►
From YouTube: 2020.05.06 - SAST to Complete working session 2
Description
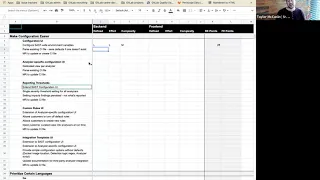
DEC scoring session of candidate scope for SAST to be declared Complete.
A
Alright,
happy
Wednesday,
everybody
so
for
buddies
weakens
is
going
well
as
we
cross
the
halfway
point
here.
This
is
a
continuation
from
what
we
did
yesterday
so
yesterday
was
about
getting
out
just
a
little
bit
more
clarity,
not
depth,
but
just
a
little
bit
more
clarity
on
everything.
That's
that's
in
candidate
scope
for
SAS
to
complete
today.
What
I
wanted
to
go
through
was
a
deck
scoring
exercise.
A
So
the
reason
for
going
this
direction
is
that
to
me
our
current
process
when
we're
declaring
a
weight
when
we're
declaring
what
a
size
is,
that
is
an
output
of
refinement
and
we're
nowhere
near
ready
for
that.
So
this
is
to
get
a
rough
estimate
as
to
what
the
relative
sizing
is
for
every
single
one
of
these
I
will
happily
share
my
screen
again,
and
we
will
we'll
see
where
this
goes.
A
Unless
there
are
objections,
so
the
way
that
this
reads
so
this
is
the
state.
So
this
is
the
same
setup
as
that
document.
We
were
going
through
yesterday,
where
they're
big
blocks
of
work
that
are
intentionally
in
verbs
and
then
underneath
these
we
have
these.
We
have
the
bolded
elements,
so
these
so
things
like
configuration,
UI
and
lines
are
specific
configuration,
UI,
etc.
Those
are
the
things
that
I
was
looking
to
score,
because
those
are
the
discrete
bodies
of
work
that
we're
being
asked
to
do.
A
C
D
D
A
C
I
wouldn't
mind
touching
on
areas
that
we
know
specifically
involved.
Front-End
I
know
I
had
representation.
Yesterday,
I
had
asked
a
couple
of
the
team
members
to
join
and
they
were
able
to
today
a
different
story.
So
yeah
we're
gonna
have
to
backburner
some
of
the
front-end
but
yeah.
If
we
could
denote
that
somehow,
okay.
A
So,
as
we
were
going
through
yesterday,
kinda
sorta,
so
the
way
that
I'm
C,
so
what
we
were
discussing
yesterday,
these
women
bullet
points
of
what
it
means
for
a
configuration
UI
to
exist,
in
other
words,
I'm
asserting
with
their
requirements.
So
all
of
these
math,
what
is
not
bolded
here,
yes,
for
high-level
requirements.
E
F
A
A
D
B
Yes,
that
would
be
why
I
said
large,
primarily
because
this
is
a
primarily
interface
driven
item
and
that
can
change
quite
a
bit
of
the
on
the
effort
and
complexity.
So
I
I
guess
just
to
justify
my
ratings
large
effort,
as
there
would
be
quite
a
bit
of
changes
involved
there.
But
the
complexity
essentially
boils
down
to
rendering
predetermined
values.
G
Yeah,
don't
just
jump
in
here
to
I
think
this
is
one
where
I
expect
every
single
one
of
these
will
need
a
lot
more
definition
around
them
on
what
we're
actually
trying
to
do.
This
is
really
for
me
to
have
an
input
back
to
be
able
to
say
hey.
This
thing
is
a
lot
bigger
than
what
I
thought
it
was
gonna
be
and
in
my
p.m.
G
brain
I
thought
it
was
gonna,
be
a
lot
faster
to
implement,
and
so,
if
it's
a
giant,
you
know
three-month
project,
I'll,
probably
scope
it
down
or
even
consider
punting
it
out,
or
there
will
be
things
here
that
I
thought
was
really
hard
and
y'all
will
surprise
me
that
it's
gonna
be
super
simple
and
instead
I'll
prioritize
that
higher,
so
that's
kind
of
how
I'll
be
using
these,
but
100%
I
definitely
know
that
all
of
this
needs
a
ton.
