►
From YouTube: Antrea Community Meeting 07/17/2023
Description
Antrea Community Meeting, July 17th 2023
A
Good
morning,
good
afternoon
good
evening
and
welcome
to
the
assistance
of
the
entry
of
committee
meeting
today
is
Tuesday
July
18th
and
we
have
two
presentations
into
the
agenda.
The
first
one
will
be
a
presentation
about
a
new
way
of
tunneling
traffic
between
us,
which
is
a
I
think
it's
called
xmask
I'm,
not
sure
if
I
pronounce
it
correctly
and
this
presentation
will
be
given
by
Shanghai.
A
B
B
Okay,
okay,
hello,
everyone,
I'm
Michelle
Helen
from
Shanghai,
Children
University
and
my
supervisor
is
student
Zhao
today
I'm
going
to
introduce
my
latest
research
xmask
to
you,
all
I
will
show
the
research
background,
the
design
of
Max
mask
and
the
evaluation
of
it.
In
this
talk,
as
we
know,
there
are
many
kinds
of
container
networks
in
the
host
Network
in
the
host
Network
containers,
Shire,
the
host
Network
namespace
and
the
host
IEP.
B
You
can
get
performers
that
are
close
to
the
barometer
Network,
but
the
containers
need
to
coordinate
ports
with
other
containers,
then
make
wheeler
and
IPL
can
emulate
virtual
mix
in
the
containers
and
also
guide
performance
that
are
close
to
the
biomedal
network.
But
under
the
network
needs
to
be
able
to
root
the
container
IP
and
the
bridge
Network,
which
is
called
no
income
mode
in
entry.
Each
each
container
has
its
own
IP,
its
own
IP
and
a
container
packets
are
directly
forwarded
into
the
Android
network.
B
The
annular
network
is
also
needed
to
be
able
to
root.
The
container
IP
in
conclusion
of
the
three
networks
can
offer
near
native
performance
but
hurt
the
flexibility
of
the
application
and
under
the
network
and
another
Choice
from
academic
Community
is
Slim.
It
shares
the
socket
of
the
root
namespace
to
the
container,
and
thus
the
containers
can
use
another
another
stack
directly
and
it
can
also
it
can
also
achieve
the
performance
close
to
the
biometric
network,
but
its
only
supports
a
connection
based
protocols,
for
example
TCP.
B
Another
common
choice
is
the
overall
Network.
It
builds
a
virtual
Network
above
the
physical
Network,
which
provides
for
a
full
flexibility
and
University
for
containers,
but
it
incurs
significant
communication.
Over
height
they
evaluate
the
gcps
throughput
tcpr
and
the
CPU
utilization,
with
different
number
of
parallel
flows.
I'll
show
you
the
result
compiled
with
the
host
Network.
B
We
use
the
perf
tool
to
start
the
circuit
time
of
each
part
of
in
the
this
first
and
we
find
that
about
half
of
the
CPU
time
is
taken
up
in
the
extra
data
parts.
We
call
this
extra
overhead
and,
according
to
the
analysis
of
the
database,
we
can
classify
the
extra
overhead
into
three
classes
that
are
encapsulating
intra
host
loading
and
policy
enforcement,
so
convey
cache
the
results
of
this
overhead.
The
answer
is
yes,
and
this
is
what
xmask
does.
B
B
To
avoid
repetitive
processing
on
packets-
and
this
is
the
architecture
of
xmask
xmask,
caches
results
of
encapsulating,
intercost,
routing
and
again
the
egress
and
Ingress
cache
and
the
policy
results
of
policy
enforcing
in
the
policy
cache.
The
results
of
encapsulating
and
routing
are
cured
by
a
part
destination
IP
and
the
policy
enforcement
result
is
accurate
by
the
five
factorial
of
the
flow
here
denotes
blocking,
as
a
cache
will
only
support
the
stateless
policies.
B
We
also
need
four
programs
to
implement
the
five
functionalities
to
make
them
easy
to
be
deployed
in
the
kernel.
