►
From YouTube: Desktop to Deployment K8s Security with Checkov
Description
No description was provided for this meeting.
If this is YOUR meeting, an easy way to fix this is to add a description to your video, wherever mtngs.io found it (probably YouTube).
B
All
right
thanks
everyone
for
joining
us
today,
whether
it's
the
middle
of
your
day
the
morning
or
the
evening,
welcome.
Thank
you
to
steve
for
joining
us.
We
are
here
to
talk
about
desktop
to
deployment
in
k8
security
with
chekov,
I'm
libby,
schultz
and
I'll
be
moderating.
Today's
webinar
I'm
going
to
read
our
code
of
conduct
and
then
I'll
hand
it
over
to
steve
jager
developer
advocate
at
palo
alto
networks,
a
few
housekeeping
items
before
we
get
started
during
the
webinar.
B
You
are
not
able
to
speak
as
an
attendee,
but
you
are
able
to
add
anything
to
the
chat,
we'll
collect
your
questions
there
and
get
to
as
many
as
we
can
at
the
end
so
be
sure
to
plug
them
in
right
there
in
that
chat,
we're
all
using
and
also
say,
hello.
Let
us
know
where
you're
watching
from
this
is
an
official
webinar
of
the
cncf
and
as
such
a
subject
to
the
cncf
code
of
conduct.
C
C
This
is
called
desktop
to
developer
and
I've
already
done
that
thing
where
I've
lost
my
mouse
course,
the
alternative
name
as
I'm
trying
to
get
it,
make
it
a
little
bit
more
exciting
because
it's
something
new
that
I've
only
just
came
up
with,
and
I've
sort
of
rebranded
it
to
batten
down
the
hatches
trying
to
keep
an
article.
You
know
kubernetes
we
like
to
do
that
kind
of
thing
with
the
wheel.
C
My
first
mate
in
open
source
package
is
chekov,
it's
something
I'll
be
using
throughout
to
demonstrate
what
I'm
using
other
things
that
do
what
it
does
are
available,
but
I
would
be
remiss
if
I
didn't
say
it's
a
package
that
I
contribute
regularly
to
so
I'm
a
big
fan
of
it.
My
name
is
steve
jager.
I
am
a
developer
advocate
for
bridge
crew,
which
is
owned
by
palo
alto
networks.
C
You
can
learn
more
about
me
there
at
that
url
and
on
my
twitter,
which
I
really
need
to
use.
More
often,
you
know
all
right.
Let's
talk
about
what
we're
going
to
talk
about
a
bit
meta.
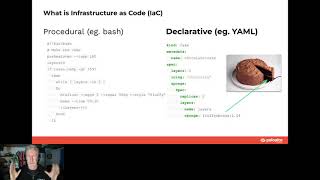
What
is
infrastructure
as
code,
I'm
sure
most
of
you
know
what
that
is
in
some
form
and
some
probably
in
some
greater
detail.
C
C
There
might
be
some
patches
that
maybe
you
haven't
used
before
or
you're,
not
aware
of,
or
maybe
you
just
like
to
get
a
little
bit
of
feedback
as
to
where
the
security
people
might
be
putting
their
little
security
tidbits
and
sprinkling
little
pieces
of
security
on
there
that
might
get
in
the
way
of
making
your
deployment
successful.
So
that's
what
we're
going
to
do
and
we're
going
to
seek
to
unlock
all
of
our
hatches
using
check
off.
Okay,
we'll
talk
more
about
check
off
later,
but
we'll
try
and
set
the
scene
a
little
bit.
A
C
All
right
os
top
ten,
it's
been
around
a
while.
You
know
it's
kind
of
like
one
of
the
things
that
absent
people
like
to
bang
on
about.
Certainly,
security
people
love
to
talk
about
the
off
the
top
ten
blah
blah
blah,
oh
wasp
top
ten,
but
it's
actually
kind
of
getting
interesting,
not
that
it
wasn't
before.
But
there's
there
have
been
some
very
important
changes
in
the
one
that
was
released
last
year,
which
kind
of
recognized
this
move
to
cloud
native
and
I'm
very
enthusiastic
about
it.
C
For
example,
some
of
the
old
dog-eared
elements
of
the
top
ten
like
injection
and
say
server-side,
request
forgery,
things
that
were
associated
with
application
security
that
the
appsec
people
love
to
talk
about
they're
kind
of
getting
less
important,
they're
moving
down
the
list
and
a
lot
of
them
are
just
kind
of
gone
like
cross-site.
Scripting
is
just
not
there
anymore.
That
was
a
thing.
It's
still
a
very
powerful
attack
vector,
but
it's
just
not
the
the
ones
that
should
be
on
our
radar.
C
What's
super
cool
now.
Is
that
this?
This
probably
shouldn't
be
super
cool,
but
I
think
that
in
a
geek
security
way,
it
is
very
cool,
broken
access,
control,
insecure
design,
security,
misconfiguration,
that's
all
in
the
top
five.
That's
awesome,
that's
not
awesome,
it's
good
it,
but
it
does
realign
the
way
we
think
about
just
misconfigurations
and
infrastructure,
as
code
is
key
to
the
way
we
provision
our
cloud,
our
kubernetes
kind
of
everything.
C
So
a
lot
of
this
stuff
is
becoming
very
important.
Infosec
and
afsec
are
aligning
just
like
dev
and
ops
did
so
long
ago.
It
is
important
and
kind
of
what
the
takeaway
here
is
that
coding
issues
like
what
we
used
to
think
we
were
writing
things
wrong,
like
sanitizing
inputs
and
making
sure
we
can't
get
cross-site
scripting,
and
these
are
being
replaced
by
straight-up,
misconfigurations
or
dependency
supply
chain
risks.
C
So
this
is
why
we're
doing
talks
like
this
to
try
and
raise
the
profile
of
these
things
and
how
we
can
have
security
mitigations
in
place
for
those
risks
awesome
the
problem,
obviously,
that
these
things
bad
designs
and
misconductions.
