►
From YouTube: High-level workflow of coverage guided fuzz testing
Description
Fuzzing documentation: https://docs.gitlab.com/ee/user/application_security/coverage_fuzzing/#coverage-guided-fuzz-testing-ultimate
Fuzz testing direction page: https://about.gitlab.com/direction/secure/fuzz-testing/fuzz-testing/
A
Hi
there
I'm
sam
kerr,
I'm
a
principal
product
manager
here
at
gitlab,
and
today
I
want
to
talk
to
you
about
coverage,
guided
fuzz
testing
and
what
the
high
level
workflow
of
using
coverage
guided.
Fuzz
testing
is
like
so
that
you
can
find
bugs
and
security
vulnerabilities
in
your
programs
and
apps
that
traditional
qa
processes
might
miss.
So,
let's
dive
right
in
so
coverage
guide,
fuzz
testing
always
is
going
to
start
with
your
application.
A
A
An
important
part
of
any
application
is
testing
it
to
make
sure
that
all
these
functions
in
the
app
work,
as
expected
make
sure
that
they
don't
have
any
edge
cases
that
cause
behavior,
that
a
user
wouldn't
expect
or
that
could
potentially
harm
you
or
your
business.
So
we're
looking
at
an
application
right
now
that
has
three
functions.
Let's
take
a
look
at
one
of
these
and
see
how
we
would
use
coverage
guide,
fuzz
testing
to
look
into
it.
A
A
A
Maybe
you
would
use
these
for
copying
into
a
presentation
for
sending
it
to
emails
or
for
archival
purposes.
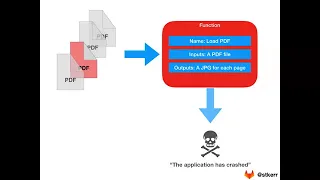
So
if
you
want
to
look
at
this
function
and
model
it
visually,
this
is
what
it
might
look
like.
It's
taking
a
pdf
on
the
top
left.
It
processes
it
in
the
body
of
the
function
and
then
it
outputs
a
number
of
jpeg
files
at
the
bottom,
and
this
is
the
normal
way
that
this
function
would
work.
A
So
one
very
important
thing
to
note
here,
though,
is
that,
because
this
loading
pdf
function
is
something
your
end
users
could
use.
This
is
a
great
place
that
bugs
could
be
lurking
in
your
program
that
you
would
want
to
find.
This
is
why
it's
a
great
candidate
for
fuzz
testing,
because
any
function
that
a
user
can
interact
with
directly
means
that
not
only
could
errors
happen
in
the
function
from
malformed
inputs,
but
it's
also
the
place
that
attackers
are
going
to
start
looking
at
your
applications
as
well
trying
to
find
those
security
vulnerabilities.
A
A
It
will
continue
to
generate
random
pdf
documents
to
try
and
exercise
the
load
pdf
function
until
eventually
one
of
them
produces
a
crash.
As
soon
as
the
application
crashes,
the
fuzz
tester
immediately
stops
and
realizes
that
hey,
I
found
an
edge
case
here,
that's
not
being
properly
handled.
This
is
most
likely
a
bug
or
a
security
vulnerability
as
soon
as
that
happens,
the
fuzz
tester
reports
that
hey
this
is
the
specific
pdf
document
that
caused
an
issue.
A
A
So
now
that
we
have
that
pdf
document,
a
developer
or
an
engineer
would
take
that
they
would
create
a
test
harness
which
has
most
likely
already
been
created
for
this
pdf
function,
and
they
know
that
there's
a
bug
in
there
somewhere,
because
the
application
has
crashed.
This
is
not
normal
behavior
that
should
be
happening.
So
the
developer
can
then
take
a
debugger.
They
can
have
print
statements.
A
So
then,
as
we
zoom
back
out,
this
function
has
now
been
tested
by
fuzz
testing.
You
know
that
is
working
better
because
that
bug
doesn't
exist
and
you
can
continue
this
process
looking
at
every
single
function,
every
piece
of
logic
in
your
application,
with
fuzz
testing
to
find
any
of
those
bugs
that
might
be
lurking,
and
this
was
a
very
high
level,
quick
walkthrough
of
what
coverage
guided,
fuzz
testing
is
like
and
how
you
might
use
it
in
your
own
development
processes.
A
A
You
can
also
look
at
the
get
gitlab
fuzz
testing
direction
page
at
gitlab.
One
of
our
core
values
is
transparency,
and
so
our
direction
page
is
a
great
way
to
understand
how
we're
thinking
about
fuzz
testing,
what
sort
of
problems
we
want
to
solve
with
it,
what
type
of
use
cases
and
industries
we
want
to
target
with
our
fuzz
testing
offerings,
as
well
as
our
short
term
and
longer
term
roadmaps
about
where
we're
going
and
where
we
plan
to
be
in
the
future.
A
And
finally,
everything
at
gitlab
is
public.
Again
we
work
asynchronously
and
definitely
feel
free.
If
you
want
to
create
an
issue
and
talk
directly
with
us,
I
said
before
my
name
is
sam
kerr.
You
can
see
my
handle
for
gitlab
at
the
bottom
right
of
the
slide,
I'm
st
kerr.
I
would
love
to
talk
to
you
more
about
fuzz
testing,
any
of
the
problems
you're
having
with
your
traditional
qa
processes
and
really
just
help
you
get
using
gitlab
and
finding
more
value
in
fuzz
testing
with
that.
Thank
you
so
much
for
your
time
really
appreciate.
