►
From YouTube: IETF100-CORE-20171113-1330
Description
CORE meeting session at IETF100
2017/11/13 1330
https://datatracker.ietf.org/meeting/100/proceedings/
B
A
Are
on
a
Monday,
so
I
probably
showed
you
do
a
little
bit
on
this.
There
are
some
idea
rules
that
we
are
working
under.
So
if
you
talk
about
technology
and
know
about
a
patent
claim
affecting
the
technology,
you
have
to
tell
us
or
you
can
decide
to
just
not
talk
about
the
technology
and
yeah.
The
whole
point
is
about
making
progress
on
drafts
where
we
hope
most
people
have
read.
A
Those
and
they're
weird
views
here
are
because
Apple
has
destroyed
the
you
know
to
a
little
bit,
so
I
had
to
convert
the
slides
to
PowerPoint
and
back
to
Kino
to
be
able
to
show
them.
So
the
brew
sheets
are
going
around
good
and
we
do
have
scribes,
so
those
people
who
ascribe
can
they
raise
the
hand,
take
notes,
nobody
take
notes,
but
yes
does
Alex
does
Marco.
Does
okay,
good?
Thank
you.
So.
A
So
the
note
well
applies
I
think
I
already
said:
what's
on
them?
Let's
talk
about
the
agenda.
We
have
two
meetings,
one
now
and
one
tomorrow.
At
the
same
time,
so
today
we
will
hover
around
work.
New
blast
calls
are
the
ones
that
have
already
been
done
or
once
that
will
happen
soon
and
at
the
end
we
will
have
a
quick
look
at
payment
over
cuerpos
Adrian.
Here,
thank
you
and
tomorrow
we
will
have
another
one
of
those
that
are
done
with
work.
A
A
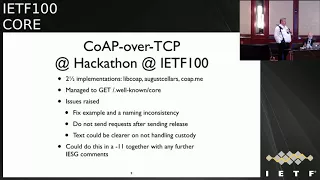
So
let's
go
right
into
the
first
item
new,
which
is
called
over
TCP.
Now
this
has
been
a
neverending
story.
We
completed
work
last
call
she
can
March
or
something
like
that,
and
we
had
a
lot
of
brouhaha
about
the
URI
schemes.
So
we
reached
an
agreement.
Finally,
how
to
handle
the
URI
scheme
problem,
and
the
current
draft
reflects
that
and
also
should
be
clearing
all
IES
three
discusses.
Can
you
have
a
quick
look
where
the
major
th
well.
A
A
There
is
also
a
dependency
on
a
small
housekeeping
document.
Hi
bye,
WebSockets,
we're
known
because
this
document
is
assuming
that
the
slash
start
well-known
mechanism
is
defined
for
WebSockets,
but
it
wasn't
so.
This
document
defines
that
and
we
will
see
we
are
aware
that
housekeeping
document
goes
but
forth
over
TCP
itself.
We
are
pretty
much
done
and
we
also
spend
a
little
bit
of
time
on
Saturday
getting
a
few
implementations
together.
A
There
is
a
pretty
well
cooked
implementation
now
in
lip
co-op,
so
that
that
was
a
little
bit
our
reference
implementation
on
Saturday
and
there
are
two
implementations
that
are
in
the
process
of
being
created,
one
from
Jim
and
one
from
me,
and
we
managed
to
go
to
the
place
where
we
could
do
a
get
on
slash
that
went
on
at
call
which,
because
of
the
fact
that
there
are
a
few
things
mandatory,
you
have
to
really
foil.
You
can
get
a
get
over
TCP.
A
A
That
is
kind
of
obvious,
but
it
could
be
made
explicit
and
also
the
text
could
be
made
a
little
bit
clearer
on
the
situation
where
you
do
a
ping
pong
and
you
have
a
custody
option
in
the
ping.
But
the
the
other
side
doesn't
want
to
do
a
custody
option
in
the
return,
and
there
is
currently
no
language
that
discusses
this
case,
and
the
point
here
is,
of
course,
that
the
delay
language-
that
is
there
for
the
case
where
the
custody
option
is
present,
doesn't
apply
to
this
case.
A
C
A
A
D
Next,
please
so,
first
of
all,
let's
take
a
look
at
the
status
of
the
document,
so
the
last
revision
is
0-2
and
the
motivation
for
this
last
version
is
that
a
few
months
ago,
highness
and
heads
up
on
0-1
before
initiating
a
working
group
last
call
so
the
the
word
the
heads
up
was
sent
to
the
core
and
eCPM
working
groups
and
also
to
the
ICC
research
group.
So
after
that,
we
received
two
reviews:
one
by
three:
oh
you're,
right.
D
D
So,
let's
go
through
the
updates
in
this
last
revision,
so
we
have
one
technical
update,
which
is
that
the
impact
of
strong
and
weak
estimators
is
now
tunable.
That's
the
impact
of
these
two
estimators
on
the
computation
of
the
RTO
as
a
result,
and
it
is
that
in
the
previous
version
of
the
document
we
we
used
some
fixed
constant
weights
for
the
contribution
of
the
weak
and
strong
estimators.
As
you
can
see,
those
weights
were
0.25
and
0.5.
D
However,
in
the
new
revision
we
have
two
neural
parameters
for
those
weights,
which
are
the
ones
highlighted
in
red,
W,
weak
and
W,
strong,
which,
by
the
way,
have
0.25
and
0.5
as
default
values.
Next,
please
so
we
also
have
quite
a
number
of
material
updates.
Actually
most
of
the
work
in
this
last
revision
has
been
editorial.
So,
first
of
all,
we
have
extended
the
abstract
in
order
to
explicitly
indicate
that
the
core
of
this
specification
is
an
RTO
algorithm.
D
So
previously
we
explained
that
in
coop
we
have
application
processing
times
that
contribute
to
the
coop
party
T,
which
in
addition
may
be
variable
with
different
distributions,
and
we
explained
in
version
0
1
that
this
is
something
that
doesn't
happen
in
TCP.
However,
now
we
have
also
added
that,
if
TCP
is
using,
the
latest
knowledge
means
there's
also
some
contribution
in
that
case,
to
the
RTT,
which
also
may
be
variable,
with
additional
delays
that
may
be
up
to
200,
milliseconds,
typically
or
in
theory
up
to
500
milliseconds.
D
Then
another
update
is
in
the
subsection
that
needs
a
discussion
when
we
describe
the
measure.
Rto
estimate
that's
for
the
2.2
and
in
order
to
better
motivate
the
need
for
the
weak
estimator,
which
is
quite
unusual
in
the
IDF.
We
now
explicitly
explain
that
the
weak
estimator
allows
to
update
the
RTO
estimator
when
our
T
DS
are
mostly
weak,
so
recall
that
we
carta
T's
are
those
for
which
the
sender
has
run
into
the
transmissions.
D
So
we
have
also
added
references
to
the
base
co-op
specification.
This
is
intended
for
readers
that
might
not
be
so
familiar
with
co-op
and
we
have
provided
pointers
to
specific
sections
and
also
to
specific
parameters
in
several
cases,
and
on
the
other
hand,
we
have
also
extended
section
7,
which
is
it
provides
the
security
considerations,
and
we
now
explain
that
an
attack
that
manages
to
prevent
packet
delivery
will
lead
to
an
RTO
increase
which
may
lead
to
a
performance
decrease.
D
Finally,
we
have
also
quite
a
number
of
updates
regarding
appendices,
so,
first
of
all,
the
old
appendix
which
was
entitled
aggregate
congestion
control
has
been
removed
from
the
document.
This
was
suggested
by
the
two
reviewers
mentioned
at
the
beginning
of
the
presentation,
and
this
also
matches
the
actual
intention
of
the
authors.
So
this
has
been
removed
and,
however,
we
have
added
three
new
appendices,
and
this
is
b
c
and
d.
D
The
first
one
appendix
b
provides
pseudocode
on
how
the
RTO
estimator
date
works,
also
on
how
the
RTO
aging
mechanism
works
and
also
for
the
variable
back
off
factor
on
another
appendix
we
have
added
some
examples
where
we
provide
numbers
on
the
calculations
for
the
week,
our
titties
for
the
variable
back
of
factor
for
aging,
and
we
also
provide
some
explanations
which
try
to
clarify
a
little
bit
the
properties
of
these
mechanisms.
And
finally,
we
have
added
the
last
appendix
which
provides
some
analysis
on
which
may
be
the
difference
of
the
values.
