►
From YouTube: IETF101-DNSSD-20180322-0930
Description
DNSSD meeting session at IETF101
2018/03/22 0930
https://datatracker.ietf.org/meeting/101/proceedings/
A
B
D
We'll
show
you
that
in
a
moment,
first
of
all,
please
take
note
of
the
note.
Well,
it
has
updated
recently.
So
if
you
at
the
back
it's
the
fighter,
pilots
will
be
able
to
read
that.
But
the
note
world
is
also
linked
from
the
the
meeting
pages
as
well.
So
you
should
always
read
it
to
make
sure
nothing's
changed
between
meetings.
D
We
have
a
minute
taker.
Thank
you
very
much.
Barbara
I
would
encourage
others
in
the
room
to
help
Barbara.
You
can
go
to
the
etherpad
there
and
make
any
additions
or
tweaks
the
things
you
said,
maybe
to
clarify
any
points
or
to
get
the
or
name
spelt
correctly.
That's
always
a
tricky
when
the
minute
taker
can't
see
your
name
match,
and
we
also
have
the
professional
job
ascribe
aquel
southland
doing
the
jabber
function.
First.
Thank
you
very
much
Mikael.
D
So
just
the
basic
working
group
info.
This
is
the
same
as
it's
always
been.
If
you
want
to
find
out
more
information
about
the
the
group,
those
are
the
places
to
go
to
and
how
to
join
the
mailing
list
if
you're
not
on
it.
Already
in
terms
of
the
document
statuses,
we
have
two
RFC's
that
have
been
published.
Now
we
have
the
one
on
the
consistency
of
labels
between
conventional
DNS
and
DNS
base
SD,
and
we
have
the
original
requirements.
D
The
working
group
items
that
we
have
that
we're
progressing.
There's
the
DNS
hybrid
Genesis,
T
hybrid
proxy
since
been
renamed
the
discovery
proxy.
That's
been
updated
after
reviewed
by
the
ISD,
so
she
will
tell
us
a
little
bit
more
about
that
shortly.
We
have
a
couple
of
privet.
We
have
in
fact
three
privacy
related
drafts
that
have
been
authored.
Those
are
currently
parked
while
we
review
the
scope
of
the
privacy
work
we
want
to
do
so.
D
The
NSS
d.push
again,
that's
been
updated
very
recently
and
Stuart
will
include
that
in
his
talk
there
is
also
the
DNS
stateful
operations
draft,
which
is
required
by
push
which,
in
turn,
feeds
into
the
discovery
proxy.
That's,
though,
being
progressed
in
DNS
op,
some
of
you
may
have
been
in
DNS
help
earlier
in
the
week
Stuart
presented
on
that,
and
there
were
no
objections
raised
in
the
room,
which
was
good,
but
Stuart
again
will
update
us
on
that
here.
D
So
expect
we're
hopeful
that
that
will
progress
and
push
in
the
discovery
proxy
with
it,
whether
we
advanced
them
at
this
time
or
not,
is
a
question
for
the
group
to
discuss
that
discuss
later.
So
the
goals
for
this
session
is,
first
of
all,
just
to
understand
any
remaining
issues.
With
that
little
triple
of
draft
I
think
we're
in
a
good
position.
D
What
going
to
progress
so,
as
I
said,
we
have
Daniel
and
Christian
have
produced
those
other
three
privacy-related
rafts,
they're,
quite
well
advanced
I,
think
the
group
generally
thinks
it's
good
work.
The
question
is:
is
that
the
right
work
I
think
we
just
wanted
to
step
back
for
a
moment
and
just
look
at
the
bigger
picture.
Briefly
before
we
look
at
the
bigger
picture
before
you
progress?
D
Okay,
that's
what
we'll
be
doing
today
and
in
more
detail
is
the
agenda
again.
So
if
it's,
if
you
reduce
to
quite
a
small
font,
so
we'll
start
with
Stuart,
giving
an
update
on
the
DNS
stateful
operations
and
on
the
update
on
push
and
the
discovery
proxy
we've
then
got
Ted
talking
about
both
the
discovery
relay
and
the
simple
home
net
naming
and
SD
architecture.
You
think.
E
D
D
F
G
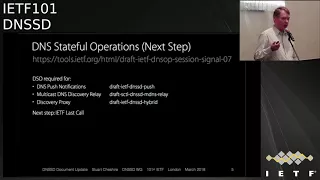
So
we'll
start
by
talking
about
the
DNS
stateful
operations.
Quick
recap
for
those
who
don't
remember
the
history.
We
started
off
with
DNS
push
notifications
to
support
the
discovery.
Proxy
and
Rob
Ellis
wisely
pointed
out
that
we're
really
conflating
session
management
with
the
specific
behavior
of
push
and
that
did
slow
things
down
a
little
bit.
But
that
was
a
good
observation
and
we've
been
working
together
on
what
stars
doff
being
called
session
signaling
late
last
year,
I
think
a
lot
of
people
finally
understood
that.
G
It
was,
it
was
not
just
about
managing
session
timeouts
for
TCP
connections
for
DNS
and
they
caught
a
new
name,
stateful
operations,
so
just
to
cover
the
recent
history
in
draft
Oh
for
last
September.
That
was
when
the
name
changed.
We
also
had
a
lot
of
debate
about
whether
every
request
must
have
a
corresponding
response,
and
we
decided
that
that
was
not
a
requirement,
and
that
was
good
because
that
simplified
the
push
notification
as
documents
and
that's
one
of
the
things
that
was
holding
up
the
push
document.
G
G
If
you
look
at
RFC
death
you'll
see
that
we
changed
quite
a
lot
in
the
draft,
but
nothing
material
about
the
protocol
over-the-air
that
was
submitted
before
this
ITF
meeting
so
DNS,
or
could
review
it
and
confirm
that
all
their
issues
have
been
addressed.
We
had
some
more
feedback
from
Paul
and
that
was
addressed
this
week
because
we
wanted
to
stay
on
top
of
this
and
not
to
learn
any
more.
So
we
we
believe
it's
now
ready
for
IETF
last
call.
We.
G
Presented
the
same
information
at
the
DNS
or
working
group
and
didn't
get
any
objection
to
that
so
I'm
hoping
the
chairs
will
decide
that
this
is
now
ready
to
move
along,
which
is
important
because
you
can
see
there
are
these
three
other
documents
right
now
that
are
depending
on
it.
So
diving
into
these
documents
now
push
notifications
was
critically
depending
on
DSO,
because
that
was
what
it
was
based
on.
G
In
the
new
DSO
draft
that
doesn't
require
replies
that
actually
simplified
a
bunch
of
text
in
the
push
notifications
documents,
there
were
some
very
awkward
texts
about
some
replies
that
really
didn't
carry
any
information,
and
the
text
was
saying
that
the
our
code
had
to
be
zero,
and
if
the
our
code
wasn't
zero,
then
what
you
had
to
do
about
it
and
and
all
of
this
was
describing
stuff.
That
should
never
happen.
So
it
was
much
simpler.
G
Tom
and
I
also
updated
the
Alka
iterative
algorithm
for
discovering
which
server
to
talk
to
so
that
will
need
some
review.
I
see
Andrew
sitting
at
the
back
there.
So
hopefully,
we've
got
some
text
now
that
satisfies
Andrew
and
if
there's
still
more
to
change,
maybe
Andrew
you
I
and
Tom
can
get
together
to
bash
that
and
make
sure
we're
all
happy
with
it.
G
We
actually
got
lots
of
really
good
feedback
from
the
iesg,
and
it
gave
me
a
lot
of
faith
in
the
ITF
process
that
we
have.
We
have
smart
people
in
the
leadership
who
had
some
really
thoughtful
comments
and
there
was
not
a
lot
of
duplication.
Actually,
all
the
different
ihe
members
had
different
areas
that
they
suggested
so
text.
There's
quite
a
lot
of
change
to
the
document
to
address
that
I
added
a
diagram,
because
somebody
wanted
a
picture
showing
what
the
network
layer
looks
like.
G
There
was
a
request
for
an
example
of
how
this
actually
works
in
practice,
rather
than
put
that
in
this
document,
I
added
that
as
an
appendix
to
the
roadmap
document
and
put
a
reference
here
to
the
road
map.
So
if
people
want
a
bit
of
a
real-world
example
to
make
it
tangible,
they
can
look
for
it
there
and,
as
always
happens
in
IFC
review,
we
had
some
more
more
wording
for
the
security
consideration
section.
G
The
road
map
is
not
currently
a
working
group
document.
That
is
something
that
the
working
group
can
decide.
What
I
added
this
week
is
the
walkthrough.
This
is
some
text
I
previously
sent
in
email
when
people
have
asked
me.
So
how
does
this
work
in
practice?
How
does
the
device
know
what
domain
names
to
query?
D
Okay,
thanks
Joe,
so
just
running
through
the
the
three
things
with
three
main
things
there
are,
the
the
DSO
does
any
other
any
comments
on
the
DNS
stateful
operations
options,
the
dns
hoc
item.
There
are
no
comments
raised
there,
I
think
as
a
working
group
I
believe
we're
well,
we
can't
influence
anything,
but
we
can
certainly
support
the
DNS.
What
working
DNS,
what
we've
been
saying
it?
We
believe
it
should
go
up.
No
I
think
that's
what
we're
going
to
do.
D
D
D
Okay
I
mean
there
I.
Think
I,
remember,
I!
Think
the
interesting
question
is
once
those
three
documents
are
all
at
the
point
where
they're
advancing
towards
publication.
Is
there
any
other
reason
why
we'd
hold
them
up?
How
are
we,
for
example,
in
terms
of
implementation?
Experiences,
that's
something
where
we
might
want
to
just
hold
off
a
little
bit
until
we
get
more
of
that,
or
are
we
happy
to
let
the
ITF
process
happen?
D
G
And
I
are
actually
working
full-time
now
on
getting
that
implementation
experience.
So
I
think
it
is
important
that
we
do
that,
so
that
we
don't
find
some
silly
mistake
and
then
end
up
with
errata
listed
on
the
document.
I'm
not
expecting
that
to
take
very
long,
certainly
in
the
next
couple
of
months
before
the
next
ITF
meeting.
D
I
think
the
the
way
the
ITF
process
works.
I
can't
see
any
of
them
actually
going
to
publication
before
the
next
meeting.
So
by
the
time
we
do
the
last
calls
and
the
ICT
reviews,
etcetera,
so
I
think
that's
going
to
sit
quite
nicely
now.
The
other
question
I've
got.
Is
there
anyone
else
in
the
room,
that's
implementing
other
than
Stewart
and
Ted
okay
good
on
John?
Oh,
yes,
on
Tom
anyone
else,
anyone
know
of
anyone
else
to
implementing.
