►
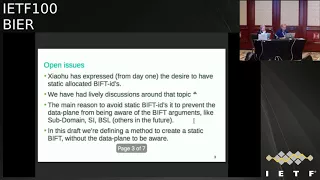
From YouTube: IETF100-BIER-20171114-1550
Description
BIER meeting session at IETF100
2017/11/14 1550
https://datatracker.ietf.org/meeting/100/proceedings/
A
B
All
right
welcome
to
beer
I'll
bring
the
slides
up
here
in
just
a
second
before
we
get
rolling.
As
always,
we
need
someone
to
take
notes
for
us.
We
need
a
minute
taker
and
as
cruel
as
I
am
you
know?
If
someone
makes
eye
contact,
you
get
selected
Pepper's
looking
down
read
an
email.
I
saw
that
I
saw
I
contact.
Nothing.
Someone
please
help
out
here.
It's
a
great
way
to
participate,
contribute
well
sing.
Songs
about
you
and
tell
stories,
would
be
legendary.
I.
B
E
B
A
F
B
B
B
B
We
get
the
charging
discussion
will
discuss
recharging.
Yes,
it's
on
that
book,
peace.
We
you
and
I
talked
about
it
already
aside.
I,
don't
think
we
need
to
bring
it
up
now.
That's
alright
anything
else,
missing
anyone's
name,
McCann
misspell.
Anything
I
can
butcher
here.
Numbers
I
can
get
wrong
dates.
B
G
So
as
most
of
you
know,
so
we
had
that
at
extension,
discussions
about
encapsulation
right
sometime,
back
MPLS
versus
now
MPLS,
and
what
do
we
do
and
we
first
defined
MPLS
encoding,
and
then
we
did
still
pulling
the
done
MPLS
encoding
for
us
it
was
always
the
goal
to
make
those
two
encodings.
You
know
the
same
as
possible
as
much
as
possible
right
to
make
Hardware
not
you
have
two
different
things.
G
So
there
was,
you
know
one
of
the
big
goals
for
encapsulation
I
think
we
succeeded
in
that,
so
we
do
have
MPLS
and
on
an
MPLS
specific
encoding
in
the
in
the
draft.
So
we're
not
going
to
talk
about
that
trailer
next
slide.
So
there
was
still
one
open
issue
that
see
how
you
know
has
been
off
there
for
a
long
time,
and
that
is
the
desire
to
have
aesthetic
assigned
b
fi
v
fi
t's.
G
Now
we
always
sort
of
pushed
back
on
that,
because
we
didn't
really
want
to
overload
the
data
plane
with
too
many
arguments.
Like
you
know,
said
identifier
subdomain
basing
length,
because
this
should
not
be
properties
that
you
know
part
I
should
actually
have
to
look
at.
So
that's
the
reason
why
we,
actually
you
know
we're
sort
of
you
know,
didn't
want
to
do
that,
but
still
there
is
for
the
non
MPLS
encoding.
They're
still,
you
know
good
requirement
to
have
such
a
feature
that
you
can
statically
define.
G
G
G
What's
really
important
is
that
for
the
data
plane
they
should
not
actually
look
at
those
values
individually,
that
you
just
look
at
this
as
a
20-bit
value.
They
look
up
and
find
the
biffed
ID
right
and
and
do
your
forwarding,
so
that's
why
we
really
say
you
know
in
this
draft
that
you
know,
data
plane
must
not
perished.
It's
this
field
to
be
wrong
to
do
next
slide
now,
so
some
of
the
benefits
of
the
static
gift
idea
is
that
you
know
if
you
hard
code.
G
It
then
there's
no
need
to
advertise
this,
so
that
does
simplify
your
network
quite
a
bit
also,
so
you
know
it's
a
globally
unique
value,
so
it's
also
easy
to
troubleshoot
right.
That's
what
you
see
like
in
in
a
segment
routing
area.
They
they
do
that
as
well.
You
know
having
statically
defined
label,
sorry
the
same
from
up
to
hop,
so
it's
a
bit
easier
to
troubleshoot
and
follow
the
path
name.
G
H
G
G
That's
like
now,
so
so
we
how
to
do
that
because
discusses
oakum
among
you
know
several
people
for
a
bit,
because
in
a
way
you
know
you
can
put
any
value
into
this
20
bits
and-
and
the
question
is
like
the
world,
do
you
need
to
write
a
draft
for
that
now?
We
still
think
it's
good
to
do
that,
because
you
can
still
you
know,
encode
those
values
in
two
different
places
in
those
20
bits.
So
we
still
think
that
cell
you
actually
in
documenting
how
to
do
that.
G
J
G
G
K
K
I
G
K
B
Yes,
as
chair
is,
this
is
you're
interested
in
for
adoption.
Oh
absolutely
yeah,
so
who
in
the
room,
has
read
the
draft?
How
many
of
you
then
think
this
is
something
that
we
should
adopt
in
the
working
group?
That's
an
item.
Okay.
Anyone
think
this
is
should
be
kicked
to
the
curb
all
right.
We've
solid
consensus
in
the
room.
Take
that
on
the
note
and
we
will
take
it.
The
list
like
thank
you.
L
So
human,
with
goalie
Nokia
I'm
here
to
present
the
p.m.
signaling,
this
draft
was
previously
called
team
tunneling.
It
was
creating
a
some
confusion
because
of
the
name,
so
we
change
the
name
of
the
draft
from
tunneling
to
signaling.
Since
then
we
got
some
feedback
from
Jeffery
and
some
other
players
I
like
to
thank
you
for
that.
I
tried
to
upload
the
new
draft
with
the
name
of
the
people
that
contributed
to
those
feedbacks.
Unfortunately,
I
was
a
little
too
late,
so
on
the
next
one.
L
L
One
thing
that
keeps
coming
out
over
and
over
again
is
the
fact
that
how
we
can,
if
it's
not
a
green
field
deployment
of
the
beer,
how
we
can
kind
of
inter
connect
beer
to
some
of
the
legacy
and
VPN
or
PIM
type
of
services-
and
this
is
what
this
strap
is
trying
to
solve.
So
basically
most
of
the
providers
out
there.
They
have
multiple,
be
use
or
multiple
segments
of
the
network.
L
Core
access
etc
and
what
we
are
seeing
right
now,
the
traction
is
that
they
want
to
upgrade
their
core
with
to
a
next-generation
core
where
they
call
a
clean
core
or
a
lean
core,
or
they
need
a
single
IGP
protocol.
They
don't
want
to
make
the
core
too
complicated,
with
multicast
protocols,
whether
that's
p,
m--,
IGMP
or
any
other
MPLS
type
of
protocol,
which
is
ml,
DP
or
point-to-multipoint
rsvp-te.
They
just
want
to
run
one
single
protocol
IGP
and
make
multicast
work
under.
L
L
So
here's
a
typical
Network
one
of
the
example
of
the
network
that
we
see
so,
as
you
can
see
here
in
the
core,
we
have
beer
and
it's
only
beer
with
IGP
under
access.
We
have
ping
domain
so
on
the
ping
domain,
all
the
routers
they
talk,
pin
with
each
each
other
and
actually
create
Pima
Jason,
see
on
the
pin
domain
that
p.m.
adjacency
gets
terminated
on
the
beer
boundary
router,
the
B
be
ours
from
that
point
on.
L
If
the
SG
is,
if
the
B
be
our
kind
of
determines
that
the
SG
needs
to
go
to
the
other
side
of
the
beer
domain,
it
will
signal
that
as
G,
whether
it's
a
joint
or
the
prune
to
the
other
side
of
the
beer
domain
to
the
other
PBR
that
other
bbr
grabs,
the
beer
packet
removes
a
beer
header,
looks
at
the
signaling
whether
it's
join
or
prune
and
kind
of
pushes
that
signaling
back
into
the
p.m.
domain
toward
the
source
of
the
multicast.
L
So
all
the
changes
in
this
draft
to
be
clear
is
from
signaling
point
of
view
on
the
data
path.
It's
really
what
we
did
previously
from
pin
point
of
view.