E
C
E
Developer,
if
I
care
about
so
the
reason
why
I
would
want
to
take
your
document
into
consideration
is
because
I
don't
want
to
have
this
stop-and-wait
behavior.
That
co-op
over
TCP
provides
me
with
the
in
star
equal
to
one
so
Biff
the
advanced
congestion
control
mechanism.
I
can
actually
change
that
and
have
a
value.
A
E
E
So
that
leads
to
my
real
question
is
I
think
it
would
be
nice
to
indicate
on
at
what
point
a
developer.
Shoe
should
actually
move
away
from
co-op,
plus
that
type
of
extension
took
over
UDP
to
a
model.
A
co-op
over
TCP,
like
co-op
over
DCP,
was
motivated
by
a
fired
rubber
or
firewall
traversal,
but
there
may
be
other
motivations
as
well
that
relate
to
the
congestion
control
or
specifically,
to
this
behavior
of
sending
multiple
requests,
which
is
sometimes
also
annoying
just.
Does
that
make
sense
what
I'm
saying.
E
E
E
Yeah
fully
understand
that,
but
and
that
big
TCP
guidance
document
gives
me
the
impression
that
TCP
is
also
highly
tuneable
and
there's
there's
a
lower
pond
as
a
higher
bar
and
so
I
don't
see
what
the
overlap
is
between
what
is
going
on
here.
What
is
going
on
in
the
elevator
with
returns
terms
of
users
of
a
transport
for
the
call
and
I
think
there
could
be
some
additional
clarification
of
it,
specifically
if
you're
not
like
working
full-time
in
a
transport
area.
E
A
E
A
A
D
A
A
So
the
next
step,
of
course,
is
doing
the
working
class
call,
so
I
managed
to
decide
when
when
to
do
that,
and
the
idea
is
to
make
sure
that's
working
last
call
is
done
in
a
way
that
the
the
transport
working
groups
that
have
indicated
interest
and
also
the
convention
control
resource.
A
research
group
is
in
the
loop
of
that
working
across
coil
and
I.
Think
Alexei
has
something
to
say
about
how
his
end
wants
to
handle
the
history
process.
F
A
G
Hello,
do
you
hear
me?
Yes,
we
do.
Thank
you.
My
name
is
Christina
Moses
and
I'd
like
to
present
the
current
status
of
the
resource
directory
document
and
the
associated
resource
directory
DNS
SD
linking
parts
I
go
I'll
go
through
the
through
the
recent
changes
briefly
and
use
them
as
a
set
up
of
to
show
where
we
are
with
the
document
and
to
ask
some
questions
about
how
we
can
proceed
there.
There
will
be
a
part
about
DNS,
St
2,
which
will
be
after
the
actual
rd
text
a
slide.
Please
one
change.
G
An
RD
can
also
come
into
play
when,
when
multicast
is
unavailable
or
when
there
are
other
reasons
why
you
don't
want
to
get
that
information
directly
from
the
node
dns
SD
is
not
directly
here
in
the
motivation,
because
I'll
show
later
that
we
can
do
everything
we
need
for
exporting
to
DNS,
st
from
what
an
RT
can
do
if
it
is
designed,
without
particular
consideration
for
our
DD
n
SSD
next
slide,
please.
So
what
is
an
inner
resource
directory?
And
we
flashed
out
how
this
looks
textually
now
as
well.
G
The
ERT
contains
links
and
the
top
line
shows
how
they
look
like
in
an
unco
file.
They
have
a
link
target
at
the
left,
which
is
evaluated
to
a
full
URI.
They
have
a
link
link
source,
which
is
usually
the
the
well-known
core
document
or
the
the
device
itself
and
in
most
Katyn
most
common
cases,
it's
implied
and
has
a
relation
or
some
other
link,
attributes
and
attributes
that
describe
the
target
so,
for
example,
resource
type
we
transfer.
G
We
take
those
links
up
in
the
resource
directory
and
Express
and
replicate
them
semantically,
which
means
that
the
serialization
might
look
a
little
different.
For
example,
the
anchor
as
in
the
bottom
line
needs
to
be
explicitly
stated
because
the
document
comes
from
somewhere,
where
this
is
not
obvious,
but
some
of
some
things
like
the
rail
relate
like
the
rel
equals
hosts,
can
still
be
implied
by
default.
So.
B
B
A
Well-Known
core
entry
would
just
say
this
part
here,
and
this
is
default.
It's
on
the
with
link
relation
hosts
and
the
empty
anchor.
Those
are
the
default
they
use
and
at
the
point
that
Christian
is
trying
to
make
is
that
this
can
stay
at
its
default
value,
but
the
anchor
where
you
actually
has
to
change,
because
in
this
case
it's
the
when
on
call
environment
that
provides
the
device
itself,
but
in
this
case
it's
the
resource
directory.
A
G
If
you
go
to
the
next
slide,
please
there
are
some
other
entities
in
the
resource
directory,
which
is
endpoints
and
groups,
and
points
is
mainly
what
using
to
manage
that
a
particular
device
registered
there
and
can
have
some
additional
properties
that
are
available
for
querying
and
groups
which
are
aggregates
of
endpoints.
That
typically
share
a
multicast
address
the
next
slide.
G
Please
all
these
entities
can
be
used
in
queries
across
the
resource
directories,
so
you
can
look
for,
as
in
the
first
example,
query
look
for
groups
which
contain
a
particular
node,
and
then
you
get
a
link
to
that
group
resource
to
the
place
where
the
group
is
registered
with
some
additional
data
about
the
group
like
what
is
its
multicast
address?
What
is
it?
Is
its
group
name?
Is
it
in
a
particular
domain?
G
G
So
this
again
gives
us
a
link
to
one
registration
resource
which
is
not
particularly
useful,
as
well
as
a
link
to
a
courier
but
contains
additional
information
in
the
metadata.
For
example,
this
has
an
endpoint
type
or
what
is
the?
Where
is
this
registered
from
from
and
most
importantly,
it
contains
the
links
which
can
be
queried
not
only
by
querying
their
their
attributes.
So,
for
example,
you
could
have
a
lookup
slash
rest
query.
G
Rt
is
temp
and
get
all
temperature
resources,
but
you
can
also
query
all
resources
that
reside
on,
say,
n,
pound
endpoints
that
are
wall-mounted,
as
in
this
example,
next
slide.
Please
we
we
did
some
more
changes
to
I
won't
go
through
every
single
of
them,
but
some
are
particularly
noteworthy.
We've
added
an
information
model
that
that
kind
of
provides
the
whole
set
up.
We,
as
I've
shown
on
on
the
first
slide,
we've
nailed
down
how
the
resolution
of
your
eyes
work.
So
what
is
what
is
result?
G
What
does
need
to
be
resolved
when
how
our
relative
references
are
evaluated
and
we
removed
sections
about
how
those
registrations
can
be
changed,
because
we
don't
have
suitable
content
formats?
For
that
yet
so
we
can't,
we
can't
specify
how
this
works
anyway,
and
we
prefer
to
specify
how
the
general
thing
works
and,
if
account,
if
and
when
a
content
format
gets
along.
G
That
allows
simple
modification
or
observation
of
collections
of
links
which
everything
in
the
resource
directory
basically
is,
then
this
can
be
added
to
the
resource
directory
without
further
changes
on
the
of
the
information
model
and
lookup
and
next
slide
please.
So
what
are?
What
are
the
the
next
steps?
We've
published
version,
12
document
a
few
weeks
ago.
Next
slide,
please,
we
do
have
some
changes.
We
know
about
that.
G
We
invite
you
to
join
us
on
the
issue
tracker.
All
the
those
open
issues
and
also
the
pending
ones,
are
described
there,
and
it
would
be
very
good
to
have
input
from
the
working
group
on
on
those
and
next
slide.
Please,
we've
really
received
comprehensive
reviews
from
Jim
shot
and
Hannah's
about
the
11
document.
Thanks
for
that,
but
I
think,
given
that
we'd
like
to
go
for
working
group
last
foursome,
it
would
be
good
to
have
more
reviews
and
also
to
get
input
from
people
who
are
actually
implementing
the
resource
directory.
G
A
As
to
expound
on
that,
now
is
a
good
time
to
implement
this
stuff,
because
we
have
really
cleaned
up
the
document.
A
lot
and
at
least
for
me
as
a
co-author,
the
situation
has
started
that
they
understand
what
the
resource
directory
is
about
and
how
it
works.
So
I
that
implement
dusts
can
now
be
in
the
same
situation.
