►
From YouTube: IETF100-LAMPS-20171113-0930
Description
LAMPS meeting session at IETF100
2017/11/13 0930
https://datatracker.ietf.org/meeting/100/proceedings/
A
B
B
B
B
B
The
two
s/mime
updates
are
currently
stuck
on
me.
I
need
to
finish
dealing
with
the
AV
review
comments
with
any
luck.
I
need
to
get
that
done
by
the
end
of
this
week,
and
then
we
can
then
the
Necker
can
sit
on
it
for
a
while
and
and
then
send
it
to
iesg
for
review
with
the
two
of
us
been
alternating,
not
managing
to
not
get
to
this
document.
To
finish
it
so.
C
B
B
B
E
Which
I
hope
to
see
adopted
as
the
beginning
of
a
working
document
for
the
working
group?
What
happened
at
the
sea
a
browser
forum
which
is
the
self
regulating
body
for
the
CIA
industry,
is
we
went
to
mandate
CAA
and
discovered
some
ambiguities
and
in
Felicity's
in
it
in
particular,
there's
this
tree
climbing
thing
we
do
where
we
go
up.
You
know
from
the
first
label
the
parent
label
to
the
parent
label.
Looking
for
CIA
records,
the
way
it
was
specified
said
that
we
should.
E
Additionally,
we
should
do
some
additional
processing
on
see
names
and
D
names
and
be
that
same
tree
climbing
for
those
see
names
of
the
lives.
The
downside
of
that
is.
It
creates
a
really
huge
number
of
lookups
and
it
creates
these
really
that
ambiguity
in
terms
of
which
CAA
record
you
want
to
use.
So
the
C
Bowser
forum
wound
up
adopting
on
inner
Atum.
So
currently
there's
an
erratum
on
CAA
and
says
this
process
seems.
E
So
this
is
a
sort
of
awkward
situation
right
now,
where
the
see
a
browser
form
has
adopted
this
RFC
bossanova
bottom,
that's
held
for
document
update,
so
one
of
the
big
things
would
like
to
do
is
actually
do
a
document
update
that
fixes
that
issue.
What
I
have
done
in
the
ancient
draft
is
rewrite.
How
that's
specified
part
of
it
is
that
the
specification
you
know
try
to
get
into
the
see
name
resolution
when
that's
already
handled
by
RFC
1034.
So
instead
it
kind
of
shells
out
okay,
RFC
1034.
E
I'm
not
sure
what
else
Philip
I
wanted
to
address
in
his
slides
here.
If
he's
ready,
he
can
jump
on
I
wanted
to
flag
one
other
thing
which
the
see
a
browser
forum
wound
up
kind
of
patching
in
which
is
error
handling
so
right
now
the
what's
specified
in
the
baseline
of
elements
is
that
if
you
get
an
error
during
lookup,
you
can
treat
that
as
permission
to
issue
so
long
as
it
wasn't
a
DNS
that
base
yeah
I'm
paraphrasing
it.
E
B
F
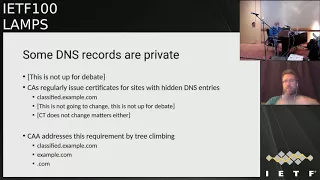
So
the
basic
problem
with
said
you
go
to
the
slide,
to
the
basic
reason
that
we
have
to
do
all
this
bizarre
discovery
thing
is
some
DNS
records
are
not
are
private,
and
this
isn't
something
that
we
can
debate.
They
just
are
and
CA
is
regularly
issued
for
city
hit
cuts
that
can't
be
seen
on
the
Public
DNS,
and
so
that's
why
there
is
the
tree-climbing
algorithm
NCAA,
the
first
problem
in
the
first
place,
and
the
problem
is
that
the
CIA
records
are
intended
to
be
communication
for
the
domain
name
hold
at
the
CX.
F
So
this
is
like
three.
Unfortunately,
DNS
records
are
published
by
domain
name
holders,
so
that
might
be
directly
or
through
a
third
party,
and
so
cname
is
used
to
map
a
set
intent
names
onto
a
single
target.
It's
also
now
used
widely
to
delegate
domain
name
holder
to
a
third
party
service
provider.
