►
From YouTube: Security Approvals Rules Feature Demo / Discussion
Description
No description was provided for this meeting.
If this is YOUR meeting, an easy way to fix this is to add a description to your video, wherever mtngs.io found it (probably YouTube).
A
So
yeah
yeah,
thanks
for
thanks
for
joining
us,
but
you
know,
one
of
the
big
kind
of
catalysts
of
this
conversation
is
a
lot
of
our.
You
know.
Enterprise
level
customers
are
coming
back
to
us
with.
You
know
a
lot
more
interest
in
the
security
products.
We
now
that
we
have
a
lot
more
of
those
dashboarding
tools.
You
know
I
think
that
the
problems
are
running
into
now
around
the
permissions
modeling
and
how
you
know
people
can
demit
dismiss
things.
What
who
can
do
that,
how
you
can
specify
that
clampdown
and
so
forth?
So
they're?
B
A
C
B
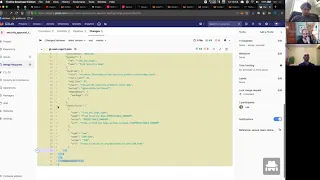
So
for
the
quick
demo
I'm
just
going
to
go
through
the
basic
steps
here,
we'll
be
adding
the
approval
so
just
like
in
the
other
approval
rule
and
there's
an
indicator
within
the
UI
that
this
is
a
special
approval
rule
that
we
have
these
new
settings
and
from
there
we'll
go
through
four
major
flows.
Opening
mr
with
no
report,
so
no
vulnerabilities
at
all
opening
an
mr
with
an
empty
report.
B
So
this
is
what
we're
actually
generating
a
security
report,
but
there
are
no
clutter
abilities
and
that's
actually
two
separate
flows
there
and
then
a
report
with
a
low
severity
vulnerability
and
then
a
high
severity
vulnerability.
So
these
are
the
basic
results,
are
being
approval
required.
When
there's
no
report,
because
if
there's
a
report,
we
should
care
empty
report,
no
approval
low
severity,
no
approval
and
high
severity
also
requires
accrual
got.
A
B
So
I
just
made
this
quick
project
we're
demoing
this
all
it
really
is
is
a
really
simple
readme
file
and
then
to
speed
along
the
process.
I
created
this
kind
of
cheat
CI
script
and
what
this
does
is
I'll
yeah
yeah
it
just
it
looks
for
this
phone.
So
what
we're
gonna
do
in
our
mrs
is
we're
just
going
to
build
the
file
ourselves
just
copy
some
JSON
over.
So
first
up,
we've
got.
B
From
merger
quest
rule,
this
UI
there's
some
some
wonkiness
to
this
right
now.
But
what
we
do
is
we
add
an
approver
here,
and
this
should
really
be
called.
Like
add
approval
rule,
it's
not
add
an
approver.
So
what
we're
doing
is
we're
adding
a
rule,
and
then
here
I'll
say
this
is
an
actual
approver
to
the
rule.
B
This
is
on
staging,
so
I'm
not
really
sure
what
groups
exist
there.
We
go
sure,
so
we're
just
go
ahead
and
add
both
of
those
there
and
then
the
way
this
currently
works.
Is
it
pattern
matches
against
a
very
precise
approver
name.
So
we
have
Doc's
on
this,
but
I
will
just
add
this
right
here
in
the
future,
we'll
be
able
to
just
select
this
from
drop-down,
similar
to
like
templating
for
CI
templates.
B
B
C
B
A
B
On
the
on
the
back
end
of
this,
there
is
actually
this
is
handled
properly
and
back
in
where
we
actually
have
a
state
model
for
like
approval
rules,
and
so
this
is
called
a
general
accrual
rule.
And
then
this
is
called
a
report.
Approval
rule
okay,
where
we
built
this
model
to
support
other
kinds
and
currently
license
truck,
is
doing
similar
things.
So
the
ideas
for
blacklist
and
whitelisted
licenses
and
we'll
use
the
same
data
model,
but
like
a
different
name
here
so
on.
A
B
Currently,
it's
just
this
minimal
one
here
and
it
was
more
good
eating
something
minimal
into
customers
hands,
so
you
can
actually
see
if
this
makes
sense
or
this
direction.
Aids,
even
the
right
way
to
go
in
the
future.
I
think
that
we
would
either
have
a
drop
down
here
or
possibly
like
a
state
drop
down,
so
you
can
say,
like
regular
rule
or
like
report
approval,
rule
yeah.
A
C
A
A
B
B
B
B
This
this
actually
got
missed
in
the
initial
work,
but
there
should
be
a
hover
tooltip
right
here
as
well
to
indicate
this,
but,
as
you
can
see,
just
got
copied
over
the
default
state
is
requiring
that
approval
and
when
this
pipeline
finishes
it
should
stay
the
same.
