►
From YouTube: IETF101-CCAMP-20180321-0930
Description
CCAMP meeting session at IETF101
2018/03/21 0930
https://datatracker.ietf.org/meeting/101/proceedings/
A
So
on
this,
the
load
wear
and
this
the
new
version
of
the
and
not
where
I
think
of
you
and
should
be
very
family
with
this
kind
of
information,
because
you
know
I,
each
working
group
needs
to
I
introduced
a
lot
where
before
presentation.
So
actually
you
know
this
lot.
We
are
men
is
about
ITF
policies,
especially
IPR
policy,
and
the
definition
of
idea
for
a
contribution
and
participation.
So
if
there
are
some
newcomers,
please
take
a
look.
A
So
it's
usually
have
their.
You
know,
audio
recording,
so
please
be
in
front
of
the
mic
and
state
your
name
before
speaking
and
for
the
minutes.
So
you
know
our
secretary
Oscar
he's
not
here
he's
quite
busy
so
on.
If
anyone
can
capture
some
minutes
and
captured
the
discussion
of
this
session,
we
are
appreciate.
Thank
you
chamber,
loom.
There
are
some
people
are
in
the
gem
balloon
I
think
we
will
keep
an
eye
home
on
the
gem
bloom.
A
A
Okay,
none!
So
an
Amanda
folder!
You
know
I
PR
process,
you
know.
Usually
we
will
do
the
IPR
polling
before
an
individual
job
becomes
a
working
group
document
or
a
working
document
or
group
document
become
goes
to
dub,
G
last
call
and
usually
we
I
and
you
know
hope
the
authors
and
the
contributors
to
the
point,
the
IP
upholding
as
soon
as
possible,
and
then
we
can.
You
know,
speed
up
to
conclude
process.
A
Another
mind
on
the
manliest:
we
always
encouraging
people
to
use
them
many
lists
as
much
as
possible.
Any
technical
issues,
technique
problems
can
be
or
should
be
discussed
on
the
list
and
also
you
know
that
working
group
consensus,
it's
determined
on
the
many
lists
and
not
about
the
you
know,
face-to-face
fits
committee.
Even
though,
if
we
get
some
consensus
here,
we
should
print
the
tutor
to
the
list
for
discussion.
B
So
they're
quite
a
lot
of
progresses
since,
since
last
meeting
we
have
a
new
RFC.
Finally,
we
put
this
this
document
on
all
the
for
a
while
waiting
for
the
generalised
extensions
to
be
done
to
be
done
in
teaser,
the
working
thesis
is
concluded
and
we
could
progress
the
SPF
availability
extension
in
C
camp
which
now
made
it,
and
it's
now
RFC
8380.
We
have
one
more
document
in
the
editor
cube.
B
This
is
another
document
that
was
depending
on
the
generalized
the
HESI
document
and
to
two
documents,
the
microwave
framework
and
the
DWDM
interface
management
framework.
Both
of
them
have
been
submitted
to
the
SD
and
they
are
now
in
the
expert
review
phase
working
group
drafts
on
agenda.
You
will
see
a
new
draft,
the
transport
mvi
applicability
statement.
This
is
a
merger
of
the
existing
working
group
draft
produced
by
the
transport
MBI,
plus
the
analysis
of
the
use
cases.
B
B
C
However,
Holly
and
I'm
taking
care
of
the
OT
in
topology
and
Italian
models,
and
this
model
is
supposed
to
have
the
augmentation
from
the
generic
team
or
those
of
the
increased
working
group
and
the
currently
we
notice
there
are
some
changes
on
the
fundamental
model
that
we
hold
on
for
this
model,
update
to
make
sure
that,
after
the
maturity
of
the
team
models,
we
can
update.
Accordingly,
we
are
now
working
together
with
the
team
of
others
to
make
everything
consistent
thanks
a
lot.
D
B
B
E
Thank
you
me,
Telugu,
see
from
away
represent
Devine
and
update
about
the
transport
MBI
design
team,
so
quick
reminder
about
what
is
the
objective
of
the
design
team
and
its
developers
on
your
skills
and
cap
analysis
to
understand
how
the
ITF
Yamada
can
be
applied
to
transport
network
and
the
coordinator.
We
see
companies
if
any
changes
needed
to
fit
into
the
applicability
and
what
we
do.
E
We
have
a
many
list
conference
calls
and
we
have
a
Geetha
where
we
track
the
changes,
the
editorials,
the
worker
and
open
issues,
what
we
have
Donna
as
already
summarized
a
quickly
by
Daniel.
We
have
a
new
draft,
which
is
a
transport
MBI
applicability
statements
which
is
basically
merging
the
three
documents
that
working
through
document,
the
two
individual
documents
we
produce
the
pasta-
and
this
is
basically
focused
on
analyzing.
The
Yamada's
can
be
used
to
control
a
multi
domain,
ot
and
networks.
E
We
provide
Sanjay
so-called
examples
to
see
how
the
diff
India
in
this
specific
use
case,
the
different
fields
are
filled,
and
basically,
we
focus
on
the
MPI
between
MD,
SC
and
multiple
PNC's,
and
we
work
about
what
is
a
topology
obstruction.
How
to
set
up
the
service
and
to
end
across
a
Muslim
a
network,
how
we
can
configure
protection
restoration,
and
we
have
recently
added
a
possibility
to
modify
the
service
from
protected
and
protect
in
the
modified
event
rhythm.
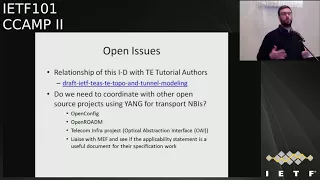
We
have
a
some
open
issues
which
are
we
are
working
on.
E
The
first
up,
initially
is
was
resourceful
on
Monday
during
the
t's
working
group.
Its
relationship
between
this
work,
our
work
and
eighty
tutorial.
We
had
a
some
discussion
yesterday
with
the
autos,
and
we
have
understood
that
the
objective
way
to
work
are
quite
different,
so
Tito
Paul
tutorial
is
mainly
focusing
on
describing
the
principle,
the
definitions
and
modeling
and
modeling
assumptions
for
the
T,
topology
and
tunnel
models,
and
the
use
case
developed
in
documents
are
merely
f2
to
explain
based
on
demand.
People
say
how
do
you
do
this
case?
E
Then
they
show
how
to
do
that
and
they
recover.
Maybe
also
some
of
us
a
topic
like
detail,
creativity,
metrics
and
constrain
part
computation.
How
do
these
advances
stuff?
Our
work
is
more
focused
on
the
under
and
a
specific
use
case,
which
is
multi-domain
no
tiene.
We
work
on
that
and
we
want
to
show
how
you
can,
in
a
multimedia
network,
configure
services
and
to
enter
maybe
some
items
like
like
the
tekken,
TV,
dramatics
or
constraints,
but
computation.
We
don't
go
into
that
details.
E
We
go
more
on
details
on
how
the
different
domains
are
coordinated,
so
there
is,
of
course
there
are
different
objectives.
There
is
a
some
overlapping
and
the
idea
is
that
the
authors
of
the
two
drafts
work
together
as
already
as
already
ran
and
trying
to
avoid
the
inconsistency,
some
duplication.
It
may
be
unavoidable,
especially
on
the
JSON
code,
but
we
will
make
sure
that
there
is
no
inconsistency.
That's
the
most
important
thing
and
people
may
be
interested
in
two
different
approaches,
so
it's
good
to
have
both.
E
So
that's
the
proposal
from
the
auto
shop
that
you
documents
them.
The
second
open
issue
is
what
to
do
about
our
worker.
So
do
we
need
to
coordinate
or
communicate
with
other
projects
like
of
a
config
or
odom
t,
IP
and
any
affair
I.
Think
again,
we
forgot
one
F
as
well,
but
okay
I
see
there
are
other
people
and
we
want
to
see
whether
we
have
to
work
together
and
make
sure
that
the
use
cases
are
covered
and
I.
B
E
E
Okay,
thank
you
good
good
input.
The
other
open
issue
is
we
got
some
input
about
the
multi-layer
city
architecture.
It
seems
that
when
you
have
any
our
key
key
but
different
here,
key
between
underlying
and
lying
technologies
and
some
information
may
not
be
available
to
the
top
level.
Mvs
see
we
are
some
discussion,
but
we
have
not
finished
analyzed.
That
one
doubt
is
whether
this
isn't
an
issue
that
applies
only
to
packet,
an
optical
multi-layer
or
is
a
general
applicable,
for
example,
to
Ooty
and
layer
0
layer
1.
E
So
we
are
trying
to
understand
because
the
main
your
issue
is
the
fact
that
the
domain
boundaries
between
IP
and
optical
do
not
match.
So
you
may
have
a
different
structure
hierarchy
and
the
ghast
curve
to
coordinated.
You
may
not
have
enough
information
if
you
have
struck
too
much
and
that
so
we
are
still
analyzing
to
validate
a
concern.
If
there
is
a
solution
and
to
describe
it
and
adapt
is
whether
it
is
generic
applicable
to
our
says
or
not,
we
still
don't
know
we're
still
working
on
that.
