►
From YouTube: IETF100-TLS-20171116-0930
Description
TLS meeting session at IETF100
2017/11/16 0930
https://datatracker.ietf.org/meeting/100/proceedings/
A
Let's
see
you
should
all
be
pretty
familiar
with
the
note.
Well,
since
this
is
Thursday,
you've
probably
seen
it
oh
and
15
times
already,
but
please
respect
it.
We
do
have
minute
takers
and
jabber
jabber
scribes.
The
blue
sheets
are
going
around
remember
when
you
speak
at
the
mic
to
state
your
name
and
let's,
as
always,
keep
this
professional.
A
There
are
professionals
good,
all
right,
here's
our
proposed
agenda.
We
do
have
a
fairly
packed
agenda,
especially
since
we
want
to
get
to
resolution
on
the
TLS
remaining
TLS
one
three
issues
and
make
progress
on
DTLS
as
well
couple
other,
perhaps
especially
eye
on
a
registry
graph.
We
also
want
to
start
moving
that
board.
C
Can
find
my
slides
here
where
they
all
right,
so
we
got
two
dots
in
the
RFC
tersky
there.
It's
miss
ref,
they're,
waiting
on
another
reference,
so
we're
about
done
with
those
that's
great.
The
Dane
draft
is
should
be
ready
to
go.
So
that's
really
good,
because
we've
been
kind
of
pinging
them
a
little
bit.
Since
the
last
meeting
we
adopted
three
drafts
for
delegated
credentials.
Smi
encryption,
the
record
size
limit
extension,
I,
think
the
delegated
credentials
in
the
SMI
encryption
stuff
is
kind
of
still
kind
of
in
its
infancy.
C
D
D
C
C
Tls
1.3
has
been
through
to
working
group
last
calls
at
this
point.
We're
gonna
discuss
some
changes
today
and
then
we're
gonna
do
we'll
probably
end
up
having
to
do
another
targeted
working
group
last
call
so
we're
just
talking
about
the
new
changes
since
last
time,
and
we
have,
as
you
will
talk
about
later
today,
that
we
think
Joe
and
I
are
writing.
C
That
draft
at
the
eye
on
a
registration
update
document
is
ready
to
go,
we'll
have
to
identify
a
shepherd
since
we
can't
Shepherd
our
own
documents
and
we'll
have
to
make
sure
Kathleen
hits
the
button
for
us,
because
she
has
that
power.
Because
again
we
shouldn't
be
part
of
progressing
our
own
documents
in
progress
is
details
1.3,
we're
gonna,
hear
about
that
later.
Look
at
example,
handshakes
40,
us
1.3
dot.
That
draft
is
going
to
get
pumped
out
once
we
get
1.3
out
the
door.
Apparently
it's
pretty
easy
to
go
in.
C
G
So
what
we
did
last,
the
very
last
they're
really
really
last
time,
I
have
to
stand
up
a
dog
rat
tails.
Am
I
great
next
slide,
so
there's
only
three
that
we'll
talk
about
the
only
important
thing
really
is
this
middle
box
issues
thing
so
and
then
we
can
talk
weekly,
and
you
know
these
keep
trickling
in
these.
We
keep
not
closing
the
draft
so.
G
You
close
the
graph,
then
things
will
start
trickling
in
on
next
slide.
So,
as
I
sort
of
said
in
the
email,
we
were
finding
that
middle
boxes
sometimes
appear
to
be
kind
of
sad.
We
need
to
go.
Shave
kill
at
one
point
three
so
with
some
more
data
later,
but
this
is
our
initial
data
from
on
Firefox
beta
on
a
forced
test
versus
CloudFlare,
by
which
I
mean
CloudFlare.
Yes,.
G
So
what
I
mean
by
a
force
test,
this
one
is
basically
a
forced
a/b
test,
so
we
have
a.
We
have
a.
We
have
a
CloudFlare
sort
of
cloth
for
our
servers,
they're,
essentially
identically
configure
between
you
know
one
some
DTLS
one
three
and
some
don't
bother
wise
or
dedica,
and
they
just
basically
do
or
question
both
of
them
and
look
at
the
error
rates.
So
that
way,
we
don't
miss
pleasure,
organic
testing
or
something
David.
We
talking
about
later
they'd.
G
So
this
no
C's
or
vinegar
or
is
like
incredibly
hot.
That's
like
well,
everybody
seems
to
see
you
can
drive
these
numbers
down
a
little
bit.
I
was
looking
at
some
of
our
numbers
from
earlier
day,
and
some
of
the
problem
is
like
China
blocking
things
so
like
we
do
force
test
against
Gmail,
like
you
like,
remove.
G
That
Erica's
way
down
but
they're
less
on
the
ordinary,
from
Taylor's
pretty
high,
regardless
on
we're
not
willing
to
take
a
one-point,
seven
or
eight
point,
seven
or
a
point.
This
is
not
one
point.
Seven
hit
come
to
the
point,
tails
one
point
three,
and
so,
if
we
were
to
do
this
as
a
browser,
we
need
to
continue
to
fly
back
but
which
I
mean
we
need
to
somehow
probe
whether
your
environment.
I
G
Just
let
it
rip
so
the
order
of
operations
here
is
I'm,
going
to
talk
briefly
about
the
PR
I've
written
based
on
their
work
and
some
feedback
from
people
and
then
and
just
walk
you
through
what
I
was
doing
and
then
the
David's
gonna
talk
about
the
data
in
chrome.
He's
got
it
next
slide.
So
there
are
two
parts
of
this
PR
one
of
the
things
you
always
do
any
other
things
you
can
do.
G
We
don't
have
to
do
the
always
that
the
parts
that
you
do
generally
pretty
look
pretty
reasonable
and
are
things
that,
like
would
have
been
reasonable
design
decisions
that
we
just
didn't
do
when
we
did
one
three
initially,
so
we
had
a
longer
skirt.
The
first
one
is
how
to
do
version
negotiation.
So
we
had
a
better
long
discussion
initially
about
when
we
did
supported.
G
Server
should
not
altered
version,
it
wanted
and
we
sort
of
people,
and
we
and
like
people
went
back
important.
You
should
be
in
the
server's
extension
supported
version
extension
or
it
should
be
in
server
below
version
and
eventually
shouldn't
in
server
hope
version,
because
that
seemed
like
the
more
normal
thing
and
even
though,
is
LOD
to
have
like
a
thing
and
then
respond
in
some
other
place
on
turns
out.
That's
bad.
G
J
G
Because,
because
you
guys
are
claiming
to
be
telling
some
point
so
in
innocent
supported
version
was
in
the
server
Hall.
So
now
we
get
to
the
things
which
are
like
a
little
less
like
happy.
It
turns
out,
and
it
there's
some
so
I
don't
be
our
measurements,
that
if
we
like
HR
I,
give
me
a
handshake,
tape-delayed
nobody's
there,
recognizer,
completely
freaked
out
and
so
on.
The
proposal
here
is
to
and
a
niche
or
and
server
home
or
some
type
overlapping
is
information.
G
K
G
D
E
D
G
Okay,
so
this
last
thing
I
wouldn't
say,
isn't
gonna
make
any
sense
until
you
see
the
next
slide,
but
you
have
to
do
it,
otherwise
it
doesn't
work
which
is
you
have
to
ignore
it
any
time
you
receive
a
change
safe,
respect
message
during
the
handshake,
if
just
throw
it
away,
so
the
reason
you're
gonna
do.
That
is
because
the
next
slide,
please,
which
is
that,
if
you
think
about
boxes,
you
have
to
do
what
we
call
compatibility
mode
and
this
you
pretend
a
such
a
presumption.
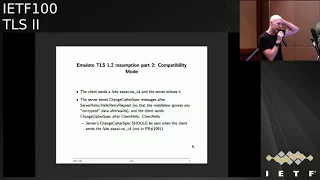
G
So
you
make
a
fake
session
ID
value,
which
I
think
we
said
is
random,
but,
like
I,
don't
have
the
ran
of
it
just
to
be
like
not
like
obviously
like,
and
the
server
echoes
it
is.
If
it
was
your
resumption
and
then
basically,
you
send
change
type
respect
messages
in
the
problem
happening
if
you
were
doing
like
if
you're
doing,
if
you're
doing
Redemption,
namely
the
server,
sends
one
way
after
the
server
below,
and
that's
where
you
come
over
to
the
finish
and
you
click
like
sometime
after
the
client
hello.
G
If
you're
doing
like
one
RTT,
you
do
it
like.
Basically,
when
you're
beginning
a
behavior
of
your
second
flight,
if
you're
doing
0tt,
you
hopefully
do
at
the
beginning
to
think
like
a
row,
we
don't
have
measurement
that
second
thing
works,
but
like
with
a
zero
duty
felt
Punk's
out
there,
like
you
just
retry
with
one
hour
TT.
If
it
happens
occasionally
disaster,
that's
not
an
insecure
flower
back,
it's
just
at
doing,
and
you
have
to
be
willing
to
fall
back
like
every
browser
stack
basically
I
mean
if
you're
doing
zero.
G
Tt
you're
quite
give
me
prep.
Sorry
anyways,
a
0
TD
has
to
be
willing
to
deal
with
like
a
bunch
of
our
conditions
when
the
server
didn't
like
0
TT
and
like
every
browser
stack,
we
tries,
and
so
like.
We
try
and
there's,
ladies
so
the
so
as
they
you
don't
ever.
You
don't
have
to
do
this
and
in-
and
you
wouldn't
do
this
in
DTLS-
and
you
wouldn't
do
it
like
in
the
quick
in
bed,
but
you
would
do
what
you
were
doing
it
you
do
it.
G
You
were
like
I'm
in
a
box.
Initially
I
did
vision.
This
is
each
side,
had
a
unilateral
compatibility
mode
and
that's
almost
entirely
true,
but
Warren
Thompson
points
out
that
the
clients,
the
ones
in
the
middle
box,
the
client
kind
of-
wants
to
tell
the
server
like
you
really
should
be
setting
this
on
the
the
CCS.
And
so
what?
G
D
Montano
observed
that
if
the
client
doesn't
do
these
extra
compatibility
hacks,
it's
basically
nothing.
You
can
do
at
the
server
end
to
repair
things
right.
So
it
has
to
be
the
client
that
initiates
this
behavior
and
if
the
client
knows
there's
a
middle
box
there
and
the
server
doesn't
follow
along.
