►
A
Last
week
we
have
been
learning
about
caverno
and
policies
and
all
the
the
interesting
metrics
stuff,
and
for
this
week
we
said
well,
we
want
to
continue
finishing
up
open
id
and
look
a
bit
into
kiosk,
whatever
that
may
be,
but
I'm
handing
over
to
nicholas
sharing
the
latest
and
greatest.
Please
please
go
ahead.
Yeah.
B
B
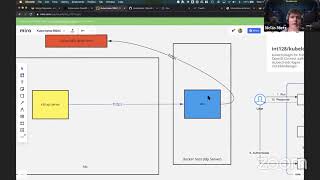
So
I
think,
two
weeks
ago
or
two
coffees
ago
we
talked
a
little
bit
about
authentication
and
authorization
in
juveniles
and
afterwards
philip
gave
an
awesome
introduction
about
more
security
to
the
authorization
part
and
also
showing
a
little
bit
about
giviano,
but
right
now,
what
we
want
to
do
again
is
to
fix
our
problem
from
last
time
with
the
open
id.
So
what
we
want
going
to
use
is
we
want
to
instruct
our
juveniles
cluster.
B
We
want
to
instruct
our
api
server,
so
it's
we
played,
as
I
can
fix
it
right
now.
It
should
be
ps3s,
so
we
want
to
instruct
our
api
server
that
he
will
call
to
gitlab
as
identity
provider
and
for
that
we're
using
a
proxy
that
is
for
dates
and
when
we
are
looking
into
dates.
It's
like.
Probably,
you
ask:
why
do
we
need
this?
It's
a
little
bit
easier
to
set
up
and
the
other
benefit
of
integrating
dates
instead
of
instead
of
directly.
B
B
So
that
means
that
we
could
use
stakes
a
single
instance
for
identities
and
he
can
can
connect
in
peril
to
github
gitlab,
probably
google
and
all
the
other
stuff
right
around
or
probably
also
to
your
own
custom
integrations
it's
also
possible.
So
for
that,
because
it's
mostly
what
I
used
in
my
own
career
was
mostly
dex
to
do
the
authentication
part.
B
B
B
B
B
And
auto
kubernetes
or
j3s
api
will
talk
to
the
dax
substance
and
we're
using,
of
course
https,
because
when
you
remember
on
the
last
row,
we
try
to
set
it
up
without
https
and
then
the
api
server
said:
okay,
it's
not
cruel
to
do
that
yeah.
So,
first
of
all,
let's
look
a
bit
a
little
bit
into
dex,
and
then
we
are
looking
back
into
our
final
stuff
on
ps3,
okay,
so
now
I
will
switch
it
to
the
terminal.
B
So,
instead
of
installing,
you
have
multiple
ways
to
install
that,
so
there's
a
binary
you
can
install
with
systemd,
you
can
install
it
with
into
anita's,
or
you
can
also
use
it
like
in
a
simple
way
that
I
try
to
use
this
mostly
that
I
insert
with
docker.
So
for
that
I
spin
up
on
this
instance.
A
dex
server
with
the
latest
version,
a
traffic.
The
traffic
will
take
place
for
for
doing
all
the
routing
and
vts
termination
and
yeah.
B
B
First,
we
having
the
image,
then
we
configure
in
here
we
also
set
so
that
we
are
sitting
here
via
commands
that
we
want
to
use
this
configurable
our
custom
and
probably
mounting
out
the
configs,
and
the
data
yeah
mostly
what's
interesting
on
traffic
is
that
we
are
using
labels
for
documenting
all
our
proxy
configuration.
That
means
that
we
say
here,
traffic
is
enabled
and
that
we
determine
which
host
we
want
to
use
and
which
endpoint
and
probably
which
dns
challenge
and
so
on
yeah.
So
for
a
better
overview.
B
What
does
it
mean?
We
can
go
back,
I
hope
so
yeah
cool
this
is
the
web
ui
of
traffic.
So,
first
of
all,
you
can
see
that
we
have.
We
have
three
concepts
in
terms
of
that.
We
have
router
and
services.
