►
From YouTube: GMT 2017-11-16 Containerization WG
Description
Agenda and Notes:
https://docs.google.com/a/mesosphere.io/document/d/1z55a7tLZFoRWVuUxz1FZwgxkHeugtc2nHR89skFXSpU/edit?usp=drive_web
A
A
A
A
A
A
A
A
A
All
right,
James,
James
I
think
we
should
get
started.
Maybe
we
should
start
from
your
stuff.
First
I'd
like
to
kind
of
go
through
your
implementation,
whatever
design
for
the
user,
hey,
Gilbert,
hey
I,
think
geez.
How
is
gonna
be
a
little
late,
so,
let's
start
with
James
first
and
then
see.
Jetton
can
join
he's
gonna
be
a
few
minutes,
but
okay
yeah,
sir
Sir
Emily
and
Norris
okay,
so
James
do
I
like
sugar
screen.
Okay
I
saw
that
sure.
C
A
C
C
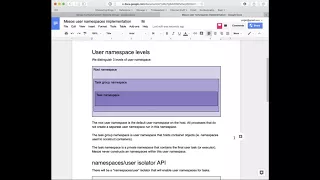
So
as
far
as
implementation
goes,
the
goals
are.
Keep
it
simple.
Let's
not
do
anything
too,
fancy
there's
one
and
we're
going
to
focus
on
user
name
spaces
for
with
regard
to
security,
domains,
we're
naughty
but
excluding
any
sort
of
ID
mapping
for
now
two
reasons
for
that.
Firstly,
I
don't
have
a
use
case
for
it
and,
secondly,
it
makes
it
a
lot
harder.
I
don't
want
to
do
with
a
yes,
so
in
in
the
model,
we're
kind
of
distinguishing
three
level.
Three
then
no
necessary
nested,
but
basically
three
API
levels
of
of
these
namespaces.
C
If
the
root
namespace,
which
is
then,
then
the
default
user
name
space
with
the
hardest,
we
have
the
task
group.
The
task
group
namespace,
which
is
a
user
name
space
that
resource
will
create
containers
within.
So,
although
it's
going
to
be
the
parent
namespace
of
you
know
their
containers,
map,
namespace
and
network,
no
space.
A
C
A
C
It's
supported
the
terminology.
Is
you
like
the
metals
terminology
you
submit
down
very
clearly
so
I
was
explaining
this
to
to
a
colleague
using
the
term
container
tree,
and
we
we
found.
That
was
a
confusing
terminology
in
that
conversation.
So
so
today,
I'm
trying
today
I'm
trying
tasks.
Okay,
so
we.
A
C
A
C
That
there's
room
for
some
sort
of
better
description
of
the
me
sauce
model,
great
including
terminology,
so
that
we
can
discuss
these
things.
You
know
okay
anyway,
so
you
go
so
there's
the
container,
basically
there's
the
container
level
namespace
and
then
there's
what
I'm
calling
a
private
men's
space,
which
is,
which
is
a
leaf
and
the
private
name
space
doesn't
have
any
other
name
spaces
created
within
it.
Certainly
that's
a
leaf
in
terms
of
the
security
model.
C
What
sorry
the
share
use,
namespace,
yeah
I,
think
I'm
trying
to
think
of
why
I'm
you
so
the
shapes
are
the
share,
use
namespace,
server,
open
question
at
the
bottom
for
that
the
show
username
space,
okay,
the
use
case
for
that
one
is
we
want
to
have.
We
want
to
be
able
to
have
tasks
that
join
the
root
namespace
and
don't
get
a
separate
container,
make
space.
C
A
C
A
C
A
C
No
than
that
this
private
user
names
first
won't
be
the
parent
of
anything,
so
it
won't.
So
when
you
construct
a
container,
you
enter
that
you
enter
their
username
space
and
the
mountain
home
space,
and
maybe
the
milkmen
and
the
previous
place,
and
all
this
other
stuff
and
the
name
spec
their
user
name.
Space
is
the
parent
of
all
these
other
namespaces
right
mm-hm.
C
C
A
A
A
C
C
C
No,
so
we
need
to
distinguish
them
because
what
matters
in
using
namespaces,
so
these
namespaces
are
defining
a
security
domain,
and
then
we
have
a
private
when
we
when
we
run
the
task
in
a
private
using
namespace
here.
What
we
want
is
we
want.
We
want
to
arrange,
so
we
will
arrange
for
the
tasks
to
run
in
a
user
name
space.