More
definition.
A
B
C
Mean
there's
definitely
a
development
workflow
here
right,
there's
the
you
parse
the
CI
file
to
get
the
inputs
to
the
form
or
defaults
and
there's
the
configuration
form
and
then
they
create
some
mo
I.
Don't
know
if
reordering
these
would
make
sense
or
help,
but
it
would
go
six
five,
seven
in
terms
of
that
process,
not
a
development
process,
but
when
you're
actually
using
the
tool.
C
B
H
This
this
seems,
it
seems
pretty
pretty
well-defined
and
low
effort
and
complexity
in
the
sense
that,
like
it
should
be
a
yeah
mofo
right
and
yeah
mo
parsers
are
I,
mean
fairly
well
known,
it's
more
about
like
just
defining
the
st.
the
default,
so
maybe
that
Ferg's
actually
more
of
a.
What
is
the
middle
one
I
know
sounds
pretty
straightforward
to
me,
but
I
could
be
missing
something.
B
E
H
Just
to
kind
of
come
back
to
the
definitions
in
the
deck
scoring
document
defined
small
means
just
this
just
defined.
It's
well
understood
that
media
means
it
has
some
open
questions,
but
defined
enough
to
understand
the
intent.
Large
means
undefined
or
too
many
gaps
to
adequately
understand
the
task.
So
that's
just
like
thinking
about
the
definition
of
it
not
so
much
the
size
of
the
task.
So
by
making
this
large
do
you
think
that
it
has
it's
undefined
or
too
many
gaps
to
under
adequately
understand
the
task?
H
H
Well,
just
most
mostly
I
was
just
honing
in
on
defined
right,
like
is
that
well
understood
the
problem,
you
think
it's
well
define,
or
do
you
think
there
are
still
some
open
questions
or
is
it
just
like
man
I,
don't
even
know
where
to
start
here
so
I
think,
probably
between
small
into
font
and
medium
here,
I
think
we
do
have
some
questions
open
question,
so
a
medium
seems
seems
fine
to
me,
but
I
definitely
don't
think
it's
large
in
the
sense
of
like
it
can't
even
understand
it.
You
know
yeah.
B
H
Yeah
something
else,
that's
probably
good
to
note
here-
is
just
whether
or
not
whitespace
or
any
other
like
comments
or
things
like
that
would
be
meaningful.
That
could
that
could
add
complexity,
because
then
you
know
we
can't
just
parse
the
mo
file
and
then
we
encode
it
because
you
could
lose
comments
or
other
things
that
might
be
meaningful,
or
maybe
we
decide
with
round
one
that's
not
as
important.
They
could
update
that
mr
but
I
think
M
there's
some
open
questions.
There.
H
B
H
H
B
A
A
What's
down
below
here,
all
right
analyze,
our
specific
configuration
you
guys
so
I
mean.
However,
that
means
so.
This
is,
as
we
were
discussing
yesterday.
Do
differentiation
from
what
was
above
is
that
these
are
things
that
effects
asked
the
SAS
namespace
they
are.
These
are
good
those
configuration
values
that
are
sassed
wide
across
all
analyzers.
These
is
women.
This
is
when
we
drill
into
specific
analyzer
configurations
themselves.
A
And
what's
not
listed
here
and
I
neglected
to
mention
yesterday
is
that
I
am
expecting,
since
this
is
a
drill
down
from
a
top-level
concern.
So
now
the
word
seer
you
was
you
SAS
has
been
established
if
you've
drilled
down
to
this
point,
where
you're
configuring,
an
existing
analyzer,
a
CI
file,
exists,
I.
B
C
C
B
So
that's
one
thing
that
I
guess
we
definitely
probably
need
to
get
consensus
on,
but
that
kind
of
goes
back
to
the
question
whether
we're
splenius
of
issues
or
treating
like
an
issue
as
delivering
a
unit
of
value
or
I.
Don't
think
that
delivering
parsing
the
existing
CI
configuration
as
a
back-end
test
provides
value
without
the
UI
component,
but
maybe
I
guess
that's
more
of
a
workflow
question.
