►
From YouTube: The Layers of Agoric
Description
No description was provided for this meeting.
If this is YOUR meeting, an easy way to fix this is to add a description to your video, wherever mtngs.io found it (probably YouTube).
A
However,
the
way
we've
been
going
about
it
way
this
most
of
this
industry
have
been
going
about
it
so
far
has
some
show-stopping
problems
that
we
have
to
overcome
in
order
to
actually
make
realistic
progress
towards
the
goal.
So,
for
one
thing,
the
way
people
compose
more
contracts,
for
example
on
theorem,
is
to
hazardous
experts,
put
a
lot
of
attention
from
carefully
constructing
smart
contracts,
and
then
hundreds
of
millions
of
dollars
disappear
overnight,
with
no
recourse,
and
this
happens
repeatedly.
A
And,
with
the
exception
of
a
few
players
like
cosmos
in
general,
every
chain
is
built
as
if
it
is
supposed
to
be
the
only
chain
in
the
world
and
then
writing
contracts
for
a
chain
you're
locked
into
that
chain,
also
creating
more
barriers
to
adoption.
So
we
want
to
overcome
all
of
these
problems.
Our
architecture
is
best
understood
in
layers.
A
At
the
bottom
is
what
I
call
the
Machine
layer
each
rectangle
here
is
a
physical
machine,
but
each
stack
is
a
logical
chain.
A
block
chain
from
our
perspective
is
a
highly
credible,
logical
machine
because
it's
built
out
of
massive
multi-layered
agreement.
Many
physical
machines,
where
those
physical
machines
are
spread
over
different
institutions,
are
spread
over
different
jurisdictions
so
that
there's
there's
no
no
one
party
who
can
corrupt
that
logical
mission
and
but
altogether
the
the
the
world
of
these
platforms
includes
public
block
chains
includes
private
permission.
A
Form
systems
includes
solo
machines,
so
we're
trying
to
build
a
system
that
supports
a
network
across
all
of
these
platforms
chains
and
non
chains,
public
and
private,
etc.
On
top
of
this,
we
build
our
VAT
layer
and
the
VAT
layer.
The
green
rectangles
are
vats.
Their
process
like
units
they're,
a
unit
of
synchrony
and
vats,
only
communicate
to
each
other,
a
synchronously
and
these
pipes
connecting
to
vats
those
are
secure
data
pipes
and
we
are
using
IBC,
in
fact,
for
those
secure
data
pipes.
A
A
There
is
a
tremendous
history
of
people
designing
cryptographic,
protocols,
Baddeley
that
have
subtle
flaws
in
them,
so,
rather
than
design
new
cryptographic
protocols
to
express
new
relationships,
we
want
to
invest
in
that
effort
once
to
create
a
secure,
distributed,
object
system.
So
that
our
electronic
rights
and
smart
contracting
can
be
in
this
symbolic
realm
of
objects
that
Express
the
contractual
relationships
in
this
logical
manner.
However,
the
new
rights
and
spark
contracts
are
still
a
distinct
level
of
abstraction.
On
top
of
that,
that
provides
its
own
compositionality
properties
that
we'll
see.
A
A
That
is
a
lot
of
additional
noise.
Ok
here,
I
mean
and
that
nuclear
I'll
be
coming
back
to
that.
But
that
loop
is
the
duality
of
he
writes
and
smart
contracts,
and
that's
the
key
to
the
compositionality
is
in
a
latte.
A
smart
contract
manipulates
writes,
but
a
smart
contract
also
creates
new
derived
rights
that,
in
turn,
smart
contracts
can
manipulate.
A
A
A
Now
the
initial
conditions
here
does
not
have
a
reference
to
Carol,
and
that
means
a
memory
safe
language
Bob
cannot
invoke
Carol
once
Alice
invokes
warm
up.
Passing
a
careless
perimeter.
What's
happening
is
alice
is
both
using
the
permissions.
