►
Description
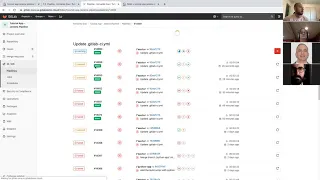
This video Demos how GitLab pipelines can integrate with Jenkins, and poll the status of a Jenkins job in order to trigger further stages in the pipeline.
C
Yeah,
that's
what
I
just
did
perfect
all
right,
thanks
shells
yeah,
so
yeah.
Let
me
get
started
so
so
pretty
much
the
the
use
case
for
this
that
we
wanted
to
get
going.
Was
some
customers
wanted
to
create
a
job?
They
had
a
build
job
already
running
in
Jenkins
and
what
ended
up
happening
is
they
didn't
want
to
migrate
all
that
get
laughing
so
a
galette
CI
file,
so
they
wanted
the
job
to
build
in
Jenkins,
for
example,
and
then,
if
that
build
were
to
be
successful,
then
we
would
continue
on
in
the
pipeline.
C
C
Yeah,
so
so
so
exactly
so,
if
Jenkins
CI
were
to
fail,
then
security,
you
wouldn't
we
wouldn't
run
the
security
scans.
But
if
Jenkins
CI
were
to
pass,
then
we'd
continue
on
and
run
the
security
scans
and
then
even
then
we
can
even
do
CD
via
Jenkins
or
we
can
do
CD
vehicle
app.
So
you
can
integrate
Jenkins
at
any
point
in
the
pipeline.
I'm.
C
No,
not
necessarily
so
so
the
Jenkins
pipeline,
so
so
the
way
that
it
works
right
now
is:
if,
if
a
build
were
to
fail
right,
then
you
wouldn't
move
on
to
catch
the
security
scans,
but
the
security
scans,
the
security
scans
can
run
then,
and
then
they
can
cause
the
bill
to
fail,
and
then
you
wouldn't
continue
on
to
the
next
step.
So
you
can
you
can
do
it.
However,
you
can
configure
it
in
a
order.
So
so.
C
D
C
This
is
just
basic
set
up
that
I'm
just
going
through
the
how
you
how
a
customer
would
set
it
up,
they
would
set
the
repository
URL
and
the
credentials
and
I'll
try
to
get
something
up.
The
demo
systems
has
a
good
write-up
on
this,
but
I
can
probably
make
it
more.
You
know
nice
and
customer
centric,
so
that
would
be
set
up.
C
We
wouldn't
set
up
any
build
triggers
because
there's
nothing
that's
going
to
trick
we're
gonna
trigger
this
job
from
running
manually
from
the
from
the
CI
from
Gil
at
CI,
so
this
wouldn't
be
configured
in
my
build
environment.
I
just
have
secrets,
like
my
CI
registry
password,
where
customer
would
create
a
service
user
which
would
have
all
these
things
on
there.
So
this
is
just
for
testing
purposes,
and
so
here's
my
actual
job
that
I
have
in
Jenkins.
So
in
this
job,
what
I'm
gonna
do
is
on
any
error.
C
I'm
gonna
exit
out
with
error
exit
code
and
all
I'm
doing
here
is
just
on
building
my
container
and
then
pushing
it
to
my
doctor,
posit
or
e,
and
then
I'm
exiting
with
the
zeros
to
show
success
and
then
in
post
build
actions
using
the
get
lab,
plugin
I'm
telling
it
to
publish
the
build
status
to
Jenkins.
So
that's
where
you
see
the
actual
external
job
come
and
run
right
after
the
job
is,
is
successful
or
failed
and
it
will
link
to
the
Jenkins
job.
C
So
now,
I
will
show
you
that
in
action,
the
job
burning
in
action,
then
I'll
go
I'll,
go
on
the
Gil
up,
see
I
fell
so
let's
run
a
pipeline
so
see
SUV
pipelines
and
I'm
gonna
go
ahead
and
run
a
pipeline
on
master.
So
remember
this
pipeline
is
gonna,
run
this
raker
twit,
so
I'll
add
exit
one
later,
so
you
can
see
it
actually
failed.
So
this
is
a
success
case.
So
you
see
that
the
build
job
kicks
off
and
what
the
build
job
is
doing.