G
Know
you
can
you
can
do
a
link,
registration
and
re
registration,
and
this
is
currently
the
only
way
to
do
it
and
the
read
registration
is
semantically
almost
equivalent
to
dropping
your
registration
and
registering
in
you,
and
this
is
what
you
can
do,
even
without
explicitly
dropping
your
registration.
So
you
can
just
pull
to
the
to
the
directory
resource
again,
as
you
would
do,
for
example,
after
a
reboot
when
you've
forgotten
that
you're
registered
and
then
the
Rd
will
accept
that
registration
and
now
have
an
updated
set
of
set
of
links
and.
E
G
E
G
You
don't
wanna,
live
time
expires,
you
can.
You
can
always
keep
your
registration
alive,
so
you
can
just
post
to
the
to
the
registration
resource
you've
obtained,
but
it
will
need
to
be
an
empty
post
and
it
can't
change
the
links
can't.
It
can't
change
the
links
now,
but
you
can
register
a
new
with
a
new
set
of
links
so.
A
E
E
Top
I
was
hoping
that
in
earlier
versions
of
the
document
that
might
be
presented
at
that
time,
patch
wasn't
available.
So
my
hope
was
that
once
the
patch
was
available,
never
actually
do
different
versions
in
their
brief
and
without
patch
that
we
would
once
patches
available,
would
actually
switch
over
to
pageant.
Allow
that
patch
to
be
used
also
for
a
registration
interface.
That
sounded
like
obvious
to
me,
but
maybe
it's
not
so.
A
A
Interesting
discussion
at
the
OCF
meeting
on
Friday
how
to
do
that,
because
the
the
the
current
March
page
document
is
geared
up
for
having
maps
of
things
and-
and
you
essentially
replace
things
in
there
by
giving
their
keys,
but
those
links
it's
on
our
maps,
they're
arrays.
So
we
we
need
a
variation
of
merge
patch
that
that
grabs
into
an
array
finds
an
element
of
the
array
based
on
one
of
the
keys
in
the
map.
That
is
the
element
of
the
and
replaces
that,
and
we
have
to
write
that
that
must
have
been
a
discussion.
H
One
of
the
things
that
really
worries
me
and
I'm,
not
too
sure
I
want
to
see
the
are
deep,
actually
progress
until
we
figure
out
how
it's
supposed
to
interact
with
the
new
URL
schemes
so
that
we,
because
I'm
not
too
sure
you
want
to
you
if
something
is
reachable
by
multiple
schemes.
I,
don't
know.
That
means
you
end
up
with
multiple
endpoints
and
so
forth,
and
what
that
means
in
terms
of
anchors,
if,
if
you're.
G
Registered
the
current
idea
is
that,
if
you're
registering
with
multiple
your
a
schemes,
you
will
still
have
only
one
registration
and
the
pending
protocol
negotiation
document
will
describe
how
you,
how
you
add
your
alternative
transports
and
how
you
can
query
them
in
the
resource.
Look
up
so
that
you
finally
get
a
resolved
link
based
on
your
preferred
transport,
when
you're
querying
the
resource
directory.
H
I
They
favor
what's
the
current
state
of
the
protocol
negotiation
document?
No,
there
was
how
close
is
it
to
being
done
because
I?
What
I
hear
Jim
saying
is
that
you
have
to
treat
them
together
and
that
if
you
haven't
reviewed
them
both
at
the
same
time,
then
you're
skeptical
that
this
one
came,
whereas
before
that
one
right,
I
think
that's
what
you're
saying
Jim,
and
so
the
real
question
is,
is
the
other
one
also
ready
for
working
request?
I
A
So
we
know
how
ocf
does
this.
We
have
an
existence.
Proof
edit
can't
be
done,
but
it
still
has
to
be
done.
So
maybe
we
can
copy
as
much
as
possible
from
from
the
ocf
solution
of
the
ER.
That
would
be
my
personal
preference,
but
that
discussion
needs
needs
to
be
here.
Yes
and
I.
Take
from
the
input
that
that's
really
a
blocking
point
for
finishing
Rd,
because
we
need
to
understand
that
now
there
are
two
kinds
of
alternative
transport
situations.
A
There
are
situations
where
you
have
transports
that
are
mostly
equivalent
in
most
of
their
technical
parameters,
so
one
may
go
through
a
firewall,
the
other
one
may
not,
but
but
once
it
works,
it
doesn't
really
make
a
big
difference
which
one
you
use
and
we
have
other
situations
where
we,
for
instance,
combine
UDP
access
with
SMS
access.
That's
a
very
different
situation
and
I
think
we
have
to
make
sure
that
we
actually
address
both
cases.
A
Yeah,
so
did
what
I
get
from
this
is
that
we
have
enough
substance
here
that
we
actually
could
start
doing
some
intro
plus
testing.
We
didn't
get
this
into
place
in
time
for
this
hackathon,
but
we
might
want
to
use
the
time
between
now
and
the
next
ITF
to
actually
do
a
little
bit
of
virtual
interrupt
testing
between
our
implementations,
so
how
we
do
that
we
have
to
find
out,
but
I
think
it
would
be
a
good
thing
to
start
with
that.
Now:
okay,
just
yes!
Yes,.
G
What
what
what
exports
to
DNS
SD
unconditional
needs
is
some
support
from
from
the
origin
server
so
from
the
from
the
endpoint,
that
is
providing
the
resources
to
say
that
it
wants
to
be
exported
and
to
provide
instance
names
because
they
can't
be
derived
from
anything
that
is,
that
is
present
in
the
resource
directory.
Otherwise,
the
current
document
that
is,
that
that
should
be
published
about
today,
describes
this
as
happening
from
a
resource
directory,
but
actually
it
can
equivalently
work
from
the
well-known
core
data
as
well.
G
So
while
an
exporting
agent
would
typically
piggyback
on
an
RD,
it
can
could
just
as
well
do
multicast
discovery
and
export
whatever
it
finds
from
there
to
DNS
st
how
this
works
has
not
really
changed
since
DNS
st
was
a
part
of
the
resource
directory
I'm
showing
next
slide.
Please
I'm,
showing
here
on
the
top
a
typical
example
of
what
it
could.
What
a
resource
look
look
up
could
look
like
in
the
in
the
Rd,
and
the
bottom
half
represents
that
information
in
Indian
SSD.
G
So
our
next
slide,
please
leave
the
information
gets
gets
moved
around
a
bit.
But
what
is
what
is
in
the
in
the
DNS
SD
record?
Is
you
DNS
SD
type
that
is
derived
from
the
resource
type
it
is
registered
in
the
domain,
which
is
shown
in
green?
It
uses
the
instance
from
from
the
from
the
link
form
a
document
as
an
instance
name
if
there
is
a
if
there's
a
sub
type
to
the
resource
type
that
can
also
be
exported
to
the
to
the
to
DNS
SD,
which
is
the
proper
part.
G
The
second
is
the
mapping
to
the
actual
address,
which
happens
in
a
server
and
a
text
record
to
form
the
complete
URL
again,
if
the,
if
the
link
is
not
formed
from
from
a
DNS
name
as
the
authority
which
is
shown
in
red
here,
it
could
also
be
derived
from
data
in
the
resource
directory,
but
then
again
could
be
derived
in
in
any
other
way,
just
as
well,
because
there
just
needs
to
be
a
or
quad
a
record
for
the
thing
that
the
server
record
points
to
next
slide.
Please.
I
So
a
question
on
the
part
in
blue,
which
is
the
Sto,
and
so
this
example
uses
an
RT
value
with
only
one
dot
in
it.
There
exist
plenty
of
RT
values
that
are
registered
with
IANA,
that
I
have
two
or
even
three
dots
in
them.
So
the
question
is:
when
going
to
DNS,
is
there
any
problem,
because
you
have
the
underscore
sto
mm-hmm?
Is
there
a
problem?
If
that
has
dots
in
the
middle
of
it
funny
fun
thing
is.
G
It
isn't
because
the
way
T
and
s
SD
works
is
it
doesn't
work
on
the
on
the
serialization
of
the
DNS
record,
which
usually
uses
a
dot
to
separate
the
segment,
but
it
works
on
the
on
the
actual
DNS
messages
which
have
fields
that
are
not
dots
delimited.
So
there
can
be
a
dot,
for
example,
in
the
instance
name
or
the
resource
type.