G
D
Okay,
good
and
then
I
think
the
final
thing
coming
from
thanks
very
much
the
final
thing
coming
out:
there
was
Stuart's,
updated.
The
roadmap
document,
I
think
it's
so.
Firstly,
I
think
it's
a
really
useful
document
for
the
working
group.
It's
showing
essentially
all
the
components
of
the
things
that
were
working
on
how
they
relate
to
each
other
and
the
sort
of
direction
forward
for
the
working
group
and
I
think
adding
an
appendix
shown
how
things
actually
work
with
a
practical
example.
D
Maybe
a
overtime
one
or
two
more
appendices
may
be
added
with
other
examples
like
that.
That
would
be
good,
so
I
think
it'd
be
a
good
thing
for
the
working
group
to
adopt
whether
we
actually
ever
aim
to
publish
it
in
the
end
or
not.
Is
another
question
but
I
think
we
should
have
a
decision
now
as
to
whether
we
adopt
it
as
a
working
group
item.
D
So
could
we
take
a
farm?
All
those
in
favor
of
adopting
the
roadmap
document
is
a
the
necessity.
We
actually
ask
a
question
Fergal
how
many
people
have
read
the
roadmap
document?
Okay,
that's
good!
So
yet
then
minutes
there
show
that
about
8
to
10
hands
went
up,
I,
think
so
all
those
in
favor
of
adopting
the
I've
so
you've
got
a
question.
First
from
Tom.
H
D
G
D
Okay,
so
all
those
in
favor
of
adopting
this
the
roadmap
is
a
welcome
goodbye,
jun-hyung,
very
musical.
Anyone
object
hum
so
noted
that
there
was
a
healthy,
humming,
favor
and
I
couldn't
hear
a
single
hum
against
so
obviously
take
that
to
the
list
as
usual.
Good
subject
to
that,
we
can
be
published
as
a
as
a
working
group
item.
I
So
don't
do
that
I
thought
I
hit
cool
you!
Well,
oh
I,
see
yeah,
sorry,
alright,
okay,
so
here
to
talk
about
discovery
relay
what
is
it
so
it's
a
simple
lightweight
relay
that
can
be
added
to
any
router.
It's
basically
it's!
The
idea
is
that
it's
like
a
DHCP
relay,
very
small
lightweight,
doesn't
need
to
be
changed
when
features
are
added
to
the
protocol.
It
acts
as
a
virtual
interface
for
discovery
proxies
off
link.
So
if
you
have
a
discovery
proxy
on
a
fairly,
you
know,
smart
machine,
that's
got
plenty
of
CPU.
I
I
So
this
idea
I'm
kind
of
going
starting
from
the
beginning,
because
I'm
not
sure
how
many
people
have
actually
have
actually
got
this
on
their
radar.
But
this
idea
came
out
when
I
was
working
on
the
home
like
the
home,
that
naming
architecture,
because
we
needed
a
way
to
separate
out
the
sort
of
simple
home
net
use
case
from
the
more
general
home
net
use
case
and
so,
but
but
actually
the
home.
That
use
case
isn't
really
the
main
use
case
for
this.
I
But
you
don't
need
to
tell
it
like
you
know
what
the
domain
names
of
the
link
are
or
any
you
know
anything
that
might
be
changing
a
lot
so
once
you've
got
it
set
up,
it
should
be
pretty
easy
to
to
just
leave
it
there
and
have
it
work,
it's
pretty
lightweight
it
does.
It
does
require
TLS,
but
at
that,
at
this
point,
I
think
requiring
TLS
has
pretty
much
table
stakes
and
so
I'm,
not
counting
that
as
making
it
heavyweight.
There
are
some
pretty
lightweight
TLS
implementations
that
could
be
used.
I
So
it
essentially
allows
you
to
really
centralized
your
network.
You
can
have
leaf
networks
that
don't
have
a
lot
of
intelligence
on
them
and
then
centralize
everything
and
it
provides
a
way
also
to
monitor
mdns
traffic
on
a
link.
If
you,
for
you
know,
for
network
management
purposes,
you
might
want
to
see
what
devices
are
out
there.
Advertising
services
and
you
can
just
connect
to
the
relay
using
proper
authentication
and
get
that
information
status.
So
the
document
actually
is
pretty
complete.
I
I
think
that
if
you
wanted
to
implement
a
discovery
relay
right
now,
you
could
just
use
the
document
as
written
in
a
work.
I
had
actually
originally
a
pretty
elaborate
management
section,
which
was
more
than
half
of
the
document,
and
I
decided
that
that
was
a
little
too
elaborate.
So
I
took
it
out.
I
think
there
were
some
interesting
stuff
in
there,
but
it
wasn't
really
about
the
discovery
relay.
I
The
document
relies
on
DNS
stateful
operations
that
Stuart
said,
and
the
Stuart
mentioned.
I
actually
did
an
implementation
of
the
relay
for
the
Singapore
hackathon
when
I
was
still
working
for
nominal,
that's
nominal
codes,
that's
that's
been
abandoned,
but
but
we're
working
on
a
new
implementation
now
and.
I
It's
not
done
yet,
but
it'll
be
done
relatively
soon.
I
think
and
Stuart's
got
a
discovery
proxy
that
can
talk
to
it,
which
is
of
course
the
other
half.
So
it
would
be
nice
to
get
some
some.
Some
working
group
working
group
review
on
this
I,
don't
think
I've
gotten
a
ton
of
feedback
on
it
ya
know
so
so
be
great.
I
Mr.,
it
said
we're
planning
on
being
in
Montreal
at
the
hackathon,
with
working
code
to
test.
So
if
you've
got
code,
we'll
be
able
to
test
with
you
and
I'm
also
planning
on
stuffing
some
of
this
stuff
into
open
wrt,
so
that
people
can
just
download
it
and
try
it
out
and
it'd,
be
nice
to
get
more
router
vendors
who
are
interested
in
this.
So
that's
pretty
much
it
any
questions.
D
So
hands
up
who
has
read
the
draft,
not
necessarily
that
the
latest
one?
Okay?
So
that's
a
small
number,
so,
yes,
we
certainly
could
do
with
more
people,
reading
it
and
giving
feedback
other
a
couple
of
people
that
were
is
none
of
them.
It's
not
a
huge
document
or
a
couple
of
people
that
might
volunteer
to
have
a
read
and
send
some
feedback
to
the
list.
Anyone
prepared
to
do
that.
D
G
It's
not
a
big
request
and
I
think.
The
other
reason
we
haven't
got
a
lot
of
feedback
on.
It
is
because
it's
pretty
straight
forward
and
I
want
to
give
Ted
credit
for
this
idea.
He
listed
me
as
co-author,
but
I
think
we
Ted's
background
in
DHCP.
He
was
very
natural
and
obvious
thing
to
Ted
that
you
have
this
very
simple
code
like
a
blooper
reel,
which
is
very
stable.
G
G
So
it's
funny
sometimes
how
these
things
come
full
circle
and
when
you
read
the
draft
it
just
what?
When
I
read
what
Ted
proposed
I
was
just
sort
of
nodding
going.
Oh
yeah,
that
makes
sense.
There's
nothing
really
controversial
there.
So
that
may
be
why
we've
not
got
a
lot
of
feedback,
because
it
just
seems
obviously
the
right
thing
to
do.
Yeah.
D
B
J
E
I
Head
of
the
tree,
I
mean
I,
don't
see
any
reason
why
I
couldn't
be
back
ported
to
a
to
an
actual
release,
but
rest
is
just
in
getting
or
getting
an
open
wrt
that
builds,
but
yeah
I
mean
this.
There's
there's
nothing
in
this.
That
is
in
any
way,
I
mean
most
of
the.
When
you
see
open
wrt,
advancing
most
of
the
advances
are
actually
Hardware,
stuff
and
sort
of
integration
stuff,
and
so
integrating
this
into
a
into
like
chaos
coma
or
something
like
that
would
be
quite
easy
right,
but
because
it.
E
Is
a
lot
easier
if
you
take
something
that
is
stable
from
an
operating
point
of
view
and
then
just
create
a
new
feed
and
see
it.
So
people
can
install
it
yes
from
there,
because
otherwise
getting
people
to
try
and
whatever's
trunk
of
all
the
time
that
then
the
hair
might
have
other
breakage,
and
so.
E
D
Yeah,
okay,
thank
you.
So
we
should
take
a
view
as
a
working
because
of
whether
we
want
to
adopt
this
item.
I
mean
from
everything
we've
heard.
It
seems
a
very
natural
idea
and
it
fits
with
the
model
that
we
have
so
all
those
there
any
further
questions
before
we
take
that
decision,
as
anyone
need
to
know
any
further
information
to
help
them
with
it,
No,
okay.
So
all
those
in
favor
of
adopting
the
discovery
really
as
a
working
group
item
please
come
now
and
any
opposition
or
anyone
think
it's
not
a
good
idea.
D
D
F
K
D
D
I
The
next
topic
is
simple:
home
net
naming
and
I
just
wanted
to
present.
I.
Think
I
presented
this
to
the
group,
maybe
once
before,
but
just
trying
to
raise
some
awareness
about.
What's
going
on
there
so
home,
that
is
using
DNS,
SD
Discovery
proxy
is
the
basis
for
the
simple
naming
architecture,
and
you
know,
there's
some
there's
some
push
in
the
in
the
home.
Networking
group
largely
for
me
to
to
use
the
registration
protocol
as
well,
but
that's
not
in
simple
naming
so
so
I'm
I'm.
I
I
So
why
does
anybody
in
this
room
care
well,
I?
Think
the
so
the
advanced
home
that
naming
architecture
really
kind
of
hits
a
lot
of
use
cases
that
we
care
about
I,
think
or
at
least,
is
relevant
to
them.
It's
possible
that
what
we
have
in
the
simple
naming
architecture
would
not
be
just
a
drop
in
thing
that
you
could
use
in
a
corporate
environment.
I
A
small
small
organization
might
not
be
a
drop
in
thing
that
you
could
use
in
a
number
of
the
use
cases
that
we've
talked
about
like
the
the
EDUCAUSE
use
case,
but
we
don't
actually
really
have
a
management
story
for
dns
SDU
right
now
and
so
I
think
that
even
if
the
home,
that
naming
architecture
itself
is
not
what
we
wind
up
using
to
address
that
usability
issue
in
other
environments,
it's
probably
going
to
be
very
relevant
to
that
work.
So
I
think
it's
worth
looking
at
for
folks
in
this
group.
I
So
what's
going
on
with
that
I
actually
I
looked
over
the
I
hadn't
worked
on
the
simple
home
that
naming
architecture
document
in
about
six
or
seven
months
and
I.
Guess
I
did
a
small
haircut
for
it
on
for
Singapore,
but
but
I
looked
at
it
about.