We
implement
this
programs
by
evpf,
ictc,
hawk
and
ice
for
the
programs,
the
egress
and
Ingress
program,
curator
caches
and
operate
on
the
package
and
the
egress
intro
program
and
the
Ingress
in
the
program
handles
cash,
Mis,
caches
cases
and
the
forwarding
of
the
package
relies
on
a
redirect
which
can
skip
all
the
overhead
on
the
data
parts
and
besides,
we
also
need
two
user
space
programs.
B
As
user
interface
and
diamond,
then
I
will
introduce
the
design
of
xmask
in
following
three
aspects:
first,
to
maintain
the
cache
transparency,
and
we
should
make
sure
that
xmask
is
transparent
to
both
applications
and
the
underlying
Network.
The
Ingress
pass
I
mean
hook.
The
equalized
program
on
the
hot
host
side
of
the
way
is
file
here.
The
program
accurate,
the
cache
and
handles
the
egress
package
from
the
containers.
B
B
Finally,
if
the
policy
cache
shows
that
the
flow
is
a
load
to
egress,
then
the
egress
program
will
redirect
the
packet
to
the
physical
needs
and
the
Ingress
program
does
a
similar
thing
on
the
receiving
of
a
website
packet.
The
Ingress
program,
first
curates,
the
cache,
then
the
program
strip
strips
the
auto
wixon
headers
and
update
the
website,
the
mic
header.
B
The
egress
program
uses
TC
redirect
and
which
can
redirect
package
or
package
from
PC
Ingress
to
TCA
egress
and
the
Ingress
program
uses
the
redirect
function
called
PC
redirect
peer,
which
can
redirect
package
from
CC
Ingress
to
TC,
Ingress
and
as
and
to
fully
authorize
the
power
of
redirect.
We
added
a
helper
function
to
the
kernel
which
can
redirect
package
from
TC
egress
to
TCA
egress
and
with
this
for
hyper
function,
the
egress
program
can
handle
the
packets
earlier
and
just
eliminate
the
next
space
from
versing
overhead
and
in
the
following
discussion.
B
Xmas
uses
this
uses
this
optional
Improvement
by
default,
and
another
important
design
issue
is
how
to
handling
and
the
cache
misses.
Xmask
initialized
the
caches
with
the
help
of
the
standard
of
the
network,
for
example,
entry
for
the
egress
Parts.
If
cache
misses
happens
on
in
as
a
request
program,
either
the
egress
cache
or
the
policy
cache.
The
program
will
Mark
the
packet
and
pass
it
to
the
older
Network,
for
example,
entry
and
then
it
will
be
normally
processed
by
the
overlay
Network
and
arrived
at
the
equalized
of
the
physical
Clinic.
B
Here
the
egress
int
program
starts
the
initialization
process
and
it
will
update
the
auto
headers
and
the
interface
index
as
the
value
of
the
port
destination
IP
to
the
egress
cache
and
mark
the
flow
as
a
load
in
the
policy
cache
and,
and
now
finish,
the
initialized
process
and
the
Ingress
path
performs.
That's
the
same.
B
The
Ingress
program
marks
the
package
on
Cache
missing
and
the
Ingress
int
program,
initialize,
the
Ingress
cache
and
the
policy
cache
and
to
properly
cooperate
with
the
connection
track
module
in
Cache
Miss
handling,
and
we
should
make
sure
that
the
egress
and
Ingress
pass
performs
the
same
for
the
same
flow
that
is
either
boss
goes
through
xmask
or
boss
goes
through
the
only
Network,
so
the
solution
is
xmask
only
process
the
packets
reinforce,
Ingress
and
egress
are
cached
and
the
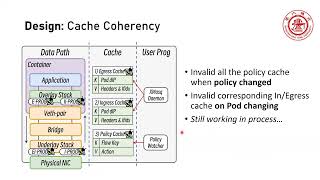
third
part
of
the
design
is
cache
coherency.
Here.
B
It
means
that
the
cash
should
perform
correctly
when
the
overlay
Network
changes.
For
example,
when
the
ports
are
deleted
or
policies
are
updated.