So
when
the
sorcerer
starts
sending
multicast
packets
in
this
case
you
know
IP
multicast,
environment,
it
gets
to
the
BB
R
and
the
BB
r
just
puts
it
into
a
beer
header
and
shoots
it
through
the
beer
domain
to
the
axis
and
on
the
axis.
The
other
bbr
removes
a
beer
header
and
forwards
a
packet
as
it
was
done
previously
in
a
beer
type
of
environment.
L
Next
slide,
please
so
again.
To
sum
this
up,
when
it
comes
to
the
implementation
of
this,
we
are
not
trying
to
reinvent
the
wheel,
there's
already
RFC
out
there,
68
26,
which
is
in
bad
ml,
DP
signaling,
which
is
basically
doing
the
same
thing
with
Pym
and
MLB
P,
and
we
are
trying
to
bring
that
technology
into
the
beer
domain.
Also,
it's
nothing
new,
it's
another
I,
guess
a
new
real
invention.
L
All
the
changes
are
from
control
plane,
point
of
view,
as
I
mentioned
previously
I'm
not
going
to
go
through
it
again
and
when
it
comes
to
the
ASM
and
SSM.
At
the
moment,
we
are
concentrating
on
the
SSM
from
ASM
point
of
view,
the
same
thing
with
RFC
68
26.
We
feel
that
it
just
kind
of
work
order.
It's
going
to
be
some
corner
cases
or
not.
We
need
to
investigate
that
a
little
bit
farther
and
see
what
we
need
to
do
from
the
ASM
point
of
view.
L
Next
is
like
please
so
from
the
beer
header
point
of
view.
From
signaling
point
of
view,
there
is
not
much
changes.
One
of
the
changes
that
we
did
from
the
previous
strap
is
we
changed
the
protocol
again
Thank
You
Jeffrey
from
Team
protocol
to
ipv4
and
ipv6
I.
Think
the
reasoning
behind
that
was
that
on
the
BB
R,
when
we
get
the
beer
header,
we
need
to
examine
the
payload
anyway.
L
So
when
we
examine
the
payloads,
we
realize
it's
a
team
packet
given
the
IP
protocol
or
the
destination
the
multicast
destination
IP
address,
so
we
extract
the
PIM
packet
signaling
packet
for
processing
on
the
on
the
corresponding
module.
If
you
will
so
nothing
new
here
from
beer
header
point
of
view,
thanks
a
slide,
please
so
again,
one
of
the
things
that
we
kind
of
had
discussions
with
was
how
do
we
determine?
Where
is
the
other
bbr,
which
is
on
the
path
to
the
source?
L
So
if
you
will,
when
the
PIM
signaling
comes
to
the
ingress
PBR,
somehow
I
need
to
figure
out
what
is
the
next
PBR
that
is
closest
to
the
source.
We
feel
that
there
is
a
lot
of
way
to
solve
this
issue
at
the
moment.
The
draft
has
left
it
wide
open
how
we
can
solve
this
issue
going
forward.
There
are
some
ideas
and
discussions
that
we're
going
to
implement
or
we're
going
to
put
into
the
next
version
of
this,
but
just
to
give
you
some
of
the
example.
L
If
it's
a
single
IGP
area
and
be
you're
kind
of
the
beer
edge
router,
they
kind
of
flood
their
beer,
ID
I
GP
to
every
other
B
router
out
there,
then
we
can
actually
use
C
SPF
type
of
calculation
to
figure
out
where
the
VBR
edge
routers
are
when
we
are
trying
to
resolve
those.
Another
idea
is
that
if
the
beer
boundary
router
is
a
B
R,
which
is
generating
the
route
aggregating
the
routes,
we
can
use
the
source
field
in
the
IGP
TLV.
L
If
you
will
to
actually
resolve
that
BB
r
again,
there
are
other
methods
to
do
that.
Static
routes
ibgp.
So
this
is
one
of
the
areas
that
there
can
be
many
depending
on
the
provider.
That
can
be
many
ways
of
resolving
that
baby
R
and,
as
I
mentioned
on
the
next
graph,
you
can
have
more
details
on
it.
It's
a
slight
please!
L
So
at
the
end,
some
of
the
things
that
this
draft
will
solve
is
obviously
tries
to
bring
beer
in
the
already
existing
multicast
environment,
which
is
non
Greenfield
deployment
in
incremental
matters,
starting
with
the
core,
and
eventually
they
can
evolve
to
the
access.
Another
thing
is
that
it's
going
to
solve
the
multicast
states
that
we
are
seeing
some
of
the
larger
operators
out
there
in
the
core
routers
when
it
comes
to
the
multicast
estates
and
or
Phi's.
L
Obviously,
as
these
networks
are
growing,
we
are
kind
of
running
out
of
resources
to
have
all
this
oil
or
files,
and
you
know
multicast
estates
and-
and
the
last
thing
is
I
guess
from
the
BGP
point
of
view,
because
you
remove
the
need
of
the
BGP
in
the
core
of
the
network,
a
clean
core,
then
when
it
comes
to
the
BGP,
address,
family
and
reaps
and
so
on,
and
so
on,
your
core
becomes
offloaded.
So
you
can
use
that
memory
for
other
type
of
implementation
that
the
router
needs.
I.
M
L
So,
as
I
said,
to
figure
out
where
the
VBR
is,
there
are
many
methods
to
do
that.
So
some
of
the
operators
that
we
talked
to
they
just
want
to
run
a
single
IGP
in
their
core.
They
don't
even
want
it
run
BGP
if
they
run
BGP.
That
means
they
want
to
run
MP
BGP
between
PE
to
PE,
because
they're
doing
dry
frozen
or
some
kind
of
nvm
VPN
type
of
service.
L
So
in
that
case,
because
BGP
is
between
the
two
end,
routers
then
in
the
core,
the
BGP
packets
are
just
any
IP
packets
and
those
be
BRZ.
They
don't
need
to
track
the
BGP.
If
you
will
rip
or
fit
for
that
matter.
Does
that
make
sense?
Or
maybe
we
can
go
to
another
slide?
I
can
explain
it
a
little
more
in
detail.
M
N
B
M
So
in
that
case,
I
think
the
same
mechanism
can
be
used
directly
for
the
overlay
signaling.
So
basically
you
can
just
do
the
today
with
Rosen
MEP
and
you
you
essentially
have
team
joins
in
the
overlay
between
the
Pease
and
now
I
think
you
can
turn
you
can
use
beer
to
carry
those
team
signaling
in
overlay.
So
what
I'm
trying
to
say
you
could
make
this
mechanism
generica
so
that
it
can
be
for
post
provider
tunnel
signaling
and
for
for
the
overlay
signaling
as
well.
M
G
Cisco,
so
we
had
some
offline
discussions
on
this
before
the
meeting
right,
so
it
was
good
so
just
to
move
for
the
record
state,
maybe
if
the
things
that
shows
updated,
yeah
so
different
to
say
it
for
the
record.
A
few
things
that
we
talked
about
so
so
discovering
the
bbr
is
key
to
the
whole
solution.
So
that
was
my
point
that
that
that's
not
out
of
scope
right,
so
the,
although
the
mechanisms
need
to
be
well
defined.
So
everybody
knows
how
to
implement
so.
G
The
one
minor
concern-
and
that's
maybe
unit
unica's
guys
can
maybe
pitch
in
here.
So
one
of
the
solutions
is
to
use
the
originator
of
the
LSA
write
as
the
to
figure
out
that
that
is
the
PBR
right.
We
injecting
the
doing
summarization.
So
the
guy
who
exercises
sunrise
routes
that
origionally
originator
ideas
used,
as
you
know,
for
routing
as
the
to
figure
out
what
the
BB
are.
I'm,
not
sure
if
that
is
a
new
way
that
is
I,
never
seen
that
used
before.
L
K
O
Let's
say
if
you
have
like
rudders
a
and
B
connected
to
the
source,
then
one
rod,
room
on
the
receiver
end
might
join
to
a
another
router
majority
B,
it's
above
a
and
B
end
up
forwarding,
but
you
might
want
them
both
to
choose
either
A
or
B.