You
know
a
week
or
two
before
the
deadline
and
realized
that
the
organization
was
just
terrible,
so
I
don't
know
it
was
kind
of
ad
hoc.
When
I
wrote
it
down
I
just
it
was
a
stream
of
consciousness.
I
So
having
that
that
break
really
helped
and
I
reorganized
the
document,
it
still
needs
a
lot
of
work.
Basically,
I've
got
a
nice
skeleton
for
it
now,
but
but
it
needs
more
detail,
and
so
it's
not
ready
to
publish
yet
but
I'm
really
hoping
to
have
something
that
looks
like
a
final
version
of
the
document
by
the
next
ITF
des
spent.
It
currently
des
spent
depends
on
the
discovery
relay
advanced
home.
That
naming
will
depend
on
the
on
the
registration
protocol.
I
I
haven't
actually
done
a
ton
of
work
on
Vanstone
net
naming,
but
there
was
a
home
net
name
mark
naming
architecture
document
that
preceded
the
simple
home
that
naming
architecture
document
that
has
a
fair
amount
of
that
stuff
in
it.
In
fact,
you
know
the
the
some
of
the
ideas
that
that
turned
into
the
registration
protocol
were
mentioned
in
there.
I
I
I
Could
be
nice
to
get
that
adopted
as
well,
because
I
think
that
that's
the
nice
thing
about
the
registration
protocol
is
that
it
basically
lets
us
have
a
migration
path
to
a
network
or
not
using
multicast
for
everything
every
service
discovery.
You
know
we
still
have
multicast
as
a
fallback,
so
we
still
have
compatibility
with
old
devices,
but
this
allows
us
to
do
things
like
you
know.
D
G
Stuart
Rashtra
from
Apple
for
the
notes
I
wanted
to
expand
a
little
bit
on
something
Ted
mentioned.
I
talked
about
Internet
of
Things,
home
automation,
and
devices
like
that
are
increasingly
becoming
very
popular.
Apple
has
the
homekit
line.
Nest
has
the
thermostats.
Now
there
are
a
bunch
of
these
things.
Ocf
is
working
on
standards
there.
The
ZigBee
organization
is
doing
it.
G
The
thread
group,
which
is
an
organization
out
I,
started
by
nest
and
Google,
is
working
on
low
power,
low
speed,
short-range
wireless
networks,
where
you
need
a
mesh
to
cover
the
whole
house,
and
when
you
have
a
mesh,
it
gets
really
hard
to
do
multicast
and
when
you've
got
battery-powered
devices
that
want
to
save
power
running
the
battery
down
and
forwarding
multicast
for
other
devices
is
also
not
good.
So
for
me
personally,
this
is
an
area
that
I
think
is
important
and
something
that
I'm
going
to
be
working
on.
G
D
And
I
think
there
is
another
draft
elsewhere
with
Charlie
Perkins
and
some
other
people
involved
in
terms
of
describing
the
issues
with
multicast
I've
forgotten
the
specific
name
of
it.
But
I
think
that's
that's
the
rationale
for
push
here
towards
remaining
compatible
with
the
existing
multicast
things
that
are
out
there,
but
in
new
work,
trying
to
lean
towards
more
use
of
multi-card
yeah.
G
D
G
I
Another
another
thing
to
say
about
the
the
registration
protocol
by
the
way
is
that
it
also
adds
some
not
huge
amount,
but
some
security,
which
is
not
present
an
MD,
an
acid
mdns.
Basically,
anybody
can
blab
on
the
network.
My
name
is
Phu
and
what
happens
if
somebody
else
had
already
claimed
Phu
is
that
whoever
was
that
already
claimed.
I
Foo
is
like
oh
I'm,
so
sorry
and
gives
up
Phu,
and
so
it's
very
easy
to
attack
services
on
the
network
by
just
you
know,
claiming
a
name
and
one
of
the
neat
things
about
the
registration
protocols
that
actually
uses
public
key
cryptography
to
to
assert
ownership
over
over
a
name
that
hasn't
yet
been
claimed,
and
that
makes
it
impossible
for
somebody
who
doesn't
have
the
private
key
to
then
claim
that
they
own
that
name.
So
you.
I
E
Michael
Abramson
again,
yeah
I
was
an
MD.
The
other
day
were
Perkins
were
he
was
presenting
that
and
I
brought
up
this
issue
in
2015
or
something
of
it
that
this
is
something
that
should
be
worked
on
and
I
still
think.
I
still
think
that
today,
the
I,
chiefly,
for
instance,
and
the
ITF
has
not
decided
like
okay.
This
is
how
we're
going
to
solve
it.
D
G
You
making
a
good
point:
we'll
have
some
cases
where
the
old
to
the
new
coexist.
We
may
have
other
scenarios
like
the
thread
mesh
network,
where
the
old
multicast
stuff
is
just
never
present
from
the
start
and
I
think
that's
another
reason.
We
want
to
push
ahead
with
developing
this,
because
there
are
other
things
going
on
the
Indus
in
the
industry
that
could
really
use
this,
and
if
we
don't
have
a
solution,
ready,
they're
gonna
have
to
invent
something
different
and
then
use.
L
D
I
mean
maybe
this
is
maybe
there's
a
opportunity
for
an
ad
to
make
a
comment
here
we
haven't
I
was
just
saying
today:
we'd
be
having
a
recharge
it
for
a
long
time.
If
at
all,
they
we've
tweaked
our
milestones
a
bit.
So
it
may
be
appropriate
to
look
at
our
Charter,
which
does
mention
things
like
mesh
networking
and
maybe
review
the
Charter
and
include
that
more
explicitly
in
our
future
work
plan.
Does
that
make
sense.
M
A
E
Abramson
ain't,
yeah
and
I
think
when
I
brought
up
the
the
multicast
issues
on
radios,
there
were
a
lot
of
people
from
there
was
three
or
four
different
working
groups
to
deal
with
radios,
6lowpan
and
money,
and
something
else.
So
we
need
to
make
sure
that
we're
not
stepping
on
someone
else
in
that
were
using
whatever
experience
and
protocols
they
might
already
have
just
did
in
this
case
we're
not
reinventing
the
wheel
because
they
had
a
lot
of
I
mean
they
came
out.
I
said
it
of
course.
E
D
G
A
D
Yes,
that
will
be
something
to
discuss
when
we
do
a
chart,
so
I
think
I.
Think
again,
just
speaking
David
I,
don't
think
we
want
to
hold
up
this
work
that
it's
holistic
there,
the
service
registration
in
particular
and
the
the
essentially
unicast
work.
So
we
don't
do
anything
to
preclude
that
progressing
quickly,
but
it
does
sound
like
refreshing.
Our
Charter
would
be
a
good
idea,
so
that's
probably
something
we
can
take
the
lists
discuss.
What
sort
of
things
should
be
added?
D
What
maybe
can
come
out
now
that
we've
either
done
the
work
or
it's
we
don't
believe
it's
any
relevant
anymore
and
I
think
maybe
even
looking
back
to
the
original,
for
example,
the
original
EDUCAUSE
request
that
led
to
us
doing,
you're
partly
led
to
us
doing
this
work
and
see
whether
we
think
we've
met
what
they
were
asking
for.
The
interesting
thing
when
we
were
looking
at
the
Charter,
so
I
think
we'll
take
the
the
Charter
to
the
list
in
terms
of
adopting
the
service
registration
thing.
D
I
D
I
G
About
to
say
the
same
thing,
I
think
when
not
enough
people
have
read
it
is
too
early.
Isn't
it
not
useful
to
ask
for
adoption
I
think
as
part
of
the
discussion
about
changes
to
the
Charter?
That's
a
good
opportunity
for
us
to
figure
out
what
are
the
things
we
want
to
work
on.
What
current
drafts
cover
those
areas
and
then
we
can
actually
give
people
a
reading
list
of
things
to
look
at
and
then
we
could.
Then
we
can
have
a
meaningful
discussion
about
it.
Yeah.
D
I
Sounds
good
so
on
the
topic
of
educause.
I
didn't
really
want
to
get
too
deeply
into
that
in
the
SSD
presentation,
because
it's
sort
of
tangential
but
yeah
the
engine
I,
actually
I
I,
had
heard
the
term
the
EDUCAUSE
petition
passed
around
a
lot
and
I
thought.
Oh
wow,
that
must
have
been
like
you
know,
ed
Rousseau.
It
must
be
like
really
detailed
and
I
know
it.
I
I
We
could
do,
and
you
know
as
I
said,
but
but
you
know
the
the
the
discovery
proxy
pretty
much
solves
the
the
transport
aspect
of
the
the
EDUCAUSE
request.
What
it
doesn't
solve
is
how
do
we
deploy
this,
and
so,
and
you
know
how
do
we
deploy?
This
is
well
you
just
put
it
on
all
of
your
things
and
it
just
sort
of
works
right
except
know.
I
If
you,
if
you
look
at
if
you
look
at
you
know
how
you
would
have
to
I
mean
this
is
something
that
we
had
to
think
about
in
the
home
map,
because
we
have
to
automate
the
deployment
right.
There's
no,
there's
no
way
to
to
to
have
the
end-user
set
it
up,
whereas
in
an
educational
environment,
maybe
we
could
have
the
IT
people
do
it.
I
D
Think
it's
something
we
have
discussed
in
the
past.
I
know:
Tom
had,
for
example,
sort
of
a
draft
that
never
got
published
about
the
actually
deploying
what
we're
doing
in
an
enterprise
and
I
Ralph
spoke
to
that
topic
two
or
three
meetings
ago,
so
I
think
putting
that
stuff
together.
I
think
what
you're
doing
with
the
HomeNet
stuff
is
kind
of
addressing
that
question
in
the
home
that
area,
but
for
a
campus
or
enterprise
having
some
equivalent
view,
point
that
were
documenting
yangmi.
E
D
So
the
simple
home
so
yeah,
the
agreement
was
to
work
up
a
an
updated
Charter,
and
out
of
that,
we
will
better
understand
the
work
that
needs
to
be
done
in
that
area
and
I
think
the
same
will
apply
to
the
privacy
which
they
would
make
as
well.
The
privacy
isn't
really
mentioned
much
in
the
charge
from
the
moment
and
out
of
that,
then
we'll
understand
which
documents
we
need
to
adopt
on
which
gaps
we
have
for
work.
We
need
to
do
okay,
so
I
think
that
covers
that
off.
A
A
F
D
D
I
N
Problem
space
that
we're
discussing
is
machined
a
machine
or
thing
to
thing
discovery.
This
is
apropos
of
the
earlier
conversation
about
reach
our
Turing
and
DNS
SD,
there's
nothing
specifically
in
our
Charter.