Then
it's.
D
G
D
G
D
G
G
M
G
N
G
G
We
know
we
know
we're
aware
this
is
a
risk.
This
is
about
getting
the
error
rate
low
enough
that
we're
going
that
they're
willing
to
make
those
little
boxes
change
I
mean
to
be
clear.
Those
little
boxes.
How
like
is
their
responsibility,
ultimately
like
those
middle
boxes,
are
basically
broken
right,
live
in
a
box,
it's
okay,
so
you
step
back
a
the
middle
boxes,
we're
dealing
with
or
defective
what
I
mean
by
that
is
they're
not
proper.
G
They
are
not
properly
handling
TLS,
properly
handling,
TLS
version
negotiation
if
they
were
probably
having
cells
version
negotiation
and
they
were
fine.
The
problem
is
their
perspective,
and
so,
if
you
and
so
as
well-
and
so
it
they
probably
so
what
I
mean
by
that
is
when
they
receive
the
client
alone,
the
the
responsibility
either
to
do
version,
negotiation
and
downgrade
or
Mike
you,
which
should
be
fine
or
to
not
your
version
ago.
G
She
ation
and
that
not
screw
the
data,
but
but
the
doing
is
intermediate
thing
whether
with
are
basically
passing
either
passing
through
the
extensions
that
are
recognized
and
then
during
this
or
and
then
mirroring
the
server's
version,
or
they
are
trying
to
do
state
machine,
especially
at
the
wrong
version
level
and
all
those
things
are
possible.
So
nobody
has
to
do
correctly.
Is
it
has
to
actually
the
version
negotiation.
G
G
D
E
D
A
G
As
soon
as
we
did
supported
versions,
that
was
a
problem
I
mean
that
the
basically
the
problem
is
you
come
to
be
hungry.
You
shouldn't
be
porting
extensions,
you
don't
recognize
and
if
you're
doing
that,
you're
gonna
have
problems
so
yeah
voice,
averse
negotiation
like
when
there's
a
version
out
arm.
Basically
we
don't
have
to.
We
don't
actually
Bev
in
some.
What
happened?
If
we
did,
we
try
to
do
the
overseer.
She
imagined,
but
we
do
know
it
cause
problems
with
servers
so
voice
it
out.
F
Net
stuff,
Apple
I
brought
this
question
up
during
the
hackathon
as
well
I'm
wondering
if
we
should
include
a
recommendation
to
let's.
Let
me
call
this
yeah
B
compatibility
mode
to
not
try
to
engage
in
compatibility
mode
on
the
first
requests,
because
if
we
did
do
that,
that
an
ossification
will
always
be
the
case
and
nobody
will
adapt
to
purity.
That's
1/3
yeah.
G
F
P
O
Data
is
a
little
bit
confusing
on
this
front,
but
we
have
some
reason
to
believe
some
of
these.
These
middle
boxes
are
a
little
staple,
and
if
you
offend
them,
they
will
black
fool.
You,
which
kind
of
makes
fallbacks
problematic,
I'm
also
generally
skeptical,
that,
like
adding
a
fallback,
is
gonna
convince
them
to
do
anything
because,
hey
it
works,
and
they
probably
won't
even
realize
something
is
going
on.
So.
G
G
Several
reasons
I'm
personally
I
say
we
don't
need
it
for
tailfin
point
three,
quick
or
DTLS
and
soak
up
those
protocols
enjoin.
The
data
is
extremely
fuzzy
and
that's
why
this
italic
is
here
on
what
do
we
need
client-side,
CCS
or
not?
I.
Don't
think
we
understand
that,
but
it's
possible,
you
might
not
need
it
and
should
I
be
yeah,
should
I
keep
having
it
forever
and
I
think
this
is
blessed.
G
G
G
G
A
G
M
Okay,
I
would
like
to
give
everybody
who
worked
on
this
like
their
beer
back.
This
is
insane
like
what
why
these
middle
boxes
they're
meant
to
do
either
deep
packet
inspection
to
help
you
with
your
playing
tags
or
to
somehow
protect
you.
If
these
boxes
are
not
getting
updated,
41.3
they're
dead
in
the
water,
and
they
do
nothing
so
they
will
either
need
to
be
updated
on
a
to
support,
alert
on
23
natively
or
they
need
to
be
removed
from
the
network.
M
Meanwhile,
if
this
breaks,
you
can
just
go
back
and
and
suffer
one
round-trip
of
latency
to
go
back
to
TLS
1.2.
Why
are
we
hobbling
till
has
one
for
three
for
the
next
15
years,
just
to
support
these
boxes
that
should
have
been
removed
or
updated
from
the
network.
Anyway,
like
is
latency
that
important
not
about
latency.
G
R
G
I
think
I
think
my
assumption
here
and
I'm
hearing
speculating,
but
is
there
two
kinds
of
metal
boxes
right
here?
One
are
just
basically
ones
that
are
doing
on
non
deep
packet.
Inspection
between
state
machine
enforcement-
those
guys
are
right,
will
never
change,
and
the
second
is
the
set
of
people
who
are
doing
who
are.
Q
Q
A
A
D
G
C
A
D
G
A
G
Myatt,
so
my
assumption
is
where
it
will
put
if,
if
you
I
proposed
ribose,
this
text
looks
like
is
this
that
the
client
can
add
its
options
to
the
patient.
Id
or
not.
The
arm
client
can
have
to
add
its
options
and
change
their
perspectives
or
not,
and
the
server
must
send
a
change
their
perspective.
The
client
sends
it
a
session
ID.
That
is
where
I
approach
the
person's
tech
say.
G
A
A
B
G
D
So
Martin
times
an
echo
and
I
had
a
bit
of
a
discussion
about
the
enforcement
of
the
CCS
thing,
and
it
is
very
unpleasant
to
enforce
this,
because
you
have
to
have
knowledge
about
all
sorts
of
things,
particularly
in
the
zero
RTT
case,
where
it's
going
to
arrive
at
a
particular
point
in
time.
We
just
not
expect
the
exact.
E
D
E
G
E
G
E
O
Oh
sorry,
alright
is
better
next
slide,
I
guess,
because
there's
no
contact
yeah,
so
back
in
February,
we
tried
to
deploy
draft
18
and
we're
really
excited
about
it
and
the
one
thing
that
did
go
well
is
nobody
hates
to
tell
us
one
through
client,
hello,
like
everything
we
did
work
the
server
hello
didn't
really
work.
Our
numbers
are
even
more
horrifying
than
occurs
yeah
that
that
means
a
fallback.
If
even
that,
I
would
be
laughed
out
of
the
room
for
suggesting
we
deploy
that
thing
we
were
really
just
making.
O
O
So
we
went
and
tried
to
figure
out
getting
as
much
information
on
these
middle
boxes
to
be
cut,
which
turned
out
to
be
kind
of
difficult
because,
like
you
have
to
get
these
people
to
talk
to
their
IT
people
and
so
on
on
a
general
rule
that
we
found
is
the
tailless
terminating
middle
boxes.
This
is
sort
of
like
these
boxes
that
will
like
terminate
the
connection.
They
are
a
trusted
CA
bla,
bla
bla.
They
generally
work
v
because
they're
just
a
client
and
server
connected
back
to
back.
O
If
your
servers
implemented
correctly,
the
client
is
appointed
correctly.
Then
everything
works
out.
Fine,
there's
some
fun,
that's
yet
o
deep,
but
there
are
a
bunch
of
other
middle
boxes
that
are
in
some
ways
the
same
middle
boxes
and
different
configurations.
Try
to
process
tell
us
about
terminating
it.
They
do
all
kinds
of
random
things.
Sometimes
we're
just
checking
length
prefixes
because
they
thought
that'd
be
fun
and
yeah.
As
a
result,
they
parse
a
whole
bunch
of
version.
O
Specific
messages
which
is
not
like
this
violates
all
of
our
assumptions
about
how
we
change
the
protocol
and
they
break.
Unfortunately,
although
they
are
not
working
correctly,
that
92%
was
kind
of
a
horrifying
I.
Don't
think
this
is
an
oversimplified
picture
like
we
do
break
some
of
the
tools
terminating
about
middle
boxes,
because
they
have
some
parts
of
their
process
that
you
could
probably
describe
as
a
non
terminating
middle
box
did
this
is
sort
of
airplay?
Okay
next
slide.
O
O
Okay,
so
yeah,
so,
given
that
draft
18
was
not
going
to
work,
we
went
and
tried
some
options
based
on
Kyle's
suggestion.
We
test
it,
so
we
actually
have
some
local
configuration
to
test
with
there's
some
some
of
the
like
information.
We
got
from
about
the
photos,
so
we
iterated
locally,
where
we
could,
but
what
we
have
locally
is
not
even
close
to
the
like
wide
range
of
stuff
we're
seeing
in
the
world,
so
we
had
to
run
some
tests
in
the
wild.
That's
unfortunately
take
some
time,
which
is
why
it's
been
like
a
year.
O
O
Also
omitting
the
client
session
ID
gives
you
an
error
rate
of
ninety
five
point,
four
percent,
so
that
also
doesn't
seem
to
work.
The
experiment
version
seems
to
work,
but
there
was
some
loss
and
we
have
these
confirmed
by
user
reports.
Their
user
reports
are
not
a
great
metric
because
you
got
like
ten
of
them
total,
but
thankfully
we
got
some
for
the
experiment.
Version
next
slide
so,
based
on
that,
we
managed
to
reduce
it
and
change
the
record
blur
version,
and
that
seems
to
work.
O
It
actually
does
better
than
one
too,
but
I
suspect
that
the
noise,
because
these
numbers
are
kind
of
fuzzy.
We
also
tried
to
get
some
HTP
level
metrics,
so
these
are
metrics
for
conscious.
So
the
reason
the
baseline
is
higher
than
occurs
is
because
we
throw
out
the
TCP
level
failures,
so
once
we
successfully
connect
TCP.
If
then
we
check
where
the
hand
at
handshake
succeeded,
we
also
tried
to
get
some
HP
level
metrics.
O
They
were
added
late,
so
I'm
not
confident
in
whether
or
not
they
like
to
measure
what
we're
trying
to
measure,
but
they
are
consistent
in
that
it
doesn't
explode,
and
it's
been
on
beta
for
a
few
weeks
now
and
was
on
my
channel
for
a
bit
and
so
far
no
user
reports
around
this
time.