We
are
http
based
so
that
we
can
check
which
current
applications
are
currently
running
here,
and
you
can
see
that
we
have
in
redex,
http
router
goes
to
the
dex
servers
and
our
deck
servers
our
final
container
at
the
end.
B
B
It
would
say
patient
found,
but
if
you
want
to
check
if
that
is
working
correctly,
as
as
your
assumption,
there's
a
properly
well-known
path
so
well
known
of
my
deconfiguration,
this
comes
from
the
standard
of
open
id,
so
open,
ids
or
authentication
protocol
that
we
are
going
to
use,
and
this
is
the
reason
why
you
can
check
how
the
configuration
for
that
endpoint
is
made
yeah.
That
would
be
also
later
needed
for
configuring.
B
So
now,
let's
look
back
into
the
instance
and
let's
check
a
little
bit
on
the
config
yemen
of
texas
so
index,
we
have
multiple
options,
so
you
can
have
multiple
search
backends
because
we're
having
not
so
many
high
traffic
and
we
don't
need
to
manage
one
thousand
millions
of
users.
So
I
decided
I
can
go
with
her
in
with
a
simple
sqlite
database
and
search
on
the
file
system.
It's
fine
mostly
for
our
stuff.
B
So
afterwards
we
can
configure
here
the
http
configuration
it's
mostly
like
that
we
can
configure
it.
You
can
also
directly
terminate
ssl
on
on
dates,
but
my
way
is
to
decide
to
do
that
on
traffic
yeah,
mostly.
What
what
you
probably
like
to
know,
or
what
you
want
to
use
is
that
you
want
to
know
which
is
visual.
The
issuer
is
the
incident
that
currently
gives
ours,
the
authentication
information
from
us.
So
that's
the
main
reason
why
you
can
also
see
here.
B
The
issue
is
the
same
value
that
we
defined
in
the
configuration.
So
it's
like
the
endpoint,
and
these
are
the
standard
endpoints
that
will
be
used
for
x.
So,
mostly
beside
all
that
we
have
here,
we
the
times
how
long
the
tokens
are
valid
and
when
they
expired
afterwards,
we
can
defile
d5
off
to
configuration
because
open
id
stacks
up
on
off
two
protocols,
so
it's
more
a
sim
layer
on
it
and
it's
a
smaller
protocol
instead
of
the
io
of
two.
B
That's
the
reason
for
thought
so
mostly
now
coming
to
the
interesting
point
so
right
now.
What
we
now
configure
right
here
is
index
is
the
gitlab
instance,
so
that
means
we
can
say.
Okay,
our
idp
goes
to
github.com.
So
that
means
when
we
are
looking
back
into
the
into
the
api
server.
So
that
means
states
knows
that
he
needs
to
connect
to
the
clip
idp
and
just
in
terms
of
this
hitler.com.
B
So
probably
you
can
also
specify
your
own
databases.
It's
fine
mostly.
For
that
reason,
when
we're
looking
back,
we
have
here
client,
secret
and
client
id
pro
you're
asking
from
what
does
it
come
from,
and
that's
the
most
important
step
that
you
need
to
do
on
gitlab
site
when
we
are
looking
onto
gitlab
and
now
I
need
to
move
my
window
a
little
bit.
B
B
Okay,
cool
what
yeah
cool
yeah
and
when
you
want
to
configure
this
stuff
is
like
when
we
want
to
create
a
new
dex
instance,
which
would
be
like
dex
testing,
and
then
we
need
to
have
a
valid
redirection.
So
that
means
like
when
the
flow
comes
into
that.
So
when
we
are
looking
a
little
bit
back
into
the
document.
B
B
And
then
probate
that
that's
not
that
was
triggered
mostly.
We
need
to
configure
configure.
That
means
that
that
the
secret
will
be
also
checked
to
the
page
when
you're
using
center
page
applications
on
or
off
it's
considered
that
you
use
non-confidential
credentials
that
you
should
disable
it,
because
the
secret
will
be
injected
into
the
client,
so
everyone
could
read
the
secret,
so
it
makes
no
sense
with
it.
