►
Description
In this session, we’ll look at using HashiCorp tools to help you as your infrastructure continues to grow, helping to manage secrets, and secure communication between applications running in multiple clusters.
We will demonstrate how to quickly get started with HashiCorp Vault and Consul using the Helm charts. Then, walk through an example application architecture where we secure service to service communication with Consul and securely manage application secrets using Vault.
Presenters:
Nicole Hubbard, Developer Advocate @HashiCorp
Justin Weissig, Technical Product Marketing Manager @HashiCorp
A
A
Google
and
a
CMC
ambassador
and
I'll
be
moderating
today's
webinar,
and
we
would
like
to
welcome
our
presenters
today.
Nicole
Hubbard
developer
advocate
at
Hoshi
core
and
Justin
wayside
sorry,
but
you
can
fix
it
later:
technical
product
marketing
manager
at
hashey
core.
Before
we
get
started,
there
are
a
few
housekeeping
items
during
the
webinar.
You
are
not
able
to
talk
as
an
attendee,
but
there
is
a
Q&A
box
at
the
bottom
of
your
screen.
A
Please
feel
free
to
drop
questions
in
there
and
we
will
get
to
as
many
as
we
can
in
the
time
that
we
have.
This
is
an
official
webinar
of
the
CNCs
and,
as
such,
it
is
subject
to
the
CMC
F
Code
of
Conduct.
Please
do
not
add
anything
to
the
chat
or
questions
that
would
be
in
violation
of
that
code
of
conduct.
Basically,
please
be
respectful
of
all
of
your
fellow
participants
and
the
presenters.
B
Alright,
so
ask
so
today
we're
going
to
be
talking
about
securing
your
kubernetes
applications
using
console
and
vault,
and
so
some
of
the
questions
I
get
asked
the
most
often
when
I'm
talking
the
customers
are
what's
a
service
mesh
and
why
should
I
use
a
service
mesh?
So
let's
start
there
and
so
to
really
understand
that.
Let's
look
at
a
history
of
like
how
we've
evolved
to
the
state
that
were
in
today,
and
so
when
you
started
off
years
ago,
more
or
less
now
we
were
deploying
our
applications.
B
We
would
deploy
monoliths
to
web
servers,
they
would
have
firewalls
that
would
limit
the
traffic
to
the
databases
and
all
of
your
traffic
coming
in
would
flow
through
a
simple
load
balancer.
That
would
then
hit
all
your
web
servers.
This
made
securing
your
applications
a
lot
simpler,
because
you've
only
had
a
handful
of
servers
running.
They
only
ran
your
single
application,
and
that
was
the
only
thing
that
ran
on
this.
So
we
had
monoliths
and
as
we
continued
to
move
into
micro
services
and
kubernetes,
we
now
have
a
new
look
for
our
datacenter.
B
But
now
we've
got
potentially
additional
data,
centers
or
cloud
providers
where
we're
running
for
grenades
and
they
have
a
requirement
for
database
access
or
key
value
stores,
as
well
as
talking
to
the
old
applications
as
well,
and
so
obviously,
here
those
has
to
look
different
than
what
we
used
to
use
for
securing
the
network
of
our
web
applications
running
on
virtual
machines
or
physical
hosts,
and
so,
as
we've
started,
to
move
into
kubernetes.
We
started
to
see
a
couple
challenges
that
you
have
to
solve,
which
are
service
discs,
are
very
server
segmentation.
B
The
service
configuration
minetti's
helps
a
lot
with
this
service
discovery
solved
with
the
services
that
you
can
define
in
communities
and
it
provides
discovery
through
dns.
You
can
also
use
network
policies
to
do
service
segmentation
within
your
cluster
to
limit
applications
from
communicating,
as
well
as
config
maps
and
secrets
within
kubernetes
or
your
configuration,
but
those
are
limited
to
your
single
kubernetes
cluster.
B
And
so
what
happens
here
is
when
your
console
servers
start
every
single
client
or
application
that
you're
running
in
your
service
mesh
nice
to
have
a
certificate
to
communicate
with
other
services.
These
are
standard,
x.509
certificates,
the
same
thing
that
you
use
for
securing
your
web
traffic.
These
are
so
these
provide
both
TLS
for
encryption,
as
well
as
since
they're
all
coming
from
a
single
certificate
authority.
B
We
can
use
them
to
provide
identity
information
so
that
we
know
that
service
a
is
cersei
and
service
via
service
B,
based
on
the
information
that's
in
that
certificate,
because
we
trust
the
CA.
We
are
also
able
to
automatically
generate
these
and
rotate
them
for
our
clients,
using
sidecars
and
other
methods
to
get
those
certificates
in
place
and
we'll
go
into
that
a
little
later.
And
so
the
next
piece
is
there's
two
components
to
the
console
service
that
you
have
the
control
plane,
which
is
console
it's
running
here.
B
We've
got
console
servers
running
and
we've
got
our
console
client
running
on
each
of
our
two
nodes
that
we're
showing
in
this
cluster.
And
then
you
have
your
data
point.
The
data
plane
is
going
to
be
represented
with
convoy
for
the
demo
today
and
on
void
acts
as
a
sidecar
proxy
for
us,
and
it's
responsible
for
actually
routing
the
traffic
between
our.
B
You
can
actually
create
an
intention
that
will
allow
traffic
or
deny
traffic
based
on
the
service
itself
rather
than
a
set
of
labels,
and
so
here
we're
able
to
say
that
our
web
service
is
not
able
to
communicate
with
any
other
services
and
then
we're
able
to
create
a
specific
rule
to
allow
our
web
service
to
communicate
with
our
database,
and
so
these
are
for
those
services,
and
these
will
actually
take
effect
for
those
services,
no
matter
where
they're
running.
So,
if
they're
running
in
your
kubernetes
cluster
they'll
be
applied.
B
If
they're
running
on
virtual
machines
or
a
separate
kubernetes
cluster,
all
of
these
intentions
follow
your
application
and
your
services,
no
matter
where
they're
running
within
your
service
mission,
and
you
can
also
manage
these
through
the
UI
of
console
and
so
through
the
UI.