That
says
we
need
to
cover
this
domain,
but
there
is
a
charter
item
in
the
core
Charter
that
says
that
their
resource
directory
must
interoperate
with
DNS
SD.
So
that's
why
we're
here
hopefully
to
to
get
some
help
from
folks
who
are
in
DNS
SD
and
may
have
use
cases
to
contribute.
The
history
of
this
draft
was
that
it
was.
N
It
started
life
as
an
individual
draft.
I
did
this
was
ax
Shelby
several
years
ago
it
was
incorporated
into
the
resource
directory
draft,
but
then
it
was
split
out
to
basically
eliminate
dependencies
that
the
art
you
might
have
on
other
work
that
was
still
immature
resource
directory
draft
as
being
teed
up
now
for
working
group
last
call
I.
Think
one
thing
we
want
to
do
is
to
gain
some
more
implementation
and
operational
experience
before
we
go
to
work.
A
group
last
call,
but
this
work.
D
N
The
topic
both
in
core
and
here
so
now
you
can
go
to
the
next
slide,
so
the
use
cases
that
we
envision,
basically
there's
a
there's,
an
obvious
use
case
at
the
edge
of
heterogeneous
networks
where
we
might
have
cross
proxies
that
translate.
Http
client
requests
into
co-op
server
requests
and
vice
versa.
N
So
for
those
who
don't
have
background
with
with
core
it's
the
kind
of
the
main
application
protocol
developed
by
ITF
for
IOT,
the
main
deliverable
of
core
was
co-op,
which
is
the
constrained
application
protocol.
It's
basically
in
its
initial
state
was
rest
on
top
of
UDP.
The
implication
there
is
that
request
can
be
multicast,
so
it
supports
something
a
little
bit
like
mdns.
N
However,
multicast
is
even
more
problematic
and
mesh
networks
than
it
is
in
Wi-Fi,
as
we've
discussed,
but
for
the
purposes
of
examples
that
all
that
will
bring
up
here,
we
could
just
imagine
that
we
could
multicast
for
four
resources
on
the
on
the
constraint
networks.
Other
bindings
are
being
worked
on
right
now,
specifically
co-op
as
being
bound
to
TLS
and/or
WebSockets
for
transport
over
the
Internet.
N
N
The
methods
that
are
available
to
operate
on
resources
are
rather
limited
to
the
crud,
create,
read,
update
and
delete
patterns,
but
also
Co
app
supports
and
an
observed
pattern.
I
think
there's
a
rough
equivalence
between
resources
and
objects.
They
both
have
behavior
state
and
identity,
albeit
resources
have
a
more
constrained
set
of
methods
that
can
work
on
them,
as
I
said
finally,
rest
supports
or
a
very
mature
rest
design
for
an
API
should
support
something
called
hypertext
is
the
engine
of
application
state.
N
So
originally
core
was
not
chartered
to
do
their
own
discovery
protocol,
but
ultimately
it
became
very
compelling
to
use
Co
app
to
do
discovery,
as
well
as
everything
else
that
it
does
so
Zack
shall
be
developed.
This
thing
called
quarreling
format
based
on
web,
linking
essentially
it's
a
it's
a
way
of
describing
links
between
a
between
a
target,
sorry
between
a
source
link
and
other
target
links.
N
So,
for
example,
if
you're
processing
a
list
you
might
have
a
link
that
tells
you
how
to
get
to
other
members
or
the
front
or
the
back
of
that
list.
If
it's
a
device,
you
might
have
a
link
that
tells
you
how
to
turn
it
on
and
off.
You
can
access
the
behavior
or
the
links
of
any
device.
By
doing
a
get
to
slash
well-known
that
slash
core,
you
can
optionally
include
a
query.
String
and
you'll
receive
back
a
collection
of
type
links
that
basically
tell
you
how
to
control
that
device.
N
So
the
web,
linking
draft
is
defined
a
set
of
target
attributes
for
these
links,
such
as
a
resource
type,
the
interface
description
and
the
size
that
you
get
back.
If
you
were
to
do
requests
on
that
now,
resource
directory
is
essentially
a
way
of
capturing
all
of
the
state
for
a
given
constraint
network
into
a
directory
so
that
you
don't
have
to
do
multi
casting
you
can
still
unicast
individual
devices,
but
it's
a
bit
like
you
know,
capturing
all
this
into
a
DNS
directory
next
slide.
N
N
Rt
is
not
a
new
on
a
new
thing;
I,
don't
know
what's
listed
here,
but
anyway,
one
thing
we're
we're
thinking
about
is
perhaps
a
federated
namespace,
so
that
all
of
the
resources,
all
the
resource
types
that
can
be
exported,
don't
necessarily
need
to
be
listed
in
detail.
But
potentially
you
could
list
in
the
registry
just
the
name
of
the
SDO
that
standardizes
the
types
of
resources
below
it
and
I'll
get
into
that
in
a
minute.
N
So
here's
a
very
rough
summary
of
what
we're
talking
about
doing
and,
as
I
said,
you
know
a
given
resource
that
wants
to
be
exported
to
DNS
SD
would
start
by
having
the
exp
attribute,
and
so
then
these
other,
these
other
things
would
be
required.
Oh
I
see
that's
why
they
previously.
The
previous
slide
said
new
and
or
required
link
attributes,
so
the
instance
attribute
would
be
required.
If
you
wish
to
export
this,
it
becomes
the
instance
part
of
the
service
instance
name.
The
resource
type
becomes
the
service
type.
N
The
URI
of
given
API
entry
point
becomes
a
part
of
the
text
record.
Similarly,
with
the
interface
description,
any
other,
any
other
attributes
would
also
go
into
the
text
record.
So
the
idea
here-
that's
maybe
a
little
bit
different
from
previous
DNS
SD
patterns-
is
that
what
we
would
like
to
do,
I
believe,
is
to
export
multiple
text
records
per
SRV.
So
we're
basically
talking
about
multiple
api's
that
live
at
port
443,
let's
say-
and
there
actually
is
support
for
that
in
the
DNS
SD
draft,
but
I
don't
think
it's
he
very
often
next
slide.
N
So
here's
a
an
example:
I
don't
have
a
pointer
I
can
wave
around
so
I've
color-coded
these
a
little
bit.
You
might
start
off
with
a
with
a
query.
There
might
be
a
mapping
agent
that
does
this
mapping
from
resource
directory
entries
into
VN
SSD
entries,
and
so
it
starts
by
basically
doing
a
discovery
of
all
the
resources
that
have
the
exp
attribute.
It
gets
back,
for
example,
something
from
this
node
at
you
know:
FD
FD,
1,
2,
3
4.
It
says
I've
got
a
sensor.
Here's
the
URI
to
it
and
read
the
content.
N
N
S
refers
to
a
schema
that
you
can
use
to
basically
look
up
and
see
how
this
thing
is
operated
and
the
resulting
resource
records
are
below
TVD
is
how
to
generate
a
quad,
a
record
if
it
doesn't
exist
and
what
domain
we
should
map
this
thing
into,
but
essentially
we
would
create
a
pointer
record
listing
a
new
OIC
type
that
have
the
instance
name
of
indoor
temp,
which
came
from
the
original
record
and
and
then
we'd
have
a
sub
type.
That
lists
this
thing
as
a
as
a
temperature
sensor.
N
O
E
N
It
this
is
not
a
well-formed
idea,
but
but
the
idea
I
think,
is
to
try
to
come
up
with
some
sort
of
technique
where
we
could
have
a
federated,
namespace
and
I.
Don't
know
if
there's
you
know
broad
support
for
this
again.
We're
sort
of
resocialized
I
think.
If,
if
we
were
to
go
with
some
sort
of
federated
name
scheme,
it
would
relieve
us
from
having
to
specify
every
single
resource
type
that
could
be
exported
in
an
eye
on
a
directory
somewhere.
N
Maybe
again,
that's
not
very
onerous
I,
don't
know
how
people
feel
about
that,
but
I'm.
Assuming
that
there
is
structure
in
the
resource
type
string
and
the
OIC
is
the
first.
You
know
label
and
then
everything
under
that
is
essentially
the
domain
of
of
that
SDL.
Again
I
just
sort
of
picked
OIC
out
of
the
air
I,
don't
I'm
not
trying
to
imply
that.
O
Okay,
so
I,
don't
know
why
you
don't
know
why
you
need
that
so
I
don't
think
we
should
assume
that
there's
any
structure
and
the
RT
value,
but
it
occurs
to
me
that
I
don't
know
why
you'd
need
that
if,
for
example,
if
you
just
put
in
some
label
that
means
that
it
was
derived
from
a
cork
worried,
why
do
you
care
what
Jessie?
Oh
it
was?
Alright,
oh
you're,
RT
values
are
unique.
Isn't
that
simpler?
What's
the
what's
the
use
case,
you
don't
want
that
all
right
and
why
can't
they
just
be
a
constant.
P
I
I
If
I
were
just
naively
thinking
about
how
to
how
to
get
Corrin,
DNS
SD
together
the
way
that
I
would
think
about
doing
it
would
be
to
say:
oh
core
is
a
service,
and
so
Deanna
says
you
just
offer
a
core
as
a
service
in
DNS
SD,
and
then
all
of
this
complexity
goes
away
because
you
just
you're
just
saying
you
can
do
core
with
this
device
and
then
what
you
do
with
the
device
using
core
is
up
to
the
core
implementation.
I.
N
Had
thought,
oh,
that
makes
sense,
or
is
that
I
think
the
key
takeaway
here
is
that
we
would
like
more
interaction
between
the
DNS
SD
working
group
and
the
core
working
group.
So
those
of
you
who
sort
of
have
a
foot
in
each
camp
it'd
be
great.
If
we
could
come
forward
with
more
use
cases
and
and
more
specifically,
operational
and
implementation
experience,
I
should
say
that
there
is
an
RD
Interop
plan
for
mid-april,
and
so
that's
maybe
the
first
opportunity
to
try
out
some
of
these
ideas.
N
G
Q
Just
YUM
I'm
says
I
think
I
can
answer
answer
that
custom,
because
I
will
be
holding
that
interrupts.
Yes,
it
will
be
work
virtual
and
there
right
now
it
sir.
It
is
not
planned
in
a
very
precise
way.
So
we
are
still
waiting
for
potential
participants
to
to
input
us
with
basically
what
they
would
be,
what
they
have
implemented,
what
they
would
be
willing
to
try
starting.
N
D
N
N
Is
that
when
this
work
was
originally
conceived,
it
was
in
the
context
of
a
protocol
that
was
being
developed.
That
was
heterogeneous
where
we
potentially
had
HTTP
clients
operating
through
cross
proxy
because
of
the
rough
equivalence
between
rest
and
HTTP
and
resting
core
or
in
Co
app.
