►
From YouTube: Antrea Community Meeting 05/08/2023
Description
Antrea Community Meeting, May 8th 2023
A
A
And
then
we
have
a
a
conversation
about
a
change
for
Windows
in
kubernetes
1.26,
where
user
space
is
being
reusable,
support
is
being
removed
from
Q
proxy
and
therefore
the
entry
proxy
will
take
over
responsibilities,
such
as
all
the
responsibilities
which
are
currently
held
by
the
cube
proxy
and
I.
Think
that
perhaps
winning
will
take
care
of
discussing
this.
That
that
is
that
correct.
B
A
D
D
D
So
that
means
that
we
cannot
use
qparency
user
space
and
mode
in
future,
and
so
we
have
to
switch
to
ensure
entry
procl.
That
is
because
there's
all
the
occupancy
has
another
mode
in
kernel
modes
on
Windows,
but
the
ensure
cannot
work
with
with
that
modes.
The
reason
it
says
and
chair
needs
to
use
open
waste
wage
extension
on
the
HS
Network,
which
was
used
for
running
pause
but
Focus
wind
kernel
modes.
It
requires
a
webp
extension.
It
is
different
from
OS
extension
and
for
the
windows
interests
Network.
D
It
requires
that
only
one
extension
can
be
enabled
on
the
single
Network.
So
that
means
we
have
to
switch
to
control
CL
and
if
we
want
to
enable
Android,
Pro
CL
on
the
Windows
nodes,
the
key
configurations
include
that
so
visually
enable
entry
process,
visual
Gates
and
we
need
to
set
policy
off
like
as
true
effects.
Entry
proxy
is
already
enabled
on
Windows
for
many
releases,
but
for
entry
proxy
proxy
all
enablement.
D
It
is
a
new
comparison
if
we
want
to
to
enable
the
process
of
feature
and
a
second
change
in
the
configuration
is
that
we
have
to
set
the
cube
or
APS
server
or
write
with
the
address
of
the
qbps
server.
Here
we
cannot
use
the
cluster
IP
service
of
the
kubernetes
service.
We
must
ensure
that
ensure
agents
can
use
this
address
to
access
the
API
server
directly.
D
D
It
is
fixed
now,
but
the
the
I
want
to
highlight
it
here
is
because
I
want
to
introduce
some
observations
and
articles,
and
the
page
is
about
it,
so
that
if
anybody
in
in
the
future
hit
the
same
issue,
maybe
it
can
switch
the
release
versions
to
to
a
newer
new
release
for
the
install.
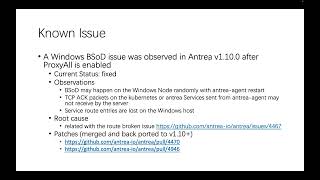
The
observations
include
that
we
absorb
results
happen
on
the
Windows
node,
randomly
with
entry
agent
restart
case.
D
In
fact
it
may
help
it
may
happen
one
way
restart
and
share
agent,
and
we
see
that
entry
agents
is
started
running
in
the
story
starts
case,
and
we
also
observe
that.
So
when
we
capture
package
on
the
server
side
on
the
kubernetes
service
or
ensure
service,
we
saw
that
some
TC
TCP
acknowledgment
packets
are
not
captured
and
on
the
server
side
here,
the
TCP
ack
packets
are
not
for
the
handshake
stage,
but
so
for
the
payload
sck
and
a
second.
D
D
There
is
a
link,
the
the
request
that
privacy
will
have
two
routines
to
process
the
logging
entries
and
once
used
to
add
the
new
service
related
routes
and
another
is
used
to
delete
the
steel
Roots
because
the
the
turbo
routines
run
in
parallel,
and
so
in
some
cases
the
new
added
results
may
be
removed
by
mistake,
but
by
the
the
other
routines.
So
in
that
case,
the
service
related
results
and
missing.
D
E
C
C
When
Edwin
mentioned,
there
was
a
an
issue
that
some
loose
may
be
deleted
by
mistake
and,
however,
today
we
also
found
that
the
issue,
or
was
also
reproducible
in
1.11.1,
which
already
takes
the
routine
deleting
problem,
but
but
that
that's
without
the
latest
patch
I
made
last
week.
So
and
after
after
that,
patch
it's
merged.
The
network
was
not
repressed
used
so
far,
so
perhaps
it's
related
to
the
traffic
that
is
being
redirected
to
open
with
switch
but
was
not
handed
because
anthroprocy
hasn't
installed.