So
this
is
what
is
done
by
MX
+
srv4
well
behaved
protocols,
unfortunately,
HTTP
is
not
well
behaved
because
it
was
invented
before
SRB
and
there's
no
MX
record
for
it.
F
So
the
prop
basic
problem
of
the
discovery
is
you
don't
have
the
distinction
in
the
DNS
record
telling
you
why
that
cname
is
that
so
I'm
go
to
slide
4?
The
big
complication
is
that
D
names
aren't
really
DNS
records.
There's
something
else,
they're,
really
a
sort
of
placeholder
that
goes
in
the
zone
file
that
is
used
to
generate
cname
records
on
demand.
F
Only
the
reason
that
it
now
appears
in
on
the
wire
is
because
of
DNS
SEC,
and
you
need
to
be
able
to
say
why
you
synthesized
a
cname,
as
Saudi
name,
appears
on
the
wall
on
the
wire,
so
ca
ca.
A
client
should
be
processing
thee
names
as
part
of
the
seat
name,
validation,
but
only
really
in
terms
of
their
DNS
SEC
validation.
F
So
if
you've
got
an
N,
SEC
3
record
that
says
that
you
should
have
had
a
seat,
D
name,
then
you've
got
to
understand
that
in
your
CAA
code,
if
you've
got
a
DNS,
if
you've
got
a
DNA
record,
that
says
that
the
cname
should
have
been
synthesized.
You've
got
to
understand
that
and
you've
got
your
understand
if
the
C
name
retro
turn
is
valid
and
then
the
C
name
returned
is
invalid.
F
So
those
are
all
things
that
your
code
has
to
understand
about
when
you
do
the
CAA
record
processing
with
DNS
SEC,
but
really
you're,
just
working
off
the
C
names.
I'll
come
back
to
this
in
a
moment.
Okay,
so
one
of
the
big
problems
that
we're
working
around
is
use
of.
C
name
is
restricted,
because
the
idea
is
that
you
are
so.
This
is
slide
number
5.
F
The
idea
is
that
you're
delegating
the
entire
zone,
so
you're
not
allowed
to
have
anything
else
in
a
see
name
in
the
DNS.
So
that
means
that
you
aren't
allowed
to
have
a
phone
that
has
a
cname
and
the
CA
a
record
and
that's
the
thing
that
gets
us
in
trouble,
because
we
have
those
administrative
C
names
that
are
used
for
internal
delegations
and
then
you've
got
those
CD
MD
names
that
are
used
for
external
delegations
and
you
don't
know
which
are
which
and
if
you've
run
the
CDN
case.
F
Well,
you
can't
put
your
CAA
record
at
your
zone
any
so
that
was
what
led
to
the
requirement
that
the
CARF
clients
follows
C
name,
so
I've
got
a
couple
of
use
cases
in
3rd
slide
6,
so
these
use
cases
are
showing
to
see
names
in
series.
So,
first
of
all,
web
example.com
is
going
to
be
name:
WWE
example
calm
and
that's
a
ministry
of
internal
redirect
and
then
we
have
example.com
so
www.example.com
going
off
to
see
the
end
of
example
net,
and
so
that's
the
third
party
redirect.
F
So
if
you
look
at
the
original
algorithm,
this
is
in
slide
7.
This
is
assuming
that
cname
mappings
are
administrative,
and
so
you
have
a
discovery
path.
It
starts
up
great
dot.
Example.Com
ghost
of
WWE
ample
comm
then
goes
off
to
see
the
end
of
it,
and
that's
really
not
something
that
you
would
like
to
do.
F
The
first
two
were
fine.
That's
what
you
want
the
next
one
example
dotnet
that
is
really
bad
duck.
Net
mutts
are
bad
but
irrelevant,
and
then
you'll
go
back
to
example.com
and
then
com,
so
CDN
have
made
the
RFC
eight
six.
Eight
four
four
algorithm
bogus
so
now
slide
eight,
which
shows
what
happens
when
you
have
the
errata
and
basically
this
cuts
out
some,
but
not
all
of
the
bogosity.
If
you
have
web
block
example.com
WWI
example
comm,
you
still
go
off
to
the
CDN
got
example
dotnet.