This
cross
proxy
is
potentially
easier
to
implement
than
a
application
layer
gateway,
so
just
to
advertise
something
as
being
core
capable
or
co-op
capable
might
not
actually
help
out
an
HTTP
client,
so
they
might
actually
want
to
get
to.
You
know
to
the
links
and
manipulate
them
through
HTTP.
R
G
Dave
made
a
good
comment
about
how
you
do
this
translation,
whether
it's
a
mechanical
translation
or
whether
there's
a
big
table
somewhere
that
lists
the
translations.
I
think
that
is
one
that
that's,
maybe
the
key
challenge
and
the
introduction
to
the
roadmap
document
talks
about
that,
because
I've
realized
that,
regardless
of
multicast,
DNS
or
DNS
service
discovery.
G
What
protocol
you
use,
if
you
don't
have
a
common
vocabulary
for
describing
services,
then
you
end
up
with
this
big
translation
table
that
this
mechanism
is
using
one
namespace
for
listing
services
and
then
another
mechanism
is
using
a
completely
different
namespace
to
describe
the
same
things.
I,
don't
know
how
we
solve
that
easily,
but
I
think
that's
the
issue.
I,
like
Dave
suggestion
that
maybe
you
lump
all
core
protocol
or
co-op
I
should
say
I
think
is
not
the
right
time.
G
All
co-op
implementations
are
under
underscore
co-opted
underscore
UDP,
but
then
you
can
use
subtypes
that
are
mechanically
derived
from
the
RT
to
let
you
do
more
selective
discovery,
so
you
not
discovering
every
co
op
device
there
is,
but
just
the
ones
you're
interested
in
I
had
one
little
NIT
on
this
slide.
At
the
bottom,
you
have
three
separate
text.
E
G
Q
S
I'm
not
wearing
my
badge,
but
you
know
me:
I'm
Barbara
stark,
hi
Carrie.
You
know
me
too
so
and
you
know
the
work
that's
been
going
on
in
broadband
forum
on
USP
and
we've
got
a
protocol,
that's
running
over
co-op
and
it
does
DNS
Sdn.
It
does
nothing
like
this.
How
would
you
expect
something
like
that?
That
has
a
completely.
P
S
D
Okay,
there's
nobody
else
at
the
mic.
Is
there
more
slides
here
or
is
that
was
at
last?
Okay,
so
there's
clearly
interest
in
this
topic
and
I
think
we
did
mention
earlier
coming
up
with
a
reach,
our
Turing,
so
maybe
factoring
in
this
type
of
interval
and
interactivity.
Whatever
the
word
is,
it
would
be
a
good
thing
to
put
into
the
Charter
I
think
if
we
good
is
Christian,
are
you
on
the
DNS
SD
list
Christian?
D
Could
you
send
a
list
info
about
the
inter
up
to
the
list
if
you're
not
on
the
list,
feel
free
to
send
it
to
the
chairs
and
we'll
advertise
it
I
think
this
is
something
we
need
to
pick
up
and
have
some
people
involved
with
and
something
like
that
in
trop
of
nth
sounds
like
a
good
way
of
getting
some
communication
going.
So
thanks
very
much
Kari.
Oh
that's
right!
That's
very
useful.
D
Dns
SD
privacy,
so
we
have
a
couple
of
people
that
is
going
to
speak
briefly.
To
that
to
prime
the
discussion
is
Krish.
Jin
yeah
is
I
an
Stewart.
So
basically,
what
we
would
like
to
do
is
to
discuss
the
scope
and
requirements,
obviously
within
the
working
group,
so
that
we
can
agree
what
work
we
want
to
do,
and
it
may
be
that
we
continue
to
progress
with
the
work
that
Daniel
and
Christian
have
done
so
far,
which
I
think
we
all
seems
to
be
the
working
group
consensus
that
it's
it's
good
work.
D
The
question
is:
is
it
the
right
work?
Is
it
the
complete
thing
we
want
to
do?
How
does
it
fit
in
with
the
broader
view
of
privacy
that
we
have?
So
you
have
a
couple
of
people
we're
going
to
just
talk
to
this
topic
first
and
then,
we've
got
essentially
the
rest
of
the
session
to
discuss
the
topic,
so
I
think
Christians
going
first,
if
I
remember
rightly,
oh,
it's
just
Christian
talking.
Is
it
so,
but
I've
got
two
slide
decks.
I've
got
the
scaling,
talk
and
I've
got
the
scenarios
scenarios
first,
cool.
R
So
the
first
feedback
was
that
we
need
to
have
consensus
on
what
scenarios
we
are
addressing,
and
so
we
added
a
couple
of
hallways
discussions
and
I'm
trying
to
summarize
this
with
the
scenario
that
we
are
saying
so
the
first
scenario
minute
the
kind
of
threat
we
are
looking
at.
All
those
threat
are
linked
to
warming
users.
I
mean
it's,
it's
pretty
clear
that
if
you
do
as
a
discovery
scenario
in
your
own
house
between
devices
that
stay
within
the
house-
and
nobody
listened
to
them,
the
privacy
consideration
are
pretty
minimal.
R
R
You
will
send
metadata
with
your
queries
and
that
metadata
can
be
used
by
advanced
service
at
the
Guyana
Hut
in
this
slide
to
correct
information.
For
example,
if
we
take
the
NSS,
if
we
use
the
NSS
in
a
coffee
shop
to
discover
the
printer
in
the
coffee
shop,
well,
obviously
that
there
is
a
printer
in
the
coffee
shop
is
not
something
that
is
secret
and
discovering.
R
It
is
not
a
big
privacy
issue,
it's
meant
to
be
Schelotto,
but
having
someone
register
who
is
using
that
printer
when
and
specifically,
was
in
the
coffee
shop
when,
because
of
metadata
leaked
by
the
discovery?
That
would
be
bad.
So,
in
that
scenario,
Wilson
are
you
in
which
a
service
public,
the
client
is
not
add
alcohol.
There
is
to
not
disclose
the
client
identity
to
make
sure
it
can
be
not
be
linked.
R
You
have
a
second
scenario,
suppose
that
David
and
Scott
are
in
a
coffee,
shop
and
they're
deciding
to
do
some
application,
so
they
use
DNS
SD
to
synchronize
the
application.
One
of
them
becomes
a
server,
the
other
one
becomes
the
client
they
discover
each
other.
They
do
some
fancy
application
and
life
is
good,
except
that
the
guy
in
the
Hat
has
looked
at
all
the
metadata,
and
now
he
knows
that
David
is
speaking
to
Stewart.
R
So
he
knows
that
both
of
them
are
here
and
also
may
well
know
what
kind
of
service
they
are
using
and
infer
what
kind
of
job
they
are
doing.
So
in
that
kind
of
scenario,
our
requirement
is
clear
men.
We
would
like
to
make
sure
that
nothing
is
public,
that
we
don't
disclose
the
client
identity
and,
if
possible,
that
we
don't
disclose
when
we
don't
use
either
the
client
or
the
server
identity,
and
we
don't
disclose
the
type
of
service
that
they
are
doing.
R
So
that's
I
think
is
the
the
classic
scenario
in
the
preparation
for
this
meeting.
We
discussed
these
two
scenarios.
I
added
and
also
one
I-
think
it
David
is
a
pretty
modern
guy.
So,
yes,
he
has
a
fancy.
Watch
has
a
fancy
phone
and
and
a
fancy
watch
is
trying
to
discover
the
fancy
phone
using
DNS
SD
to
see
hey,
should
I
update
my
screen
or
something
and
that's
pretty
much
the
same
scenario
as
the
one
we
have
seen
before.
R
G
I'm
glad
you're,
including
all
these
norwich,
you
said
this
is
pretty
much
the
same.
It
mostly
is.
There
is
one
difference,
though,
which
is
that
in
this
scenario,
David's
watch
and
David's
phone
are
both
owned
by
David.
Yes,
so
there's
Ennis
in
a
sense,
a
bobble
that
those
devices
talk
to
each
other,
but
they
don't
talk
to
other
things
in
Scenario
to
David
could
be
exchanging
copies
of
the
slides
for
this
meeting
with
me
with
you
with
Tim,
so
you
can't
assume
that
those
devices
were
set
up
by
the
same
owner
at
home.
G
R
But
it
is
not
the
same
scenario
and
and
that's
pretty
much
a
scenario
that
we
are
concerned
with.
Okay
at
the
8th.
The
next
in
the
next
point
that
I
wanted
to
say
is
that
if
you
look
at
the
general
class
of
solutions
for
those
problem,
they
all
involve
having
some
kind
of
secret
shared
by
the
client
and
the
server
and
used
to
protect
the
discovery
mechanism.
I
mean
how
you
do
that
exactly
will
vary,
of
course
greatly.
R
Depending
on
the
specific
protocol.
You
shoes,
but
I
mean
this
requirement
that
they
be
some
kind
of
secret.
Shared
is
pretty
much
in
event
to
the
scenario
now
the
point
there
is
that
we
have
two
ways
to
think
about
those
secrets
and
in
many
implementations
like
when
you
are
doing
your
pairing
of
your
Bluetooth
device
with
your
car,
something
like
that,
we
are
using
one
single
secret
exchange
to
do
both
the
authorization
of
the
service
and
the
protection
of
the
discovery
and
as
the
classic
pairing
scenario,
that's
not
necessarily
the
only
scenario
I
mean.
R
In
fact.
If
you
look
at
the
discover
your
climate,
it
may
well
be
adequate
to
have
a
lightweight
discovery,
filter
off,
which
is
just
meant
to
ensure
that
the
message
that
we
are
changing
don't
leak
metadata
and
to
have
a
distinct
authorization
for
CTO,
which
is
meant
to
ensure
that
the
client
is
authorized
to
access
the
resource
that
the
server
wants
to
make
available.
R
A
D
R
I
was
not
I
could
not
travel
there,
but
basically,
if,
if
we
see
we,
we
got
feedback
event
we
at
ITF
100
and
there's
a
lot
of
feedback.
But
I've
tried
to
put
that
in
the
big
bullet
points.
Okay,
there
is
a
first
ever
of
feedback,
which
is
relevance
and
where
events
in
the
sense
that
we
have
discussed
that
in
the
DNS
SD
working
group
discuss
privacy,
but
we
got
actually
very
little
feedback
in
the
working
group
as
if
there
was
only
minimal
interest.
R
Don't
know
about
that,
I
mean
if
the
suit
Truman
had
actually
the
second
specific
piece
of
feedback
on
the
solution
that
we
proposed
focused
on
three
points.
One
was
that
in
our
solution,
we
proposed
a
pair
device
model
which
is
in
line
with
many
would
say.
Historic.