E
We
have
some
discussion
on
the
client
services,
so
the
the
big
issue
is
that
the
eternal
it
creates
a
tunnel
between
the
end
nodes,
but
we
need
to
configure
how
they
assess
a
fee.
For
example,
it
ran,
says
traffic
is
classified
and
is
map
it
into
the
T
tunnel
and
we
are
working
as
subjects
to
use
the
motors
that
will
be
presented
by
and
later
in
the
agenda.
E
But
ok,
that's
something
we
have
to
analyze
in
the
next
phase
and
that
we
have
some
minor
detail
in
technical
discussion
like
how
the
I
to
RS
identifiers
and
identifiers
match
together,
and
somebody
brought
it
the
idea
to
think
about
also
what
happens
when
you
have
audio
CN
in
the
network.
So
we
have
to
think
about
that
yeah,
ok.
So
next
steps
is
to
progress
to
address
in
the
opera
technical
issue
to
integrate
edge
as
an
example
and
provide
more
it
as
an
example.
We
have
a
w.
E
B
Okay,
so
regarding
the
liaison
well,
the
ATF
as
a
formal
reason,
relationship
with
the
some
of
the
bodies
that
that
you've
listed
I,
don't
see
any
issue
in
preparing
a
liaison
and
sending
it
sending
it
out
mostly
now
that
the
draft
is
a
working
group
document.
So
if
you
want
to
try
to
propose
attacks
on
the
mailing
list,
that
we
can
discuss
it
and
and
send
it,
we
will
then
try
to
understand
who
to
send
it.
F
F
Secondly,
we
have
the
simplified
some
of
the
names
of
the
data
nodes
where
we
have
removed
a
duplication
of
the
group
or
container
name
we'll
see
in
the
data
node
names.
And
finally,
we
have
added
a
couple
of
examples
at
the
end
of
the
the
draft
to
explain
how
to
instantiate
two
typical
configurations
in
the
radio
link
domain,
one
configuration
called
want:
R
0.
That
means
that
we
have
one
radiating
terminal
containing
one
carrier,
termination
interface
and
the
second
one
is
a
bonded
configuration
where
two
carrier
termination
interfaces
are
included
in
one
radiating
terminal.
F
This
is
the
example
of
showing
the
1+0
configuration,
so
we
use
a
picture
or
a
figure
to
illustrate
the
configuration
as
such,
and
this
figure
is
showing
both
ends
of
a
radio
link
which
is
terminated
by
the
radio
link,
termination
or
terminal,
and
then
in
this
example,
it
contains
one
carrier,
termination
and
the
actual
instantiation
is
done
shown
for
the
NIR
and
one
of
the
ends
of
of
this
radio
link.
So
here
we
show
one
instantiation
of
the
interface
of
type
radio
link
terminal
and
the
Associated
interface
of
type
II
carry
termination
and
way
forward.
F
We
believe
that
the
model
definition
is
complete
and
it
has
been
stable
for
some
time.
We
have
one
comment,
though,
that
I
would
like
to
get
your
important
input
on,
and
that
is
a
suggestion
from
Tom
to
break
out
the
enumerations
or
the
type
definitions
and
put
that
into
a
separate
module
and
I
would
like
to
have
your
input
on
that.
If
that's
the
way
to
do
it
or
if
we
should
keep
it
within
the
same
single
module
module,
otherwise,
we
would
like
to
ask
for
a
work
group
by
lost
call
again.
Thank
you.
G
H
Tom
parent
good
morning-
yes,
it's
just
based
on
experience,
particularly
with
bibs
and
Teressa
extent,
with
yang
that
what
starts
off
as
one
piece
then
turns
into
two
separate
pieces
with
two
different
life
cycles,
and
so
looking
at
the
long
long
list
of
cram
in
particular
I,
don't
know,
I'm
sure
you
know
much
better
than
I
whether
that
list
is
likely
to
change
or
not,
and
if
there
were
new
ones
coming
along
6400
raise
to
five
sixes
and
so
on.
Then
it
would
make
sense
to
break
out
that
list.
H
If
you
look
back,
you'll
see
that
it's
quite
commonly
been
done
with
mid
modules,
and
it's
also
been
done
with
things
like
interfaces
interface,
types
where
the
interface
types
been
separated
out,
because
the
expectation
is
over
the
next
few
years.
The
lifecycle
of
interface
types
will
be
different
to
the
lifecycle
of
the
interface
yang
module
and
a
number
of
examples
of
that
already
systems
cause
it
as
well.
So
it's
a
rather
belated
thought
means
quite
a
bit
of
work,
theaters
and
parade.
H
F
B
H
That's
what
they
do
with
the
interfaces
I
mean
and
there's
an
ultimate
separation.
Well,
in
the
case,
the
mid
modules,
quite
a
lot
of
the
you
numeration
to
put
under
the
control
of
IANA
and
put
under
expert
review,
and
so
you
didn't
even
have
to
cycle
an
RFC
in
order
to
add
new
interface
types
to
the
list
of
interfaces.
In
this
case
we
would
be
to
the
list
of
modulation
techniques,
and
so
the
ultimate
would
be
given
under
an
yarn
or
control
with
expert
review.
H
The
most
tightly
coupled
is
what
we
got
at
the
moment
with
a
single
module.
So
if
either
part
of
that
information
changes,
we
have
to
recycle
the
RFC
or
put
in
something
that
the
dog
mends
hit
or
whatever
so
there's
a
spectrum
of
possibilities
and
to
rehang
modules
within
the
one.
Rfc
is
the
simplest
separation,
but
it
as
I
say
it
all
depends
on
on
what
you
think
is
gonna
happen
to
that
list.
H
G
Amy
again,
I
have
another
questions.
When
you
mention
about
the
sir
case,
it
was,
the
new
in
nations
won't
be
changing
a
few
years.
I
would
like
to
ask
how
many
is
the
few
years,
maybe
in
three
or
five
years
or
longer
than
that,
so
we
should
based
on
what
kind
of
numbers
we
should
make.
This
decision.
H
Don't
batch
again
I'm
saying
that
I
don't
know
what
the
likely
lifecycle
of
that
list
is
and
I
think
your
expertise
in
this
room
is
far
greater
than
mine.
So
if
you
think
that
list
has
been
stable
for
10
years
never
going
to
change,
then
there's
no
point
in
doing
anything,
but
if
you
think
a
new
ones
going
to
come
down
the
road
and
the
usually
come
down
the
road.
G
Amy
again,
I
agree
with
Yunus,
maybe
10
years-
that's
no.
We
won't.
We
are
not
able
to
see
that,
but
I
could
say.
Maybe
three
years
you
will
keep
on
changes
and
I
still
preferred
this
later,
but
we
will
keep
the
more
user
within
one
draft
or
so
it's
easy,
not
we
could
update
and
keep
them
because
they
are
so
record
greater
with
each
other.
So
that's
my
suggestion.
B
So
I'll
tell
you
what
we
have
not
yet
discussed
about
this,
so
it's
just
my
opinion,
not
ours.
This
is
so.
We've
been
working
on
young
models
for
a
while
now
and
I
would
like
to
have
something
published,
and
this
is
the
only
module
that
has
no
dependencies
on
ongoing
drafts.
All
the
tunnel
topology
models
depend
on
publication
of
of
other
documents.
This
one
is
based
on
an
RFC,
so
this
is
the
one
that
we
can.
B
We
can
progress
if
you
feel
that
there
is
a
number
of
parameter,
a
portion
of
the
module
that
is
stable
and
isn't
not
going
to
change.
We
can
split
the
document
and
progress
just
that
one
I
would
say
to
go
this
way.
If
that
amount
of
parameters
is
the
something
they
can,
you
can
be
implemented.
It
is
something
that
the
standalone
doesn't
make.
Much
sense
is
pointless
to
progress,
just
a
subset
of
parameters
that
is
useless
in
the
end.
If.
B
B
B
F
Way,
I
don't
believe
that
it's
possible
to
split
it
into
two
parts
where
one
part
is
stable
and
the
other
one
is
more
likely
to
change
the
parameters
or
the
inaugurations.
We
talked
about
or
or
a
key
to
the
model,
so
we
cannot
break
out
any
of
them
and
say
that
we
we
take
care
of
them
later
on.
They
are
core
for
the
modelers
as
it
is.
F
B
It
seems
to
be
the
good
basis
to
address
a
Tom's
Tom's
concern
in
the
sense
that
the
modular
is
a
quite
of
future
proof
if
a
quarter
to
understand
what
you're
saying
so,
this
would
make
me
think
that
keeping
things
together
shouldn't
be
a
problem.
If,
with
a
single,
a
short
document,
you
can
augment
it
easily.
G
And
Amy
again
so
I
think,
even
if
we
split
into
two
modules,
I,
don't
think
that's
a
significant
to
change,
because
it's
more
like
a
a
structural
rearrange.
The
definition
with
real
capes
are
then
the
same.
The
technique.
We
don't
change
any
technical
parts
so
but
num
an
hour
will
be
fun
with
either
way.
If
there's
more
suggestions
to
keep
them
together
and
I
personally,
like
to
progress,
that's
more
important.