G
G
Names
and
implementations
largely
support
that,
but
there
is-
and
this
now
brings
us
to
the
next
slide,
still
the
open
question
of
how
those
things
should
be
mapped
exactly
because
what
the
issue
we
are
having
here
is
that
for
resource
types
there
is
a
registry,
so
you
could
register
the
sto
dot
anything
resource
type,
and
there
is
a
registry
for
DNS
as
these
service
types,
which
is
not
the
same
registry
and
which
is
not
coordinated
and
most
entries
or
many
entries
will
not
need
to
be
in
both.
So
the.
I
Question
question
yeah
I
realize
I
may
have
phrased
my
question
slightly
differently
than
I
should
have,
but
you
probably
answered
the
question:
I
was
asking
what
I
should
have
said
was
there
exist,
RT
values
with
multiple
dots
and
here
it
into
a
sto
plus
a
temp
piece
and
I
should
have
asked.
How
do
you
know
which
dot
discipline
just
boils.
G
G
If
resource.type
is
unknown
to
the
dns
SD
exporter,
it
should
not
be
split
by
any
dot,
but
it
should
be
exported
as
some
type
coop
UDP,
with
the
whole
resource
type
of
the
subtype
and
particular
as
a
particular
s.
Do
so,
whoever
registers
a
resource
type
can
say,
can
also
register
a
DNS
SD
type
and
their
sub
types,
and,
along
with
those
registrations,
provide
a
pattern
in
which,
by
which
those
resource
types
can
be
converted
to
DNS
SD
types.
G
G
G
G
C
A
A
A
Let
me
just
as
an
author
comment
on
the
pace
in
which
this
document
has
gone
on
for
a
long
time.
We
have
had
essentially
a
little
bit
of
progress
at
each
eye,
each
EF,
but
nothing
in
between,
and
if
you
look
at
the
commits
that
on
the
github
repository
now,
it
really
has
taken
off
and
we
have
significant
progress
and
we
want
to
keep
up
that
pace
and
and
finish
this
work
so
again.
Comments
like
like
those
from
from
tamiya.
A
A
J
So,
on
a
very
macro
level,
you
can
see
the
main
drafts
that
are
part
of
this
package.
Here,
it's
a
little
bit
offset
so
basically
so
here
we
have
the
tree
main
draft
documents
that
are
the
yang
to
see
bro
mapping
this
draft
and
come
by
itself.
So
we
had
some
actions
from
the
last
time
which
were
riveted.
J
Drafts
perform,
interrupts,
deployed
asset
registry
like
down
to
the
straight
to
the
point
so
on
the
update
and
on
the
review
of
The
Drifter
different
drafts,
the
yang
to
seaboard
draft
hasn't
moved
because
one
of
the
things
that
we
said
is
these
three
drafts
basically
they're,
moving
in
as
a
package
right
the
moment
that
we
have
some
inter
up
and
and
that
we
see
that
everything
is
working
weld
and
we
do
the
working
group
last
call
for
all
the
three
of
them.
So
basically,
here
we
are
ready
for
working
group.
J
J
J
To
be
able
to
I
don't
need
to
turn
around
always
so
we
have
existing
implementations,
as
I
said,
since
the
last
time
we
had
some
and
right
now
we
are
really
improving
our
implementations,
so
we
have
two
implementations
that
are
proprietary
implementations.
One
is
go
line.
When
you
see
we
have
two
partial
implementations
that
we
had
some
knowledge
from
the
last
IDF
and
one
of
the
goals
was
for
this
IDF
to
have
an
interrupt
with
at
least
two
implementations
of
them
and
to
have
a
hackathon.
B
J
Our
initial
expectations,
because
some
of
most
of
the
key
people
that
are
were
not
able
to
come
here
to
Singapore,
and
so
we
needed
to
scale
back
on
this,
but
we
did
our
best
so
I'm
here
to
present
what
is
our
best
at
this
point.
Well,
after
several
changes
and
many
many
discussions,
we
actually
managed
to
do
a
virtual
Interop
over
the
internet
between
two
implementations.
J
So
the
first
point
here
is
that
one
of
the
implementations
actually
manages
to
run
a
full
calm
eye
with
a
subset
of
the
functions
that
are
fetch
patch
and
post
for
our
pcs
running
on
ipv6.
The
other
one
is
full,
but
you
know
can
interoperate
with
itself.
So
it's
not
much
enough
interoperability
between
two
different
implementations.
So
the
point
that
we
really
did
was
to
say:
okay,
we
need
to
have
at
least
these
implementations
to
be
able
to
show
that
they
are
running.
J
So
we
have
fetch,
which
is
the
basic
of
everything
where
you
can
go
and
can
really
retrieve
information
from
the
server.
So
here
the
client
and
you
can
retrieve
information
from
the
server,
so
the
type
of
request
that
was
so
we
needed
to
have
a
use
case
a
test
case,
so
we
was
using
the
module
ITF
system
and,
more
specifically,
we
were
just
trying
to
get
the
system
date
right.
What
is
the
current
time?
J
B
J
Are
able
to
fetch
single
values,
fetch
a
container
fetch
two
values
in
one
single
request
that
are
announced,
two
separate
values
whenever
we
try,
so
we
found
some
issues
with
some
of
the
implementation,
so
we
are
now
it's
like
minor
bugs.
We
are
fixing
this,
and
with
this
we
actually
managed
to
validate
the
yang
to
see
bor
string,
mapping
derive
types
container
representations,
and
we
have
also
validated
the
delta
encoding
and
having.
J
J
So
the
first
thing
is
that
ITF
system
may
may
not
may
not
be
the
may
not
be
the
easiest
module
to
use
as
an
interoperability
basis,
and
one
of
the
things
is
basically,
you
know
we
want
to
test
everything
we
want
to
say:
okay
is
there,
this
is
an
integer.
This
is
a
string.
This
is
slow.
This
is,
you
know
we
want
to
be
able
to
have
like
a
basics,
all
the
things
that
can
be
presented
present
in
a
yang
module.
J
So
one
of
the
things
that
we
are
starting
to
do-
and
this
is
starting
again
right
now,
so
we
are
ramping
up.
We
had
so
to
give
you
a
short
idea
of
the
timeline
that
we
had
until
the
past
IGF.
We
had
be
weekly
meetings,
so
we
were
managed
to
advance
pretty
well
from
since
the
last
IDF
to
this
one.
It
was
like
summer
and
all
these
kind
of
different
issues
that
that
happened.
So
we
were
less.
We
didn't
manage
to
have
this
beautiful
virtuous
meetings
and
right
now
we
are
restarting
them
again.
J
So
that's.
The
first
issue
that
we
would
like
to
address
is
to
have
this
basic
young
modules
in
order
to
test
this
functionality
on
the
protocol
level,
and
here
this
is
a
question
also
to
have
maybe
net
mod
have
already
established
such
a
baseline
yang
modules
for
testing
I'm,
not
aware,
but
now
I
see
Eric
saying
no,
so
no
so
maybe
it
is
something
that
we
could
contribute
also
to
the
network
community.
J
So
that's
the
first
point.
The
second
point
is
that
you
know
these
famous
Delta
encodings
that
are
super
efficient
and
are
really
really
nice
and
we
really
do
like
them,
and
one
of
the
things
is
that
and
with
Andy
we
were.
He
was
also
saying
this
in
the
past.
It
could
be
a
little
bit
tedious
when
we
are
trying
to
debug
complex
requests
and
complex
queries
that
have
different.
J
You
know
you
have
several
sub
trees
and,
and
you
could
get
a
little
bit
lost
in
case
you
you're
just
so
lonely
watching
that
watching
the
payload
and,
of
course,
with
with
the
right
tools.
This
is
not
a
problem,
but
we
are
not
there
yet
having
the
full
tools
that
we
have.
All
the
you
know,
the
burgers
that
keep
everything
in
place,
so
one
of
the
things
is
that
we
are
really
would
like
to
propose
is
to
have
this
option
in
the
server
and
or
the
client
that
can
say,
okay.
J
Well,
you
know,
I
would
like
to
disable
for
this
session,
this
the
Delta
encodings,
and
then
we
go
and
tag
the
sits
with
seaport
actor
39
that
has
been
allocated.
It's
an
identifier
and
it's
to
just
to
indicate
hey.
This
is
the
sit.
It
is
not
the
Delta
said
it
is.
It
is
directly
to
sit
and
the
same.
The
simplest
thing
in
this
is
that
you
know
you
in
your
code.
You
just
need
to
whenever
the
code
is
parsing
it
you
know
they
don't
need
to
do
anything
special.
J
They
are
just
doing
Delta
Delta,
oh,
that's,
not
a
delta!
