►
From YouTube: DevSecOps & GitLab's Security Solutions
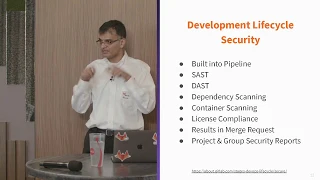
Description
In this talk during a GitLab Connect DC event, Solutions Architect Sameer Kamani covers DevSecOps and offers a look at GitLab's security features.
Read more about our product vision: http://bit.ly/2IyXDOX
Learn about FOSS & GitLab: http://bit.ly/2KegFjx
Get in touch with Sales: http://bit.ly/2IygR7z
A
B
Am
a
solution
architect,
as
I
mentioned,
I
support
a
portion
of
the
civilian
team.
My
background
is
software
engineering,
so
I
was
a
developer
propellerhead
for
many
many
years
and
I
came
through
the
ranks
of
doing
waterfall
many
many
years
ago
and
I
remember
distinctly
about
four
years
back
when
a
project
manager
sat
me
down
and
said.
Oh,
this
is
great.
We've
got
this
wonderful
project
plan
where
you've
got
your
development,
your
tests,
your
production
stuff,
and
it's
all
waterfall,
it's
awesome,
but
we
need
to
crash
it
and
I
said.
B
Excuse
me
crash
what
what
do
you
mean
crashing
and
he
goes.
Can
you
do
this
in
this
much
time
and
I
just
looked
at
him
like?
No,
how
do
you
do
that
and
he
goes
well.
That's
your
job
you're,
the
creative
guy
in
the
room.
You
figure
that
out
so
I
still
remember.
It.
I
still
talk
to
him.
Once
in
a
while
and
I
tell
him.
B
I've
got
an
answer
now,
except
I'm
about
three
years
for
four
years
late,
but
anyway,
so
I
have
ten
years
of
experience
in
government
sector,
lots
of
federal
state,
local
development,
stuff,
you
name
it
all
kinds
of
compliance
frameworks
and
checks,
and
you
know
the
mist
853
is
kind
of,
like
you
know,
stamped
into
my
brain,
pretty
well
so
that
sort
of
stuff
and
then
to
add
to
that
I
did
about
three
years
worth
of
work
in
cyber
security
and
boy.
That's
not
dog
years!
B
That's
like
dog
years
times,
dog
years
type
of
work
right,
so
you
learn
just
so
much
just
by
being
in
the
cyber
security
industry.
So
that's
sort
of
the
background
and
what
I'll
be
talking
about
is
security
in
DevOps
right.
That's,
a
big
hot
topic!
These
days,
I'll
get
into
the
details
about
that
and
then
I'll
talk
about
how
gitlab
is
approaching
that
there
are
many
approaches.
B
There
are
many
ways
to
slice
it
and
dice
it
get
like
is
in
a
unique
position
in
being
able
to
do
that
in
a
very
effective
way,
and
that's
what
I'm
gonna
be
talking
about.
Hopefully,
we'll
have
enough
time
for
Q&A.
I
do
tend
to
talk
a
lot,
so
I
might
go
a
little
bit
over,
but
I
apologize
for
that.
If
that
happens
all
right.
So
first
tell
me
about
you.
How
many
of
you
know
def
def,
sec.
Ops
is
right.
B
So
all
right,
some
of
you
might
have
already
run
me
out
of
the
room
and
said
def
Chekhov's,
that's
not
a
thing.
Devops
is
a
thing
and
SEC
is
just
everywhere.
Well
yeah,
but
sometimes
you
gotta
spell
it
out,
especially
for
those
pointy-haired
bosses
who
don't
get
that
right.
So
so,
how
many
of
you
do
dev
sac,
ops,
alright,
you're,
the
winner
cool.
B
As
you
can
see,
it's
not
very
prevalent.
How
are
you
performing
application
security
and
in
your
process?
Is
it
happening
during
the
development
lifecycle?
Or
is
it
this
wonderful
jet
engine?
That's
just
flying
through
your
developers
are
just
churning
out
code
and
screeching.
Halt
security
raises
up
their
hands.
Goes
you
got
stuff
in
your
code.
You
got
to
go
fix
now
your
projects
like
five
years
behind,
because
you
can't
get
it
out
right
so
that
that
happens
a
lot
and
then
predominantly
you
know
what
tools
are
using.
B
B
Alright,
so
we
did
a
survey
very
recently.
Good
lab
did
one.
The
survey
results
are
posted
on
our
website.