H
Tone
Pech
most
of
my
life
I
seemed
to
be
encountering
people
who
come
out
to
me
and
say
Tom.
We
wish
we
didn't
to
you
five
years
ago
done
what
you
suggested.
I
have
the
art
of
seeing
the
right
answer
being
unable
to
persuade
people.
It
is
the
right
answer,
so
my
I
are
would
say,
spit
out
that
list
of
identities
into
a
separate
young
one
you'll
keep
it
in
the
RFC
but
spit
it
in
into
a
separate
yang
module.
That's
that's
what
I
would
do
or
do
to
do.
G
G
So
this
microwave
technology
to
after
is
argument
and
t-top
knowledge
models,
which
is
also
argument,
is
a
network
technology
model.
The
use
case
of
the
microwave
technology
were
thinking
about
the
following
two
cans.
The
first
one
is
for
resource
management
and,
for
example,
you
could
exposures
or
radio
link
frequency
to
the
topology
and
then
enables
you
if
you
want
to
do
our
rate
planning
and
the
frequency,
for
example,
to
decrease
in
a
various
level
of
each
radio
link.
So
this
could
be
one
possible
use
case.
G
Another
path,
important
the
use
cases
for
past
computation
as
it's
been
introduced
or
for
several
times.
That
is
this
radio
link
will
have
two
feature
to
change
its
span
device.
So
it
is
important
to
understand.
What's
the
current
bandwidth
of
the
radio
link,
and
so
we
included
this
information
into
the
microwave
topology
model
and
also
in
our
case
that
we
will
use
the
availability
to
describe
the
link
characteristics.
So
we
will
also
report
through
the
topology
model,
and
then
this
is
the
topology
young
tree.
It's
quite
simple.
G
In
the
first
version,
we
introduced
a
new
network
type,
which
is
microwave
technology,
and
then
under
that,
we
argument
are
teaming
attributes
which
includes
a
link
frequency
channel
separation,
or
you
could
call
it
a
channel
bandwidth.
We
use
channel
separation
in
our
case
and
then
also
have
a
nominal
bandwidth
and
currently
penguins,
and
then
the
link
availability.
G
So
well,
I
would
like
to
explain
how
this
model
is
related,
always
the
microwave,
the
interface
model.
The
one
neurons
have
just
introduced
I
list.
This
two
models
under
the
architecture
by
using
architecture
of
France
I,
see
Jian.
So
in
our
step,
our
understanding
that
the
topology
model
is
expected
to
use
it
as
a
networks-
terrorists
young
model,
so
it
should
be
a
user
between
the
mtsc
and
PNC
our
while
the
interface
young
model,
S
device
defined
for
the
physical
layer
configuration.
G
So
it's
a
kind
of
differ
device
configuration
module
which
is
supposed
to
be
used
between
the
PNC
and
the
network
elements.
So
at
the
level
of
the
PNC,
we
are
expecting
that
PSA
should
convert
the
information
from
the
top
knowledge
model
into
the
interface
model.
For
example,
the
link
frequency
from
the
top
knowledge
model
should
map
to
the
TX
frequency
into
the
carrier.
Termination
of
the
interface
model.
So
there's
some
mapping
between
the
two,
and
it
is
also
explained
that
in
our
say,
80
199.
G
We
have
different
layers
of
the
models
and
it
is
possible
to
reduce
the
low
layer
young
models
by
the
how
high
earlier
modules,
but
we
still
need
to
explore
more
how
exactly
as
this
map
enum
could
be
achieved
and
then
in
the
drop-down
appendix
we
add
to
JSON
example,
because
we
stored
that
the
JSON
coder
will
be
quite
helpful
to
understand
how
to
use
this
young
models.
The
first
example
is
about
the
single
of
microwave
link,
which
is
the
simple
case,
and
here
we
demonstrated
that
way.
G
The
current
signal
will
be,
isn't
it
so
it's
kind
of
a
isn't
it
over
microwave
link
and
we'll
use
the
modulator
technology.
The
concept
from
the
Tito
biology
so
advert
in
the
t,
Ethernet
table
which
model
you
will
say,
there's
a
isn't
it
t
links
and
then
this
T
links
will
have
a
underlay
containers
which
is
supported
either
termination
and
the
Eternals
in
the
microwave
topology,
and
then
in
the
lower
layers,
the
Tito
biology
of
microwave.
You
receives
a
microwave
kernels
and
the
microwave
links
and
under
the
microwave
links
you
can
say:
what's
the
young?
G
What's
the
dead,
anode
definition
we
just
introduced
in
in
for
most
nights
and
the
second,
the
second
case
will
be
a
little
bit
complex
than
the
first
one,
which
is
the
crime
signal,
will
still
be
the
Ethernet
service
and
then
the
second
we
will
use
to
microwave
think
we
could
two
plus
zero
to
transporter
to
Ethernet
services.
So
we
have
a
several
discussion,
always
some
of
the
tree
topology
waters
regarding
how
to
model
with
this
to
microwave
bundle
links
here
it
is
showed
that
or
we
use
the
bounded
boundary
case
in
the
Tito
biology.
G
So
you
can
say
that
doesn't
the
Ethernet
technology
will
be
same.
So
I
didn't
repeat
friends
of
almost
nice
and
this
Roger,
you
could
say
at
the
microwave
technology
we
could
have
the
two
component
links
but
there's
different
ideas,
whether
this
two-component
mixture
be
shown
that
ism
tea
technology
of
you,
because
there's
arguments
to
say
or
whether
this
microwave
links
Phoenix,
but
my
personal
questions-
that
if
we
don't
show
that
in
the
microwave
technology,
then
well,
we
can
get.
This
Bing
contributes
for
this.
Each
individual
component
needs.
G
So
this
is
a
little
bit
unclear
to
me
right
now
and
then
the
next
one
last
page
is
talking
about
the
next
steps.
Then
the
first
try
plan
is
that
we
were
updated.
Draft
again
will
receive
some
offline
comments
to
complete
the
JSON
example
in
the
appendix,
and
then
it
is
handed
to
in
ECM
wtl
to
have
a
microwave,
SEO
podcast,
and
this
microwave
technology
model
will
be
verified
in
that
practiced.
G
So
we
are
expecting
more
update
according
to
the
discussion
and
and
finally,
we
would
like
to
propose
to
use
this
draft
tools
as
a
starting
point
to
defined
as
a
microwave
technology
young
module.
So
we
would
like
to
ask
for
working
group
adoption
and
finally,
in
this
video
we
will
all
have
a
side
discussion
and,
if
you're
interested
you're
working
to
join
us.
Thank
you.
J
J
G
A
G
G
K
I
A
I
Here's
a
update
to
this
wrapped
what
happened
since
NASA
my
Ida
meeting,
so
we
update
a
new
version
version
5
and
add
a
new
section
to
this
version.
It's
many
about
open
issues
and
and,
as
a
is
a
lot
said,
this
section
is
not
into
intend
to
be
removed
in
a1
it
published,
and
also
it's
just
as
a
trigger
to
to
check
more
discussion
about
whether
the
issue
about
our
sweetie
station
folate
layer,
which
one
is
better
which
one's
better
and
which
wise
should
be
adopted
by
this
work
and
also
in
this
update.
I
So
here's
about
this
side
is
up
is
a
summary
about
the
open
issue.
Now
this
many
about
the
flexi
control
plan,
there's
some
question
about
the
relationship
between
module
layer
and
the,
and
this
has
B
TV
stations,
whether
actually,
currently
we
at
least
four
options
here,
maybe
you
can
go
yeah.
This
is
the
first
one
option,
one
for
this
one
there's
only
one
station
established
it
can
handle
all
layers.
I
Control,
for
example,
can
just
use
one
position
to
set
up
Mexico,
flexi
current
or
even
to
set
up
our
space
over
this
track
ceilings,
and
the
second
option
is
that
is
just
under
country
outlet
direction.
Just
just
like
for
each
layer
we
can
use
a
dedicate
our
decision.
For
example,
the
flexicord
can
use
a
dedicated
session
receipt
client
can
use
a
dedicated
room,
and
so
this
way
you
can
each
session
can
just
only
behind
each
on
necessary
information
and
and
it's
extremely
necessary
information.
Don't
matter
don't
think,
come.
B
I
Can
you
speak
a
little
bit
louder?
Please,
okay,
Thanks,
maybe
slant
direction
yeah.
This
is
a
option,
two
option
straight.
It's
just
just
like
come
it's
a
mix
of
the
option.
One
option
two
in
this
in
this
option
we
can
just
use
one
our
decision,
just
for
only
for
the
example
phoneme
for
the
fact
see
the
related
super
layers,
for
example,
excellent,
the
first
probe
just
use
one
RGB
decision
and
for
other
layer
control
can
use
another
delicate
art
decision,
so
option
for
is
about.
I
I
B
Well,
identifying
the
pros
and
cons
could
could
be
helpful
to
to
make
a
decision.
Actually,
I
would
be
in
favor
of
number
three
to
do
everything
that
is
flexi
together
and
everything
that
is
known,
flexi
in
a
different
search
such
the
one.