B
It's
like
more
of
security
of
yeah,
so
the
most
important
steps
that
you
need
to
do
is
that
you
need
to
grant
two
scopes.
It's
first
of
all,
read
user,
so
that
we
get
all
the
information
of
our
users
that
want
to
log
in
and
also
that
we
are
able
to
give
permissions
based
on
my
id.
So
that
would
be
the
two
steps
that
I
needed
to
create
the
application
I
created
this
already.
So
when
you're
looking
this
into
the
final
stuff,
you
can
see
here
the
application
id
for
secret.
C
B
And
you
see
that
I
read
this
two
stuff,
so
when
we
are
looking
back
into
our
application,
you
can
see
the
client
id
is
totally
the
same,
so
it
starts
with
92
and
if
it
can't
see
through
this
here
with
three
seven
yeah.
So
that
means
what
does
happen
is
in
the
end,
so
that
gitlab,
our
dates
mostly,
will
connect
to.
B
B
We
can
use,
also
define
groups
so
which
groups
are
allowed
on
gitlab
to
log
in
later
or
can
get
a
valid
identification
token,
and
currently
only
users
from
everyone
can
contribute.
Group
are
allowed
to
do
that.
So
that
means
only
users
from
everyone
can
contribute,
can
probably
later
authenticate
against
your
cluster.
B
That's
really
cool
yeah
in
the
end.
What
we
did
then
afterwards.
We
need
to
configure
also
a
client
so
because
currently
our
api
server
will
talk
to
to
dates,
but
also
probably
when
you
remember
on
the
part,
we
will
use
the
ctl
and
the
tube
cto
will
talk
to
the
cube
api
server
and
that's
the
reason
why
we
need
to
to
define
a
client
how
cuba
city
electron
connect
to
that
slowly.
B
We
will
come
to
the
point
a
little
bit
later
and
deeper,
but
it's
only
for
your
mentioning
that
you
saw
that's
it,
so
that
was
the
configuration
of
decks
mostly
and
now
we
can
hopefully
spin
up
our
cluster
again
and
see
that
everything
is
working.
So
for
that
what
we
now
need
to
do
is
we
need
to
configure
first
of
all
the
api
server
and
then
afterwards
we
need
to
configure
our
chip
ctl
to
use
to
use
the
password.
B
B
I
will
check
first
of
all
of
all
instances:
okay
people.
So
when
we
are
remember
bait,
we
did
ansible,
so
I
said
also
instability
locally.
I
spent
up
new
fresh
machines
that
max
provided
last
time.
I
used
the
same
book.
I
want
only
to
check.
First
of
all,
if
the
instance
is
available-
and
you
can
see
the
instance
available-
and
probably
I
figured
out
it
back-
hopefully
or
not-
hopefully,
but
sadly
that
I
see
that
you
can
also
see
that
across.
But
it's
another
problem
that
we
need
to
figure
out.
B
B
B
Now
we
will
wait
a
little
bit
and
then
afterwards
we
should
have
the
server
configured
yeah.
So,
but
in
the
meantime,
would
you
do
something
else,
so
I
did
a
small
change.
You
can
also
see
already
my
pull
request
that
I
prepared
for
today,
and
that
means
now,
as
I
said,
we
need
to
configure
the
tube
api
server
to
speak
two
days
and
that's
now
we
will
look.
B
How
does
it
work
so,
as
you
remember,
probably
from
the
last
time
where
we
tried
to
configure
it,
I
set
it
up
multiple
arguments
in
it
and
for
that
reason
I
checked
the
ansible.
How
does
it
work
and
also
try
directly
include
it
included
into
this,
so
that
means
like
okay.
Now
the
api
server
knows
onto
which
stacks
instance.
He
needs
to
record
at
least
so.
That
means
we
have
three
items
that
we
need
to
look
at.
B
So,
first
of
all
the
issue:
l,
that
means
like
the
the
instance
that
we
have
for
dates
then,
probably
which
username
a
claim
we
use.
We
will
use
the
email,
as
username
probably
later,
can
change
this
as
well
and
also
which
clients
or
clients
are
allowed
to
connect.