So
I
think
how
we
choose
right
to
Senate,
pin
join,
might
be
more
complex
or
you
may
not
want
to
do
it
in
a
different
way
than
just
looking
at
the
usual
kind
of
shortest
path.
P
K
Nokia
do
not
disagree.
I,
however,
I
would
disagree
where
we
should
be
documenting
things
like
that.
That's
a
general
beer
problem.
You
would
you
you
would
think.
Similarly,
where
we
didn't
define
in
other
multicast
technologies,
we
left
to
the
you
know
the
protocols
that
do
this
election.
So
this
is
a
good.
This
is
a
problem
to
have
problem
to
solve,
but
is
this
the
place
or
should
we
use
this
from
other
place?
K
O
So
I
will
say
you
know
I
partially
agree
with
what
you
said
earlier,
that
you
wanted
to
keep
somebody's
out
of
the
document,
because
there's
multiple
ways
of
doing
this
and
part
of
my
point
is
that
yeah,
it
seems
obvious
to
do
the
shortest
path
whatever.
But
maybe
you
want
to
do
something
else
in
some
cases,
even
though
maybe
you
don't
want
to
specify
everything
in
this
document,
it's
nice
to
X,
plus
the
problem
a
little
bit
and
I'll
see
you
added
some
text
for
that
already
I.
J
L
So
if
the
Corps
decides
to
spend
some
money
and
upgrade
the
core
to
a
next-generation
core
which
uses
beer,
maybe
then
the
access
as
an
example
of
wireless
access,
which
is
completely
a
different
bu,
they
might
said
we
do
not
want
to
change
our
multicast
as
of
now,
we
might
want
to
have
that
ten
years
from
now.
So
these
are
the
type
of
problem
we
are
seeing
that
in
one
of
these
be
use
they
want
to
go
to.
The
next
know.
J
I
mean
if
you,
if
you
really
have
the
you
know,
the
piece
are
operated
by
a
different
department
from
the
piece
that
that
that
is
very
persuasively.
So
do
you
have
a
real
example
for
the
first
one
for
the
twenty?
Fifty
six
is
not
good
enough
replication
is
that
is
their
hard-won
well
mobile,
backhaul.
L
L
Okay,
and
when
you
look
at
so
in
mobile
backhaul,
the
multicast
is
called
en
VMs
as
I'm
sure
everybody
knows
so
when
you
start
doing
in
VMs
type
of
services
with
this
next
generation
multicast
with
beer,
oh,
the
replication
could
be
an
issue,
especially
in
mobile
backhaul.
When
you
go
to
the
5gm
you're
talking
about
some
of
these
services
with
4k
downloading
of
IP
tvs
or
whatever
that
they're
trying
to
bring
into
the
into
the
market,
it
becomes
a
big
problem.
L
B
N
N
Okay,
so-
and
so
you
see,
is
the
Monte
Casa
de
portago,
so
obvious
in
attendance
of
Bureau
PFD
should
have
be
based
on
the
FD,
a
mighty
point
draft.
So
so
we
were
use
demand
Emoto,
and
this
is
the
based
on
the
artists,
a
pharaoh
I've.
Fifty
fifty
eight
eighty,
and
so
there
is
no
three
three
away
and
the
fixed
for
the
PR
on
the
shooter
used
source
address
and
mighty
screaming
with
her
to
the
minus
alpha
T
sessions
so
forth.
N
Stars
of
the
dress,
if
with
undernea
network
is
MPR's
wasting
intelligence
also
dress
is
we
have
our
idea
and
enhance
table
and
you,
food
under
nail
network
is
non
empty,
our
network,
so
the
source
address
is
therefore
our
ID
and
we
offer
I
chi
ID.
Okay,
this
is
and
next
step.
Nancy
is
the
fury
capsulation.
N
So
as
we
know
that
the
purity
caps
a
nation
is
a
defined
in
the
real
MPIC
determination
draft
and
then
if
it's
a
protocol
further
happen
where
the
venue
is
file,
so
the
pain-
oh,
that
is,
oh,
am
I
Noda,
so
we
were
use
this
lamp
in
order
to
or
defend
the
FDA
control
and
control
packet,
so
we
were
defined.
The
bureau
am
hacking.
The
format
in
this
document
annotation
Angela,
as
the
petitioner
shows,
where
defend
way
further.
This
is
the
Sanford
version
and
also
the
message
type.
N
So
it's
a
defender,
om
or
taco
before
it
is
a
PFD.
So
so
you
know
om
control.
Packet
of
failure
is
a
bureau
deputy
packet
and
also
we
defended
phonetic,
fair,
so
it'll
well,
usually
also
optional,
chemistry,
chemistry,
immunity
under
how
we
should
a
retention
data,
Bureau,
I'm
hodda,
so
can
user
to
the
next
om
or
tortoise.
So
we
used
I'm
message
attack
so
wasting
data.
N
For
my
point
that
pair
we
don't
need
a
tool
for
the
the
multi
point
of
tell
no
no
I
needed
the
IP
UDP
port,
who
identified
the
PDF
of
the
packet.
So
this
is
a
pure
PFD
consolation
Lannister!
Oh,
this
is
the
put
a
strap
for
the
beauteous
session.
So
wait
you
find
a
two
ways
to
put
astraphobia
of
the
Appetit
session.
N
So
first
one
is
one
hopeful,
but
it
stretching
the
we
can
use
the
is
as
the
PFD
and
chair
way.
So
just
is
the
defender
in
our
say
secret
just
here,
so
that
your
to
certain
and
Tonetta
is
a
deputy
in
a
board
chair
way
format.
So
I'm,
I'm,
G
idea
further
uses
a
pyramid,
a
technology
identifier
and
an
RPI
D,
and
we
suggest
that,
and
so
when
you
award
an
RPI
D
to
be
a
standard
as
say
two
for
Pia.
N
I
So
since
I'm
confer
Gregg
Mirsky
as
it
II,
we
discussed
that
and
of
course
this
is
an
option
and
something
that
for
us
as
a
group
to
discuss,
but
just
trying
to
be
minimalistic.
Why?
Because
it
seems
as
a
duplication.
So,
yes,
we
have
not
directly
address,
but
indirectly,
we
do
know
the
source
of
BFD
control
packet.
M
M
I
There
is
very
good
topic
for
discussion
because,
since
I'm
involved
in
our
other
OM
related
proposals
in
there
that
used
the
assumption
that
bfr
ID
identifies
the
source,
for
example,
MTU
discovery
does
that.
So
if
there
is
some
possibility
and
plans
to
decouple
that
it
will
be
good
to
have
this
discussion
and
then
we
can
have
take
appropriate
action
in
the
protocol
side.
But
thank
you
for.
D
Bringing
that
Oh
Greg
Tony
Pete
River
operationally.
How
do
you
imagine
this
is
being
used,
so
the
d-max
is,
as
far
as
I
see
first
sub
domain
right
because
you
use
the
bfr
ID.
So
you
run
this
per
sub
domain
now,
obviously
the
overlay
doesn't
use
that
or
do
we
imagine
every
overlay
using
their
own,
multiple
eft
or
is
it
the
operator?
But
it
is
the
operator.
Then
how
will
he
know
which
set
to
run
is
bfd2
and
how
is
the
different
from
having
the
beer
ping,
which
we
already
have?
I
D
I
How
you
can
run
okay?
It
depends,
you
know.
If
we
look
for
development
of
BFD
implementations
that
originally
they
were
probably
software
based
and
then
we
got
it
more
and
more
in
a
hardware,
assisted
manner
and
scaling
is
enormous,
so
here
I
think
that
it
would
be
interesting
question
to
discuss
what
really
want
to
monitor
and
how
to
monitor
whether
it's.
I
I
I
need
to
point
out
that
BFD
for
the
multi
point
to
point
to
multi-point
BFD
does
not
allow
route
to
monitor
end
point.
It's
vice-versa.
It's
other
way
around.
It's
an
end
point
monitors
the
route
because
it's
unidirectional
and
arm.
