►
From YouTube: Container Host Security - Getting Started with Falco
Description
Fern with Technical Marketing presents on the value of adding Container Host Security to your infrastructure and takes questions from Customer Success team members.
Key Topics:
* Intro to and Benefits of Falco
* Installing Falco via GitLab-Managed-Apps
* Creating a Custom Rule
* Examining Falco Logs
* Falco Alerts
* Container Host Security Roadmap
A
B
Thanks
john
yeah,
so
today
I'm
going
to
be
covering
container
host
security
and
pretty
much
I'm
just
going
to
be
going
over
how
it
works
within
gitlab
how
to
set
it
up
and
I'll
do
a
little
quick
demo
and
then
have
a
q
a
session
so
just
make
sure
everyone's
pretty
well
caffeinated.
For
this
everybody,
I'm
on
my
like
third
cup
of
coffee
right
now,.
B
B
B
B
So
it's
so
it
searches
all
the
logs
and
then
let's
say
it
finds
a
log
where
directory
is
being
created
and
one
of
the
rules
says
hey
alert.
If
a
directory
is
being
created,
then
what
it'll
do
is
it'll
go
ahead
and
generate
that
alert,
and
then
let
us
know
like
hey,
there's
something:
that's
not
supposed
to
be
happening
on
the
system
or
there's
something
that
we're
monitoring
for
on
this
system
and
we've
detected
that
that
this
has
happened.
So
then
we
can
go
ahead
and
send
alerts
to
whatever
medium
we
want.
B
So
we
can
send
alerts
to
let's
say
pagerduty:
we
can
send
alerts
to
the
gitlab
dashboard,
which
I'll
show
you
a
little
bit
about
that
later
today,
but
something
that
hasn't
been
implemented.
But
it's
in
the
road
map
it
can
send
alerts,
it
can
send
things
to
a
file.
It
can
send
syslog.
It
can
send
things
to
prometheus,
pretty
much
it's
highly
configurable
and
can
be
done.
You
know
in
any
way
that
you
need
so
just
to
give
you
a
couple
of
examples
of
what
the
actual
rules
are.
B
Some
example
rules
are
hey,
let's
alert
when
a
shell
is
running
a
container,
so
it
could
be
something
malicious
happening
where
someone
got
into
a
container
that
they're
not
supposed
to
have
access
to.
Maybe
it's
a
container
that
no
one
should
have
access
to
and
it
should
all
be
deployed
through
the
ci
cd
pipeline.
Well,
if
a
shell
is
running
in,
it
could
be
some
type
of
malicious
intent.
B
Someone
got
in
that
wasn't
supposed
to
so
we
can
alert
on
that
and
we
can
provide
even
more
details
on
you
know
what
exactly
the
shell
script
that
was
running
is
writing
to
directories
that,
like
slash
dev,
which
shouldn't
be
written
to
unexpected
connections,
non-authorized,
namespace
changes
and,
and
so
much
more
one
of
the
fun
ones,
is
a
process
that
other
than
skype
or
webex
that
tries
to
access
your
camera.
So
it
pretty
much
runs
on
the
container
host.
B
B
B
So
there
is
a
migration
process
to
moving
everything
over
to
the
new
standard,
which
is
going
to
be
the
cluster
management.
Pro
project
template
and
I'll
go
a
little
bit
into
depth
on
that,
but
in
the
future,
I'm
going
to
make
a
video
on
my
grading
so
I'll
make
a
little
video
on
showing
how
to
migrate.
These
applications
since
has
a
lot
to
do
with
the
gitlab
protect
stage,
but
for
now
I'll,
just
just
give
a
little
bit
of
details
on
what
the
actual
cluster
management
project
is.
B
So
let
me
just
go
ahead
and
show
you
so
the
gitlab
manage
app.
So
this
is
this
is
like
the
old
way
of
doing
it.
You
would
include
a
template
to
the
gitlab,
ci
yaml
and
then
you'd.
Add
a
config.yml
under
gitlab
managed
apps
in
the
config,
and
then
you
just
pretty
much
put
the
name
of
each
application.
Input
installed
equals
true
and
what
ends
up
happening
is
for
falco.
It
looks
something
like
this.
You
just
say:
falco
installed,
equals
true
and
then
you
can
add
a
bunch
of
other
data.