You
can
see
it
basically
what-
and
this
is
a
global
survey
right.
So
this
is
all
across
the
world
federal
isn't
terribly
far
behind,
but
they're
they're
catching
up.
So
some
of
these
numbers
don't
exactly
apply
to
federal,
but
they're
they're.
Getting
there.
What
was
found
was
that
DevOps
is
being
adopted
very
quickly.
B
People
feel
like
they're,
getting
a
lot
of
visibility.
By
doing
the
DevOps
model,
they
are
able
to
deliver
applications
faster.
They
are
able
to
deliver
more
and
more
faster,
so
continuous
deployment
is
becoming
real.
So
there
used
to
be
a
time
when
all
this
stuff
would
be
developed
very
quickly
and
then
it
would
go
and
sit
in
somebody's
desk
for
some
approvals
and
then
there
would
have
to
be
documentation
upon
documentation
needed
to
be
written
so
that
a
deployment
team
can
deploy
the
thing.
That's
all
churning
out
right.
B
So
now,
that's
all
coming
out
real
quick
about
45
percent
of
the
respondents
said
that
they're
doing
it
at
least
somewhere
in
the
organization.
So
that's
good
and
generally
that's
tied
to
the
mobile
side
of
the
world
right,
because
mobile
tools
tend
to
be
more
around
the
DevOps
model.
Security
is
still
a
problem
about
50%
of
the
respondents
said
well
guess
what
yeah
we're
developing
quickly
but
Security's
coming
up
and
biting
us
in
the
back
end
after
we've
actually
done
more
development.
B
So
that's
a
problem
and
then
what
that
leads
to
is
that
developers
have
forgotten
what
they're
doing
there's
context
switching
they
have
to
fight
with
security
to
talk
about.
Why
did
you
write
this
piece
of
code
because
it's
all
history?
It's
all
forgotten
security
is
not
even
aware
of
why
this
was
written.
They
just
care
about.
Well,
it's
broken.
Well,
there's
some
vulnerability
in
there.
You
got
to
fix
it.
It's
a
it's
a
it's
a
lot
of
work
and
talk
remote
work.
B
Obviously
it
supports
efficiency,
so
people
who
do
a
lot
of
remote
work
take
that
to
your
management
team
because
they,
you
know
they
need
to
implement
this
more
and
more
frequently
to
do
remote
work
and
then
testing
is
hard
which
we
all
know.
It's
still
hard.
It's
going
to
continue
to
be
hard
because
of
the
way
that
testing
is
carried
out
and
there
are
many
solutions
out
there
for
it.
B
So
this
is
kind
of
the
security
landscape
right.
You
have
static
analysis
that
has
to
be
done
and
a
lot
of
people
do
light
analysis
and
their
integrated
development
environments,
which
isn't
generally
very
security,
focus
it's
more
quality
focused.
Then
it
gets
put
into
this
code
repository
where
suddenly,
these
bigger
tools
get
involved
and
they
do
the
security
and
the
bottom
is
kind
of
the
landscape.
As
you
see
today.
B
Is
you
get
all
these
different
tools
and
technologies
that
have
talked
to
each
other
and
each
security
report
is
in
a
separate
tool,
separate
silo
of
its
own,
so
think
about
it?
You
get
security
involved
earlier
in
development
cycle.
It's
still
not
easy
for
them
right.
So
for
every
one
developer,
how
many
security
people
are
generally
in
an
organization?
Think
about
that
concept
and
then
think
about
how
many
tools
they
have
to
deal
with
as
opposed
to
a
developer,
has
to
do
a
developer.
B
Just
has
to
do
their
development
work
right
so
generally,
they
are
one.
Maybe
two
maybe
three
tools:
security
has
to
think
about.
You
know
organizational
security.
They
have
to
think
about.
You
know,
network
security.
They
have
to
think
about
application
security.
They
have
to
think
about
monitoring.
They
have
to
think
about.
You
know
you
yeah
responsiveness,
I
mean
there's
a
lot
of
stuff
going
on
for
them
and
then
in
front
of
them.
Now
you
throw
four
or
five
different
tools
just
to
do
one
piece
of
security
and
they
go.
B
Oh,
my
gosh,
my
work
is
just
too
much
they're
overloaded
right
now,
zoom
out
a
little
bit
more
kind
of
to
my
point
about
how
many
tools
are
you
using?
This
is
what
the
current
infrastructure
looks
like.