You
can
actually
see
all
of
your
intentions
in
one
place
if
you
prefer
user
interfaces
now,
how
do
we
actually
integrate
this
with
our
applications
and
so
for
kubernetes?
B
B
In
this
case,
you
would
talk
to
a
port
on
localhost,
that
is
the
proxy
that's
running
here
for
your
web
service
and
your
traffic
will
flow
into
there
and
then
that
proxy
will
wrap
all
of
your
traffic
from
there
for
you
and
eventually
get
it
to
the
database
securely
and
we'll
walk
through.
What
that
looks
like
now
to
do
this,
the
only
thing
you
have
to
add
is
an
annotation.
So
once
you
add
this
annotation
of
console,
Hasek
or
column
such
connect
inject,
this
will
inject
all
of
that
sidecar
proxy.
B
For
you-
and
this
is
there's
a
mutating
web
hook,
that's
deployed
when
you
deploy
the
console
home
chart
that
will
add
everything
needed
to
make
this
and
wire
it
up,
and
so
how
does
this
traffic
look?
So
here
we've
got
our
webserver
running.
We've
got
our
proxy.
These
are
all
and
on
that
same
note,
there's
a
console,
client,
so
console
clients
deployed
into
the
crew
Bonetti
cluster
as
a
daemon
set,
and
then
on
our
other
node.
We
have
our
database
with
a
sidecar
proxy
and
the
console
client
for
that
node.
B
The
console
server
can
be
running
inside
of
a
kubernetes
cluster
or
outside
of
it.
It
doesn't
matter
for
the
purpose
of
getting
this
working,
and
so
when
the
webserver
wants
to
communicate
with
the
database,
it
opens
the
connection
to
the
proxy
server.
Now,
instead
of
the
database
and
the
proxy
server,
we'll
ask
the
local
console.
B
Client,
hey
where's
the
database
using
the
service
discovery
component
we
talked
about
earlier,
and
the
console
client
will
return
that
database
and
then
the
proxy
will
open
that
TLS
connection
to
the
proxy
for
the
database
and
then
from
there
that
proxy
will
validate
that.
The
database
is
allowed
to
commuter
that
the
web
server
is
allowed
to
communicate
with
the
database,
and
since
we
created
that
intention
earlier,
it
is
authorized
and
so
that
TLS
connection
is
a
sound
in
the
case
where
that
connection
isn't
authorized
that
tail.
B
That's
where
these
things
start
to
become
very
valuable
and
so
another
thing
that
the
mesh
gateway
can
help
you
with
is:
if
you've
got
to
kubernetes
cluster
is
deployed
and
they're
actually
using
the
same
IP
space
or
you've
got
sets
of
vm's
running
or
any
network
segments
where
they're
the
same
overlapping
IPs.
So,
in
this
case
on
the
Left,
we've
got
datacenter
one
running
our
API
and
web
services
and
they're
using
the
10.8
1.1
hypee
address,
and
then
we've
got
our
database
to
running
in
a
completely
separate
data
center,
all
right.
B
The
database
in
a
separate
data
center
using
10.8
1.2
for
the
IP,
and
this
allows
so
connecting
these
networks
using
VLAN,
peering
or
VPN.
It's
very
complicated
because
you
have
to
do
some
special
address
translations
so
that
those
services
and
one
subnet
can
actually
talk
to
the
IPS
and
the
other
subnet.
B
However,
you
want
and
that
convection
is
secured
and
all
of
that
traffic
gets
matted
as
it
leads
your
mesh
gateway
and
goes
into
the
next
mesh
gateway
so
that
those
services
are
now
able
to
communicate
without
having
to
re
IP
or
networks
or
deal
with
the
overlapping
eyepiece.
You
don't
even
have
to
think
about
them
in
this
case,
and
so
these
mesh
gamma
rays
are
built
using
envoy.
They
sit
there
at
the
edge
and
they
wrap
all
of
that,
and
they
also
use
those
same
certificates
that
we
talked
about
earlier.
B
You
can
now
add
HTTP
routing
traffic,
splitting
or
custom
resolution,
and
so
we
can
do
things
like
this
here,
where
a
request
comes
in
to
web
dot
service
console,
but
it
ends
with
slash
API
and
so
now
we're
our
people
to
actually
change
that
routing
and
say
that
anything.
That's
for
slash
API!
Instead
of
routing
that
to
our
web
service,
we're
gonna
route
that
to
more
API
service
and
then
for
our
traffic
splitting
we're
gonna
say
we
can
define
subsets,
and
so
these
are
different
versions
or
different
groupings
of
our
applications.
B
And
so
here
we
can
actually
do
splitting
where
80%
of
our
traffic
goes
to
version.
1
of
our
API
and
20%
of
the
traffic
goes
to
version
2
and
then
for
the
custom
resolution
we
actually
define
here.
How
do
we
figure
out
what
that
subset,
B
to
is
or
subset
Canary,
and
so
we
define
a
selector
just
kind
of
like
true
Nettie's
labels
based
on
the
metadata
of
your
console
service,
and
so
in
this
case
we
defined
meredith
version
equals
2
and
that's
how
we
define
version
2
for
our
api.
B
So
in
addition
to
all
of
this
layer,
7
and
networking
components.
Now
what
about
secrets?
How
do
we
manage
those
terminations
built-in
secrets?
But
what
else
can
we
do
and
how
can
we
automate
and
store
these
certificates
that
we
need
to
generate
all
in
a
single
place
as
well?
And
so
that's
where
vault
comes
into
play,
so
vault
focuses
on
secret
management
and
data
encryption
as
well
as
access
to
all
of
this,
and
so
we
can
take
a
look
here
and
we
can
see
that
vault,
it
integrates
the
main
thing.
B
So
you
can
see
some
examples
here
from
Eddy's
OpenStack.
We
can
integrate
with
databases
as
well
as
integrating
with
the
cloud
providers
you're
using
as
well
Horrocks
if
you
have
SSL,
and
so
how
does
won't
work
so
you've
got
clients,
you've,
got
secrets
and
there's
the
authentication
piece.