What
the
problems
that
happen
is
all
well
all
sorts
right.
There
are
lots
of
precedence.
I'm
not
going
to
get
into.
I
could
spend
the
whole
time
talking
about
examples,
but
huge
outages.
C
Now
the
good
news,
in
addition
to
the
oauth
top
10,
is
that
misconfigurations
are
certainly
things
that
are
the
way
we
can.
The
way
our
our
new
environments,
like
cloud
native
and
kubernetes,
can
be
compromised.
Those
are
becoming
first-class
citizens
and
that's
great
just
take,
for
example,
this
ingress
nginx
issue.
Let's
call
it
from
last
october:
it
got
a
cve
number,
which
is
common
vulnerability,
enumeration
normally
reserved
for
things
that
we
associate
with
more
absent
style
things,
and
that
is
a
good
thing.
C
I
mean
it's
not
good,
that
there
are
bugs
coming
up
in
kubernetes
and
associated
associated
components,
but
it's
good
that
they're
getting
the
attention
they
deserve.
So
that's.
That's
pretty
solid,
all
right,
so
there's
the
problem.
What
are
we
trying
to
solve
is
to
make
sure
all
these
bad
things
don't
happen.
What
are
we
using
to
provision
and
how
would
we
create
these
problems?
Well,
we're
using
infrastructure's
code.
Most
people
are
very
few
people
are
going
into
the
console
and
going
click.
Click
click
all
right.
C
Thanks
now
again
this
three
bucket
click
click
click,
we're
not
really
doing
that
anymore,
we're
creating
it
as
code,
we're
putting
it
into
git,
and
that
is
our
single
source
of
truth
and
we're
doing
it
in
a
variety
of
languages.
Now
I've
got
a
few
in
bold
here,
there's
a
good
reason
for
that.
Now,
I'm
going
to
be
focusing
by
the
way
on
I'm
going
to
say,
gamble,
helm
customize,
my
repo
is
done
in
customize
because
I
like
customize,
and
it
still
represents
yaml.
C
C
Now,
there's
a
lot
of
really
good
alternatives
to
declarative
methods
like
ansible,
still
super
popular,
believe
it
or
not.
Bash
super
popular
still,
of
course,
probably
never
going
to
go
away:
lots
of
procedural
things
done
in
bash
and
really
new,
exciting
ones
like
palumi
that
are
really
playing
into
the
hands
of
languages.
We're
really
familiar
with
like
typescript,
to
create
infrastructure's
code,
so
these
are
all
very
valid
and
very
cool.
But
what
do
I
like
about
declarative
methods
and
particularly
how
kubernetes
leverages
them?
C
C
Bash
is
going
to
say:
I
want
to
preheat
the
oven,
I'm
going
to
set
my
layers
to
zero,
I'm
going
to
go
into
a
bit
of
an
f
loop
to
make
sure
the
oven's
at
temperature
and
I'm
going
to
go
through
and
I'm
going
to
mix
the
flour
with
the
egg
circular
style,
I'm
going
to
make
it
mix
it
until
it's
fluffy.
What
does
fluffy
mean?
I
don't
know,
I
don't
know
how
to
bake.
Nevertheless,
we're
gonna
bake
it
for
30
minutes
and
then
layers
plus
plus
until
we
have
all
our
layers.
C
I
haven't
even
started
on
the
icing
fine
over
on
cake
and
here
I'm
using
yellow.
Now
I
could
use
terraform
and
there's
a
question
in
the
chat.
That's
asking
where
the
terraforms
in
between
procedural
and
declarative,
I
would
say
it
is
not,
I
say,
is
very
much
declarative
and
the
things
that
are
a
part
of
things
that
might
make
it
seem
non-declarative,
I
think,
are
generally
bad
practice,
but
that's
a
subject
for
an
entire
other
webinar.
C
What
I'm
doing
is
declared
is,
if
I
am
saying
I
want
this
and
I'm
relying
on
the
creation
of
it
and
this
maintenance
of
its
state.
So
I'm
getting
asking
for
a
chocolate
cake.
I
am
asking
for
two
layers.
I
am
going
to
use
the
fluffy
sponge
image
for
my
sponge,
because
I
trust
that
one
and
I
have
scanned
it
and
it's
all
good
and
kubernetes
is
going
to
make
that
happen,
and
it's
going
to
make
sure
it
stays
that
I
always
have
two
layers.
C
C
I
run
my
declarative
twice:
declarative
whatever,
whatever
the
provider
in
the
case
of
terraform
or
the
orchestrator
in
terms
of
kubernetes,
looks
and
goes,
you
already
have
a
cake,
you're
good.
So
that's
the
idea.
You
can
run
it
more
than
once
and
you
still
get
the
same
result.
That's
a
key
piece
of
declarative
technology.
What's
also
nice
is
that
when
I
look
at
what
I
want,
I
see
I
see
the
end
state
and
that's
great
for
security,
because
it
means
I
can
check
and
go
well
that
end
state
is
not
secure.
C
When
I'm
looking
at
procedural
well,
I
kind
of
actually
need
to
understand
all
the
logic,
because
procedural
for
the
most
part
is
called
tiering
complete.
So
it
means
you
can
do
everything
with
it.
You
can
create
loops.
You
can
get
loops
wrong
and
create
a
million
layers
and
it's
very
difficult
to
apply
security
to
understand
the
end
result
and
that
quite
it
really
requires
some
advanced,
almost
static
analysis
tools.
C
All
right,
what
is
get
ops,
I'm
sure
you
know
what
git
up
says,
but
let's,
let's
do
my
take
on
it
just
to
double
down
on
that
get
ops
is
great.
It
started
2017
this
the
cncf
friendly
chap
here,
alexis
richardson,
who
also
lives
in
the
same
neck
of
the
woods
that
I
do
first
started,
describing
git
ops
patterns
and
kind
of
coined
the
phrase
yay
hooray
alexis
shortly
afterwards.