Because
if
there's
no
security
report,
we
still
require
approval.
B
So
there's
there's
two
two
hook
points.
One
is
when
a
it's
called
I
think
the
service
is
called
like
refresh,
merge
request
and
that
fire
is
when
you
open
a
merge
request
or
when
you
push
any
code
and
that
always
resyncs
the
rules,
so
it
resets
this
number
to
whatever
the
setting
is
of
the
project
and
then
after
the
pipeline
runs.
It
optionally
can
decrement
this
to
zero.
If.
A
B
B
B
A
B
A
B
Part
of
the
reason
that
we
didn't
explore
that
too
deeply
what
we
initially
built.
This
is
because
it
gets
really
noisy,
really
quick,
because
you
have
the
reset
and
the
decrement
recent
decrement
with
every
code
change.
So
you
just
fill
up
the
log
there.
So
we've
been
looking
at
strategies
on
how
to
like
reduce
that
noise.
B
Yeah
I
make
silent
demo
just
one
change
here
with
this
one.
What
I'm
going
to
do
in
this
case
is
I'm
going
to
push
up
a
change
to
this
wrench.
That
is
just
like
a
text
change,
but
what's
going
to
happen,
is
when
I
push
up
the
code,
this
is
going
to
become
required
again
and
then
read
Eckerman,
and
that
just
demonstrates
that's
slow,
real,
quick.
C
B
B
A
Cool
yeah
this
makes
sense
I
appreciate
running
through
that
I
think
this
would
be
good
to
get
in
front
of
people
and
see
how
you
know
how
people
interact
with
it
and
what
the
response
to
it
is
I.
Think
that
you
know
one
one
thing
I
see
coming
up
still
in
conversations
is
when
a
vulnerability
comes
back
reported
you
know,
a
developer
could
still
approve
that
that
bar
dismissed
that
vulnerability,
which
you
know
if
someone
would
came
in
to
just
do
a
review.
A
They
may
see
that
that's
been
dismissed
and
say:
oh
that's
been
dismissed
so
that
I
know
I'm
good
here.
I
can
I
can
approve
this
without
necessarily
knowing
that
the
right
person
had
had
done
that
approval
right.
So
I
think
that's
that's
something
that
I
see
coming
up
still
because
it's
kind
of
similar
in
line
with
what's
coming
up
now,
although
again.
B
Definitely
help
for
that
and
one
thing
that
we
then
so
this
is
a
parent
issue
and
I
link
to
this
on
the
top
here.
One
thing
we've
been
trying
to
do
more
and
more
in
development.
Is
we
do
this
thing
called
a
development
log,
and
so
I
include
this
portion
here,
and
this
includes
both
the
status
of
the
issue
as
those
being
developed.
B
It's
because
this
one
took
quite
a
few
changes
to
make
and
then
decision,
points
and
decision
points
here
is
where
you
can
track
the
discussion
on
specifically
that's
just
missing
feedback
will
not
be
disabled
when
security
removals
are
enabled,
because
there's
kind
of
a
lot
of
Education
still
consider,
and
if
you
click
this
here,
you
can
see
where
we
actually
made
that
decision
and
why
we
made
that
decision.
So
this
might
provide
some
feedback
on
where,
where
we
kind
of
win
there,
you
know
totally
it's
awful.
B
So
in
this
case
we
kind
of
had
to
decide
the
full
scope
of
disable.
We
don't
really
have
that
granular
permissions
right
now
and
it
becomes
a
bit
tricky
and
so
that
one
yeah.
We
definitely
need
to
discuss
that
more.
But
it's
a
complicated
question
specifically
like
the
feedback
mechanism
that
you
disable
or
dismiss
it's
not
very
granular,
so
like
we
would
have
to
figure
out
what
which
method
of
interactive
vulnerabilities
to
allow
our
just
low.
It's
not
make
sense
like
creating.
Does
it
follow
up
or
dismissing
right.
A
One
thought
that
I
had
that
I
mean
it's
similar
to
how
this
is
implemented
in
some
ways.
Is
that
when,
when
you
have
a
security
group,
are
secured
someone
somehow
to
prove
ER
for
those
reports,
that
person
is
the
only
person
who
could
be
also
dismissing
those
vulnerabilities
right
in
the
raid.
You
know
in
that,
and
that
would
make
logical
sense,
because
you
would
think
if
that
person
was
there
to
approve
that
those
were
okay,
they
would
have
to
go
through
that
list
anyway.
B
A
A
A
B
C
C
You
know
with
prospects
or
customers,
and
it's
basically
saying
you
know
fine.