You've
got
your
name
of
your
tool,
and
now
you
got
to
have
to
in
you
kind
of
have
to
have
versioning
of
the
tools
and
the
knowledge
about
which
tool
changing
what
version?
How
does
that
connect
to
this
other
thing?
What
does
that
plugin?
Look
like?
B
Oh
that's,
a
free
plugin
that
somebody
wrote
and
is
no
longer
supporting
how
do
I.
You
know
what
do
I
do
it's!
It's
madness
madness!
So
that's
where
I
get
lab
comes
in,
and,
and
many
of
you
who
are
using
it
lab-
probably
have
seen
a
lot
of
this
so
just
show
of
hands
how
many
of
you
use
get
labs
just
as
source
code
management
tool.
B
There
you
go
all
right,
there's
so
much
more
in
get
lab
that
you
could
be
using
it
for
right
source
code
management
is
just
one
piece
of
it,
but
the
biggest
benefit
is
even
if
you're,
just
using
git
lab
as
a
source
code
management.
The
fact
of
the
matter
is
that,
as
part
of
one
single
application
to
do
other
things,
while
you
know
some
people
may
say
well,
it
doesn't
compete
against
this
very
special
specialized
tool.
That
does
blah
blah
blah
for
me.
B
Well
yeah,
but
guess
what
it's
not
the
cost
of
the
tool
of
how
many
features
it
has
or
function
it
has.
How
much
is
it
costing
you
to
have
that
tool
in
your
environment
right?
That's
the
question
tool,
tax
I
think
it's
Forrester
I
think
had
that
terminology
so
tool
tax,
it's
it's
a
it's
a
it
costs
money.
It
costs
time!
Think
about.
If
that
money
is
freed
up
from
that
infrastructure
side
of
it,
that
could
be
used
for
your
project
to
do
other,
better
things.
B
So
that's
just
another
slide,
showing
you
a
little
bit
more
about
that.
Basically
we're
looking
where
our
vision
is
to
try
and
encompass
as
much
of
the
breadth
with
the
depth
and
provide
you
the
ability
to
do
more
and
more
just
from
one
application,
so
you're
not
switching
context,
you're
not
going
to
five
ten
different
places
to
do
this
right,
so
we're
embracing
security
in
a
big
way.
B
We
you've
probably
heard
about
the
zero
trust
approach
that
we
have
taken
for
gitlab
com
and
get
lab
as
an
organization.
You
probably
heard
about
the
security
tools
that
we
are
now
starting
to
embed
within
get
lab.
How
many
of
you
have
heard
about
that?
I
mean
you,
okay,
all
right
cool,
so
now,
you've
just
heard
it
from
me.
We
are
putting
security
tools
in
get
lab
as
one
single
application
approach
underneath
the
covers.
B
They
may
be
separate
tools
that
are
specialized
to
do
certain
things,
but
we
are
aggregating
stuff
and
we're
bringing
it
to
the
front
and
making
it
all
kind
of
work
together
seamlessly.
So
once
again
that
one
application
approach,
you
don't
have
to
go
looking
for
that
plug-in
and
that
plug-in
and
that
other
tchotchke
you
it's
all
baked
in
and
that's
what
we're
trying
to
do
so
I'll
get
into
the
deep
dive.
B
So
a
lot
of
you
who
are
not
aware
of
the
C
ICD
capabilities
of
get
lab
and
I'm
looking
at
those
people
who
raise
their
hands
just
using
it
lab
at
source
code
management.
There
is
much
more
to
get
lab
and
this
is
like
the
most
lovable
feature.
That's
in
get
lab
is
the
continuous
integration
continuous
delivery
model
that
we
offer.
So
how
does
that
work
right?
It
starts
out
with
creating
an
issue.
You
create
an
issue.
You
write
information
in
there.
B
You
provide
details
to
the
developer
of
what
you're
doing
some
people
put
user
stories.
Some
people
put
stream-of-consciousness.
It
could
be
anything
it
doesn't
matter,
then,
at
some
point,
the
developer
realizes
okay,
I'm
gonna
start
working
on
this
and
they
click
the
Create,
merge,
request
button
and
they
start
working
on
the
actual
problem.
Now
some
of
you
have
been
in
development
environment
know
this
about
when
it,
whenever
you're
developing
about
80%
of
the
time
is
in
deciding
and
designing
your
stuff
and
20%
of
the
time
is
in
turning
that
into
code.
B
That
actually
works
all
right.
So
once
you
get
that
once
you
get
that
through
that
process,
you've
got
your
CI
CD
pipeline
running
and
that
can
be
kicked
off
automatically
every
time
you
commit
the
code,
that's
hugely
beneficial
right.