C
This
legend
of
kubernetes
left
a
comment:
oh
github's,
the
best
thing
whoa,
but
more
importantly,
what
I
put
in
bold
declarative
configuration
is
the
key
to
dealing
with
infrastructure
as
code.
I
completely
agree
with
that
and
kind
of
just
afterwards.
Maybe
it's
almost
a
throwaway
comment.
It
sets
the
stage
for
the
next
generation
of
tools.
Well,
checkup
is
one
such
tool
that
actually
leverages
this
declarative
nature.
C
So
in
the
combination
of
state
as
code
and
the
code
being
the
single
source
of
truth,
then
we
have
this
concept
of
potential
for
runtime
immutability,
where
we
never
change
runtime,
we
only
ever
change
code.
This
is
all
good.
It
means
we
can
apply
security
super
early,
all
right,
quick
recap:
declarative
infrastructure.
C
C
These
are
the
kubernetes
open
source
infrastructure
code,
languages
that
are
famous
for
well,
most
yeah,
I'd,
say:
yaml
is
probably
mostly
famous
for
kubernetes,
of
course,
things
like
github
actions
as
well
declaring
resource
objects
and
relationships,
and
we
can
leverage
that
for
security,
because
githubs
establishes
get
as
the
single
source
of
truth
get
equals
run
time.
So
why
scan
runtime
when
I
can
scan
get
because
I
know
what
the
state
is
going
to
be
fabulous
now,
something
I'm
not
going
to
talk
about.
C
C
All
right,
let's
take
a
little
journey
alongside
all
of
our
code.
Our
code
starts
on
our
desktop
as
a
small
child,
and
it
moves
throughout
the
pipeline
through
all
these
various
stages
which
are
kind
of
the
hatches.
These
are.
These
are
the
moments
that
well
security
enthusiasts,
like
me
like
to
think
all
right.
Well,
can
I
throw
some
security
in
there?
How
hard
is
that
going
to
be,
and
then
there's
a
reality
of
who's
responsible
for
each
part
of
this
pipeline?
C
How
difficult
is
it
to
put
those
in
place,
and
you
can
kind
of
see
I've
got
some
markers
on
there
certainly
way
over
on
the
left
on
the
desktop.
If
I
find
a
problem
in
my
desktop,
whether
it's
just
a
programmatic
problem
or
whether
it's
like
just
a
spelling
mistake
or
a
missing
whatever
or
bracket,
I
mean
I
find
it,
I
fix
it
there.
There
are
lots
of
in
ide,
linters
and
checkers
that
help
me
do
all
that.
C
That's
the
fastest
and
easiest
way
to
fix
problems
right
there
and
then
what's
cool
is
that
that
labor
is
divided
amongst
thousands
of
developers
and
I'm
probably
maybe
only
looking
at
same
only
looking
at
one
large
deployment
that
has
10
different
resources,
the
service
and
ingress
pods,
all
that
kind
of
stuff
right.
I
got
it
all
in
my
head,
it's
all
good!
C
Well,
it
progresses
through.
I
might
do
some
things
on
the
command
line,
so
I
included
it
there
because
there
is
an
option
for
security
there.
Maybe
I
set
some
things
up.
Maybe
I
do
my
git
via
the
command
line,
and
I
maybe
I
use
something
pre-commit
if
you're
not
familiar
with
pre-commit
there's
a
pre-commit
hook
that
you're
that
you
can
use
a
framework
and
we'll
see
it
in
a
moment
and
then
it
goes
into
ci.
So
this
is
why
we're
kind
of
all
safe
in
blue
in
ci.
C
C
Well
now,
that's
the
scary
part
that
the
poor
10
security
people
and
by
the
way
that
is
a
roughly
accurate
estimate.
If
you've
got
a
thousand
developers,
you
probably
have
10
security
people
and
they're
monitoring
and
they're
just
kind
of
sweating
and
hoping
for
the
best
that
they
don't
ever
detect
an
anomaly
and
that
their
complicated
security
tools
that
are
looking
for
those
anomalies
are
complicated
enough
for
the
complication
of
the
anomalies.
It's
nuts,
it's
not
a
it's!
C
The
reality
of
deploying
is
that
monitoring
is
always
going
to
happen.
You
have
to
do
it,
but
your
value
for
money
is
in
ci
really,
because
whether
it
be
github
actions
or
circle
ci
or
whatever
it
is,
you
want
to
do.
There's
there's
always
going
to
be
some
way
to
drop
some
easy
security
in
there
and
check
off
is
no
different.
There
is
an
easy
way
to
do
that,
but
from
a
from
a
developer
perspective,
what
I'm
trying
to
demonstrate
here
is
that
there
are
earlier
options.
C
C
Maybe
it's
quicker
if
you're
enterprise
it
might
be
weak,
but
there's
there's
there
is
a
kind
of
a
published
average
there
and
that's
not
great
right,
because
I
always
like
to
think
when
I've
checked
something
again.
It's
like
I'm
done.
I
can
go
work
on
something
else
now
I
can
switch
my
brain
into
a
new
gear
and
I
can
go
so.
How
can
I
make
sure
that,
even
though
I
know
that
there
will
be
security
measures
in
ci
they're
not
going
to
bother
me
all
right?
Well,
let's,
let's
take
a
look.
C
Let's
take
a
look
at
how
we
can
do
that
an
easy
way
and
then
I'll
start
by
introducing
chekhov,
because
if
you've
never
heard
of
chekov
well,
then
I
have
to
tell
you
what
it
is:
don't,
of
course,
free
and
open
source
misconfiguration
scanner
for
iec
for
infrastructure
as
code
intended
to
be
used
in
ci
pythons,
that's
kind
of
how
it
was
originally
built,
how
many
there's
lots
of
different
rules
and
checks
and
policies,
but
those
span
many
many
languages.
