►
From YouTube: IETF101-MLS-20180322-1550
Description
MLS meeting session at IETF101
2018/03/22 1550
https://datatracker.ietf.org/meeting/101/proceedings/
C
B
Alright,
so,
as
our
new
area
director
arrives,
I'd
like
to
welcome
everybody
to
the
messaging
layer,
security
Boff,
if
you're
expecting
something
else
or
if
you're
in
the
other
room
no,
this
is
this
is
the
right
room.
So
today
we're
going
to
go
through
several
presentations
and
talk
about
a
proposed
charter
for
messaging
layer,
security.
D
C
The
note:
well,
it's
Thursday,
you
should
have
seen
this
a
bunch,
so
we're
not
going
to
linger
on
this
very
long,
buts
in
the
slides.
If
you
really
want
to
read
it,
we
got
a
minute
take
here.
We
got
a
jabber
scribe.
Please
sign
the
blue
sheets
as
they're
going
around
unless
you're
not
already
subscribed
to
the
mailing
list.
It's
there
and
the
jabber
room
is
also
listed
on
the
slide.
B
Alright,
so
this
is
the
overview
of
the
agenda:
we're
going
to
start
with
a
bit
of
agenda
bashing.
If
anybody
has
any
changes,
they
want
to
propose,
as
well
as
following
that
we're
going
to
do
a
30-minute
problem
statement,
followed
by
an
architecture,
presentation,
a
protocol,
Draft
presentation,
as
well
as
a
state
of
formal
minute
analysis,
and
then
we're
gonna
spend
most
of
the
remainder
going
over
the
Charter
text
very
closely
and
we'll
end
it
off
with
some
Boff
questions.
C
E
All
right,
Thank,
You,
Charis,
thanks
everyone
for
being
here
so
I,
wanted
to
give
everyone
an
overview
of.
Why
we're
here
today,
the
group
of
us
who
proposed
this,
why
we
care
about
this?
What
problem
we're
trying
to
solve
next
slide?
Please!
So
if
you
look
at
the
app
store,
any
App,
Store
really
and
look
at
for
secure
messaging
apps,
nowadays
you
get
a
bunch
of
them.
I
think
we've
got
people
who
work
on
most
of
these
here
act
today.
Actually,
a
lot
of
these
are
using
really
similar
protocols.
E
Variants
on
signal
protocol
are
especially
prevalent.
Some
of
them
are
using
super
different
things.
A
Cisco
spark
there
in
left
column
and
iMessage
use
pretty
different
protocols,
but
what's
common
about
all
of
them,
is
that
they're
uncommon
they're
all
using
different
protocols,
maintaining
their
own
libraries,
their
own
software,
and
because
all
these
protocols
are
different,
they
have
independent
security
analyses
and
some
of
them
have
gotten
very
thorough
security
analyses
and
academic
papers,
and
some
of
them
have
no
analysis
at
all
that
I
know
of
anyway,
and
so
the
goal
of
this
well
next
slide.
E
The
goal
of
what
we're
doing
here
is
to
kind
of
address
that
situation.
The
concrete
target
we're
after
is
an
asynchronous
group
messaging
security
protocol.
Well,
delt
will
dive
in
to
unpack
that
on
the
next
slide,
but
the
idea
is
to
get
something
that
can
meet
the
the
needs
of
all
those
apps
that
were
on
that
last
slide
and
more
and
other
applications
that
have
these
common.
That
common
use
case
in
common
yeah
now,
to
put
a
little
finer
point
on
that,
we're
there's
a
couple
of
aspects
of
interoperability.
E
We
are
after
and
some
we
aren't.
So
the
impact
of
these
specifications
that
we're
trying
to
get
here
I'll
skip
to
the
bottom
and
say
that
we're
not
trying
to
get
full
interoperability
between
messaging
applications.
That's
a
much
more
complicated
question
involving
a
message
transport
involving
how
you
express
application
level
notions.
E
E
So
the
analogy
here
is
that
there's
tons
of
applications
that
use
HTTP
that
use
TLS
and
use
TLS
in
different
ways,
and
so
the
idea
here
of
MLS
is
design
design,
a
messaging
security
protocol
that
can
be
used
in
many
different
applications
in
many
different
ways
and
what
you'll
see
in
these
documents?
The
architecture
we'll
discuss
kind
of
the
are
general
architecture
for
how
we
imagine
a
messaging
protocol
and
how
MLS
can
fit
into
that
context.
And
then
the
protocol
documental
describe
the
draft.
We
got
what
we
got
so
far:
yeah
EKG
hi.
F
Daniel
con
Gilmore
ACLU,
so
just
as
a
clarifying
question
on
this
slide,
you
mentioned
that
application
level.
Interoperability
is
in
non-goal.
This
does
not
address
single
application
with
multiple
say
servers
or
federated
communication.
So
I
just
want
to
be
clear
that
federated
communication
like
across
server
domains
or
things,
is
also
how
to
scope
for
this.
I
would
say
so.
Yes,
okay,
just
wanted
to
make
sure
that
that's
clear
too,
because
it
seems
like
that
would
be
a
relevant
point
right.
We
have
XMP
already,
for
example,
and
we're
not
trying
to
do
that.
That's.
E
Correct,
yes,
I
think
I
think
probably
won't.
We
want
to
be
compatible
with
use
cases
like
that
and
not
block
that
I.
Think
Dave
Kirtland,
if
he's
in
the
room,
has
already
been
thinking
some
about
how
to
address
XF
in
PP,
but
I
think
that's
something
we're
not
it's
not
kind
of
a
primary
goal:
okay,
yeah.
G
My
perspective
XMPP
has
like
no
medications
to
structurally
at
all
other
than
like
it's
you
know.
Are
they
on
the
same
server
right?
So
you
need
it,
but
I
mean
if
somebody
were
layer,
authentication
structure
on
top
an
XMPP,
then
you
could
imagine,
then
you
imagine
everybody
who
would
like
to
here.
Do
that
would
be
able
to
talk
over
XMPP
with
Federation
yeah
I
think
there
were
the
route
that
the
case
I
think
that
is,
that
is
that
it
is
like
not
really
in
the
scope
at
all.
E
And
and
I'm
really
yeah
I
think
that
a
lot
of
other
Federation
that
where
Federation
will
become
an
issue
for
this
protocol,
is
in
the
authentication
layer
and
that's
all
I'll
speak
more
a
bit
more
about
authentication
there.
Let
me
just
table
that
for
the
moment,
so
next
slide,
please
well
doc,
unpack
this.
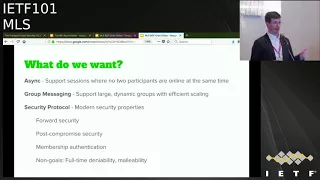
E
This,
the
concrete
substantive
thing
we're
after
here,
so
we've
got
a
few
components
to
this
description,
so
whatever
protocol
we
need
here,
we
get
here
needs
to
have
this
asynchronicity
property
and
what
that
means
is
we
want
to
be
able
to
have
these
secure
messaging
sessions
where
no
part
to
participants
are
online
at
the
same
time.
So
if
I'm,
starting
up
a
chat
with
you,
mad
I
should
be
able
to
get
some
information
with
that.
E
So
this
is
more
than
just
a
one-to-one
protocol.
So
tell
us
the
case:
we've
had
the
most
experience
within
the
IETF
is
explicitly
a
one-to-one
protocol.
There's
a
client
and
a
server,
and
the
use
case
were
after
here
is
groups.
There
are
some
protocols
that
have
been
really
well
vetted
in
in
the
one-to-one
space
and
I.