Yes,
there
is
an
X
version
of
BFD
with
what's
called
active
tails,
which
will
be
at
least
now
plan
to
be
published
as
informational,
where
the
tail
can
inform
the
head,
which
is
the
route
in
our
case
that
it
doesn't
see.
I,
don't
see
you
right,
but.
D
D
K
K
K
So
the
the
dangerous
with
things
like
this
is
they
become
standards
and
then
people
try
to,
and
then
we
we
being
pushed
to
implement
that
for
a
sake
of
implementing
that
and
then
extending
this
for
a
sake
of
extending
it
for
every
single
multicast
group
in
the
network
and
before
you
know
it,
yes,
then
we
have
enormous
scaling
and
by
the
way
nobody
wants
to
pay
for
that
so
way,
and
then
people
complain
that
they
get
is
to
come
to
complex.
So
now,.
D
But
jumping
on
the
other
hand,
I
have
to
say
that
from
customer
size,
B
or
beer
o
am
is
considered
as
a
very
interesting
property
of
the
technology.
In
the
case
of
the
operational
model,
I
think
there
will
be
something
people
will
be
willing
to
pay
for
well
scale
and
he's
good
to
do.
But
that's
what
I'm
asking
rats
that
an
operational
model
we
want.
We
want
to
do
because
I,
don't
think
that
will
scale
just
like
enter
said.
Okay,.
I
I
Egress
monitor
ingress
that
determines
their
model,
then
basically
you're
monitoring,
each
ingress
that
you're
interested
and
then
you
can
have.
For
example,
one
was
one
protection
and
you
can
switch
to
another
ingress
if
you
want
to
okay,
but
I,
agree
that
let's
discuss
it
on
a
mailing
list
possible,
applicable
or
use
of
this
method,.
D
G
I
Cisco
just
just
want
to
make
one
point
about
the
scale.
So
today,
if
you
want
to
do
BFD,
you
have
to
do
it
over
a
point-to-multipoint
LSP
right
now
with
beer
there
are
no.
There
is
no
LSP
State,
so
the
skills
gonna
be
better
than
what
we
do
today
right
because
there's
no
trees,
so
it's
gonna
be
per
ingress
and
not
per
tree.
K
O
Stick
with
us,
so
yeah
I'm.
Imagine
if
you
are
doing
this
in
the
under
way,
and
basically
someone
wants
to
monitor
the
the
physical
infrastructure
or
whatever
in
the
beer
domain.
Then
they
don't
really
know
where
the
ingress
is
gonna,
be
and
I'm
afraid
this
one
scale.
If
you
want
to
potentially
have
every
single
beer
out
or
being
a
potential
ingress
router,
because
then
you
end
up
with
every
every
beer
out
or
having
to
monitor
every
separate
potential
ingress
router.
If
you
do
it
in
the
overlay,
then
you
might
know
who
is
the
ingress
router?
I
B
K
Maybe
you
and
your
dog
are
maybe
want
to
come
and
Greg,
because
I
I
left
lift
hand
once
not
twice
and
we're
talking
here
about
in
some
other
the
drafts
about
extending
beer
quite
to
their
access
devices.
You
can
have
a
DDoS
attack
with
that.
As
soon
as
you
go
that
deep
you
can.
You
can
DDoS
attack
because
you're
going
from
a
lot
of
ingress
points
to
an
ingress,
so
I
think
we
need
a
little
bit
of
a
security
section.
20.
Q
Good
afternoon
I'm
Sandy's
I'm
from
the
EE,
the
first
patron
phishing,
is
for
peer
in
ipv6.
We
have
caused
our
honey
and
the
at
first.
The
motivation
of
disruption
is
used
to
elements
lack
home
net
and
maybe
some
small
network.
The
network
may
not
have
had
worse
part
of
a
peer,
encapsulation
and
purus,
or
even
support
for
special
internet.
Have
we
know
that
the
PR
unit
has
not
been
defined
yet,
and
the
native
ipv6
encapsulation
for
PR
Hopa
Hopa
boarding
in
pure
ipv6
elements
allow
to
process
peer
in
the
slow
path.
Q
So
the
solution
is
very
simple
and
let's
see
the
ipv6
header,
the
destination
of
the
packet
are
issued
to
the
neighbors
link
local
address.
Maybe
we
can
use
a
loop,
a
ping
interface
at
us
when
we
use
the
web
interface
address.
The
other
chest
should
be
the
same
as
the
neighbors
pfr
prefix.
The
source
of
the
packet
should
be
one
of
the
BFI
us
loopback
interface
address,
and
it's
also
and
should
be
the
same
as
the
PFI
OSPF,
our
prefix,
the
TTL.
P
Q
The
pure
header
is
aligned
with
the
former
defending
here
in
PRS
encapsulation
for
now
and
purest
version.
So
we
know
that
to
the
east
and
the
TCPS
have
no
less
significance
here
and
the
PFD
ID
is
also
the
combination
of
subtle
man
set
identifier
and
the
beats
jinglun's
we
met.
The
remaining
fields
are
unchanging
with
and
PR
umpires
encapsulation
dropped.
M
N
Q
One
way,
if
you
want
to
use
unicast
that
connect
ingress
replication,
you
can
do
it,
but
if
you
can
use
Union
use
the
most
Acosta,
you
can
use
this
function,
yeah
so
I
think
the
efficiency
of
ingress
replication
and
the
F
inches
of
this
structure
may
be
the
same
and
the.
But
in
some
situations
it
may
be
the
difference.
So
we
think
that
we
can
provide
any
ways
to
implement,
achieve
the
result
so
operator
or
anyone
can
choose
the
function.
Yeah.
M
Q
M
D
Okay,
I
have
a
question
from
the
from
Jabbar
from
one
nine
two,
two,
eight
five,
seven,
seven,
six,
three
six,
oh
I,
see
this
I
see
me
Jewish.
Why
is
restricted
to
link
lock
Oh
and
what
happens
if
you
extend
it
across
multiple
ipv6
next
hops
I
can
see.
Are
humans
both
ways?
Perhaps
you
don't
want
an
encapsulation
specific
tunneling
mechanism.
D
G
Cisco
I
should
have
similar
comment
to
Jeffrey
that,
by
putting
a
knife,
six
Heather
in
front
doesn't
mean
you're
doing
ipv6,
because
the
the
four
and
lookup
that
you
do
to
send
out
the
packet
is
based
on
the
bit
string,
all
right,
so
you
make
it
seem
like
v6,
but
that
there's
nothing
to
do
with
v6
really.
So,
if
you
want
to
carry
v6,
maybe
it's
better
to
do
the
you
know
the
non
MPLS
encoding
and
take
an
ether
type
and
put
it
is
six
packet
reversed
order?
B
As
chair
I
think
what
hasn't
been
address
these
in
the
presentation
is
that
we
don't
have
a
label
or
cap
in
this
environment
and
we
don't
have
a
neither
type
yet
right.
So
we
want
implements
that
get
something
going.
I
think
it's
an
easy
way
to
get
something
moving,
but
you're
right.
This
is
not
v6
and
the
same
way
that,
with
you
know,
in
the
past,
people
try
to
wedge
bits
into
the
v6
header
in
some
way.
B
B
K
You
kind
of
almost
said
remove
my
comment,
but
my
comment
to
that
was
I
would
not
call
it
a
v6
I
would
call
slow
path,
we're
processing
and
things
I
can
do
with
and
then
and
then
yak
things
I
can
do
with
various
headers
to
pound
the
thing
to
software.
You
don't
even
need
to
do
this.
You.
There
is
other
bits
in
existing
ipv6
IP
before
that
will
pound
the
packet
to
a
software
and
as
soon
as
you
have
it
in
software,
there's
nothing
preventing
software
from
having
a
configuration.
D
D
B
R
D
So-Called
fat
option
will
hinge
on
the
fact
whether
the
bebo
home
net
guys
show
interest
in
that
stuff,
because
there
there
is
an
open-source
implementation
on
going
for
a
beer
sensor
for
bebo,
and
if
they
pick
that
stuff
up
home,
it
doesn't
have
a
multicast
architecture
and
that
becomes
inherent
part
and
it's
a
kind
of
an
possibility
to
do
to
get
very
quickly
early
implementations.