So
I'll
just
take
the
value
as
it
is
and
I
continue.
So
it
is
a
pretty
straightforward
solution.
It
helps
debugging
and
you
know
you
run
your
server
in
advance
in
the
bug
environment,
you
debug
and
then,
whenever
you
decide
that
it's
good
well,
it
is
able
it
by.
A
Reaction
to
this
is
you
can
do
that,
but
don't
kill
anyone
I
mean
you
really
should
fix
up
your
to
it
store
handle
this.
It's
not
that
hard
and
I
think
doing
this.
This
take
39
heck
is
about
the
same
amount
of
work
as
fixing
up.
Those
two
is
so
why
don't
just
fix
up
those
two
it's
and
do
the
right
thing
so
I.
J
Think
one
of
the
things
is
good
when
we
want
to
have
an
interrupt,
is
to
I
mean
we
can
say:
okay,
we're
going
to
do
this
dirty
hack,
but
if
you
can
have
it
on
your
interrupts,
that
would
be
really
cool.
So
please
everyone,
hack,
you're
good,
and
then
you
know
just
the
hack
it
so
yeah.
Somehow
III
agree
with
this.
But
it's
it
is
a
very
neat
solution.
I,
don't
see
any
back
and
any
any.
J
A
A
L
J
Ok,
so
that's
a
point
point
taken,
that's
improved,
so
another
point
that
we
had
from
this
first
interrupt
was
that
actually
we
have
this
minimal
set.
That
is
pretty
straight
forward
and
that
allows
us
to
have
the
full
functionality
of
comma
and
the
one
of
the
points
that
we'd
like
to
do
to
just
state.
J
So
this
way
we
can
like
really
go
with
that
with
comma
minimal,
come
I,
extend
it,
and
you
know
we.
Basically,
it
boils
down
to
this
like
we
have
these
implementations
and
we
will
be
very
happy
to
have
other
people
having
different
implementations,
but
until
we
have,
this
is
the
only
thing
that
we'll
be
able
to
interrupt.
J
B
J
Then
we
started,
you
know
like
building
the
whole
the
whole
system
around
it.
I
can
declare
partial
success
so
yeah
we
started
it.
We
have
the
yang
module
and
everything
is
working
and
then
a
partial
failure,
because
actually
I
made
some,
maybe
not
the
best
choices
in
the
use
of
the
in
the
choice
of
the
Python
tools
that
were
out
there,
and
so
we
reached
or
yeah.
J
We
reach
to
some
point
where
we
understood
that
the
the
choices
of
the
basic
libraries
that
we
chose
for
Yang
actually
makes
it
super
difficult
to
make
the
Seabourn
encoding.
Well,
so
I
need
to
go
back
a
step.
This
was
after
discussion
with
the
medmont
team
and
basically
rebase
the
development
of
the
of
this
part
with
ydk,
which
is
the
yang
development
kit
which,
based
on
your
yang
file,
produces
Python
code.
So
this
is
the
only
thing
that
needs
to
be
done.
J
So
I
was
really
hoping
that
we'll
be
able
today
to
come
and
say:
hey.
We
have
this
working
baseline
implementation,
it
needs.
You
know
it's
interrupts
with
these
other
parts,
but
I
think
that
we
should
like
step
back
a
little
bit
and
prepare
for
for
the
next
for
the
official
hackathon
that
will
take
place
at
the
ITF
101
and
where
most
of
the
people
that
are
actually
quite
active
and
which
and
who
are
working
a
lot
at
in
come
on.
Come
I
will
be
there.
J
So
that's
about
the
hackathon,
and
so
as
I
said
next
steps
be
weekly
meetings
from
now
on.
That
will
ensure
that
we
have
the
full
interrupts
in
London
with
the
fetchin
patch,
so
something
like,
as
I,
said,
to
call
my
minimum
and
have
the
hackathon
also
and
prepared
the
open-source
implementation
from
their
own.
J
So
these
are
the
next
steps
and
on
the
yang
to
see
board
documents,
I
get
the
feeling
that
we
will
not
be
introducing
the
option
39,
it
looks
so
cool,
it's
off
some
problems
and
the
option
worst
was
there,
so
okay,
so
that
one
is
done
and
on
the
Kamiya
documents,
what
we
could,
what
we
propose
to
do.
So
this
is
like
an
option,
and
this
is
something
I
would
like
to
hear
the
working
group.
J
If
you
have
any
opinion
on
this,
would
you
like
to
see
how
my
minimal
and
come
I
extended
if
this
will
give
come
I
minimal,
like
it's
just
going
to
be
like
removing
a
lot
of
text
of
the
current
document,
simplifying
some
stuff
and
having
three
basic
operations
and
then
having
like?
Maybe
a
second
section
that
does
this
or
a
second
document,
that
that
does
the
firt
that
that
you
is
the
first.
A
A
It
shows
how
to
to
use
them
with
comai.
So
this
is
all
wonderful,
but
it's
a
lot
of
complexity.
I,
don't
know
how
many
media
types
we
are
generating
there
and
it's
not
really
solving
a
big
problem.
So
maybe
this
minimal
form
is
a
good
thing,
but
maybe
another
way
to
look
at
this
is
it
might
make
sense
to
edge
catch
as
as
a
third
message
that
we
want
to
support,
but
that's
it.
So
we
don't
really
want
to
do
the
other
things.
A
J
I
really
yeah
that
that's
something
that
we
really
looked
at
it
and
we
discussed
about
it,
and
the
thing
is
that
in
get
you
have
a
URI.
So
if
it's
simply
having
a
gear
to
sit,
so
you
can
forget-
and
you
want
to
get
one
item
that
is
identified
by
one
sit.
It's
super
easy,
there's,
no
problem
with
this.
The
question
is:
if
you
want
to
do
a
get
on
an
item
that
is
part
of
a
list.
A
J
J
Maybe
it
could
make
sense
if
you
want
to
say
okay,
you
know,
I
can
only
get
like
the
first
level
of
the
things
like
if
I
have
a
first
level
element
like
if
it's
a
container
I
can
do
a
get
and
I'll
get
the
whole
stuff.
If
it's
an
item,
I
can
get
a
single
leaf.
I
can
get
this
leaf,
but
if
I
want
to
get
like
the
first
item
of
a
container,
maybe
now
this
one
I
could
get
also.
J
A
Examples
actually
they
get
so
I
just
wanted
to
throw
this
in
the
room
that
maybe
we
don't
want
to
do
a
minimal
and
an
extended,
but
we
won't
simply
do
the
right
thing
and
that
may
be
exactly
fetch
and
match.
Odd
may
be
fetching
fetch,
plus
more
method
like
but
looks.
Let's
look
through
the
examples
and
see
what
actually
makes
sense.
We
don't
have
to
support
all
of
risk
just
because
it's
there,
okay.
J
J
So
that's
on
Carmi
and
now
on
Sid,
so
cities,
the
identifiers
that
are
used,
income,
I
and
here
just
a
short
reminder.
So
ass.
It
is
simply
a
64-bit
number.
That's
of
course
it
is
a
64-bit,
but
in
because
it's
expressed
in
C
bar
it
can
be
on
one
byte
to
buy
it's
four
bytes
and
and
so
forth.
So
it's
pretty
dynamic.
It
is
a
file,
so
you
have
like
a
young
schema.
J
That
represents
the
reason
that
that
map's,
the
reason
or
C
bar
if
you
want
and
then
you
have
the
lifecycle
of
a
model
and
you
have
allocation
policies.
So
you
have
a
two-tire
allocation
policy
that
you
have.
The
first
one
is
managed
by
Ayana.
It's
called
the
mega
range
registry
and
you
know
Ayana
allocates
chunks
of
1
million,
sits,
and
then
we
have
a
second
level
registry
that
people
go
and
you
know,
can
much
more
actively
allocate
range
sub-ranges.
J
So
since
the
last
time
we
have
these
three
that
are
solved
and
this
one
that
was
somehow
you
know
we
were
not
here.
Is
it
really
solved?
Are
there
any
problems?
So
we
discussed
again
and
again
with
with
I
Anna,
we
discussed
also
it
so
many
people
and
I
said.
Ok,
you
know
we
should
not
be
just
keeping
the
working
group
last
call
for
this.
J
These
are
things
that
could
be
solved
when
it
comes
to
Ayana
and
then
we
say:
ok
well,
there
is
this
detail
or
this
detail
that
should
be
will
be
changed,
but
generally
the
document
is
good.
So
that's
that
it's
good.