So,
behind
the
scenes,
the
stuff
is
just
kind
of
churning
out
a
runnable
application,
so
you're
able
to
deploy.
You
know
it
deploys
it.
It
creates
a
review
application.
It
does
all
these
things
and,
in
addition
to
that,
it's
running
security
scans
right
at
that
moment,
ok
huge
benefit,
so
I
I
have
an
application.
B
That's
in
gitlab
great
I
changed
some
piece
of
code,
not
realizing
what
I
am
going
to
do
in
terms
of
the
security
aspects
of
it.
I'll
just
write
the
code
because
I
gotta
meet
a
requirement
and
I
gotta
meet
it
within
the
sprint
time
line
that
I
am
on
and
I've
got
other
priorities
but
running
it
through
the
pipeline.
B
Having
that
do
the
scan
automatically
and
providing
the
result
gives
me
that
comfort
that
I'm,
not
gonna,
suddenly
do
something
that's
wrong,
oh
by
the
way,
it
also
keeps
it
all
in
context
of
what
I'm
working
on
so
I
just
wrote.
Ten
pieces
of
ten
lines
of
code
I
that
I
went
home,
I
came
back
next
morning
and
I
see
the
pipe
line,
run
complete
and
there's
one
security
issue
that
shows
up
in
there
all
right,
I
know
what
I
was
working
on
last
night:
I
can
kind
of
continue
working
on
it's
not
like.
B
B
B
One
of
the
things
that
get
lab
does
is
when
the
pipeline
runs.
It
is
actually
able
to
deploy
the
application
to
a
live
running
environment
by
creating
a
review
app
for
you
and
then
that
makes
it
available
for
dynamic
scanning
to
run
as
well
and
provide
your
results
while
you're
running
the
well
you're
just
kind
of
writing
code.
B
It's
got
SAS,
static,
analysis
right,
so
source
code,
analysis,
dynamic
analysis,
dependency
scanning,
so
it
will
do--
look
through
your
dependencies
and
run
a
scan
on
it
and
provide
your
results
to
say:
hey,
there's
a
CVE
on
this
one
dependent
item
that
you
pulled
through
from
some
other
open
source
product
or
whatever
that
you've
downloaded
last
night.
Here's
the
patch
for
it
go
download
it.
So
you
it'll
give
you
the
CVE
link
to
it
container
scans
containerization
is
very
it's
like
baked
into
get
lab.
We
have
a
container
registry.
B
We
actually
can
run
a
container
scan
and
provide
your
results
of
that.
So
very
much
like.
What's
a
container
scan
product
that
people
use
their
twist
lock
twist
lock
very
much
like
twist.
Lock,
we
use
Claire
same
sort
of
stuff
and
it
does
that
license
compliance.
That's
a
key
point!
How
many
of
you
actually
use
open
source
libraries
in
your
code
bases
how
many
of
you
know
of
usage
of
open
source
libraries
in
your
codebase?
B
Let's
start
with
that
question:
license
compliance
can
do
that
right
and
it
will
also
tell
you
what
kind
of
open
source
license
that
library
is
under
and
whether
you
have
blacklisted
or
whitelist
of
that
at
an
organizational
level.
That's
important.
Some
organizations
cannot
digest
other
licensing
terms
of
an
open-source
product
because
those
terms
are
restrictive
in
some
way.
B
B
All
right
so
I'll
start
out
with
this
screen
here.
How
many
of
you
are
familiar
with
the
gate,
lab
user
interface?
How
many
of
you
work
with
it
like
once
in
a
year?
How
many
of
you
work
with
it
like
once
in
a
month
how
many
of
you
work
every
day,
all
right
cool?
So
so
many
of
you're
familiar
with
this.
So
this
is
not
news
to
you,
but
for
those
who
have
who
didn't
raise
your
arms?
B
Basically,
you
have
the
ability
to
create
group
structure,
so
you
so
we
can
group
things
in
a
structural
fashion,
think
of
like
folders
in
your
Windows
environment
or
whatever,
and
you
can
place
these
projects
or
repos
as
most
people
call
at
which
I
like
I,
don't
like
to
call
it
repos
it's
repo
is
a
component
of
the
project.
Project
is
much
more
encompassing
than
that,
but
you
can
have
many
of
those
projects
within
a
group.
So
I
have
a
group
here
called
Samir
come
on
yeah.