She
has
to
invoke
Bob
in
bypassing
careless
parameter,
she's,
giving
Bob
permission
to
invoke
the
Carol.
So
there's
already
a
permission
system
at
the
core
of
the
object-oriented
programming
paradigm,
with
all
familiar.
A
To
get
it
from
objects,
object
capabilities:
all
you
have
to
do
is
probably
the
things
that
are
outside
the
object,
peridot,
any
way
that
you
have
to
say
that
this
way
of
causing
effects
of
using
references
and
invoking
other
objects.
But
this
is
the
only
way
causality
is
carried
in
the
system
and
therefore
this
graph
of
references
is
the
only
permission
system.
This
is
the
permission
system
that
you
manipulate
and
you
manipulate
it
with
the
normal
expressiveness
of
object-oriented
programming,
we're
all
familiar
with
how
to
manipulate
this
reference
graph.
A
Now
that
we
leverage
that
familiarity
so
that
you
can
take
the
normal
expressiveness
of
object-oriented
programming
to
manipulate
this
reference
graph
for
the
purpose
of
manipulating
the
Malaysia
the
permissions
relationships
in
order
to
express
security
patterns,
so
we
repeatedly
find
security
patterns,
others
think
complicated.
We
can
express
with
intuitive
straightforward.
A
We're
doing
this
in
SBS,
which
is
pure
atmosphere,
which
is
a
object
capability.
Secure
runtime
for
JavaScript
I've,
been
on
the
committee
since
the
echo
script
committee
since
2007,
getting
all
the
enablers
I
need
in
there
for
JavaScript
to
support
SAS
well
now,
SES
itself,
a
standards
write,
wonderful
thing
about
javascript
is
a
starting
point.
Is
it
has
a
clean
separation
between
the
language
which
is
essentially
purely
computational
versus
the
host
that
contributes
all
the
I/o
abilities?
A
B
C
A
A
A
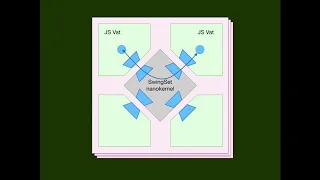
We're
going
to
start
with
multiple
vats,
a
signature
where
we
built
this
thing
called
swing
set,
which
is
analogous
to
an
operating
system.
Microkernel
called
the
swing
set
nano
kernel
and
it
stands
between
a
set
of
bats.
So
each
VAT
is
a
unit
of
synchrony,
but
the
swing
set
as
a
whole
is
the
unit
of
determinant.
B
A
Abstract
interface
between
the
vats
on
the
kernel,
anything
that
is
an
isolation
mechanism
that
speaks
that
protocol
can
plug
into
the
system.
So
we
expect
to
be
supporting
wagons.
That's
there
as
well
there.
The
comms
bat
is
the
special
one
that
enables
these
things
to
speak
over
ibc
to
other
swing
sets
running
on
other
chains,
so
our
technology
is
a
chain
and
pendant
that
cross
chain
the
first
chain
building
on
rebuilding
as
a
cosmos
zone.
A
A
So
electronic
rights
has
have
a
rich
taxonomy.
Particular
kind
of
electronic
rights
can
differ
from
each
other.
The
number
of
dimensions,
although
we
mentioned
two
from
this
table,
a
shared
versus
exclusive,
but
the
object
level
when
Alice
permits
Bob
to
invoke
Carol
or
North.
In
this
case,
that's
payment
object.
Alice
still
has
that
permission,
so
Alice
is
sharing
them
through
the.
A
Money,
for
example,
is
exclusive
and
actually
I
won't
go
into
the
others.
The
point
is
that
object
capabilities
are
specifically
the
rights
explained
in
the
left-hand
column,
whereas
new
rights,
this
new
level
of
abstraction,
be
built
out
of
objects,
covers
the
whole
taxonomy,
and
does
it
in
a
way
that
facilitates
writing
generic
smart
contracts
contract
that
can
manipulate
any
write
that
can
be
described
by
the
ER
TPP
interfaces
there's
another
way
in
which
objects
and
smart
contracts
differ
from
each
other,
which
is
the
basic
object.