We
have
not
have
not
changed
anything
so
right
now.
The
next
thing
is
okay.
So
what
about
it?
Yeah
Peter.
L
J
Thank
you
Peter.
So
that's
actually
an
excellent
question,
so
you
know
so
whenever
you
have
a
yank
file,
you
have
a
tool
to
generate
the
seed
files
of
the
correspondence
it's
a
tool.
That's
like
a
plugin
for
PN.
So
it's
like
it's
the
super
standard
thing
that
people
use
for
yang
and
it's
just
like
a
plugin.
It
is
not
yet
in
the
main
branch,
but
it
has
been
stable
for
a
long
time
now.
So
what
we
did
was
basically
we
put
it.
We
made
a
web
interface
to
around
it.
J
We
wrapped
it
up
and
it
works,
and
since
this
weekend,
so
this
was
like
the
partial
hackathon
that
we
had
around
some
several
virtual
places.
We
have
also
set
up
the
seed
registry,
so
this
is
the
first
seed
registry
that
is,
that
is
out
there.
That
is
in
some
kind
of
a
minimum
value
of
MVP
Mode
minimum
well
protected.
J
So
we
will
start
operating
it
a
little
bit
illegally,
just
to
see
how
it
goes
right
in
the
second
million
of
the
of
the
sit
registry,
because
there
is
for
the
moment
there
is
no
megasuck
mega
range.
Its
registry
Ayana
has
not
created
this,
so
we
cannot
legally
obtain,
like
1
million
blocks,
to
start
to
play
with.
So
what
we
are
going
to
do
is
we
are
going
to
say,
hey.
We
pretend
as
if
we
have
this
thing
by
the
time.
The
last
were.
J
The
working
group
last
call
passes
and
Ayana
goes
all
through
the
whole
process
and
the
mega
range
registry
is
created,
but
in
the
meantime
we
will
get
the
feeling
and
people
will
start
using
it,
and
hopefully
you
know
it
will
just
get
translated
at
the
moment.
Everything
is
in
place.
We
will
just
say:
ok,
yeah,
it's
there.
So
we
have
this
too.
A
J
A
J
Doesn't
know
what's
going
to
do,
and
so
this
is
the
DCT
interface,
so
we
have
so
this
is
the
best,
the
basic,
the
login
page.
So
this
was
this
has
been
existing
for
like
a
couple
of
months
now,
so
you
can
come
and
then
you
can
click
on
login
all
this
stuff.
So
you
come
in
you
register,
so
you
fill
in
some
information
about
yourself
like
from
which
country
and
so
forth.
We
have
a
super
secure
way
of.
M
J
J
So
you
have
this
welcome
page
and
here,
if
you,
if
you
go
to-
and
you
see
so,
this
could
be
sensors
Peters
question
here.
You
have
the
tools
right
away.
You
have
seat
file,
generation,
sit
validate
and
sit,
consistency
check.
So
if
you
click
on
these
links,
you
don't
need
to
go
on
to
login.
To
do
this.
You
just
provide
your
rank
file
on
a
web
interface
and
then
it
produces
you
to
sit
visit.
J
So
what
you
need
to
do
is
you
need
to
login
request
a
seat
range
so,
for
example,
your
the
10
C
user.
You
go
there
and
use
the
10th
company
and
you'll
get
the
range
from
1
million
ten
thousand
to
1
million
11.
So
these
are
your
1000
seats
and
then
you
go
here
on
this
file
generation.
You
click
and
you
say:
okay,
I
have
these
thousand
seats.
This
is
my
yang
file
and
then
the
tool
populates,
the
produces
the
seat
file
that
corresponds
to
it
and
puts
the
correct
seat
files.
N
A
J
J
J
Other
time
zones
were
updating
stuff
and
right
now
it's
not
working,
but
it
will
be
working
by
the
in
the
next
two
or
three
days
like
you
can
we
can
just
go
and
and
and
and
lock
it
and
you
can
just
go
and
log
in
and
try
it
and,
as
I
said
so
this
one
this
one,
these
two,
these
three
points
were
actually
addressed
by
what
Carson
said.
So
this
is
like
the
first
place
that
we'll
be
testing
the
whole
thing.
J
J
These
are
the
the
design
constraints
that
we
put
to
ourselves
so
right
now,
the
question
is:
do
we
do
a
skull
on
it,
or
do
we
wait
more?
We
would
like
to
see
some
cross
validation
with
net
mod,
and
you
know
that
that
we
started
getting
all
these
discussions.
But
what
is
the
right
time
to
do?
What
is
right
thing
to
do
as
a
next
step.
A
A
B
A
A
J
So
I
agree
on
this
point
on
the
go
with
you
at
this
point
about
the
sit
so
draft
course
it
will
actually,
you
use
a
yang
file
to
our
yang
module
to
define
the
structure
of
the
file
or
I
mean
the
structure
of
the
CID
file.
So
the
the
way
this
the
way
these
information
is
stored
for
all
the
citizens.
Oh
sorry,.
J
The
way
this
information
is
stored
is
actually
described
as
a
yang
file.
It's
a
young
schema
and,
moreover,
we
are
basically
saying
okay.
Well,
they
are
so.
These
are
some
useful
things
to
know
about
about
a
yang
module.
So
we
have
this
basic
M
module,
and
then
we
have
these
like
correspondence
when
we
say
they
did
well.
There
is
this
link.
There
is
this
URI
and
this
is
the
city
that
is
allocated.
So
it's
some
kind
of
a
meta
information
about
the
it's
superlight
meta
information
about
the
initial
yang
module.
J
J
Use
command
to
allocate
see,
what's
it
ranges,
that's
an
excellent
idea.
I
think
that
I
will
invite
him
on
the
next
Interop
to
come
and
decode
the
the
part
into
the
citric
history
code.
But,
yes,
that
could
be
really
cool.
That
would
be
yeah,
it's
possible
and
so
now
I'm
going
to
pass
the
word,
but
before
passing
the
word
to
the
mic
to
to
Hank
who
on
hankies
okay.
So
during
this
hackathon
there
was
something
really
interesting.
That
happened,
and
that
was
that
people
on
the
next
table
were
really
really
busy.
J
Bringing
this
new
great
feature
to
the
world
of
yeah.
That
is
push
so
yank
push
that
is
used
for
telemetry,
and
that's
that
what's
really
interesting
is
that
this
is
actually
a
cross
working
group
work.
So
you
have
sockem
net
conf
and
core
that
are
working
on
this,
and
you
have
a
very
interesting
way
to
to
see
how
you
you
have
like
a
whole
process.
So,
basically,
for
the
moment
it's
using
XMPP,
you
have
a
process
to
to
see
how
a
collector
or
something
that
is
observing
like
like
an
observer,
can
go
and
can
discover.
J
So
there
is
this
new
technology,
that's
called
yank
push,
and
it
is
based
on
that
content
Resco
for
the
moment
and
right
now,
it's
actually
the
moment
to
go
and
and
go
to
deeper
into
the
car
my
world
into
the
world
of
IOT
into
the
world
of
very
efficient
tallip
telemetry
and
Hank
and
Eric
in
a
couple
of
other
people
have
actually
wrote,
and
they
have
written
draft
on
this.
That
is
the
problem
statement
and
now
Hank
is
going
to
to
say
in
much
better
way
what
it's
all
about.
Thank
you.
K
Yeah
hi
I'm
Hank
next
slide,
so
yeah
young
pushes
build
and
designed
in
Netcom
for
group
leading
parties
are,
for
example,
co-authors
of
this
problem
statement
about
the
there
a
lot
more
people
involved
in
that
it's
called
the
yang
push
design
team,
essentially
written
with
a
Z
I,
think
that's
a
tradition.
So
we
created
a
problem
statement
that
basically
tried
to
actually
effectively
identifying
gaps
in
the
co-op
realm
and
the
Kumaran
in
order
to
create
Akamai
datastore.
K
K
First
of
all,
telemetry
means
in
this
context
that
the
data
store
contains
state
and
that
state
is
a
kind
of
subscription
to
change
its
configuration
operational
data.
So
in
essence,
if
you
think
back
a
few
10s
of
years,
SNMP
traps
we're
doing
the
same
thing
and
they're
now
reached
yang
so
to
speak,
and
our
faciliate
hid
in
extra
quota
calls
that
a
net
conf
and
restaurants,
so
the
streaming
of
continuous
changes,
happens
on
the
device
without
further
interaction.
Coming
from
the
client.
K
We
have
a
lot
of
things
to
do
here.
