►
Description
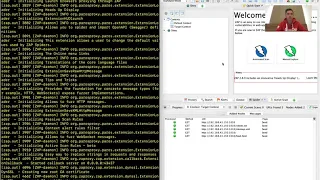
A demonstration of how the AJAX spidering feature of DAST works, and the kind of problem it solves.
A
A
Hello,
I'm,
cam
and
today
I'm
going
to
be
demonstrating
how
the
Ajax
scan
capability
works
in
dust,
so
I'm
just
gonna
share
my
screen
like
a
goalie,
alright,
now
the
problem,
this
solves
is
imagine
we
have
a
page
which
I'm
running
locally
this
food
website.
It's
just
got
a
bunch
of
text
and
a
link
to
bacon
click
on
bacon
and
there's
just
another
page
full
text.
Now
I'm
gonna
run
dust
on
this
website
and
we'll
see
what
happens.
A
Alright,
so
I've
kicked
up
dust
and
you
can
see
it
running
in
this
zap
UI,
so
I'm
running
it
on
this
kind
of
debug
mode,
so
you
can
just
see
what's
happening
and
you
can
see
that
the
normal
Ajax
spider
has
run.
It's
detected
all
these
nodes.
If
we
open
up
the
site's
here,
you
can
see
it's
found
food,
but
it
hasn't
found
bacon
and
while
it's
found
some
vulnerabilities
such
as
this
guy
for
food,
there's
no
vulnerabilities
for
bacon
and
if
we
look
at
the
reason
this
has
happened.
A
If
we
go
back
to
food
and
look
at
the
source
code,
you
can
see
that.
Excuse
me,
you
can
see
that
the
bacon
link
is
dynamically
added
using
javascript
and
the
normal
spider
that
spiders
using
that
spiders
is
just
essentially
HTTP
requests,
it
doesn't
understand
JavaScript,
and
so
it
never
finds
the
bacon
link
and
no
vulnerabilities
will
be
found.
So
the
Ajax
spider
functionality
is
about
fixing
this.
So
what
happens?
Is
we
use
the
appropriate
configuration
value?
A
A
Now,
if
we
expand
the
site's
nodes
again,
you
can
see
it's
found
bacon
and
it's
also
sound
found
this
favicon.
So
basically,
any
West
at
the
browser
makes
zap
cool
and
dust
will
now
understand,
and
you
can
see
that
we
now
have
a
vulnerability
for
bacon.
So
that's
it!
That's
how
the
edge
ex
spidering
works.
I,
hope
you
found
this
useful
jeez.