It
covers
all
major
infrastructures
code
languages,
it's
not
like.
C
I
have
thousands
for
kubernetes
you
bring
it
explode
to
even
consider
that
there'll
be
that
many.
I
hope
there
isn't,
but
they're
mainly
best
practices.
Some
of
them
are
certainly
security.
Related.
Some
of
them
are
just.
This
is
a
bad
way
to
do
things
and
a
lot.
Some
of
them
are,
I've,
got
graph
based
analysis
checks.
That
just
means
we're
checking
relationships
as
well.
So
if
this
is
connected
to
this,
then
let's
just
make
sure
that
all
makes
sense
you
can
get
it
for
free
at
checkoff.io.
C
I
have
a
checkup
data
right
here.
If
you
just
want
to
kind
of
bring
that
up
hey
there,
we
go
that's
what
check
out
fire,
you
can
download
it.
You
can
look
at
that.
It's
free
go
grab
it
all
right,
customize.io,
okay,
so
you
may
use
ammo,
you
may
use
helm,
you
may
go
okay,
I've
heard
of
customize,
but
I
don't
really
use
it.
You'll
notice
there's
a
little
goat
on
top
of
the
m
here.
C
That's
because
we're
working
on
a
repo
you
can
see
it's
in
huge
on
the
bottom
of
the
screen
bridge
crew,
io
customized
code,
where
we're
trying
to
create
a
development
deployment.
It's
in
the
next
deployment.
It's
got
its
own
container
image.
That
is
just
frankly
default.
Let's
call
it
default,
it's
not
secure.
Defaults
are
really
secure
and
then
there's
a
path
for
prod
that
actually
everything's
fixed
and
it
should
go
past
most.
C
Okay,
getting
back
to
here,
what
we're
going
to
do
is
you
can
see.
I've
got
the
little
hatches
right
if
runtime
equals
freedom,
then
we
need
to
get
through
all
of
these.
In
order
to
make
that
happen,
and
I'm
going
to
show
how
what
the
security
measures
kind
of
look
like
at
each
one,
I
guess
it's
probably
easier
to
do
it,
and
so,
ideally
we're
going
to
go
backwards.
C
I'm
going
to
start
hatch
five
then
go
to
four
and
then
three
to
another
one,
and
then,
hopefully
you
get
a
feel
for
when
security
people
like
to
lecture
or
about
shift
left
or
if
you
go
to
a
conference
and
you're
like
what
is
shift
left.
You
see
this
in
kubecon
or
you
see
it
somewhere
right.
This
is
what
we're
talking
about
this
meet
this.
We
assume
developers
know
what
that
means,
and
frankly,
most
of
the
time
they
don't.
C
C
Let's
do
some
hands-on:
let's
do
some
playing.
This
is
way
more
fun.
Let
me
adjust
my
microphone
and
try
not
to
make
it
so
noisy,
hatch.
Five.
This
is,
I
think
this
is
the
one
from
lost
that
series
lost
all
right.
This
is
a
kubernetes
admission,
controller
location
deployment,
the
pros
of
an
admission
controller.
A
C
Now
this
is
this
is
personal
opinion.
Let
me
just
make
that
absolutely
clear:
it's
applying
the
no
brainer
security
controls
pre-flight,
if
you've
gotten
all
the
way
to
the
point
where
kubernetes
is
checking
what
you're
doing.
I
hope
you've
done
some
stuff
beforehand
right,
because
certainly
the
admission
controller
that
we've
got
for
check
off.
It
doesn't
check
everything.
It
checks
the
stuff.
That's
super
bad!
Think
of
it
like
a
bouncer
at
a
club.
The
bouncer
doesn't
want
to
know
your
back
history.
It
doesn't.
C
C
So
if
I'm
using
something
in
my
admission
controller-
and
I
can
use
that
earlier-
the
same
checks
with
the
same
tools-
that's
good,
because
that
means,
if
I
pass
my
own
my
own
security
standards
using
this
tool,
then
there's
gonna
be
some
weird
thing
in
the
emission
controller.
That's
gonna
catch
me
out.
So
knowing
you
know,
it
sets
reasonable
expectations.
So
that's
a
good
thing.
Consistency
I
bridge
crew
platform
does
measure,
does
keep
track
of
checks
even
if
they're
on
the
command
line.
So
you
have
a
single
point
of
reference.
C
I'm
only
going
to
say
this
here
because
I
realize
it
sounds
like
an
ad
so
forget
that
optional
errors
are
not
always
conveniently
develop
visible
to
developers
getting
blocked
by
a
mission.
Controller
is
well,
it's
kind
of
annoying
actually
fixes
may
require
reading
documentation.
I
had
to
put
that
in
there
because
it's
kind
of
obvious
right,
so,
let's
see
in
action.
What
does
that?
What
happens
all
right?
So,
let's
swipe
over
here,
let's
make
sure
my
kubernetes
cluster-
is
still
alive
by
just
seeing
what's
in
it.
C
All
right,
so
I've
got
a
I
am
using.
What
am
I
using
I'm
using
a
rancher
desktop,
so
I
have
a
rancher
kubernetes
cluster
here,
I'm
in
my
kubernetes
goat
directory,
and
you
can
see
that
I've
deployed
a
validation
web
hook
here.
This
is
the
one
sketch
I
have
hiding
out
in
it
and
I'm
going
to
use
I'm
going
to
just
do
the
basics
first,
though,
actually
my
marine
public's,
like
boom.
C
Okay,
now
you
can
ignore
all
this
stuff
at
the
top,
because
this
is
just
me
setting
up
the
image
but
down
here
this
is
the
these
are
the
manifests.
I
can
probably
get
away
with
doing
that.
Okay,
great
here's
the
base
now
the
way
customize
works.
If
you
don't
already
know
it's
kind
of
like
a
class
structure,
which
is
why
I
really
like
it
my
base
deployment
is
here:
it's
got
my
deployment,
my
service,
my
storage.