For
example,
we
sometimes
want
to
have
a
subset
of
things
from
the
module
we
do
not
want
to
subscribe
to.
Everything
like
as
a
thousand
leaves
in
the
module.
So
we
have
a
filter
expression
in
this
subscription,
which
is,
for
example,
differentiating
it
from
the
pub
sub
that
is
already
existing
in
coop
and
in
the
end
it
will
enable
data
motion
that
is
way
more
safe,
descriptive
than
it
is
now
using
standard
modules.
K
I
think
about
800
in
audio
is
already
defined
in
the
IDF
and
therefore
the
principle
of
not
reinventing
the
wheel
is
being
applied
here.
Also
using
coop
and
the
binary
representation,
via,
of
course
in
the
future,
enable
far
better
scalability
I
mean
this
is
an
overused
term,
but
it
effectively
really
will
enable
a
lot
of
more
telemetry
on
the
wire,
especially
if
composite
devices
start
to
have
their
own
data
stores
inside
them.
So
a
device
might
be
a
set
of
multiple
data
stores.
K
So
how
are
we
planning
to
do
this?
Fetch
is
not
only
able
to
do
then
observe
operation
to
basically
establish
a
subscription,
but
also
is
able
to
convey
a
filter
expression
due
to
its
capability
of
containing
a
body.
So
we
are
creating
media
types
that
will
be
enabling
XPath
expression,
for
example,
all
as
we
just
heard
a
specific
get
on
a
subtree
to
get
everything
from
that
set
down.
If
it's
a
leaf,
it's
just
one
value
copy
or
container,
so
you
can
also
do
subtree
subscriptions
with
the
gates,
basically
without
the
filter,
expression.
K
I,
think
all
right
so
I
have
to
think
about.
This
is
what's
coming
up
just
before
my
report
here,
so
we're
going
to
do
right.
At
least
two
drafts
I'm
not
highlighting
here
that
there's
something
called
call
home
I'm
just
mentioning
that
now,
so
the
data
store
sometimes
wants
to
yeah
find
a
suitable
client
that
it's
supposed
to
subscribe
to
it,
and
this
can
be
triggered
by
just
initiating
the
ETS
or
DTS
connection
and
then
say
peer
allowed
to
send
and
then
the
rules
change.
K
The
client
then
starts
the
dynamic
subscription,
for
example,
and
then
we
go
into
the
realm
of
it
on
whirring
bootstrapping
and
such
result.
That
might
be
a
little
bit
complicated
for
today
we're
starting
with
the
fetch
and
get
operations
with
the
observe
to
get
the
subscriptions
on
Akamai
data
store.
The
one
thing
here
is
that
komai
is
not
really
very
visible
in
that
confer
group,
so
we
are
trying
to
remediate
that
situation
by
bringing
all
more
net
conf
people.
K
Looking
into
a
specific
this
new
draft,
it
would
be
the
subscription
to
the
kamae
datastore
and
my
rough
educated
guesses
that
will
be
about
45,
fine
7%
experts
from
coal
mine
and
a
little
bit
more
experts
from
I
come
very
to
make
this
a
feasible
document
and
a
feasible
approach.
So
I
think
this
is
my
little
report.
B
B
K
O
Yeah,
basically,
we
intentionally
with
the
egg
push
did
not
limit
the
XPath
elements
that
can
be
used.
We
leave
not
to
implementation,
and
anybody
at
this
point
can
choose
what
subset
they
want
to
support,
because
it's
very
difficult
to
choose
which
subsets
you
want
that
we
certainly
didn't
want
to
do
it
generically
across
all
kind
of
technologies.
So
we're
a
lot
of
the
the
standard
allows.
Xpath
implementations
will
choose
which
things
are.
E
E
O
K
So
let
me
have
it
before
the
next
question
comes
in
that
we
are
targeting
two
sides
of
the
same
coin.
Here.
First
of
all,
we
are
targeting
less
volume
on
the
wire
and
more
self
descriptiveness
of
today.
Basically,
raw
values
that
are
pushed
around,
so
that's
supporting
unsolicited
push,
those
informations
and
we
actually
know
what's
happening.
What's
pushed
to
you,
this
is
not
a
IOT.
This
is
just
another
and
one
at
enhancement
and
natural
progression
of
how
to
make
better
use
of
your
resources.
Then.
P
K
Other
hand
we
have
constrained
devices
and
they
might
not
really
like
the
complexity
of
XPath
expressions
and
answering
our
pcs
all
the
time.
So
you
can
fall
back,
of
course,
to
the
most
simple
way
to
do
just
a
sub-tree
subscription.
This
is
to
be
CDs
hider.
This
is,
will
be
stuff
we
have
to
discuss
when
we
divide
the
drop
in
progress
or
offer.
Now
Eric
has
a
comment.
Yeah.
O
To
follow
up
on
the
other
answer,
because
this
is
related,
the
yang
push
does
allow
filters,
and
we
have
transport
drafts
for
Netcom
HP
to
comité,
so
it's
possible
to
put
for
transport
what
specific
filters
or
what
elements
you
want
to
support.
So
there's
no
reason
you
cannot
apply
additional
constraints
by
transport.
N
C
Iot
constrained
notes,
I
mean
it
does
a
very
nice
job
of
giving
a
general
framework
for
for
pushing
data
right
limitary
in
in
an
IOT
rolled
with
with
constrain
devices.
You
know.
Originally,
we
had
this
thing
called
observe
that
kind
of
did
that
right,
so
I'm
trying
to
understand
how
we're
going
to
get
this.
If
you
ever
look
at
the
push
framework,
it's
a
well,
it's
a
rather
heavy
framework
when
you
compare
it
to
something.
That's
constrained.
C
Exactly
what
this
means
to
constrain
devices
that
you
know
observed
was
was
all
they
really
needed,
and
and
then
what
what
does
push
really
look
like
in
that
context,
I
I'm
very
concerned
that
you
know,
as
we
start
bringing
the
stuff
over
from
net
mod
and
net
conf,
and
we
get
all
the
things
that
go
around.
You
know
more
expectations
that
you
would
have
on
on
routers.
Then
you
would
I
have
on
on
IOT
device
that
you
know
this.
This
framework
working
really
working
a
it,
might
work.
C
K
This
is,
this
is
touching
the
topic
of
a
call
home
or
finding
a
home
to
call
home
to
if
your
boot
strapping
or
if
your
drop
ship
or,
if
you're
imprinted
or
if
you
enrolled
at
some
point,
you
want
to
send
out
data
as
an
Alex
II
device,
a
lot
of
mechanisms
how
to
bring
the
things
into
the
field,
and
this
here
allows
for
a
very
slim
down
semantics,
well-defined
output,
that
is
interoperable
with
everything
else.
It's
already
out
there,
which
is
a
big
benefit.
K
If
you
have
a
lot
of
other
devices
that
are
already
data
stores,
a
lot
of
post
processing
infrastructure
that
can
handle
all
that
information,
it
is
kind
of
practical
if
the
things
it's
just
appear
in
your
domain
and
then
push
information
to
you
can
be
processed
and
just
like
the
exactly
same
way.
There
is
a
homogeneity
to
the
complete
process
that
in
simplified
interoperability
drastically
also
what
you
are
getting
it
is.
It
is
a
hazard,
huge
overhead,
so
but
an
IOT
device
can
have
some
hard-coded
someone
I
wish.
The
video
would
see
that
one.
O
Other
item
there
is
a
parallel
structure
you
might
guys
might
have
heard
of
DDS
service.
The
same
mechanisms
are
shown
to
work
on
IOT
devices.
There's
our
proof
points
that
if
you
don't
require
deep
filtering,
there
are
implementations
which
do
similar
stuff,
except
it's
not
using
yang.
It's
using
you
know
whatever
the
language
is
there.
A
So
customer
the
underlying
question
here
is:
is
yang
good
for
you
and
I.
Think
that
that's
a
complex
question
and
not
everybody
will
answer
this
question
with
yes,
but
for
those
areas
where,
where
yang
is
actually
useful
technology
to
work
with
the
next
question
is:
can
we
make
that
scalable
and
scalable
not
upwards,
but
as
we
are
always
interested
in
downwards?
So,
okay,
can
we
define
a
version
of
this?
This
yang
push
environment
that
actually
makes
sense
on
a
limited
device
that
is
probably
not
going
to
be
your
light.
A
Switch,
it's
probably
going
to
be
a
little
bit
more
powerful
device.