I,
don't
know
if
that's
scope
or
outer
scope
there.
A
A
A
H
A
A
There,
these
are
my
guesses
reason
for
doing
this,
so
this
is
where
we
get
into
new.
This
is
assuming
that
we're
doing
this
particular
feature
for
a
report.
What
we're
persisting,
what
level
of
severity
findings
we
are
persisting
here.
So
this
is
following
the
same
thing
where
we
are
we're
parsing
in
an
existing
value.
Right
now,
I'm
saying
see
I
file,
but
it's
not
really
a
CI
concern,
so
wording
being
what
it
is.
We
got
to
do
something
that's
going
to
update
it.
A
H
Yeah
I
think
across
the
board,
I
think
it
looks
the
same
for
the
first
two
items
obvious
the
way
I
think
about
it,
I
mean
without
us.
Further
defining.
You
know
the
boundary
between
some
of
these
things.
The
last
one
there
have
been
persistent
logic
for
finding
what
what
is
that
you
might
have
just
said
that
I
missed
it,
but
all.
A
B
J
B
A
C
C
C
A
A
G
One
thing
I
want
to
add
here
is
that
this
is
written
as
if
this
is
the
UI
implementation
of
this
I
do
absolutely
like
thinking
iteratively
here
like
there
is
value
of
us
doing,
supporting
it
in
the
config,
creating
a
nice
UI
to
interact
with
it.
So
like
keep
that
in
mind
as
we're
going
through
this.
H
So,
during
that,
allowing
customer
to
create
new
rules
that
seems
like
a
large
with
defined
I
have
no
clue
how
it
would
even
turn
off
default
rules,
kind
of
makes
some
sense
in
the
sense
of
like
most
of
the
analyzers.
You
know
the
scanners
have
some
form
of
configuration.
They
can
disable
that
rule,
but.
B
H
H
B
E
B
Yeah
I
think
that's
probably
the
question
that
would
place
the
effort
at
medium.
I
think
that
the
definition
of
what
we're
turning
things
off
seems
pretty
straightforward
but
and
I
I
guess.
This
is
actually
there's
an
outstanding
EMR
about
this
right
now,
which
is
to
go
SEC
one
which
is
wanting
to
disable
specific
rules
that
are
that
they
don't
care
about.
So
goes
that
calls
that
G
104
for,
like
a
rule
that
they
don't
care
about.
B
B
K
K
You
know
that
I
think
you
can
specify
the
rules
of
Charles
rules
with
that
like
a
some
config
file,
but
they
analyze
our
BOTS,
actually
change.
You
know
the
way
that
they
either
parse
or
to
me
it's
just
like
how
we
have
those
analyzers
turnoff.
The
rules
is
still
kind
of
fuzzy
and
seems
like
a
large
effort.
H
B
A
A
H
The
only
real
danger
with
that
approach
is
it
could
be
easy
to
solve
it
in
such
a
way
that
then,
when
you
started
abstracting
to
multiple
analyzers,
then
you
have
backwards
compatibility
breaks
as
we
realize
wow.
This
is
not
sustainable
to
continue
in
this
approach
for
all
of
them.
Looking
at
some
yeah
I
mean
I.
Think
that
definitely
would
help
in
terms
of
helping
us
to
iterate
and
move
forward,
but
I
do
think
we
need
to
at
least
this
you
know,
spend
a
minute
or
a
second
to
I.
A
F
B
J
H
H
Think
I
think
you're
right
to
say
both
of
us
are
large
because
you
can
think
about
the
two
like
the
multiple
compartments
here.
It's
really
undefined
the
effort
means
cross
team
collaboration
with
our
vulnerability
research
team.
So
that's
a
high
high
effort
and
then
the
complexity
is
probably
like
defining
some
form
of
a
DSL
or
something
which
is
fairly
complex,
I
think
that's
how
across
the
board
in
the
way
I
break
it
apart,
I
would.
A
Separate
vulnerability,
research,
integration
on
this
item
from
this
I
know
this
is
yeah.