I
could
have
put
these
on
one
file,
but
I
like
the
fact
that
they're
separated
out.
C
Why
is
it?
Because
what
customize
does
is
it?
Creates
this
overlay
or
almost
like
an
override
so
for
development?
I'm
not
overwriting
anything.
In
fact,
all
this
customized
yaml
says
is
my
base
is
up
here
in
base
so
that
there's
a
kind
of
drawing
a
connection
between
the
two
same
as
customize
says
my
overlays
are
here,
so
there's
just
a
simple
file
that
says
this
is
how
we
do
things.
C
C
C
So
look
at
this
weird
thing:
this
is
an
overlay
and
actually
all
I'm
doing
is
changing
the
replicas,
adding
some
annotations
and
adding
some
anti-infinity,
but
on
its
own
this
is
useless.
So
hopefully
you
get
a
feel
for
that.
Just
imagine,
base
plus
overlay
equals
deployment
or
equals
result
manifest.
That's
what
we're
going
to
do
so
we
clear
this
and
let's
have
a
go.
C
Then
let's
apply
the
bad
one
right
k
now,
if
you're
not
familiar,
customize
is
built
into
cube
ctl
instead
of
a
dash
f
use,
dash
k,
it's
right
there,
you
don't
have
to
have
a
plugin
or
anything
super
special
like
that.
Just
do
it.
You
know
overlays
and
I'm
going
to
go
dev,
that's
it!
I
want
everything
in
there
to
go.
C
That
seems
to
make
sense
to
me.
There's
a
service
in
there
yep
that
works.
Nothing
wrong
with
the
service,
so
remember
there
was
no.
I
think
there
even
was
a
service
file
in
there,
so
it
grabbed
it.
Oh
no
dev
doesn't
have
anything.
So,
let's
grab
the
service
out
of
base.
Now
this
is
taking
a
little
longer.
C
Why?
Because
the
deployment
is
not
great
and
when
it,
when
the
oh,
when
the
admission
controller
doesn't
fails
it
like
that
we're
going
to
get
some
some
feedback.
So
this
is
pretty
standard.
Kubernetes
stuff
here
error
from
the
server
when
creating
this
admission
web
hook,
the
ninth
request:
okay,
normal
just
that'll,
any
any
admission
controller
will
do
that.
C
C
Now
there
is
17
total
issues,
so
this
is
what
I
meant
by
the
no
brainers
the
we
have
the
mission
controller
by
default
list
looking
for
really
bad
stuff,
but
we
do
give
you
a
link
on
how
to
go.
Look
at
all
the
rest
of
it.
I'm
not
going
to
go
there,
I'm
just
making
you
aware
you
can
do
that,
okay,
so
that
is
what
it
looks
like
now.
Where
would
this
text
be?
C
C
All
right,
the
cons,
error's
not
conveniently
visible.
We
talked
about
that
all
right,
ash
number,
four,
there's
the
safe!
That's
what
we're!
After
what's
hatch,
four
uh-huh,
this
is
the
roi
location.
This
is
where
security
is
definitely
gonna,
be.
If
it's
not
there,
it's
gonna,
be
there
soon
you
get
far
more
granular
security
controls.
You're
not
gonna,
be
looking
for
the
low
hanging
fruit,
the
bad
stuff
just
root,
you're
gonna
you
can,
you
can
do
everything
there
again
controlled
by
git.
C
Plug-Ins
are
available,
so
super
easy,
instant
roi
for
both
security
and
ops
awesome
cons
once
again,
eleva
the
errors
are
not
conveniently
there
for
you.
So
let's,
let's
take
a
look
at
what
that
looks
like
now.
I
have
to
go
the
other
way
back
over
here,
all
right,
here's
customize
code.
I
hope
that's
big
enough.
I
think
it
will
be.
I
can
probably
bump
it
up
a
little
bit,
so
we
can
do
that
all
right
now
we
saw
the
tree
of
what's
here
it's.
C
This
is
exactly
the
repo
customize
scope,
I'm
going
to
pop
and
look
at
the
workflows.
I've
got
two
workflows
set
up.
I've
got
one
for
prod
and
actually
I
think
I've
specifically
set
up
prod
only
to
ever
go
when
I
make
changes
to
prod
and
I
need
to
add-
I
only
just
made
this
so
I'll-
add
bass
to
that
and
then
for
dev.
I'm
checking
anytime
anything
changes.
This
is
going
to
fire
this
morning.
C
I
actually
made
a
change
to
the
name
of
preflight
and,
of
course,
my
check
for
devcd
ran
to
reduce
security
and
it
failed.
Now
you
can
see
there's
an
annotations
here,
we're
opening
a
server
format,
so
we
can
see
some
of
the
bad
things
that
are
here,
which
is
all
right,
and
if
I
want
to
look
apply
security
context,
I
can
click
in
here
and
it's
going
to
leap
into
my
logs
and
jump
down.
Show
me
exactly
where
that
one
was
okay,
it's
getting
a
little
better.
C
I
can
see
that
I
should
not
run
with
a
lot
of
privilege
escalation
or
I
can
look
up
and
see
that
readiness
probe
should
be
configured
like
this
is.
These
are
all
good,
legitimate
things
that
I
probably
should
learn,
learn
how
to
do,
and
in
fact
I
can
even
click
here
on
these
guides,
and
I
can
go
straight
to
the
information
that
tells
me
how
to
fix
it
with
little
cut
and
paste
answers
that
I
can
add
to
my
code
cool
we're
getting
better
because
now
I'm
getting
some
help,
I'm
getting
I'm
getting
fixes.
C
C
Hatch,
three,
the
ones
that
we
can
do.
I
think
that'll
make
life
a
lot
easier
pre-commit
if
you're
not
familiar
with
pre-commit.
Let
me
just
talk
about
the
pros
of
pre-commit.