B
That's
me
and
then
I
have
a
spring
group,
and
these
are
all
my
spring
applications
and
then
I
have
a
ruby
group
for
my
ruby
applications
and
so
on
I
happen
to
name
them
that
you
could
name
them
by
your
divisions
or
your
organizational
whatever.
Whatever
you
want.
There
are
functions
now
when
I'm
in
my
group
view
I
have
a
security
dashboard
that
I
can
view,
so
I
can
click
on
that
and
right
there.
It
gives
me
a
chart.
B
This
I
mean
managers,
love
lines
and
pictures
right.
So
this
is
like
totally
up
their
alley.
It
shows
them
right
up
front
how
many
vulnerabilities,
how
many
criticals
hi
mediums
and
lows
there
are.
It
shows
you
how
the
developers
are
working
through
it.
So
it's
you
know.
Their
downward
trend
in
this
example
is
indicated
that
somebody
is
actually
fixing
some
things
and
then
down
below
is
a
list
of
those
vulnerabilities.
So
I
can
actually
look
at
what's
going
on
right
from
this
dashboard.
B
Not
only
do
I
get
the
nice
pretty
graph,
but
I
also
can
view
the
the
results
exactly
the
other
thing
I
can
do
is
I
can
sort
by
projects.
So
then
I
want
to
zero
in
on
okay,
which
project
is
actually
causing
many
of
these
vulnerabilities,
which
is
the
noisy
project
which
one
do
I,
need
the
development
team
to
go
to
training
right.
That's
a
huge
huge
point.
B
Second
one
is
by
report
type.
So
I
can
you
know
I
am
a
security
engineer
at
an
EDA
company,
let's
say
and
I
only
care
about
the
dynamic
scans,
because
that's
the
only
part
of
what
I'm
worrying
about
I
can
just
very
easily
just
filter
that
and
say:
ok,
what
did
the
dynamic
scan
results
show
or
if
I,
if
I'm
interested
in
the
dependency
scans,
then
it'll
show
me
that
and
so
on
so
forth,
so
I
can
do
the
slicing
and
dicing
right
from
here.
I
can
multi-select
so
I.
B
B
Applications
have
this
kind
of
layout
on
them
and
then
each
individual
line
is
a
project
line,
so
I
have
multiple
projects
under
there
and
it
shows
me
each
of
these
lines
and
how
they're
burning
through
the
vulnerabilities
all
right.
So
that's
that
then,
as
we
drill
into
a
project,
many
of
you
use
get
lab
are
probably
familiar
with
this.
If
you've
used
github
very
familiar
with
this
kind
of
user
interface,
where
it's
very
similar,
but
basically
you
see
your
project,
you
can
you
can
do
your
issues
right
here.
B
You
can
create
your
merger
quest
right
here.
You
can
create
your.
You
can
view
your
CI
CD
pipeline,
so
I'll
show
you
the
pipeline
in
a
minute,
but
some
of
you
are
not
familiar
with
git
lab.
What
you'll
see
is
I
am
NOT
context.
Switching
I,
don't
have
my
JIRA
console
over
here
and
my
Jenkins
console
over
here
and
my
IDE
over
here
and
any
of
that.
It's
all
right
in
one
browser
interface.
Yes,.
B
So
yes
yeah,
so
yeah
I'll,
repeat
that,
so
the
question
was
a
lot
of
the
features
that
that
I
talked
about
in
the
dashboard
area
are
very
similar
to
sonarqube,
and
the
question
is:
is
the
intent
to
be
become
the
competitive
product
against
owner
cube?
Is
the
intent
to
kind
of
do
what
they're
already
doing?
The
answer
is
a
little
bit
of
both
okay,
yes,
competitor
in
a
certain
sense,
we're
both
open
source
products.
B
We
both
like
open
source
stuff,
so
not
from
that
perspective,
but
from
a
perspective
of
providing
it
to
you
in
one
dashboard,
that's
the
key
one
application
right
now,
I
just
mentioned
JIRA
console
Jenkins
console.
You
probably
need
to
have
your
solar
cube
console.
You
probably
need
to
have
your
ID
now
you're
talking
more
and
more
things
being
added
into
your
environment.
If
you
are
using
sonar
cube
and
you
love
it,
you
love
the
aggregation,
features.
B
Wonderful,
you
can
take
the
results
out
of
get
lab
and
post
it
over
there
and
do
what
you
need
to
do
over
there.
That's
fine,
but
we
obviously
would
prefer
you
to
work
in
one
environment
because
it
just
makes
you
more
productive
in
that
sense.