C
Is
it's
running
this
custom
Python
script,
that
I
wrote
that
just
triggers
the
Jenkins
API?
So
what
it's
doing
is
it's
running
this
Python
script
that
is
calling
Jenkins
is
starting
the
job
and
then
it's
waiting
as
polling
for
the
job
status.
So
it'll
keep
checking
the
job
status
to
see
if
the
job
you
know
that's
failed
or
if
it's
thora,
if
it's
still
running
it'll,
keep
checking
it
and
I
added
a
timeout
to
it
and
if
it's
successful,
then
it'll
show
the
result
as
successful.
C
So
it's
going
to
trigger
the
job
and
then
the
job
will
automatically
fail,
and
then
you
will
see
that
none
of
these
security
scans
will
run,
and
this
can
be
done
in
the
same
order
we
can.
We
can
also
have
like
that.
Let's
say
the
next
job
would
be
deploying
a
deploy
job.
You
can
do
this.
You
can
have
this.
If
any
of
the
scans
fail,
then
we
won't
go
to
the
deploy
job
so
and
that's
what
you're,
what
you're
mainly
worried?
The
customers
are
mainly
looking
for
its
end.
C
B
C
So
external,
the
only
the
only
thing
external
is
is,
is
just
because
of
this
right
here
because
of
this
post
build
action,
but
there
can
be
different
post,
build
actions,
means
differently
and
and
they'll
just
pop
an
external
job
will
always
pop
out
at
the
end.
It
doesn't
actually
run
a
job
or
do
anything
it's
just
posting
status,
so
it's
not
really
relevant
to
it's
just
so
you
can
go
back
and
check
the
status
of
the
Jenkins
job
easily,
but
it
doesn't
do
anything
else.
I
see
okay,
so
you
can
have
multiple.
C
You
can
have
like
10
different
ones
with
different
names,
so
see
how
this
one
called.
The
build
name
is
Jenkins
I
can
name
a
Jenkins
build
and
then
I
can
name
another
job.
Jenkins
deploy
and
I
can
I
can
name
a
whole
bunch
of
different.
You
know
post
build
actions
and
then
do
all
those
external
jobs
will
show
up
at
the
end.
It.
C
C
C
C
A
C
And
so
now,
to
show
a
little
bit
more
of
the
of
the
technical
side
and
the
yeah
and
see
I
yeah
mo.
You
can
do
these
things
where
you
allow
failure,
which
can
be
a
boolean
value.
So
if
you
say
allow
failure
equals
false.
For
example,
in
the
security
scans,
I
can
say
a
la
failure
equals
false.
If
any
of
those
tests
were
to
actually
fail,
then
we
wouldn't
move
on
to
the
next
stage
in
the
pipeline.
C
So
that's
the
way
that
you
can
configure
it
so
so
for
the
case
of
you
want
the
scans
to
run
first
and
then
do
the
deploy
job.
What
you
would
do
is
you
would
you
would
have
your
deploy
job,
for
example,
and
you'd
run
your
script
but
and
deploy
job
would
be
in
the
stage
after
the
test
job,
for
example,
and
what
you
would
do
is
in
the
different
security
scans.
You
would
say
a
la
failure
equals
false
that
way.
If
any
security
scan
fails,
you
wouldn't
move
on
to
the
deploy
stage.
B
It's
a
failure
in
the
context
of
a
security
scan.
Are
you
just
talking
about
like
the
disk
fail
to
actually
run
the
scan
like
you
didn't
didn't
properly,
execute
or
I
mean,
because
the
other
side
of
the
security
scan
is
that
you
know
you
may
have
vulnerabilities
that
you
don't
want
to
pass
but
comes
back
and
you
you,
you
might
want
to
fail
against.
Like
hey
I
found
the
crit
vulnerability,
that's
considered
a
failure
that
this
is
just
just
literally
talking
about
the
job
not
operating
correctly,
though
right
yeah.
B
C
A
C
A
D
B
D
B
B
It
feels
like
we
need
to
have
some
sort
of
threshold
that
you
know,
checks
the
severity
levels
of
findings
of
all
the
jobs
and,
if
it,
if
it
you
know,
is
above
whatever
their
threshold
that
has
been
defined
as
part
of
the
job,
then
maybe
then
it
fails
that
based
off
of
that,
even
if
the
job
past,
because
they
operated
correctly
right.
