►
From YouTube: IETF101-RIFT-20180320-1330
Description
RIFT meeting session at IETF101
2018/03/20 1330
https://datatracker.ietf.org/meeting/101/proceedings/
A
B
Afternoon,
everybody
welcome
to
eat
our
first
meeting
in
London.
We
are
happy
to
start
this
working
group
working
on
new
Internet
source,
novel
routing
protocol
for
data
centers.
We
are
looking
forward
to
working
with
all
of
you
and
welcome
again
so
Jeffrey
and
myself.
We
are
co-chairs
eventually
we'll
be
looking
for
secretary.
B
B
C
B
B
So
agenda
for
today,
so
we
are
going
to
start
with
chairs
barking
and
would
also
like
to
discuss
with
you
approved
shelter
and
next
steps.
So
we'll
have
representation,
motivation,
additional
requirements,
use
cases.
Tony
is
going
to
go
in-depth
on
real
details
and
then
we'll
have
first
presentation
of
yonk
model
and
extensions
for
beer.
B
B
We
are
on
track
with
delivering
one
time,
at
least
so
far,
and
we
would
like
to
hear
from
you
what
does
the
future
work
you'd
be
interested
in
we've
had
quite
some
discussion
on
certain
charging
extensions.
We
kind
understand
how
to
do
them.
I
think
we
also
looked
into
how
to
provide
different
kind
of
resolution
of
next
hub
in
default
route
cases.
So
there's
going
to
be
document
describing
this
another
point
is
beer
and
there's
already
jobs
that
we
are
going
to
present.
E
A
E
This
is
actually
a
you
know,
and
originally
I
rift
was
designed
to
be
a
datacenter
protocol.
This
was
actually
an
attempt
to
look
at
rift
looking
at
specification
and
see
if
it
could
be
adapted
for
other
use
cases
in
one
of
the
use
cases
that
you
know
we
that
I
was
thinking
of
possibly
adapting
it
for
what.
A
E
Use
in
excess
in
access
networks,
so
it
was
designed
to
be
purely
informational.
The
primary
goal
of
this
is
to
actually
evolve
rift
into
the
traffic
has
been
submitted.
It's
you
know
it's
you
know
Kofu.
There
will
be
other
interested
parties
looking
to
adapt
drift
again.
It's
designed
to
promote
drift
for
use
in
general
access
networks
and
not
just
in
data
center
networks.
E
Many
people
call
integrated
fabric
solutions,
possibly
call
for
open
source
projects
and
possibly
just
start
to
get
other.
You
know
open
source
routing
software
stacks.
You
know
they're
involved
in
rest
activities.
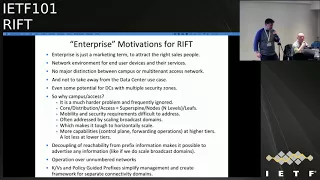
Obviously,
enterprises
in
quotes
it's
a
marketing
term.
I
it
would
be
best
not
to
going
to
debate.
What's
the
difference
between
enterprise
and
not
enterprise,
it's
impossible
anyway.
E
I
just
defined
it
for
the
purpose
of
this
discussion
for
user
access
devices
and
their
services
again,
there's
whether
you
call
the
campus
or
multi-tenant
access
network,
it
doesn't
matter,
it
doesn't
take
away
from
the
data
center
use
case.
You
know
certain
data,
centers,
multiple
security
zones,
meaning
a
people
who
legacy
you
know
legacy
web
environments.
You
know
so
anyway,
by
budget
drift
even
come
up.
It's
a
first.
It's
a
problem,
that's
frequently
ignored
by
many
people.
So
the
way.
Typically,
people
look
at
campus
networks.
E
E
Mostly
a
lot
of
the
requirements
that
exist
in
some
of
these
access
networks
are
addressed
by
scaling,
broadcast
domains,
but
they're
a
little
touchy
horizontally
scale
and
the
one
thing
that
actually
makes
it
a
like
a
good
match
is
the
fact
that
rift
was
actually
very
nicely
designed
as
a
protocol
to
address
the
traverse.