C
That
is
not
the
parent
of
any
other
user
names
roses,
because
in
order
to
have
privilege
over
some
namespaced
kernel
resource
your
task
and
the
resource
that
were
checking
that
you're
having
privilege
against
needs
to
share
a
common
user
name
space.
So
what
private
using
namespace
means
is
that
we
guarantee
that
you
that
there
is
no
other
kernel
resource
that
has
your
user
name
space
in
common.
C
So
if,
for
example,
you
are
able
to
say
you're
running
a
regular
program,
it's
my
private
user
name
space
and
you
were
able
to
acquire
some
capability
right,
you're
able
to
acquire
some
privilege,
which
was
unexpected,
that
wouldn't
let
you
manipulate
the
user
name
spaces
that
we
use
to
construct
the
container
because
those
user
name
space.
Those
those
namespaces
like
the
mountain
named
space,
for
example,
is
owned
by
a
different
user
name
space.
So
you
don't
share
a
common
path.
Oh.
A
Okay,
so
maybe
like
it
will
be
easier
if
you
explained
that
the
whole
flow
you're
saying
that
for
the
container,
oh
okay,
you
create
user
name,
if
the
container
and
and
then
and
then,
if
you
set
this
private
user
name
a
flag
to
chew,
we
actually
like
launched
a
seizure
or
the
task.
You
actually
put
that
into
a
another
separate
user
name
space.
Maybe.
C
A
A
C
C
The
first
implementation
I
have
everything
will
choose
inside
the
container
namespace
uh-huh,
that's
the
default
behavior.
The
default
I
have
you
for
the
outside.
It
used
to
launch
everything
into
the
container
namespace
uh-huh,
and
the
issue
is
that
is
I.
Guess
there's!
No.
We
sure
that
it's
it's
fine
and
it
reads
it's.
It's
gonna
protect
your
host.
It's.
A
A
A
A
C
So
you
know
you
can
say
that
you
can
say:
hey
I
when
I
have
I
have
my
tasks.
It's
in
the
container.
The
container
has
a
user
name
space
and
the
task
has
privilege
within
that
container
and
there's
that's
fine,
so,
okay,
the
tasks
can
can
do
things
to
the
container
okay
yeah
and
then
you
could
say
well,
I
have
this
task
and
it's
it
can
tell
you,
but
I
really
don't
want
it.
I
really,
don't
want
it
to
do
anything
to
the
container.
Well,
they
come
back
to
use
Case
Squad
at
that
space.
C
C
C
E
C
C
A
C
A
C
B
Sorry,
I
missed
a
part.
Can
I
ask
another
question,
so
the
Linux
info
is
attached
to
the
container
info,
which
is
used
whenever
you
launch
a
container
with
whether
that
is
an
executor
container
or
the
you
nest
container.
So
so
that's
why
in
there
we
even
with
a
share
pinning
space
thing,
you
only
say
the
parent
versus,
not
you,
you
don't
say
the
root,
because
you
don't
know
your
your
accessible.
If
the
root
is
accessible
to
you
right,
if
it's,
if
you're
already
under
the
nested
container,
then
you
preparing
is
already
not
root.
Can.
A
Is
where
it's
still
available
to
you,
my
understanding,
sir
Sir
James,
correct
me
if
I
was
wrong.
My
understanding
of
this
is
usernames
is
like
a
special
namespace.
So
there
is
a
relationship
between
like
other
namespaces
compared
to
like
say
you
can
say
a
mal
namespace
is
it's
under
that
particular
user
name
space
because
of
dad
that
kind
of
complicated
the
flag
on
that?
A
C
Yes,
it
works
the
way.
Yes,
the
supreme
work.
Fine.
So
if
yours
say,
if
we
implement
share
username
space,
then
what
that
this
manage
that
would
be
join
the
username
space
of
your
logical
part.
So,
if
you're
an
executive
container,
you
will
join
the
roof
username
space.
If
you're
a
mr.
container,
you
would
join
the
username
space
of
your
executor.
B
C
A
E
B
Username
saves
in
it
and
then
I
guess:
that's
your
container
username
and
container
username
space
right,
which
is
which
has
other
names,
but
this
is
when
you
clone
and
then,
when
you
clone
you
just
yeah
that
makes
us
container
rights
are
launched
there,
which
then
would
fork
exact
your
image
processed
image.
So
what
else
is
this?
How
do
you
achieve
this
private
username
space
after
that?
Basically,
starting
from
that
point
on,
how
do
you
do
additional
isolation
so.
C
A
A
A
C
If
I'm
suspicious,
then
what
I
would
do
is
I
would
say
well,
but
I
want
to
do
you
say:
I,
say
hey.