This
is
about
providing
the
ability
for
customers
to
manipulate
what
rules
are
executing
rather
than
us,
manipulating
the
default
rule
packs
that
customers
will
get
which
I
would
assert.
Is
the
vulnerability,
research,
integration
point?
Okay,.
H
B
H
A
B
H
D
So
sorry,
just
gonna
jump
in
really
quick
on
22.
Is
there
a
a
reference
architecture
or
like
some
some
other
vendor
who's
already
done?
Something
like
this,
you
know
is
this
a
matter
of
you
know
what
are
the
allowable
fields
to
manipulate?
You
know
I'm
just
trying
to
help.
You
know
at
least
help
myself
understand.
What
does
this
really
mean
by
customers
create
new
rules?
You
know
III
assume
that
there
are
fine,
a
finite
number
of
knobs
to
turn,
but
but
but
I
don't
know.
That's
why
I'm
asking
the
question
yeah.
G
We
do
have
one
competitor,
I,
don't
know
how
to
pronounce
it
the
tree
that
tree
that
basically
allows
rule
customizations
on
there
and
it
allows
sort
of
a
hyper,
specific
contextualization
of
rules
they
even
provide,
like
rule
packs,
based
on
what
kinds
of
projects
you
have.
So
if
you've
got
I'm
gonna
make
this
up
like
a
react.
J/S
project
like
here
are
some
rules
that
you
might
want
to
use.
If
you
have
that
kind
of
project.
D
B
Yeah
I
think
that's
definitely
indicative
of
that,
for
what
it's
worth
I
was
not
really
considering
that
aspect
as
much
as
the
task
of
trickling
these
rules
down
to
the
individual
scanners.
So
there
there's
definitely
large
back
into
effort
there
around
getting
our
scanners
to
cooperate,
which
is
either
creating
a
custom
engine
or
modifying
the
existing
ones,
and
then
there'd
also
need
a
large
effort
on
the
front
end
of
how
to
provide
a
scape
schema
for
the
rules
we
inputted.
B
B
I
Can
share
more
on
that
soon.
I
have
not
really
dug
into
the
details,
I'm
kind
of
seeing
what
kind
of
access
I
can
get
to
these
portals
right
now.
If
anybody
has
any
test
accounts,
please
let
me
know,
but
I
yeah.
A
competitive
analysis
is
always
really
interesting
without
test
accounts,
because
it
involves
a
lot
of
time,
looking
at
demos,
on
YouTube
and
looking
through
documentation,
and
things
like
that
so
I'm,
just
starting
to
dig
into
that
now,
but
I
can
follow
up
when
I
have
more
on
that.
So
penny.
D
D
I
D
Yeah,
like
I,
said
I
just
I'm,
you
know
I'm
watching
the
time
as
well,
so
I'm
trying
to
be
as
brief
as
possible,
but
still
maintain
the
the
content.
I
yeah
I'm,
just
like
I,
said
I'm
just
trying
to
break
it
down
in
my
mind.
As
far
as
you
know,
what
does
this
look
like?
What
would
a
schema?
Look
like
you
know:
do
we,
if
we're
dumping,
all
this
data
into
tables?
B
A
A
Oh,
let
me
introduce
this
again
from
yesterday.
The
distinction
between
this
and
nine
through
twelve
is
that
the
intention
of
nine
through
twelve,
is
dealing
with
what
we
have
today,
so
existing
existing
scanner.
Excuse
me,
language
check,
existing
analyzers
and
the
configuration
options
we
have
for
them
right
now,
which
is
pretty
bling.
A
The
idea
for
25
through
28
is
is,
is
a
bring
your
own
scanner
type
of
party
for
projects.
If
somebody
as
an
accountant,
if
there's,
if
there's
an
integrator
that
would
like
to
provide
a
docker
container
and
the
ability
for
how
do
we
know
where
to
run
it
and
hot,
and
how
do
we
know
how
to
run
it?
That's
what
this
is
intended
to
provide.
That's
what
this
section
is
intended
to
enable.
H
A
G
B
G
This
is
today,
like
our
customers.
Just
do
not
understand
how
our
scans
work,
so
this
whole
UI
convention
is
a
way
to
help.