So
it's
more
like
the
cube,
client,
yeah
and
probably
also
where
we
get
the
group
information
from
and
also
if
someone
needs
to
be
prefixed
with
an
a
yeah.
B
C
A
A
B
A
A
B
B
So
currently,
opm
id
is
a
built-in
strategy.
So
that
means
that
you
don't
need
to
extend
it
and
open
id
connect.
It's
like
not
we're
talking
about
autod
the
right
term
would
be
open.
Id
connect
and
automatic
connect
is
a
standard,
so
you
can
probably
use
every
provider
that
supports
open
id
connect,
so
you
can
also
use,
for
example,
t
clock
as
authentication
provider.
There
are
a
lot
of
more
tongues
on
systems
that
supports
it.
B
B
You
can
also
use
static,
token
files
or
bootstrap
tokens
also
service
accounts,
but
that's
more
pain
off
of
managing
and
opening
these
phenomena,
standards
that
you
use
in
every
provider.
So
it's
like,
if
you're
going
to
manage
tubernator
services
like
ets,
arca
s,
although
each
has
elastic
q
and
interservice
azure,
turbinated
servers
and
dke
google
kubernetes
engine,
they
are
all
supporting
automatic
connect
out
of
the
box
and
you
can
connect
with
your
local
aws,
azure
or
google
account
to
that.
B
Another
option
that
is
also
really
cool
is
that
you
can
also
use
web
token
notification.
So
that
means
that
you
can
write
your
own
authentication
provider
on
that.
If
you
want
to
do
that,
but
mostly
I
wouldn't
recommend
to
do
that
at
all
use
a
standard
because
then
you
don't
have
problems
to
to
find
more
people
to
onboard
on
this
stuff,
and
probably
you
have
a
bigger
community
to
get
support
when
something
is
not
working
in
terms
of
re
instead
of
reinventing
the
whole
wheel
again.
B
C
B
A
B
C
B
A
B
B
A
B
B
B
C
B
B
Because
I
want
to
check,
if
you
can
you,
the
tube
ita
server,
doesn't
report
anything
if
everything
is
working,
so
it
means
like
when
the
dex
connection
works.
If
you
remember
the
last
time,
we
checked
the
other
locks
and
we
see
okay,
the
it
doesn't
work
at
all
and
so
on,
and
you
can
now
see
there's
currently
no
errors
in
there,
but
when
we
are
checking
the
systemd
file.
B
B
So,
as
you
remember
last
time
we
set
up
the
user
and
so
on,
and
for
that
we
need
also
to
configure
our
cheap
ctl
again
and
to
set
up
the
credentials
for
our
know
for
on
new
user.
I
might
just
it
would
be
my
name
and
also
what
we
need
for
that,
because
we
are
using
open
id
and
cube
cti
doesn't
support
open
id
directly
out
of
the
box
because
we
need
to
fetch
both
cube
ctl
on
the
token
and
so
on.
B
There
is
a
plugin,
a
plugin
that
stores
q
blog
in
where
it's
what
it
really
does.
It
does
for
us
the
whole
open
ide
flow,
so
it
means
like
he
will
open
locally
our
instance
to
gitlab,
and
we
can
log
in
and
then
we
are
authenticated,
get
authenticated
means
that
we
get
the
token
back
and
then
we
can
use
it
against
the
nodes
to
get
all
this
stuff.
B
Yeah
mostly,
I
would
say
we
would
start
on
first
with
executing
it,
and
then
I
explained
the
whole
dry
drum
flow
overflow
of
valerian
goes
and
so
on.
So
I
think
it's
more
clear
afterwards,
instead
of
explain
first
the
diagram.
So
for
that
reason
we
need
to
configure
our
cheap
ctl
to
use
our
credentials.
B
I
put
this
in
a
separate
command
line,
so
what
we
now
need
to
do
is
like,
as
you
remember
now,
we
need
to
set
up.
We
use
this
plugin.
I
installed
it
already.
It
was
installed
after
the
recommendation
of
the
of
the
developer,
so
that
means
when
you're
going
down
to
the
side,
I
only
installed
youtube
pin
inside
directory
via
homebrew.