So
let's
kind
of
walk
through
this
real
quick.
So
as
a
client,
I'm
gonna
make
a
request
to
the
vault
API
and
then
I
have
to
authenticate.
So
this
gets
passed
back
to
a
back-end.
B
It
could
be
I
pass
credentials
or
it
could
be
that
vault
is
redirecting
me
to
hata
or
Active
Directory,
logins
or
whatever
you're
using
for
identity
yield.
Then
authenticate,
there's
also
integrations
for
kubernetes
services
so
that
your
service
accounts
opens
within
communities,
can
validate
and
authenticate
against
the
vault
API
and
that
identity
from
kubernetes
comes
with
those
and
then
so.
B
These
are
all
passed
in
and
then
we've
got
the
secrets
piece,
which
is
now
that
I've
authenticated
I
want
to
be
able
to
get
secrets,
and
so
these
can
go
out
to
one-time
passwords
key
value
stored
passwords,
where
we're
just
storing
that
the
password
is
X
value
as
well
as
going
all
the
way
out
to
integrations
with,
for
example,
AWS
where
you
can
request
credentials
for
AWS
and
you'll
be
proven.
Those
credentials
will
be
created
specifically
for
you
with
the
permissions.
B
B
D
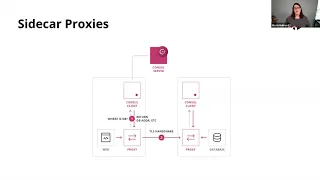
Perfect,
hey
awesome
thanks
Cody,
they
also
basical
so
I'm
just
sharing
my
screen
here
and
then
so
for
the
demos
today,
I
sort
of
wanted
to
go
hands-on,
we'll
jump
over
to
the
command
line
and
actually
walk
through
like
what
this
looks
like
in
real
life.
So
just
to
sort
of
give
you
a
high
level
of
what
we're
gonna
look
at
I
just
wanted
to
chat
about
the
slide
here
called
the
sidecar
proxy,
so
we're
gonna
set
up
a
web
app.
That's
basically,
you
know
just
a
web
server
and
then
database
server.
D
So
that
console
is
intercepting
the
traffic
with
the
proxies,
and
then
we
can
sort
of
you
know,
set
these
intentions
that
say:
hey
you
know
what
this
web
app
is
only
allowed
to
talk
to
this
database
or
what
happens
if
we
say
interrupt
that
traffic
and
say
you
know
what
this
web
app
can't
talk
to
that
database,
we'll
just
sort
of
cover
some
of
the
sort
of
behind
the
scenes
kind
of
cool
stuff
that
you
can
do.
Another
thing
that
we're
gonna
demonstrate
is
injecting
a
secret
from
vault
into
the
web
app.
D
D
All
sorts
of
you
know
like
open
LDAP.
You
know
all
sorts
of
databases
like
say
my
sequel.
If
you
wanted
to
do
say,
credential
rotation,
you
can
have
Volvo
connect
to
your
database
and
rotated
credentials.
So
you
know
vaults,
sort
of
a
Swiss
Army
knife
of
Secrets
stuff,
but
I'm
just
gonna
show
you
a
very
brief
summary
myth
today.
So
I
just
wanted
to
give
you
a
high
level
of
like
look.
The
design
looks
like
a
architecture
overview
before
we're
going
to
build
out
and
then
we'll
go
and
build
this
piece
by
piece.
D
D
So
you
can
see
I
have
my
treatment,
cluster,
full
disclosure
here,
I'm
just
gonna
copy
and
paste
the
commands
over,
because
you
know
it
goes
quicker
and
you
don't
have
to
watch
me
type.
So,
oh
so
in
the
top
panel
here
I
have
my
coupe
cluster
and
then
in
a
bottom
panel
here
I
just
have
a
while
loop
going
that
watches
what
pods
are
running
within
this
cluster.
This
will
just
sort
of
give
you
a
view
of
how
things
are
changing
as
I'm
going
through
the
demo.
D
So
first
thing
I'm
going
to
do
is
change
into
my
namespaces.
I
might
have
already
done
this
yeah
I
did
perfect
cool,
so
one
cool
thing
that
we
did
is
so
we
have
two
home
charts,
one
for
vault
and
one
for
console
and
what
you
have
to
do
before
was
you
know
we
had
them
sitting
in
repose
and
you
know
had
to
go
and
clone
the
repo
and
you.
D
Him
on
your
local
filesystem,
but
we
had
great
feedback
from
the
community
to
say:
hey.
Why
aren't
you
integrating
with
the
official
home
registry,
so
we've
gone
ahead
and
done
that
and
I'll
show
you
two
examples
where
you
can
find
out
more
information.
But
if
we
just
add
the
repo
here
and
then
we
can
search
the
repo
and
you
should
see
both
our
home
charts
here,
so
we
have
one
for
console
and
one
for
vault
and
then
you
know
you
can
just
do
like
how
install
the
various
chart,
but
for
the
console
piece
here.
D
I
wanted
to
show
you
that
piece
where
we're
running
the
sidecar
injection
aspect.
So
what
I
have
here
is
you
know
my
app
back-end?
This
is
the
database
counter
the
front
end.
This
is
a
front-end
app!
That's
gonna!
Connect
over
to
the
database.
I
have
a
patch
here:
I'm,
gonna,
I'm
gonna
show
you
something
cool
that
you
can
do
with
vault,
where
you
can
inject
secrets
without
having
that
half
know
anything
about
fault,
and
then
we
have
our
helm
console
config
file
here.
So
let's
just
take
a
look
at
this.
D
He
said
I
wanted
to
sort
of
highlight
here.
Is
this
console
connect
piece?
This
will
allow
us
to
do
the
sort
of
allow
and
deny
wiring
up
of
what
apps
can
talk
to
you
know
so
how
our
web
app
can
chat
over
to
our
database,
and
you
know
how
we
can
sort
of
interrupt
that
connection
if
we
wanted
to
so
that's
kind
of
what
that
is,
and
then
actually
let
me
just
cancel
this
here,
so
we're
doing
a
he'll
install.