The
situation
in
which
you
can,
with
wisheth
higher
tiers
ie
the
tiers
no
closer
to
the
super
spy
tier.
E
There
are
a
lot
more
control,
plane
and
forwarding
operations
that
can
be
done
in
devices
at
those
tears
than
at
lower
tiers
and
rift
is
actually
very
much
designed
to
address
that.
So
that
made
it
like
a
very
good
match.
Second
of
all,
you
know
bridge
the
coupling
she
ability
from
prefix
information
makes
it
possible
to
advertising
information
like
if
we
do
actually
want.
Just
you
know,
do
broadcast
the
main
scaling
for
some
reason
or
another.
E
We
can
operate
over
number
network,
key
values
and
policy,
guy,
guided
terrific,
simplified
management
framework
for
separate
connectivity
to
me.
So,
obviously,
to
you
know
we
wanted
to
kind
of,
like
you
come
up
with
lists
of
other
requirements
that
could
make
rift
a
good
match
for
some
of
these,
like
network
use
case.
So
first
there's
network
slicing
again
it's
in
quotes
because
difficult
to
define.
Okay,
it's
basically
are
those,
as
you
create
very
short
private
routed.
E
E
Instead
of
so
it
was,
the
goal
was
to
kind
of
like
again.
It
is
a
protocol
for
access
networks
and
the
goal
was
not
to
kind
of
like
you
know,
cheek
habit
follow
the
traditional,
maybe
VPN
model
was
overlay
and
underlay,
but
to
but
you
followed
more
more
of
a
multi
instance.
One
or
a
multi
topology
model,
plus
our
edge
core
model
is
reversed,
so
bringing
a
transport
service
model
would
actually
nullify
most
of
the
benefits
of
rift.
Obviously
the
idea
was
we
improve
on
the
other
discovery
process.
E
Yeah,
we
configured
the
slice
components
we
flood.
So
the
first
kind
of
thing
that
we
wanted
to
maybe
consider
looking
at
is
that
in
a
traditional
in
the
original
specification,
q-value
t-I-is,
which
you
know,
which
means
you
could
say
our
equivalent
of
the
the
other
says,
other
LSP
is
they're,
actually
they're,
actually
going
traditionally
southbound
for
things
like
let's
say
configuration,
the
possibility
was
to
consider
flooding
them.
Northbound
use
the
other
configure
instance
Hades,
possibly
borrow
from
from
their
FCAT
196,
which
is
is,
is
the
configuration
create?
You
know,
create
Network
instances.
E
If
there
is,
you
know
if
there
is
a
if
there
is
something
southbound
what's
installed,
you
know,
dependent
crowd
are
called
in
default
origination,
we'll
cover
that
in
a
minute,
laure
tears
can
explicitly
request
default
information
and
obviously
address
the
biggest
thing.
Is
that
and
that
is
that,
if
we're
going
to
build
a
multi,
multi
instance
network
see
how
we
can
address
the
fact
that
we're
Altima,
you
know
that
we're
designing
this
protocol
to
originate
the
default
downstream
so
effectively.
You
know
we're
creating
a
traditional.
E
E
E
Obviously
there
would
be
separate
nor
there
would
be
separate
northbound,
SPF
and
southbound
SPF
calculation
for
each
instance
no
different
than
in
a
single
instance.
Drift
install
installing
fit
depending
on
what
other
discovery
tells
us
that
it's,
but
it
has
to
be
installed.
We
can
use
obviously
any
tunneling
or
encapsulation
technologies
and
I'm
sure
additional
drafts
will
be.
E
Some
of
the
some
of
the
nodes
would
not
populate
the
ribs
and
propagate
advertisements.
If
there
is
no
need
to
do
so
and
policy
groups
prefixes
are
leveraged
for
policy
control
like
you.