The
cache
must
change
accordingly,
and
currently
we
make
Xmas
to
invalid
all
the
all
the
policy
cache
when
policy
change
and
invalid
the
corresponding
Ingress
or
equals
cash
on
Port
changing,
and
we
are
still
working
in
process
on
this
part,
and
so
this,
the
design
of
box,
mask
any
questions.
B
A
B
Xmask
improves
the
transaction
rate
by
at
most
105
percent
and
weights
and
the
CPU
utilization
at
most
22
percent,
lower
again
compiled
with
Android
for
UDP
experiments.
The
results
shows
that
Xmas
improves
the
throughput
by
at
most
54
on
the
transitional
rate.
By
at
most
63
and
in
both
experiments.
B
The
CPU
utilization
is
very
close
to
anterior
and
we
also
evaluate
whether
the
new
redirect
hyper
function
brings
performance
Improvement,
but
unfortunately,
the
support
are
and
the
CPU
utilization
remains
almost
the
same
weights
always
out
the
new
redirect
helper
function,
and
then
we
evaluate
tax
must
on
some
popular
distributed
application
and
for
memcache
D.
The
average
relationship
is
29
lower
with
xmask,
while
the
soft
irq
utilization
is
60
lower
compared
to
entry.
B
The
average
latency
is
26
percent
lower
with
xmask,
while
the
soft
irq
utilization
is
44,
lower
compared
to
anterior
and
finally
for
engines,
May
evaluate
the
HTTP
1
and
HTTP
3
latency
for
hdv1.
The
image
relationship
is
29
percent
lower
right.
The
software
IQ
utilization
is
98
lower
compared
to
entry
and
for
HTTP
3.
The
software
interrupt
utilization
is
97
lower,
while
the
latency
Remains
the
Same
and,
in
conclusion,
by
introduce
cash
to
the
already
Network
Xmas,
can
miss
all
the
important
requirements,
including
performance,
flexibility
and
universality.
A
B
Oh,
thank
you
for
your
questions
and
actually
I
must
is
at
first.
Atmos
is
not
a
CMI,
and
it's
actually
like
a
plugin
of
cni,
for
example,
and
trip
and
xmask
is
implemented
by
eppf
and
and
the
evpf
can
just
plug
in
into
the
kernel
and
without
a
result,
notice
to
the
cni
or
the
application,
and
it
can
just
cooperate
properly
with
unsure
result
and
changed
by
and
share.
A
Yeah
yeah
I
believe
so,
basically,
you
can
deploy
X
Mask
completely
transparently
to
Andrea.
So
basically
you
don't
need
to
have
a
code
in
antria.
That
is
aware
that
xmask
is
running
like
changing
the
configuration
of
Entry
or
for
enabling
xmask.
That's
that's
not
needed,
and
similarly
xmask
will
be
able
to
work,
for
instance,
both
with
Andrea
and
Calico,
depending
on
which
cni
the
kubernetes
cluster
is
running.
D
E
E
E
B
F
G
B
B
H
G
H
B
B
I
I
B
I
B
Yes,
yes,
currently,
it
is
handled
by
actually
in
the
cache
Miss
in
the
cashmere's
handling
case,
the
egress,
the
egress
in,
for
example,
regress
int
program,
only
initialize
cash.
If
the
the
egressing
package
is
a
wasteland
packet
and
only
only
a
wix9ine
packet
could
have
have
its
Port
destination
IP
in
the
cache
and
in
the
egress
program
it
if
it
couldn't
find
the
cash
and
the
egress
program
will
don't
handle
it
and
all
the
external
package
it
will
just
pass
to
the,
for
example,
entry
apparently
I
have
noticed
by
this
way.
I
I
D
B
B
F
J
J
Then
you
sort
of
like
let
the
entry
determine
whether
the
policy
should
be
connected
or
dropped,
and
you
learned
that
just
put
in
the
policy
cache
now
you're
also
saying
that
if
there
were
any
policy
changes,
this
become
obsolete,
because
you
know
you,
you
don't
want
to
use
the
policy
cache
again
I'm,
just
wondering
how
do
you
actually
detect?