Again
you
get
the
same
advantages
you
had
before
errors
are
visible
to
developers.
You
don't
have
to
use
the
api
keys
or
bridge
group
platform.
All
all
that
stuff
is
optional,
checkups
free!
You
can
use
it
for
lots
of
stuff.
C
You
thought
you
were
done,
that's
one
of
the
things
that
drives
me
nuts,
I
like
pre-commit,
but
it's
again
one
of
these
things
where
it's
like.
I
am
about
to
go
for
lunch.
I
am
not
fixing
security
issues,
so
there
can
be
a
lot
of
errors
because
pre-commit
implies
you
waited
to
the
end
to
commit.
So
if
you
did
a
lot
of
stuff,
then
there
could
be
a
little
bit
of
trouble
there.
C
So
just
as
an
intro,
if
you
don't
know
pre-commit,
I've
got
it
here.
It's
a
really
super
easy
thing
to
install
that
takes
advantage
of
the
commit
hooks
that
allows
you
to
write.
Little
tiny
manifests
that
run
certain
things
before
you
commit
and
allow
commits
to
adhere
to
certain
measures
of
of
quality
security.
Whatever
you
want
right.
So
if
I
look
at
cat
dot,
pre-commit
config
and
don't
hit
it
twice,.
C
Well,
I
can
see
them
in
my
pre-commit
config
and
by
the
way
this
is
part
of
my
get
repo,
so
we're
kind
of
like
in
a
half
way
house
now
between
ops,
controlled
security
and
kind
of
a
collaboration
between
ops
and
developers,
because,
as
a
developer,
I
need
to
have
the
pre-commit
installed
on
my
on
my
local
machine,
okay.
Otherwise
this
gets
ignored.
However,
this
file
can
be
in
the
control
of
security
and
ops
to
say
what
gets
run
so
that
we
know
we're
now
we're
in
a
hybrid,
very
devsecops
kind
of
situation.
C
So
it's
going
to
go,
get
the
tools
I
need,
if
I
don't
already
have
them
pinned
to
a
certain
version,
so
everything
stays
consistent.
It
knows
I'm
using
customize
because
that's
the
type
of
repo
it
is
so
okay
cool.
If
I
do
a
get
status,
I
can
see
that
yeah.
I
did
recently
make
some
changes
to
this
product
deployment.
Everything's.
Okay,
it's
a
few
other.
I
don't
really
care
too
much
about
it.
Okay,
all
right!
Let's
just
do
the
one.
I've
got
right
there,
let's
clear
that
out
and
let's
do
let's
commit
that
one.
C
Okay
boom
and
you
notice,
as
he
needs
to
do
some
normalization
of
his
pre-commit
config,
but
that
doesn't
matter
it's
still
going
to
run
check
off
just
before
I
do
this
commit
to
make
sure
what
I'm
actually
putting
there
passes
the
test
and
it
does
not
yeah
okay,
so
this
actually
kind
of
looks
familiar
now.
This
is
the
same
stuff
that
we
saw
earlier,
except
now
it's
in
beautiful
color.
I
do
like
that.
C
We
have
the
same
help
and
we
know
code
segments
because,
if
there's
a
lot
of
different
resources
in
one
file,
it
actually
highlights.
This
is
the
resource
specifically
that
have
the
problem,
and
I've
got
all
the
same
things
that
I've
got
there
before.
Okay,
good,
that's
kind
of
good,
but
if
we
see
all
the
things
I
got
wrong.
C
No,
I
waited
a
little
too
long
and
I
wouldn't
even
say
I
waited
too
long,
because
this
was
a
cut
and
paste
from
the
internet,
so
I
pasted
it
and
went
to
community
and
then
ran
out
of
the
box.
It's
like
nope,
you
gotta
do
a
little
bit
extra
work
here
before
we're
gonna
allow
this
in
yikes,
certainly
not
gonna
get
past
ci.
C
Definitely
not
gonna
get
past
the
bouncer
at
the
door
of
my
kubernetes
cluster,
okay,
but
not
bad
everything's
on
my
local
system
now,
and
I
can
see
it
all,
so
that's
a
plus
all
right.
We
did
that
already
hash
number
two
command
line
very
similar
rows,
all
the
same
as
you
had
in
the
previous
one
right.
You
can
see
everything
it's
all
there.
Granular
security
controls
all
really
good,
except
it
command
lines
are
optional.
C
C
He's
like
I
hope
you
do
it,
but
you
kind
of
probably
won't.
Maybe
not
that's
not
great
and
again,
if
it's,
if
there's
a
lot
to
it,
there
could
be
a
lot
of
errors.
Also,
you
need
to
understand
the
command
line.
Options
yeah
we
didn't
have
to.
We
haven't
even
looked
at
that
so
far
and
we've
had
lots
of
cool
results
right.
So
let's
come
back
over
here
and
let's
see,
let's,
let's
take
this
now.
C
Other
command
line
tools
are
available,
but
they
probably
all
look
the
same
in
that
they
have
an
absolute
bucket
load
of
command
line
options
which
is
both
horrifying
and
exciting
because
it
means
wow.
This
thing
does
everything
and,
oh,
my
goodness,
I've
got
to
learn
how
it
works.
That's
a
disaster.
C
I
mean
the
good
news
for
this
particular
one
is
that
it's
generally
easy
for
the
most
part
you
watch
like
a
basic
how-to
on
this
dash
d
means
check
everything
below
me.
I
don't
even
have
to
say
what
frameworks
it'll
just
figure
it
out
on
its
own,
so
it's
both
difficult
and
easy
at
the
same
time,
like
all
command
line
tools,
in
this
particular
case
say
I
I'm
going
to
say
framework
yes
and
there's
customize
right
there,
so
I'm
going
to
say
just
look
for
it.
It's
faster,
if
you
just
say,
use
the
customize.
C
C
Is
that
now
you
remember
the
weird
one
that
was
in
test
that
just
didn't
make
any
sense.