You
called
12
targets
exactly,
but
I
will
need
it
well
understand,
better
pros
and
cons.
L
The
double
or
Nokia
at
the
previous
IETF
meeting
when
this
draft
was
presented,
we
actually
provided
some
comments
also
on
the
mailing
list
after
the
meeting
I
think
in
the
replies
to
that
email,
I
understood
that
the
concerns
or
comments
that
we
made
have
been
confirmed
and
now
looking
at
the
latest
revision
of
distract
I,
don't
see
that
these
comments
have
been
incorporated
into
the
document.
So
what
are
the
next
steps
regarding
these
comments?.
I
L
B
L
No,
it
was
confirmed
that
the
concerns
we
erased
are
valid
concerns,
but
they
were
not
taken
into
account
on
the
latest.
Revision
of
the
document
was
produced.
So,
as
we
said,
the
update
the
latest
update,
that's
presented
here
is
just
providing
a
new
section
with
open
issues
right.
So
could
you
please
revive
the
discussion?
Yes,
I
can.
Thank
you.
Thank
you.
A
I
A
I
M
M
M
This
topic,
it
is
a
party
has
come
true
of
beyond
100
Gig,
okay
network,
it's
about
a
son
for
a
mocha
token,
okay,
a
second
started
to
tell
what
happened
during
a
society
of
meeting
and
the
during
last
IDF
media
to
face
discussing
happy
during
happy
hour
month
also
than
a
contributor
of
the
traffic,
that's
based
on
the
to
tactical
scenario,
dedicated
in
appendix
of
0
to
7
or
none
and
the
discussion.
Many
on
the
challenges
to
come.
M
M
Take
a
look
at
a
scenario
force
the
force
of
scenario
and
it
starts
the
the
finger
is
copy,
the
from
they
put
several
none
and
rewrite,
but
it's
not
different.
This
is
in
this
scenario.
It
deploys
out
using
all
audios
in
design
between
tool
and
parts
connecting
to
layer
one
earlier.
Only
a
0tu
course
connects
within
one
optical
transport
network
102
using
is
actually
carried
by
one
okay,
8000
tae.
M
That
is
the
optical
path.
So,
after
the
discussion
we
sink,
we
also
saying
that
out,
you
see
a
note
you
see,
ending
can
be
automatically
established
aft
altogether
ways.
Does
that
help
out
over
the
optical
path.
This
is
the
FASTA
scenario,
and
the
second
scenario
is
a
little
complicated
in
the
scenario
1
and
an
audio
saying
and
actually
supported
a
pass
rate.
M
They
find
out
he'll,
say
audio
cues
in
desam
segments,
which
I
intend
carried
by
the
optical
party
in
this
scenario,
discussing
with
singer
in
a
scenario
the
audience
will
be
established
automatically
after
together
with
set
of
the
optical
paths.
While
we
sing
has
us
there
some
doubts
about
how
do
you
singing
the
instability
in
the
Senate.
M
Especially,
what
I'm
talking
about
is
a
transponder
point:
how
to
set
harbor
and
to
end
the
OTS,
a
link,
of
course,
a
transponder
connected
to
out
here
and
course
connects.
So
this
is
the
second
scenario.
That's
based
on
these
two
scenario
and
after
that
discussing
we
can
work
from
cholangitis
and
made
some
uncertainty
about
asset
Howell.
What
you're
sending
we
think
has
a
it's
still
exists,
and
this
uncertainty
may
have
a
relationship
with
the
progress
at
UT.
So
it's
much
the
another
career
I
was
thinking
and
then
also
under
some
contribute.
M
We
just
decided
that
the
scope
of
this
draft
currently
may
be
wish
to
the
mainly
focus
on
how
to
set
up
audio
ke
audio
for
access
P,
/
audio
settings.
We
also
give
some
evaluation
to
the
current
attention
of
GNP
as
a
single
owner
and
the
Jamieson
writing
defining.
Obviously,
something
was
a
Dallas
fc7
729
after
discussing
was
saying
that
the
signaling
and
the
writing
mechanism,
the
findings
is
I've.
Seen
recently,
can
be,
it
can
be
reused.
M
M
Oh
dear
fall
unto
audio
Satan,
as
in
the
in
this
case,
one
audio
Satan
has
255
key
gets
lost
and
20
of
them
are
unlocking
that
what
you
fall
and
about
next
steps,
I
think
we
should
invite
ball,
reviewing
a
comment
and
then
maybe
I
think
I
can
purple
to
request
the
father
working
purple
Dobson
the
reason
that
I
want
to
request
for
working
for
adult
size
because
to
reading
the
fossilized
I
think
I
talked
to
contributor.
Oh
no
I
got
a
feedback,
a
phone
yeah,
but
not
all
of
them.
M
C
M
From
a
on
a
face-to-face
and
the
feedback,
I
got
from
them
asking
it's
about
him,
they
some
of
them.
That's
Italian,
listen
hit
two
cracks,
so
they
sound,
there's
a
feedback
form
then
I
think
maybe
it's
time
to
request
for
what
can
go
about
saying,
I
think
it
would
be
a
good
start
upon.
Okay,
thank
you.
Humming.
N
N
M
N
A
M
A
M
B
O
I'm
a
little
confused
about
looking
at
agenda
and
and
the
you
know,
draft
itself,
and,
and
now
this
discussion
is
even
more
confusing
so
in
in
the
in
the
agenda.
It
lists
essentially
two
titles
and
I
could
figure
that
out
because
it
looks
like
there
was
a
framework
and
a
solution
and
then
in
the
draft
itself.
The
major
title
is
the
first
of
those
two
titles
and
then
the
title
at
the
top
of
each
page
is
a
BGP,
erm,
I'm,
sorry,
extensions,
the
G,
but
whatever
it
is
100
extensions.
O
M
Want
to
give
some
explanation,
saying
I
think
a
solution
is
needed,
but
we
don't
need
to.
I
dint
sorry
to
do
some
acting
job
to
current
the
traffic
week.
I
just
want
to
give
some
very
recent,
give
some
analysis
s.
The
current
current
to
the
mechanism
defining
is
signaling.
Traffic
can
be
reused.
It
should
it's
because
it's
because
of
the
emergence
of
a
some
new
stuff.
B
Q
Q
Q
So
this
is
based
on
RFC
76
98
the
framework
and
requirement
for
the
Flex
grid.
Dwm
networks,
this
basically
arguments
t
tunnel
model,
so
major
changes
from
the
previous
version
is
basically
we
separated
out
from
topology
model
from
tunnel
model.
It
is
to
be
a
one
model
and
a
link
channel
is
now
reusing,
LSP
from
T
a
tunnel
model
as
opposed
to
private
extension
and
NN
nmda
compliant.
Q
So
this
is
a
basically
a
young
model
that
we
argument
from
Thea
tunnel
model.
As
you
see
here
and
I
believe
order,
layer,
1,
layer,
0
young
models
have
been
adopted,
except
for
this
one-
and
this
is
probably
the
last
one
to
be
adopted
and
move
on
after
based
eternal
model,
you
know
has
been
stabilized
so
I
think
it
may
be
time
to
adopt
this
work.
B
It
was
mostly
question
a
matter
of
time
that,
because
we
have,
we
have
pulled
I,
don't
remember
four
or
five
documents
in
a
row.
So
it's
not
it's
not
just
that.
These
one
had
something
wrong.
It
was
just
a
backlog
of
full
of
documents
to
be
adopted,
but
let
let's
try
two
to
see
if
what
the
working
group
thinks
so
how
many
people
have
read
this
document
quite
a
lot.
How
many
people
think
this
is
a
good
starting
point
for
a
working
group
document.
B
H
H
But
the
rest
of
the
information
around
it
is
is
lacking
and
my
comments
have
made,
which
unisys
very
happily
picked
up,
or
mostly
along
that
line,
and
so
what
I'm
looking
at
it
is
a
young
model
and
looking
at
the
guidelines
that
have
recently
been
republished
and
seeing
how
well
does
it
conform
with
guidelines?
And
so
the
reason
I
didn't
raise
my
hand
to
your
second
question
is
the
lack
of
performance
of
guidelines.
H
Maybe
the
author's
very
happy
to
take
all
that
on
board
and
fix
it.
But
I
haven't
yet
got
to
the
stage
of
actually
posting
a
comment
on
the
list
and
seeing
what
was
once
I
get
to
comments
of
that
nature
about
you
know
the
copyright
being
wrong
with
lack
of
references
there
being
references
embedded
in
one
place,
the
home
after
things
in
in
the
guidelines
reproducing
a
young
model
and
it's
a
conformist
who's.
It's
my
concern
rather
than
the
technical
content,
which
I
suspect
will
be
of
the
interest
to
more
of
the
audience
here.
R
C
R
Q
Was
discussed
previously
and
then
for
topology
model,
you
know
not
to
mention
this
tunnel
model,
so
I
think
working
group
chairs
suggested
just
stay
with
W,
Sun
and
flats
great
separate
photo
Palooza
model,
so
we
just
call
out
the
same
pattern:
I
attack.
You
know
when
your
argument.