F
F
So
instead
of
the
algorithm
chasing
see
names
at
all,
we
don't
do
any
of
that
and
instead
the
discovery
path
will
be
web
example.com
underscore
prefix
web,
not
example,
calm
then
WWE
example,
comm
prefix,
the
same
example.com,
prefix
of
the
same
and
so
on.
So
that
means
that
you
don't
end
up
doing
any
bogus
records.
The
only
disadvantage
is
that
you're
doing
slightly
more
rip-rip
lookups,
but
you
know
this
is
ca
work.
This
is
validation.
This
is
really
not
something
that
is
a
huge
deal.
F
So
if
we
go
to
slide
10,
which
is
the
final
month,
I
have
the
remaining
problem,
we
then
have
is
D
name
and
D
name
throws
a
spanner
in
the
works
in
that
the
stick
system
I
just
described,
is
not
compatible
with
DNA
and
there
really
is
no
way
that
you
can
make
it
compatible
and
well
the
solute.
The
only
solution
that
I
can
think
of
is
you
just
tell
people
not
to
do
DNA
the
problem
with
D
name.
Is
that
you're
not
like
any
records
underneath
number
one
and
number
two?
F
F
E
E
In
terms
of
adding
the
prefix
records,
there's
two
things
I
wanted
to
discuss.
You
know
one
Phillip
suggested
that
you
know.
If
we
implemented
this
prefix
algorithm,
we
wouldn't
actually
do
rap
MC
names,
I.
Think
that's
the
wrong
approach
to
take
I
think
the
problem
with
RFC
6844.
Is
it
tried
to
reinvent
the
basics,
you
name
semantics
for
self
and
pressed
by
different
processing,
I
think.
Whatever
result
we
want,
should
you
know,
follow
normalcy,
name,
semantics.
E
So,
in
other
words,
if
you
look
at
web
example.com
using
your
recursive
resolver
you're
gonna
get
back
a
result
that
includes
following
the
cname
chain,
and
you
should
process
that
in
the
normal
way.
So,
in
other
words,
one
of
the
records
you'd
get
back
would
be
from
the
CDN
or
you
know,
whatever
this
cnam
target
is
and
I
think
that's
not
a
missed
feature.
I
think
that's
a
what
you
want
in
that
the
target
of
the
cname
is,
you
know,
that's
the
canonical
name
of
that
domain
and
does
have
some
say
in
what's
authorized.
E
I
think
there
are
some
interesting
questions
here
about
CD
ends,
setting
hostile
records
with
regards
to
their
customers,
but
I
think
that
does
come
down
to
the
relationship
between
EC
the
ends
and
their
customers
at
a
higher
level.
I
think
you
know
there's
this
question
of
you
know:
okay,
we
we
took
four
years
to
finally
implement
CAA
and
production.
E
You
know
we
got
agreement
among
CAS,
it's
actually
out
there
and
it's
live
for
about
two
months
now,
as
of
September,
it's
mandatory
for
all
CA,
so
we're
just
now
starting
to
see
some
of
the
real
world
implementation.
So
I
think
it
would
be
a
mistake
to
fundamentally
change
discovery
algorithm
at
this
time.
E
I
think
one
approach
we
should
probably
take
is
revise
the
RFC
such
that
you
know
we
fix
the
bugs
we
found
and
it
clarifies
how
to
interpret
the
errata
manners
and
that
way
the
cab
format
can
refer
to
a
specific
standard
stock
that
fixes
those
and
then
independently,
pursue
a
more
radical
change.
That's
likely
to
take
more
time
to
get
adopted.
F
Yeah
I'm
not
going
to
problem
with
what
he
said:
people
have
a
use
for
cname
I
got
no
problem
with
that.
I
was
merely
replying
to
precisely
the
set
of
requirements
that
I
had
seen
and
I
hadn't
seen.
Somebody
saying
that
they
wanted
to
see
name
as
well,
so
yeah
following
the
cname
for
1/2
seems
reasonable
to
me.
So
I'm.
Ok
with
that.
F
F
B
B
E
Yeah
so
I'm
the
text
record
thing
I
think
somebody
else
may
propose
that
I'm
actually
in
favor,
of
keeping
the
CA
a
resource
record
type.