Think
a
lot
of
what
this
is
and
mentioned.
This
later
is
to
kind
of
generalize
some
of
those
lessons.
We've
learned
from
those
protocols
to
make
them
work
better
with
groups.
Yes,
please
hi.
H
E
At
least
in
the
drafts
we
have
now,
there
is
a
condition
of
continuity
of
a
session
and
I.
Think,
oh,
maybe
I'm.
Looking
over
a
catriel,
our
our
academic
friend
here
I
think
some
of
the
goals
we
have
around
post
compromised
security
probably
depend
on
carrying
that
state.
I,
don't
know
we
need
to
discuss
it
a
lot
but
yeah
right
now.
E
We
do
have
that
notion
that
there
is
a
group
and
there's
a
conversation
that
involves
over
time
that
is
correlated
in
their
state
that
gets
carried
along
yeah
thanks
for
the
question
so
yeah,
so
we
need
so
we're
supporting
groups
here,
it's
not
just
one
to
one
and
we're.
We
have
a
goal
to
support
large
and
dynamic
groups.
E
It
gets
to
be
kind
of
difficult
to
do
a
hundred
thousand
D
H
operations,
it's
to
had
someone
say,
or
you
know
things
that
are
quadratic-
that
might
work
at
small
scale,
get
really
difficult
at
the
scale
of
you
know,
once
you
had
some
zeros,
so
large
dynamic
groups
and
try
and
address
those
pretty
efficiently.
Now,
let's
talk
about
the
security
properties,
we're
trying
to
get
and
I've
got
a
cartoon
on
this
in
the
next
slide.
There's
a
few
major
security
properties
were
trying
to
get
here.
E
E
Authentication
is
a
concept
that's
going
to
be
critical
here,
so
that
we
know
who
were
encrypting
to
who
can
read
these
messages
that
are
confidential.
What
the
boundary
of
the
confidentiality
is
and
finally
there's
some
explicit
non
goals.
We
want
to
call
out
here
that
have
been
properties
of
some
problem.
Some
protocols
in
the
prior
art
deniability
is
one
I've
said
full
time
deniability
here,
because
we
may
want
to
have
some
deniability,
but
we
know
we
need
a
non-denial
option
for
several
cases
that
we've
talked
about.
E
E
G
E
It's
kind
of
the
opposite
of
integrity
yeah
after
the
fact
you
yep
all
right
next
slide
kind
of
is
a
cartoon
of
what
we
mean,
the
the
topics
of
the
properties
we'll
talk
about
most
or
for
our
security
and
post
compromised
security.
This
is
to
cut
a
cartoon
of
what
we
mean
by
that,
so
both
of
those
properties
are
addressed
as
a
point
compromise.
The
assumption
that
an
end
point
is
fully
compromised.
All
of
its
secrets
are
published.
E
The
attacker
at
a
point
in
time
and
the
idea
of
having
forward
secrecy
and
post
compromised
security
properties
in
a
protocol
is
that
there
are
some
protocol
actions
that
establish
these
boundaries.
So
in
TLS
you
get
forward
security
when
you
do
a
a
new
handshake
with
fresh
th
exchange,
because
the
fresh
entropy
from
that
d-h
exchange
cuts
off
anyone
who
had
the
secrets
to
the
session
in
the
past
so
that
that
would
be
kind
of
the
left
hand
boundary
here.
If
you
think
about
this
in
TLS
sense,
post
compromised
security
is
kind
of
similar.
E
F
Sorry,
this
is
dkg
again.
I,
actually
think
that
your
explanation
of
forward
security
was
incorrect
and
it
may
just
been
a
slip,
but
I
think
it's
easier
to
think
of
forward
secretly
forward
security
in
a
messaging
context
as
deletion
schedules.
What
gives
you
forward
security
is
not
that
you
created
a
new
D
H
pair
or
even
that
you
ratcheted
forward
a
secret,
but
that
you
destroyed
the
prior
secret.
That's
what
gives
you
the
forward
security,
the
destruction
of
the
old
secrets,
not
the
new
stuff.
Well,.
E
Is
what
gives
you
the
forward
security
yeah?
You
need
to
transform
the
group
state
to
something
that's
inaccessible,
to
people
that
have
the
history
and
then
delete
the
history
yeah.
Absolutely
so
next
slide.
Yeah
I
just
wanted
to
call
out
the
prior
art
here
for
comparison.
There's
been
a
bunch
of
work
on
this
in
past.
I
won't
go
through
the
specifics.
I
think
the
the
overarching
the
important
thing
to
take
away
here
is
that
you
know
the
more
recent
stuff
is
which
is
closer
to
the
bottom.
E
Next
slide,
please
so
yeah.
This
is
just
kind
of
a
cartoon
of
what
we
mean
by
ratcheting
it
show
of
hands.
People
have
heard
of
ratchets
and,
in
the
crypto
sense,
okay
good.
So
this
is
pretty
familiar
idea,
so
we
generally
talk
about
two
types
of
rackets.
The
left-hand
side
shows
hash
ratchets,
which
are
you
know,
forward
security
things.
E
In
this
case,
to
get
pcs,
they
want
other
concepts,
so
these
are
kind
of
the
things
the
tools
were
using
from
the
prior
art
to
get
some
of
these
properties.
The
other
thing
is
that
we've
cut
we're
kind
of
pulling
from
the
prior
art.
Is
this
idea
of
init
keys
or
pre
keys
a
lot
in
the
literature
which
are
things
that
I
can
publish
in
the
cloud
that
allow
someone
to
initiate
a
conversation
with
they
provide
a
public
key
and
some
related
information?
E
Someone
can
use
to
initiate
a
conversation
with
me
and
begin
sending
me
messages
without
my
being
online,
so
those
are
that's
going
to
be
kind
of
the
key
to
getting
in
a
synchronicity
in
a
couple
senses
we're
gonna,
have
some
user
init
keys
and
we'll
have
group
init
keys.
John
will
talk
about
that
more
and
when
we
talk
about
the
protocol
later
next
slide,
please
so
this
just
kind
of
sum
up.
This
is
a
cartoon
of
the
the
scope
I
talked
about
earlier.
E
So
you
know
by
analogy
to
TLS
here,
as
I
said
before,
there's
lots
of
applications
out
there
that
use
TLS
HTTPS,
my
that's
my
mum,
SMTP,
XMPP,
etc
and
they're
running
over
different
transports.
Tianna.
If
you
incorporate
details
in
this
picture,
they're
transported
in
different
ways,
they
might
be
transported
in
HTTP
for
those
of
you
who
came
to
the
a
TLS
law
earlier.
This
discussion
is
earlier
this
week,
there's
different
transports.
E
You
can
transfer
these
security
protocols
different
way
and
they
carry
different
things
and
but
there's
a
common
security
layer
that
addresses
the
I
want
to
have
a
secure
connection
between
a
client-server
use
case
and
similarly
off
to
the
side
there.
They
there
is
a
relatively
generic
authentication
function,
built
into
TLS,
where
you
can
plug
in
a
certificate,
and
you
can
do
a
signature
to
create
a
certificate.
Verify
message
that
authenticates
the
holder
a
key
pair,
but
the
details
of
the
PKI
that
get
used
with
TLS
aren't
specified
in
TLS.
E
There's
just
that
clean
interface
point
and
so
I
think
that
kind
of
encapsulates
what
we're
trying
to
get
at
here.