There
is
a
policy
change
in
that
case.
B
That's
a
good
question
and
we
are
still
working
this
in
process
and
currently,
in
my
in
my
mind,
I
think.
Maybe
we
should
monitor
the
commands
of,
for
example,
saying
I,
for
example,
I'm
sure
and
if
there's
a
new
command
and
we
should
evaluate
all
the
cash
and
this
still
working
process
will
have.
We
have
not
finished
this
design.
J
Okay,
okay,
thanks
because,
because
from
from
my
point
of
view,
I'm
thinking
that
you
know
the
policy
changes
do
happen
right
and
and
also
I
wanted
to.
Also,
you
know
stress
on
the
visibility
here,
because
from
my
understanding,
if
the
policy
do
change
and
there's
nothing,
the
policy
catch
doesn't
alter
at
all,
it
will
cause
a
packet.
You
know
maybe
to
drop,
to
be
dropped
and
and
try
to
even
know
about
it
right
now.
People
will
be
wondering
why
this
is
job
that
now
you
know
they
need
to
know
about.
J
B
J
D
B
They
don't
know
if
of
unless
you
manage
that
and
sure
May
deploy
many
complex
policies
and
some
flow
may
be
effected
by
a
new
policy
that
that
that's
just
deployed
to
the
interior
and
maybe
even
sure
it
should
be
denied,
but
in
unsure
the
xmask.
It
does
not
know
so.
I.
Think
in
this
inter
scenario.
We
should
invalid
the
cash
and
yes.
B
B
J
F
D
D
D
H
B
F
B
I
D
G
C
May
I
ask
what's
the
future
plan
for
this
project,
for
example?
To
do
you?
Do
you
want
to
make
this
project
a
generous
solution
for
all
singers,
like
Calico,
so
I
know
they
are
they
have
like
using
EBV?
So
do
you
plan
to
like
to
make
this
project
can
works
with
CDM
or
caracal
or
or
you
you
plan
to
like
develop
more
features
for
for
projects
like
I'm,
sure,
I
I,
wonder,
what's
the
yeah
what's
the
plan,
what
was
the
future
design.
B
Well,
plan
forces
to
first
I
I
want
to
calculate
this
project
with,
for
example,
in
cheer
and
for
sending
because
this
evpf
complex.
So
we
may
remember
what
contests
later
and
first
I
want
to
solve
the
problems
that
mentioned
before,
for
example,
service
to
Port
communication
and
some
don't
and
cooperate
with
other
features,
yeah
and
sure
and
communication
with
equalized
and
so
on,
and
so
Calvary
series
sitting,
maybe
later
later
solution
later
twice.
B
Because,
because
in
cash
in
my
understanding
in
cash,
the
cash
only
supports
the
stateless
cash
and,
of
course,
if
you
want
to
support
stateful
policies,
and
you
can
encode
the
state
into
the
so-called
flowkey
and
follow
key
and
convert
the
policy
to
a
status
policy.
And
and
now,
if
xmask,
can
support
the
state
for
policies.
B
I
A
All
right,
so
that
was
a
great
presentation
and
a
lot
of
very
good
questions,
but
unfortunately
we
also
have
another
topic
to
discuss
for
today.
So
I
have
to
ask
if
there
is
a
any
final
question
for
Shanghai,
please
ask
now.
Otherwise
we
can
always
follow
up
in
the
entria
channel
in
the
kubernetes
block
and
Shanghai
I.
Don't
know
if
you
already
joined
the
channel,
but
you
know
if
you
are
there,
there
should
be
some
follow-up
with
the
members
of
gentria
Team
concerning
how
to
integrate
xmask
in
Andrea.
A
G
G
Thanks
hello,
everyone
so
I,
come
out
of
this
will
deliver
a
short
presentation
on
this
topic
and
to
have
Windows
obvious
containerization,
and
it
is
a
container
D
runtime
only
so
the
motivation
of
this
task
is
currently
Windows.