The
task
has
its
own
user
name
space
and
that
user
name
space
is
not
the
parent
of
any
other
name
spaces
in
the
container.
So
if
the
task
was
able
to
acquire
privilege,
it
wouldn't
have
any
privilege
over
the
container
because
they
have
disjoint
username
spaces.
C
A
If
it's
well,
if
it's
default,
I
secure
just
hit
the
agent
API
to
create
a
stick
container,
so
the
NASA
continue
is
under
a
different
user
name.
Space.
Alright
yeah,
then
Daniel,
lock
that
the
container
will
actually
like
focus
at
the
actual
task
in
that
the
same
real
name
space
as
that
nasty
container
yeah.
C
This
this
is
the
same
case.
All
right,
you
have
a
you,
have
a
you
as
a
user
name
space,
which
is
the
parent
of
the
container
right
mm-hmm.
If
the
Todd.
If
the
task
has
that,
has
a
common
parent
as
the
container,
then
the
task
and
acquire
privilege
over
the
container,
it
doesn't
matter
what
how
deeply
the
container
is.
Mister
mister
borges
calls
make
sure
I
see.
A
A
C
C
C
B
E
Just
can
you
hear
me?
Yes,
okay,
I
was
doing
the
comparison
with
the
the
pit
namespace
actually
in
this
isolate
others.
Only
two
level
right
like
what
you
try
to
introduce
here,
is
a
three
level
name
facing
feature
like
your
route
versus
container
versus
user
and
for
the
p.m.
space,
for
example,
for
example,
there
is
only
two
level
right,
no
paintings.
A
E
A
Depends
on
which
a
secures
if
you
use
default
a
secured
and
that's
separate,
but
if
you
use
the
old
style
command
s
okay,
so
the
executor
is
kind
of
like
legacy
and
secured
do
its
own
for
kids.
A
can
only
really
really
is
leverage
the
username
space
mm-hm.
Sorry,
not
the
pen.
Sorry,
don't
create
a
printing
straight
for
the
task.
A
A
E
Okay,
because
in
a
in
my
vision,
I
mean
there,
there
is
a
surely
of
similarities
between
user
name
places
and
UID
name
species,
for
example:
ok,
ID
namespaces,
are
you
Oh,
like
you,
can
as
a
naming
convention
generalize
the
fact
that
there
is
child
and
parents,
because
we
were
talking
about
nested,
containerization
and
etc?
So
why
not
changing
the
naming
instead
of
fruit,
calling
parent
and
self?
You
know
that's
coming
tried.
Oh
yeah
I
think
anything.
E
C
A
I
first,
you
want
this
feature
because
I
can't
have
the
same
argument
saying
that
right,
like
just
ignore
the
implementation
details
like
from
security
perspective,
I
pretty
well
my
test,
you
not
be
able
to
see
containers
pit
containing
like
the
pin
a
space
of
the
container
like
the
in
the
process.
I
guess
we
probably
need
to
allow
these.
D
A
This
may
be
foot,
do
the
same
for
penance.
Oh
I
love
those
basically
I.
Think
for
pennies
based
people.
Some
people
want
say:
hey
I,
don't
want
to
manage
my
own
index.
Please
do
anything
for
me
or
some
people
just
prefer
I'd
say
I
want
to
do
my
own
in
their
time
on
our
system
V,
so
we
purchase
support.
Oh
I
think
we
definitely
to
support
both
yeah
I.
Think.
C
C
Because
user
name
spaces
are
different,
so
we
can
talk
about
some
I,
don't
know
what
the
API
looks
like
we
can
I
mean
we
can
talk
about
what
okay
I
doesn't
have
to
be
a
flag.
The
API
could
be
something
different,
but
ultimately
you
want
to.
You
can
separate
these
things
out
in
a
way
that's
completely
transparent.
So.
B
C
So
it
may
sauce
when
you're
talking
about
Nesta
containers,
it's
just
logical.
Mr.
right,
you
just
have
I
mean
yes,
it's
just
a
logical
nesting
of
containers.
Oh
this
is
some
internal
notion
of
opportunist
and
when
you
have
a
private,
the
private
user
names
face
here,
it's
not
a
container.
What
you're
doing
is
your
protect
your
leveraging,
these
namespace
security
model
to
protect
the
container
from
a
task.
So
it's
a
completely
different
thing.
B
C
It
doesn't
do
anything
because
the
container
they
on
the
container
is
constructed
out
of
kernel
objects.
The
parent
of
the
kernel
objects
is
a
user
name
space.
You
launch
a
task
with
the
same
user
name:
space
parent.