You
know
you
do
you
yeah
you're
committed.
You
run
your
pipeline,
you
do
the
security
analysis
there,
but
how
do
we
know
that
you
know?
We've
got
a
baseline
on
on
which
we're
you
know,
making
those
checks
so
I
didn't
know
whether
there's
anything.
Obviously
we
can
run
pipelines.
A
I
kind
of
wonder
that
why
that
you
would
need
that
if,
if
you
were
using
get
flow-
and
you
have
the
feature
branch
model
and
your
master
is
a
protected
branch
that
you
do
your
deployments
from
any
merge
that
gets
into
that
master
branch
is
gonna.
Kick
you
know
that
commit
is
going
to
kick
off
the
pipeline,
so
you
always
have
a
snapshot
of
current
state
in
the
Med.
B
So
part
of
that
is
anytime
you're
in
a
pipeline
on
master
its
running
it
against
everything.
That's
currently
there
there's,
obviously
an
issue
if
it's
like
within
the
get
history
over
time-
and
this
is
oh
sorry,
this
one-
this
is
a
checker
that
we
have
in
12
for
for
triggering
a
secret
detection
on
the
full
history
of
the
repo.
So
this
is
currently
in
development
and
there's
a
bit
of
UI
here
around
whether
how
we
want
to
handle
that
it's
basically,
we
need
some
kind
of
interface
for
users
to
take
off
that
skin.
B
C
C
A
A
A
B
A
B
B
A
Well,
you're
well
you're
kind
of
looking
around
for
that
one
one
thing
I'm
curious
if
this
has
been
brought
up
in
discussion,
was
when,
when
you
have
a
vulnerability
that
needs
to
be
addressed,
you
know
having
that
vulnerability,
Blackey
block
the
you
know
basically
block
the
merge
of
that
merge
request.
I
know
that
you
know
having
approvals,
of
course,
is
kind
of
a
roundabout
way
of
doing
that.
A
But
one
thought
was
that
you
know
we
have
the
resolved
discussions
where
you
have
to
resolve
all
the
discussions
before
you
can
do
that
I
felt
like
it
could
kind
of
fall
in
line
with
that.
You
know
a
discussion
topic
that
has
to
be
resolved
before
you
know
it's
another
chat
or
that,
and
it
would
also
allow
you
to
have
better
link
ability
between
you
know.
B
What
we
currently
see
in
the
UI
is
vulnerabilities,
are
they're,
basically
occurrences,
they're,
current
or
the
term
you've
been
using
its
findings
really,
and
we
need
to
come
with
a
new
way
of
interacting
with
vulnerabilities,
more
similar
to
making
them
kind
of
an
issue
about
objects.
So
the
idea
is,
like
you
can
add
labels
to
vulnerabilities.
You
can
discussions
about
vulnerabilities,
you
can
close
them
wasn't
commit
things
like
that,
and
that's
that
that's
the
idea
with
this
feature
all.
A
B
So
it's
nice
and
he
just
posted
a
gigantic
comment
on
us
15
months
ago.
So
perfect,
timing,
yes,
so
this
the
ideas
of
finding
you
promoted
to
a
vulnerability.
Vulnerability
has
done
something
and
this
atmosphere
like
a
triaging
process.
So
we'll
do
like
a
triage
list.
Once
it's
promoted
to
a
vulnerability,
you
can
even
attach
multiple
findings
to
a
single
vulnerabilities,
such
as
occurrences,
and
then
you
can
create
issues
throughout
the
vulnerability
resolve
it.
It's
actually
very
similar,
something
like
an
epic
model
there.
B
B
Yeah
this
is
this
is
one
that
we're
really
excited
about
getting
to
so
we're
just
wrapping
up
de
discovery
on
it,
and
we
should
start
implementation
on
that
next
release
and
it
could
result
in
quite
a
few
changes.
It
flows
and
the
way
that
vulnerabilities
are
handled
right
now,
but
there's
gonna
be
really
critical.
It
also
allows
us
to
do
things
like
allow
external
sources,
so
we
knew
like
hacker
when
it
reports
coming
in
and
you
can
convert
those
into
vulnerabilities
from
external
sources
as
well.
Yeah.
A
Well,
that
was
really
helpful.
Thank
you.
So
much
for
the
time.
I
really
appreciate
that,
if
there's
any,
you
guys
ever
need
any
feedback
or
anything
like
that
around
you
know
going
through
this
flow,
or
you
know
customer
thoughts
on
this.
You
know
feel
free
to
pull
me
in
and
or
something
I'll
find
some
of
the
team
to
it
to
help
with
that,
we're
happy
to
help
with
these
things
and
looking
forward
to
all
these
changes.
Awesome.