In
the
last
round
we
did
have
user
reports
we'll
see
if
this
survives
disabled,
I'm
very
optimistic.
B
So
Cedeno
can
go
more.
Thank
you
for
doing
these
measurements
and
for
reporting
back
I
confess
that
I
am
uneasy
about
the
unreproducible
'ti
of
these
experiments.
So
I
I
appreciate
that
you
have
the
resources
to
be
able
to
pull
this
off
most
of
the
rest
of
us
don't
and
if
we're
making
decisions
on
this
basis.
B
E
B
O
Q
O
G
E
N
G
The
Delta,
like
all
that,
but
on
the
end,
this
end
and
and
because
it'll
be
our
22,
won't
be
it
won't,
be
1.3
good,
like
it
won't
be
committing
us
permanently.
There's
a
totally
screwed
up,
but
I
don't
see
another
way
to
make
the
change
I
mean
like
the
bronze
with
the
field.
That's
find
out
right,
and
so
like
I
mean
showed
me.
This
tell
me
what
they
wanted
to
do
when
I
was
like
kind
of
like
vomiting
and
but
I
mean
I'm.
G
G
G
G
O
I
Us
hi
Nick
Sullivan
Claire
I'm
committed
we're
committing
to
build
a
website.
We
have
it
half
made
that
allows
you
to
very
fast
to
change
changes
in
TLS
versions
so
that
it
doesn't
take
an
entire
browser
rollout
to
get
the
code
in
into
browsers
and
do
these
experiments
so
there
are.
There
are
ways
of
quickly
updating
the
code
it
has.
It
doesn't
go
out
to
everybody,
it
has
to
it's
a
selective
group,
but
if
someone
is
having
problems,
we
can
use
it
to
like
this
to
debunk,
then
I.
H
Think
you
know
so
you
say
that
you
would
be
a
lot
more
uneasy
if
there
were
changes
to
the
crypto.
But
it's
not
entirely
clear
to
me
that
you
could
actually
characterize
this
as
no
changes
to
the
crypto,
because
you
know
we
now
have
these
safe
respect,
messages
that,
like
everybody's,
ignoring
and
they're,
interspersed
among
the
crypto
and
I
feel
a
little
bit
uncomfortable
about
that.
Not
a
lot
of
we.
P
S
Itself,
I
share
a
little
bit
about
Dan's
concern
about
the
non
reproducibility
I.
Think.
A
lesson
to
take
away
for
the
future
is
more
transparency,
more
involvement
with
a
wider
group
of
people
experiment
the
I
understand
the
trade-offs
with
that.
Also
in
terms
of
a
lesson
for
the
future.
I
agree
with
her
that
this
is
just
like
offending
geek
aesthetics,
but
we
should
explicitly
document
why
this
is
happening,
not
naming
names
or
shame.
S
B
It
needs
more
okay,
I'm,
like
I,
could
get
crack
at
that.
So,
in
addition
to
the
documentation,
if
we're
talking
about
what
this
means
for
the
future
I'm
wondering
if
the
folks
who
are
building
out
these
measures,
infrastructures
could
commit
in
some
way
to
having
the
measurement
projectors
be
able
to
report.
When
we
can
turn
off
the
grid
sets
we.
B
Not
asking
me
to
make
commitment
right
now,
but
like
though
that
would
be
it's
one
thing,
it's
great
to
have
this
data
in
the
design
process,
but
if
we're
adding
things
that
we
know,
we
want
to
get
rid
of
eventually
it'd
be
great
to
have
the
folks
who
have
that
infrastructure
be
able
to
help
us
also
get
rid
of
it.
Let
me
plan
I'm
ordering
identify
packet
officially.
G
G
G
Great,
so
now
that
we
resolved
like
the
difficult
thing
this
other
stuff
is
like
smooth
sailing.
So
we
only
have
two
minor
trivial
issues,
but
you
have
PRS
for
right
now
the
close
notify
Intel
tell
us.
One
too,
is
like
foreclose
on
certifies
the
I,
basically
the
when
your
reciprocal
identify
you're
required
to
flush
or
discard
all
your
outstanding
untranslated
data,
but
of
course
means
you
can't
hit
like
we're.
Can't
let
stuff
you
already
sent
and
you
can
tree
campus
on
from
the
TCP
buffers
so
like.
G
G
A
fin
business
how
you
things
are
how
you
was
done
with
this
side
in
sometimes
you
want
to
keep
running
after
that,
so
the
puzzle
here
in
peer.
What
1092
is
to
basically
just
remove
the
thing
that
says
that
you
have
to
like?
Do
you
have
like
flashlights
or
data?
Allow
you
to
keep
sending
so
it's
a
half
closed.
G
This
is
this
is
nice
thing
is
this
is
back
without
of
all
previous
behavior,
because,
as
I
said,
it's
unobservable,
the
other
side
didn't
comply
with
this
requirement
in
the
first
place,
and
and
if
you
choose
to
end
of
course,
you
can
always
continue
to
comply
with
the
Carmen
few
stitches.
So
we,
this
aggression
a
little
bit
a
while
back
and
I
sort
of
like
what
kind
of
person
waded
off
but
I've
been
frustrated.
G
Now
that
I
think
this
is
the
right
answer,
so
I
guess
one
question
that
did
come
up
by
Hubert
Carrillo
was
how
you
respond
if
you've
already
sent
close
in
to
fry
and
you
get
some
sort
of,
and
you
get
some
sort
of
bogus
packet
which
can
still
happen
because
it
which
could
always
have
happened
because
you
can
assign
clothing,
apply
another
guy's
stuff,
it
could
be
in
flight
and
then
you
send
an
alert
or
you
just
like.
Hang
up
the
phone
like
I
would
probably
eat
this
entirely.
On
the.
D
T
D
G
G
I
think
people
may
be
okay,
I
think
so
in
particular
like
if
you
have
like
an
internal
session
cache,
like
probably
you
don't
like
you
know,
probably
you
don't
accidentally
try
to
resume
with
the
wrong
s
and
I,
but
but
certain
servers
aren't
good
about
that
unfortunate
us
and
I
I'm,
not
assumption,
know
I,
think
NSS
actually
is
but
I
mean
for
an
endpoint.
Boyhood
is
I,
think
open
does
not
so
the
on
Victor
posted
posted.
G
This
PRM
1080
bit
definitely
have
I'm
suggesting
basically
slightly
relaxed
these
requirements
to
make
them
a
look.
A
little
more
like
HTTP
connection
coalescence,
namely,
but
the
client
is
still
required
to
only
resume.
Yes,
Nye
is
in
the
certificate,
but
if
the
ship
can
have
multiple
subject
names,
it
could
like
resume
any
of
them
on.I,
but
it
should
only
resume
if
the
SNI
is
the
same
on,
because
the
reason
is
the
server
like,
probably
isn't
gonna,
let
you
do
it
anyway.
If
you
change
it
on
the
with
it.
G
G
Check
that
the
SN
is
the
certificate,
but
that
by
shot
that
killed
the
from
my
perspective,
I
I'm
a
little
a
little
uneasy
at
this
point,
probably
answer
I'm
an
easy
bet.
Folks,
we
have
seen
problems
with
SLA
management,
there's
a
paper
by
Antoine
de
Malabo
and
other
people
about
about
SLI
mismanagement,
session
caches,
but
those
were
deactivated,
one
two
on
but
the
situation,
but
most
of
those
things
actually
turn
out
to
be
situations.
G
Reading
inconsistencies
between
like
be
did
the
SMI
lady
should
be
Hostetter
and
stuff
like
that,
and
it
turns
out
that,
like
we
already
have
what
those
problems
with
the
HTTP
connection
classes,
we've
already
basically
decided
that,
like
we're,
gonna
think
tweet
oily,
but
out
of
the
sands
and
it's
difficult
as
if
they
as
if
they
were
part
of
it.
Part
of
the
connection
state
so
like
I
know,
I
always
hate
taking
something
out
which
kind
of
feels
like
a
security
concern,
so
I
guess
I'm,
not
gonna
I'm.
Not
only
this
program
advocate
for
this.
G
D
D
G
B
U
Can
you
hear
me
okay,
so
so,
basically,
this
is
the
reason.
I
believe
this
is
reasonable.
Is
we
currently
support
if
you're
connected
to
foo.example.com
and
the
chair
site,
give
a
part
at
example.com
and
you'd
have
a
wild
card
for
start
at
example.com?
Then
you
can
HTTP
connection
pool.
But
if
you
connect
to
food
at
example
that
come,
you
cannot
later
resumed
and
zero
RTT
to
bar.example.com
and
there
isn't
security
wise.
Any
reason
to
do
this
so
say:
PR
lifts
the
strict
requirement
from
RFC
606
six.
It
still
discourages.
U
Implementation
from
always
cross
resuming-
and
there
are
two
reasons
for
this
one-
you
don't
necessarily
know
that,
like
all
the
main
served
within
the
same
search,
actually
shares
a
session
key.
The
second
ticket
encryption,
key
and
wasting
one-time
tickets
is
suboptimal
in
terms
of
performance
and
two.
There
are
some
implementations
which
might
not
be
ready
and
get
in
some
ways
confused.
As
ever
mentions,
there
were
multiple
bags
in
implementations
where
they
did
not
quite
realize
what
was
going
on.
U
So
the
premise
is
originally
I
wrote
a
TR
which
added
an
extension
to
new
session
ticket
which
allowed
you
to
do
this
and
Acker
told
me
to
bring
it
in
a
separate
draft
and
I
will
later
brink
and
separate
draft.
Is
a
working
group
agrees
that
in
general,
this
restriction
is
unnecessary?
I
will
write,
I
have
a
draft
to
actually
negotiate
cross
resumption,
so
this
is
mostly
opt-in,
and
this
is
mostly
CPR
is
mostly
agreeing
diseases,
crypto,
security-wise
safe
to
do,
and
it's
only
implementation
issues
which
are
preventing
us
from
turns
at.
L
Microts
I
mostly
agree
with
Spectre
I,
think
we're
basically
in
the
situation
where
it's
som,
some
basically
use
it
as
a
way
to
select
the
certificate
and
other
use
cases
will
actually,
when
you're,
just
using
it
to
select
a
certificate.
If
a
slightly
different
sni
value.