Actually
it
doesn't
make
much
difference
at
the
end,
yeah,
okay,
yeah.
So
it's
more
logistic
issue
and
I.
Think
working
group
has
already
made
made
a
decision
to
go
this
way.
So
technically
it
doesn't
make
much
difference,
but
you
know
it's
not.
Q
R
No
I
just
say
if
you
separate
tunnel
proposal
that
makes
perfect
sense
right,
but
if
you,
for
example,
use
to
augment
ation
separate
augmentations
from
the
base
station
or
model
one
for
lambdas
and
another
for
flexure
grid,
then
obviously
would
have
to
repeat
many
cemented
matrix
right
in
both
like,
for
example,
to
do
with
optical
impairments.
So.
Q
Q
So
this
document
of
the
Sun
and
in
terms
of
times
comment
conformance
I'm,
not
sure
what
was
the
real
comment?
I'm.
Sorry.
What
do
you
mean
by
conformance
document
is
like
in
conformance
it
said?
Technically,
it's
okay,
but
document
needs
to
be
more
conformance.
Oh
I,
don't
understand
what
conformance
means
so
that
I
can
pass
down
to
the
others.
B
B
C
Okay,
good
morning,
everyone,
this
is
hamer
from
Hebei,
I'm
going
to
introduce
the
updating
from
three
different
documents,
including
the
client
signal,
young
model,
client,
apology,
yamamoto
and
the
client
on
your
model.
So
we
have
this
three
models:
application
applied
in
different
scenarios,
and
this
is
the
second
work.
There
are
two
version
we
are
having,
so
we
actually
did
receive
some
offline
comments
after
we
upload
the
document
is
this
time
and
before
my
introduction
to
the
updated
details,
I
would
like
to
firstly
answer
two
typical
questions.
C
C
Ok
use
a
figure
in
r3,
8080
309,
and
what
we
can
see
is
layer.
2
sm
is
a
kind
of
customer
service
model
which
is
referring
to
the
interface
a
in
notation,
a
between
the
customer
and
the
service
Orchestrator
so,
and
the
models
proposed
in
this
draft.
The
client
model,
which
is
mainly
the
Ethernet
model,
is
a
network
configuration
model
which
can
be
directly
used
between
the
controllers
for
Ethernet
configuration.
B
C
Actually,
well,
there
are
something
certain
something
uncertain:
the
second
years.
The
model
in
this
draft
can
be
confident
be
considered
as
a
network
configuration
model.
This
is
a
physician
and
second
considering
the
service
delivery
model.
We
said
I,
don't
think
we
still
have
a
consensus
on
whether
it
belongs
to
this,
and
whether
the
air
to
SME
is
also
the
service
delivery
model.
We
need
to
have
I
agree.
C
I
think
it
will
definitely
make
sense
if
we
can
really
figure
out
how
this
model
work
together
with
the
layer,
two
service
model,
of
course,
and
the
second
question.
Okay,
is
actually
a
follow
up
path.
With
the
previous
question
of
how
this
model
is
applied
because
of
we
have
three
graphs,
including
four
different
young
files,
then
how
it
would
be
applied
in
the
real
network
configuration
so
here
we
propose
actually
two
separate
different
application
scenarios.
C
The
first
one
is
Ethernet,
only
we
consider
Ethernet
as
a
transport
network,
and
we
do
not
consider
any
blind
in
this
scenario.
That
means
we
only
have
a
flat
layer
of
network
that
is
composed
by
Ethernet
nodes,
so
consider
it.
It
has
a
single
layer
technology.
Then
it
would
only
be
necessary
to
to
set
have
the
ethernet
'knows
using
the
instant
nano
models,
and
this
should
be
based
on
the
is
new
topologies,
that
connected
from
the
controller.
C
Paese
is
an
anthropology
model,
so
this
is
respectfully
in
draft
number
three
and
draft
number
two
and
the
second
scenario
would
be
a
kind
of
application
of
Ethernet
as
a
client
of
the
transport.
So
in
this
kind
of
scenario,
there
isn't
a
need
to
work
closely
with
out
here
now
then
there
may
be
a
single
box
that
integrates
both
is
an
a-10,
the
ODN
notes.
R
We
have
this
discussion
conscious
about
the
service
mapping
thing
right,
so
service
mapping
actually
occurs
in
the
same
way.
So
we
have
a
service,
for
example,
Ethernet,
service
or
IP
service
like
layer,
3,
VPN
service
right
and
then
this
is
what
client
sees
that
and
then
you
have
basically
the
network
operator,
the
provider
which
met
the
service
in
this
layer
into
infrastructure.
R
This
is
one
thing,
and
then
there
is
a
totally
different
thing
of,
for
example,
a
client
service
being
in
one
layer
and
infrastructure
in
a
different
layer
like,
for
example,
say
Ethernet
service
and
ot
internals
right
this.
This
actually
would
G
805
calls
adaptation
its
internally
a
relationship,
and
this
could
be
caught
by
the
topology
model
right
because
we
have
all
the
semantics
basically
saying
that
particular
tunnel
termination
point
can
adopt
certain
client
links,
so
so
this
need
to
be
very
clearly
separated.
R
C
B
R
Well,
for
one
reason
is
that,
for
example,
there
could
be
switching
in
this
very
layer,
I
thought
like,
for
example,
Ethernet
services
could
be
mapped
on
on
the
tunnel
that
could
be
switched,
but
not
me,
like
you
know,
villain
IDs
or
it
could
be
a
switch
by
say
s
tax
right.
This
is
one
thing,
but
but
the
other
thing
is
that
the
adaptation,
it's
a
totally
different
animal
right.
C
Okay,
we
are
here
yeah
and
actually
well.
Originally,
this
drafter
is
named
as
ulti
inclined
the
signal
young,
so
Ethernet
is
definitely
one
of
the
kind
of
signal
types
of
faulty
an
but
according
to
the
ODN
control,
plane
draft
may
be
1762.
There
are
also
other
GP
there's
two
different
klein,
the
signal
types,
a
including
those
kind
of
flew
SDH,
or
something
like
that.
C
C
We
also
as
a
support
to
reporting
the
wheel
and
classification
operations
supported
by
access
links,
and
we
also
change
the
types
of
kind
kind
facing
parameters
from
empty
to
bullying,
as
it
would
be
clear
to
understand
how
to
use
it,
and
we
also
update
some
text
so
for
tunnel
model.
There
is
no
much
update
according
to
the
model
itself,
we
basically
make
it
an
empty
compliance
and
update
the
text.
C
So
currently
we
hope
we
can
at
least
make
the
tunnel
server
generalized
and
so
not
only
focus
on
T
end,
but
we
also
find
it
is
difficulty
to
to
make
the
client
signal
general
arise
because
the
ethernet
a
is
too
much
different
with
other
kind
of
client
signals,
and
we
also
received
some
comments
offline
from
some
operators
saying
that
they
only
or
let
me
say
at
least
they
mainly
focus
on
Ethernet
models.
So
we
would
like
to
extract
the
Ethernet
part
of
this
works
and
move
separately
with
the
other
kind
of
client
signals.
C
L
C
C
What
is
the
client
and
node
kind
link
that
may
be
applicable
to
be
found
in
this
genus
or
TP
generic
models
so
because
this
work
is
also
automating,
the
TP
models?
So
so
we
we
think
those
kind
of
the
common
area
is
already
covered
by
heat
for
health
models,
and
this
we
just
make
is
net
model
and
other
kind
of
models
augmenting
to
that
he
directly.
S
Hi,
it's
Glenn
Parsons,
so
I
guess
I
don't
understand.
I'll
start
with.
Maybe
a
clarification
of
this
is
OTN
yang,
OTN,
being
itu-t
g,
709,
yang,
I
presume
and
I'd
like
to
understand
why
we're
working
or
you're
proposing
network
management
data
models
here
in
C
camp,
as
opposed
to
an
I
to
t
study
group
15,
question
14,
which
is
working
on
network
management,
information
models
and
data
models
and
such
so.
Maybe
you
could
help
me
understand
that
first
and
then
I
can
make
detailed
comments.
S
S
S
C
Maybe
you
could
help
me
understand,
I,
think
we
need
to
separate
your
questions
one
by
one
so
consider
okay,
this
worker
is
specify
the
mode
or
how
to
configure
the
ethernet
service.
Given
there
is
a
transport
network,
that's
carrying
the
Ethernet
service
and
basic
idea
is
to
configure
the
Ethernet
access
link
after
you
to
make
sure
that
the
Ethernet
service
Ethernet
technically,
is
correctly
configured
and
look
according
to
your
comments
on
other
progress.
S
Mf
is
defining
service
for
for
Ethernet
there's
three
levels:
it's
a
very
complex
life
cycle
service,
orchestration
model
with
multiple
types
of
service,
different
abstractions
from
business
relationship,
service
relationship,
network
element
relationship,
that's
the
M,
EF
and
then
I
Triple
E
is
working
on
the
detailed
pieces,
there's
liaisons
with
ITU
and
question
14
on
some
of
the
the
details
and
then
there's
the
L
to
SM
work
here,
which
is
in
a
different
group.