Implementation
of
the
NSS
D,
but
which
may
not
be
in
line
with
the
emerging
usage
and
the
emerging
usage,
is
that
people
install
applications
and
that
the
device
are
controlled
by
the
application.
R
R
So
it's
clearly
something
where
you
have
to
have
application,
and,
yes,
you
can
achieve
that
by
having
in
the
operating
system
a
centralized
service
which
is
then
specialized
with
a
lot
of
access,
control
procedures
and
things
at
that
is
clearly
one
way.
But
a
very
simple
way
is
to
imagine
that
you
are
doing
the
discovery
from
within
the
application
itself
so
that,
basically,
things
are
well
compartmented
and
intervals.
R
R
It
was
complicated
in
terms
of
scaling.
In
particular,
some
of
the
exchange
require
the
large
number
of
application
or
a
large
number
of
messages.
So
I
went
back
to
with
to
the
drawing
board
and
say:
okay,
do
we
have
a
fundamental
tension
between
privacy
and
scaling
and
what
are
the
trade-offs?
And
that's
what
I
would
like
to
present
here
and
in
order
to
examine
those
trade-offs?
I
looked
at
three
options:
the
first
option
is
what
we
are
now,
which
is
require
a
pairing
process
which
leads
to
pairwise
secrets.
R
That's
actually
what
most
coffee-shop
do
to
let
you
access
their
Wi-Fi
switch,
but
that's
one
possible
thing
and
clearly,
because
you
have
something
shipped
by
every
client,
your
your
scanning,
for
what
you
are
going
to
be
different
and
the
third
design
is
to
have
something
based
on
public
key
and
effectively
treat
that
shared
secret
use
for
the
chat
secret,
the
public
key
of
the
server.
So
let
me
justify
that
for
a
moment,
a
public
key
is
a
unique
identifier.
R
R
R
But
you
have
a
first
message,
the
query
message,
which
is
say:
hey
I'm,
looking
for
this
server
and
you
do
that
by
adding
sending
a
hash
of
the
key
and
the
nonce
or
if
you
want
to
spend
more
cycles
like
an
encryption
of
the
nonce
with
the
public
key
of
the
server,
but
only
the
server
can
decode
it.
And
then
the
reply
comes
from
the
server
and
the
replies
includes
an
encryption
of
the
norms
with
the
private
key
of
the
server
that
the
client
can
verify
to
check
that
yeah.
R
R
R
The
also
dimension
is
the
number
of
servers
that
you
have
forged,
client
or
not.
Let's
say
the
same,
because
there's
some
kind
of
a
fan-out
happening
there
and
a
third
interesting
dimension
in
terms
of
network
traffic.
It's
the
number
of
servers
that
are
present
in
the
scope.
So,
for
example,
my
phone
can
be
paired
to
50
other
phones
for
some
game
application
or
whatever,
but
of
those
50
game
partners.
Maybe
only
five
I
knew
room
at
a
given
time,
so
these
are
the
difference
between
a
M
and
P
in
that
scaling
property.
R
R
Well,
if
you
want
to
have
pairwise
keys,
you
will
have
one
record
their
third
device,
so
a
B
n,
if
you
arm
to
have
something
which
is
common
to
all
clients,
beat
of
shared
password
or
public
key.
You
would
have
just
one.
So
that's
so
far.
Okay,
the
number
of
response
to
a
query.
If
you
do
dns
SD-
and
you
say
hey
how
many
server
out
there
that
implements
service
number
X
and
I'm
saying
that
was
the
ocean
design
that
we
have
in
which
the
service
is
specify
as
to
privacy
service.
R
Well,
in
the
case,
are
further
the
pairing
solution.
You
will
receive
n
times
P
responses,
because,
while
you
have
any
response
per
server
and
your
pizza
was
present
and
the
client
will
sort
out
which
of
those
are
good
in
the
shared
secret,
you'll
receive
one
response
of
every
seller,
and
so
in
the
public.
R
The
there
is
a
variation
of
that
that
we
have
not
implemented
in
our
draft,
but
could
be
done
suppose
that,
instead
of
making
the
instance
name
a
function
of
the
norms,
you
make
the
service
name
a
function
of
the
notes.
So
basically
servers
at
the
theis
random
service
is
randomized
service
and
clients
can
predict
which
randomization
scheme
the
server
is
using.
R
R
Another
dimension
of
scaling
there
is
weather.
Caching
is
possible,
so
in
mdns
in
particular,
we
do
caching
by
listening,
to
responds
to
auto
of
clients
and
caching
them,
and
if
you
have
a
pairing,
a
pairwise
secret.
You
cannot
do
caching,
because
each
response
is
manufactured
for
exactly
one
client
in
the
shared
secret
kind
of
stuff.
Then
you
can
do
caching,
because
it
will
Sam
responds
to
every
client.
R
R
If
you
have
a
pairwise
secret,
you
will
just
need
to
repair
one
secret.
You
will
need
to
say
all
Stewart
York
is
compromised,
let's
get
a
new
one,
but
if
you
have
a
shared
secret,
you
are
going
to
obviously
need
to
go
contact
all
the
clients
you
had
that
have
that
just
secret
and
tell
them
hey.
You
know
what
of
our
global
key
is
compromised.
We
have
to
pick
a
new
one.
Everybody
has
to
change
so
that
gives
you
this
cause
for
radiation
them.
R
R
Obviously,
if
you
can
impersonate
the
client,
you
will
be
able
to
discover
all
the
servers
that
the
client
can
discover
and
that's
true
for
every
solution
now.
The
next
thing
is,
can
you
not
just
discover
the
servers
but
also
the
clients
that
are
connected
to
the
server
and
if
you
have
a
shared
secret
like
a
shot
password?
The
answer
is
yes,
absolutely.
R
R
R
In
the
case
of
the
shared
secret
yeah
and
in
the
secret
public
key.
Ok,
you
can
say
you
can
pretend
that
the
server
is
present
and
if
you
pretend
that
the
server
is
present,
you
are
going
to
discover
the
other
guys
now,
in
the
case
of
the
public.
Key
I
may
be
a
bit
pessimistic,
because
if
you
pay
the
cost
of
having
your
query
encrypt
a
secret
with
the
public
key
of
the
server,
then
basically
you
need
to
have
the
private
key
of
the
server
to
decrease
of
secret.
R
R
So
if
I
summarize,
in
the
case
of
the
pairing,
we
have
more
messages
in
the
case
of
the
public
key,
but
we
can
repeat
that
if
we
make
the
secret
dependent
on
the
device
on
the
service,
ID
meant.
Basically,
if
we
have
to
do
cell
excuse
me,
if
you
have
the
service
ID
depend
on
the
secret
of
risk.
It
is
by
the
secret,
in
which
case
we
are
back
to
order
of
one.
R
R
O
Into
a
theater,
I
think
there's
another
row
that
you
said
verbally
and
I
want
to
confirm
that
I
have
the
other
contents
right
is
the
other
row
is
cost
of
CPU,
then
pairing
and
shared
secret
are
basically
symmetric
and
therefore
fast
by
comparison
and
shared
secret.
Public
key
is
asymmetric
and
therefore
a
slow
by
comparison
is
that
correct.
That
is.
R
R
So
yeah,
that's
that's
true.
So,
if
you
ask
me,
for
my
preferences,
without
constraints,
I'll
be
tempted
to
go
to
something
like
this
secret
public
key
class
of
solution,
because
it
has,
it
has
some
pretty
good
properties
in
terms
of
effectively
in
terms
of
provisioning.
Many
pavia,
if
you
want
to
publish
on
a
client
in
the
case
of
with
a
public
key,
you
just
have
to
give
them
a
copy.
If
you
want
to
polish
on
a
client
with
a
pairwise
secret,
you
have
to
do
something
complicated.
R
A
So,
thank
you
very
much.
Christian
I
think
this
did
a
really
good
job
of
showing
the
various
possibilities
we
have,
and
so
I'd
like
to
kind
of
kick
off
a
discussion
in
a
working
room
where
our
goal
for
today
would
mainly
be
to
figure
out
requirements
as
in
the
use
cases
that
Christian
described
earlier
are
those
the
ones
we
want
to
solve.
Are
there
other
ones
we
want
to
solve
other
ones
that
we'll
just
basically
don't
want
to
solve,
because
at
the
end
of
the
day,
there
are
quite
a
few
compromises
here.
A
There
are
quite
a
few
options,
for
example,
if
you
want
to
do
a
symmetric
or
asymmetric
crypto
and
based
on
what
security
properties
we
want
our
system
to
have
some
of
these
will
work
and
some
of
these
won't.
So
if
people
have
questions
or
topics
they
want
to
bring
up,
please
come
ahead
now.
Otherwise,
I'll
start
with
a
few
questions,
get
people's
opinion.
A
T
Chris,
we'll
just
a
quick
query:
vine
question
Chris:
what
are
what
kind
of
constraints
are
we
setting
for
the
type
of
cryptography
using
so
I
Christian,
discuss
this
basic
symmetric,
key
stuff
and
then
standard
public
key
stuff,
but
there's
more
there's
newer,
flavors
of
cryptography.
They
could
be
applicable
here
particular
some
work
at
the
endpoint,
a
and
others
did
from
Stanford
on
this
exact
problem,
private
service
discovery
and
they
use.
You
know
fancy
identity
or
pairing
based
cryptography,
and
maybe
we
should
or
should
not
look
at
that.
There's.
T
It's
not
at
all
been
discussed
in
the
ITF,
but
the
properties
that
provides
are
quite
nice.
In
particular,
it
gives
you
stronger
identity,
hiding
when
you're
advertising
or
placing
service
records
somewhere
and
when
a
sender
who
our
client
wants
to
contact
the
service
when
it
sends
its
initial,
like
whatever
request
right
terminology,
would
be
that's
completely
hidden
and
they
have
Fulton
eye
ability
of
actually
doing
so
so
I
would
like
to
like
lobby
for
including
these
newer
types
of
primitives
and,
of
course,
maybe
consulting
with
the
security
area
or
the
CFR
G
to
see.
D
A
G
Chris,
you
asked
a
question
generally
of
the
room.
My
opinion
is,
we
should
not
be
ruling
anything
out
in
principle.
We
should
look
at
it.
We
may
decide
later
about
what's
appropriate
or
not
appropriate
or
or
easy
to
implement,
but
but
definitely
we
should
not
rule
anything
out
before
we've
looked
at
I
will,
as
David
said,
I
was
not
aware
of
dampeners
work.
I
will
add
that
reference
you
sent
me
and
I
can
update
the
draft.
I
think
this
is
a
relatively
new
area
a
few
years
ago.
A
N
At
the
end
of
the
day,
exactly
what
sort
of
metadata
is
being
exposed
by
the
roaming
client?