C
The
open
flows
for
the
service
IPS
on
Windows,
the
OS
user
space
runs
no
no
didn't
run,
as
doesn't
run
as
part
of
the
Android
port.
It's
a
standalone
process,
so
we
thought
that
U.N
will
restart
entry
agent.
The
service
flows
should
be
there
and
should
be
installed
by
the
last
round,
should
still
be
there
and
should
be
able
to
continue
processing
the
traffic
to
the
service.
C
However,
after
some
tests
we
found
that
after
Android
agent
starts
up
and
the
service
flows
are
gone
and
I
found
that
it's
because
the
service
group
we
have
a
service
group
coming
up
on
Android
agent,
startup
and
that
operation
cleans
up
all
Service
Groups
open,
Flow
groups
in
open
with
switch,
and
you
know
the
service
entry
proxy
depends
on
the
service
group
and
even
the
open
flows
referring
to
that
groups
will
be
directed
deleted.
So
it
didn't
work
as
we
expect
every
time
Android
agent
starts
up
and
there
is
a
Time
window.
C
The
service,
the
the
traffic
to
the
service
IP,
will
not
be
processed
correctly
and
will
be
treated
as
normal
traffic
towards
external
IPS,
because
they
are
not
poor
IPS
and
they
are
not
node
IPS.
So
we
we
treat
them
as
an
external
IPS
and
perhaps
the
final,
the
the
final
action
of
that
those
traffic
will
be
again
redirected
to
and
took
it
away,
interface
from
open
research.
C
In
this
situation,
there
may
be
a
circle
that,
in
the
hosted
network
name
space,
we
install
loots
to
redirect
traffic
towards
the
service
IP
to
open
with
switch,
but
in
open
with
switch
before
answer
plus
it's
ready.
We
redirect
the
traffic
back
to
the
host
Network
namespace
and
we
don't
know
whether
this
cause
problems
on
Linux
yet,
but
on
Windows.
This
may
cause
the
some
very
high
CPU
usage
and
the
manual
usage
and
eventually
leads
to
system
crash.
C
That's
our
server,
but
we
haven't
plugged
it
yet,
and
maybe
we
we
should
also
check
our
Linux
houses,
will
Behavior
and
the
the
key
of
the
latest
patch
is
that
we
only
generate
the
traffic
towards
the
service
IP
after
answer
plus
is
ready.
This
guarantees
that
if
the
anti-agented
generates
a
package
to
service
IP,
it
will
be
redirected
to
open
with
switch
and
the
new
open
switch.
It
will
always
be
processed
correctly
and
netted
to
one
of
the
endpoint.
C
And
perhaps
this
may
indicate
some
other
potential
issues,
because
we
in
the
latest
release,
1.11
and
all
release
after
that
we
use
a
single
bigger
cluster,
IP,
say
IDR
to
as
the
destination
IP
of
the
loot
for
service
IPS,
which
means
that,
for
example,
if
the
services
IDR
we
got,
we
calculated
is
10.96
dota
0.0
and
if
the,
if
the
agent
or
any
port
tries
to
access
one
service
IP
one
one
IP
in
that
block.
But
it
is
not
a
real
service.
Ip.
The
package
may
be
Circle.
C
C
And
that's
one
General
issue:
we
need
to
further
investigate
under
one.
Not
another
potential
issue
is
that
previously
we
thought
that
the
open
waste
the
open
flows
will
be
kept,
will
will
be
kept
on
and
their
agent
start,
but
it
seems
that
it
will
be
removed.
So
if
some
traffic
needs
the
the
flows
installed
by
Android
proxy,
we
need
to
ensure
the
all
of
them
must
be
run
after
enter
browsing.
A
Three
two
and
the
time's
up.
Okay,
so
we
know
what's
the
status
here
and
what
we
need
to
do
and
I
have
to
say
it's
probably
not
the
feature
that
we
were
looking
to
develop
about.
It
doesn't
seem
that
we
have
any
any
choice
here.
We
have
to
do
it
all
right,
so
maybe
we
can
move
to
the
general
update
on
the
1.12
release,
Channel.
C
C
C
Has
we
I
think
we
just
missed
this
handling
this
field
and
it's
not
by
intention
and
and
follow
the
problem
by
running
some
kubernetes
config
Network
tests,
the
the
each
service
could
have
a
one
one
or
more
external
IPS,
in
defined
in
its
spec
and
in
Q
crossy,
they
also
or
proxy,
and
these
IPS,
and
by
this
patch
12
plus
it
will
do
the
same
and
I
have
reviewed
this
patch
I
think
there's
no
risk
for
this
one.