So
they
people
comply
with
this
stuff
right.
B
D
B
G
K
And
this
is
you
just
hit
on
Andrew
doggone,
okay,
just
hit
on
my
point.
If
this
is
informational
transitional,
we
probably
spend
more
time
talking
about
it.
Then
it
would
be
to
implement
this
because
it
doesn't
need
interoperability,
doesn't
like
transitional
informational,
we're
not
going
to
be
deploying
this
in
networks
across
multiple
vendors
by
how,
by
the
way,.
Q
Okay,
the
second
presentation
is
for
your
flooding.
Let's
see
the
problem
statement,
it's
a
typical
hybrid
Network,
and
we
from
this.
We
know
that
different
routing
protocol,
Roxie
in
different
region
and
the
even
state
heater
routing
is
used
in
some
regions.
I
am
sorry
about
I
forgot
to
write
some
reading
with
the
stating
of
configuring
route.
You
can
imagine,
and
so
they
are.
There
are
tents.
There
are
only
tens
of
routers
in
every
region
and
even
being
some
region
like
the
figure
below,
without
that,
as
there
is
only
one
hop
wording
in
this
network.
Q
This
is
religion.
So
if
we
want
to
deploy
appear
in
such
network
without
that
from
the
existing
technology,
we
can
use
HP
extension
to
advertise
beer
know
the
information.
So
so
we
can
deploy
several
PR
domain
in
this
network
and
the
the
bottle
route.
Her
must
converted
the
beer
encapsulation
like
such
as
mr3
mr
for
p1,
who
before
must
make
the
beer
encapsulation
commercial,
so
multiple,
PR,
encapsulation
and
decapsulation
functions
will
be
queries,
the
efficiency
of
air
for
early
next
piece.
Q
So
we
we
think
that
if
we
can
merge
several
regions
into
one
period,
so
you
think
that
this
network
is
only
deploy
deploy
with
with
one
beer
domain
so
and
we're
encapsulation
and
decapsulation
times
will
be
decreased
and
the
beer
forwarding
infinity
will
be
improved,
but
a
new
problem
occurred
how
to
build
a
beautiful
wedding
across
multiple
routing
regions
and
I
bought
to
draw
a
picture
with
the
statical
configuring
network.
So
if
we
use
the
existed
IDP
extension
to
do
it,
we
know
that
maybe
we
can
do
some
conversion
in
border
routers.
Q
It's
also
the
mr3
and
before
you
want
to
be
full,
they
must
convert
the
information
and
it
worked
I
said,
and
but
it
may
be
at
some
complicity
in
the
border
with
her
spot.
Etta
I
saw
some
pro
so
some
problems,
but
if
the
region
is
wrong
in
static
configuration
routing,
no
so
there's
no
IP
protocol
running
in
this
region
and
how
can
I?
How
have
we
advertised
the
PR
know
the
information
in
this
rigid?
Q
So
next,
so
we
with
a
lot
who
use
protocol
dependent,
have
flooding
mechanism,
the
PR
know
the
information
can
be
flood
with
him.
Blogging
mechanism
defined
in
p.m.
sauce
is
cover,
be
as
touch
and
the
extension
may
be.
Aligned
with
I
was
PF
of
Isis
or
PTP
extension.
Some
changeable
payment
made
to
adopt
this
function
and
every
note
in
domain
build
a
beer
forwarding
plane
according
to
the
flooding.
Q
We
are
not
info
and
its
own
federal
people
to
build
a
supporting
playing
and
without
the
dependent
of
IDP
or
PDP
role
in
computing,
and
the
fable
is
the
forwarding
information
base.
You
know
that
next
and
I
think
somebody
will
confused
with
destruct.
So
we
make
two
clarification
here
and
this
structure
do
not
want
to
replace
the
OSPF
or
Isis
or
PT
PBR
extension.
Q
This
draft
is
just
a
supplement
of
routing
protocol
extension,
especially
in
hard
with
element
that
we
know
that
appear
eliminates
team
protocol
states
in
Corbin
men,
but
this
job
is
not
bad
for
the
tool
to
say:
oh,
you
must
a
user
pay
me
in
her
network.
We
just
use
the
flatten
function,
define
them
in
ping,
dropped
to
deliver
a
beer
note
the
information.
So
without
this
we
can
we,
we
can
use
another
function
to
flood
the
information
and
we
in
order
to
get
is
the
same
result.
Q
So
we
use
ping
protocol
fool
to
build
as
a
appear
for
it
in
plain,
do
not
means
that
we
will
use,
pin
protocol
to
build
multiple
trees.
So
we
will
not
use
protocol
to
build
the
body
hostages,
and
we
have
some
discussion,
the
mailing
list
with
debris-
and
we
know
such
MFO
some
network
who
is
deployed
with
ITP.
We
can
do
the
IDP
conversion
in
the
bottle
reuters.
So
maybe
we
can
write
another
doctor
for
the
peer
proxy
and
what
has
the
pyramid,
information
and
the
disruptor?
J
Q
J
Q
J
F
Q
Q
K
Remote
yeah
yeah
I
would
like
to
understand
no
use
case
2
because,
okay,
that's
not
true,
this
is
quarter.
163
doesn't
do
this,
169
doesn't
do
it.
China
doesn't
do
this.
We
actually
have
routers
in
those,
so
none
of
them
has
that
so
maybe
some
Metro
I
don't
know
somewhere
a
Chinese
provider
is
done
by
another
provider,
so
they
don't
have
that
problem
either.
So
I
would
like
to
understand
the
use
case,
because
I
would
further
like
collapse.
Your
like,
oh,
like
you
showing
course
PL
like
different
or
SPF
demise.
K
L
L
Q
So
I
only
draw
two
routers
in
in
the
figures
below
there's
tens
of
wrote
her
senior
moment
and
the
peer
domain
3
and
the
edge
router
can
be
the
the
other
parts
in
this
network.
So
if
we
want
to
deploy
and
peer
in
this
network,
the
mr1
and
I'm
r2
and
as
the
other
I
haven't
said,
Jo
Jo
at
all
sure
the
routers
is
bother.
Reuters,
oh
yeah,.
Q
B
So
we're
out
of
time
on
this,
it
sounds
like
what
we
have
and
any
questions
he
coming
up.
So
hips
are
poor,
cut
me
off
towards,
but
the
questions
are
kind
of
going
the
same
direction.
What's
the
environment
here,
what
are
you
doing
for
unicast?
Why
you
looking
a
solution
like
this
there's
this
transitional?
This
is
a
static
environment.
So
we
need
to
better
understand
that.
Maybe
we
take
that
list
and
we
can
expect.
J
B
S
S
This
document
proposes
a
set
of
extensions
to
Bo
encapsulation.
As
you
know,
the
pure
encapsulations,
the
repeal
header,
can
only
carry
one
bitstream
and
so
I
suggest
their
purity
header
can
contains
more
than
one
its
dreams
and
their
modification
is
as,
as
you
know,
their
beauty
is
just
part
of
the
architecture.
The
relation
and
packet
format
with
fear
are
different
ways.
S
Positions
of
the
or
at
adjacencies
passes
through
the
BFF
ir
to
we
have
ears.
The
traffic
engineering
may
be
a
carriage
in
more
than
one
its
dream
so
last,
so
we
just
to
extend
their
bear
encapsulation
and
alley
optional,
optional,
satya,
we
is
carried
in
purity
header.
The
page
indicates
a
beauty
packet
when
it
is
that
it
streams
apt
your
way
at
indeed
finds
the
bitstream
related
information
and
the
bits
and
each
of
strean
stop.
Joey
corresponds
to
a
particular
compilation.
S
The
first
one
is
their
sub
T
are,
we
is
carry
duress
psi
BSL
information,
they're
dirty
package
will
carry
more
than
one
bit
strings
up
Joey
and
the
end
page
indicates
that
there
are
more
than
or
more
one
or
more
bit
strings
up.