D
We
got
the
config
file
and
then
we're
using
our
official,
our
registry,
which
is,
should
greatly
simplify.
If
you
want
to
get
fired
up
with
this,
so
we'll
get
that
going
and
then
down
in
the
bottom
panel
here
you
should
start
to
see
hey
consoles
firing
up
while
that's
going
I'm
going
to
get
a
vault
also
installed
so
I'm,
saying,
hey
home,
install
vault
and
I'm
actually
setting
this
additional
flag
here
that
says:
hey
I
want
to
run
the
server
in
dev
mode,
so
with
vault.
D
I
should
probably
mention
that
you
know
if
you're
not
familiar
with
console
or
vault
they're,
they're,
open
source
and
then
there's
also
enterprise
offerings
to
you
know.
Enterprises,
you
know,
obviously,
will
support
you
and
there's
a
lot
of
added
benefits
to
that
enterprise
features,
but
the
open
source
offerings
are,
you
know,
very
feature
complete
and
there's
a
tons
of
people
that
are
using
them
so
long
everything
I'm
going
to
show
you
today
is
available
on
the
open
source
definition.
D
D
Now
you
can
see
bolts
up
and
running
and
we
have
this
sidecar
injector
piece.
This
is
specific
to
kubernetes.
So
what
we
found
in
chatting
with
you
know
both
open-source
users
and
enterprise
users.
As
they
say,
hey,
you
know,
I
have
a
vault
cluster
and
we've
put
all
our
we
sort
of
centralize
all
our
secrets
in
it.
So
they've
could
get
like
auditing
logging,
and
you
know
credential
rotation
and
all
this
kind
of
cool
workforce
stuff,
but
we
don't
necessarily
want
to
modify
our
apps
to
take
advantage
of
vault.
D
Is
there
some
way
that
you
could,
like
maybe
inject,
a
secret
right
into
the
file
system?
So
that's
what
this
injector
piece
does,
and
you
know,
were
you
using
the
mutating
admission
webhook
component
of
creepy
needs
to
take
advantage
of
that
so
I'll
sort
of
highlight
that
in
a
second
here
you
might
actually
be
thinking
hey.
Why
not
you
just
using
kubernetes
secrets
and
that's
a
really
good
question
and
the
reality
is
you
for
a
simple
web
app
like
this?
D
You
probably
could
be-
or
you
maybe
should
be
and
that
you
know,
there's
overhead
to
using
vault
vault
is
really
meant
for
like
like
many
apps,
so
you
know
if
you
just
have
one
at
web
app.
It's
sort
of
depends
on
the
use
case
that
you
don't
want
to
go
after,
but
if
you're
just
injecting
a
simple
secret,
you
know
you
could
use
the
kubernetes
piece,
but
volt
really
shines
when
you
have
additional
sort
of
use
cases
or
when
you're
running
lots
of
different
apps.
D
So
you
know
vault
can
do
you
know
encryption
all
these
advanced,
secretive,
dynamic
rotation
stuff.
So
once
you
start
getting
into
more
of
these
advanced
use
cases-
and
you
know
you
see
the
secret
sprawl
sort
of
not
going
out.
That's
where
involves
really
shines,
and
you
know
you're,
it's
going
to
be
very
cumbersome
to
sort
of
use,
sort
of
just
static
secrets.
D
Also
one
cool
thing
I'll
show
you
here
with
the
vault.
Is
it
allows
you
to
do
policy,
so
you
can
say
hey.
You
know
what
this
particular
pod
is
only
allowed
to
grab
these
particular
secrets.
So
once
you
get
into
a
sort
of
complex
use,
cases
like
that
or
or
things
where
you
want
more
granular
sort
of
access
control,
that's
where
our
vaults
are
really
cool
all
right.
So
it's
not
a
login,
a
vault.
D
D
So,
let's
add
this
policy
I'm
reading
it
under
just
app
I'll
show
you
this
in
a
second
and
then
what
I
want
to
do
is
I
want
to
enable
vault
to
communicate
with
kubernetes.
So
right
now,
vault
is
running
on
kubernetes,
but
it
doesn't
have
a
way
to
like
wire
into
kubernetes.
To
say
you
know,
hey
this
particular
pause,
asking
for
a
secret.
Are
they
allowed
to
what's
the
policy?
You
know
you
don't
want
a
pod
just
to
fire
up
and
be
able
to
pull
down
on
your
secrets
right.
D
D
Maybe
I'll
just
walk
through
this,
so
I'm
setting
up
that
hey
Maya.
This
is
gonna,
be
my
web
app.
You
know
app
front-end
I
wanted
to
access
this
particular
policy.
So
I'm,
saying
hey,
you
know
what,
when
this
app
fires
up,
I
only
wanted
to
access
that
policy
where
it
can
download
those
particular
secrets.
This
allows
you
to
super
fine-grained
control
of
what
apps
are
able
to
access.
What
secrets
you
can
go
back
in
time
to
save
vault,
logging
or
auditing
to
say:
hey,
one
app
is
using
one
secret.
How
often
are
they
doing
it?
D
What's
their
rotation
schedules,
all
that
kind
of
like
cool
stuff,
more
advanced
features
that
you're
going
to
need
once
you
know
your
apps
taking
off
and
then
so
we
don't
all
the
wiring
up
set
up
behind
the
scenes.
We
just
need
to
configure
a
secret,
so
I
have
a
little
secret
here,
called
hello
world
with
the
username
CN
CF
and
passwords
the
ncf
demo
right.
D
D
We'll
notice
in
here
there's
nothing
special
we're
not
the
plug
definition
has
nothing
about.
It
doesn't
know
anything
about
console,
it
doesn't
know
anything
about
vault.
There
is
an
annotation
in
here
that
says:
hey,
you
know
inject
the
console
sidecar,
but
that's
it
we're
not.
You
don't
have
to
do
anything
complex
in
here.
D
And
then,
once
that's
up
and
running,
what
I'm
going
to
do
is
how
vault
will
work
will
it'll
inject
secrets
into
a
particular
path
into
the
file
system.