B
B
B
And
then,
furthermore,
there's
applications
and
we
can
go
to
falco
and
then
here
we
can
configure
what
values
we
want
like
the
standard
helm
way,
and
we
would
also
configure
a
home
file
to
just
give
more
information
on
where
the
actual
chart
is
housed
and
where
the
helm
files
is
housed,
and
this
is
also
done
for
customizing
things
different
things.
So
this
is
something
new
within
gitlab.
That's
just
been
brought
up,
so
you
know
I'll,
be
adding
more
videos
and
more
details
on
this.
As
you
know,
it
progresses.
B
But
now
to
go
back
and
if
you
want,
you
can
start
adding
your
questions
to
the
document
and
I'll
review
that
document
after
after
this
presentation,
then
we
start
answering
things
one
by
one,
so
custom
rules
and
falco.
So
you
saw
some
of
the
rules
that
you
know
are
already
on
there
and
already
default.
But
what
if
we
want
to
add
something
specific,
so
falco
has
some
guidelines
on
as
to
the
syntax
of
how
you
write
rules.
B
B
This
message
here
so
file
below
and
known
directory
open
for
writing
so
and
it'll
provide
us
information
on
the
username,
the
exact
command
that
was
run,
the
file,
its
parent,
a
whole
bunch
of
other
information.
Now
this
is
all
syntax
that
you
would
have
to
read
from
the
thoughtful
documentation.
So
you
can
structure
it
yourself
and
make
your
own
rules.
You
can
set
the
different
priority
as
to
how
you
want
it
to
learn.
It
could
be
an
error
warning
info
and
then
you
can
give
it
a
tag
and
then
for
more
information
on
this.
B
B
B
So
so
now
that,
let's
say
we
have
now
we
have
falco
installed.
Let's
say
we
have
a
new
rule
for
detecting
a
new
directory.
So
what
do
we
do
with
that?
What
do
we
do
with
all
that
information
like
what
happens
when
a
world
is
detected
like
why?
Why
do
we
care?
Well,
what
we
do
is
we
we
create
alerts
so
that
way,
if
any
of
those
rules
are
ever
broken,
we
can
alert
something
and
have
some
action
performed
so
so
different
ways
of
alerting
the
standard
out.
B
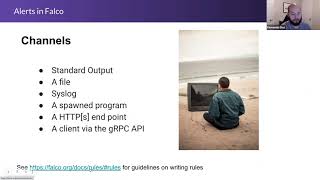
It's
a
file.
You
can
alert
to
syslog.
You
can
alert
to
a
program
to
an
https
endpoint
to
a
client
via
grpc,
so
pretty
much.
I
can
call
anything
an
example
would
be.
I
can
actually,
you
know,
send
myself
an
email
of
hey,
an
alert
was
triggered.
An
alert
was
triggered.
That
would
be
a
very
simple
way
of
doing
it,
but
I
can
also
go
to
slack,
maybe
and
just
have
a
slack
channel
where
every
time
something
is
anytime,
any
rule
is
broken.
B
So
if
I
look
at
how
to
write
an
alert,
you
can
see
that
there
is
file
output,
so
I
just
add
the
syntax,
and
this
will
tell
me
what
file
name
to
go
to
syslog
program
output.
So
this
is
the
one
that
I
wanted
to
show
y'all,
which
is.
I
can
set
a
program
that
I
actually
want
to
to
run
to
run
whenever
a
rule
is
triggered.
So
here
you
can
see
I
just
mail,
someone
sending
a
mail
to
someone
that
there
was
a
focal
notification.
B
So
it's
just
very
simple,
but
this
can
you
know,
get
as
complex
as
you'd
like
it
to
get
or
get
as
configured
as
you
wanted
to
get,
but
pretty
much.
What
will
happen
is
like
anytime,
a
rule
is
broken.
It'll,
just
mail,
you,
a
focal
notification,
follicle
notifications,
so
you'll
get
probably
a
billion
emails
depending
on
your
cluster
and
same
thing
with
slack.
So
you
can
configure
this
to
stack.
B
So
I
couldn't
demo
this
because
I'm
not
a
slack
admin,
so
I
didn't
have
access
to
creating
the
application,
but
at
some
point
I'll
probably
request
that.