Shall
we
immediately
preceding
dirty
away
when
it
is
that
the
repeat
string
is
off
arrival
as
the
and
that
defines
their
connection
of
the
distances
from
PFI
are
to
OPF
years.
S
The
the
second
format
is
to
set
their
PPI
FG
ID
instead
of
the
SDS
FSL
compilation,
because
they
are
where
they
are
mapped
from
sd
as
I
BSL
and
it
is
assigned
from
their
computer,
and
it
really
represents
a
particular
date
index
forwarding
table
yes
that
nest.
This
is
a
example
purity
forwarding
with
bit
strings
up
TR.
We
is
a
simple
example
with
two
bit
strings
up:
gia
waves.
S
Jarrell
is
chill,
there
are
to
be
a
they
have
ears,
so
there
are
two
as
I
as
I
am
RTS
eyes
as
I
stare.
Oh,
and
there
is
one
so
we
must
displayed
there.
Mr.
it
string
to
two
parts
and
their
packet,
you
carry
to
bitstreams
and
they're.
The
number
one
they're
PFI
are
the
replicator
they
are
ever
via.
Fi
are
received
a
package
with
the
two
big
screens
at
joey's
and
a
true
we'll
look
take
low,
carbs
rounder.
S
J
J
The
the
idea
is
primarily
to
I
mean
instead
of
having
two
smaller
bit
strings.
You
could
have
one
longer.
So
is
the
idea
that
each
of
the
bit
string
would
kind
of
be
the
maximum
size
that
I
mean
I'm
I
haven't
I
haven't
worked
with
kind
of
forwarding
plane
for
a
long
time
right
so
I
mean
you
tell
me
if
you
know
in
your
company,
people
have
said
that
this
would
be
a
better
way
to
do.
S
G
Cisco,
so
actually
the
same
comment
as
to
Liz's.
That's
a
the
limit
of,
for
example.
256
bits
is
because
there's
a
maximum
size
that
you
can,
then
she
read
into
memory
and
do
for
then
look
up
some.
So
if
you,
after
support
actually
add
a
teal
V
after
that
data
can
read
in
you
might
as
well
take
a
bigger
mask
of
512.
That's
a
much
simpler
solution
and-
and
you
know,
I'm
parsing
theories
in
the
data
plane
is
probably
not
some
something
we
want
to
do,
and.
I
R
B
B
J
S
Ok,
the
last
presentation
is
about
beauty
forwarding
and
we
coworker
with
China
Unicom
a
China
telecom.
The
document
propose
a
central
of
excitations
to
realize
beauty.
Forwarding
is,
it
is
just
a
suggestion
or
implementation,
including
the
assignment
of
the
paid
positions
to
attach
instances
enter
configuration
of
P
IFT.
S
This
is
a
problem
with
multi-core
si.
This
problem
was
discussed
her
in
the
maining
list.
The
problem
is
that,
after
the
distances
from
p,
fi
are
to
be
fer
is
a
time
for
Marty
/
si
and
the
transit
translate
PFR,
who
doesn't
have
to
given
si
for
a
beard.
A
packet
and
a
to
the
purity
packet
may
be
dropped
in
in
that
PFR.
As
the
figure
shown
there
si
and
splitted
their
domain
into
three
parts,
they
will
can't
they
can't
not
be
transmitted
from
tutor
BFE
ours.
So
the
Lester's
night.
S
So
we
suggested
their
process
for
beauty
forwarding,
there's
step
one.
The
controller
host
will
discover
the
let
worker
topology
step,
two,
the
multicast
of
flow
of
lay
to
determine
what
Marcus
flow
leads
to
be
sent
from
PFR,
to
which
PFA
ours
step.
Three,
the
computer
cause
to
calculate
sir
research
passes
from
VFR
to
every
peers
and
step
for
this
controller
as
I
stir
bits
bit
positions,
including
the
SI
p,
SL,
si
compilation
to
the
urgency,
according
to
the
explicit
a
to
pass
under
the
assignment
method.
S
The
cogniser
bitstreams,
according
to
the
Express
h,
passes
under
their
feet.
Partitions.
The
the
nested
step
is
once
Derby
IFT
under
the
bitstreams
or
poor
was
programmed
into
that
they
did
plan.
Then
durability
package
can
can
be
used
to
forward
to
their
PF
yars.
So
this
is
the
process,
then
the
assignment
of
the
pit
position.
We
suggest
or
suggest
a
dementia
policy
of
the
pit
position
as
following.
S
If
we
have,
if
the
multicast
flow
is
to
send
from
psi
R
to
M,
we
have
ears,
then
we
will
calculate
M
explicit
passes
from
the
AVR,
a
PFR
to
and
PF
years.
Then
we
we
are
assigned
cases
of
SDB
SL
and
si
compilations
and
the
decay
is
small,
then
smaller
than
M.
According
to
their
assignment
policy,
then
we
also
suggest
er
to
surface
policy
is
that
there
are
more
than
one
marked
custard
flow.
We
are
use
the
same
resource
like
SDP
SL
and
the
si.
S
N
S
The
the
master
extension
of
the
configuration
for
VI
ft
is
that
the
BI
ft
is
the
one
some
tomato
for
PFR.
So
before
it
a
it,
is
the
table
indexed
by
si
bit
position.
So
we
extended
this
to
the
table
in
testified,
PFT,
ID
and
bit
position
and
the
BI
ft
is
assigned
by
computer
and
it
is
a
unique
or
in
the
domain
it
indicates.
S
S
Present
the
we,
for
example,
we
can
add
I'm
there
for
the
bit
position
from
VI,
f,
PF,
p,
f,
ir
2
from
to
p
f1,
p,
f,
er,
wonder
pars,
we
can
add
I'm
therapy,
I
F
yeah
pfft,
I
D
1
to
this
part
and
your
P
IFV,
I
FG
ID
is
2
to
the
past
2.
So
this
this
solution,
we
are
saved
her
bit
position
and
there
it
will
current
guaranteed.
Er
SI
is
north.
S
Marty
Custer
much
much
/
s
I
will
not
be
dropped
in
there
transit
transit,
PFR
and
the
last.
Thank
you.
The
example
2
is
based
on
their
example,
one
if
the
remati
cost
of
flow
in
lead
to
be
the
bit
position
of
the
markers
of
flow
needed
to
be
a
dime.
The
based
on
the
mat
caster
flow
1,
then
the
yellow
Nimes,
a
stirrer
pass
older
mark
has
a
flow.
Then
there
are
p
IFT
ID
is
2
and
is
shared
waster
flow
one
we
just
lead
to
as
I'm
there.
S
J
I
guess
the
whole
goal
is
to
have
as
little
s
per
flow
state
right
I
mean.
Obviously
you
will
always
have
for
some
group
of
states.
Other
other
bits
that
you
need
to
do.
The
traffic
engineer
is
kind
of
the
same
softness
that
you
have
in
segment
routing
right,
but
I
think
that
the
focus
should
be
on
optimizing,
that
you
have
as
little
as
possible
stayed
across
as
many
as
possible
flows
right.
So
those
would
I
think
be
the
the
crucial
goals
yeah.
T
Rachel
from
Hawaii
my
connect
as
a
clarification
question,
yes,
is
you
you
have
two
current
Asians:
did
they
have
any
of
the
same
problem
or
just
saved,
observe
different
problem
because
I
my
thinking,
my
fittings,
that
your
first
draft
you
know
already
you
know-
can
solve
the
problem
across
the
different
si.
So
yeah
and.
S
T
E
T
In
our
opinion,
it
has
a
scalability
issue,
because
we
all
know
that
the
the
B
string
sides
are
of
a
one
packet,
the
limits,
so
one
beer,
tea
packet
can
only
travels
through
a
small
area
that
would,
of
course,
it
can
be
solved
by
sending
multiple
packets,
but
just
illustrated
in
the
the
picture
below.
But
in
our
opinion
it
doesn't
look
like
the
complete
end-to-end
traffic
engineering,
so
I
pronounced
work.