So
I
don't
think
we
are
targeting
class
one
devices
here,
but
still
can
can
we
make
this
work
in
a
way
that
it's
not
dominating
the
the
actual
application
that
is
running
on
the
node,
but
it's
available
for
making
these
event
streams
available
for
for
telemetry
purposes
and
right
now,
I
wouldn't
say
yes,
sure
we're
trip
still
trying
to
do
that,
but
I'm
pretty
optimistic.
K
Yet
to
add
to
that
comment,
that's
that's
what
the
problem
statement
which
is
published
has
really
highlighted
the
first
section
most
of
the
building
blocks.
Are
there
and
they're
actually
quite
feasible
to
build
something
way
more
static,
then
the
typical
data
store,
if
you're
required
to
do
so.
If
you
do
not
have
the
resources
to
react
in
a
RPC,
interactive
error,
detecting
way
and
now
I
Hank.
E
K
K
Document
understand
the
unfortunately,
the
this
is.
This
is
bad
conduct.
I,
think
the
problem
statement
has
a
lot
of
approaches
as
for
suggestions
to
make
it
better
understandable.
So
it's
not
only
a
problem
statement,
but
it's
also
a
set
of
proposed
solutions,
unfortunately,
which
is
bad
conduct.
We
should
have
done
this
in
two
documents,
but
the
bias
now
are
the
problem
statement
by
providing
for
every
solution
area
a
set
of
proposals
how
to
solve
this,
and
we
already
in
this
it
is
already
outdated.
K
A
A
N
N
K
Ignore
the
slide,
there's
nothing
to
do
with
core
fact
is
that
yes,
core
and
core
can
be
used
here
and
that's
it
ignore
the
slide.
This
slide
shows
how
pushed
information
can
be
post
processed
in
a
security
automation
domain
that
a
second
and
can
be
used
to
create
apology
pictures
by
unchanged
subscriptions
for
neighborhoods
discovery
between
devices
and
or
whatever.
If
your
USB
serial
connector
just
was
connected
and
your
switches
now
many
really
locally
configured,
these
are
change.
K
Events
in
operational
State
that
can
be
pushed
to
a
second
collector
and
then
be
further
distributed
in
security.
Automation
domain
that
is
able
to
detect
anomalies,
does
machine
learning
or
something
else.
So
this
is
basically
a
application
of
young
push,
and
we
want
this
to
be
bolder
than
that
conformist
community.
We
see
a
lot
of
applications
that
are
already
trying
to
create
multiple
data
stores
per
device,
and
the
number
of
telemetry
streams
will
increase
drastically
if
this
process
of
this
trend
continuous.
So
please
ignore
this
light
in
the
context
of
cohab.
N
But
you're
still
looking
for
something
that
kind
of
fits
the
overall
ecosystem
using
yang
using
the
push
mechanism
and
so
on,
but
you're.
Looking
for
this
blue
part,
that
was
at
the
bottom
going
to
the
devices.
It
should
use
kind
of
the
same,
how
we
model
data,
how
you
transmit
it
but
you're,
using
for
a
good
transport
that
uses
coop
the
coop,
observe
and
some
some
optimized
futures
and
not
the
experiment
and
heavyweight
stuff.
We.
K
Are
still
on
not
unsure
how
to
deal
with
a
very
complicated
XPath,
stuff
I
think
they
have
to
be
a
bit
compromises.
This
is
the
interest
most
interesting
thing.
That's
not
been
discussed.
Yet
it's
about
the
media
types
of
emissions
we
have
to
do,
but
in
general
you're
correct
there,
as
the
fact
is,
there's
so
many
yang
modules
out
there
and
and
most
of
them
are
actually
kinda
useful
I
mean,
despite
the
800
done
by
ITF,
that
about
I,
think
2000,
then
in
total
by
the
industry.
K
So
there's
a
lot
of
good
stuff
out
there
and
and
not
making
use
of
that
it's
kinda
redundant
and
probably
not
the
best
idea
so
that
that's
that's
one
of
the
more
drivers
for
using
yang,
again
I
know.
People
are
kind
of
fed
up
with
that
term.
At
some
point,
I
know
and
some
other
stos
use
something
else
entirely,
which
is
not
necessarily
better
other
ways
to
express
models,
and
this
is
just
another
way
to
ensure
long-lasting
interoperability
and
reducing
redundancy
and
defining
models
for
data
that
has
been
transported
for
years
already.
A
P
So
this
was
a
last-minute
decision
to
come
to
this
session,
based
on
interactions
I
had
last
week
at
w3c
TPACK,
with
wave
of
things
working
group
and
and
some
people
there.
So
I
chair
the
payments
working
group
at
WC
and
there's
a
note
there's
a
number
of
API
is
rolling
into
browsers
today
for
payments.
P
The
way
they
work
is
that
the
website
constructs
a
payment
request
which
it
submits
to
the
API
and
in
that
request,
is
a
set
of
accepted
payment
methods,
so
the
API
itself
and
the
data
model
is
quite
generic
and
you
could
put
anything
in
there.
What
has
emerged
as
a
desire
from
part
of
that
working
group,
as
well
as
the
web
things
working
group
to
look
for
ways
to
bind
that
same
data
model
to
alternative
transport,
so
not
a
browser
API,
but
the
the
initial
proposal
was
HTTP.
P
The
the
people
I
spoke
with
in
San
Francisco
interested
in
exploring
if
bindings
would
also
be
with
digging
into
so
the
the
expected
interaction
would
be.
Some
thing
makes
a
request
and
instead
of
getting
a
response
to
that
request,
it
gets
a
request
to
pay
the
payments
made.
Some
other
way,
and
then
the
request
is
retried,
so
it's
it's.
It's
likely.
The
work
will
continue
within
a
w3c
group
for
some
time,
but
making
you
aware
of
it
in
case
you're
interested
in
getting
involved.
P
A
A
P
The
way
their
data
model
works
is
it's
quite
possible
that
the
response
can
be
very
static,
so
your
coffeemaker
could
be
pre-configured
or
have
a
very
static.
So
it
could
work
very
well
in
a
very
constrained
device
as
well.
It
doesn't
need
to
do
any
payment
processing
itself.
It
would
need
to
be
able
to
do
something
like
produce
the
payment
request,
information
which
could
be
very
static
and
then
validate.
E
Bit
this
one
is
I
just
open
the
document
scanned
true,
but
it
doesn't.
It
sounds
like
related
to
the
AIDS
framework,
but
it
does
actually
use
the
x-ray
book.
It
doesn't
use
access
token.
He
doesn't
use
OS
in
at
least
from
a
quick
glance,
so
you
seem
to
be
defining
something
that
is
somewhat
similar.
But
if
your
own
header
format
and
everything
else,
it
may
be
ace.
P
Q
Familiar
with
other
word
limits,
API
works,
but
my
question
is
like
what
said
of
what's
interactions
between
the
device
and
the
arm
and
the
client
depends
on
what
you
see.
They
keep
those
the
client
or,
if
you
think
evils,
the
client
are
basically
generic
web
browsers
and
one
sort
of
idiom
is
appropriate.
Q
If
you
assume
it
is
a
something
we
know
the
standardized
protocol
another
should
it
be,
is
really
sure,
and
so
given
that,
given
that
the
it,
the
interaction
from
I
mean
so
in
the
in
the
web,
browser
puns
this
problem
by
basically
paying
a
JavaScript
API
and
having
stuff
behind
the
covers,
and
so,
if
you're
on,
given
that
the
pay
actual
payment
operation
here
is
a
miracle
occurs
behind
the
scenes.
It's
important
understand
what
you
think.
The
capabilities
that
device
are
of
the
client
may
get.
P
A
request
and
then
and
subsequently
initiating
the
payment-
yes
I,
think
it's
very
determined
by
the
payment
methods
that
are
used.
So
some
payment
methods
could
be
an
exchange
of
tokens
that
are
understood
to
be
valid
for
a
prepaid
arrangement
that
that
could
be
perfectly
valid
or
or
it
can
be
much
more
sophisticated
that
the
client
actually
has
to
go
online
to
a
payment
service
and
execute
upon
human
tissue.
The
the.
Q
Two
no
I
again
I'm,
not
asking
the
question
of
what
the
payment
mechanism
is.
I'm
asking
the
question:
if
we
think
the
device
is
that
is
doing
this
work,
I'm
failing
to
see
why
that's
irrelevant,
because
the
capabilities
that
device-dependent
dictate
what
kind
of
API
or
interaction
mechanism
is
appropriate.