I
should
mention
this
is
psycho
injection
is
totally
unique
to
kubernetes
right,
typically,
how
you
get
interact
with
vault
is
you'd.
Have
you'd
modify
your
application
to
include
saying,
like
our
SDK
or
interact
with
our
API,
where
you're
saying
hey,
hey
vault,
before
I
connect
to
this
database?
What's
the
username
and
password
or
something
like
that
right?
D
But
this
way
you
know,
if
you're
using
a
say,
a
12
factor
app
or
something
like
that,
we
can
inject
the
secret
and
then
you
can
use
something
like
console
template
to
take
those
secrets
and
push
them
into
environment
variables,
or
something
like
that.
Alright,
so
I'm
just
going
to
connect
into
this
app.
So
basically
I'm
going
to
exactly
to
this.
This
pod
and
I'm
gonna
say:
hey
list
the
contents
of
this
directory.
You
know
this
is
obviously
gonna
fail
because
we
haven't
injected
any
secrets.
D
Yet
yeah,
you
can
say,
hey,
there's
no
such
file,
but
what
I
wanted
to
show
you
is
this
piece
here
this
patch,
so
this
patch
does
is
it
says:
hey
I'm,
patching
some
annotations
in
that
pod
definition.
Let's
say
hey,
you
know,
I
want
to
inject
a
secret
I
wanna.
This
is
the
secret
I
want
to
pull
down.
You
know
secret
hello,
world
and
behind-the-scenes.
What
we've
done
is
we've
wired
it
up
that
this
app
front-end
is
only
allowed
to
download
those
particular
secrets
based
on
the
role
of
this
particular
application.
D
This
really
protects
you
saying
like
hey,
you
fire
up
a
pod
and
it
goes
and
downloads
all
your
secrets.
Obviously
you
don't
want
that
race
and
then
on
the
vault
side.
You
know
all
this
is
audited
and
logged.
Saying
hey!
You
know
what
my
app
front-end
pulled
down
this
secret
at
this
particular
time.
So
one
cool
thing
we're
doing
here
is
we're
saying:
hey
you.
B
D
Obviously,
I
want
to
pull
down
this
secret.
The
helloworld
secret,
but
I
want
to
set
it
up
into
a
particular
string.
You
know
so
I'm
giving
a
post-grad
string
here.
Connection
string
and
I'm,
saying
hey,
give
me
the
username
and
give
me
the
password
and
then
I
want
to
output
that
to
the
file
system,
and
then
my
app
is
gonna.
Go
by
pick
up
this
connection
string
and
connect
over
to
our
database.
D
Alright.
So
now
that
we've
seen
that
let's
go
ahead
and
deploy
this
patch,
and
so
once
I
run
this
command.
What
we're
gonna
see
here
is
we're
gonna
see
this
app.
An
additional
pod,
Vyra
called
app
front-end
and
it's
gonna
have
both
in
an
it
container.
That's
with
fault,
so
fall
and
check
with
secret
before
your
app
fires
up.
This
just
protects
it
from
saying
hey.
If
your
app
fires
up-
and
it
doesn't
see
the
secret-
it's
gonna,
if
it
crashes
or
something
like
that.
Obviously
you
don't
want
that
right.
D
So
your
apps
gonna
fire
out
vault
will
inject
the
secret
before
your
app
starts
and
then
vault
will
have
a
little
sidecar
container
sitting
there.
That
will
periodically
check
to
make
sure
that
Secrets
on
up-to-date
and
inject
the
new
one,
if
say
it,
changes
this
really
comes
into
sort
of
those
more
advanced
use
cases
I
was
chatting
about
and
that
default
supports
dynamic
secrets.
So
you
can
have
a
secret
rotate
say
every
30
minutes
or
something
like
that
and
vault
will
sync
over
that
password
or
the
secret
data
into
your
container
cool.
D
So,
let's
patch
this
and
then
we'll
see
what
happens
cool.
So
we
see
our
new
pod
firing
up.
You
can
see
that
the
containers
numbers
is
different
because
we
have
our
vault
sidecar
container
in
there
now
right,
so
our
old
app
is
terminating
and
then
what
we'll
do
is
we'll
go
ahead
and
wall
cat,
the
secret
file,
so
I'm,
just
gonna
executor
the
front-end
container
again
and
then
I'm
gonna
basically
cut
the
contents
or
list
the
contents
of
this
file
and
if
everything
works,
which
it
just
did,
you
can
see
our
Postgres
connection
string.
D
So
you
see
our
username
and
our
password
worked
properly
with
our
template
and
it
pushed
that
to
the
filesystem.
Now
our
app
is
able
to
go
check
that
file
and
pull
that
in
and
use
it
to
connect
to
a
database.
So
one
thing
I
should
probably
mention
is
that
I
want
to
actually
show
you
what
this
looks
like
in
web
browser.
So
I
have
a
couple
tabs
here
and
I'm
just
gonna
wire
up.
E
E
D
Cool,
so
you
can
see
we
have
our
services,
we
have
console
running,
we
have
our
app
front-end
and
then
we
have
a
console,
sidecar
proxy,
so
everything's
looking
good
so
far,
I'll
just
sort
of
zip
through
the
various
tabs
here.
So
you
can
see
our
nodes.
You
know
we
have
our
three
healthy,
cheek
AE
nodes.
D
You
know
with
console,
you
can
have
like
key
value
store
so
see.
You
had
some
particular
data
that
you
know
you
wanted
in
your
cluster
or
something
like
that.
You
can
throw
that
in
there
you
can
set
up
ACLs
and
then
we
can
also
set
up
intentions.
Intentions
is
basically
what
I'm
going
to
use
to
demonstrate.
The
hey.
You
know:
can
we
block
traffic
or
can
we
allow
traffic
between
our
web
app
and
our
database
Beckett
cool
and
then
let's
jump
order,
this
tab
and
I'm
just
gonna
show
you
the
web
app.
D
So
the
web
app
is
super
simple.
All
it
is
is
just
a
counter
when
it
connects
to
the
backend
it
increments.
The
counter
and
that's
it
you
can
see
hey.
You
know,
accounting
services
unavailable
right
now.