So
I'm
just
trying
to
piece
all
this
together
because
yeah
you.
S
G
Ami
actually
I
would
also
add
into
Glenn's
comments,
and
this
lab
aware
of
that
Olaf
is
also
have
an
Ethernet
of
fine
management
model.
So
I
agree
that
there
are
several
stills
are
defining.
This
looks
like
the
same
thing,
so
we
need
to
push
them
in
together
and
say:
what's
a
difference
and
to
me
I
think
I
also
look
into
the
ME
of
Ethernet
service
model.
I
think
that
Y
is
clear
because
it's
kind
of
a
very
high
level
use
at
the
customer
service
delivery
model
so
which
is
different
from
the
current
one.
G
E
Thank
You
Tallapoosa
from
away
I
would
like
to
help
as
well
I.
Think
if
you
look
at
this
picture,
what
I
mean
is
clearly
shown
that
we
have
the
layer,
2
SM,
which
is
applicable
between
the
customer
and
a
service
Orchestrator,
and
what
we
are
doing
is
now
is
working
on
the
interface
on
top
of
the
controller
on
that
interface.
E
We
can
use
that
to
create
if
you
want
to
create
an
Internet
service,
ring
it
from
one
eatin,
SS
s,
port.
What
other
is
transport
we
need
to
know
between
which
the
OT
on
TTP
we
need
to
set
up
the
tunnel
and
that's
the
internet,
a
lot
information
that
we
get
from
the
topology.
So
we
need
to
explore
to
expose
at
that
interface.
E
The
internet,
topology
SS
link
leads
inter
layer
lock,
the
TTP
of
the
OTN
and
all
these
attributes,
and
this
not
work,
is
not
going
to
be
done
anywhere
and
my
understanding
is
our
T.
Poly
model
is
more
able
to
1q
Bridge
management,
so
it's
more
apart.
The
device
configuration
model,
so
they
are
applicable
on
different
part
of
the
overall
contour
architecture.
Thank
you.
What.
B
R
Even
worse
can
I
also
would
like
to
answer.
You
know.
Various
ultimen
I
didn't
get
his
name,
but
the
thing
is
that
if
something
is
called
Ethernet
yon
model,
a
huge
number
of
different
things
could
be
named
by
that.
Okay
and
huge
different
of
aspects
could
be
also
considered
like,
for
example,
say
Mafeking
defined
I
want
to
have
say
appeal,
which
is
time
constraint.
It
should
not
go
beyond,
say
10
millisecond
latency
right,
but
how
you
can
actually
achieve
this.
That's
totally
different
problem
right.
R
And
then
there
should
be
a
third
type
of
model
which
basically
it's
a
device
specific
model
which
which
can
tell
each
device
on
the
edges
of
the
service,
how
you
map
the
services
onto
the
infrastructure
right,
that's
a
third
type
and
all
of
these
things
are
called
Ethernet
right
and
some
of
them
are
the
world.
In
idea.
R
Some
of
them
are
the
world
in
different
organizations
and
even
in
ITF,
some
of
them
have
to
do
with
lecturers
and
like
connectivity,
restrain
and
say
we
want
IDs
to
like
see
toxmap
in
and
stuff
like
that,
but
some
like
in
C
Company
earth.
This
has
a
lot
to
do
with
the
traffic
engineering,
particularly
and
also
what
we
contribute
to
the
community
as
how
this
infrastructure
could
be
mapped
on
the
services
which
are
seen
Network
wide.
B
C
Okay,
this
is
a
second
presentation
from
me,
but
our
totally
different
topic.
This
is
not
young.
This
is
talking
about
the
interworking
of
the
GNP
ours
control
and
the
centralized
controller
system.
So
this
has
been
the
second
presentation
last
time
we
did
this
in
Singapore
and
briefly
introduced
the
motivation
of
this
work,
so
things
are
now
becoming
different
after
the
appearance
of
the
controller
system.
Originally,
the
control
plane
is
fully
distributed
with
GMP
ours
protocols
that
define
the
ITF
C
temper
working
group.
C
K
C
Past
computation,
routing
and
start
and
and
so
on,
to
get
a
better
performance
and
their
understanding,
so
the
corresponding
output
from
the
centralized
controllers
may
have
the
ICT
and
framework
and
the
controller
hierarchies.
We
also
have
restaurants
that
consented
always
together
with
young
models
and
also
the
PC
protocols,
especially
for
past
computations.
C
So
the
changes
are
from
previous
version.
We
have
two
new
clusters
and
we
have
also
updating
the
scenarios
which
we
think
this
is
most
important
for
this
kind
of
informational
work,
that
this
kind
of
scenarios
are
requesting.
The
inter
work
between
the
centralized
controller
system
with
the
previous
distributed
control
plane.
So
the
scenarios
included
poverty,
collection
and
synchronization
multi
domain
layer,
service,
provisioning
and
the
controller
reliabilities
I
will
expand
in
the
future
slides
and
we
also
update
to
the
reference.
C
So
here
is
a
personal
scenario.
We
want
to
analysis
is
a
kind
of
interworking,
more
detailed,
because
this
is
the
most
fundamental
scenario
in
the
network
control.
So,
given
the
group
of
devices
composing
some
network-
and
it
is
now
controlled
by
a
single
controller-
and
there
may
be
a
PC
embedded
for
past
commutation
and
there's
some
other
of
the
control
functions
need
to
be
achieved
by
the
interface
between
the
controllers
and
the
network
elements.
But
given
this
kind
of
network
architecture,
we
are
trying
to
categorize
all
the
interface
in
the
networks
into
three
different
levels.
C
The
first
level
number
one
it's
between
the
neighbors.
We
call
this
temporarily
called
as
the
neighbour
level
interface
and
the
main
function
and
requirement
for
this
kind
of
interface
is
to
discover
the
neighbor
neighbor
and-
and
we
and
the
support
some
of
the
exchange
of
information
between
neighbors
to
understand
each
other,
and
the
second
would
be
are
still
between
the
network
elements.
But
it's
a
kind
of
domain
level
or
we
call
this
network
element
level.
So
even
for
those
kind
of
two
network
elements
is
not
directly
connecting
with
each
other.
C
The
informations
can
be
flooded
and
received
by
each
network
elements
in
domain,
so
typical
typical
protocol
would
be
OSPF
or
isis
as
seen
in
the
on
this
level,
and
the
third
type
of
the
interface
is
the
interface
that
connects
the
controller
with
the
network
elements.
So
this
is
URI
request,
an
interaction
between
the
controller
and
the
network
elements
and
the
typical
protocols
include
the
p7
that
comes
with
young
models.
So
around
will,
when
we
really
deploy
a
network.
C
The
topology
is
initially
is
initialized
and
reported
to
among
the
network
elements
and
between
the
network
and
the
element
and
controller.
So
while
our
mp4
interface,
type
100,
SPF
or
is,
is
for
interface
type,
2
and
P
Cybernet
comes
for
interface
type
3
and
when
there
is
an
update,
for
example,
we
add
one
node
to
the
existing
network.
Then
we
need
to
synchronize
the
information
to
all
the
other
network
elements
together
with
the
PCE,
together
with
a
controller
or
PC
level.
C
C
Show
how
the
different
protocols
is
applied
for
the
different
tasks
so
for
a
past
computation,
the
distributed
control
plan
will
need
to
use
OSPF
protocol
to
to
compute
the
pass.
Well,
if
there
is
a
centralized
compute,
we
use
PCE,
no
matter
whether
it
is
a
distributive
signaling
or
it
is
a
centralized
signaling.
The
PCE
is
used
to
compute
the
pass,
but
things
are
going
to
be
different
once
we
need
to
separate
the
pass
and
usually
for
distributed.
Oh
we
can.
We
can.
We
can
use
RTP
and
in
centralized
pass
computer
plus
distributed
the
signaling.
C
We
can
also
use
our
vp
pass.
This
is
the
story
for
pc
initiated
and,
finally,
if
we
want
to
come
centralize
the
signaling,
we
can
also
use
PCP
or
that
comes
to
configure
the
corresponding
devices
and
after
the
RSP
is
set
up.
There
is
look
a
kind
of
resource
update
we
earlier
this.
It
can
be
done
by
OSPF
or
pc
peres.
C
Right,
yeah
yeah:
absolutely
we
should
list
it
also
here
and
that
may
change
the
default
and
the
search
scenario
we
add.
Can
you
please
end
in
moment?
Okay,
okay,
this
is
a
controller
reliability,
and
this
is
something
new
topic
and
we
focus
on
solving
the
problem.
Once
the
controller
is
shut
down.
How
will
the
full
system
acted
to
solve
this
problem?
We
nowadays
we
have
to
branches
off
approaches.
The
first
one
is
controller
Federation
by
backup
controller
and
the
second
one
is
also.
C
L
T
Okay,
this
is
a
zero
one
version
update
of
the
layer,
one
connectivity
service
model.
You
may
recall
the
first
presentation
at
last.
The
ATF
are
in
Singapore,
so
just
a
quick
recap
about
what
is
the
purpose
of
this
draft?
We
starting
from
the
RFC
48
47.