Yes,
please,
okay,
yeah!
This
is
tensions
in
our
work.
Our
jobs,
yeah
I,
hear
the
first
thing
that
we
rethink.
T
The
previous
definition
of
si
is
set
identify.
We
think
it
should
be
maybe
better
to
define
as
a
segment
arid
index
in
pure
GE,
so
that
the
number
of
additions
aside
each
bit
position,
including
one
si,
is
not
larger
than
the
value
of
PSAL
or
so
we
defined
some
rules
should
be,
you
know,
be
we
have.
T
Firstly,
a
packet
is
allowed
to
travel
to
multiple
segments,
the
areas
with
some
different
si.
So
to
do
that,
we
should
stack
multiple
pastry
information.
We
don't
you
of
course
belong
to
dependent
s
ice
into
the
warm
packet
header,
but
we
cannot.
We
cannot
allow
it
as
big
as
enough
as
best
as
possible.
So
the
total
length
of
all
the
best
range
that
the
package
can
carry
is
maximum
a
PS
l
4/7,
an
ID
e
6.
So.
T
B
It
there's
no
way
to
know
what
those
how
many
n
destinations
is
going
to
be
and
how
many
headers
need
to
go
there
and
how
many
you
need,
which
one
you
use
when
you
get
there
so
I
think
we're
kind
of
going
down
that
same
challenge,
path
of
scale,
I
mean
stacking
them.
We've
seen
in
the
past
is
not
necessarily
a
viable
solution,
but
we,
we
do
have
a
couple
different
groups
working
on
some
scaling
issues
and
they
have
you
talked
with
them.
If
you
discussed
this.
J
G
J
T
It's
a
similar
to
that
one,
but
we
didn't
define
the
deep,
detailed
information
for
the
information
we
think
it
could
be
work
like
you
know:
MPLS
label
things
like
that.
If
you
travel
through
one
segment
area,
you
can
pop
up
at
you
useless
one
and
then
use
a
new
one,
and
if
you,
if
you
know
the
the
devices
had
were,
has
a
problem
to
condemn
mo
to
to
recognize
the
the
the
the
size
of
the
B
string,
multiple
my
best
ring
information.
T
K
Just
a
quick,
quick,
let's
come
and
do
doggone
okay
I
would
just
say
want
to
underline
what
Greg
mentioned
second
ago.
There
are
groups
working
on
those
statements,
I
think
it's
good,
if
you,
if
you
guys
start
talking
to
people
communicate
this
is
this-
is
a
group
that
really
works
very
well
with
with
multiple
people
working
together
instead
of
like
bringing
just
raw
drafts
without
without
even
talking
to
anybody,
even
they.
T
T
D
So
another
observation
and
the
timing
is
right
to
actually
formulate
what
you
guys
think
is
the
future
direction
we
should
be
pushing
into,
because
the
Charter
would
be
probably
under
some
discussions
right
and
here
the
solutions
are
not
even
the
most
important
part.
It
is
formulating.
The
problems
worth
tackling
in
the
next
generation
are
more
important
to
formulator.
Okay,.
R
R
Firstly,
we
can
see
the
difference
from
the
default
topology
and
the
PMP
to
obligee
for
the
normal
beer.
We
use,
for
example,
like
the
ICP
extension
to
the
beer
and
they
use
the
IDP
default.
Obligee
and
beer
will
have
the
in
the
network.
We
have
the
redundancies
and
loop
butter
in
the
specific
matic
multicast
atrophic.
It
will
select
the
best
of
us
and
butter.
If
you,
if
we
pre
build
the
PMP
panel,
we
can
get
the
we
get
a
bit.
R
Wonky
topology
and
the
wheat
will
get
more
or
less
neighbors
and
in
this
topology
we
have
no
loop
in
the
past
next,
please
so
from
the
figure
we
can
see
that
in
the
topology
and
in
the
photo
blah
G
there
are
four
I
had
the
link
to.
There
are
three
and
if
we
use
the
P
2
MP
channel
as
the
topology
like
the
multicast,
the
tree
r1
as
the
root
and
the
branch
has
the
r1
r2
r3
and
another
Barnes
8
R
1,
R
4,
and
so
our
four
has
no
neighbor
of
r3.
R
R
R
We
were
just
and
the
bitstream
in
the
beer
header
and
the
iraqis
fpm
and
the
we
can
forward
that
click
next
and
this
solution
only
make
manner
change
from
the
p2
MP
and
VPN
and
for
the
normal
Putin
P
I'm
a
peon.
We
used
the
IP,
MSI
or
aggregated
IP
MSI
to
carry
many
SG
multicast
of
traffic,
and
we
it
will
that
make
more
made
wisdom
more
bandwidth
and
because
we
think
that
the
how's,
the
prin,
is
only
carried
at
the
bottommost,
the
PA
just
a
leaf
ve
in
the
I'm,
a
pimp,
UMP
solution.
R
R
R
And
the
previously,
the
I
mentioned
that
in
the
entropy
we
can
use
as
a
in
the
live
live
protection
and
we
can
use
as
a
sickness
number
and
the
one
forwarding
the
package
from
the
source.
A
there
are
two
to
the
r2
and
r4,
and
it
will
impose
a
secret
number
and
for
the
chanting
22p.
It
doesn't
care
about
that
and
in
the
egress
PE
it
will
select
to
avoid
the
the
pathway
layer.
R
L
R
B
But
let's,
let's
move
this
longer,
but
it's
definitely
the
challenge
that
really
understand
what
we're
trying
to
solve
here.
I
think
life's,
as
Andrew
pointed
out,
there's
a
schism
between
architecture,
doc
and
the
intent
here
so
I'd
challenge
to
go
back
and
look
at
that
stuff
takes
us
up
the
list,
bring
some
questions
out
and
see
what
we
get
some
response.
Alright,.
E
B
P
Hello,
everybody
good
afternoon:
I
am
the
Russia's
broadcaster
and
presenting
this
on
behalf
of
my
co-authors,
see
if
we
go
to
the
next
slide,
please.
This
draft
is
in
relation
to
the
use
case
that
describes
HTTP
level
multicast.
So
just
as
a
background,
HTTP
level,
clients
a
benefit
from
the
dynamic
multicast
group
formation
that
is
enabled
by
the
beer
and
the
server-side
nap,
creates
a
list
of
outstanding
client
nap
requests
to
the
same
HTTP
request
URI
and
when
response
is
available,
beer
forwarding
information
is
retrieved
and
used
to
send
the
HTTP
response.
P
So
in
this
draft
we
kind
of
elaborate
this
use
case
and
it
and
introduce
some
requirements
for
a
beer,
multicast
overlay.
So
in
terms
of
requirements
in
you
should
we
propose
to
supporting
multiple
fqdn
based
service
endpoints
to
exist
in
the
overlay
and
also
fqdn
based
service
requests
at
the
network
level
to
suitable
fkd
and
based
service
endpoint
and
using
the
policy
based
selection
also
must
allow
for
multicast
delivery
of
HTTP
response
and
also
provide
direct
path.
Mobility
next
slide,
please.
P
So
in
the
multicast
overlay
operations
we
basics
proposed
a
function
called
path,
computation
element
which
is
responsible
for
selecting
the
correct,
multicast
endpoints.
The
result
of
the
selection
is
a
bare
path,
identifier,
which
is
delivered
to
the
Knapp
upon
initial
path,
computation
request
and
the
path
identifier
is
used
for
any
future
request
for
a
given
URL
based
request,
and
so
here
these
operations
is
elaborated,
more
HTTP
requests
say
sent
by
an
IP
based
device
towards
the
fqdn
of
the
server
defined
in
the
HTTP
request.
P
This
information
is
requested
from
the
PC
and
in
now,
when
new
client
requests,
our
new
client
NAP
request
arrives
at
the
server
the
HTTP
request
looks
is
there
is
still
any
outstanding
requests?
The
client
nap
is
if
there
is
so,
the
client
nap
is
added
to
an
internal
request,
able
or
all
the
requests
can
be
also
suppressed
from
being
sent
to
the
server
and
when
the
server
side
nap
receives
an
HTTP
response.
