►
From YouTube: Why Everyone Should Care About eBPF by Neependra Khare
Description
eBPF - Game changer technology to program the Linux Kernel dynamically. Using eBPF, we can now program Linux Kernel dynamically and get insights, which were not possible earlier or were very expensive . It is changing the game in the system's side the way JavaScript helped us bring everything on the browser. There are now many emerging use-cases of this technology. In this talk we'll discuss about its background, uses cases in security/tracing/networking/observability with some hands-on demo.
A
A
A
A
A
So
before
ebbf
there
was
bpf,
which
is
berkeley
packet
filter,
as
the
name
suggests
it
is
used
to
filter
the
network
packets
in
any
os.
We
have
two
primarily
things:
one
is
user
space
and
the
kernel
space
in
the
user
space
we
have
programs
like
browser
editors
and
so
on,
while
on
the
kernel
side,
we
have
programs
using
which
we
can
interact
with
the
devices
like
network
card
disk
and
so
on.
A
The
core
of
eppbf
is
lies
in
enhancing
or
extending
the
capabilities
of
the
linux
kernel
without
changing
the
kernel
code
or
loading
a
module,
and
this
makes
things
very
similar.
So
if
you
have
been
part
of
the
linux
kernel
community,
you
know
that
to
bring
up
a
linux
feature
in
the
kernel
may
take
up
two
years,
which
is
just
too
much
and
by
the
time
the
future
has
arrived.
We
may
have
moved
on
as
well,
but
by
dynamically
programming
the
kernel
with
epbf.
A
It
changes
the
game
significantly
and
we
can
now
come
up
with
n
number
of
use
cases
for
that,
and
we
will
look
them
in
few
minutes.
We
can
attach
eppbf
to
different
programs
like
any
linux
kernel.
Anything
in
the
network
stack
any
user
space
program
and
so
on.
So
we
can
attach
this
program
to
any
of
these
events
and
whenever
those
events
happen,
we
can
perform
something.
A
There
are
many
use
cases
for
epbf
now
now,
if
you
look
at
in
the
cloud
world,
we'll
talk
about
kubernetes,
which
runs
multiple
containers,
and
these
containers
in
most
cases,
are
just
programs
and
if
we
can
attach
the
epbf
at
the
color
level,
we
can
actually
look
at
what's
happening
in
every
container
and
so
on.
So
rather
than
putting
something
at
per
container
level
like
a
side
car,
we
would
filter
them
out
or
we
can
inspect
them
at
the
kernel
level.
So
things
would
become
very
simple.
A
A
If
we
have
lot
of
parts,
then
that
can
be
significantly
slow
because
of
the
way
ip
tables
would
work.
But
again
if
we
have
lot
of
parts,
but
on
a
similar
case,
if
we
move
to
the
eppbf
based
cni
plugins,
like
cilia,
things
are
very
fast
because
we
are
not
going
anywhere
in
the
ip
tables
route.
We
just
go
from
the
color
layer
itself,
and
that
makes
things
very
fast.
A
A
In
the
security
terms,
we
can
have
the
tooling
built
around
networking
and
the
runtime
security
as
well
fall
code,
tracy
and
the
policies
are
some
of
the
example
of
security
things
there.
Similarly,
for
observability,
we
have
different
tools
like
pixi
and
so
on,
using
which
we
can
observe
in
the
system
what's
happening
through
and
throughout
before
we
jump
into
the
architecture
of
eppf.
A
A
A
So
if
I
run
this
script,
it
is
going
to
collect
the
system
calls
called
by
every
program.
Now,
if
I
just
press
ctrl
c,
you
can
see
that
there
have
been
few
programs
which
are
running
on
system
and
they
have
called
different
number
system
calls
like.
The
node
program
has
called
41
system
calls,
and
so
on
now,
with
the
next
example,
we
are
going
to
list
down
all
the
best
commands
which
have
run
throughout
the
system.
So
I
run
this
particular
program
and
let's
say
if
I
open
up
a
new
terminal
and
run
few
commands.
A
A
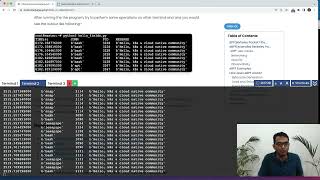
Now,
in
the
next
example,
we
are
going
to
trace
new
processes
via
the
exact
calls.
Let
me
run
this
program
here,
so
the
program
is
now
running.