Tell
that
story
to
get
entry
places
of
hey.
Did
you
even
know
that
sonar
cube
Rd
has
an
integration
with
get
lab,
here's
how
to
enable
it-
and
in
fact,
maybe
even
here's
a
button
to
apply
the
mr
to
your
CI
file.
Things
like
that.
A
G
And
we
had
this
conversation
in
slack
yesterday,
like
documentation,
is
part
of
everything
that
we
do
or
should
be
at
least
so,
I
like
it.
It
should
be
factored
into
all
of
these
things,
though.
I
recognize
that,
like
when
we
first
do
a
UI
like
there
will
be
a
lot
of
documentation
that
I'll
have
to
go
with
that.
B
So
speaking,
more
generally
to
this,
it
is
feature
the
word
we're
using
for
these
groupings.
Feature
capability.
I
still
don't
feel
like
I
have
a
good
understanding
of
what
this
is
beyond
like
insert.
Ci
template,
so
I
guess
I
need
I
would
need
more
details
to
to
make
me
I
mean
I
would
need
to
read
more
of
a
description
of
what
this
is
to
feel
more
comfortable,
applying
scoring
to
each
one
of
these,
so
by
which
I
got
some
demos
to
large
I.
G
J
B
E
B
B
A
A
And
any
surprise
later
on,
that
makes
these
magically
smaller
is
always
a
welcome
gift.
So
this
is
so
not
that
we're
trying
to
pad,
but
I'm
hearing
too
many
questions
to
want
this
to
go
smaller.
So
unless
anybody
objects,
I
want
to
go
to
more
comfortable
ground
for
the
engineers
that
are
here,
that's
the
analyzers
themselves.
A
Understand-
and
this
one
in
particular
to
me,
is
a
little
bit
most
squib
is
the
most
squishy,
because
I
don't
know
how
to
do
line.
31
get
the
so
reminder
where
this
is
coming
from.
There's
been
customer
bake-offs
go
sec,
the
open
source
project
against
some
of
our
point
of
some
of
our
competitors
like
check
marks,
and
it
just
does
not
hold
up.
How
can
we
make
it
do
better.
B
G
It's
been
done
is
basically
a
implementation
of
osj
Spring
Framework
we're
basically
we're
running
that
against
a
whole
large
number
of
tools.
I
think
this
is
a
great
point
that
if
we
find
a
go
benchmarking
project
like
I
would
love
to
connect
it
into
that.
It's
a
way
to
really
put
data
behind
what
we're
trying
to
accomplish
with
this.
E
G
Have
I've
had
multiple
customers
bring
up
our
go
sack
scanner,
particularly
basically,
they've
done
their
own
in-house
bake-off
between
the
impact
not
even
get
lab.
Just
the
open-source
go
sex
scanner
versus
something
like
Vera
coat
or
fortify,
and
have
found
like
a
like
a
10x
difference
in
the
number
of
vulnerabilities
that
it
finds.
Oh.
H
G
Where
I
mean,
is
there
a
better
scanner
to
use
them
go
sec?
Maybe
is
there
something
we
can
do
to
scan
more
things
I
know
go
is
a
weird
language
from
a
dependency
perspective,
so
I
think
there's
a
lot
of
different
areas
that
we
can
go
mainly.
The
goal
here
is:
we
use
go
internally.
We
want
to
benefit
from
better
findings,
and
our
customers
are
also
telling
us
that
we're
not
competitive
with
our
bill
offering.
H
Okay,
cool,
I
think,
given
that
and
like
the
squishiness,
meaning
there's
a
couple
different
directions,
that
the
m
is
a
good
definition
for
me.
I
think
effort
is
probably
a
morbid.
Well,
it
just
depends
upon
how
much
we
want
to
slice
off
here
right,
like
I'm,
assuming
that,
as
we
dig
in
there's
a
good
chance
that
we
can
chunk
the
work
either
small,
medium
or
large
right
and
can
tackle
it
at
different
levels.
It
depends
upon
how
much
you
want
to
improve.