I
use
truemostly
on
my
database.
So
this
was
the
reason
why
it
is
you
we
could
also
copy
all
the
commands
from
here.
B
B
B
We
didn't
configure
it
now
in
the
context
this
to
be
also
done
later,
but
that's
the
steps
that
we
only
did
so
mostly
here,
we've
seen
the
client
secret
from
dex
that
we
know
on
the
the
extra
crops
that
we
want
to
get.
I
probably
need
to
change
it,
okay
and
that
client
id
and
so
on,
and
probably
what
it
does
cube
ctl
now
do
what
it
really
does
is
hey.
B
B
That's
in
another
binary
path:
I
didn't
have
directly
my
plan
so
to
show
it
to
you.
Let
me
think:
okay,
it's
fine.
We
do
it
afterwards.
So
now,
for
example,
I
want
to
get
secrets
with
our
new
user
and
for
that
we
can
specify
in
the
tube
ctl
the
user
command,
and
this
will
use
lily
or
username
class.
B
B
Chipset
knows
only
we
want
to
connect
with
date,
access
of
my
deep
provider
and
also
with
your
api,
so
when
it's
only
with
tips
and
but
we
want
now
to
log
in
with
gitlab.
So
for
that
reason
we
can
now
clicking
on
logging
with
gitlab,
and
now
we
see
authenticated,
hey,
that's
true,
and
now
probably
what
you
can
now
see
here
is
when
I
now
try
to
get
the
secret
is
that
the
user
is
not
anymore.
It's
not
any
more.
The
standard,
cluster
admin
user.
I
don't
have
access
to
that.
B
B
This
is
the
part
that
we
currently
can
see
here
and
now
it's
used
for
username
you're
asking
why
it's
not
the
username
so
why
it's
not
solid
now
or
why
it's
not
niklas,
and
this
comes
from
because
we
are
questioning
a
different
stroke.
So
currently
we
are
cresting
on
the
s
username
using
the
email.
So
it's
like
okay
up
my
dinos
on.
Is
it
really
using
the
email
right
now?
So
that's
the
reason
why
our
username
is
odc
dash
highest
solid..
B
So
actually
now
everyone
who
has
the
config
can
connect
to
this
cluster
and
use
this
command
to
log
in
and
who
is
in
very
own
contribute
group
is
automatically
so
the
next
step
would
be
now
to
give
access
again
so,
for
example,
doing
some
airbag
stuff
so
that
we,
this
user,
says
a
robot.
So
probably
we
can
do
this
fastly.
B
B
C
B
B
B
B
B
A
A
B
A
B
B
Let
me
check
where
it
was
yeah.
You
can
see.
Okay,
as
you
see
as
we
configured
this
stuff,
so
nothing
happens.
So
a
browser
doesn't
open.
It
was
like
okay,
it
doesn't,
we
will
see,
how
does
it
work
and
what
really
happened
was
that
when
we
are
executing
the
first
command
so,
for
example,
cube
ctrl
get
secret
and
when
we
are
looking
back
into
this,
what
does
it
flows
is
that
first
chip,
cta
triggers
no
tube
login
and
q
plugin
opens
a
browser
directly.
B
B
B
Now
we
authenticate
against
dates
and
for
that
we're
using
our
little
prevention.
So
it's
like
that.
We
get
this
so
afterwards,
we
have
authenticated
successfully
on
dates
with
our
gitlab
idp
token
will
be
responded
to
to
the
local
client
to
queue
login,
and
then
we
are
starting
in
the
process
of
the
qp
ctl
gates
for
token,
with
the
final
request
and
the
tube
api
server
only
controls,
if
a
token
is
valid
mostly
it
doesn't
do
any
like.
B
If
I
have
directly
permissions
on
the
topic
or
something
like
that,
it
does
only
checks
if
it's
valid
and
how
does
it
work
so
it's
valid
the
whole
token.
How
does
it
look
like
they
use
a
standard
destroyed,
jpt
or
judge
mostly
in
base,
and
now
we
need
so
much,
let's
check
if
we
can
find
something
about
this,
because
I'm
also
curious
about
how
does
it
work.
