►
From YouTube: Antrea Community Meeting 04/11/2022
Description
Antrea Community Meeting, April 11th 2022
A
So
good
morning
and
good
afternoon
or
good
evening,
this
is
the
anthia
community
meeting
and
today
is
tuesday
april
the
12th,
of
course,
for
some
of
you
it
will
be
still
monday
april
11th
for
today,
as
you
can
already
see
on
the
screen,
we
have
a
very
interesting
presentation
from
chan
about
a
proposal
for
traffic
control
capacity
and
very
interested
to
hear
about
it.
So
without
waiting.
Please
change.
Go
ahead.
B
Another
way
is
that
you,
you
need
to
run
a
demon
set
which
have
a
host
network
demonstrate
a
dim
set
with
the
host
network
mode
ports,
and
you
need
to
run
that
that
port
on
specific
node
and
as
there
you
need
the
privilege
to
capture
the
traffic
from
specific
interfaces.
So
it's
not
quite
easy
to
for
for
troubleshooting.
B
B
Today
there
is
no
way
to
deploy
a
network
protect
protection
mechanism
and
to
to
to
intercept
the
north
to
to
intercept
the
east
west
traffic.
Maybe
you
could
deploy
such
software
or
hardware
at
the
edge
node
of
your
network,
but
you
cannot
intercept
the
class
and
the
in-class
traffic,
so
it
would
it
will.
It
would
be
great
if
we
can
provide
such
capacity
and
reserve.
B
Is
that,
as
mentioned
about
in?
If
we
don't
have
this
capacity,
user
can
only
intercept
the
north
south
traffic,
but
not
is
the
west
traffic,
so
we
propose
to
add
a
traffic
control
api
using
the
id
and
the
traffic
control.
Api
accepts
clients
request
about
the
the
desired
behavior
of
phone
users
to
control
the
poor
traffic
with
open
flow
lures.
B
B
We
can
also
support
a
local
port
for
the
scenario
that
the
network
analyzer
is
running
on
each
node
directory,
so
we
can
just
create
an
o
open
with
internal
port
and
redirect
the
traffic
to
that
port.
Then
the
network
analyzer
could
listen
to
the
internal
part
directory
and
the
product
could
be
can
also
be
a
physical,
physical,
nic
or
a
waste
pair
if
the
application
is
running
in
another
named
network
namespace.
B
B
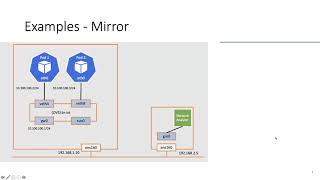
For
example,
the
port
is
a
fake
technique
or
is
a
user-created
us
device,
and
the
peer
name
is
used
to
represent
the
name
of
the
pr
device
from
which
the
traffic
will
be
sent
back
to
os.
It
should
only
be
set
for
a
direct
action
for
me
reaction.
This
is
not
needed,
because
we
only
need
to
mirror
the
traffic
to
the
traffic
destination,
but
for
redirect
action
we
need
to
because
there
is
no
copy.
B
The
traffic
is
directed
directly
redirected
to
the
traffic
destination
and
after
a
network
firewall
process
it
it
may
drop
it
or
it
may
allow
it.
So
even
it
will
need
to
send
the
traffic
back
to
the
pipeline
after
it
process
it.
So
we
need
to
know
which
device
it
will
come
back
for
so
that's
the
purpose
of
this
field
and
for
remote
kind
of
for
remote
network
analyzers,
and
we
provide
two
kinds
of
destinations.
B
C
B
B
Yeah
in
this
proposal,
both
scenarios
are
supported.
If
users
don't
want
to
create
their
own
product,
meaning
that
they
don't
want
to
deal
with
anything
related
to
open
with
switch.
Otherwise
they
want,
they
need
to
mount
open
with
way
open
with
switch
database
and
the
circuit,
and
they
need
to
manage
open
with
switch.
So
that's
one
scenario,
so
we
provide
this
internal
property.
You
can
set
it
to
true.
B
B
B
C
B
C
B
I
can
think
of
of
why
use
the
case
of
in
kubernetes
that
you
have.
You
can
create
a
host
path,
volume
and
the
host
path.
Volume
can
be
type
of
directory
and
a
file
and
or
even
circuit
file
and
the
different
ports
can
use
same
host
path
volume.
But
if
you
create
one
volume
in
one
port
saying
this
volume
should
be
directory
and
in
another
port
you
see
this
port
should
be
a
file,
then
they
they
will
have
same
situation
they
conflict.
B
C
C
B
B
C
B
Yeah,
that's
one
way
yeah,
but
I
I
I
also
discussed
this
with
only
and
when
she
that
that's
actually
my
original
proposal,
but
I
feel
if
we
I
was
not
thinking
about
conflict
map.
I
was
thinking
about
the
configuration
of
android
agent,
but
that
when
we
use
the
one
to
use
it,
we
need
to
use
it
where
need
to
configure
the
configmap
and
restart
android
agent.
It's
a
little
different
from
a
config
map
describing
the
tunnel
this
destination
or
a
conflict
map
for
all
possible
traffic
destination.
B
C
Yeah,
I
got
it
again.
I
think
my
my
only
important
if
later
reason
is
policy
will
be
like
security
policy.
You
can
have
many
policies
and
then,
with
different
matching
rules
for
the
share
one
point,
then
it's
become
little.
I
don't
know
at
least
I
feel
it's
probably
not
very
straightforward
to
try
to
share
the
port.