But
what
you
can
do
is
you
can
just
get
the
json
output
and
then
just
post
that
to
the
slack
service,
make
a
little
bot
or
something
that
or
a
web
hook,
that
any
time
that
a
rule
is
broken
into
alerts,
it'll,
post
a
slack,
so
this
little
bot
will
go
ahead
and
post.
B
B
B
B
B
B
B
B
Okay,
so
these
are
all
the
logs
for
for
falco,
so
I
just
made
it
nice
in
this
json
format.
But
now,
when
I'm
looking
at
the
different
logs,
you
can
see
that
there's
been
some.
Some
triggers
there's
a
lot
of
different
notices
and
different
things,
but
there's
been
some
triggers
where
you
can
see
that
there
was
a
new
directory
detected
so
detected
new
directory
and
that
that's
an
issue.
So
that's
something
that
I
would
have
to
examine
so
error
file
below
a
known
directory
opening
for
writing.
B
So
you
can
see
that
there's
issues
with
all
these
new
directories
that
are
that
are
being
created.
So
I
would
have
to
add
more
information.
Like
my
what
you
may
call
it.
My
rules
are
not
configured
completely
properly
where
it's
showing
like
the
actual
file
and
everything
happening,
but
you
can
see
that
there
are
errors
being
detected
of
files
being
created
so.
B
So
detect
a
new
directory,
you
can
see
that
there's
been
lots
of
alerts
on
all
these
directories
created.
So
I
created
a
bunch
of
different
directories
and
now
they're
being
shown
as
detected.
So
you
can
see
that
the
rules
are
being
broken
within
this
instance.
I
don't
know
if
I
can
grab.
I
can
grab.
B
Let's
see
if
it'll
show
the
files
no
yeah,
so
it
won't
show
the
files.
I
would
have
to
add
more
to
the
actual
configuration
to
show
what
actual
files
are
being
created,
but
at
least
I
can
see
that
there's
some
tampering
being
done
on
the
system,
so
I
can
always
just
go
and
verify
that,
but
you
can
see
that
there
are
errors
that
are
applied
because
a
file
has
been
created
so
so
yeah.
B
B
B
B
Okay
yeah,
so
now
you
saw
like
that
they're
actually
being
triggered,
so
I
don't,
I,
you
saw
the
rule
actually
being
broken,
but
there's
no,
I
don't
have
any
alerts
set
up
right
now,
just
because
I
didn't
couldn't
get
it
to
work
on
slack,
but
I'll,
show
more
detail
kind
of
alerts
actually
being
sent
over
to
a
file.
That's
something
I
had
to
play
around
with
a
bit
more,
but
just
to
kind
of
give
you
an
example
on
what
alerts
are
going
to
look
like
in
the
future.
B
So
eventually,
this
is
where
we'd
like
to
see
the
alerts
right
now,
they're
only
there
for
container
network
security
and
anytime,
a
network
policy
is
broken,
you'll
see
the
alerts
on
here,
but
we
want
to
get
that
for
container
host
security
as
well.
That's
one
of
the
pieces
that
we're
trying
to
put
in
and
then
also
have,
statistics
for
for
the
container
host
security
as
well,
but
right
now
everything
is
just
within
container
network
security,
but
we
we
want
to
have
everything
for
our
container.
B
We
want
to
have
the
same
things
for
container
host
security
for
container
network
security
applied
here,
so
you
would
also
see
instead
of
just
seeing
network
policies.
We'd
also
want
to
see
actual
rules
here
and
have
you
know
definition
between
everything
and
have
it
done
in
the
ui.
So
you
don't
have
to
go
back
and
forth
between
the
yammels
and
the
gui.
B
B
B
What
what
I've
done
here
is.
I
put
it
in
just
view
mode
where
I'm
just
making
sure
that
that
we're
just
alerting
on
different
things.
So
then
we
can
go
ahead
and
take
these
steps
and
further
the
security
of
our
items.
So
a
lot
of
times.
What's
what
you
know,
different
security
teams
would
do,
is
they'd
actually
run
it
and
see
what
the
common
things
that
happened
are
and
then
from
there
and
force
more
policies
to
actually
stop
things
from
happening
to
actually
block
things.