B
B
Okay,
now
I'm
more
lazy,
because
I
don't
have
strings
in
it.
Yeah
and
I
don't
know
copy
paste
it
that
I
don't
need
to
do
that
and
now,
when
we
are
looking
into
this
token,
you
can
because
it's
a
job
code.
You
can
see
all
the
information
so
what's
currently
in
there,
so
you
can
see
okay,
whose
issue
it's
like
our
dex
instance,
which
client
was
used
with
lottery
inclines.
It
was
really
declared
before
which
email
we
used
is
like
a
high
assault.
B
B
B
A
B
Yeah
and
as
you
see,
for
example
now
when
we
are
using
instead
of
only
the
username,
we
can
also
define
a
group.
So
it's
like
probably
when
we
would
say:
okay,
someone
from
only
the
other
users
from
everyone
can
contribute.
Two
are
allowed
to
do
that
and
we're
checking
the
permissions
again.
It
says:
hey,
it
doesn't
work.
B
Why?
Because
when
we
are
looking
in
our
token,
is
only
everyone
can
contribute
or
not,
and
that's
how
you
can
now
define
all
the
processes
on
giving
a
cluster
access
to
everyone.
You
have
also
the
option
index
to
allow
every
group,
but,
for
example,
if
you
want
to
fill
it
like
because
we're
using
a
public
instance
of
gitlab,
so
it's
not
our
internal.
Everyone
can
contribute.
B
There's
a
good
documentation
about
that
on
vegeta
documentation
which
information
are
shared
and
which
information
you
can
get
at
least
so
I'm
really
try.
I
currently
I
didn't
figure
it
out
how
to
do
that,
but
I'm
really
interested
to
get
the
nickname
also
so
that
we
can
have
only
digital
username
in
the
cluster
instead
of
using
our
email
addresses,
because
sometimes
people
could
have
multiple
email
addresses
in
one
micron.
B
No,
it
depends
on
the
system
a
little
bit
if
you
have
unique,
usernames
or
unique
email
addresses
yeah,
but
there
could
be
another
story
like
I
can
report
at
least
or
write
in
your
post.
How
to
do
that
and
yeah.
That's
it
mostly
about
all
the
almighty
stuff
right
now
now
we
are
a
little
bit.
I
thought
I
would
be
a
little
bit
faster.
A
You
can
continue.
I
was
just
thinking
about
shot
or
jwt,
because
this
was
part
of
the
aws
user
group.
Last
week
on
monday
I
attended,
and
there
is
a
feature
request
for
adding
more
jot
attributes
somewhere.
This
is
not
directly
related,
but
what
you
did
now,
but
it's
interesting
to
debug,
to
to
decode
it
and
and
also
use
the
attributes
for
granting
access
to
specific
resource
system.
B
B
Probably,
as
I
mentioned,
if
you're
looking
into
the
newer
cluster
setups,
for
example,
of
eks
there's
also
now
the
possibility
to
do
this
with
also
with
dot
tokens
so
and
they
use
the
same
concept.
So
it's
like,
because
you're
using
open
id
and
tubernators
has
an
of
my
identity
provider
that
and
then
you
can
practice.
That's
really
true.
So
it's
like
that.
You
have
no
multiple
options
to
do
the
authentication
part
and
you
need
only
to
speak
one
protocol
and
not
hey,
I'm
currently
the
provider
apes.
B
B
A
B
A
B
What
we
now
want
to
do
now
we
have
users
in
our
system.
Now
we
want,
probably
so
that
every
user
can
work
in
this
cluster
but
on
a
really
efficient
base.
So
that
means
in
the
end,
that
we
need
to
manage
our
users
so
that
they
have
limits
so
that
they
can't
use
all
resources
in
our
clusters
and
probably
want
also
to
see
how
many
resources
are
used
and
that's
mostly
based
on
a
multi-tenant
system,
so
that
multiple
users
and
then
have
their
own
shared
resources.