It
doesn't
matter
like
what
you've
done
internally
to
my
sauce,
to
keep
track
of
this
logical
tree
of
containers.
What
matters
is
the
relationship
between
the
kernel
objects.
A
C
A
Shared
the
dog
to
the
the
slack
Channel
that
container
migration
China
sure
I
haven't
seen
this
stuff
before
sure.
I
only
wrote
it
this
morning,
okay
sounds
good,
so
I've
heard
like
the
next
step,
is
true
to
comment
on
this
dog
and
think
think
more
on
this
I
don't
think
like
the
one
hour.
It's
something
like
half
an
hour
is
sufficient
for
this,
like
for
any
to
think
more
on.
I
thought
it
would
be
ten
minutes.
Okay,
yeah,
sorry
about
that.
A
G
G
G
G
G
G
G
Go
back
to
the
agent
rock.
We
see
that
I
think
we
see
that
from
the
a
from
the
Braavos
login,
you
can
see
that
we
decided
to
leave
the
bunker
players
from
the
system
and
we
also
I
think
there's
also
log
lines
here
say
we
we
are
marking
a
cup
of
tea,
I,
think
there's
also
there's
also
actually
else.
We
logs
indicating
that
certain
logs
so
other
layers
that
the
Mexico
image
is
using
a
marked
as
kept
during
the
GC.
Oh
I
think
it
is.
C
G
E
G
A
G
C
A
A
D
A
D
It's
me
yeah
yeah,
so
there's
only
step
like
10
minutes,
so
maybe
we
can
quickly
go
through
the
display
of
the
OGC.
It
is
a
basic
one
Oh
before
before
that.
One
thing
to
note,
it
is
like,
if
you
want
to
use
the
GC
for
mazes
continuously,
you
have
to
and
your
cluster
it
up
way
from
a
previous
version
to
1.5
or
later
you
have
to
drink
all
the
container
on
the
agent.
Otherwise,
the
the
GC
gonna
be
disabled.
A
A
G
D
C
D
So
this
could
be
a
hat.
We
already
have
a
discussion
about
the
auto
GC,
so
it's
it's
hard
to.
It
can
take
some
time
to
decide
truly
auto
GC.
So
right
now
here
the
auto
here
means
it
is
basic
support
for
auto
GC,
and
we
just
introduced
on
here
st
Roger
in
the
agent
in
the
agent
code,
to
allow
operator
to
specify
some
agent
flag
to
so
that
we
can
trigger
the
image
garbage
crashing
theoretically
and
the
the
discussion
start
from
the
what's
the
policy
we
want
to
trigger
their
GC.
D
Did
you
see
weekly
or
monthly,
so
the
auto
one
we
prepare
to
go
with
the
size
based
and
so
right
now?
If,
if
you
look
at
you
guys,
look
at
the
currents
and
execute
the
same
box
GC
in
our
you
know,
ask
you
to
sandbox
GC.
We
will
schedule
sandbox
for
garbage
collection,
and
then
we
have
to
agent
that
can
show
that
one
it
is
the
same.
Dosage
is
a
heirloom.
Another
is
the
watch
interval
and
we
can
introduce
similar
mechanism
for
the
image
layers.
D
So,
for
example,
the
head
Jong,
it
can
be
like
point-
can
be
zero
to
one
and
if
it's
like
one,
it
means
like
if
the
usage
of
the
disk
up
more
than
get
up
to
like
90
percent,
it
will
trigger
the
GC
automatically,
and
the
watch
interval
means
like
how
frequent
me
check
with
this
usage,
and
so
this
to
it
has.
It
has
to
be
like
both
set
or
not
set,
and
we
also
have
another
cracker
control
the
exclusive
excluded
image.
So
it
means
like
it
just
matched
the
operator
API.
D
B
No
I
guess
my
question
is
the
head
room
and
all
of
the
calculation
is
that
it
based
on
a
size
or
that
basically,
the
remaining
free,
this
free
disk
space
of
that
volume,
but
that
disk
I
thought
there
is
gonna,
be
your
like
a
size
for
the
disk
image
for
they
for
the
image
cache.
It
is
not
size.
It's
the
percentage
of
the
this
usage
of
the
entire
disk
usage
right
yeah.
A
B
See
I
see
I
said
so
I.
Guess
it's
not
like
this.
This
wouldn't
work,
but
I
can
see
that
this
is.
This
is
kind
of
modeled
after
the
sandbox.
Do
you
see,
and
now
the
fetcher
cache,
even
though
I'm
sure
we
want
to
improve,
but
at
least
the
fetcher
cache
you
have
a
have
a
designated
size
and
you,
you
know
the
size
of
the
things
you
put
in
there
and
and
based
on
least
recent
use.