Would
you
say,
because
you
to
select
the
same
certificate,
then
you're
gonna
do
the
exact
same
thing
with
like
a
VGA
connection,
coalescing
that
seems
silly
to
forbid
resuming
the
session,
but
then
just
resume
different
SNI
and
send
connections
in
place.
T
So
walking
through
this,
what
I
imagine
happening
is
I,
go
to
have
an
example
that
that
net
it
gives
me
a
set
of
other
subject
all
names
and
certificate.
I
may
or
may
not
have
any
interaction
with
those
names.
I
get
my
a
new
session
ticket
I
go
away
and
I
wish
to
come
back
and
go
to
bar
dot
example:
dotnet
instead
of
food,
that
example
dotnet.
It's
not
clear
to
me
in
this
case
why
I
don't
make
an
initial
request
to
food.
T
G
Viktor
can
answer
this,
but
but
I
think
latency
and
that
the
browserstack
doesn't
want
to
do
that
right.
It
depends
basically
at
the
when
you
come
down
when
you,
when
you
come
down
from
the
like
that.
The
point
where
you're
making
the
TLS
connection
like
you've,
already
decided
by
HTTP
you're
gonna,
do
okay
but
remain.
G
U
But
that's
my
impression
I'm,
not
sure
I
quite
understand
the
question.
So
the
reason
is
that
you're
trying
to
connect
to
foo.example.com
and
then
you
talk
to
bar
dot
example.com.
But
you
don't
have
an
existing
connection
to
foo
and
connecting
to
bar
is
trick
to
it
faster
than
connecting
to
foo
and
then
trying
to
talk
to
bar
later
so.
T
G
T
G
It's
just
latency
and
some
love,
but
information
convenience
I
mean
like
what
were
you
mean
like
imposing
in
these,
because
all
the
problems
by
basically
doing
by
basically
you'd
feed
in
food,
you
feed
in
bar,
we
do
the
lookup.
We
find
that
we
find
the
certificate
they
had
do
in
barring
it.
We
look
at
the
s
and
I.
We
use
the
first
time
and
then
we
just
throw
the
SNI
out
put
a
new
one
in
and
then
we
look
at
it.
G
T
C
C
C
G
I
I
guess
I
see
that
how
you
could
do
that,
but
will
point
out.
This
is
exactly
the
sort
of
this
type
of
configurations
that
got
people
in
trouble
with
s
and
I
and
such
a
presumption
confusion
in
the
beginning
right
exactly
having
the
exactly
keying
your
behavior,
the
behavior
of
light,
which
surgeries
into
on
the
S
and
I
and
having
those
be
different
and
have
been
having
to
Machaerus
actually
heard
of
crushing
at
the
session.
Cash
is
exactly
how
you
in
trouble
like.
If
you
look
at
the
host
header,
it's
cool.
G
U
G
I
agree:
I'm,
just
I'm,
just
saying
that
if
you
have
a
situation
in
which
in
which
you
have
in
which
you
have
that
they
sometimes
you
have
the
SN
I'm
surveys,
yet
sometimes
it's
not
some
parts
of
the
other
faiths
overlap
and
some
parts
are.
If
they
don't.
That's
like
how
you
get
confusion,
I,
don't
know
how
to
mount
an
attack
here.
I'm.
Just
saying
that
you
would
you
go
back
and
read
the
paper
by
by
don't
alone,
others
like
they
like,
they
were
like.
Basically,
taking
advantage
of
confusion
are
routing.
W
Good
secure,
Google
I
mean
generally
in
support
for
cross,
as
my
second
assumption
other.
It's
not
clear
to
me
that
just
the
fact
that
you
sure
the
certificate
to
the
same
beautiful
cost-
and
in
that
case
you
will
be
sending
every
data
on
consumption.
That's
not
destined
to
the
healthiest
mu,
which
is
like
food,
which.
G
O
O
It
might
be
a
little
bit
fuzzier,
but
suppose
I
were
to
cross
resume
a
food
Arcana
session
with
bar
calm,
the
s
ni
that
I
send
is
still
bar
calm,
and
so,
if
the
server
were
to
look
at
the
s
ni,
it
still
says
bar
calm.
The
now
there's
a
slight
subtlety
here,
which
is
the
s
ni,
is
ambiguous
in
that
you
might
believe
s.
Ni
is
a
connection
level,
routing
thing,
in
which
case
it
is
not
part
of
session
state
or
you
might
believe
s.
O
Ni
is
like
some
negotiated
property
of
the
session
and
that
when
you
resume
you
like
use
the
same
one,
if
you
believe
in
in
the
first
interpretation
where
it's
a
per
connection
thing
then
like
cross
presumption
is
just
like
this
is
a
ball
of
crypto
like
either
worked
or
didn't
work,
but
like
this
is
a
key
either
you
have.
This
is
a
PS
k.
O
I
know
you
have
the
desk
area
didn't
have
a
guess
k
if
you
believe
that
is
a
per
session
property,
then
now
you
open
the
door
to
this
confusion
where
the
server
name
API
in
your
like
library,
returns
foo,
when
the
other
one
was
bar.
In
that
case,
I
would
say
that,
like
so
I
think
we
should
merge
as
PR,
but
there's
one
subtle
consequence
of
it,
which
is,
if
you
believe
it
is
per
session
state.
You
must
implement
RFC
60-66
as
well.
Otherwise
you
will
get
confused.
Could.
O
I
cannot
like
there
is
already
a
must
in
there.
It's
just
that.
Like
some
implementations
ignore
it,
so
we
ignore
it
because
I'm
expecting
that
Victor
will
come
down
and
ask
us
for
it
pretty
soon,
but
in
preparation
for
that
we
removed
all
per
session
as
a
nice
date.
There
are
some
limitations
which
both
ignore
it
and
have
procession.
That's
a
nice
date,
and
that
combination
is
not
a
good.
G
G
G
I'm
so
I'll
wait
for
David
to
send
me
a
PR
against
the
PR
and
then
all
personally,
okay
next
slide
right.
So
where
are
we
emergencies?
Be
ours
issue
22
like
a
Bronco.
It
won't
be
this
week,
but
I
hope
it'll
be
like
Monday.
I
could
be
this
week
if
I
like
actually
get
dancing
up
into
anyone
and
then
I
promise
you
22.
G
E
G
C
G
Have
so
this
is
in
beta
now,
I
did
like
the
thing
is
in
beta
now
I've
got
to
like
write
the
experiment
actually
test
it,
which
I'm
gonna
do
like
basically
next
week
and
I'm
hoping
to
have
data
in
the
next
I
would
say,
I
mean
the
optimistic
version.
We're
gonna
have
data
by
the
end
of
the
month.
The
pessimist
version
I
have
dated
by
this
time
next
month.
D
V
G
C
C
D
G
G
G
E
O
G
Will
report
back
asap
what
we
plan
to
do,
but
at
least
we
can
definitely
can
definitely
do
a.
We
can
definitely
do
any
spare
in
it.
I
like
the
way
our
stuff
works.
I
can
test
get
anybody's
circle
so
once
again,
another
set
of
server
farms
I
can
nest
against
them
too,
and
I'm
happy
to
publish
the
code.
We're
getting
pretty
easy
for
doing
this
so
like
his
worries,
a
matter
of
like
I
need
to
be
able
to
for
Firefox,
be
like
I
think
it's
up.
O
G
G
C
S
G
I
G
G
Thank
you.
Everybody,
okay
with
honest
and
Meg
Indra
Candra
like
last
minute,
couldn't
make
it
honest
over
there,
so
during
a
modest
number
changes
since,
oh
one,
so
I
did
this
short
record
hunter
thing,
which
I
can
talk
about
I'm
talking
to
each
of
these
things
short
record,
hit
things
sure
record
headers,
I
added
the
I
basically
made
it
clear.
You
could
do
an
empty
AK,
which
you
sometimes
need
in
cases
where
you're
receiving
like
say
you
receive
the
servers,
incriminate,
extensions
but
university.
G
The
server
hello,
like
you
like
to
build
a
shortcut.
The
round-trip
plan
and
I
read
her
ski
updates.
Without
you
faxed
keep
it
really
well,
that's
light.
So
we
had
a
loan
discussion
of
how
to
make
the
record
header
short.
He
back
in
back
in
Prague
and
people
and
I
sort
of
took
home
that,
like
we
hadn't
taught
the
might
as
well,
we
could
as
well
as
we
could
and
Martin
and
I,
went
back
and
workshop
in
a
bit,
and
so
we
figure
out
how
to
improve
things
quite
a
bit
I
think
so.
G
Basically,
the
idea
is
that
there
are
actually
two
new
header
formats.
One
of
which
is
basically
just
a
trimmed-down
version,
the
original
hundred
format
and
one
of
which
is
like
actually
like
super
compressed
and
the
point
and
the
key
difference
between
them
is:
do
they
have
a
length
field
and
zucchini?
Can
you
pack
more
than
one
in
a
in
a
record
alright
more
than
one.
D
G
Yeah,
so
on
you
this,
this
is
just
like
wait
where
ever
use
details,
147,
actually
use
this,
and
and
because
your
version
ago,
she
ation
first,
you
know
exactly
what
you're
getting
by
the
time
using
this
value.
So
it's
pretty
straightforward.
Next
slide
there
now
fancy
one
is.
This
is
basically
Martin's,
which
is
basically
a
you.
Take
up
rocking
the
sequence
and
you
pack
them
in
to
a
single
into
a
single
two
byte
word
do
a
word
with
the
appraoch
being
one
bit
in
the
sequence
being
or
remaining
what
12.
G
So
the
this.
This
has
some
restrictions
on,
which
is
why
it's
not
the
basic
format.
First
of
all,
you
can
only
do
one
or
tgd,
because
on
the
epic
bit
is
too
short
to,
let
you
basically
destroy
any,
which
are
the
multiple,
a
box
that
are
employed
during
0tt
work.
That's
part
of
why
the
other
ones
got
two
pieces
that
are
one
and
the
other
is
dad.
G
You
can
only
have
one
run
for
bracket
because
no
lengths,
you
can't
figure
out
how
long
that
hello
in
the
value
is,
but
it's
to
buy
their
prices
much
better,
so
yeah,
so
they
and
by
the
way
you
if
you
work
it
out,
you
candy
mocks,
there's
a
rule
5d
marks,
but
basically
the
bottom
line.
Is
that
no
matter
what?