Yes,.
C
B
Guess
the
last
thing
I'll
say
about
that
specifically:
is
that
I
think
this
is
because
the
way
we
do
it
inside
get
lab
it's
okay,
because
it
still
goes
through
a
merge
request,
and
you
see
those
vulnerabilities
listed
there
now.
If
we're
talking
about
this
in
context
of
Jenkins,
now
all
the
sudden,
you
start
to
make
that
a
little
bit
confusing,
because
you're
not
seeing
that,
as
necessarily
as
part
of
a
merge
request
anymore,
because
you're
doing
that
yeah.
A
C
B
C
Not
that's
right
so
that
that's
just
depending
on
the
on
the
use
case
from
most
likely
they
would
be
using
if
they're,
using
on
get
lot
for
source
code
management
and
they
would
should
be
using
a
merger
cross
flow
and
that's
where
the
approvals
can
be
set
up.
But
then,
but
it'll
continue
on
in
the
pipeline,
because
the
that's
just
an
approval
right
for
the
end
result.
It's
not
an
approval
for
blocking
at
a
certain
point
in
the
pipeline,
yeah.
C
So
that'll
be
one
thing:
I
have
to
figure
out,
I
mean
I'm
for
sure
it
can
be
done
by
pulling
something
or
accessing
the
API
through
like
a
separate
job.
The
thing
is,
you
know,
is
that
one
thing
that
we
want,
you
know
is
a
little
bit
too
hacky
having
another
job
that
accesses
that
get
lot
of
API
to
look
at
the
vulnerability
status
or.
B
I
feel
like
the
ideal
state
here
with
that
would
be
kind
of
the
minimal
viable
change
here
would
be
that
we
incorporate
another
security
job
that
runs
after
these
security
jobs
in
a
subsequent
stage.
That
then
goes
and
checks
the
the
artifact
report
of
the
scans
and
based
off
of
the
variable,
that's
defining
that
job
of
what
what
is
acceptable
level
of
criteria.
B
They
could
fail
that
job
so
that
no
more
of
the
no
more
of
the
process
continues
on
in
the
pipeline
and
you
know
still
will
show
the
results
from
the
merge
request,
but
you
just
don't
have
to
run
those
extra
build
steps.
So
you
know
maybe
a
review
app
or
whatever
else
may
inside
that
merge
request
pipeline
now.
It
should
now
be
something
for
the
development
team
that
we
would.
C
B
C
Result
is
not
equal
to
success,
then
we
exit
with
a
failure,
if
it,
if
it
is,
we
just
exit,
and
the
customer
would
write
something
like
this
in
order
to
determine
the
status
of
the
Jenkins
shop
to
see
if
they
should
move
forward
or
kick
it
or
kick
it
off
or
exactly
what
they
need.
So
this
was
just
further
start.
This
is
just
like
if
it's
running
those
security
scans
is
dependent
on
the
Jenkins
job
passing
or
failing,
but
if
they
just
want
to
kick
off
the
job,
they
can
just
use
the
Jenkins
API.
C
C
Yeah,
so
if
every
project
has
a
different
job
right,
then
you
would
have
to
redo
it.
You
know
for
every
project,
because
it's
its
job
dependent.
So
you
know
you
might
be
kicking
off
a
different
job
in
each
pipeline,
and
in
that
case
then,
then
you
will
have
to
you
know
you
can
you
can
definitely
do
a
template
and
probably
write
like
a
helmet
chart
or
something
for
for
our
something
in
ansible
or
something
to
automate
and
just
change
the
names.
A
The
reason
I
ask
is
it's
great
that
we
can
do
this
at
the
same
time.
I
worry
about.
Do
we
make
it
so
simple
that
we
then
people
don't
have
an
incentive
to
leave
Jenkins,
but
I.
Think
the
incentive
to
leave
Jenkins
is
twofold.
One
is
we
can
automate
some
of
that
if
they'll
use
our
CI
and
the
other
is
in
terms
of
audit
ability,
you
know
if
you
don't
really
want
a
developer
going
in
and
being
able
to
change
the
UML
file
to
say
pass
everything
the
security
people
would
have
a
fit
about
that.