It
was
a
little
bit
of
a
pain
at
first,
because
some
networks
reject
it,
but
support
has
actually
been
pretty
good,
so
I
think
there
isn't
a
need
to
switch
the
text
records
for
the
main
discovery,
but
I
think
there
was
some
discussion
around
doing
it.
For
that
underscore
pretext
in
terms
of
like
I
mentioned,
I,
actually
have
a
draft
and
I'm
going
to
participate
and
actually
authorship.
E
There
I
think
the
next
formal
step
IETF
process
wise,
is
to
get
that
adopted
as
a
working
group
document,
and
we
can
collaboratively
iterate
on
it
and
I'll
definitely
agree
with
something.
Phil
said
a
cab
forum
doesn't
want
to
be
involved
in
specifying
this.
It's
not
standard-setting
body.
It's
the
body
that
adopts
these
things.
I've
been
separately
involved
in
encouraging
cab
forum
members
to
participate
or
the
IETF
in
this
process.
So
they
can
have
that
input
and
I.
Think
that
was
it
I
think.
F
G
Hi,
this
is
Shaun
Turner
I
think
we
shouldn't
stand
on
process
if
they're
gonna
implement
it
and
they
found
bugs
and
they
wrote
up
a
way
that
they
were
they're
doing
it.
Now
we
should
document
it
to
fix
what
we
did
wrong.
It
would
seem
silly
that
we
wouldn't,
if
we
have
this
this
way
and
the
authors
seem
like
they're,
actually
agreeing
with
each
other.
So
all
we
have
to
do
is
identify
people
that
read
it
and
kid-like
agree
to
it
in
the
IETF
right.
G
F
E
So
my
position
is
that
we
should
document
the
errata
version,
essentially
not
literally
with
the
errata
text,
because
there
were
some
in
Felicity's
in
that
as
well.
The
simplification
doc
I
have
proposed
implements
the
errata
algorithm
from
the
one
that's
actually
in
production,
but
uses
much
simpler
language
with
fewer
ambiguities.
Basically,
by
pulling
out
the
the
parts
that
try
to
we
specify
cname,
so
I
believe
pretty
strongly.
E
We
should
document
what's
in
production,
making
RFC
for
that
that
supersedes
the
old
one
and
then
move
on
to
something
that
would
fundamentally
change
the
discovery
process,
but
it
you
know
I,
think
anything.
That's
going
to
fundamentally
change
the
discovery
process
should
be
motivated
primarily
by
seeing
how
things
have
played
out
in
production
and,
for
instance,
if
people
say
you
know
this
algorithm
that
we
all
know
that
isn't
serving
me
correctly.
I
can't
express
this
policy,
that's
really
important
for
me
to
express
and
then
we'll
be
able
to
decide.
B
I'm,
not
the
actual
chair,
so
I
can't
make
any
sort
of
actual
final
decisions
from
a
peer
process.
Point
of
view.
We
actually
can't
reach
arter
until
we
get
one
document
in
and
through
the
iesg.
We've
got
a
document
there
now
so
and
it
is
actually
through
because
you
push
the
publish,
so
we
can
actually
start
that
recharter
process.
Okay,.
G
So
this
is
Sean
Turner
I
guess
I
can
get
them.
You
know
so.
I
I
like
the
idea
of
a
supersedes,
but
I'm
not
really
super
strongly
and
like
one
way
or
the
other.
If
somebody
has
a
really
strong
opinion,
let's
just
go
with
that
one
and
do
it
like
get
the
errata
out.
It
ought
to
be
pretty
straightforward.
Pretty
simple
to
do
it
shouldn't
take
years
to
get
get
that
version
out
the
door.
Let's
just
do
it.
B
B
B
D
D
Currently,
we
are
we're
describing
Oh
Eddie's
for
DSA
is
see,
they
say
and
and
of
course
I
say,
and
here
is
the
the
IDSA.
The
exact
numbers
will
be
specified
by
this
later
that
it
would
be
a
very
easy
work
for
me
to
do
so
right
now,
I,
just
we
just
put
symbols
X&Y
for
now,
and
those
will
be
updated
later
and
Oh.