Because
these
values
always
fell
in
the
32
to
63
range
and
and
the
contact
the
otherwise
application,
you
can
always
forget
what
it
is.
So
it
works.
Fine
yeah.
D
D
G
O
G
O
G
O
D
G
Slide
so
you
need
to
so
the
one
thing
you'll
notice
is
you
used
to
be.we
like
youth,
long
ass
values
and
they
couldn't
overflow?
And
so
you
know
things
are
simple:
if
you're
wanting
your
short
values,
if
like
deal
with
it,
values
being
short,
and
so
basically,
you
know
reconstruct
the
sequence
number
in
that
box
from
having
from
just
the
residue
at
the
bottom,
on
the
we're
using
the
same
algorithms
as
quick
uses.
Basically,
which
is
you
the
next
sequence
number?
G
G
Effectively
of
like
the
previous
left
hands,
like
you
perceived,
and
so
what
you
do,
is
you
basically
use
the
full
sequence
number
that
would
get
you
closest
to
like
the
thing
you
expected
to
receive?
Next,
it's
not
works.
Fine,
the
does
a
basically.
What
you
do
is
the
lord
of
into
the
epic
match
you
just
decrypt
right
away.
G
If
the
higher
bridge
the
epic
match
that
don't
morbid
about
don't
match,
then
basically,
you
file
that
you
week
is
like
the
epic
like
the
next
one
or
the
next
one
down,
and
then
you
look
to
see
what
sequence
over
would
get
you
closest
and
you
take
that
I'm.
Actually,
Martin's
gonna
save
you
in
a
second.
We
don't
it
on
that.
You
won't
actually
to
deal
with
this
as
badly.
If
you
keep
the
key
update
patch
it
he
wants
so,
but
so
this
is
a
pretty
simple
world.
We
don't
have.
G
We
have
this
implemented,
but
we
think
it
work
and
we
haven't
had
the
first
man
put
in
class
because
yes
like
right,
you
go
forward
one
more
and
we've
got
that
ok,
so
right,
so
the
I
brought
a
poky
update
back
on
when
you're
taking
it
out
you're
doing
like
a
story.
We
like
looking
at
the
epic
fit
and
like
going
oh
well,
go
forward,
but
now
you
don't
need
that
so
yeah
and
we're
trying
to
avoid
trial
decryption.
G
So
basically
I
put
the
camp
date
back
in
and
right
now
we're
just
like
the
old
time
favorite,
which
is
you
saying,
send
the
key
update
and
you
start
changing.
You
change
keys
right
all
right
and
then
you
have
a
update,
request,
knock
down
our
request
to
death
and
the
other
side
respond
and
the
way
and
and
you
just
and
the
reliability.
G
G
When
I
complained
about
this
before-
and
that
was
wrong
now-
which
is
it's
not
a
good
idea
to
start
sending
it
right
away
because
you
have
reordering,
then
basically
the
receiver
has
some
complicated
elements
are
managing
it
us
neutral
decryption,
which
is
like
roast
branched
out
the
packet,
which
eventually
things
will
succeed
like
not
be
great.
So
Martin
suggestion
was
that,
unlike
chillin
point
three
you,
you
know,
you
can't
change
the
new
key
until
you
perceive
that
he
updates
acknowledgement,
because
they
even
their
site,
is
ready
for
it.
G
G
D
Yeah,
come
on
Tom,
somehow
out
of
poker,
trying
to
implement
this
and
ran
into
problems
with
timers.
So
it's
not
necessarily
perfect,
because
you
in
the
test
that
I
was
running
I
still
had
the
the
handshake.
Related
time
is
running
and
overlapping
nose
we're
trying
to
do
a
K
up.
There
was
a
little
truck.
D
G
G
Gonna
make
this
change
in.
What's
anybody
bucks
and
then
also
route,
simplify
that
perfect
circle?
Okay,
back
one
more
flight
right,
so
this
is
like
I
think
chewy
non-controversial
on.
There
are
cases
where
you
can't
repair
part
of
the
flight.
So
say
you
get
on
Sh.
Let's
see
it's
a
sh
t,
er
sent
right
and
and
for
some
reason
the
e
company
comes
in
first,
so
you're
just
succeeding
on
this
thing.
You
know
it's
encrypted.
You
got
that
bump.
G
G
This
time,
as
you
can
see,
is
in
this
case,
she's
had
an
empty
and
empty
AK,
which
is
now
permitting
like
just
a
matter
of
changing
the
floor
like
zero
instead
of
one
and
then
and
then
the
other
side.
Doesn't
it
change
its
logical?
The
other
side
logic
is
the
same
logic,
which
is
whenever
you
get
an
act.
Basically,
unless,
if
you
haven't
retransmitted
recently,
you
just
right
away
of
everything,
you're
missing
and
the,
and
so
this
causes
the
other
side
to
return
the
whole
flight.
G
There's
no
way
around
that,
because
you,
because
you
can't
punch
things,
have
an
encrypted.
Otherwise
you
get
that
lock
on
so
on
this
shortcut
to
retransmit
timer,
so
it's
better
than
nothing,
and
it's
basically
only
thing
you
can
do
in
this
cases
and
given
there,
which
isn't
hammers,
are
quite
long.
It's
actually
a
pretty
big
optimization.
So.
D
D
K
G
D
G
F
E
C
G
D
Q
C
Q
M
V
C
G
G
Thomas
and
Tobias
this,
unlike
everything
else
I'm
talking
about,
is
not
entirely
baked,
though
it
is
not
entirely
unbaked
either
next
slide.
So
this
is,
like
recap
from
frog
initially
like
the
same
basic
craft
was
in
DTLS,
1,
3
and
people
I
think
we're
kind
of
sad
because
they
felt
like
it
wasn't
quite
as
finished,
perhaps
and
like
also
perhaps
they
felt
like
the
privacy
properties
were
like
awesome
that
they
were
hoping
for
and
then
writing
in
the
details
may
inspect
might
not
be
a
great
idea.
G
G
So
the
basic
idea
is
like
really
straightforward.
The
extension
that
basically
says
here
is
the
ID
that
I
would
like
you
to
use
when
you
send
to
me
and
then,
and
then
the
potential
negotiation
and
then
once
you've
done
that,
then
you
send
with
a
sentence.
I
gave
you
and,
as
usual
at
the
client
like
once
like
use
the
server's
ID
button
once
and
as
oh
man,
he
sends
an
empty
ID
to
listen,
just
listen
their
side
on
software
negotiation
works,
and
so
you
can
always
say:
I
have
like
a
zero
length,
ID.
G
What
you
do
if
you
like,
if
you
want
to
receive,
if
you
want
to
send
what
Roma
not
receive
with
one
on
the
important
they're
not
framed
on
the
wire-
and
this
is
gonna-
be
a
point
of
like
some
controversy
in
a
minute,
so
just
FYI
next
slide
so
I,
don't
even
like
I,
didn't
even
write
up
like
the
negotiation
I
have
in
a
document,
but
they're
not
gonna.
Do
it
here,
like
so
obvious,
is
with
the
wire
form.
It
looks
like
oh
by
the
way.
This
is
also
for
one.
D
E
G
If
she
don't
like
that
next
slide,
so
one
point
three
I
didn't
manage
them
put
this
in
the
draft,
because,
if
you
doing
I
pleading
competence,
but
it's
pretty
obvious
so
because
we
look
like
on
the
zone
graph
contains
like
the
details
of
point
three
ciphertext
Russians
that
are
the
new
ones
right.
It's
like
goes
in
the
same
place.
It
goes
before
the
length
and
when
there's
no
length
it
goes
before
like
they're,
not
unlike
ones.
G
So
it's
like
pretty
obvious
next
slide,
so
one
thing
that
people
noted
was
that,
like
this
got
a
privacy
problem-
and
you
don't
want
like
have
the
same
connection
ID
like
in
perpetuity
and
as
I
think
I
mentioned
repeatedly
like
much
to
sort
of
my
personal
embarrassment
after
spending
like
a
crap-ton
of
time,
trying
to
figure
out
how
to
like.
Do
you
know,
privacy,
preserving
connection
IDs
like
I
gave
up
included
ID
not
to
do
them
and
that
the
best
we
had
to
do
was
like
give
people.
G
X
T
G
I
hacked
this
thing
up,
and
it
looks
like
this,
which
is
basically
the
message
called
new
connection
ID
and
it
says
please
now
use
this
kind
of
heavy
like
like
here's,
a
new
conditioner
you
could
use,
and
it
has
two
semantics
that
are
indicated
by
this
like
enum.
The
semantics
are
either
throw
away
your
existing
connection,
IDs
and
use
this
one
now
or
here's
one
you
might
want
to
use
in
the
future
if
people
like
it.
So
just
we
have
lunch
today.
Yesterday
there
was
some
confusion
about
this.
G
G
E
G
G
Other
ones
and
then
I
send
you
four
more
with
the
spare
bed
set.
It's
like
this
is
not
like
ideal
I'm,
like
I'm,
trying
to
think
as
I
was
having
a
bunch
of
people
that
maybe
it'd
be
better
to
make
this
an
array
in
here,
and
then
you
wouldn't
have
to
sort
of
send
a
pile
of
them.
Okay,
then
you
would
have
like
sort
that
the
message
numbers.
E
G
D
G
I
don't
know
again
like
I
guess.
My
view
of
the
state
of
this
document
is
I
mean
I,
said
at
the
end
of
this
ass
for
acceptance
and
one
of
things
I've
been
asked
for
and
I
assume
people
want
to
screw
with
some
of
the
mechanisms
here
so
I'm
presenting
this.
But
I'm
not
like
saying
this,
like
a
funnel
for
yeah.
G
Next
slide
so
right,
so
the
bunch
open
issues
people
raised
I
in
private
analyst,
but
the
biggest
one
is
do
we
need
a
way
to
tell
if
I
connect
ideas
present.
That's
the
idea
here
you
might
have
a
server
which
will
allow
you
to
use
connection
which
would
like
you
use
a
connection.
Id
doesn't
enforce
it,
and
so
now
you
might
be
getting
messages
like
from
people,
clients
which
didn't
have
a
connection
ID,
eight
clients
we
did,
and
now
you
figure
out
which
ones
it
is
and
like
I
assert.
G
You
can
do
this
with
some
packing
this,
but
I
think
people
I
talked
to
were
kind
of
sad
about
it.