B
If
you
are
thinking
about
multi-ten
systems,
you
can
look
like
like
a
high
tower
or
something
like
that,
where
every
apartment
has
its
own
settings,
but
it's
like
one
system,
one
building
only
and
this
outer
and
cluster,
and
now
we
will
add
to
our
cluster
independent
departments
or
apartments,
at
least
where
we
create
all
the
resources.
So
it's
like
vm
code,
stuff,
the
robot
names.
B
Everything
will
be
then
done
right
here
slowly
and
we
will
integrate
this
so
that
we
have
a
full
cluster
overview,
our
full
cluster
user
and
role
management
out
of
the
world,
because
this
one
part
is
mostly
missing
on
a
lot
of
people.
People
mostly
intending
to
start
with
cluster
admin,
and
then
this
slide
in.
B
I
saw
in
a
lot
of
companies
that
that,
in
the
small
in
a
lot
of
companies,
they
have
only
one
account
and
everyone
uses
plus
admin
with
the
same
account
it's
like,
if
you
give
someone
access
via
ssh
with
a
root
account
and
everyone
uses
the
same
root
account,
so
it
makes
no
sense,
so
you
can't
auditing
it
and
this
hard
part
and
security
related
stuff.
So
what
we
did
today
now
is
like
yeah.
We
mastered.
Finally,
we
open
id
stuff.
B
A
B
He
should
save
me
before
yeah
that
we
have
at
least
the
base
service
that
we
need
to
work
on
our
cluster
platform,
because
it's
a
platform
and
you
want
to
develop
apps
on
it
and
we
don't
want
to
invent
every
time
the
wheel
on
setting
up
an
ingress
controller
or
setting
up
dns
or
setting
up
dns
certificates
and
also
user
management.
So
these
are
our
base
services
and
probably
we
want
to
deploy
them
all
at
once.
B
A
Yeah
and
I
think
when
we
come
to
the
point
where
we
want
to
either
add
it
to
ci,
cd
or
isc
or
in
or
githubs,
which
was
mentioned
earlier.
This
also
involves
adding,
for
example,
prometheus
or
a
different
sidecar
for
monitoring
into
the
cluster
and
yeah.
We
can
like
iterate
on
that
and
build
the
base
system
and
then
add
new
features
to
it,
but
without
reinventing
the
wheel,
as
you
said,
and
like
learning
yammer
all
the
time
just
going
ahead.
Yeah.
B
A
But,
to
be
honest,
the
roles
are
like
you
have:
they
are
not
really
like
split
up
in
a
specific
sense.
It
just
made
sense
who
is
a
regular,
attendee
or
regular
member
getting
maintained
access?
The
founders
got
all
x's
and,
and
everyone
else
gets
developer
access
we
could
play
around
with
that
it
would.
It
would
be
interesting
for
us
to
learn
if
we
can
do
that.
Yeah.
A
So
this
is
basically
I
don't
know
how
far
we
we
get
there,
but
like
we're
going
with
kubernetes,
and
we
are
now
adding
so
everything
which
is
needed
touching
base
with
monitoring
and
observability
at
some
point,
and
I'm
also
in
touch
with
alex
jones
about
other
devops
and
kubernetes
and
observability
as
well.
So
we
can
continue
the
journey
and
like
make
2021
like
the.
We
learn
kubernetes
together
a
year,
basically
yeah
and
try
to
build
something
which
others
can
use
and
others
can
also
try
out
by
using
printer
production.
A
B
I
mean
playbook
on
documentation
parts,
it's
like
not
creating
ends
of
this
stuff.
It's
like
hey,
a
playbook
is
like
okay,
a
documentation
where
you
seriously
oversteps
and
what
goes
what
goes
up
and
down
mostly,
we
run
it
or
you
know
internal
company
for
engineers,
so
that
everyone
knows
how
the
stuff
is
working.
A
Let's
just
wrap
it
up
and
say
thanks
for
watching
everyone
we're
looking
forward
to
meeting
you
next
week
same
time
same
date
like
9am,
pt
or
6pm
central.
Was
it
not?
No,
it's
not
9am
pt,
it's!
Actually.
It's
10
am
pst
because
in
the
us
there
is
data
saving
and
for
us
at
6
pm
in
our
time
zone
in
central
europe
time.