So
we
want
a
security
protocol
that
can
serve
this
group
messaging
function,
kind
of
independent
of
transport
and
independent
of
exactly
what's
being
carried
in
those
messages,
and
also
have
this
interface
point
over
to
some
authentication
scheme
so
that
we
can
take
different
authentication
schemes
and
plug
them
in
in
a
way
that
gets
where,
where
we
know
something
about
what
security
properties
we
get.
So
you
need
to
define
that
interface.
E
I
Hi
everyone,
I'm
Imelda,
Maura
I'm,
the
tech
lead
for
cones
and
robots,
see
security
in
Google,
so
we'll
talk
about.
Amelia's
architecture
covers
the
system,
overview
and
functional
security
requirements.
So
this
is
bitly.
Any
massif
estimate
expect
to
be
server
side
and
client
side.
So
server
side
has
a
certification
and
services
most
of
the
times
are
operating
under
under
the
same
entity,
but
they
are
logically
separate
clients
either
a
bunch
of
users.
Issues
are
maintained
at
one
or
more
device
like
web
desktop
mobile
from
the
protocol
perspective.
I
Hd
device
is
a
separate
entity,
that's
a
good
client.
So
in
this
picture
we
have
like
four
four
members,
a
b
c
and
d,
and
there
is
a
group
between
a
B
and
C.
It
has
three
devices
ps2
one
cs1,
so
syndication
services
basically
provides
mapping
between
user
IDs
like
email
or
phone
numbers
to
long
term
items,
C,
Keys
delivery
services.
It
ensures
an
order
and
reliable
message,
delivery
and
attachment
and
if
any
reordering
the
message
the
client
should,
the
protocol
should
be
able
to
detect
that
and
also
store
and
achieve.
Initial
user
need.
Kids.
I
I
However,
the
the
second
always
nosiest
by
doing
like
some
traffic
analysis,
so
some
application
might
just
end
up
storing
the
group
numbers
on
the
server
and
one
last
saying
the
server
is
also
responsible
for
evicting
long-term
inactive
users
just
to
protect
for
secrecy
like
most
application
to
the
using
like
30
or
45
days,
and
after
that
we
just
effective
50
with
our
clients.
From
the
conversation,
it's
like
this
okay,
so
user
will
do
what
you
expected
to
do
in
any
messaging
systems.
I
We
adjust
our
group,
send
receive
messages,
invite
remove
members
join
or
leave
existing
groups
or
add
remove
devices
from
the
vertical
perspective
and
to
remove
members
and
move
devices
you're
the
same
device
at
the
end
of
college,
just
a
single
client.
So
it's
a
vertical
layer.
They
are
the
same
operation
and
all
call
all
clients
are
peers.
So
anyone
can
add
remove
any
other
one.
The
Ackland
for
this
operation
would
be
up
the
application
layer.
So
in
this
situation
like
a
one
would
create
a
group
with
T
and
C.
I
So
a
one
will
request
in
it:
keys
for
a
2,
a
3,
B,
1,
B,
2
and
C
1
click,
shirt,
secret,
verify
the
signature
and
this
inactive
great
shirt
secret
and
keep
the
message
and
sent
to
B
and
C
and
B
SC
will
calculate
the
same
shirt
secret
decrypt.
The
message
and
optionally
will
trigger
a
nuclear
vision
to
improve
future
for
secrecy.
Next
slide.
Please
ok,
functional
requirements
scalable,
so
the
protocol
should
be
able
to
support
large
group
up
to
50,000
clients.
I
Isochrones
should
be
able
to
start
all
the
other
operations
of
the
need
for
all
clients
to
be
online
and,
of
course,
multi
device,
and
because,
as
I
mentioned
device
are
obtained,
a
separate
entity,
so
multi
device
could
be
supported.
Natively.
However,
when
you
add,
a
new
device
will
not
be
able
to
access
the
previous
conversation
history,
but
it's
always
up
to
the
application
to
support
this
estate
recovery.
I
So
if
any
device
or
any
clients
lost
the
state
should
be
able
to
recover
it
without
affecting
the
group
and
the
Ruby
state
method
is
our
collection
is
to
protect
user
privacy,
so
authentication
service
order.
A
service
should
only
collect
the
manometer
data
to
deliver
the
message
Federation
as
Richard
mentioned,
so
we
don't
expect
a
full
interval
receive
it
at
the
application
layer.
However,
as
a
protocol
layer,
different
implementation
should
be
able
to
interpret
so
far.
You
need
a
Mike.
J
K
I
This
is
a
privacy
concern
concerning
this
issue,
but
I
believe
most
of
the
protocol
today
support
multi-vise
have
the
same
issue.
However,
there
isn't
some
tricks,
you
can
do
with
a
sphere
for
art.
The
cheese
structure
can
actually
work
around
this.
For
example,
can
you
can
talk
about
this
more
in
the
protocol,
but
one
idea
of
this
I
have
all
devices
under
the
same
node,
so
from
other
users
can
only
see
a
single
node.
You
don't
know
how
many
devices
you
have,
but
this
is
a
problem
with
any-any.
K
F
I
G
G
M
I
E
D
I
I
Ok,
so
so
far,
so
good
last
point
burgeoning
let's
make
things
more
complex,
so
yeah
Emily.
It
should
support
multiple
versions,
and
it
should
make
sure
that
picking
the
highest
supported
version
between
outlines
and,
of
course,
have
mitigation
for
downgrade
attacks.
Cleaner,
sightings,
okay,
security
requirements,
so
method
secrecy.
Only
it
should
have
only
a
group
member
exists.
Current
group
member
should
be
able
to
decrypt
and
access
the
messages.
I
Intention,
authentication
messages
only
be
accepted
if
sent
from
an
investment.
Good
member,
we
again
another
asterisk
case.
We
could
optionally
improve
this
by
adding
padding
to
the
message
to
make
it
hard
for
charity
and
Isis
for
secrecy,
as
explained
earlier
so
means
if
an
attacker
have
access
to
all
the
encrypted
traffic
and
current
key
material,
they
should
not
be
able
to
decrypt
message
orders
and,
as
all
this
key
the
attacker
have,
and
what
school
and
security
it's
the
other
way
around.
I
So
if
an
attacker
has
stuck
in
existing
key
material
at
time,
T
and
this
key
material
oblivia
time,
T,
prime,
that
data
will
not
be
able
to
decrypt
any
message
of
such
a
boring
group
membership
security.
So
only
all
client
should
have
the
same
view.
Group
member.
They
could
use
like
something
like
my
batteries
or
cheese's.
Something
like
that
added
client
should
not
be
able
access
previous
message
before
joining
the
group
and
same
for
remove
the
client.
We
should
never
access
to
the
message
after
delay.
I
Attachment
security
should
have
the
same
properties
for
messages
except
the
encryption.
T
key
through
the
attachments
tends
to
have
longer
life
time
because
of
the
bandwidth
your
chance
to
download
this
later,
so
they
might
have
a
weak
or
pcs
property.
This
origin
authentication
this
means
no
other
client,
can
impersonate
any
other
client
in
the
conversation.
So
I
ask
consent
messages
that
please
come
from
Bob.
I
This
will
require
adding
a
signature
for
your
message
and
another
asterisk
is
deniability,
so
it's
very
painful
so
I
know
so
it
Emily
specifically
explained
it
doesn't
require
the
nobility,
but
so
particularly
container,
which
there
are
four
camps.
First,
camp
I
don't
understand
the
ability
and
I
don't
care,
which
is
easy.
Second
camp
I
understand
the
reality,
but
live
don't
work.
This
way
all
I
need
to
do
is
just
a
screenshot
of
the
application
to
prove
the
sender
of
the
message.
Still
easy,
sir
camp
is
the
object
of
the
nobility
I.