So
I
know
my
co-authors
are
gonna
want
to
talk
about
this
topic,
though
I
think
I
proposed.
You
want
to
this
topic
until
after
excited
wheeler
stuff,
the
draft
or
not,
there's
no
point
like
iterating
on
it.
If
we
just
hate
the
whole
concept.
The
second
topic
that
came
up-
oh
these
things,
basically
I,
probably
defer
o'clock,
decided.
E
G
E
G
G
Knew
about
this
because
I
worked
on
it
for
quick,
but
somehow
forgot
it
when
I
did
this
work.
Is
that
if
you
just
like
how
the
record
sequence
number
advancing
one
at
a
time,
you
get
cross
connection
any
leakage,
and
so
you
need
to
change
that.
You
need
it
like.
Basically,
we
randomized
the
sequence
number
when
you
start
sending
the
technically
speaking
you
could
just
reran
demise.
You
know
laterally
when
you
changed.
G
That
is
not,
however,
ideal
because
the
screwed
up
the
ng
replay
mechanisms,
because
when
you
get
a
new
message,
see
CID,
you
know
it's
it.
You
know
that
the
sequence
that
was
very
analyzed,
but
the
question
is,
what's
the
let
where's
the
left
edge
of
the
replay
window?
And
you
don't
know
because
you
just
got
something
like
maybe
in
the
middle
look
there
may
be,
it
may
be
a
middle
of
a
flight
right,
and
so
we
nice,
the
only
compute
or
the
next
edge
of
the
replay
window.
G
Is
that
the
good
news
is
we
have
this
technique
in
quick?
Where,
basically,
you,
just
essentially,
you
basically
have
basically
at
the
beginning
a
connection
you
just
I,
wish
a
short
key
that
you
use
for
basically
to
compute
the
gaps
between
the
knit
between
the
connection
ID
on
sequence,
numbers,
and
we
could
just
place
that
right
so
as
a
same
sort
of
barrows
like
I,
think
I
designed
that
somehow
forgot
about
it.
So
these
are
all
pretty
modest.
G
P
E
A
G
V
I
Hello
I'm
going
to
talk
today
about
expert
authenticators
next
slide,
please
so
TLS
exported
authenticators
is
a
draft.
That's
meant
to
solve
a
specific
problem,
which
is
that
some
application
layer
protocols
they
need
additional
certificates,
whether
it's
from
the
client
sign,
post,
handshake,
authentication
in
TLS
1.3
is
a
little
bit
awkward
and
optional,
and
perhaps
in
some
scenarios,
given
a
TLS
connection,
you
might
want
additional
server
certificates
next
slide.
I
Please
exported
authenticators
is
a
way
to
allow
TLS
library
to
export
a
piece
of
data
that
allows
you
to
bind
an
additional
certificate
to
the
existing
connection,
and
this
can
be
done
on
the
client
side
or
the
server
side.
The
structure
of
this
blob
is
to
find
a
document.
It
looks
very
much
like
a
server
hello
series
of
messages,
certificate,
certificate,
verify
and
finish
next
slide,
please.
I
I
You
discussed
this,
and
the
discussion
was
that
this
perhaps
needed
some
academic
review
or
some
sort
of
formal
analysis
before
moving
to
last
call
next,
please
so
in
the
meantime,
guess,
Kramer's
and
Jonathan
Hoyland
from
Oxford
have
created
a
preliminary
tamarin
model
to
prove
the
security
of
expert
authenticators
in
the
context
of
HTTP
two
additional
certs
there's
some
promising
results
for
this
next
slide.
Please,
but
in
in
recent
discussions
there
is
a
little
bit
of
duplicated
logic
or
undefined
logic
in
the
draft
right
now
as
written.
I
It
requires
the
application
to
select
certificates
and
to
select
the
extensions
that
go
into
this
certificate.
Furthermore,
there's
no
real
binding
between
requests
and
responses
other
than
the
context,
so
the
logic
for
selecting
certificates
and
selecting
extensions
already
exists
in
TLS.
There's
a
construct
called
this
certificate
request
and
certificates
in
TLS
1.3
are
bound
to
the
request.
Next
slide,
please
so
with
expert
on
authenticators,
we
came
up
with
a
proposed
change
to
the
draft,
which
is
a
new
exported
request.
I
I
M
D
Request
certificates
verify
all
that
sort
of
stuff
this.
Naturally,
it's
neatly
within
that.
Within
that
model,
you
can
put
those
signature,
algorithm
negotiation,
we've,
never
separate
independent
from
the
stuff.
That's
in
the
in
the
handshake.
It
just
seems
to
work
out
really
neatly
so
I
like
to
change.
I
C
What
he
said
anybody
anybody
against
this
change.
Is
anybody
read
it
I
got
one
I
got
yes
all
right
cool,
so
I
mean
Mike.
That
was
one
of
the
one
of
the
driving
these
cases
from
your
former
employer.
I
think
what
we
should
do
is
well.
He
wants
to
take
it
to
the
list.
Do
you
have
a
timeframe
from
when
you
think
that
the
tamarin
results
will
you
know
be
closer
to
the
final
I
I.
I
I
I
V
V
C
E
C
D
C
So
tried
to
get
one
of
you
guys
to
write
this
draft
and
nobody
did
so
Joe
and
I
volunteered
to
write
a
draft.
It
basically
went
through
and
looks
at
all
Diana
registries.
We
need
to
update
them.
I
want
to
make
sure
this
isn't
a
blocking
thing
for
teals
from
point
three.
So
let's
get
this
in
gear
and
get
it
done
so.
C
Draft
next
I
wasn't
sure
how
much
time
we're
gonna
have
how
long
the
key
loss
discussions
are
gonna
go.
This
is
the
quick,
don't
bury
the
lead.
This
is
basically
what
I
want
to
do.
So
we
got
time,
let's
go
into
the
next
slide.
These
are
the
changes
that
we
made.
I
mean
the
big
one
was
to
be
factoring,
so
essentially
the
internet.
C
It
started,
it's
been
growing
if
we
put
in
registry
and
the
rationale
was
in
the
introduction
and
it
seemed
like
it
would
be
better
to
put
the
rationale
for
each
one
of
the
changes
in
the
peeps
intersection.
So
we
did
that
we
decided
that
you've
got
that
recommended
column.
We've
probably
better,
actually
explain
what
it's
there
for
then
we
did
the
better.
We
did
a
thing
on
the
list
where
we
figured
that
we
would
remove
the
CC
and
that's
cipher
suites
from
the
recommended
column.
They
can
still
be
used.
C
E
C
Be
an
idiot
and
just
implement
these
things.
When
we
actually
look
at
the
algorithm
and
we
we
had
an
expert
with
you
to
the
supported
groups-
that's
really
it
so.
This
is
mainly
a
big
procedural
document,
so
we're
at
the
point
now.
Next
there's
no
really
open
issues
in
the
github
repo.
So
our
theory
is
next
get
Kathleen
to
start
her
ad
review.
Steven
Farrell
has
kindly
offered
to
Shepherd
it
forth
because,
obviously
he
can't
ship
her
own
document.
So
I'll
work
with
him
to
get
a
shepherd
with
you.
A
C
Y
So
the
problem
is
that
servers
are
vulnerable
to
denial,
service
attack
against
handshake.
Essentially,
we
never
say
that
kind
of
a
beautiful,
sunny,
fine
little
messages.
If
we
gain
the
server
to
react
in
the
first
place,
parfum
processing
can
shake
up
to
even
steps
being
a
server
to
host
a
copy
with
several
concessions,
and
the
cookie
exchange
complicates
the
effect
upon
us
in
some
extent,
but
it
is
oriented
only
to
non
fat
adversary'.
Y
So,
of
course,
the
service
is
still
exposed
to
own
path
of
bursaries,
ranging
from
adversaries
able
to
screen
and
inject
messages,
for
instance,
a
confined
flows
into
city
before
leveraging
that
is
cooking,
possibly
up
to
adversely,
in
addition
able
to
stop
traffic
most
likely
from
legitimate
clients
as
the
whole
state
of
a
new
several
a
stage.
Of
course.
The
specific
attack
attack,
in
fact.
Y
The
handshake
token
is
built
up
by
conquering
the
first
relation
with
the
server
and
provide
for
firing
that
requests
trust,
encore
in
first
place,
establish
handshake
with
the
server
then
practically
the
has
to
check
the
handshake
talking
to
be
fresh
and
it's
not
the
device,
and
in
case
it
name
Jake.
Otherwise,
it
aborted.
Y
Y
The
handshake
with
that
server
in
the
first
place,
and
this
very
rejection
process
is
otoscope
to
the
document,
but
kind
of
your
locally
on
the
very
same
ta
or
out
of
evidence
provided
by
the
client.
The
client
has
obtained
and
beforehand
and
of
course,
communication
with
the
TA
I
mean
between
the
client
and
the
TA
must
be
secured.
The
specific
things
are
Alice
couple
is
document.
Well,
as
we
see
there's
no
additional
communication
needed
in
TA
and
server.
Y
Yeah,
this
is
just
a
graphic
overview,
so
you
start
from
the
TA
endless
journey
long
term,
PKM,
client
requests
gate,
establish
handshake
with
server
s,
the
a
generic
token
provided
the
client
on
this
new
channel.
Then
the
file
starts
to
handshake
with
the
fine
hello,
including
also
the
e
OS
protection
extension
with
intern
sever,
verifies,
I,
think
a
success.
The
entry
quality
isn't
supposed
to.
Otherwise
it's
meet
the
boat.
It.
Y
Somewhere
little
step
by
step,
so
the
final
party
s
worth
of
innovation
with
us,
then
the
DA
considers
the
counters
at
us
as
token
dance
and
complete
smack
on
the
ass
on
desktop
announced
as
an
H
Mac
using
the
long
term
key
game
share
with
the
server
it
is
dense.
A
token
fascinating
token.
Aliceandmac
implements
the
counter
associated
to
that
server.
The
knees
apart,
look
lighten
so
the
only
semantics
to
me
is
is
agreed
between
blue
tae
and
the
server
after.
Y
Then
the
client
simply
prepares
the
client
below
infants
used
to
start
the
unshaped
with
the
server,
including
also
us,
protection
of
potential
bomb
and
the
area
of
sanctions
to
define
hello
and
simple
starts
in
shape.