Transaction
is
the
one.
A
You
know
asks
Bob
if
I
give
you
ten
dollars
now.
Can
you
hold
the
ticket
for
me
in
case
I
want
to
buy
it
from
you
before
Monday.
So
that's
logically,
a
cover
call.
This
is
the
code
to
express
it.
The
crucial
parts
of
that
code
is
those
wines
which
escrow
Bob's
rights
in
the
call
on
before
the
cover
call
exists
as
a
contract
that
Bachmann
Vitalis
participated
and
that
line
which
prevents
Bob
from
canceling
until
the
deadline
expires.
A
Yeah
the
important
thing
about
the
cover
call
as
an
example,
is
it's
a
contract
that
unfolds
over
time
every
contract
that
unfolds
over
time
creates
a
derived
value.
These
two
chairs,
on
both
sides
of
the
table,
represent
Alice's
ability
to
participate
in
the
cover
call
as
the
one
who
can
who
can
buy
the
ticket
and
Bob's
ability
to
participate.
As
the
one
who
s
wrote,
the
ticket
Alice
until
the
contract
expires
Alice
by
sitting
in
this
chair
is
in
a
valuable
position.
A
So
the
same
mechanism
that
creates
the
chair
creates
it
as
a
chair
issuer
and
all
of
these
rights
take
it,
which
is
assuming
we
can
go
fungible
chairs
with
your
specific
silver
coins.
Here,
these
contracts
are
not
specific
to
any
of
those
rights.
These
contracts
are
generic.
They
can
handle
any
of
these
rights.
A
The
escrow
exchange
written
with
knowledge
of
what
it
shared
issuers
and
the
result
is
that
these
very
generic
building
blocks
can
be
composed
together
in
the
same
kind
of
higher
order
manner
in
which,
in
a
for
example,
in
a
functional
programming,
language
or
an
object,
programming
language,
you
can
compose
functions
and
objects
together
to
get
rigid
reach.
Expressivity.
A
A
A
Right
now,
real
world
contracts,
the
underlying
technology
are,
is
prose
written
on
paper
for
expensive
lawyers
and
adjudicators
to
interpret
yeah
so
be
so
so
many
of
the
terms
of
a
real-world
contract
cannot
be
automated.
Some
of
them
can
for
contracts
that
can
be
automated
or
for
contract
portions
that
can
be
automated.
We
can
drop
bite,
bite,
bite.
Haven't
you
for
some
mechanism
be
on
chain
execution.
We
can
drop
the
transaction
costs
compared
to
lawyers
by
at
least
eight
orders
of
magnitude,
and
that
means
we
can.
C
A
The
architectural
ideas
actually
predate
watch
there
was
a
pre
watching
vision
of
smart
contracting,
but
think
the
key
thing
about
the
blockchain
technology
is
some
contracts
and
some
institutions
money
being
the
most.
The
clearest
example
really
benefit
by
running
on
a
single
logical
computer
that
has
worldwide
credibility
without
prearrangement,
and
only
what
block
chains
are
the
only
technology
we
have
I
can
achieve
that
kind
of
credibility
for
a
single,
logical,
computer,
so
contracts
that
need
that
should
run
on
blocked
roads.
A
A
Yes,
very
much
so
the
well.
What
what
we're
building
at,
especially
at
the
ERT
P
level,
is
a
rich
framework
so
that,
just
as
people
writing
applications
for
the
browser
have
rich
frameworks
like
react.
The
people
writing
applications
on
node
have
rich
frameworks,
we're
planning
to
provide
a
rich
framework
and
a
lot
of
prefabricated
contract
components
like
the
escrow
exchange
engine,
these
being
highly
reusable
composable
components.