So
once
we
fire
up
the
the
backend,
this
should
flip
over
to
green
and
then
we
should
see
an
incrementing
counter.
D
This
is
just
our
WebSocket,
so
it
should
probably
come
off
by
us
and
as
we
do
that,
so,
let's
switch
back
to
the
console
and
we'll
fire
up
that
web
app
heard
that
back
in
maybe
I'll
just
show
you
what
it
looks
like
and
you'll
notice
in
here
there's
like
nothing,
nothing
special
right,
we're
injecting
the
console
sidecar,
but
that's
it
so
you'll
notice.
You
know,
maybe
in
the
demo
here
yeah
we
do
mention
the
annotations
around
console
involved,
but
these
apps
they
have
no
idea
about
vault
or
console.
D
You
know
it's
happening
transparently
to
them
behind
the
scenes.
This
is
sort
of
one
of
the
really
cool
benefits
of
this
is
that
you
know
you
have
to
go
in
refactor
or
rebuild
your
apps.
Obviously
you
can.
If
you
want
to
include
our
SDKs,
you
know.
Maybe
you
can
take
advantage
of
advanced
features
and
stuff
like
that,
but
yeah,
it's
it's
pretty
cool,
alright.
So
let's
go
ahead
and
fire
off
our
back-end
all
right.
D
So
you
can
see
the
backend
coming
up,
I'll
just
wait
till
it's
all
ready
and
then
I'm
gonna
flip
over
to
the
web
browser
here
and
we'll
reload
this
awesome.
So
you
can
see
hey
it's
connected
now
and
you
know
it's
using
our
back-end.
You
know
if
I
just
hit,
I
refresh
a
bunch
of
times
but
I'm
you
can
see.
The
counter
goes
up,
which
is
awesome,
that's
pretty
much
it
from
my
demo.
D
So
you
know
I
think
we
have
a
good
chunk
of
time
for
the
Q&A
period,
so
I'm
gonna
do
is
I'm
gonna,
stop
my
sharing
and
then
maybe
we'll
go
over
to
the
call,
and
we
also
have
Cody
from
our
Technical
Marketing
Group
here
you
know
we're
colleagues
and
we're
happy
to
answer
any
questions.
Also,
we
have
a
slide
that
shows
our
resources
of
you
know,
basically
how
you
can
get
going
with
console
and
kubernetes.
You
know
if
you
want
to
go
and
install
the
whole
chart.
D
Basically,
here's
step
by
steps
on
what
you
need
to
do.
One
sort
of
hidden
gem
that
I
really
wanted
to
share
with
you
is
our
learn
site.
So
learn
a
chic
or
calm.
It's
just
packed
with
cool,
hands-on
labs.
So
hey
you
know,
I,
don't
know
anything
about
console.
How
do
I
just
get
started
or
you
know,
hey,
I'm,
a
more
advanced
user.
How
do
I
maybe
get
going
with
it?
You
know
we
have
a
whole
bunch
of
like
just
loaded
content
here
and
then
you,
you
click
in
here.
D
You
know
you
can
see
sort
of
hands-on
live
stuff.
The
same
thing
goes
for
vault.
You
know
we
have
health,
chart,
documentation
and
same
thing
with
the
vault
to
learn
site
so
learn
hash,
Norcom,
slash
vault,
and
you
know
it's
just
awesome.
You
know
I'm,
you
know
I
I,
work
here
and
I
go
into
these
labs.
All
the
time
too,
like
find
stuff
on
itself.
C
C
D
Hundred
percent,
so
the
one
main
thing
about
this
is:
you
know
if
you're
totally
dedicated
to
a
particular
cloud
provider
and
you're
heavily
embedded
with
them,
and
you
have
like
simple
use
cases.
I'd
say
you
know
why.
Why
wouldn't
you
use
that
cloud
provider
on
the
flipside
is
where
it
gets?
Tricky
is
once
you
start
going
down.
That
path
is
I'd,
say
a
lot
of
companies
aren't
that
simple
and
that
you
maybe
have
especially
enterprise
companies
right
you
have
on
pram.
Maybe
you
have
lots
of
data
centers.
D
What
if
you're
using
you
know
one
cloud
and
then
you
have
oh
I
want
to
back
up
to
another
cloud.
Just
in
case
you
know
4dr
preferences
or
something
like
that.
That's
where
all
the
sudden
boom
complexity
just
totally
goes
off
the
charts.
In
that
you
know,
your
developers
have
a
workflow
for
interacting
with
secrets
on
one
common
provider.
D
Now
they
had
to
add
a
bunch
of
exceptions
for
working
on
this
other
cloud
provider
nevermind
if
he'd
have
to
do
a
non-prime
sort
of
the
hidden
gem
of
vault
is
the
sort
of
seamless
workflow
across
all
this.
In
that,
if
you
use
vault,
you
can
have
a
common
workflow,
a
developer
workflow
that
goes
across
on
all
these
various
clouds.
D
In
that
you
know,
vault
sort
of
acts
as
an
abstraction
layer
right,
you
can
put
all
your
secrets
into
vault
and
then
vault
has
plugins
that
will
go
on
interact
with
all
these
various
cloud
providers,
so
that's
sort
of
like
not
only
from
like
a
developer
workflow,
but
just
from
you
know
a
security
practice
standpoint.
I
don't
have
a
DevOps
team
that
has
to
go
in
secure.
This
particular
cloud
with
secret
manager.
I
don't
have
to
go
on
secure
on-prem
seems,
like
secrets,
littered
all
throughout
source
code.
D
C
So,
just
just
I'd
like
to
understand
a
little
like
to
summarize
they're,
like
I,
think
that
what
you're
saying
is
around
like
it
could
be
able
to
work
flow
problem
right
if
you're
looking
for
consistency
and
how
you
use
these
secrets
between,
like
multiple
environments
of
all
shines
really
well.
For
that.
Oh
no.
C
If
you're
an
AWS
user
and
you're
just
deep
in
AWS
management
already,
it
does
necessarily
make
sense
to
rip
that
out
and
drop
vault
in.