It's
a
simple
change
and
another
is
a
behavioral
change
in
anthropology.
C
C
C
Okay,
then,
let
me
simply
describe
the
the
change
is
about
how
we
handle
the
traffic
from
Port
and
from
external
I.
Think
this
patch
changes
the
behavior
to
align
with
the
cube
losses
that
it
always
learn
and
balance
the
traffic
from
local
port
to
external
IP
or
node
port
to
the
to
the
whole
cluster.
C
Instead
of
respecting
the
the
external
traffic
of
the
service,
Eastern
traffic
policy
of
the
policy,
the
the
reasoning
behind
it
is
if
there
is
no
short
circuit
circuiting,
the
the
packets
will
reach
the
external
loan
advance
and
we
are
eventually
be
distributed
to
endpoints
across
the
whole
cluster.
So
when
Andrea
policy
does
proxy
the
external
IPS,
you
should
do
the
same
instead
of
only
browsing
to
local
endpoints,
I
think
and
it's
the
current
Q
process
behavior
and
is
defined
in
Signet
Network
test
and
the
second
major
error
is
narrow
policy.
C
We
had
a
fourth
Futures
Improvement
in
this
era
and
the
first
I
think
is
to
support
IP
based
group,
Association,
quality,
API
and
unfortunately,
I
I
didn't
get
enough
time
to
review
this
part.
So
far,
and
it's
on
my
list-
and
perhaps
I
will
do
it
in
today-
yeah
and
any
reviews
from
the
other
reviews
and
maintenance
are
welcome
and
currently
I
think
we
we,
the
dispatches,
are
lockable
reviews
and
the
second
is
for
user
requested
requested
feature:
adding
low
label
log
label
to
the.
A
C
C
And
so
do
the
so.
The
part
I
think
this
is
to
keep
in
line
with
some
networking
firewall
products.
That
user
could
also
match
the
source
ports
in
net
policy
API-
and
this
is
the
last
one-
is
to
implement
the
propose,
the
future
by
Upstream
Network
policy,
with
two
apis
I
think
and
according
to
Yang
I
think
the
fastest
race
should
be
Pro
prioritized
and
the
last
one
may
need
more
more
review
effort,
because
it's
a
big
change.
E
C
C
C
And
I
think
this
one
yeah
this
doesn't
introduce
new
features
but
to
make
the
code
more
robust
in
some
scenario
that
we
didn't
need
even
need
the
if
some
API
service
and
web
hooks
and
the
last
one
is
a
big
Improvement
in
the
memory
usage
of
financial
agent.
It
removes
some
unnecessary
cash
for
anti-agent
and
I.
Think
the
Implement
is
about
100
megabits
and
more
megabits
memory
reduction
reduction
with
this
number
of
open
Flow
entries.
C
C
And
Nest
is
about
test.
We
have
three
PRS
for
newly
tested
for
these
packages
again
and
I
guess
they
have
been
differed
several
times
from,
for
example,
this
one
it
has
been
nearly
half
a
year.
So
maybe
let's
try
to
include
them
in
this
release
and
I
see
this
one
has
already
been
upload,
so
no,
there
should
be
no
risk
for
this
one
and
the
last
one
is
a
documentation
Improvement
for
using
Android
with
Rancho,
Crafter,
I
I,
guess
no
real
risk
for
this
one.
B
C
Yeah,
it's
a
small
change.
Okay,
that's
the
current
status
of
we
will
enter
release,
one
daughter,
cow,
yeah,
I,
I,
guess
we'll.
We
we
need
to
improve
the
efficiency
of
reviewing
under
spend
more
time
on
it.
I
will
also
spend
more
time
in
the
following
two
weeks.
Currently
we
have
two
days
or
two
weeks
and
one
day
left
for
for
the
release.
A
A
A
Three
two
one
zero,
and
so
it
might
be
all
for
today.
So
it
seems
that
this
might
be
the
end
of
today's
meeting
and
I
would
like
to
thank
wening
and
China
for
bringing
up
the
topics
for
discussion
today,
and
we
will
meet
again
in
two
weeks
time.
So
thanks
a
lot
for
joining
and
I
wish
everybody
a
great
evening
or
a
good
afternoon.