B
A
D
D
B
The
package
is
the
package:
there's
not
like
layers,
which
could
be
shared
a
lot,
so
that
sure
has
a
venture
cache
as
the
size
and
the
easy
thing
is
things
you're.
Putting
the
printer
cache
it's
easy
to
calculate
its
size.
So
you
basically
just
store
the
size
of
these
of
stuff
you
put
in
the
patrick
hussion
without
watching
the
disk,
because
because
you
know
or
once
when
you
are
fetching
it
down
and
then
you
just
do
to
do
the
math
internally.
A
A
D
And-
and
we
do
have
the
plan
when
let
me
introduce
the
unified
works
door,
we
my
move,
the
federal
cash
and
permissions
are
together
and
to
have
the
unified
restore
to
control
tinna
of
continued
image
and
virtual
cash
uri.
So
and
then
we
do
a
hash
for
ten
together
and
at
that
time
of
you
introduce
another
GC
way.
Another
GC
with
different
agent
flag
to
can
show.
So
it
might
be
a
good
hint
to
start
to
start
to
think
about,
like
yeah.
A
A
A
A
I,
don't
wanna,
do
it
D
you
I
mean
how
do
you
get
the
size
for
that
entire
layers
like
it's,
it's
a
trade-off
right
so
like
either.
You
have
some
way
to
imaginary
figure
out
based
on
tar
file
and
the
compression
ratio
to
calculate
the
the
size
of
the
layer,
or
you
do
tu,
which
is
kind
of
expensive.
If
the
layer
is
huge
and
I
expect,
it's
gonna
take
a
long.
G
G
A
A
D
B
Yeah
so
I
guess
yeah.
We
should.
We
should
think
about
that.
But
even
though
I
guess
the
point
here
is
not
about,
you
know
whether
that
can
be
unified
or
not
it's
just
about
so
right
now,
we're
basically
relying
on
the
operator
or
the
user
to
to
be
able
to,
or
for
multiple
discs,
to
do
heart
level,
heart,
hardware,
level,
isolation
of
discs-
and
you
set
aside
this
disk
for
this
purpose
and
that
for
that
purpose,
but
mm-hmm
other.
A
I
guess
you
get
my
point:
yeah
yeah,
so
I
get
the
point,
so
I
think
there's
a
lot
more
I
need
to
do,
for
example,
the
upper
layer
for
overlay.
We
need
to
cap
the
size.
That's
another
thing
that
we
want
to
do
things
like
this,
so
it's
this
is
just
like
a
stopgap
solution
to
make
it
production
kind
of
production
ready.
If
you
don't
have
GC
like
even
very
simple
GC
policy,
then
it's
not
production,
already,
I!
Think
yeah.
C
A
B
D
It
is
we
can,
we
can
definitely
introduce
the
API,
but
if
you
involves
an
interface,
some
new
interface
in
the
continuous
area
which
I
might
light,
because
because
we
don't
have
the
image
management
management
at
this
point
and
then
if
we
want
to
introduce
this
and
like
show
GC
ago
layer
or
show
all
layers,
it
is
like
kind
of
like
we
can
introduce
some
temporary
solution.
So
why
not?
We
just
do
all
together.
Do
the
image
management
all
together
in
the
unified
artifact
store
in
in
the
near
future.
A
So
October
I
think
like
having
some
metrics.
If
it's
not
hard
to
die,
those
mattress
I
would
prefer
just
adding
those
metrics.
It's
always
good
to
have
more
metrics
than
having
like
last
matches
yeah
if
it's
easy,
but
if
it's
hard
you
think
it's
hard,
then
it's
okay
I
think
we
should
spend
more
energy
on
the
unifier
artifact
store,
because
that's
the
direction
that
we
think
it's
makes
sense
in
the
future.
Yeah.
A
B
C
A
Yep
all
right
sounds
good
thanks,
guys,
I
think
we
were
over
time
thanks
everyone
for
attending
so
on.
So
we
part
have
a
demo
for
a
standalone
Pantera
next
next
time
and
because
the
all
the
killer
are
committed
and
you
wouldn't
call
up
down
on
the
user,
make
space
discussion
and
this
one
too,
okay,
I
guess
you
haven't
seen
Alexander's,
you
have
to
send
out
design
talks
with
the
community,
and
then
we
can
iterate
on
that
which
decide.
Oh
the
auto
GC
the
flag,
you
wanna,
add
yeah
yeah
sure.
Maybe
we
will
send
the
elevation.