If
you
tried
to
scan
that
with
some
tools
that
you
use
for
yaml,
it
would
look
like
garbage.
It
wouldn't
work.
I
I
I
like
this
because
it
does
understand
the
fact
that
that
bunch
of
garbage,
if
I
go
if
I
type
customize-
oh
let's
get
rid
of
that.
So
I
get
my
autocomplete
on
overlays
test.
C
It
understands
in
advance
to
combine
them
and
use
the
customized
present
in
kubectl
to
kind
of
create
the
manifest
so
that
I
only
get
the
combined
correct
output.
So
that's
also
very
cool
and
important,
but
I
have
the
same
thing
I
saw
before.
So
it's
just
as
difficult
or
as
easy
as
it
was.
If
I've
only
got
one
thing
wrong
great.
If
I've
got
a
lot
of
things
wrong,
it
can
be
a
big
elephant
to
eat.
A
C
C
You
get
the
same
level
of
granular
security
controls.
You
get
all
the
stuff
you
can
put
and
get
you
get
errors
conveniently
visible
to
you
and
fixes.
Now.
This
is
a
little
caveat
right.
I
have
to
say
and
fixes,
because
chekhov
does
have
the
notion
of
providing
instant
fixes,
particularly
in
the
ide,
in
fact,
I
think
exclusively
in
the
id
also
in
the
platform,
but
for
developers
right
there,
except
not
for
kubernetes.
C
Yet
it's
one
of
the
projects
that
we're
working
on
I'm
working
on
it
soon
coming
soon,
so
I
put
it
in
there
anyway,
but
we'll
see
evidence
of
it.
When
we
look
at
the
idea
in
a
moment,
no
need
to
learn
the
command
line,
options,
huzzah,
everything's
kind
of
abstracted
away
yay
when
you're
done
you're
done
these
all
sound
good.
What
are
the
cons,
I
don't
know
seems
like
seems
easy.
A
C
C
We
changed
the
version,
it
must
be
100
times
a
day,
it'll
be
at
900
by
tomorrow
and
if
you're
familiar
with
squiggly
lines
in
vs
code,
by
the
way
we
support
jetbrains
ids
as
well
checkoff
does,
I
think
most
ides
tools
try
to
support
most
things.
You
install
it
over
here.
It's
there,
it's
easy
to
find.
There's
my
corn
flakes
there's
my
eslant
cause
all
the
things
you
expect
and
the
squiggly
line
you
hover
over
and
you
know
all
those
errors
we
just
saw
here.
They
are
again
pretty
cool
right.
C
I
can
roll
down.
What
do
you
know
and
when
I
get
to
the
bottom,
you
see
where
it
said.
No
quick
fix
is
available.
That's
the
coming
soon
that
I
was
mentioning.
We
do
have
quick
fixes
for
some
things,
but
I
got
all
the
same
stuff
I
did
before.
I
can
click
on
these
and
I
can
jump
straight
to
the
how
to's
learn
how
to
do
things
ensure
my
set
comp
profile
is
sent
to
docker
default.
C
Okay,
I
can
click
and
learn
about
that
and
I
can
start
to
make
the
changes
I
need
to
make
in
here
to
make
that
sort
of
thing
correct
so
that,
ideally
I
I
don't
have
any
problems
that
would
be.
That
would
be
wonderful,
wouldn't
it
well.
Let's
just
do
a
little
quick
one.
Then,
let's
I
know
it's,
I
don't
have
a
security
context
either,
which
is
also
a
rule
that
I
shouldn't
I
shouldn't.
C
I
should
have
one
and
I'm
going
to
do
this
here.
Let
me
just
get
rid
of
the
animal,
doesn't
like
weird
things.
So,
okay,
so
I've
added
a
security
context.
I
have
sitcom
profile
and
I've
set
it
to
runtime
default.
That's
me,
being
a
good
boy
now
we
can
see
that
I
still
have
problems
but
set
compost.
My
second
one
and
it's
gone
now.
C
If
I
roll
down
there,
there
used
to
be
two
security
contacts,
because
there
is
two
one
of
them
is
missing,
so
the
one
for
containers
is
now
present,
so
I'm
chipping
away
actually
at
those
17
errors
that
I
had,
and
I
can
slowly
go
through
this
and
make
sure
my
base
is
good
to
go
now.
This
makes
sense
to
have
in
my
base
there's
no
reason
why
this
wouldn't
be
there.
It's
not
like
it's
special,
it's
not
like
for
deb.
I
don't
want
that.
I
might
as
well
leave
it
there.
C
C
C
So
this
is
what
we're
trying
to
do
is
encourage
developers
on
their
desktop,
even
if
you're,
using
a
weird
framework
like
customize
to
transition
yourself
from
what
can
often
just
be
a
default
deployment
to
an
example
of
what
is
a
secure
one
and
to
do
that
with
sort
of
in
ide
helpers
and
help
that
allows
you
to
both
learn
well
how
to
make
secure
code,
but
do
it
in
your
environment
in
advance
so
that
you
blow
through
all
of
those
hatches,
and
that
is
let
me
just
go.
Do
one
my
thing
over
here
now.
C
Actually,
the
service
should
still
be
there.
It
is
okay,
good
that
should
succeed,
and
I
should
that
evidence
that
that
went
all
the
way
through
ci.
It's
all
there.
It's
all
good
and
it's
now
going
to
become
persistent
in
my
kubernetes
cluster
and
I
wasn't
bothered
by
any
of
the
nasty
gates
along
the
way.
C
C
C
The
important
thing
I
was
trying
to
do
is
really
make
make
developers
and
ops
and
create
some
empathy
between
them
all
so
that
you
see
like
security's.
Vision
of
this
is
well.
How
can
I
get
into
automation,
or
how
can
I
avoid
monitoring
too
much?