Okay,
so
it's
not
so
much!
Oh
we're
gonna
take
sort
of
cube
out
of
it.
It's
so
much
as
sir
users
can
continue
using.
B
B
This
is
what
it
looks
like
in
terms
of
the
execution
of
it
right.
So
I
ran
a
pipeline
over
here.
That's
what
my
pipeline
looks
like
as
you
can
see
right
during
my
test
phase
I
ran
the
stass
test
and
I
ran
the
dependency
scan
and
so
and
so
forth.
So
all
of
those
tests
were
run
parallely
while
the
pipeline
is
being
executed.
Another
new
feature
that
we're
introducing
is
directed
acyclic
graphs,
DAGs,
which
are
which
kind
of
break
this
model
a
little
bit,
but
they
allow
you
to
kind
of
hop
across
to
so.
B
That's
a
different
topic
for
another
time,
but
it
shows
you
security
right
at
the
pipeline
run,
so
we
think
that
that's
important
to
expose
right
there.
It
shows
you
how
many
vulnerabilities
were
detected
again.
These
are
individual
tool
executions,
so
it
shows
you
for
each
type
of
test
that
I
ran
what
the
results
were,
but
then
we
actually
aggregate
those
results
into
our
in
a
merge
request
view.
So
some
of
you
have
seen
the
merge
requests.
You
probably
recognize
this
is.
This
is
where
everything's
happening.
You've
got
your
branch
over
there.
B
You've
got
your
code,
that's
been
written,
so
I
only
changed
a
bunch
of
lines
of
code,
but
what
it
did
was
it
actually
made
it.
So
we
found
the
modern
bodies
and
we
marked
which
ones
we're
the
same
and
which
ones
actually
got
fixed.
So
if
I
expand
this
view,
what
I'll
see
is
everything
with
a
red.
X
basically
is
stuff
that
did
not
get
fixed,
but
the
green
checkmark
cell
tells
me
what
I
did
actually
fix
so
from
a
security
management
perspective.
B
I
want
to
see
those
green
checkmarks,
so
I
can
I
can
say
yeah.
This
is
good
what
our
code
changes
you
made
that
looks.
Good
I
can
approve
this,
so
there's
there
can
be
an
approval,
Authority
and
a
chain
over
here
around.
You
know
this
merge
request
before
it
actually
gets
merged
into
your
code.
That's
another
key
point:
all
of
this
is
occurring
while
I'm
in
my
branch
running,
you
know
just
changing
my
code
in
my
little
branch,
my
work
area
and
before
I
merge.
B
B
Let's
see
so
there's
the
stats
asked
list.
There's
my
dependency
scanning
list,
there's
my
container
scanning
list
and
then
there's
my
DAST
list.
So
it
gives
me
all
four
or
five
big
categories
that
I
want
to
see
and
then
we
break
out
the
license
management
piece,
but
I
can
also
show
you
how
that
appears,
so
the
license
management.
It
actually
tells
me
these
are
the
two
licenses
in
the
libraries
that
I'm
using
as
part
of
my
project
over
here.
B
The
other
thing
that
I
can
do
is
I
can
actually
click
on
this
one
ability,
while
I'm
viewing
it
I,
can
look
at
the
details
of
this
vulnerability
by
clicking
on
the
CDE
link,
which
will
take
you
to
the
CDE
website.
I
can
create
an
issue
right
from
here
and
when
I
do
that
it
actually
pulls
in
all
the
details.
So
let
me
go
click
that
button,
probably
not
a
good
idea,
but
what
it
would
have
done
is.
B
B
So
we
we
rely
on
open
source
tools
to
scan
the
code
and
all
the
other
tools
are
open-source
tools
and
we
rely
on
some
of
them
for
their
nightly
builds.
So
whatever
new
stuff
came
in
will
be
packaged
in
that
and
it's
a
docker
container
that
we
pull
down.
We
actually
run
the
scan
against
you
know,
whatever
you
know,
source
code
or
if
it's
a
running
site
or
whatever
so
we're
getting
the
latest
details
about
those
CVS
before
they
come
in.
B
Yeah,
so
the
question
is:
can
we
can
we
configure
to
a
specific
set
of
checks
that
we
may
want
to
put
in
like
the
Stig
or
whatever?
We
are
not
there
yet,
but
we
are
working
towards
that.
So
that's
the
idea
right
now.
We
just
leave
it
at
the
native
level,
which
is
CV
or
cwe.
That's
all
we
report
right
now.