We
want
to
provide
that,
provides
a
framework
about
layer,
1,
VPN
services
and
in
particular,
these
RFC
describes
in
the
old
use
cases
and
all
the
dynamic
provisions,
the
dynamic
provisioning
that
was
take
for
also
the
scope
of
our
draft.
T
So
our
draft
provide
the
young
that
a
model
for
layer,
one
BPM
connectivity
service
model
and
also
it
is
based
the
bottom.
The
work
on
that
is
made
in
this
deficit
48:47,
but
also
is
made
in
agreement
with
MAF
work
on
layer.
One
connectivity
services
now
we
can
describe
volt
are
the
most
common
deployment
scenario
that
are
in
scope
for
a
layer,
one
with
the
end
services,
so
the
first,
that
is,
the
basic
use
cases
for
the
layer,
one
VPN
for
external
customer.
T
T
Customer
that
ask
for
a
simple
layer,
one
connectivity,
but
okay,
we
can
consider
this
is
cope
because
our
FEC
48:47
consider
this
case.
So
it's
better
to
consider
also
this
deployment
scenario.
The
second
one
is
about
the
multi
service
backbone
for
internal
customer.
That,
in
our
opinion,
could
be
the
most
common
use
case,
because
it
include
the
interface
between
the
Sdn
controller
for
different
services,
so
layer,
2,
layer,
3
and
so
on,
and
the
network
Sdn
controller
for
layer
1
media.
T
Ok,
this
is
just
as
light
to
describe
the
difference
between
layers
to
assembly
or
3sm
that
are
the
other
service
model
that
ATF
is
working
on
with
the
layer
once
he
connectivity
service
model.
So,
first
of
all,
we
have
to
Assam
and
the
layer.
Tsm
are
service
models,
so
our
focus
on
customer
service
interface
layer,
one
GSM
can
be
the
southbound
interface
of
the
service,
Sdn
controller
towards
the
network
as
the
uncontrol.
So-
and
this
is
the
typical
archetype
that
I
mention
before,
for
the
multi
service
backbone
for
internal
customer,
for
example.
T
Ok,
this
is
the
model,
it
is
very
simple,
so
we
have
address
in
his
light.
Where
address
also
one
out
comment
we
received
in
Singapore.
In
particular,
we
put
the
Uni
data
client
protocol
and
the
value
that
this
variable
can
assume
was
one
over
and
the
comment
that
we
receive
at
last
meeting
so
of
course,
gigabit
at
an
intangible
internet
fibre
channel
and
so
on.
T
There
are
also
some
lies
on
with
the
MAF,
so
we
are
working
together
to
move
forward
or
so
this
work.
Of
course,
this
is
in
scope
in
our
opinion
of
Sikkim
working
group,
because
this
is
the
home
of
layer,
0
and
layer,
1
technology
and
so
asking
for
working
up
adoption.
If
you
consider
that
document
is
stable
and.
A
A
D
D
Basically,
what
we
have
today
is
pretty
good
the
draft
like
76
98
that
defines
all
the
parameter
that
must
be
signal
to
the
network,
to
define,
to,
let's
say,
to
identify
and
distribute
media
channel
information,
and
but
we
don't
have
the
possibility
or
we
don't
have
yet
the
way
to
signal
what
is
inside
the
media
channel
inside
the
media
channel
dermis.
There
can
be
either
a
single
carrier
or
there
can
be
multiple
carriers
and.
D
D
D
D
D
That
might
be
one
part,
one
part
of
transceiver
en
connected
to
one
part:
road,
orderly.
There
must
be,
or
there
can
be,
multiple
parts
of
en
connected
to
a
single
roadmap
or
it
doesn't.
Care
is
just
a
way,
a
different
way
to
model
the
interconnection.
In
any
case,
once
the
client
asked
for
a
LSB,
so
a
media
channel
in
this
case
because
we
are
in
the
SSO
an
environment-
may
require
okay.
D
Give
me
these
this.
They
give
me
a
connection
between
the
egress
node
to
the
the
ingress
node
to
the
egress,
not
with
this
bandwidth
net
bandwidth,
for
example,
foreign
Rica
and
I,
give
you
the
de
step,
let's
say
the
availability
of
possible
for
ports.
Then
this
is
signal
via
uni
to
the
gmpls,
and
then
is
the
gmpls
deciding
number
one.
The
routing
number
to
the.
D
Media
channel
window
and
the
media
channel
width
is
actually
depending
on
the
modulation
format,
on
the
FEC
and
on
others
other
optical
parameters.
So
what
can
happen
is
that
the
control
plane
may
decide,
for
example,
to
implement
the
400
gig
LSP,
using,
for
example,
all
four
ports,
because
the
circuit,
the
LSP
length,
is
so
high.
So
that
has
to
use
a
modulation
format
like
QPSK,
which
is
pretty
performant
but
low
bandwidth,
and
then.
D
So
make
a
media
channel
pretty
wide
because
as
to
contain
four
carriers
instead
of
in
case
of
LSP,
very
short,
like
I,
don't
know:
500
kilometer,
for
example,
where
a
different
kind
of
modulation
format
like
16
QAM
may
be
used,
and
so
only
two
carrier,
and
only
two
ports
are
needed.
In
this
case,
the
media
channel
will
be
only
a
bit
narrow,
let's
say
almost
50%,
now
that
the
one
that
was
carrying
four
carries
so
to
signal
all
the
stuff
between
either
the
client
and
the
network
and
inside
the
roadman
networker.
D
We
we
added
some
TLV,
that
is
that
are
used
to
signal
all
this
information
between
crying
the
network
and
inside
the
network
inside
the
MPLS,
and
those
parameters
are
and
say,
mentioned
here.
So
the
first
one
is
for
the
request,
the
number
of
carrier
that
the
client
can
provide
so
the
number
of
ports,
basically
that
the
trying
can
provide
or
kami
available
to
the
network
to
make
any
recipe
the
total
bandwidth.
D
This
is
that
the
total
bandwidth
is
the
net
bandwidth
is
not
actually
the
post
factor
and
we
saw
total
value,
is
100
200
400,
wonder
450
500.
Whatever
and
then
other
two
parameters
that
let's
say,
tell
the
network:
ok,
what
I'm
asking
you
number
of
carrier,
for
example,
I,
say
for
total
bandwidth
400
this
our
parameter
that
are
mandatory
or
this
our
parameter.
That
can
be,
let's
say,
best
effort.
So
if
you
cannot
give
me
400
gig
on
for
carrier,
so
give
me
whatever
you
can,
and
this
is
the
s
and
be
flexible.
D
Optical
feasibility-
and
the
part,
of
course,
is
to
take
care
of
the
modulation
format,
the
FEC
and
the
betrayed
the
bit
about
the
the
frequency
of
the
symbols,
the
symbol
rate,
let's
say
on
top
of
that
gmpls
must
identify
per
carrier.
The
carrier,
identifier-
that
is
basically
can
be
a
thing.
Simple
number
simple,
integer,
one,
two,
three,
whatever
J,
which
is
the
granularity
of.
D
D
D
D
We
wanted
to
propose
this
method
as
as
an
example
or
as
to
share
everybody.
What
has
been
done,
because
we
think
we
are
addressing
a
real
problem
in
sense
that
if
you
want
to
make
a
multi
carrier
little
channel
signaling
today,
okay,
that
must
be
that
might
be
different
solution.
Different
proposal,
I
am
personally
not
aware
of
this
is
one.
D
D
L
Butler
Nokia
I,
don't
know
whether
they
are
negative
yet
to
some
extent,
probably,
are
you
aware
of
the
latest
developments
at
itu-t
study
group
fifteen
regarding
inverse
multiplexing
and
OTS
IG,
because
they
are
moving
in
that
direction
as
well?
Second
point
is
they're
actually
addressing
services
with
a
larger
data
rate,
so
it's
beyond
100
Gig
and
looking
at
this
looking
at
the
subcarriers,
it
looks
like
the
granularity.
This
currently
defined
in
a
flex
grid
is
sufficiently
low.
So
this
is
a
twelve
point.
Five
gigahertz
and
I
think
this
granularity
is
probably
suitable.
D
D
Probably
what
we
miss
here
is
the
link
between
the
DWDM
part,
because
here
and
actually
the
the
client
is
the
ability
decide
where
outer
house
or
we
have
a
DW
m
interfacing
the
router.
So
we
don't
pass.
We
don't
have
a
a
clear
mapping
between
the
Internet
traffic
and
the
yen,
but
sure
I
agree
with
you.
If
you
have
a
transponder
I
think
we
will
miss
something
and
open.
J
D
D
So,
basically,
what
the
client
can
tell
to
the
network
is
the
kind
of
modulation
format,
the
FEC,
the
baud
rate,
number
of
carriers
that
are
available
bit
per
symbol,
so
basically
the
spectral
efficiency
subcarrier
bandwidth,
so
the
minimum
distance
that
should
be
taken
between
the
two
subcarrier
garb
and
in
case
of
a
carrier
is,
let's
say
at
the
side
of
the
media
channel,
so
basically
the
filtering
carbon
and
then
Jackson
our
X
power,
Oh,
SNR,
robustness
and
max
polarization
power
difference.