Don't
need
deniability
I.
I
Think
I
need
a
clip
to
prove
for
the
message
center
and
for
scam
with
people
who
really
really
care
about
the
narrative.
You
think
it's
awesome.
We
can't
live
without
it.
So
it's
a
hard
to
make
everyone
happy,
but
should
be
great
of
support
to
cult
and
optionally
support
innovative.
This
will
come
up
with
the
cost
by
exchanging
so
we
can
find
by
using
identity
anymore.
So
if
the
durability
mode
is
on,
this
means
we
have
to
every
user
has
to
change
new
signature
keys
over
then
I
will
channel
yes,
yes,.
N
Maybe
it's
too
early
to
discuss
this,
but
just
stop!
Oh
sorry!
Yes,
your
I've
been
complaining
about
people
not
doing
that,
because
I
can't
note
it
down
so
you're,
absolutely
right,
I'm
the
demco
DC
from
INRIA.
So
on
the
previous
slide
you
mentioned
versioning
and
I
am
afraid
it
might
be
too
early
to
discuss
this,
but
we
should
probably
just
have
it
in
our
minds,
so
there's
versioning,
which
is
good,
but
at
the
same
time
we
seem
to
be
adopting
versioning
and
cipher
suites
at
the
same
time
in
the
protocol,
because
we
have
versioning.
N
But
at
the
same
time
we
also
have
curve
two
five,
five
one
nine
and
p25
six
and
we
can
choose
between
the
two
as
my
understanding
correct
in
the
Congrats.
Yes,
so
it
seems
that
it
might
be
wise
to
attempt
to
limit
the
amount
of
state
malleability
and
maybe
only
rely
on
versioning
in
terms
of
which
ciphers
are
adopted
instead
of
having
both
versioning
and
also
within
the
same
version.
The
ability
to
switch
between
multiple
ciphers,
especially
because,
for
example,
curve,
255
or
nine
does
not
require
input.
Validation
for
diffie-hellman,
while
P
256
does.
I
I
It's
too
early
to
ask
I
will
do
with
this
omission.
Okay.
Next
one
beats.
Oh
ok,
security
consideration.
It's
a
good,
bad
and
ugly,
so
delivery
service
compromise.
This
should
be
good
because
the
server
should
not
be
able
to
decrypt
or
access
any
of
the
messages.
However,
it
can
try
to
modify
or
alter
the
message,
but
the
protocol
should
be
able
to
take
this
and,
of
course,
you
can
always
do
gos
attacks.
I
Okay,
the
bad
education
service
compromise.
This
will
can
return,
because
this
is
there
because
it
can
return
in
credential.
This
will
allow
impersonations
and
can
only
be
defeated
by
the
guy,
who
is
going
to
ask
the
biggest
questions
or
transparency
logging,
which
is
a
key
transparency.
The
obvious
client
cover
wise,
because
the
attacker
can
actually
read
and
read
accusing
message
and
send
receive
messages.
However,
it
should
not
be
able
to
do
is
the
server
old
peers
and
this
would
be
defeated
once
the
key
material
is
updated.
F
So
this
is
TKG
Union,
so
this
is
description
of
what
we
expect
the
attacker
to
be
able
to
do
right,
but
my
understanding
is
that
this
draft
does
not
attempt
to
define
the
actual
delivery
service
mechanism
or
the
authentication
service
mechanism.
Is
that
right
or
do
we
also
intend
to
define
a
specific
education
service
mechanism,
or
do
we
just
say,
I
think
as
as
the
earlier
slide
deck
said,
clean
interface
goes
here,
you
know
figure
it
out.
For
yourself,
are
we
trying
to
actually
specify
what
that
interface
is?
I?
Think.
E
Yeah
I
think
that's
right.
You
cagey,
we
are
trying
to
I
think
this
dog
was
trying
to
capture
a
high-level
description
of
the
universe
of
possibilities.
When
we
get
to
specification,
we
won't
try
and
specify
the
all
the
parts
of
that
universe
will
need
it
that,
as
you
said,
the
technical,
clean
interface
to
the
authentication,
part
and
I
think
is
Gary
is
probably
gonna
say
we
might
highlight
the
need
for
certain
other
mechanisms,
in
addition
to
just
an
authentication
service.
So.
F
F
G
J
I
P
P
So
this
protocol
is
based
around
something
called
asynchronous
ratcheting
trees
and
the
idea
is
that
every
participants
in
the
conversation
will
have
some
view
of
this
tree
which
their
cache
client
site
and
then
they're
a
series
of
operations
which
essentially
mutate
mutate
the
tree
and
thus
mutate
to
the
overall
conversation
state
and
so
we'll
go
into
these
in
more
depth.
But
these
are
some
fairly
obvious
ones:
creating
groups
adding
users
updating
keys
less
obvious,
but
this
is
for
the
forward
secrecy
and
post
compromised
security
and,
of
course,
removing
people
from
conversations
it's
like.
P
P
The
tree
can
be
manipulated,
asynchronously
and
we've
actually
proven
the
confidential
confidentiality
of
group
keys
just
for
static
routes.
So
far,
so
there
is
more
work
to
be
done
on
this,
but
it
we
have
enough
proofs
to
be
fairly
confident
that
hits
a
roughly
solid,
primitive
and
so
in
MLS
we
draft
so
far,
we've
taken
it
a
bit
further.
P
So
we've
constrained
the
story
structure
a
little
more
we've
added
support
for
dynamic
groups,
so
that
you
can
add
and
remove
members
and
we've
sort
of
tried
to
look
a
little
at
race
conditions,
although
that's
fairly
embryonic
work
at
the
moment.
Next
slide,
please
so
to
just
give
some
intuition
about
how
this
works.
It's
essentially
the
fact
that
you
can
derive
a
different
key
pair
from
some
random
string.
So
as
the
output
opport
iffy
Hellman
key
exchange
is
a
random
string,
you
can
use
that
to
form
a
different
key.
P
So
with
respect
to
C
here,
we've
highlighted
the
direct
path,
which
is
just
the
sequence
of
ancestors,
from
C
up
to
the
root
key,
the
root
being
the
one
node
which
has
no
no
ancestors
the
root
by
the
way
is
used
as
to
provide
the
group
secret,
which
is
used
for
protocol
keying
material.
The
co
path
is,
then
the
sequence
of
siblings,
of
the
path.
P
Apart
from
the
root,
of
course,
which
has
no
sibling
so
for
C.
Here
this
is
D
a
B
and
D
F
G
H.
Then
we
also
have
the
frontier
of
a
tree,
and
the
idea
here
is
that
to
add
someone
to
a
tree,
you
need
to
actually
add
a
new
node
and
what
you
need
to
compute
their
path
up.
The
tree
is
their
their
key
itself
and
their
co
path,
and
so
the
frontier
provides
the
co
path
for
a
hypothetical
new
node
that
will
be
added.
That
may
be
added
at
some
point
in
the
future.
P
So
creating
a
group
given
a
list
of
members
that
there
is
probably
an
option
to
create
this
directly.
But
in
the
draft
so
far,
we've
essentially
treated
this
as
initially
starting
with
a
single
leaf
and
composing
a
series
of
ads
in
the
paper.
We
actually
do
define
how
to
create
a
group
directly,
so
this
should
be
fairly
easy
to
implement
into
the
drafts
and
there
are
performance
reasons
to
do
it
that
way,
but
either
way
we
have
something
which
should
work
in
theory.
P
Next
slide.
Please
so
next
option
is
that
what
we
call
the
group
initiated
ad?