Eddie
is
in
the
same
category
of
the
signature,
algorithms
in
the
NIST
sock.
D
Oh,
the
format's
and
keys
identifiers
will
be
provided
in
our
draft
and
our
document
later
for
now
we
just
put
a
placeholder
in
the
draft,
and
this
is
something
I
don't
know.
Should
we
specify
oh
I
DS
for
both
I'll
say
standards
or
just
only
one
of
them
in
some
of
the
previous
documents,
I
saw
we
specify
both
for
PSS
and
because
she
has
one
by
five,
but
that
we
all
know
the
one
by
five
is
one
people
are
actually
using
for
pickets.
So
so
I
don't
know
what
what
our
group
want
to
do
and.
D
G
A
G
It
included
to
be
complete,
so
it's
all
listed
there
and
then
we
can
reevaluate
and
say:
do
we
really
need
to
include
them?
Yeah
I
think
the
answer
really
should
be
no,
so
that
we
can
make
it
easier
on
everyone,
and
then
people
won't
do
silly
things
like
use,
Ayana
registries,
to
measure
you
know,
implementations
and
how
well
they
conform
to
all
the
things
listed
in
the
standard,
because
people
don't
do
them
at
least
that
I'm
aware
of.
H
H
B
D
D
G
I
guess
when
in
deshaun
trainer
employing
new
algorithms,
we
should
go
first
like
this.
The
kiss
approach
right,
but
let's
just
pick
the
ones
that
we
know
people
would
want
if
they
were
gonna
drop
them
in.
If
their
variable
length
like
has
anybody
actually
asked
for
them
to
be
variable
length
we
fair
enough,
but
I
mean
like
before
we
would
just
go
off
and
specify
like
$20
value
of
values
or
whatever
for
the
length
of
them.
We
probably
should
have
somebody
say
that
they
wanted
it
for
us.
B
C
B
C
See
DSA
keys
are
fixed
size,
so
you
could
just
require
that
the
that
the
keys
be
expanded
in
the
same
size
right
so
as
a
participant
not
know
I'm,
not
an
ad
I
propose
we
jettison
DSA
and
hence
is
identifiers
that
answer
this
question
and
and
require
the
pre
CDSA
they'd
be
meant
to
be.
You
know,
they'd
be
same
length,
but.
C
C
C
D
D
Not
I
think
I
think
fixed
land
would
be
just
fine
and
but
the
the
whole
idea
of
the
shape
variable
and
originally
was
you
know
for
to
building
the
whole
symmetric
crypto
core
in
one
thing,
because
in
any
case,
if
you
run
a
system,
you
need
a
random
memo
generation
right,
anyone
that
want
to
be
efficient
and
in
different
applications.
You
want
my
one
different
sizes.
So
that's.
Why
did
the
reason
to
design
something
with
variable
our
lands,
because
it
could
be
used
for
many
different
things?
D
E
D
So
that's
a
big
ETS
number
one
version
1
by
5
and
the
same
thing.
F
and
Y
will
be
provided
later
and
the
same
with
is
easy.
They
say
and
then
for
the
shake
instead
of
the
H
Mac,
we'll
just
use
a
normal
shake
would
have
in
this
specification.
We
have
a
fix
a
boot
lens
for
for
for
the
TAC,
and
we
use
the
the
the
the
shape
specify
in
our
in
the
NIST
FIPS
185
and
it's
very
simple
and
is
efficient,
and
that
is
way
how
to
do
macking
with
shakes.
I
D
B
D
B
Wrap
up
so
we
should
be
starting
a
charter
discussion
relatively
soon.
There
is
a
candidate
charter
which
I
have
not
read
as
in
my
mailbox,
but
it's
not
clear
exactly
how
soon
that's
going
to
start
Russ
is
going
into
surgery
tomorrow
and
he
has
an
expected
five
to
six
week,
recovery
period
after
that,
so
I'm
not
too
sure
how
much
he's
going
to
be
active
between
now
and
Christmas.
So
we'll
see
what
happens
in
terms
of
that,
but
we
will
definitely
try
to
get
the
current
documents
done.