P
The
NAP
concerns
the
internal
request
table
for
any
outstanding
HTTP
requests,
and
then
it
retrieves
the
beer
forwarding
information
for
the
reverse
direction
for
all
outstanding
ETP
requests
and
it
emits
the
path.
So,
in
terms
of
functionality,
there
are
some
protocol
considerations
basically
nap
to
nap
protocol
nap
to
PC
protocol
and
also
overlay
transport
protocol
for
exchange
of
the
earlier
information,
the
registration
protocol
to
registration
and
tirion
based
services
and
also
content
certificate
distribution.
Protocol
for
HTTP
support,
I
think:
that's!
That's
the
functionality
for
to
support
this
HTTP
multicast.
K
Ndred
organic
SOA.
Thank
you.
First,
two
chairs
to
schedule
something
more
sane
at
the
end,
so
we
finish
well,
can
you
can
you
point
maybe
to
a
little
bit
of
the
documents,
how
they
how
this
works
without
beer,
because
it
seems
that
you're
trying
to
use
beer
for
something
which
great
but
I
would
like
to
a
little
bit
understand
the
other.
You
know
they
use
that
the
existing
thing
how
it
works
before
I
can
comment.
If
what
you're
doing
makes
sense
the.
B
P
J
J
U
G
Sisqó
I
did
it
trouble
to
understand
the
bigger
picture,
but
maybe
I'm
missing
some
some
HTTP
knowledge
here,
okay
good,
so
you
mentioned
PC
element
right
for
path.
Selection,
now,
I
think
that
would
only
work
in
combination
with
with
traffic
engineer
it's
beer
because
you
have
a
path,
but
that
doesn't
mean
that
you
have
routing
State
in
the
in
the
in
the
network
itself.
So
is
this
statistical
tie
to
ability
or
is
there
like
beer
information
in
the
network.
B
I
think
the
gap
here
or
sorry
to
catch
up.
We
were
like
really
ton
of
time
where
you
died
too
I
think
the
problem
is
still.
We
don't
understand
what
the
existing
solution
does
without
beer.
So
if
we
had
that
I
think
we
could
then
ask
them
the
more
intelligent
clerkships.
Alright.
Thank
you.
Okay,
thank.
B
B
As
three
years
from
both
to
RFC
in
in
the
for
team
plane,
so
that's
I
think
that's
substantial
Pat,
everyone
selves
on
the
back
and
let's
continue
to
move
this
up
forward
all
right,
so
we
have
some
other
Shepard
write-ups
coming.
We
have
some
ICP
work
to
get
published
out
and
then
next
is
charter,
so
tour
list
specifically
and
those
others
who
have
published
some
te
Docs
that
wasn't
in
our
initial
charter.
B
So
we
kind
of
held
off
on
that,
but
I'm
talking
to
the
ADEs
I
think
there's
a
lot
of
support
for
going
towards
adding
that
to
the
charters
and
move
forwards.
The
question
is:
standards
track
migration.
Keeping
this
thing
open.
This
is
the
14
plane
I.
Think
we
see
a
lot
of
different
use
cases
coming
up.
We
have
some
om
work.
That's
got
to
be
polished
as
well.
There's
a
lot
of
things
still
to
be
done
here.
What
we've
done
is
built
a
foundation
and
now
hopefully,
we'll
have
castles
growing
on
top
of
that.
B
K
Absolutely
I
think
we
should
move
it
to
standards
and
and
more
so,
we
should
also
actually
show
others
how
not
lightly
people
are
taking
things
like
this,
because
I
think
we
we
spent
quite
a
bit
of
time
and
and
set
a
high
threshold
of
moving
something.
What
are
those
experimental
two
standards,
tonzura.
B
That's
the
justification.
Draft
is
Andrew
and
I
be
working
on
that
okay
I
knew
Peter
the
last
year,
hopefully
soon
we
want
to
get
this
stuff
moving
before
the
end
of
the
year,
because
you
know
holiday
collapse
and
everything
and
then
will
be
run
at
a
time
and
Elise
got
some
personal
agenda.
She
wants
to
get
stamped
off
before
she
goes
on
to
the
big
ad
cloud
in
the
sky.
B
K
No,
no
I
think
I
think
we
I
think
the
standard
move
is
I.
Think
that
question
that's
done,
I
think
we
put
it
to
the
floor.
Few
ideas
back.
We
worked
on
this.
We
we
proven
that
we're
not
going
to
take
it
lightly.
So
we
raised
the
barrier.
We
didn't
say
right
away.
Yes,
yes,
let's
do
it
just
because
we
wanted.
We
brought
the
implementation,
we
brought
vendors.
We
brought
operators
into
the
picture
we
doing
now,
drafts
that
are
driven
by
a
push
to
introduce
this
into
the
networks
in
the
into
real
networks.
K
B
V
This
thank
you
can
see
the
grand
my
hair
now
anyway,
so
to
reach
her
I
want
to
I
would
like
to
her.
Obviously
I
have
great
aspirations
to
get
the
returner
done
well
before
the
next
IETF.
To
do
that
is
going
to
take
some
serious
work
from
the
working
group.
First
there's
the
document
which
greg
has
promised
me
before.
Let's
see
two
weeks,
you
said
so
well
before
Hanukkah
starts
right.
Excellent
I
can
say
that
after
Thanksgiving,
but
that's
seem
a
little
harsh,
but
this
is
the
DA.
V
That's
addressing
me
good
enough
understanding
of
this
and
it's
catching
on
adequately
in
industry
and
for
operators
that
we
see
it
going
forward.
I
mean
it's
not
a
quick
technology
question.
It's
a
business
question
industry
question
get
that
document
we're
going
to
try
and
move
that
through
the
working
group
faster
than
you
have
ever
seen.
If
people
are
happy
with
it,
but
that
means
you're
going
to
have
to
review
it.
V
So
you
know
to
go
along
with
the
Chris
presents
for
the
holidays,
you're
going
to
want
to
have
a
good
review
of
this,
because
I'd
like
to
have
it
done
in
January.
That
will
give
us
time
to
reach
writer
and
then
once
we've
retired,
we
can
do
some
status
updates
status
updates.
Do
you
have
to
go
through
the
process
and
last
call's
intelligence?
We're
gonna,
have
five
documents
or
so
six
document
needs
to
be
status
updated.
So
we
need
to
move.
K
V
Well,
that's
why
wearing
it,
our
team
does
rock.
Thank
you
for
all
very
much
I
mean
this
has
been.
The
work
here
is
really
good
and
I
personally
was
really
excited
to
see
like
the
HTTP
work,
because
it's
an
indication
that
they're
starting
to
be
some
understanding
of
how
this
technology
could
start
aiding
an
application-level
multicast
and
in
a
way
that
we
just
haven't
ever
been
able
to
do.
It's
gonna,
be
really
great.
So
beyond
that
the
TE
stuff
we
Greg
talked
about
I
need
to
hear
what
other
things
should
go
into.
B
K
B
J
And
so
obviously
I'm
not
sure
about
the
whether
this
has
to
do
with
the
routing
in
the
data
center.
But
more
you
know
if
you
look
into
all
the
distributed
applications
in
the
data
center
right
where
they
basically
are
parallelizing
across.
You
know
multiple
devices
and
you
need
to
get
the
same
data
to
five
or.
B
Six
adjacent
nodes
in
the
bomb
tomorrow,
yeah
right:
these
are
the
items
to
think
about
adding
the
Charter
or
the
specific
abroad,
but
you're
all
invited
to
contribute.
Any
more
comments
about
the
direction
sounds
like
we've
got
fairly
solid
consent.
Okay,
who
thinks
we
need
to
keep
the
group
up
and
recharter
towards
opening
up
for
more
solutions
so
who
things
we
shut,
everything
down
and
ship
it?
Nobody
perfect
we're
all
in
consensus
once
again
holding
hands
singing
Kumbaya
who
thinks
we
need
version
2.0
of
a
beer
beer
all
right,
who's,
gonna
help
pay
for
it.