This
is
the
operation
whereby
someone
within
the
group
wants
to
add
someone
else,
and
so
what
we
need
here
is
what
we
call
the
user
init
key.
These
are
also
may
be
familiar
to
some
of
you
as
pre
keys,
as
termed
in
the
signal
protocol.
P
It's
like
so
the
next
operation
is
the
user
initiated
at
so
this
is
motivated
by
use
cases
such
as
conversation
invitation
links.
So,
where
I
want
to
add
you
to
the
group
but
I,
don't
necessarily
have
your
account
in
the
service,
so
I
just
send
you
a
link
which
allows
you
to
add
yourself
to
the
group,
and
what
we
have
here
is
another
difficulty
known
to
the
whole
group.
This
is
actually
the
same.
P
Add
key
that
we
had
before
sorry,
ok,
which
the
witch
kept
which
camp
can
be
used
to
initiate
this
new
person
into
the
group,
and
then
they
can
use
the
the
published
frontier
of
the
group
as
their
new
Co
path
to
compute
the
new
state
of
the
tree
and
then
publish
that,
and
in
this
instance
they
have
to
publish
their
entire
path.
No.
J
E
In
fact,
the
the
concrete
reason
why
this
got
added
to
the
protocol
was
I
was
trying
to
implement
this.
In
the
context
of
missing
you
gap,
it
was
like
Waldo,
I
do
and
I
get
a
new
device,
so
yeah,
that's
the
same
thing.
So
it
is
you
pre,
publish
this
group
in
it
key
that
represents
the
group
state
for
new
potential
new
users
and
then,
when
someone
new
pops
up
the
wants
to
join
the
group,
they
just
download
that
and
initiate
themselves
into
the
group.
Now.
There's
authorization
concerns
around
that
and.
P
And
whether
the
application
chooses
to
use
this
feature
can
be
down
to
the
can
be
application.
Specific
okay
next
slide,
please.
So
the
next
point
is
just
updating
your
own
key,
so
not
mutating
the
people
within
the
group,
but
just
updating
your
owns
secrets
so
that
we
can
get
post
compromised
security,
and
so
this
is
very
similar
to
the
previous
operations,
but
involves
changing
your
own
leaf,
probably
a
new
random
value
and
then
calculating
your
new
paths
and
publishing
that
path.
P
P
So
the
next
part
is
removing
a
user.
There
is
a
lot
of
nuance
involved
in
this,
but
fundamentally
it
is
possible
to
simply
issue
what's
effectively
update
operation
for
someone
else
in
the
group
to
a
key
that
they
do
not
know,
publish
that
new
path,
and
then
at
that
point
they
cannot
compute
the
root
of
the
tree
because
they
do
not
have
leaf
or
a
private
leaf
key
and
thus
are
locked
out
of
the
group.
Of
course,
publishing
a
new
key
for
somebody
else
now
means
that
you
know
their
key
in
the
tree.
P
P
P
There
are
a
lot
of
logistical
details,
particularly
with
removing
people
from
the
group,
as
I
mentioned.
We
really
don't
want
situations
where
somebody
knows
other
private
keys
in
the
group,
as
it
makes
it
very
difficult
to
then
remove
them
from
the
group.
So
we
need
to
iron
out
exactly
how
that
should
work
message.
Sequencing
is
obviously
a
fairly
big
issue,
because
we
need
to
make
sure
that's
conflicting
updates
to
the
tree,
don't
kind
of
cause
split
in
the
state
and,
of
course,
message,
protection,
authentication,
transcripts
integrity.
P
The
current
authentication
scheme
in
the
paper
is
pretty
similar.
We
need
to
elaborate,
particularly
with
respect
to
deniability,
with
many
asterisks,
as
mentioned
in
the
previous
talks,
and
we
also
may
want
to
include
some
discussion
of
how
attachment
should
work
as
typically.
These
are
not
sense
within
the
core
messaging
protocol,
but
centers
references
to
some
attachment
stored
elsewhere.
J
P
D
E
So,
just
to
clarify
I'm
Phil's
question
of
what
keys
we
expect
participants
to
have.
We
assume
that
there's
basically
two
key
pairs
per
participant,
there's
an
identity
key
pair.
That's
long
lived
in
used
for
authentication
and
there
is
a
leaf
key
pair
which
is
used
to
contribute
to
the
group
key
for
confidentiality,
which
is
short
lives.
It
changes
whenever
you
send
an
update
message
for
pcs.
Q
A
question
I
couldn't
really
quickly
see
this
from
the
draft,
but
Karthik
Raghavan
indriya.
So
the
question
is
I'm.
Assuming
that
people
will
be
members
of
multiple
groups,
so
can
they
reuse
their
same
identity
key
in
different
trees,
the
same
diffie-hellman
keys
in
different
trees?
How
does
that
work
so.
P
Identity
keys,
we
would
probably
expect
to
be
kind
of
universal.
Of
course
they
come
patience.
This
is
what
you
would
store
and
authenticate
by
the
authentication
service
or
key
transparency,
the
leaf
keys
within
the
conversation.
We
were
thinking
of
being
different
for
different
conversations.
If
we
wanted
them
to
be
the
same
I'm
sure
that
would
be
a
fun
challenge
for
you
to
approve
security
properties
of
apps,
but
we're
not
assuming.
R
E
E
Get
encapsulation
schemee,
like
I,
think
the
idea
was
in
order
to
get
a
reasonably
complete
functioning
here
when
we
were
chatting
among
the
folks
who
had
apps,
everyone
had
done
some
sort
of
attachment
scheme
because
we
all
have
you
know,
constraints
on
the
messaging
plane,
and
so
the
thought
was
it
might
make
sense
to
take
a
look
at
clarifying.
That's
we
could
have
some
analysis
or
basically
well.
G
Ericka's
crawler
being
just
a
labrum
that
I
think
the
sense
was
that,
as
Richard
said,
it
was
relatively
straightforward
once
hit
a
shared
key
to
build
a
messaging
app.
But
that
then,
if
you
wanted
to
have
attachments
that
was
not,
as
a
movie
straightforward
how
to
build
that
and
that
people
had
sometimes
built
in
ways
that
were
not
optimal.
And
so
that
therefore,
were
describing
how
to
build.
It
was
probably
a
contribution
and.
S
T
P
M
P
In
in
theory,
this
general
operations
should
be
asynchronous,
so
you
should
be
able
to
just
have
a
list
of
operations
which,
when
someone
comes
online,
they
fetch
them
and
they
are
able
to
update
themselves
to
the
new
state
at
the
group.
Okay,
in
terms
of
two
people
doing
conflicting
operation
same
time,
based
on
kind
of
based
based
on
the
same
state,
doing
different
things.
That's
sort
of
an
open
issue,
yeah.
M
J
P
P
N
E
L
P
So
it
does
mean
that
if
at
one
point
your
tree
contained
50,000
people
and
now
it
and
after
some
sequence
of
removals,
it
now
only
contains
two.
Then
you've
got
a
pairwise
group
with
the
tree
depth
of
16,
which
we
I
mean
tree.
Depth
of
16
is
still
computationally
feasible
and
most
situations,
but
it
is
suboptimal
and
we
basically
consider
that
it's
a
fairly
unlikely
scenario
to
be
I
do
but.
C
D
U
Is
it
in
scope
to
be
thinking
about
our
bank
a
duck?
Sorry!
Is
it
in
scope
to
think
about
the
forward
secrecy
of
messages
generated
by
a
client
that
is
offline
racing
with
removal
from
the
group
so
that
you
know
the
generated
messages
would
be
generated
to
a
key
that
is
known
by
the
member
that
is
getting
deleted.
