
which
is
you
buy
it
for
transformational
libraries?
Well,
if
everything
I'm
talking
about
is
only
ever
used
for
transformational,
libraries,
the
overall
risk
profile,
the
overall
aggregate
risk
profile
that
were
faced
through
people
building
applications
and
giving
attackers
opportunities
by
linking
in
libraries
that
they
should
not
have
trusted
that
risk
profile
goes
down.
The
vetting
burden
goes
down.
A
It
means
that,
when
you're
trying
to
vet
what
libraries
you
should
link
in
you
can
you
can
see
Oh
for
these
transformational
libraries
I'm
not
giving
them
anything
dangerous
anyway.
I
still
should
worry
some,
but
I
can
worry
much
less
and
you
can
focus
your
vetting
effort
and
that,
to
me
is
one
of
the
main
payoffs
as
a
software
developer
is
our
precious
security
review.
Vetting
effort
can
be
more
intelligently
spent
on
the
things
that
still
are
dangerous
after
we've
been
able
to
make
many
things
that
didn't
need
to
be
dangerous,
making
them
unday
ngerous.
B
B
A
A
A
A
B
Good
thanks
right,
I
be
just
quickly
check
if
there
is
any
question
and
github
on
our
YouTube.
Give
me
just
one
minute
from
that,
but
I
don't
think
there
is
any
yeah,
no
question
on
YouTube.
So
thanks
a
lot
for
this
amazing
presentation,
I
think
we
will
follow
up
on
and
github
to
see.
The
next
step
will
be
okay.