Obvious
is
running
as
a
host
service,
rather
than
inside
container
that
we
have
in
Linux.
So
it
is
different
from
that.
G
One
thing
is
different
from
Linux
is
that
the
OBS
driver
should
be
configured
on
the
Windows
node
before
before
installing
the
entry
agent
pod,
so
that
would
be
done
through
Scripts,
so
that
is
done
currently,
but
currently
also,
the
user
space
OBS
processes
are
started
as
a
Windows
service
on
the
Windows
node.
But
now,
if
we
want
to
run
the
OBS
user
space
processes
inside
the
container,
then
only
OBS
driver
would
be
installed
on
the
Windows
node
in
kernel.
G
G
Few
things
we
had
while
doing
this,
a
new
windows,
obvious
image,
was
created
for
anti-obvious
container
Windows
container.
We
had
new
windows
OBS
image
based
on
server
core,
because
OBS
user
space
processes
had
some
dependencies,
such
as
openssl
and
VC
redist,
and
that
were
not
able
to
run
on
the
image
based
on
Nano
server
So.
Currently,
entry
of
Windows
base
image
is
based
on
Nano
server
and
on
that
we
cannot
have
the
dependencies
of
the
OBS
which
are
required
to
run
the
vs
command.
So
we
needed
a
base
image
based
on
server
core.
G
Another
thing
is
that
the
when
the
obvious
process
has
start
for
the
first
time
there
is
a
com.db
file
configuration
file
for
OBS,
so
this
file
is
not
stored
on
the
container.
This
file
is
created
and
stored
on
the
Windows
host
to
ensure
that
the
OBS
Port
information
won't
be
deleted.
So
when
first
time
obvious
container
starts
so
it
first
checks
that
whether
the
con.db
file
is
present
or
not
on
a
specific
path
on
the
host
that
is
on
the
Windows
node.
G
If
that
con.db
file
is
not
present,
it
will
create
it,
and
if
it
is
already
present,
it
would
use
that.
So
in
restart
case,
we
would
use
the
existing
com.db
file
and
not
create
the
new
one
and
if
it's
and
if
the
obvious
container
is
starting
for
the
first
time
on
that
node,
then
new
con.db
file
would
be
created.
K
G
We
can
do
that,
but
there's
a
huge
difference
between
the
size
of
server
core
and
Nano
server.
So
if
we
are
ready
to
go
with
that,
and
then
we
can
do
that
because
the
currently
the
base
image
in
the
Nano
server
is
also
used
for
other
two
yamls
which
we
have
and
we
have
windows.yml
and
antria
windows
container
data
timer.
In
that
case
we
don't
support
running
obvious
inside
the
container,
so
it
would
be
useless
to
have
OBS
processors
in
that
image.
G
If
we
want
to
have
same
image
for
both,
then
we
need
to
maintain
two
base
images,
one
with
the
current
one
and
another
base
image
with
the
server
core,
so
maintainability
would
be
little
difficult
then,
and
the
size
would
be
size
anyway.
Currently
also
anyone
would
not
run
only
entry
agent
container.
G
G
A
And
it
appears
that
we
don't
have
another
question,
since
we
have
a
few
minutes
in
a
more
available
into
this
meeting.
If
you
have
any
other
topic
that
you
would
like
to
bring
up
or
I
don't
know,
perhaps
any
other
question
regarding
the
xmask
presentation
that
we've
just
saw
please
go
ahead.
I
will
wait
as
usual
about
30
seconds,
for
you
to
ask
any
question
or
bring
up
any
additional
topic.
If
not
we'll
close
the
meeting
here.
A
Alright,
it
appears,
then
there
are
no
more
points,
no
more
questions
for
today,
so
that
might
be
all
for
today,
thanks
as
usual
for
attending
it,
and,
most
importantly,
thanks
for
to
these
presenters
for
their
contribution
and
I
wish
everyone
a
good
afternoon,
good
day
or
a
good
evening,
or
in
the
case,
for
the,
for
example,
good
night.
Thanks
a
lot
for
attending
and
talk
to
you
in
two
weeks
time.