P
Think,
probably
out
of
scope,
at
least
so
far
as
now
and
I.
Think
I
think
it's
reasonable
to
consider
that
if
a
client,
if
a
client,
believes
that
someone
is
in
the
group
at
the
time,
it
sends
a
message.
It
is
reasonable
for
that
person
to
receive
the
message,
but
that's
probably
a
sort
of
fine
point
to
discuss
later
eius.
V
So
half
of
us
used
orange
and
half
of
us
used
green,
so
apologies
to
your
retinas,
so
I'm
cat,
Rio
I'm
from
Oxford
I'm,
basically
here
to
say
hi
I
am
an
academic.
So
far,
there's
a
few
of
us
around
we're
interested
in
working
on
this.
It
seemed
to
work
pretty
well
for
TLS
right,
so
we
hope
we
can
do
similar
sorts
of
things.
However,
since
I
don't
very
often
get
to
represent
all
academics
ever
at
the
IETF
I'd
also
like
to
say,
let's
see,
Julie
fee
was
great.
Mls
visibility
draft
is
coming
soon.
V
V
There's
a
fair
amount
of
experience,
so
Karthik
you
already
heard
from
if
you
are
outside
this
morning
afternoon,
works
on
TLS
Kass,
who
is
my
supervisor
also
worked
on
the
TLS
analysis,
Benjamin
who's
sitting
there
F
star
NFS,
so
we
have
some
experience
looking
at
protocols,
although
there's
a
bunch
of
new
and
interesting
challenges
in
the
messaging
context
that
you've
heard
about
that,
we
look
forward
to
looking
at
if
is
related
to
project.
Like
my
PLA
life,
1.3
work,
the
5g
work,
my
fellow
student
Martin
was
working
on
and
so
on.
V
Next
slide,
please
right
so
just
to
give
you
an
update
on
what
an
alpha
they've
been
so
far,
so
John
put
up
a
link
to
the
end-to-end
encryption
paper
which
we
wrote
a
few
months
ago
and
that
really
defines
the
ratcheting
3
primitives
that
you've
got
an
intuition
for.
So
if
you
want
more
formal
definitions
that,
if
you
enjoy
reading
conference
paper
formats,
you
can
check
their
write
in
that
paper,
we
spend
a
fair
amount
of
time,
looking
at
security
properties
and
looking
at
them
fairly
formally.
V
V
We
did
to
sort
of
separate
things
so
there's
a
key
tool
you
can
think
of
as
it
were,
which
is
the
ratcheting
trees
and
the
first
thing
we
did
is
we
abstracted
away
from
the
concerns
that
people
here
will
really
be
interested
in
things
like
message
formats,
dynamic
groups,
how
you
add
people
what
exactly
it
means
to
add
people,
how
you
deal
with
race
conditions
and
so
on.
We
abstracted
away
from
that
a
little
bit
and
just
looked
at
the
core
cryptographic
primitive.
V
This
is
unauthenticated
for
now,
and
we
gave
pen
and
paper
cryptographic
proof
which
is
a
security
reduction,
so
we
would
use
for
security
of
that
to
the
diffie-hellman
a
function.
This
is
a
fairly
standard
proof
technique
that
it
has
its
pros
and
it's
cons,
but
that's
what
we
did
and
that's
really
looking
at
the
core
ratcheting
trees.
Of
course,
that's
not
nearly
enough.
If
you
actually
want
this
to
be
secure
or
usable,
you
also
need
to
make
guarantees
like
if
I
remove
somebody
from
a
group
and
then
send
a
message.
They
didn't
get
it.
V
If
the
group
has
people
added
to
it,
then
you
have
forward
secrecy
in
the
way
if
you
are
hearing
about
earlier.
So
the
other
thing
we've
started
to
look
at-
and
this
is
very
early-
work
is
doing
symbolic
analysis
using
mechanized
tools,
so
we
looked
using
the
tamarind
mover,
but
I
hear
there
was
also
probe
arif
work
happening,
perhaps
even
right
now,
depending
what's
on
that
computer
screen
next
slide,
please.
V
So
what
do
we
want
to
contribute
going
forward?
We
have
some
formal
definitions
of
fairly
low
level
properties,
we're
going
to
want
to
provide
very
precise
definitions
of
all
the
properties
you
saw
earlier
and
if
includes
things
like,
if
you
have
a
state
recovery
mechanism
for
I
dropped,
my
phone
in
the
toilet,
but
honestly
I
really
want
to
be
in
this
group.
Please
put
me
back
in
the
interaction
of
that
with
confidentiality
is
subtle,
but
we
think
you
can
express
it.
You'll
want
something
like
well.
V
You
got
told
that
this
person
is
claiming
that
they
have
lost
their
device.
You
can
deal
with
that
as
you
will,
but
we
can
encode
that
into
a
formal
property
we
one.
We
ideally
want
the
properties
here
to
be
fairly
general.
We
don't
want
to
hard-code.
This
is
how
whatsapp
would
use
it,
but
again
that
should
be
fine.
V
So
hopefully
that
will
be
an
easy
addendum
to
all
of
this
as
well.
Next,
like
this,
that's
about
it
so
really
I,
don't
have
much
to
say
at
the
moment
other
than
we're
interested
in
analyzing
things.
We
hope
to
follow
the
TLS
process,
so
we
hope
that
drafts
will
be
posted.
That
we'll
be
able
to
pick
one
make
some
comments,
maybe
make
some
comments
for
help
and
help
the
protocol
analysis
and
yeah
we're
working
on
it
and
we're
still
going.
Q
Berlin
India,
so
one
thing
I'd
like
to
mention
here
is
that
I
mean
things
like
post
compromised
security
and
forward
security,
its
forward
secrecy
and
so
on
are
properties
that
sort
of
this
part
of
protocol
proofs
and
protocol
verifications.
We
understand
them
quite
well,
so
we
state
them,
but
they
may
actually
not
be
the
most
intuitive
ways
in
which
application
developers
and
the
people
are
actually
going
to
use
MLS
may
want
to
think
about
the
security
goals.
Q
V
Is
particularly
true
in
the
group
context
where,
if
you're
very
used
one
to
one
messaging
or
one
to
one
communications
like
TLS,
it
turns
out
there's
a
whole
lot
of
other
funny
properties.
The
pop
up
when
you're
worrying
about
say
three
people
in
a
group
a
simple
example:
there
is,
if
you
have
a
shared
key
with
one
other
person,
then
if
you
get
a
message
encrypted
under
that
key,
you
know
they
sent
it.
B
B
I
R
Matthew
Hobson
again
from
matrix
to
oak
I,
think
we
were
one
of
the
prior
art
mentioned
on
Richard
slides.
Thank
you
on
the
ohm
and
Meghan
ratchets
that
we
did
encrypt
so
is
pluggable
in
matrix
as
a
decentralized
communications
protocol,
I,
guess
addressing
a
similar
problem,
but
the
next
layer
up
the
stack
at
the
application
level
and
is
certainly
interested
in
MLS
as
a
successor
to
the
army
mecca
and
stuff
we're
doing
today.
R
S
N
I'd
also
like
to
the
grant
so
I'm
Nadeem
Cove,
a
CI
responsible
for
cryptic
at
but
I'm
also
I've
been
working
on
this
on
secure
messaging
for
eight
or
nine
years.
This
is
something
that
has
grown
from
like
a
niche
experimental
thing
to
affecting
the
most
immediate
way
that
billions
of
people
communicate.
We
need
a
standard
on
this.
We
need
something
open.
We
need
something
that
can
be
absolved
of
any
sort
of
human
notion
on
whether
we
get
to
implement
it
or
not.