How
can
I
make
sure
that
at
least
I've
done
all
I
can
as
early
as
I
can
to
make
sure
that
it
goes?
C
And
conversely,
the
developer
experience
is
that
well,
if
we
can
they're
security
vendors
in
particular,
it's
kind
of
a
vendor's
fault,
sometimes
because
don't
make
it
easy,
but
if
we
do
make
it
easy
like
that,
so
that
you
can
learn
about
security,
you
could
kind
of
have
an
education
piece
in
there,
and
you
know
that
all
right
this
wasn't
that
hard.
I
made
a
secure
deployment
and
I
know
it's
just
going
to
fly
through.
We
all
win
right
all
right.
Well,
we
already
saw
it
actually.
In
summary,
this
configurations
are
first
class
problems.
C
Arguably
more
than
the
old
hacker
style
application
vulnerabilities,
one
little
misconfiguration
can
cascade
into
all
sorts
of
bad
things
as
an
attacker
dives
into
the
soft
interior
of
your
development
pipeline
infrastructure's
code
equals
get,
ops,
get
equals.
Runtime
security
and
git
is
good
defaults.
Even
from
trusted
sources
are
not
always
secure
infrastructure,
as
code
security
can
and
should
be
applied
at
all
phases.
The
ideal
is
that
all
of
those
phases,
all
of
those
hatches
are
actually
present,
even
though
in
practice
rarely
are
they
all
there.
C
C
If
we
all
do
it
together,
otherwise
you
might
get
caught
in
ci
or
worse
after
a
the
b
word.
Bad
things
happen.
Okay,
thanks
very
much,
I'm
definitely
out
of
time.
I'm
gonna
see
if
there's
any
questions
in
the
chit
chat,
more
information,
you
can
see
down
there,
bridge
crew,
check
off
customized,
goat,
etc,
etc.
C
C
It
has
a
notion
of
suppression,
so
if
you
want
to
create
well
a
few
different
ways,
frankly,
if
you
have
a
huge
deployment,
you
can
run
check
off
baseline
and
it
will
say
all
right
everything
I
see
I'm
going
to
consider
that's
in
the
past,
it's
technical
debt
and
then
you
run
check
off
again
and
it
will
say,
there's
no
problem.
So
it's
only
looking
for
new
problems,
so
that's
one
way
of
creating
a
whitelist.
Another
way
is
that
you
can
have
hard
fails
or
soft
fails.
C
You
could
just
soft
fail
anything
in
the
past
and
then
there's
the
notion
of
suppressions,
which
are
supported
in
line
or
can
be
supported
through
the
bridge
group
platform,
because
if
you
are
using
the
platform,
you
can
have
global
suppressions
like
for
your
entire
organization,
to
say.
Never
look
for
this
thing
because
it
doesn't
apply
to
us.
So
yes,.
C
C
Yes,
I
well.
Actually
I'm
I'm
a
big
fan
of
reg
up
who
just
said
the
more
the
more
left.
I'm
gonna
say
you
go,
the
happier
you'll
be.
The
reality
is
having
having
all
the
hatches
in
place
is
good
because
they're
all
gonna
be
there
whether
there
are
security
controls
there
are
not
as
a
developer.
I
don't
know
where
they're
going
to
be
necessarily,
I
know,
certainly
a
bridge
crew.
We
use
pre-commit
and
we
use
ci
for
sure.
C
So
I
use
the
id
and
I
make
all
the
fixes.
This
is
more
of
a
personal
experience,
but
more
than
likely
when
you've
got
so
many
different
personas
involved
developers,
ops
and
security,
they're
all
going
to
have
their
moments
where
they're
going
to
add
security,
and
they
will
not
necessarily
care
if
there's
already
security
in
ci
or
you're
already
doing
your
desktop,
so
they
are
going
to
be
in
a
lot
of
different
places
and
there
will
be
defense
and
depth
ideally.
So
it's
not
so
much
as
redundant
as
redundancy
is
a
bad
thing.
B
C
That's
a
really
big
depends
question,
because
you
can
create
custom
policy,
you
can
create
policy
both
written
in
python
and
you
can
create
them
using
very
simple,
logical
gamma,
and
we
have
like
a
little
generator
for
doing
that
in
the
bridge
group
platform.
So
if
you've
got
something
unique
and
there,
if
there's
a
known
security,
misconfiguration
or
mis
misuse
case
that
you
can
characterize,
then
you
can
create
a
rule
that
will
check
anything
like,
for
example,
the
one
that
we
looked
at
earlier,
the
kubernetes
nginx
ingress
when
that
came
out.
Well,
that
was
new.
C
C
That
may
be
a
larger
question
answered.
Yes,
we
support.
Terraform
terraform
is
the
first
language
we
ever
supported,
so
our
coverage
for
terraform
is
quite
extensive,
so
we
can
maybe
I
can
also
say
if
you're
on
the
cncf
slack,
you
can
always
find
me
there
and
you
can
ask
me
more
direct
questions.
So,
let's
I'll
throw
that
out
there
for
questions
that
it
might
take
too
long.
C
Perfect:
okay,
how
can
checkup
helm
with
stacking
ammo
configuration
files,
I
think
you're
saying,
can
you
handle,
can
check
off
handle
helm?
Yes,
is
the
answer?
That's
a
very
quick
one.
I
think
I'm
going
to
say
yes
to
that
anything
else.
Maybe
how
do
you
slack
more
andreas
yeah
feel
free
we're
using
slack
so
much
already
you
somehow
you
need
more.
C
B
B
All
right
well
steve,
thank
you
so
much
this
was
awesome.
It
sounds
like
you
got
a
lot
of
good
back
and
forth
with
everyone
and,
like
I
said,
the
slack
channel
is
in
the
chat
right
above
so
be
sure
to
click
on
that,
and
you
all
can
keep
keep
it
going.
That's
our
online
programs
channel
so
join
it
and
keep
the
conversation
rolling,
and
we
will
see
you
next
time.