B
A
H
A
H
H
A
B
B
I
would
say
that
for
the
next
all
that
create
integration,
test
projects
defined
is
looser
than
the
effort
and
complexity
of
simply
adding
one.
My
process
for
adding
an
integration
test
is
pretty
straightforward,
so
I
would
say
small
for
all
of
those
effort,
complexity,
but
maybe
medium
for
the
defined
okay.
H
A
B
I
H
G
A
As
to
what
we're
missing,
I'm,
not
entirely
sure,
but
there's
something
we're
gonna
need
to
do
in
order
to
sign
off
on
it
saying
yes,
we
can
do,
we
need
a
reference
or
we
need
to
test
projects.
That
is
an
Android
test
project
and
prove
that
it
works,
and
if
it
doesn't
work,
that's
gonna
define
what
the
effort
is.
This
is
probably
very
much
the
definition
of
a
test-driven
development
project.
B
E
Think
it
makes
sense,
and
we
also
we
talked
about
it's
better-
to
be
higher
than
lower
on
our
guesses.
So
you
know,
depending
on
on
what
we're
lacking
for
that
integration,
we
get
that
defined
that
others
might
definitely
go
down,
but
it's
hard
didn't
say
that
with
much
confidence
until
we
know
more,
what's.
H
D
A
Another
tab,
if
you're
interested
okay,
I
will
be
contrarian,
but
this
is
me
giving
my
own
opinion
ends,
but
since
daniel
put
me
in
charge
of
defining
all
of
this
told
you
made
a
mistake
kidding
with
all
of
this
for
everybody's
watching.
The
recording
I
would
argue
that,
but
I
would
argue
that
this
is
the
definition
of
than
something
that
we
don't
know
exactly.
What
to
do.
However,
it
is
I
have
a
hard
time,
imagining
that
it
will
result
in
anything
more
than
a
simple
extension
of
what
we
have
today.
A
H
Me
ask
you
this
question,
then
what
happens
if,
as
we're
defining
this
for
realizing?
Well,
we
have
to
write
our
own
analyzer
where
it
is,
you
know
more
than
just
extending.
Do
we
just
say?
Well,
then,
that's
a
whole
nother
thing
we
reassess
just
like
we
do
in
window
gallant
I
mean
yeah.
So
so,
if
we
get
into
this,
we
realize
wow
this.
H
This
is
like
for
spaceships
or,
let's
start
then,
okay,
well,
we'll
reassess
rather
than
so
I,
don't
know
that
we
need
to
weigh
that
as
much
as
it's
either
wrapped
being
a
new
analyzer
or
sorry
scanner
or
it's
you
know,
extending
the
scanners.
We
have
burning,
always
as
we
have
right.
That's
what
you're
thinking.
That's.
G
A
So
and
I
think
once
we
get
into
a
refinement
we
find
out,
oh
then
we
get.
We
have
our
brown
pants
on
and
we
figure
out
that
this
is
absolutely
massive.
We
reconsidered
we,
we
reevaluate.
If
this
turns
out
to
be
something,
that's
absolutely
insane,
then
that
might
be
quatre.
That
might
be
a
time
that
gets
bumped
to
a
higher
maturity
level.
As
a
result,
I
would
hope
that
we'd
have
that
conversation,
otherwise
we're
doing
big
design
up
front.
H
So
I
think
that
might
speak
to
the
difference.
How
we
could
have
a
large
definition,
but
you
know
maybe
less
than
large
effort
in
complexity
is
when
just
thinking
beyond
like
what's
the
threshold
right
some
of
this
stuff,
even
even
if
the
definition
is
small,
is
still
like.
Well
I
mean
I,
guess,
yeah!
Well,
I!
Guess,
if
it
I
guess
it's
an
example.
Maybe
for
reference
would
be
like
you
know
if
it
was
doing
something
with
the
animal
it's
and
it's
completely
undefined.
H
It's
like
well,
okay,
but
at
the
end
of
the
day
we
know
we're
working
with
you.
Animals
so
I'll
be
Emma's,
verse,
essence,
Radford
and
complexity,
because
once
we
get
to
implementation
and
the
hard
part
is
actually
defining
it.
In
this
case,
it's
still
a
car
right.