So
they
did
the
difference
between
the
carrier
power.
D
That
is
again
to
be
honest,
not
implemented
this
one,
but
is
something
that
would
be
beneficial.
It's
not
implemented
because
today
we
shared
this
information
between
the
client
and
the
network,
using
data
controller,
the
centralized
controller,
and
basically
that
is
the
reason,
but
if
you
have
a
full
G
MPLS
network,
not
having
the
controller.
At
this
point,
the
LMP
and
sharing
this
parameter
is
mandatory.
A
So,
for
example,
there's
a
link.
There
is
just
two
ends
of
a
link
and
this
this
and
can
advertise
the
capability
of
this
end
and
another
and
can
also
advertise.
You
know
the
ability
of
itself
and
then
the
one
or
the
network
can
get
there.
You
know
the
link
information
because
they
can
correlate
this
kind
of
capability
between
these
two
ends.
Yes,.
D
Yes,
yeah,
you
got
a
good
point,
says
that
if
the
gym
implements
source
routing
so
as
to
know
number
one,
the
characteristic
of
the
port
at
ingress,
but
as
to
know
whether
and
has
to
check
whether
the
ingress,
egress
node
has
the
same
capabilities
or
at
least
capabilities
compliant
with
the
ingress,
not
because
a
deado,
otherwise
the
LSP
is
not
feasible.
That's
it!
Yes,
the
answer
is
yes.
D
Yeah
I'm
pretty
confident
that
is
mature,
because
you
know,
as
I
said,
we
have
an
implementation
up
and
running.
We
didn't
see
any
big
issues,
of
course,
as
I
said,
can
be
improved
as
Peter
said
and
really
appreciate.
The
comment,
but
I
think
is
a
good
starting
point
and
if
it
becomes
a
working
group
document
then
is
open
to
any
any
comment
and
any
contribution
as
well
I
mean.
C
D
D
For
DWM
interfaces,
so
exchange
of
parameters
between
in
client
and
network
and
then
the
same
information
are
or
different
kind
of
information
or
standard
information.
Let
me
say
our
model
as
a
young.
Let's
start
from
the
Olympic
consideration.
I
think
this
is
a
really
document
that
is
consolidated
in
the
past.
We
discuss
quite
a
lot,
what
put
inside
what
to
put
inside
the
TLD,
and
then
agreement
has
been
reached,
and
so
non
modification
was
done
since
the
last
ITF.
This
one
again
is
something
that
I
believe
is
is
useful
and
then
can
can
go
through.
B
Also,
these
drafts
probably
are
at
a
point
in
which
we
should
decide
whether
to
progress,
DRAM
them
or
probably
stop
working
on
on
this
kind
of
activity.
Well,
now
that
the
DDI
BDM
interface
framework
is
an
RFC,
it
was
a
need
ready
to
a
beehive.
Sorry,
not
yet
it's
time
to
consider
working
on
the
distinctions
and
not
just
the
framework
sort
of
uncompleted.
D
K
D
D
D
L
L
D
D
D
U
Nicholas
ombo,
so
this
draft
refers
to
a
specific
use
case
for
a
young
model
for
finished
state
machine
presented
in
in
Emmett
mod.
So
the
the
use
case
is
is
the
following.
What
we
want
to
do
is
to
instruct
the
optical
transponder
about
recovery
actions
to
do
in
case
of
the
physical
layer
degradation
or
more
in
general,
to
instruct
optical
transponder
about
reconfiguration
in
case
of
physical
layer
changes.
U
So
here
you
can,
you
can
see
the
reference
to
the
more
generic
young
model
in
that
mode
for
flexible
transponders
we
mean
transponder,
supporting
the
possibility
of
configuring,
several
values
of
the
bitrate
modulation
format
and
code
rate,
so
this
set
of
transmission
parameters.
Format,
in
fact,
are
are
configured
based
on
some
physical
layer
conditions
and
they
can
be
reconfigured
in
case
the
physical
layer
condition
condition
change.
U
So
what
not
normally
what's
happened
so
assume
to
have
an
active
service
connection.
We
have
degradation
at
the
physical
layer
so
something
that
can
be
seen
as
a
bit
error
rate
increase
over
some
threshold.
An
alarm
is
generated
toward
the
on
demand
or
in
general,
toward
the
management
system
does
some
new
computation
of
transmission
parameter
is
performed
and
the
SDN
controller
reconfigure
it's
the
the
transponder
so
that
the
recovery
can
take
place,
so
this
operation
can
be
time-consuming,
especially
if
several
connections
are
interested
by
the
failure.
U
So
this
is
the
the
young
model.
You
can
see
the
current
state,
which
is
defined
by
a
specific
configuration
of
the
transmission
parameters,
so
betrayed
modulation,
format,
encode
rate
we
have
a
list
of
states
to
which
state
is,
is
associated
a
transition.
So
here
for
a
for
a
transition,
we
consider
a
bit
error
rate
change
with
respect
to
the
generic
young,
more
generic
young
model.
Here
we
we
have
augment
the
model
with
the
first
two
squared
attributes.
U
So
the
threshold
parameter
in
this
case
we
can
set
the
threshold
on
the
bit
error
rate
or
on
the
OS
n
R,
and
we
have
also
threshold
the
operators
operator.
If
the
bit
error
rate
is
higher
than
or
lower
than
the
transition
is
triggered,
then
we
have
some
actions
so
in
this
case
the
the
reconfiguration
of
the
modulation
format
or
or
the
order
code
rate
and
after
the
execution
of
this
reconfiguration,
some
new
actions
can
be
executed.
U
For
example,
a
new
action
can
be
then
the
notification
to
the
SDN
controller
that
the
reconfiguration
has
taken
a
taking
place.
Then
we
go
to
the
to
a
new
state.
So
simply
we
can
see
these
two
state
to
state
machine.
We
are,
for
example,
in
in
the
first
state,
which
is
which
refers
to
PM
16qam.
If
we
have
an
event
of
bit
error
rate
over
the
threshold,
we
we
can.
U
R
Can
call
way
so
let's
distinguish
software
us
from
our
trailers
right.
So
if
it's
a
soft
failure,
there
is
no
rush
in
do
any
anything
all
right.
So,
basically
something
this
goes
out
of
like
a
normal
behavior
and
it
is
possible,
for
example,
to
update
is
the
end
controller
and
he
will
actually
explicitly
reconfigure
the
device
right,
yeah
yeah.
So
if
it,
if
it's
actually
heart
failure,
then
sometimes
there
is
no
time
for
communication
between
the
device
and
the
controller,
and
you
want
need
to
know
in
advance.
R
But
in
this
case
it
would
be
better
to
have
like
some
hard
configuration,
such
as,
for
example,
parameters
so
that
associated
with
the
Recovery
Options
a
while
the
tunnel
is
established
versus
to
provide
a
script
kind
of
flexible
logic
which
more
flexible.
However,
it
will
be
slow
as
well
right.
So
basically,
where
do
you
see
the
the
real
value
of
being
able
to
program
the
actions
in
this
flexible
way?
You
know
like
in
your
particular
case,.
U
R
U
R
U
On
the
device
but
well
yeah,
it's
true-
this
use
case
specifically
target
script
to
in
to
be
installed
in
in
the
device,
because
the
problematic
that
we
have
seen
with
the
with
the
operator
it
was
that
we
wanted
to
create
more
scalability
at
the
controller
and
and
also
a
faster
reaction.
So
for
this
reason
yeah
it's
it's
true.
We
installed
the
script
into
the
the
device,
the
agent,
but
this
is
a
the
young
model.
Finally,
is
so
so
generic
is
a
finished
state
machine
we
can.
We
can
install
it
also
at
the
SDN
controller.
Now.
R
C
R
And
or
some
tickler
whatever,
and
then
you
are
basically
three
on
Moodle
and
you
provide
a
script
that
could
be
translated
into
the
side
script
and
invoked
in
case
a
or
fara.
So
what
I'm
saying
is
that
it
will
contribute
to
the
latency
of
the
restoration
right
that
because
because
if
you
have
like
a
like
a
hard
program
and
project,
it
would
be
faster
to
do
this
anyway.
But.
B
C
R
Well
then,
consider
another
situations
like
like,
for
example,
sort
failures
or
whatever
any
sim
prediction
or
whatever.
So
then,
where
is
the
rush
right?
So,
for
example,
why
Cannot
I
just
notify
the
the
SDN
controller
about
certain
event,
and
then
he
will
explicitly
reconfigure.
It
will
be
easier
for
the
for
the
controller
to
do
this.
Well.
U
C
B
U
R
R
C
R
But
but
this
is
basically
it's
kind
of
a
policy
that
you're
imposed
on
the
device.
Okay,
in
it's
a
flexible
policy
defined
by
the
client
and
implemented
by
the
server
it,
it
assumes
that
there
is
a
for
example,
if
there
is
like
environment
scription,
environment
on
the
other
Odom's,
and
not
all
of
them
have
such
thing
right
and
and
basically
in
case
of,
say,
protection
or
restoration.
It
is
better
to
have
a
heart-to-heart
logic.