To
me,
this
is
existential
and
I
would
like
to
see
it
happen.
C
That's
to
all
the
people
that
the
reception
that
they
said
well,
we
try
this
before
and
it
didn't
work
who's
here
all
right.
So
now
we're
ready
for
some
I
charted
the
Charter
that
was
posted
to
list.
There
happened
some
comments
and
they've
been
amended.
It's
at
least
four
slides
and
sixteen
point
five.
So
as
we
walk
through
this.
Y
B
Well,
we
will
read
it
through
and
if
there
are
specific
comments,
we
want
to
be
very
clear
as
to
what
the
correct
charter
text
is
and
whether
or
not
there
are
questions
okay,
so
the
first
one.
So
several
internet
applications
have
a
need
for
group
key
establishment
and
message
protection
protection
protocols
with
the
following
properties.
Asynchronicity
keys
can
be
established
without
any
two
participants
being
online
at
the
same
time
forward
secrecy.
Full
compromise
of
a
node
at
a
point
in
time
does
not
reveal
past
root,
keys,
post,
compromised
security.
B
Full
compromise
of
a
node
at
a
point
in
time
does
not
reveal
future
Group
group
keys
membership
authentication
each
participant
can
verify
the
set
of
members
in
the
group
message.
Authentication
each
message
has
an
authenticated
sender,
scalability
resource
requirements
that
have
a
good
scaling
that
have
good
scaling
in
the
size
of
the
group,
preferably
sublinear.
M
S
L
And
Schwartz
this
is,
this
is
definitely
equivalent
of
a
node
does
not
reveal
future
group
keys
works
for
some
definition
of
fault
compromise
that
is
read-only.
If
you
can
modify
the
client,
then
you
can
have
it
tell
you
everything
in
the
future.
Is
that
your
your
definition
of
full
compromises
a
little
weaker
than
mine,.
B
Z
U
Benkei
Nook
wearing
the
ghost
of
my
ace
working
group,
chair
hat,
so
the
text
up
here
at
the
top
about
new
group,
key
establishment
and
message
protection
is
perhaps
more
general
mark
than
you
want
in
that
over
an
ace.
We've
had
some
very
contentious
discussions
about
keying
for
a
groupie
establishment
for
IOT
messaging,
which
I
assume
you
do
not
want
to
bring
here.
The.
D
Home
baker,
the
men,
bishop
authentication
I'm
pretty
sure
that
if
I
have
a
group,
that's
larger
than
a
thousand
people
I'll
be
wanting
to
keep
the
group
membership
confidential.
So
I'm
not
sure
that
that
is
actually
a
requirement.
That
is
a
feature
of
the
protocol
architecture
you
chosen
rather
than
something
that
everybody
is
always
going
to
require.
The
other
thing
I'm
a
bit
concerned
about
is:
if
we
don't
actually
do
any
form
of
Interop
testing.
C
AA
E
We're
gonna
will
far
afield
but
to
Phil's
point
about
interrupt
testing.
I
would
say
you
you
would
do
MLS
and
are
out
testing
like
you
do
TLS
in
are
out
testing.
It's
not
it's
tied
to
a
given
transfer,
you're
gonna
to
us
in
our
testing
over
TCP,
and
you
know
you'll
verify
you
can
pass
some
data
over
it,
but
what
you're
really
testing
out
is
that
is
the
key
negotiation
in
encryption.
C
Alright,
thank
you
for
taking
notes,
whoever's
taking
note,
so
we
can
put
the
second
here's
slide
to
several
widely
deployed.
Applications
have
developed
their
own
protocols
to
meet
these
needs.
All
these
protocols
are
similar
note.
You
are
close
enough
to
interoperate.
As
a
result,
each
application
vendor
has
had
to
maintain
their
own
protocol
stack,
can
independently
build
trust
and
the
quality
of
the
protocol.
The
primary
goal
of
this
working
groups
develop
a
standard
messaging
security
protocol
so
that
applications
can
share
code
and
so
that
there
could
be
shared
validation
of
the
protocol
cuz.
C
It
was
with
TLS
before
3.
It
is
not
a
goal.
This
group
to
enable
interoperability
between
messaging
applications
beyond
the
key
establishment,
authentication
confidentiality
services,
so
our
ability
would
require
alignment
in
many
different
layers.
Beyond
security
example,
standard
message,
transport,
an
application
semantics,
the
focuses
as
work
is
to
develop
a
messaging
security
layer,
that
is,
that
different
applications
can
adapt
to
their
own
needs.
C
Had
probably
introduced
that
all
right,
so
I'll
just
read
the
next
one
too
and
developing
this
protocol,
we
will
draw
the
lessons
learn
from
several
prior
message-oriented
security
protocols,
in
addition
to
the
proprietary
messaging
security
protocols
deployed
within
existing
applications.
Some
of
these
include
s/mime,
open,
PGP,
off-the-record
and
signal.
The
intent
of
this
working
group
is
to
follow
the
pattern
of
TLS
1.3,
a
specification,
implementation
and
verification
proceeding
in
parallel
by
the
time
we
arrive
at
RFC.
We
hope
to
have
several
interoperable
implementations,
as
well
as
a
third
thorough
security
analysis.
C
Finally,
note
the
consensus
is
required
both
for
changes
to
the
current
protocol
mechanism
and
retention
of
current
mechanisms
in
particular,
because
something
is
in
the
initial
document
set
does
not
apply.
There
is
a
consensus
around
the
future
or
around
how
it
is
specified
and
then
the
milestones
which
are
pure
bull.
C
So
it's
you
know.
May
2018,
for
the
initial
architecture
to
the
official
group
documents
to
adopt
the
messaging
protocol
mean
if
we're
gonna
do
what
we
did
in
TLS
and
build
in
like
delay
for
the
researchers
to
parent
their
tamarin
proofs
I
normally
slip
all
these
dates
to
the
right.
All
the
2019
days
to
the
right
by
6
months,
if
we're
gonna
add
at
a.
O
C
Think
about
picking
these
dates
is
there
almost
you
watch
it
opens
that
we
start
to
get
nasty
grams
from
our
ad
or
from
the
data
tracking
Center
to
say,
update
these
things
up
these
things.
So
we
can,
if
everyone's
basically
kind
of
happy
with
the
first
two
I,
think
we're
okay
and
then
the
last
three
will
just
add
a
year
plus
I.
G
AB
E
C
B
AC
F
B
F
E
E
B
W
W
Yeah,
okay
yeah,
so
if
I,
if
I
may
sort
of
beg
to
differ
on
that
actually
and
Jonathan
Rosenberg,
so
this
sort
of
interesting
protocol
we're
defining
that
it's
not
actually
meant
to
provide
interoperability
across
different
vendors
products.
So
I
see
like
I
mean
what
would
be
the
point
of
specifying
the
actual
message
protection
technique.
This
was
never
meant
interoperate.
In
my
view.
W
The
main
objective
here
is:
you
know
it
is
to
provide
something
that
has
a
correctness
capability
and
that's
it,
and
so
that
we
can
say
it
works
and
we
can
do
some
testing
against
the
test.
Shim
with
some
implementations.
Just
to
make
sure
it
is.
Yours
is
correct,
but
besides
that,
like
none
of
these
things
are
planning
to
operate
and
so
I
think
we
should
do
the
minimal
amount
that
delivers
correctness
and
no
more.
E
Yeah,
let
me
frame
this
differently,
I
think,
in
order
to
get
something
that
is
sufficiently
detailed,
that
we
can
verify
security,
probably
the
security
properties
were
going
to
want
to
verify
authenticity,
transcript
integrity,
etc.