It's
like
it
could
be
easily
be
like
create
a
new
analyzer.
B
B
If
we
simply
cannot
do
it
like
I,
don't
I,
don't
see
how,
in
a
similar
fashion
it
what
ifs
fog
bugs
do
we
know
if
spot
books
is
even
capable
of
scanning
Android
projects,
unless
we
know
for
sure
it
is
I,
don't
know
how
we
can
apply
a
effort,
a
complexity
that's
lower
than
large,
because
we
moving
forward.
It
may
be
possible
to
move
forward
by
building
an
analyzer,
but
that
doesn't
mean
that
my
building
analyzer
is
not
solving
the
problem.
It's
providing
a
vehicle
for
the
problem
to
get
somewhere.
B
So
I
guess
that's.
Why
I
like
for
a
lot
of
these
I
just
need
a
lot
more
details
before
I
feel
comfortable
about
like
applying
waste
to
these
things.
I,
don't
know
exactly
what.
If
we
wrote
a
scanner
that
look
that
at
a
single
common
rule,
would
that
be
a
scanner,
because
I'm
sure
we
can
come
up
with
one
by
just
looking
through
calling
Docs
and
figuring
out
what
an
unsafe
system
call
is
Oh.
A
L
H
A
H
H
So
there
is
a
potential,
though
we
could
use
deep.
It
has
integration
with
sonar
cube,
so
I
wonder
if
how
pluggable
full
or
extensible
detectives,
but
if
it's
extensible,
maybe
we
could
that
plus,
you
know
some
of
the
other
stories
down
further,
where
you
know
our
security
vulnerability.
Researchers,
you
know,
can
define
rules
that
then
work
with
detect,
but
you
know
I
actually
get
it
having
a
there's,
not
really
an
open-source
security
tool.
A
H
H
H
It's
honestly
like
the
interrupt
story
with
Coughlin
and
Java
is
amazing.
It's
like
you
can
paste
Java
code
into.
What's
that
main
IDE,
and
then
it
just
gives
you
common
like
the
interrupts
story,
it's
like
seamless,
so
it's
like
an
updated
version
of
Java
in
many
ways,
but
a
lot
better
in
a
lot
of
ways.
That's.
H
Think,
once
you
have
the
definition,
I
think
that
for
is
small,
but
because
I
think
it's
especially
since,
like
also
when
you
think
about
it's
a
preferred
way
to
do
and
rate
projects
is
probably
pretty
straightforward
to
generate
it.
It's
just
defining
what
a
vulnerabilities
look
like
in
that
concept
on
in
that
context,
and
then
it
seems
like
it
would
be
pretty
straightforward,
but
that's
my
point
of
view
of
these
okay.
B
B
H
B
B
A
A
H
G
H
B
B
G
E
H
I
E
H
H
A
A
Part
of
this
was
how
do
we
get
started?
How
do
we
approach
this
and
that's
what
we
were
going
through
this
first
time,
this
first
time,
I
think
we'll
have
a
little
bit
more
muscle
memory
with
it
going
through
it
again
and
I
will
have
mediums
filled
in
for
just
about
I
will
put
in
a
straw
person's
argument
for
what
each
one
of
these
are
in
advance.
Well,.
H
A
H
H
A
To
me
is
a
scan.
A
pipeline
has
been
executed.
We
have
findings
that
are
a
result
of
a
merge
request
and
we
are
providing
there
a
way
over
to
the
web
IDE
to
start
working
on
those
and
result
and
work
through
them
as
a
part
of
a
merge
request
workflow.
So
this
is
not
true,
shifting
left
into
a
web
ID
so
that
you're
doing
inline.
B
Of
sorry
so
I
guess
I
would
say
we
associate
security
scans
with
branches
not
merging
cross.
So
a
whether
or
not
a
merger
quest
is
currently
open.
We
would
actually
I
think
that
we
would
have
to
instead
be
linking
to
the
pipeline
page
and
I.
Don't
know
if
that's
the
intent
of
this
does
this
feature
depend
on
a
merge
request.
Having
been
opened.