It
seems
to
me
that
we
cannot
cloak
the
IP
of
the
of
the
client
or
the
IP
of
the
responder
or
the
fact
that
the
client
is
doing
discovery
in
the
first
place.
Based
on
you
know,
perhaps
the
port
that
it's
accessing
so
I,
guess
at
the
end
of
the
day,
is
this
work
really
about
cloaking?
What
the
client
is
trying
to
discover
and
what
it's
getting
back?
In
response?
That's
number
one
number
two.
N
R
Thanks
Gary!
Yes,
if
you
look
at
the
original
draft
that
we
do
the
DNS
SD
privacy,
we
listed
the
set
of
metadata
that
are
in
the
DNS
SD
headers,
and
you
have
things
like
a
service
name
in
the
clear
service
instance
name
in
the
clear
and
host
name
in
the
clear,
and
these
are
independent
of
the
IP
addresses.
In
the
case
of
the
coffee-shop
scenario,
you
don't
care
that
much
about
your
IP
address.
You
just
got
it
from
the
coffee
shop,
so
it
doesn't
matter.
It's
not
something
new.
R
T
Kind
of
clarifying
the
process
related
question,
I,
guess,
sort
of
related
with.
What's
your
saying
is
there
or
what
are
the
plans
for
collaborating
with
the
security
area
on
this
particular
problem,
because
they
will
of
course
have
very
strong
opinions
about
which
type
of
crypto
we
use
or
which
type
of
security
sign?
We
have
and
better
to
start
that
earlier,
rather
than
later,
yes,.
D
R
Had
an
evolution
both
of
the
of
the
privacy
of
the
discovery
and
the
padding
and
they
say
well:
yeah,
okay,
you're.
Basically,
the
high
level
thing
of
the
the
privacy
discoveries
that
we
are
using
a
few
sketti
discovery
to
find
a
service,
a
pirate
service
and
then
doing
a
terrace
connections
that
servicing
so
basically
were
using
non
components.
And
if
you're,
using
known
components,
you're
pretty
much
in
the
clear
sure
sure.
T
A
O
So
follow
up
on
a
couple
of
the
comments.
Let
me
start
by
following
up
on
the
comment
about:
what's
old
and
what's
new
there's
a
related
field,
that's
old,
because
this
is
only
solving
half
of
the
problem.
Okay,
so
what's
old
is
if
I've
already
discovered
you
and
I
want
to
open
up
an
authentication
channel
with
you.
How
do
you
do
that
in
a
way
that
preserves
privacy
right
and
so
on?
Christians
first
use
case
where
one
side
is
publicly
inside
is
private.
That's
the
typical
case.
O
It
everybody
does
an
authentication
today
and
one
side
is
private.
Okay,
the
other
cases
where
both
sides
want
to
be
private
from
intermediaries
and
not
reveal
their
identity.
It
a
case
that
is
a
field
that
has
been
around
for
at
least
15
years.
It
originally
started
as
being
called
the
secret
handshake
protocols
and
now
the
new
term,
as
of
maybe
eight
years
ago
or
whatever
has
renamed
as
authentication,
sorry
affiliation,
hiding
authentication,
so
eh-eh-eh
search
for
affiliation,
hiding,
authentication,
you'll
find
stuff.
O
I
actually
gave
a
talk
at
the
core
working
group
a
couple
times
ago,
where
I
had
a
whole
slide
of
a
bunch
of
one
bullet
references
of
things
in
that
area.
Okay
and
so
I
also
sent
emails
to
the
C
FRG
saying
this
is
well
known
in
the
literature
to
have
affiliation,
hiding
authentication,
but
there's
nothing
any
standard
or
any
widely
available
implementation,
but
in
the
research
it's
been
around,
for
you
know
eight
to
ten
years,
can
we
do
something
in
the
center
suite
that
actually
uses
with
protocols
like
TLS?
So
far,
nothing's
happened
yet.
O
Okay
and
the
point
is
what's
new-
is
to
say
well
this
problem
that
says:
I
only
want
to
discover
things
for
which
authentication
would
have
succeeded.
That's
the
new
part
of
the
problem
and
what
Christian
and
people
are
trying
to
address
now
is
how
do
I
discover
things
for
which
the
authentication
using
one
of
those
mechanisms
or
that
style
of
scenario,
would
have
succeeded
and
I
want
to
discover
things
that
would
not
have
it
succeeded
right
and
I
want
to
do
that
without
reviewing
the
other
metadata
that
Christian
mentioned
right.
O
That's
the
part
that
is
relatively
new
okay,
but
the
discovery
is
only
half
of
the
problem.
I
have
to
be
able
to
open
up
an
authenticated
session
with
you
know,
TLS
or
whatever
else
it
is,
and
if
the
same
scenarios
are
just
going
to
reveal
your
identity.
Anyway,
that's
only
half
the
problem,
okay,
and
so
we
actually
need
work
from
CFR,
G
and
other
people
for
the
other
parts
of
the
problem,
and
so
how
do
we
relate
to
the
rest
of
sag
and
so
on?
O
Yeah
we
need
some
work
and
standards
and
so
on
to
make
sure
that
say,
typical
TLS
libraries
and
protocols
have
affiliation
hiding
authentication
schemes
that
preserves
the
identity
of
both
sides
right
today,
usually
one
side
reveals
it's
at
dinner
to
the
other
one.
Then
they
establish
a
session
right.
O
T
Thanks
Chris
but
yeah
just
going
back
to
the
work
of
Bonet,
they
do
in
fact
their
solution
does
provide
mutual
privacy
for
both
this
and
their
in
the
for
the
client
and
the
server
by
exploiting
the
fact
that
there
is
a
dis,
private
discovery
step
beforehand,
so
that
these
two
kind
of
problems
are
very
tightly
coupled.
If
you
do
just
you
know,
try
to
connect
to
a
server
and
then
authenticate.
T
D
R
R
Is
and
it's
pretty
much
what
they've
Terrell
said
is:
should
we
be
concerned
with
the
policy
property
of
the
actual
connection
between
client
and
server,
and
and
and
that's
it,
that's
a
piece
of
work.
My
tech
is
that
that
piece
of
work
is
probably
something
which
is
more
on
the
TRS
working
group
than
the
DNS
SD
working
group,
and
that's
why
I
did
not
want
to
take
it
here.
R
A
Way,
I
would
rephrase
that
is
as
a
requirement
do
we
have
a
requirement
that
private
discovery
allows
us
to
bootstrap
and
authenticate
it
encrypted
channel.
So
one
example
that
does
it
lead
to
assured
secret
or
public
keys
that
we
can
use
for
TLS.
That
would
be
might
be
a
reasonable
requirement.
Yeah.
R
If,
if
you
look
at
the
1213
SSD
privacy
to
have
the
two
fails,
do
have
the
second
faceted
here
is
a
TLS
connection,
and
when
we
specify
that
we
are
very
concerned
precisely
with
this
kind
of
TLS
leakage,
specifically
the
replay
attack
I
mean
if
some
once
we
place
the
your
clients,
connection,
attempt
and
the
server
does
a
handshake.
The
interior
servers
handshake
reveals
the
server's
identity.
R
So
that's
why
we
add
basically
a
shot
secret
mineral
PSK
in
the
original
grant,
hello
that
will
protect
the
handshake
and
allows
the
server
to
not
do
that.
Now,
whether
we
want
to
have
that
class
of
solution
generalize
to
also
application,
that's
indeed
something
we
can
debate
Pertamina
yeah.
We
may
want
to
respond
to
those
four
four
questions.
First,.
G
G
That
I
think
it
may
be
question.
We
can't
answer
it's
a
question
that
we
should
document
that
we
say
the
tradeoff.
If
you're
building
a
super
low
power
battery
device,
then
you
don't
get
these
privacy
benefits
or
if
you
want
the
privacy
benefits.
You
probably
can't
do
that
with
something
running
on
the
lithium
coin
cell,
because
you
can't
go
to
sleep
so
my
suspicion
is.
We
won't
solve
problem
number
two,
but
we
need
to
lay
out
the
trade-offs
that
you
get
to
pick
one
or
the
other,
but
not
both.
H
Tompa
so
teri
seems
like,
in
the
first
case
that
you
are
going
to
limit
what
you
can
do
if
you
require
that
Christian
stuff
seems
to
be.
You
know
working
independently
of
that
and
once
you,
you
have
to
reveal
something
to
go
through
a
proxy
and
so
you're,
obviously
going
to
reveal
more
than
you
would
have
to
do
it.
If
you
don't
so
I
think,
there's
two
cases
here
and
we
might
be
okay
to
have
a
subset
that
works
for
the
proxy,
but
it
won't
be
the
same
as
what
Christian
came
up
with
thanks.
E
B
A
E
K
This
is
Dave
Robbin.
That
leads
me
to
my
burning
question
and
I've,
been
sitting
here
waiting
for
somebody
to
discuss
when
you
talk
about
granularity,
going
sort
of
to
an
application
granularity
instead
of
a
device
granularity
to
me
and
then
trying
to
hide
that
application.
The
problem
with
that
is
that
that
application,
that's
trying
to
hide
the
application
doing
the
discovery
itself.
It's
doing
it
with
my
MAC
address,
which
I
had
another
application.
That
did
this
completely
plain
text
thing
over
here.
That
completely
identifies
me.
K
So
what's
the
point
it
had
this
super
application.
That's
trying
to
secretly
find
something,
but
my
traffic
is
originating
from
a
device
that
has
been
clearly
identified
by
other
leaky
things.
So
in
the
case
of
the
blood-gas
monitor
or
a
printer
or
a
specific
function
device
that
has
one
function
and
one
application.
It's
easy,
because
that
that
random
MAC
address
that
he
got
that's
completely
private,
but
it's
associated
with
that
one
application
and
that's
fine.
K
His
entire
existence
is
that
one
application,
but
when
you
have
a
multi-tenant
kind
of
thing
platform,
with
only
one
IP
address,
how
do
you
have
any
privacy
of
the
apps
to
me?
That's
sort
of
like
each
app
needs
to
run
in
its
own
little
virtual
machine
with
its
own
bridge
MAC
address
and
it
you
know
it
has
its
own
stack,
I,
don't
I,
don't
know
any
other
way
to
do
it.
How
can
an
app
hide
without
having
its
own
stack
its
own
IP
address?
That
is
completely
opaque,
so
I
think.
A
I'll
attempt
to
answer
that
and
I
think
the
people
at
the
mic
can
add
to
that.
It
depends
what
you
mean
by
what
we
mean
by
hiding
in
the
in
the
example
or,
let's
say:
I
have
a
phone
that
is
simultaneously
trying
to
print
on
the
coffee
shop
Network,
but
also
talking
to
a
medical
device
that
I
have
right.