Let
us
now
go
and
let's
say,
do
few
more
things
here.
Let's
say
if
we
run
date,
command
do
a
bash
here
and
so
on,
and
let's
go
back
here
and
check
now
we
can
see
here
what
are
the
new
processes
we
have
called
here,
and
these
are
being
listed
here.
A
A
A
Now
on
the
screen,
we
can
see
different
bpf
trace
types
which
you
can
attach
at
different
places
in
the
system.
So,
as
you
can
see,
we
can
attach
them
with
respect
to
devices
memory,
cpu
user
space
programs
and
so
on.
So
we
can
actually
put
or
have
these
scripts
for
each
in
individual
subsystem.
What
we
have
here
and
we
can
then
see
what's
happening
exactly
on
our
system
at
any
point
of
time
now
we
have
seen
the
basic
examples.
Now,
let's
see,
how
does
ebpf
actually
works?
A
So
here
is
a
high
level
diagram,
which
is
going
to
explain
you
how
things
are
happening
behind
the
scene,
so
we
need
to
load
our
ebbf
programs
by
the
bpf
byte
code,
which
we
can
write
manually
but,
of
course,
writing
manually
by
codes.
It's
just
going
to
be
too
much
complicated
and
that's
why
we
have
different
tool
chain
which
have
been
built
using
which
we
can
easily
write
these
ebbf
programs.
So
there
are
different
tool
links.
We
have
see
the
example
of
bpf
trace
already.
Then
there
is
bpf,
compiler
collection.
We
call
this
bcbc.
A
A
So
now,
once
we
have
the
byte
code
either
by
writing
it
manually
or
from
any
one
of
these
tools,
we
can
load
that
byte
code
to
our
kernel,
with
the
bpf
system
call
and
first
we
hit
the
verifier,
which
would
verify
whether
the
code
which
you
are
loading
is
safe
to
run
on
the
kernel
or
not.
If
it
is
not
safe,
then
verifier
would
fail
it
and
not
run
it
post
verification
we
are
going
to
use
just
in
type
compilation,
step
to
convert
our
instructions
to
the
respective
architecture.
A
What
we
have,
and
once
we
have
done,
that
we
are
going
to
attach
the
program
to
different
events.
What
we
have
and
those
events,
as
I
said
earlier,
can
be
any
kernel,
call
can
be
any
user
space
programs
any
trace
points
or,
and
many
more
so
once
we
have
attached
to
any
of
these
events
and
if
those
events
occur,
we
are
going
to
do
the
data
collection
and
the
data
collection.
A
A
Now
here
is
a
very
simple
program
which
we
would
write
with
bcc
and
python
and
try
to
hook
it
with
an
event.
So
whenever
that
event
happens,
we
get
some
data
out
and
we'll
see
that
so
again,
there
are
different
front
ends,
as
I
have
mentioned
earlier.
So
we
are
going
to
use
the
bcbc
library
with
the
python
program
to
run
the
particular
example.
So
only
we
just
added
the
front
end
now.
So
let's
see
how
this
is
going
to
happen.
A
So
if
you
look
at
in
this
particular
program,
we
are
simply
saying
that
whenever
this
particular
function
is
being
called
run,
the
print
hello,
kts
and
clarity
community,
now
what
we
are
doing
is
we
are
loading,
this
particular
bpf
program
and
attaching
it
to
the
system
called
clone.
So
whenever
we
are
going
to
fork,
we
are
going
to
run
this
function
and
print
out
the
output
like
hello,
kts
and
the
clogged
community.
So
let's
try
to
run
this
particular
program
now.
A
So
we
are
now
running
this
program.
Here
is
all
there
now,
let's
go
ahead
and
do
some
fork
so
just
going
to
kind
of
spin
up
few
more
terminals
here,
maybe
right
date,
some
other
commands
here
and
now,
as
you
can
see
here,
as
we
kind
of
perform
any
of
the
clone
functionality
by
any
means
in
the
system,
we
are
getting
this
particular
output
on
our
screen.
A
So
with
apbf,
we
are
just
bound
by
our
imaginations
with
eppf.
We
can
program
the
color
dynamically
and
to
the
end
user
or
developer,
we're
just
going
to
have
an
api
call
using
which
they
can
program
the
kernel
for
their
own
choice
and
that
just
brings
enormous
flexibility
to
the
developers
to
bring
up
many
and
many
use
cases.