We're
going
to
need
to
specify
this
whole
you,
you
would
need
to
say
the
message
protection
forum
endless
provide
this
and
this
and
this
and
this
and
this
at
which
point
you
might
as
well
define
a
syntax.
Does
those
things.
D
Phil
Han
Baker
I
I
disagreed
that
I
I
I
think
that
we
can
have
the
output
of
the
Interop.
Honest
simply
be
the
key
values
that
you're
going
to
use,
because
you
know
the
output
of
this
is
ultimately
going
to
be
a
master
secret
that
changes
with
state
changes
to
the
tree
of
members.
The
reason
that
I
would
like
to
keep
this
out
of
this
group
is
that
the
obvious
next
standard
process,
which
will
be
an
app's
process,
will
be
to
propose
a
standard
messaging
format.
I
mean
you
know.
We
are
our
standards
body.
D
The
internet
needs
an
interoperable
messaging
platform,
that's
based
on
an
open
standard
that
anybody
can
set
up
a
server
that
works
like
SMTP,
and
that
is
something
that
the
ITF
should
be
doing.
But
the
fact
that
we
have
this
group
doing
key
negotiation
shouldn't
block
the
apps
area
from
doing
that
part
of
the
task
and
the
fact
that
vendors
would
rather,
we
didn't,
come
to
an
open
standard
shouldn't,
stop
that
either.
G
So
I
guess
I'm
gonna
disagree
with
claim
that
all
we
need
is
the
key
values.
If
you
want
to
provide
treasure
integrity-
and
you
want
to
provide
you
know,
group
integrity,
you're
gonna
need
to
stand
up,
standardize,
I,
specifically
the
contents,
the
messages
and
so
like.
If
people
really
feel
like,
they
don't
want
to
specify
whether
it's
cozy
or
josé
or
CMS,
like
you
know,
I
can
III
guess
we
get
to
find
an
abstract
description
of
what
the
messages
had
to
contain
in
the
messages.
Largely
are
a
ad.
G
G
You
know,
you
know
message
which
services
animation
service
and
similarly,
you
could
say:
well
those
abstract
messaging
service
whose
property
is
it
takes
a
you
know
it
takes
a
key
and
a
bunch
of
metadata
and
you
know
a
and
and
and
some
data
and
it
spits
out
like
a
blob
and
then
on
the
way
in
the
door.
It
takes.
G
R
That's
that's
an
easy,
easy
job
and
you
can
set
up
your
own
server
and
you
can
all
of
us
the
bits
that
the
bits
that
the
XMPP
will
me
and
proxying
from
that
the
apps
world
will
meet
guidance
on
is
its
is
I,
can
tell
you
what
what
format
the
messages
inside
the
encryption
should
be.
I
can
tell
you
what
format
the
messages
outside
the
encryption
should
be.
R
I
cannot
tell
you
in
what
order
to
do
the
signing
or
the
and
the
encryption,
and
nor
would
I
try
to
tell
you
if
you
guys,
if
you
guys
all
say
well,
you
can
negotiate
all
these
keys
and
then
you
do
rot13
or
even
double
rot13
for
extra
security.
That's
fine!
I'm,
just
gonna
go
along
with
that,
but,
on
the
other
hand,
I
do
know
what
needs
to
go
inside
the
messages
I
do
not
do
know
what
needs
to
go
outside
and
how
to
transport
them
around
the
network.
AD
Yeah
matthew,
Miller
I,
think
I'm,
probably
going
to
echo
a
few
of
these
other
ones.
That
I
think
we
can
find
a
boundary
here
on
what
we
need
to
do
that
we
can
come
up
with
interoperable
implementations
as
long
as
we've
got
inputs
and
outputs
that
we
can
collapse
into
a
way
that
we
can
do
an
interoperable
test,
I
think
will
be
I.
AD
Think
will
be
okay
for
what
we're
looking
at
trying
to
do,
and
you
know
whether
that
is
kaze
Jose,
whether
it's
we
start
with
the
tos
structure
and
find
some
mapping
that
works
for
the
testing
framework.
I.
Think
I
think
any
of
those
are
equally
valid
at
this
point.
At
this
point,
in
fact,
I
think
this
is
almost
worth
just
punting
a
little
bit
further
on
and
just
saying
we
will
work
on
something.
AA
:
joins
a.
It
seems
that
we're
debating
almost
a
bike
shed
issue
here,
which
is
at
the
very
bottom
of
our
thing.
We
have
some
stuff
that
falls
out
into
a
container
and
we're
talking
about
whether
we
need
to
define
no
container
an
abstract
definition
can
depict
container
or
point
out
that
this
maps
to
different
containers
and
most
of
the
people
who
set
stood
up
at
the
mic
ten
minutes
ago
or
I'll
going
to
map
this
to
different
containers.
Let's
just
leave
this
this
working
group.
C
W
Just
want
to
be
clear:
I
just
want
to
be
clear
because
I
don't
want
to
miss
it.
Jonathan
Rosenberg
I,
don't
want
to
miss
it
expectations
or
wrong
working
group
members
around
different
goals,
I'm
sort
of
hearing
some
people
want
to
build
interoperable
messaging
implementations,
and
that
certainly
requires
you
to
do
an
extra
layer
of
diligence.
I
mean
even
at
the
core.
How
you
specify
this
thing
when
your
goal
is
correctness
and
not
interoperability
at
any
layer
of
the
system,
is
probably
pretty
different.
W
AC
B
G
B
B
G
E
B
B
W
Rosenberg
I'm,
gonna
sort
of
repeat
my
prior
comment
and
like
since
we're
not
specifying
a
protocol
if
I
want
I
could
build
like
my
application
on
top
of
it,
that,
like
emails,
the
keys
to
everyone
in
the
universe,
I
mean
no
one
will
use
my
app,
but
like
okay
like.
Why
do
we
even
specifying
this
we're.
G
B
M
B
B
D
D
D
D
R
Is
similar
to
Philip
I?
Think
if
you
actually
add
one
word
into
that,
then
it
it
will
stand,
but
without
that
one
word
it
will
fail
and
I
can
give
you
lots
of
common
messaging
applications
where
this
won't
work.
Mailing
lists
won't
really
work.
The
mailing
list
that
we
used
in
the
ITF,
for
instance
those
aren't
entirely
uncommon.
There
are
a
number
of
other
a
number
of
other
cases
message
boards
anything
along
those
lines,
and
these
are
all
asynchronous
messaging
messaging
applications.
R
Well,
okay!
Well,
it
depends
on
how
you
look
at
it
if
you,
if,
at
any
time
your
your
messaging
application,
relies
for
its
utility
on
the
on
access
to
historical
information
for
people,
then
that
fails
now.
Typically
I
describe
those
as
you
either
have
synchronous
messaging
applications
in
as
much
as
you
expect
the
other
person
to
get
the
message
you
know
in
a
timely
manner
or
else
is
asynchronous
where
it's
it's
new.
You
expect
people
to
look
at
messages
out
of
order,
and
you
know
massively
different
massively
different
times.
R
D
E
B
G
G
C
We've
had
a
little
bit
of
debate
here
there,
but
basically
it
kind
of
seems
like
people
have
got
to
the
point
where
they're
like
we're:
okay,
so
we're
gonna
have
a
home
on
that
actual
question.
So
please
I'm
gonna.
Do
it
twice
right,
please
hub
now,
if
please
come
now,
if
you
don't
so,
please
hum
now,
if
you
think
the
problem
statement,
if
the
problem
is
sufficiently
understood.