Then
the
server
receive
the
client
hello
has
to
check
that
the
DRS
protection
attention
is
fresh
using
the
token
Alice
in
including
extension,
so
it
has
to
recompute
the
Mac
and
check
it
against
the
convened
one
and
it
matches
negative.
It
has
the
body
en
shake
immediately.
Otherwise
you
just
don't
hear
any
specific
protocol
and.
Y
In
the
docking
to
cover
some
additional
points,
as
the
social
assumption,
this
extension
is
not
strictly
needed
for
session
assumption
actually
caused.
Given
the
existence
of
a
session
already,
the
server
is
perfectly
able
to
assert
ones,
validity
and
even
possible
replace
of
client.
Twenty
hello
sent
for
assumption
can
be
handled
by
means
of
other
mechanisms
like
white
below,
recording
but
TLS,
one
Tuesday's
that
at
least
clients
are
supposed
to
the
parental
of
messages
sent
for
Assumption,
including
extensions
that
they
would
include
if
they
were
starting
a
new
session.
Y
So
if
you
won't
be
a
compliant
with
this-
and
this
is
very
important-
we
considered
the
TA
came
provided
client
the
end
she
talked
and
talked
about
before,
plus
a
limited
number
of
the
Samsung
tokens
built
up
for
it.
The
same
logic
essentially
be
used
by
the
client
in
case
of
session
assumption
and
just
for
the
sake
in
the
end,
to
be
combined
with
that
statement.
Y
Plus,
as
I
mentioned,
when
processing
the
extension,
the
server
is
supposed
to
check.
That
extension
is
fresh
and
there's
mobile
using
token
us,
including
the
extension
in
the
graph.
We
propose
a
possible
approach
do
that,
based
on
sliding
window
and
of
course,
it's
up
to
you
to
arrange
wind
of
proper
size
so
that
you
can
clean
off
the
actual
accuracy
or
of
the
plate.
I
know
messages
and,
and
the
memory
overhead
on
the
server
plus.
Y
Of
course,
it
may
take
a
long
time,
but
eventually
the
context
of
s
on
the
server
drops
around,
and
that
is
of
course
you
don't
want
to
reuse
km
now
pairs
to
generate
a
shake
tokens
for
requesting
client.
So
when
that
happens,
the
PA
must
know
the
long
turn
key
with
the
server,
and
that
is
first,
we
recommend
the
TA
to
enforce
rate
limit
in
issuing
nancy's
or
essentially
and
say
tokens
to
recipients,
to
avoid
that
even
legitimate
clients
can
quickly
consume
the
non
spaces
even
server
at
the
same
time
than
serve
other
requesting
clients.
Y
Environments
where
details
about
the
transfer
protocol,
so
the
security
protocol
to
be
used
are
left
to
separate
documents
called
profiles,
and
there
is
especially
the
DTLS
profile
for
such
framework.
That,
in
the
latest
version,
has
a
knowledge
the
problem
and
is
pointing
yet
this
document
as
a
possible
approach
to
address
it,
and
that
is
quite
easy
to
achieving
the
profile
by
the
way,
because
it
is
efficient
that
the
authorization
server
and
framework
acts
as
the
trust
anchor
on
this
approach.
Y
Y
Meg
thanks
again
for
that,
but,
of
course,
other
feedback
that
you
are
very
very
welcome,
and
this
activity
will
also
consider
within
an
EU
project,
about
security
in
smart
grids,
where
we
produce
also
proof
of
concept
implementation
of
this
approach
on
details,
one
two
in
California
and
standard,
but
that
implementation
is
aligned
to
the
design
describing
version
zero.
When
our
next
step
is,
of
course,
to
the
line
that
implementation
two
special
one
of
the
drop.
P
H
Dock
so
I've
actually
read
the
draft
a
couple
times.
I
read
a
couple
weeks
ago
and
then
again
a
couple
days
ago
and
still
left
me
kind
of
confused
to
your
talk
today
helped
somewhat,
but
it
sort
of
seems
like
you
know.
The
proposal
is
to
make
the
DTLS
server
more
robust
to
us
at
the
expense
of
moving
that
out
over
to
the
TA,
and
the
TA
is
perhaps
still
susceptible
to
do
us.
Y
Q
H
To
get
this
this
token,
and
it
has
to
use
it
pretty
quickly,
they're
off,
because
of
the
way,
the
the
lack
of
direct
connection
between
the
decal
server
and
the
TA
means
that
it
has
to
do
the
the
sequence
we
knowing
in
earlier
train
detected.
These
things
are
valid,
and
so
the
DTLS
client
could
get
these
these
tokens
and
then
just
use
it
for
a
while
its
tail
and
astok
trying
another
one
sure.
Y
H
Y
F
Y
Y
Now,
as
I'm
sure,
you
need
to
secure
communication
between
client,
yes,
well,
you
can
do
that
with
other
means
that
possibly
provide
other
solutions
of
their
own
against
that.
But
even
if
you
go
for
Els
for
detail,
is
between
PI
and
and
gay
I
can
first
assume
that
it's
more
reasonable
to
have
relative
with
you,
TAS
or
bastard
against
that
or
easier
to
protect
and
way
compared
to
many
more
devices
that
connect
at
servers
they're.
Putting
much
greater
numbers.
M
This
is
Hannes
so
so
far
we
had
the
us
mechanism
added
to
detail
s
already
two
previous
version
and
still
exists
today,
with
1.3
and
I
haven't
heard
any
complaints
that
it
it
doesn't
work.
It
doesn't
fulfill
its
purpose,
so
I'm
curious
whatever
you
so
may
be
solving
a
problem
that
hasn't
been
out
there.
Yet
did
you
did
you
notice
any
efficiency
with
this?
He
does
mechanism.
Y
M
Cookie
exchange
you
you
do
have
also
so
in
difference
in
the
old
Daedelus
version.
You
had
to
add
this
hello
retry
request
had
a
verify
request,
depending
on
which
version
of
TLS,
and
it
basically
does
a
return
readability
check.
It
also
has
a
cookie
mechanism,
which
is
a
useful
thing
if
you
to
avoid
reflection,
attacks
and
also
to
delayed
state
allocation
and
doing
heavy
computation,
which
is
pretty
good
in
some
sense.
So
did
you
encounter
any
problems
with
that
mechanism
without
actually
having
to
add
anything
beyond
that?
No.
M
M
M
M
Z
So
our
motivation,
it
is
what
we're
seeing
today
and
it's
a
device
boots.
Your
problem,
you
see
when
a
customer's
deploy
some
of
our
endpoints
in
our
our
collaboration
on
point
specifically
but
for
endpoints,
the
unboxer
network,
sorry,
the
unbox
box
and
powered
up
for
the
first
time
in
our
network,
there's
a
TLS
terminating
middle
box
between
the
device
and
our
Cisco
Cloud
and
the
device
is
dead
in
the
water.
It
doesn't
cross
the
middle
box.
It
is
no
way
of
connecting
for
cloud
and
what
we're
trying
to
solve
that
problem.
Z
Z
And
there's
a
few
different
ways
of
doing
it.
The
first
one
is
expensive
and
involves
an
integration.
If
you
Devi
was
doing
it.
The
first
thing
we
could
do
is
we
could
put
an
operator
specific
configurations,
call
you
device
prior
to
chip
in
it,
so
when
it
leaves
the
factory
we
know
where
it's
going.
We
put
specific
configuration
with
the
device
directly
across
the
middle
box.
The
second
one
is
the
operator
disabled
to
get
a
termination
on
the
middle
box.
Z
Z
With
that,
the
operator
think
it's
too
expensive,
it's
too
time-consuming,
but
we're
proposing
to
do
is
work
around
this
by
a
device
logic.
So
what
we
want
to
do
is
establish
an
application
near
connell
over
the
middle
box
to
establish
a
secure
connection
to
cloud
and
download
the
information
from
the
clouds
enable
device
I'm
secure,
Network.
Z
There's
multiple
different
ways
establish
an
application
they're
encrypted
Channel.
We
could
find
something
using
gilfs
art,
JWA,
J,
Dilla
peak.
We
could
define
an
encapsulation
using
noise
and
our
wiki
just
reuse
to
T,
let's
document
again
tequilas
record
application.
There
are
design
goal
to
do
this
as
simply
stops
when
this
few
lines
of
code
as
possible
on
the
client
and
it's
few
lines
of
code
hopped
on
the
server
and
our
rationale
is
device
are
really
called
tequila
stock.
Z
Api
is
a
network
layer
funny
just
get
the
drug
Chicago's
that
API
is
twice
and
the
second
time
we
call
to
this
tunnel
that
information
over
the
over
the
application
and
so
transfer
what
we're
proposing
to
do
with
transport
to
TLS
packet
inside
a
QP
and
I'm
transport
perplexity
less
per
clicking.
The
button
must
buddies.
The
reason
why
we're
doing
this,
it's
the
lowest
common
denominator,
if
it's
greatest
chances,
conversing
middleboxes
we're
discounts
at
university,
making
proxemic
where
this
chance
to
get
to
work
louder.
Z
That's
the
reason
why
one
due
to
those
common
denominator
and
the
application
Eric
Taylor
serves
the
district
address
using
standard
takes
me
guess
your
eyes.
It's
more
suited
to
applications
that
look
like
HTTP
and
as
I
say,
what
we're
trying
to
do
is
just
use
a
security
to
bootstrap
and
then
fall
back.
That's
impossible.
Z
Z
So
there's
uploads
and
discussion
points
here.
Both
doggies
want
to
turkish
all
the
way
down
and
so
we're
doing
an
application,
Aaron
Krypton
and
over
the
transport
layer
and
water,
preventing
middle
monsters
from
Franklin
except
up
and
block
that
same
question
is
equally
applicable
for
Annie
and
client
application
crypto,
but
are
using
noise
to
be
destroying
something
using
all
day
and
jwe.
It's
the
same.
Temperature
applies
of
preventing
limited
box
and
intersecting,
seeing
that
this
looks
like
encrypted
traffic
and
running
on
a
blockage.
Z
Z
What
we
were
intending
doing
is
just
using
application
air
TLS
for
the
handshake
and
then
falling
back
to
maybe
or
using
key,
exporting
and
encrypted
key
encoding.
Don't
necessarily
need
to
do
that.
So
one
of
the
questions
we
need
to
ask
is
is
just
read.