Let's,
let's
let
me
think
about
that,
and
then
we
can
do
a
flight
on
it.
B
B
B
One
part
the
receiving
port
is
named,
firewall,
0
and
internal
set
to
two
means.
We
need
to
create
this
open,
this
pose
as
a
os
internal
port,
and
we
will
also
create
another
port
os
internal
port
named
the
firewall
one,
and
then
user
click
could
deploy
network
firewall
in
in
line
mode,
meaning
that
it
could
receive
one
receive
traffic
from
one
interface
and
decide
whether
you
want
to
drop
it.
If
we
drop
it,
the
traffic
will
not
send
back
to
the
pipeline.
B
B
B
After
that
country
agent
will
handle
the
traffic
control
resource.
It
will
create
or
update
the
port
for
tunnel
destination
if
it
does
not
exist
or
if
it
changes
anywhere.
It
will
filter
ports
running
on
its
own
node,
based
on
the
specifying
the
label
selectors
and
get
their
open
flow
port
ids,
and
then
it
will
call
open
flow
interfaces
to
install
or
uninstall
lures,
which
mirrors
or
redirects
traffic
of
the
selected
ports
and
for
display
implement
data
implementation.
B
B
Update
the
open
flow
loss
to
output
the
traffic
we
are
interested
in
to
one
more
destination,
so
the
benefits
of
such
approach
is
that
we
can
filter
traffic
based
on
protocol
port
and
iphones
and
because
there
is
no
native
support
for
traffic
redirect
traffic
redirecting
if
we
use
flow
based
mirroring,
we
can
unify
the
approach
for
mirroring
and
redirecting
the
traffic
classifying
code
will
be
shared.
The
only
difference
between
these
actions
is
that
how
the
action,
the
open
flow
action
or
for
of
their
corresponding
for
the
corresponding
traffic
control
apis
objects.
B
B
B
B
B
B
B
That's
the
current
plan,
and
I
also
have
some
open
questions.
First
thing
is
about
the
api
name.
Currently
I
name
it
traffic
control,
but
I
think,
maybe
is
too
large
for
what
the
api
actually
does,
because
in
linux,
traffic
control
tool
can
do
many
things
mirror
and
traffic
is
only
one
feature
of
it.
So
another
proposal
I
have
is
quite
a
mirrored
is
corresponding
to
tc
mirrored
function,
or
maybe
we
could
use
two
different
apis
for
mirroring
and
redirecting
separately
so
that
it
this
object.
B
Api
name
can
be
more
specific
for
its
for
its
purpose,
and
another
question
is
about
what
should
we
do
for
directions,
whether
where
the
traffic,
whether
we
should
treat
it
state,
4
way,
meaning
that
when
direction
is
ingress,
should
it
cover
the
should
it
cover
incoming
traffic?
Only
or
should
it
cover
the
outgoing
response?
A
I
just
think
that
we
should
not
use
something
which
maps
a
specific
utility
or
maybe
not
something
that
is
mapped
to
dc
mirrored
mostly
because
most
people
don't
even
know
what
it
is,
but
something
like
traffic
controller
perhaps
is
kind
of
nice.
Then
you
know
naming
everyone
can
have
a
different
opinion.
A
B
For
validation,
for
example,
to
edit
the
mirror
feature,
we
just
need
to
run
long
long,
remote
for
free.
This
can
even
be
a
kubernetes
node.
We
are
managing
the
ci
is
managing
and
it
could
we
could
capture
traffic
or
just
count
the
package
number
of
specific
interface
to
see
whether
it
received
the
traffic.
A
B
And
for
redirecting,
I
think,
maybe
sam,
we
could
create
such
an
object
in
in
a
test,
and
then
we
just
use
a
os
pair
device
to
connect
this
to
interfaces.
Then
the
original
package
would
will
still
go
back
to
the
os
pipeline
directly
without
being
dropped.
Then
we
can
count
whether
the
number
of
the
packets
are
same
as
the
number
of
the
traffic
between
the
two
ports.
C
C
B
I
think
so
because
currently
you
went
to
support
state
four
we
need
to.
We
need
some
actual
status
to
be
come
to
be
stored
in
connection
track.
Otherwise
we
don't
know
whether
this
is
a
response
traffic.
If
it
is,
if
we
only
need
to
support
stateless,
I
think
we
don't
need
to
start
anything
in
city.
C
C
B
B
C
C
B
C
D
Yeah
in
that
case
I
was,
I
was
going
to
ask
the
question:
have
we
entertained
the
option
of
having
the
destination
to
destination
as
a
separate
crd
itself?
I
mean
I
feel
like
there's
enough
information
for
it
to
be
a
standalone
resource,
and
then,
if
we
were
talking
about
us
some
tunnel,
we
can
definitely,
you
know
just
define
a
crd.
Just
referring
to
this
is
a
destination
created
for
this
tunnel
and
the
other
resources
can
just
refer
to
it
by
name
just
like
the
cluster
group.
B
B
D
C
C
C
B
A
I
guess
we
can
interpret
this
silence
as
a
no.
I
guess
I
mean.
I
think
this
was
a
great
presentation,
a
great
new
addition
to
andrea
features,
really
looking
forward
to
see
it
in
in
the
first
in
andrea
1.7,
according
to
the
road
mapperchon
listed
today.
So
thanks
a
lot
for
this
presentation,
sean-
and
I
guess
this
is
also
all
for
today,
unless
anyone
has
something
else
to
bring
up
before.
We
finish
the
call
I'll
just
wait,
10
seconds
to
see.