B
H
H
B
B
A
H
Don't
know
what
the
API
looks
like
for
like
opening
a
file
in
the
web
IDE,
but
I
would
think
that
this
is
pretty
small
across
the
board,
because
we
should
already
have
the
branch
and
you'll
just
be
at
the
head
of
that
branch
in
that
file
at
that
line,
and
we
have
all
of
that
should
have
all
of
that
in
a
finding
correct
I
mean
that's
a
question
to
have
it
not
work
super
tightly
with
that
data
model.
I.
A
Alright,
let
me
well,
this
is
what
I
had
in
mind
66.
So
this
is
what
was
in
my
head.
Please
tell
me
where
I'm
wrong
or
update
I'm
wrong
here
in
the
context
of
a
pipeline
being
run
in
this
case,
I
was
asserting.
It
was
within
a
merge
request.
Security
findings
have
been
discovered
right
now.
It
results
in
a
modal,
where
you
get
some
certain
information
and
that's
where
the
journey
ends
or
you
can
dismiss
it
or
what
have
you?
A
I
A
A
L
A
With
this
was
the
finding,
this
is
what
it
was
called.
Hopefully
we
have
a
recommendation.
Whatever
data
we
have
that's
coming
with
from
the
JSON
payload
and
line
69,
you
could
argue,
is
not
in
VC,
but
we
were
amending
what
was
coming
from
analyzers
with
recommended
actions
based
upon
the
findings
that
it
had
that
it
was
put
forward.
H
H
So
I,
don't
think
it's
super
complex
from
the
sense
of
if
all
we're
doing
is
providing
API
is
in
the
data
for
them
to
so
you
know
you
have
support
in
ie.
If
we're
doing
the
IDE
work
ourselves
like
whether
that's
front-end
or
back-end
or
whatnot,
then
pretty
high
complexity
in
the
sense
that
it's
at
least
from
my
perspective,
it's
hard
because
it's
not
close,
they
act
like
it's
I'm,
not
working
that
side
of
the
code
area
the
code
base.
H
Maybe
it's
different
for
someone
else
here,
though,
so
it
kind
of
depends
upon
how
much
an
actual
web
IDE
work
we're
doing
as
opposed
to
just
exposing
the
data
for
them
to
do,
or
maybe
they
already
have
a
way
to
highlight
syntax
from
quality
tools,
or
some
of
these
things
are
already
defined.
I
don't
know.
Does
anybody
here
know
that.
G
Yeah
I
think
you
bring
up
a
good
point
here.
This
is
probably
of
all
the
things
listed
on
the
page,
the
one
that
bleeds
the
most
into
other
areas.
I,
definitely
think
this
is
one
where
we
can
probably
get
other
teams
to
do
the
work,
for
this
start
I
think
approaching
it
from
the
do
our
scanners
and
do
our
reports
have
the
right
data
to
be
able
to
implement
this
somewhere
else.
E
It
I
do
have
something
that
goes
into
that
question
and
the
answer
or
the
answer
to
that
right
now
is
not
always
because
you
know,
sometimes
our
findings
get
out
of
sync
out
of
date
right
so
they're
like
they're,
pointing
at
the
wrong
place.
I
I,
don't
know
that
we
necessarily
need
to
bring
solving
that
into
this
into
this
particular
problem.
But
it's
you
know
something
to
be
aware
of.
I
mean
you
know.
A
If
the
file
location
moves
and
we're
talking
about
from
so
you're
talking
about
tracking
findings
as
their
location
moves
over
time,
yeah,
okay
I
will
live
dangerously
and
assert
that
if
we're
talking
about
a
merge
request
workflow,
then
that
is
not
a
concern
here.
If
we're
talking
about
providing
a
remediation
from
a
finding
from
a
security
dashboard,
I
would
argue.
H
H
Maybe
it's
already
exposed
I,
don't
know.
The
link
is
probably
the
biggest
question
that
maybe
that's
already
available
in
the
EM,
our
widget
and
it's
just
they
just
need
to
put
all
the
pieces
together
to
create
a
link.
I
would
think
that
there
need
to
be
some
API
or
some
exposing
to
the
template.
Okay,.