But
if
you
want
to
be
able
to
have
as
your
dataview
as
tcp
vSphere,
you
have
a
consistent.
So
keep
it
consistent
secrets
platform
between
them,
alt
kind
of
becomes
a
really
good
way
to
go.
Yeah.
D
I,
honestly
I,
wouldn't
you
overshoot
on
the
complexity
side?
It's
like
you
know
if
you're,
if
you're
a
small
start-up-
and
you
just
have
you
know,
you
know
a
few
apps
and
you're
running
an
AWS.
Why
wouldn't
you
use?
You
know
the
AWS
secret
manager,
or
you
know,
you're,
probably
just
hard
coding
to
be
a
hundred
percent
realistic,
you're,
probably
not
even
using
the
secret
manager.
D
Vault
really
shines
when
you
want
to
have
like
auditing
logging,
more
advanced
stuff,
like
dynamic
credentials.
You
know
that
are
short-lived,
that
have
a
TTL
all
just
handles
it
all
for
you
behind
the
scenes.
So
you
don't
have
to
be.
Let
us
sort
of
handle
like
the
secret
side
and
you
can
focus
on
your
app,
is
sort
of
the
I'd
say
pitch
I'd
give
there,
but
a
lot
of
companies
that
aren't
using
ten
Khan's
like
realistically
right.
D
There
may
be
using
on
Prem
and
they're,
using
a
cloud
provider
or
maybe
they're
totally
born
in
the
cloud,
and
they
want
to
have
another
cloud
provider
as
a
backup
rate.
So
vault
it
is
gonna.
Save
you
so
much
time,
even
in
just
simple
use
cases
like
that,
where
I
have
one
cloud
and
I
have
another
comm
provider
and
that
you
know
you're
not
duplicating
workflows,
you're,
not
duplicating
how
do
I
secure
it
over
here
and
over
here
vault
you
just
use
vault
as
an
abstraction
layer
and
it'll
handle
it
all
for
you.
C
D
D
C
D
D
There's-
probably
probably
multiple
things
here
happening
here
and,
like
you
know,
there's
probably
specific
to
your
particular
environment
or
something
like
that.
But
you
know
it's
part,
probably
see
two
things
happening.
One
is
hey.
I
want
to
provision
infrastructure
that
is
probably
like.
You
know,
an
infrastructure,
automation
thing
that
you
wouldn't
necessarily
handle
with
alt,
but
maybe
you'd
handle
through
like
care
form
or
something
like
that
for
the
secret
side
of
things,
hey
I
have
a
bunch
of
Secrets
and
I
want
to
share
them
with
a
particular
set
of
developers.
D
Vault
has
a
gay
user
interface.
Also
I
was
like
a
command
line.
Api
you
can
use
it.
Basically,
however,
you
want
to
interact
with
it.
If
you
basically
put
your
passwords
inside
of
it,
you
can
set
up
policies
to
say,
hey,
you
know
what
these
particular
users
can
access
these
particular
set
of
secrets.
So
from
the
secrets
aspect,
that's
that's
easy
to
do
with
volt,
but
it's
probably
there's
probably
a
infrastructure
component
to
the
question
here
that
I
need
to
understand
more
phone.
C
C
That
that
can
be
complex
and
it's
surely
and
least
getting
started,
but
especially
in
kubernetes.
A
lot
of
the
interaction
is
taken
care
of
through,
like
the
annotations
that
that
Justin
showed
in
his
demo.
As
far
as
saying
that
it
goes
when
you
move
out
of
kubernetes,
there's
there's
a
little
bit
of
a
different
workflow
around
creating
with
the
service
files
or
registering
services,
but
oftentimes
that
can
be
automated
through
the
API
or
through
the
way
services
register,
as
they
come
up
on
virtual
machines.
It's
much.
C
To
Tunis
it
get
started
with
like
the
registration
of
services,
because
the
sidecar
model
kind
of
takes
care
of
all
of
that.
For
you,
as
far
as
like
a
console
service,
mesh
complexity,
standpoint
on
kubernetes,
it's
actually
very
simple
to
consuming
it
started
with
I,
don't
see
a
lot
of
complexity
there,
it
gets
a
little
bit
more
I,
don't
want,
say
it's
more
complex,
it's
just
a
little
bit
of
a
different
workflow
when
you
start
interacting
with
virtual
machines
versus
what's
in
kubernetes,
so
maybe
Daniel.
D
So
there's
a
question
here
about
hey
I
have
four
different
environments.
You
know
prod,
q8,
etc.
I
have
a
few
different
data
centers,
and
how
does
this
work?
So,
although
you
know
I'll
speak
to
the
vault
side,
because
I'm
most
obviously
familiar
with
that
one,
but
you
know
you
could
have
multiple
clusters
for
each
of
these
environments,
but
you,
you
can
also
do
see.
Maybe
I'll
just
focus
on
sort
of
a
prod
use
case.
You
know
if
you
have
multiple
data
centers
and
you
want
to
run
vault
in
prod.
D
Console
and
vault
are
just
liners.
You
know
you
can
install
them
without
using
kubernetes,
it's
not
coordinating
specific
or
anything,
but
obviously
we
have
the
home
charts
that
make
this
super
useful.
If
you
want
to
do
that
on
the
vault
side,
if
you're
running
vault
in
production
across
multiple
data
centers,
that's
sort
of
where
vault
enterprise
would
come
into
play
in
that
you
know,
you
set
up
a
vault
cluster
and
then
you
can
have
replication
where
you
basically
replicate
those
secrets
over
to
another
cluster.
C
C
A
lot
of
that's
because
we're
integrating
so
tightly
with
Envoy
in
that
way,
so
that's
definitely
possible,
definitely
stuff.
You
can
do
and
things
that
we
would
really
encourage.
You'll
start
to
see
a
lot
more
about
that
coming
out
around
console
in
our
conversations,
especially
now
that
we
have
we've
created
our
own
ingress
gateway
to
speed
up
getting
started
on
that.
Those
are
things
that,
like
we
really
want
people
to
be
able
to
do
so.
It's
definitely
in
the
product.
Now
you
can
do
that
today.
Absolutely
I
think
that,
like
yeah.