Application
areas
for
the
two
round-trips
for
the
handshake,
then
followed
by
clicking
mechanisms
are
really
just
transferred.
Z
All
your
application
data
inside
the
teal
at
all
time,
under
transport,
reliability,
pitched
messages
can
get
lost
transport
each
other's
records
inside
the
hand
kick,
and
that
is
somewhat
mitigated
by
PS
using
a
TLS
for
the
for
the
initial
handshake,
then
falling
back
after
your
first
e-bikes
transport
lightly.
He
isn't
such
a
problem
than
either
and
one
of
use,
HTTP
connections
and
that
isn't
going
to
work
for
life.
Z
In
all
scenarios,
we
have
deployments
where
we
have
HTTP
proxies
in
front
of
pilot
permit
in
little
boxes,
so
your
endpoints
don't
have
to
connect
any
way
and
then
wanted
all
to
connect.
It's
going
to
hit
the
middle
box
and
pls
virtualization
is
gonna,
pay
all
the
energy
and
then,
if
you
try
to
do
a
second
connecting
top
of
that
connect
our
complaint
perspective,
they
mean
get
the
deployer,
reverse
proxying,
come
to
your
service
and
how
to
connect
there
and
below
to
break
many
bottles.
Z
G
P
G
You
what
happened
to
me
issue,
P
connections,
aren't
like
that.
Like
ten
H
CPH
attention
is
like
we
live
description
of
the
server
right,
and
so
you
pull
up
the
connection
and
you
start
doing
this
stuff,
and
then
you
know
the
the
server
turns
down.
I
shouldn't
figure
out
what
on?
What's
holding
that
connection
to
why.
G
Yeah
yeah
well
well
connection
tracking,
not
touch
exactly
right,
and
my
point
is
my
point
is
like
you,
you
so
do.
I
understand
this
draft
to
me
edge
to
something
you.
You
know
they
should
be
connection
your
busily
time
to
tell
us
the
tell
us
records
over
HTTP
right,
which
is
like
like,
or
these
purposes
in
are
probably
my
point.
Is
you
do
that
and
then
you're
like
sending
some
data
and
the
server
is
like
yeah?
You
know
I'm
like
tired
in
this
connection.
G
Z
G
G
No,
not
a
matter
of
finiti,
it's
a
matter
of
it's
a
matter
of
from
the
tls
perspective
when
you
reconnect
to
the
server
right
on
dad
I
mean
so
you
can
just
be
like
you
can
just
save
a
lifetime
with
the
TLS
connection
is
bound
the
lifetime
of
the
HTTP
channel
right.
But
that's
like
not
really
great
because,
like
I
mean
like
what
you
really
would
like
to
have
is
like
that.
G
There's
no
logical
connection
between
the
between
the
HTTP
connection
in
the
tailless
connection,
and
then,
when
you
like,
if
you
actually
it's
torn
down,
you
don't
through
the
resumption,
you
just
do
something
else.
You
just
basically
say
well,
yours,
like
record
number
322
and
I
just
sent
321
right
and
so
I'm
just
going
to
figure
out
like.
G
AA
This
is
probably
one
of
the
more
flagrant
cases
there
and-
and
that's
all
I'm
warning
you
it's
gonna,
be
looked
at
through
that
lens.
If
you
adopt
this
I
think
as
an
organization,
we
probably
need
to
work
through
how
we
use
HTTP
a
bit
more
before
we
get
to
such
an
advanced
state.
You
know,
HTTP,
for
better,
worse
is
becoming
to
be
regarded
as
a
transport
by
people,
I
mean
hey.
AA
The
next
version
of
HTTP
is
being
defined
in
the
transport
area,
so
I
don't
know
if
that's
good
or
not,
but
I
think
that
there
are
numb
problems
here.
Having
said
all
that,
there
is
a
discussion
in
the
HTP
working
group
right
now
about
how
to
negotiate
to
open
up
effectively
a
new
tunnel
in
an
HTTP,
2
and
upwards
connection
and
I
think
you'd
have
a
much
more
positive
engagement.
If
you
went
through
that
kind
of
route.
AA
Z
E
Z
AA
Z
AA
K
F
K
I'm
still
trying
to
understand
like
what's
the
problem
that
you're
trying
to
solve
is
like
you
have
a
middle
box
that
doesn't
know
anything
about
this
on
unbox,
client
and
and
you
unbox
it,
and
now
it
wants
to
wants
to
connect
to
some
application
server
from
where
it
will
get
credentials
for
the
middle
ball.
Am
I
right.
Z
K
G
Z
K
I
think
maybe
you
need
to
look
at
other
possible
solutions
for
doing
this
and
how
probably
other
networks
do
this?
Is
they
do
it
even
a
layer
below
IP,
so
they
usually
EAP
and
you
can
do
radius
tunneling
to
any
server
on
on
on
the
cloud
wherever
you
want
to
and
send
these
send
the
information
about
the
middle
box?
You
want
to
I'm
just
throwing
a
new
idea
at
you,
because
what
most
gateways
do
do
this
authentication
right?
They
do
use
here
fee
and
they
do
use
some
back-end
like
radius
or
diameter.
Z
Z
K
K
J
Z
Z
J
M
M
B
Appreciate
it,
so
this
is
all
a
cat-and-mouse
game.
Yes,
I
appreciate
your
mousing
efforts
like
we
need.
Apparently
we
need
more
Mouse's,
but
I
don't
understand
where
this
all
stops.
I
mean
you've
already
said,
Turtles
all
the
way
down.
As
your
first
discussion
point
here
and
what
you've
designed
looks
to
me
like
a
generic
stream
transport
over
HTTP
I,
don't
I
may
be
misunderstanding.
It
I
apologize
that
I
had
not
read
your
draft
and
I'm,
not
sure
why
this
needs
to
be
TLS
specific.
B
B
Basically,
it
sounds
to
me
like
you
want
connect
so
that
you
can
get
past
middle
boxes
that
are
gonna,
be
confused
by
connect
and
let
you
through
I
just
you
know,
we
can
specify
all
kinds
of
mouse
protocols
and
then
the
cats
can
get
hungrier
and
then
we
can
specify
more
mouse
protocols,
but
I
don't
know
like
at
some
point:
I,
don't
know
where
that
spreads,
and
you
have
it.
You
have
a
vision
where
it
ends
well,.
B
Z
B
Z
Well,
one
of
the
reasons
why
we're
proposing,
like
actually
standardizing
transporting
Kayla's
records,
is,
and
also
we
do
intend
falling
back
as
soon
as
we
establish
trust,
because
it's
a
TLS
record,
it
becomes
really
really
easy
for
the
middle
box
to
explicitly
identify
work.
What
were
transporting
to
see
you
don't
see
it,
they
will
actually
be
able
to
look
at
look
at
the
byte
stream
with
it.
That
is
a
TLS
record.
I
know
exactly
what
this
is,
and
so.
Z
B
Z
F
J
Think
the
point
I
was
trying
to
make.
Is
it
the
the
more
common
case?
Is
that
when
the
middle
box
interposes
itself
in
TLS
layer,
it's
authenticated
under
CA
that
the
device
you're
the
client
doesn't
trust,
and
so
the
client
drops
the
connection
client.
You
know
the
middle
box
means
happy
to
let
the
thing
through
easily.
Even
if
the
middle
box
is
happy
to
lock,
you
can
clear.
The
client
can't
verify
the
server's
identity.
Yes,
you
can't
actually
get
out
right.
Z
J
J
The
posture
for
the
network's
you're
in
at
the
at
least
in
this
use
case
that
Owens
articulated,
so
that
that's
what
gives
me
some
hope
that
you
know
there,
because
this
is
designed
to
make
lives
easier
for
them,
both
middle
boxes
and
the
devices
that
it
find
them.
There
may
be
some
possibility
of
baton.
I.
R
You
have
mirror
formerly
a
middle
box
manga,
there's
a
reason
that
the
middle
box
is
decrypting,
the
traffic-
it's
not
because
it
is
fun
because
the
middle
box
wants
to
get
to
inspect
the
content,
then
you
go
and
make
the
continent
cryptic.
The
first
rule
of
firewall
is
firewall,
is
supposed
to
enforce.
Policy
cannot
understand.
What's
trying
to
do.
R
This
is
word
and
weird
you
drop
so
by
doing
this
extra
layer
of
TLS
or
any
any
other
kind
of
crypto
you're
making
you're
marking
your
traffic
is
weird
and
making
it
so
that
the
middle
box
is
going
to
drop
it.
Unless
the
little
drop
box
has
a
specific
rule
to
get
this
particular
traffic
go
through,
and
then
you
don't
need
to
decrypt
it
like
in
a
business
environment.
I
bought
a
new
samsung
fridge
in
this
empty
fridge
wants
to
talk
to
some
samsung
cloud,
for
whatever
reason,
that's
a
potential
effect.
R
Z
Understand
that
I
know
I
thought
middle
box
vendors
and
we
are
a
middle
box,
vendor
house
watch
for
middle
box
group
as
well
right
and
in
general.
If
the
middle
box
starts
to
drop
any
traffic,
it
doesn't
understand
that
I
think
maybe
this
is
encrypted.
I,
don't
know
what
this
is.
It's
going
to
break
you
money
application,
the
middle
box.
Don't
actually
do
that
blog
deployments?
Z
AA
This
way
is
I
understand
it
because
you
know
it'll
get
through
existing
middleboxes
and
you're
kind
of
like
opting
them
into
that
without
their
engagement
I'd
much
rather
see
something
with
engagement
with
the
middle
box
community,
where
you
can
work
out
something
that's
explicit,
and
that
has
a
future
rather
than
just
what
feels
kind
of,
like
hope,
based
engineering,
you're,
hoping
that
they
won't
decide.
Oh
we're
gonna
block
that
too,
and
so
yeah
I'd
still
have
a
lot
of
concerns
and
thanks
TKG
for
that
respect.
C
All
right,
so,
just
so
everybody's
clear,
we're
not
gonna
have
a
working
group
adoption
calling
this
draft
there's.
Obviously
more
discussion
needs
to
happen.
Do
that
I've,
no
problem
using
the
TLS
to
do
that?
A
gentle
reminder!
You
need
to
go.
There's
this
there's
a
thing
in
here.
So
thank
you
for
your
time,
but
please
expedite
leaving
the
room.
Thank
you.