B
So
I
know
how
to
do
this
in
container
network
security,
I
know
how
to
write
network
policies
which
block
and
within
the
web,
application
firewall
now
with
falco.
I
have
to
look
more
into
details.
I
know
that
is
something
that
it
does
support,
but
I'd
have
to.
You
know,
have
to
get
back
to
you
on
that.
C
Yeah
thanks,
I
I
was
writing
the
the
question
yeah
the
idea
it
was
the
same
from
from
a
firework
perspective.
You
start
logging
what
is
happening
and
then
you
define
your
final
set
of
policy.
There
is
a
specific
moment
where
you
are
going
in
production
that
you
want
to
prevent
those
kind
of
factions
that
just
receiving
an
alert.
So
I
I
want
you
to
investigate
if
we
have,
if
we
know
something
about
that
stage,
but
thanks
for
the
for
the
demo
and
the
answer.
B
Yeah
we
we
had
it
for
the
waff
which
we've
deprecated,
which
was
based
off
of
modsec,
so
I
mean
it's
a
good
point
to
have
something.
You
know
something
alternative
to
that
to
be
able
to
block.
I
think
right
now,
most
customers
won't
want
to
block
they'll
just
want
to
monitor
and
then
kind
of
enforce,
more
strict
security
policies
after
after
their
findings.
So
so
I
think
for
right
now.
This
is
something
this
is
something
definitely
viable,
but
I'll
keep
working
with
y'all.
C
D
D
Sure
man,
quick
question
competition,
you
know:
do
our
competitors
offer
stuff
as
far
as
this
goes
are
folks,
usually
using
just
the
you
know,
a
free,
open
source
version
of
of
of
container
and
post
security.
Do
we
know
of
anything?
That's
you
know,
bundled
with
anything
else
that
we
can
compete
against.
There's
there's.
B
Different
things,
honest,
there's
different,
a
lot
of
different
companies
that
actually
compete.
What's
the
name
that
that
actually
put
different
tools
on
kubernetes
to
monitor
so
systig
is,
are
the
producers
of
falco,
so
that's
one
of
their?
They.
They
offer
more
solutions
around
that,
and
then
there
is
what
what's
that
observability.
B
I
can't
man,
I
can't
remember
the
name
of
that
company.
No,
a
new
relic,
so
new
relic
also
has
features
like
that
which
can
observe
everything
going
on.
It's
pretty
much
a
lot
of
companies
that
log
different
things
and
then
perform
events
depending
on
what's
found
in
the
log.
So
like
there's
another
one
called
log
log
dna
there's,
so
it's
a
bunch,
there's
a
bunch
of
different
tools.
Now
they
all,
they
mainly
offer
logging
solutions
and
like
debugging
type
stuff
and
searching
through
logs.
B
So
it
would
be
mainly
those
companies
because
you
can
alert
based
off
of
what's
found
in
the
logs,
so
they
don't
offer
something.
Some
complete
solution
like
gitlab.
They
just
they'll,
mainly
focus
on
that
one
part:
okay
and
yeah
splunk
as
well
table.
Just
put
that
so
splunk.
Does
this
as
well?
There's
there's
a
lot
of
competitors
that
we
have
that
do
this
okay
appreciate
it.
B
Now
we
do
have
to
modernize
them
a
little
bit
before
we
release
them
because
of
the
changes
within
the
gitlab
managed,
apps
and
different
things
like
that,
but
we
will
provide
different
workshops
and
different
tools
so
that
way,
customers
can
go
step
by
step
and
learn
how
to
use
these
tools
or
or
anyone
within
gitlab
that
wants
to
learn.
So
those
are
a
few
of
a
few
of
the
things
that
that
we're
working
on
and
just
having
applications
that
anyone
can
use.
B
A
B
So
yes,
no
more
questions,
then
you
know
thank
you
all
for
attending
and
you
can
always
reach
out
to
me
on
slack
or
reach
out
in
the
tech
marketing
channel.
If
you
need
any
more
information
and
then
I'm
going
to
try
to
do
a
migration
video
on
migrating
from
get
lab,
managed
apps
to
this
new
project
management
cluster
and
if
I
can
get
some
slack
access
I'll,
happily,
post
the
video
on
you
know
sending
these
alerts
and
stuff.