E
C
Answering
the
next
line
back
to
back
to
our
firm
Christopher
and
intentions
can
span
multiple
instances,
so
in
console
refer
to.
This
is
Federation.
So
if
you
take
multiple
console
clusters
and
you
better
ate
them
together
into
that
one-
consistent
service,
metro,
train
environments-
you
can
have
those
intentions
span
across
them,
so
the
intention
looks
like
front
end.
Can
talk
to
API
but
console
itself
understands
okay,
I'm
gonna
send
this
over
a
mesh
gateway.
I'm
gonna
send
this
traffic
to
the
end
point,
but
that.
C
Is
still
kept
in
place
that
that's
security
that
MPLS
encryption
is
kept
in
place
and
the
intentional
asset,
so
the
intention
is
actually
fairly
simple,
the
upstream
creation
so
like
when
Justin
showed
in
the
community
sam'l
file.
You
do
end
up
specifying
that
secondary
data
center,
so
you
say
like
that,
our
API
data
center
for
that
stripping
them
at
the
end
of
the
port,
but
that's
pretty
pretty
straightforward.
The
intention
is
just
here
goes
to
there
right
if
console
understands
how
to
do
that,
how
to
do
that,
translation
downstream
and.
E
So,
just
to
add
to
that
a
little
bit,
I
think
the
question
was
around:
can
expand
multiple
service
instances
and
so
in
console
when
you
register
a
service
you're
registering
a
service
that
could
have
multiple
instances
of
that
service.
So
maybe
you
have
an
API
tier.
Then
you
have
multiple
API
workers.
Those
would
all
just
be
represented
in
console
as
a
single
API.
So
in
the
air.
The
intention
would
apply
to
that
group,
but
you
don't
have
to
individually
reference
those
individual
instances.
B
D
To
just
share
my
screen
for
a
second,
so
in
this
blog
post.
Basically,
we
talked
about
you
know
the
sidecar
injection
that
demo
that
I
sort
of
walked
through
you
know,
there's
a
video
hey,
maybe
if
you
just
you
can
easily
Google
this
up
and
what
retreat
yourself,
but
I
just
wanted
to
show
you
sort
of
the
piece
that
makes
this
happen
is
hey.
D
If
you
will
or
something
like
that,
as
you're
as
you're
asking
from
the
pod
into
kubernetes
into
vault
hey,
how
do
I
actually
grab
this
secret
and
so
we're
we're
hitting
that
policy
that
says
yeah
this
service
account
is
allowed
to
read
these
secrets.
That's
how
you
we
sort
of
enforce
that
a
this
particular
pod
can't
download
all
the
secrets
or
something
like
that.
But
there's
sort
of
a
larger
thing
happening
here
in
that
yeah
we're
injecting
the
secret
into
the
file
system.
D
If
we're
we're
making
some
assumptions
here
that
hey,
you
know,
you're,
you
know
what's
running
inside
your
pods
and
you
know
what
sort
of
accessing
this
particular
secret,
but
there's
sort
of
a
higher-level
thing
here
in
that
we
want
to
give
you
a
spectrum
of
sort
of
use
cases
that
you
can
use
with
vault.
We
know
that
hey
this,
isn't
maybe
the
best
option
for
your
particular
use
case
right.
So
we
want
to
give
you
access
to
the
api.
We
want
to
give
you
access
to
you
know
injecting
secrets.
D
We
want
to
give
you
like
a
variety
of
options
that
sort
of
fit
your
your
both
your
security
requirements.
It
also
sort
of
your
use
cases,
so
so,
obviously,
the
most
secure
way
of
doing
it
is
connecting
directly
with
the
vault
api.
In
that
you
can
have
a
basically
a
direct
path,
but
yeah.
We
want
to
give
you
a
variety
of
options.
D
C
In
a
khole,
both
both
said
this,
but
something
to
call
out
that
I
think
is
really
really
like
interesting
and
cool
about.
All
of
this
is
that
most
of
us,
you
can
go
and
do
right
now
right,
you
can
go
pull
the
stuff
down
and
give
it
a
try.
You
know,
buy
anything
like
it's
all
open-source
software
right
are
there.
Are
there
some
like
really
advanced
features
about
like
scaling
the
enterprise
that
are
that
are
behind
license
sure,
but
significant
portions,
all
of
the
stuff
that
was
demoed
today?
C
Hoshi
work
tools
have
a
great
a
great
way
of
doing
the
what
we
call
what
we
call
dev
mode,
where
you
just
run
it
locally
on
your
system,
so
I'd
highly
encourage
anybody
who
wants
to
even
check
the
stuff
out
check
out
the
UI
click
around
pull
down
the
binaries
and
run
them.
It's
really
really
easy,
and
a
lot
of
the
learned
guides
are
based
on
being
able
just
run
locally
on
the
fly.
Yeah.
D
100%
and
there's
a
massive
community
behind
it
too
right,
if
you
run
into
a
problem
or
something
like
that,
you
go
to
Google,
hey
this
error
message:
chances
are
you
going
to
find
either
one
of
our
learned
guides
or
the
forms
or
github,
or
something
like
that,
where
someone's
already
run
into
the
same
thing?
So
it's
it's
not
like
you're,
just
going
on
this
on
your
own
or
something
like
that.
E
Yeah,
so
there
was
a
question
about:
are
there
plans
to
allow
constantly
be
configured
via
Kate's
resources
or
an
operator?
It's
definitely
something
that
we're
looking
to
do
within
the
next
release
as
to
have
CR
DS
to
allow
you
to
manage
both
console
intentions
and
layer.
Seven
routing
configuration.
D
D
A
There
are
a
couple
more
there,
but
I
think.
That's
all
we
have
time
for
today
reminder
to
everyone
that
this
is
going
to
be
up
on
the
scene.
Cf
website
after
this
scene,
yep
dot,
IO,
slash
webinars.
So
if
you
want
to
refer
back
to
it
or
if
you
want
to
ask
the
speakers,
questions
I'm
sure
that
they're
open
to
that
any
any
contact
information.
You
all
want
to
share
for
future
questions.
