►
Description
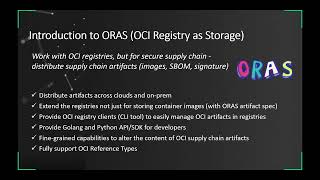
Don’t miss out! Join us at our upcoming event: KubeCon + CloudNativeCon Europe in Amsterdam, The Netherlands from April 17-21, 2023. Learn more at https://kubecon.io The conference features presentations from developers and end users of Kubernetes, Prometheus, Envoy, and all of the other CNCF-hosted projects.
A
Next
I
will
walk
you
through
the
sense
of
Open
Source
projects
in
this
area,
such
as
Note
3,
V2,
auras
and
ratify.
For
example.
We
can
leverage,
Note,
3
V2
to
sign
and
verify
artifacts,
and
we
can
use
auras
to
promote
artifacts
across
registries
and
if
you
are
running,
applications
on
kubernetes
gratify
enables
kubernetes
clusters
to
verify
artifacts
security
prior
to
deployment.
A
So
if
you
want
to
automate
and
build
a
secure
supply
chain
in
CSD
Pipeline
with
GitHub
actions,
we
will
also
provide
provide
our
practice
with
these
projects.
Let's
start
from
the
real
concerns
we
hear
from
our
end
users
and
I
guess
you
might
also
struggling
with
these
problems
in
your
software
delivery
process,
not
only
security
engineers.
A
Foreign
that
you
will
find
securing
software
supply
chain
is
similar
to
secure
the
traditional
manufacturing
supply
chain.
Like
the
left
diagram,
it
includes
several
rounds
of
quality
check
and
testing
from
producing
materials
to
deliver
foods
to
the
customers.
Ensuring
the
food
is
safe
enough
to
the
market.
A
A
When
we
talk
about
the
secure
supply
chain,
software
build
materials,
AKA
spawn,
is
also
a
required
concept.
U.S
government
has
executive
order
to
require
software
vendors
to
generate
and
provide
spawn
fire
for
customers.
We
can
take
a
look
at
these
spdx
type
of
Spawn
file
at
the
right
diagram
generally.
It
includes
packaging
file
and
licensing
information,
and
other
information
saw
take
this
diagram.
As
an
example,
we
can
introduce
Nursery
to
sign
your
image
engine
resignation.
A
A
Okay,
let's
jump
to
the
first
project
we
wanted
to
cover
in
this
webinar
notice
for
v2,
which
is
used
to
sign
and
verify
artifacts
in
an
easy
way
in
general.
Not
only
V2
includes
three
components,
not
three
CLI
tool.
We
can
call
it
notation,
it
is
used
to
sign
and
verify
artifacts
and
manage
certificates
and
policies.
A
A
Okay,
let's
get
started
before
you
try
out
this
demo,
you
need
to
install
notation
and
have
a
container
image
in
your
registry,
so
you
will
find
we
are
using
notation,
Alpha
4.
and
we
have
pushed
and
contain
the
image
to
our
registry,
so
only
we
can
use
notation
list
to
find
the
attached
image
attached
signature
from
this
image.
A
A
A
A
A
A
A
A
A
A
A
So,
as
you
can
see
from
this
diagram,
you'll
find
oras
has
provided
a
bunch
of
CI
commands
like
OS,
attach,
which
is
used
to
attach
files
to
an
existing
artifact
or
else
copy
allows
you
to
copy
artifacts
from
one
target
to
another
Target
before
we
get
started.
Let's
take
a
quick
look
at
this
workflow
powered
by
auras.
A
A
A
A
A
Okay.
Currently
we
can
see
that
there
is
a
spawn
file
attached
to
this
image
in
our
local
registry.
Okay,
let's
delete
this
folder
that
store
the
spdx
spawn.
Next,
we
can
use
our
spool
to
pull
that
artifact
from
our
registry,
which
is
used
to
improve,
which
is
used
to
prove
if
auras
can
pull
the
artifact
with
the
spawn
file
to
our
local
folder,
okay
copy
it
and
tap
it
here.
So
here
we
need
to
specify
the
digest
of
this
spdx
spawn.
A
Okay,
if
we
can
download
the
spawn
file
by
our
spool,
that
means
we
can
use
auras
to
pull
and
push
any
OCR
artifacts
from
the
registry.
Okay,
in
our
previous
two
demos,
we
have
generated
signatures
for
our
sample
image
and
attached
a
spawn
file
to
that
image.
So
last
but
not
least,
how
to
verify
artifacts
security
priority,
deploy
it
to
kubernetes,
Cluster
I
think
ratify
the
answer.
A
As
we
introduced
at
the
beginning
of
this
webinar,
we
can
use
ratify
to
enable
kubernetes
clusters
to
verify
artifacts
prior
to
our
deployment.
So,
as
you
can
see
from
this
part,
ify
can
work
with
Opa
GateKeeper
to
enable
the
policy
to
check
and
validate.
If
the
contained
image
meets
our
verification
policy
or
not,
is
this
container
image
has
been
signed
and
validated
by
ratify?
That
means
it
can
be
deployed
to
the
kubernetes
cluster.
If
not,
it
will
pass
failed
and
it
will
not
deploy
to
the
kubernetes.
A
A
Well,
let's
go
back
to
my
terminal
and
yeah.
I
have
installed
ratify
beta1
and
next
we
can
use
ratify
to
validate.
If
a
signed
image
can
be
deployed
to
the
kubernetes
cluster
or
not
okay,
we
can
use
kokato
run
signed
apps,
which
is
sample
image.
So
for
the
first
time
we
use
a
side
image
that
has
been
signed
by
notation,
so
we
can
specify
a
sample
image
here.
A
A
A
A
A
All
right,
I
think
we
did
three
demos
that
demonstrated
the
workflow
in
this
secure
supply
chain.
So
if
we
want
to
automate
all
of
those
steps
in
your
script,
how
can
we
handle
that?
How
can
we
automate
this
secure
supply
chain
in
CSD
I?
Think
the
simplest
way
is
write
a
workflow
script
that
in
a
GitHub
actions.