A
I
would
be
okay
if
the
printing
system
leaks
that
my
IP
address
and
people
know
that
David's
printing,
but
I
would
still
want
to
keep
hidden
the
fact
that
David
has
this
medical
device
they
or
that
David
is
running
the
this
medical
application
and
I.
Think
you,
if
one
leaks
the
fact
that
there
is
an
IP,
that's
sending
packets
still
trying
to
hide
like
the
name
of
services.
It
supports
his
value.
K
G
Yeah
yeah,
we
covered
a
bunch
of
different
topics
there.
One
thing
I
would
say:
is
you
you
raise
this
hypothetical
thing
as
if
it
was
ridiculous,
I,
don't
think
it
is
I,
don't
think
it
is
I.
Don't
think
it
is
out
of
the
question
that
we
could
imagine
every
application
having
its
own
MAC
address
and
its
own
user
space
stack.
Now,
that's
not
the
work
of
this
working
group,
but
that
there
is,
there
is
increased
yeah
Kristi,
saying
we're
going
there.
G
Windows
has
pretty
windows,
has
pretty
good
mac
address
randomization,
which
is
Christian's,
work
and
I.
Think
in
the
next
in
the
coming
decade,
we're
gonna
see
more
and
more
awareness,
there's
been
new
new
rule
changes
in
the
European
Union
about
data
privacy
for
customers.
So
there's
a
lot
of
awareness
of
this
and
I
think
stuff
like
that
is
going
to
happen.
G
The
question
of
the
granularity
came
to
my
mind
because
of
a
couple
of
examples
and
if
I
give
those
it
might
make
it
clearer
many
many,
but
ten
years
ago
now,
Apple
launched
this
service
called
back
to
my
Mac
and
it
had
similar
privacy
concerns
that
we
used
to
call
it.
The
Steve
Jobs
problem
that
when
he
checks
into
a
hotel
in
New
York
with
his
laptop
running
back
to
my
Mac,
if
it
looks
up
the
DNS
records
for
s
job
members,
Mac
comm
in
the
clear
then
the
paparazzi
can
report
paid.
G
G
One
of
the
issues
with
back
to
my
Mac
is
it
is
more
or
less
a
per
device.
Implementation.
Laptop
computers
can
have
multiple
user
accounts.
They
can
have
multiple
people
logged
in.
At
the
same
time,
I
can
be
locked
in
by
SSH
to
a
machine
that
someone
else
is
using
and
my
back
to
my
Mac
file
system
and
their
back
to
my
Mac
file
system,
we're
all
in
the
same
file
system.
Our
kernel
doesn't
support
per
user
file
systems,
so
you
better
trust
what
it
comes
down
to.
Is
you
better
trust?
R
E
So
there
was
a
comment
on
jammer
from
Daniel.
Okay,
so
should
a
medical
device
really
join
a
public
Wi-Fi
network
for
communicating
with
the
phone,
but
I
think
here
that
it
is
using
Wi-Fi,
not
the
public
Wi-Fi
right,
so
it
is
talking
over
Wi-Fi,
but
it's
not
joining
the
public
Wi-Fi
right.
That
Stewart
probably
says
yeah.
G
Hi
Daniel
I
just
ran
up
to
the
microphone.
The
concern
we're
looking
at
here
is
it
a
lower
level
than
what
we
might
call
joining
a
Wi-Fi
network
or
associating
with
an
access
point.
If
you're
transmitting
radio
signals
at
all,
then
other
devices
in
the
vicinity
can
receive
those
signals,
and
we
want
to
make
sure
that
even
though
they
can
receive
them,
they
can't
make
sense
of
what
they
mean.
E
Michael
Lorenzen
us
so
I
was
also
thinking,
so
this
is
privacy
is
I,
want,
probably
want
to
expose
what
services
I'm
doing
differently
to
different
devices,
users
and
so
on.
Is
this
or
is
that
what
we're
talking
about
here
as
well
when
it
comes
to
sir,
if
I
see
what
my
device
is
broadcasting
its
broadcasting
when
I
come
here,
sometimes
I
see
my
printer
at
home
being
broadcast
well,
why
does
it
do
that?
It
should
not
probably
do
that
right.
E
A
R
So
yeah
I
mean
yes,
I
mean
I
I'm
kind
of
convinced
that
we
want
to
do
application.
There
are
also
reason
to
the
application
like
possibility
that
effect
applications
can
move
them
from
one
machine
to
another,
and
things
like
that,
that's
and,
and
and
yes,
I
mean
I
pretty
much
echo
is
your
turn
arises
that
we
should
walk
for
discovery
proxy,
mostly
man,
I
I
I
I
can't
see
why
we
would
not
okay
and
that
for
the
slippiest.
Now
that
scenario
aya
argue
that,
from
the
client
point
of
view
is
not
so
much
and.
R
Such
measure
dns
SD
scenario
as
an
mdns
in
our
the
first
one
and
basically
it's
back
to
the
hostname,
considered
harmful
I'll,
see
the
the
structure
of
mdns.
As
saying
slacker,
I
publish
my
host
name
and
I
publish
things
like
that,
which
tend
to
be
unique
identifiers.
It
can
be
talked
and
there
are
two
live.
R
If
you
look
at
the
draft
at
the
privacy
to
aft,
we
at
WestEd
by
saying
that
there
are
really
two
levels:
I
mean
that
does
the
effective
EDM
DNS
mechanism
in
which
you
have,
but
they
are
also
in
the
DNS
SD
publishing
mechanism
and
we
should
publish
a
hostname
when
you
publish
a
service
and
it's
completely
under
the
hood.
So.
D
In
the
example
on
the
screen
there
that
you
produce
that's
a
printer
and
one
would
imagine
the
printer
is
in
secret,
people
can
see
it
it's
there.
You
want
to
discover
it's
kind
of
unsafe
public,
but
certainly
well
advertised
within
the
organization
or
building,
whereas
in
this
situation,
where
it's
a
person,
that's
where
yeah.
E
R
R
Well,
that
should
be
randomized
I
mean
you
should
randomize
that
that
you
don't
leave
that
information
and
that's
not
tied
to
any
of
the
service
discovery
mechanism.
It's
some
kind
of
a
low-level
thing
that
we
may
want
to
excise,
and
just
do
because
that
it
has
no
influence
on
the
service
that
hostname
never
appears
on
the
UI,
except
on
the
black
hats
UI.
So.
D
D
D
How
should
we
shape
capturing
these
issues
going
forward?
Should
we
try
and
bring
all
this
down
and
distill
it
into
one
draft
where
we
describe
these
requirements
drawing
from
those
three
sources,
whether
that
might
all
go
into
Stewart's
existing
draft
I
don't
know
which
could
be
sucking
fresh,
but
it
sounds
like
we
want
to
get
all
these
things
captured
in
one
place
and
we
would
like
presumably
to
encourage
a
couple
of
other
areas
to
look
at
it
as
well.
D
J
My
name
is
Nam
kovalevskiy.
We
have
been
just
emulating
responding
to
that
cue.
Several
years
ago
there
was
a
GU
project
called
webinos
that
was
a
cross-domain
project
and
was
trying
to
discover
how
what
kind
of
all
kinds
of
devices
that
people
will
use,
including
those
they're
wearing
on
their
body,
interact
with
the
rest
of
the
world.
With
the
other
things
on
the
body
or
with
things
that
other
people
are
carrying
on
their
body.
There
was
a
concept
of
like
a
personal
domain
or
personal
zone
or
cloud.
J
J
Now
is
well,
you
know
there
may
be
more
like
that
right
or
they
may
be
in
a
kind
of
a
separation
zone
around
like
these
individuals,
that
that
is
an
entity
in
itself.
That's
currently
not
discovered
here
on
these
slides,
and
maybe
it's
worth
looking
worth
looking
at
that
I'm
just
I
can
share
links
to
that.
Yes,
but
in
a
place,
if
you
could
share
that
song,
the
Miriam.
R
A
D
We've
got
three
bodies
of
text
to
draw
from
there
plus
the
discussion
today
where
it
goes,
I
think
as
chairs
we
mind,
but
it's
important
that
the
work
starts.
Moving
forward
continues
to
move
okay,
so
I
think
with
just
a
few
minutes
left
to
go,
will
draw
and
start
drawing
to
a
close.
That's
been
very
useful.
Thank
you.
Everybody.
D
D
Of
those
so
we're
good
there,
the
service,
registration,
yeah,
that'll,
obviously
push
forward,
and
the
recharter
in
law
will
help
with
that.
So
the
things
I've
got
written
down
here
is
things
you've
agreed
and
maybe
some
actions
just
wrapping
up
the
first
one
was
the
road
map
documents
being
agreed
in
the
room,
so
we'll
check
that
adoption
with
the
list.
D
D
The
next
thing
was
we
agreed
it's
time
the
working
group
had
a
look
at
its
Charter
and
we
will
I
think
through
the
list,
decide
what
things
need
to
go
into
the
Charter
and
maybe
what
things
come
out
so
I
think
there's
one
of
the
things
there
is
the
the
new
unicast
oriented
work.
What
things
we
need
there
to
support
that
the
second
one
I
think
will
be
as
David
said,
there's
not
much
in
there.
If
anything.
D
5Th
thing
I've
got,
then
is
there's
probably
scope.
Has
some
new
document
I?
Don't
think
we
nail
down
anyone
to
specifically
work
on
it
at
that?
It's
probably
you
can
probably
guess
who
it
might
be.
We've
got
some
good
guidance
on
deployment
in
home
net,
but
the
deployment
in
the
campus
stroke
enterprise
world
some
document
on
guidance
on
that
and
that
maybe
again
comes
back
to
the
type
of
thing
that
came
up
in
edge
of
cause
as
well.
That
type
of
document
would
be
good.
D
We've
had
some
earlier
work
and
thoughts
on
it
from
Tom
and
Ralph
so
pulling
something
together.
There
would
be
good,
but
we
don't
have
any
specific
anyone
in
the
frame
right
now
in
terms
of
the
interrupts
with
core
we've
had
indication,
there's
an
inter
off
in
April,
and
details
of
that
will
be
sent
to
the
lists.
D
I
think
some
participation
from
this
working
group
in
that
Interop,
which
I
believe
there's
going
to
be
virtual,
would
be
a
good
thing
for
the
group
and
then
the
last
thing
that
the
privacy
work
that
we've
agreed
that
we're
going
to
pull
together
a
draft,
whether
it's
building
on
Stuart's
existing
one
or
new
one,
to
describe
security
requirements
and
to
scope
that
so
we
can
then
get
a
much
clearer
view
of
what
we're
doing
with
the
future
work.
So
I
think
that's
so
everything
I
have.
Is
that
saying
right,
I'm
getting
nods
for
my
right?