If
traffic
needs
to
be
explicitly
for
word,
that
you
say
security
devices,
scrub,
there's
traffic
shapers
or
other
things
that
may
be
deployed
in
the
traditional
access
network.
So.
E
E
This
actually
may
come
up
if,
if
the
leaves
and
in
other
forms
of
network
boundaries
that
exist
all
around
other
information
exchange
protocols
without
stream
and
downstream
systems,
for
example,
we
make,
of
course
still,
for
example,
running
some
other
stack
and
possibly,
let's
say
bgp
protocol
that
may
exist
some
there
there
could
be
other.
You
know
there
could
be
other
protocols
that
may
be
installed
even
an
end.
E
Another
end
systems
anyway.
There
may
need
to
be
a
possibility
to
flag
some
of
those
prefix
ties
so
that
we
can
differentiate
external
us
so
that
we
can
differentiate
those
external
prefixes,
for
example,
if
we
should
not
be
propagating
them
southbound
some
of
those
prefixes,
maybe
workload
specific,
say,
network.
E
Are
given
two
different
workloads
that
move
around
the
network?
So
that's
where
we
get
into
interesting
problem
of
of
mobility
that
exists
in
access
network
and
and
what
happens
with
some
of
those.
You
know
mobile
workloads,
whether
those
workloads
are
user,
X's
devices,
whether
those
workloads
they're
wireless
devices,
whether
those
workloads
are
potentially
other
mobile
systems.
E
What
what
would
be
a
good?
What
would
be
a
good
ideas
to
address
how
those
were
close
move
around
the
network,
meaning
that,
if
a
particular
network
layer
address
appears
in
one
place
or
another
others
in
the
network,
there
has
to
be
a
way
to
quickly
address
that.
Obviously,
drift
by
its
mechanism
is
designed
to
easily
you
know
easily
provide
to
easily
provide
summarization.
So,
as
you
know,
it
doesn't,
nothing
actually
has
to
be
propagated
in
the
southbound
direction,
but
there's
something
exists
in
one
branch
and
the
southbound
direct
here's
another
branch.
E
The
idea
was
to
possibly
consider
doing
some
kind
of
purge
tie.
That's
designed
to
do
nothing
but
to
go
in
virtually
all
right,
possibly
carrying
a
special
mondo
flag.
That
would
allow
those
ties
to
be
used,
and
then
you
know
and
and
then
and
then
maybe
to
create
other
systems
to
possibly
optimize
in
cash
things
so
that.
E
So
external
connectivity
and
super
spine
connectivity,
so
often
external
connectivity
is
deployed
of
leaf
nodes
should
be
treated
no
differently
than
their
external
drought.
So
the
idea
was
that
the
default
could
be
flooded.
Northbound
of
such
situation
exist,
some
people
will
deploy
special
border
nodes
or
super
spines
will
act
as
border
nodes
and
and
those
can
form
their
own
flooding
to
me.
So
the
idea
was
to
possibly
start
considering
the
you
know,
east-west
flooding,
but
there
is
one
caveat.
This
is
not
you
know.
E
This
is
not
a
request
to
you
know
to
some
culture
and
super
spines
into
your
backbone
or
a
backbone
area
like
if
we
have
distinctive
domains.
That's
you
know,
that's
not
going
to
address
it.
It
is
mainly
to
get
the
external
is
mainly
to
get
the
external
information
deal
with
interconnected
super
spots.
E
Yeah
then,
the
final
in
the
final
requirement
that
may
be
even
more
annoying
see
Tony,
it's
the
and
that's
about
another
very
corner
case
requirements
for
a
daisy-chain
leave
notes.
It's
it's
access
network
use
case.
It's
not
a
datacenter
use
case.
No
one.
You
know.
No
one
builds
data
centers
like
that
anymore
or
really
so
what
actually
happens
is,
and
it
would
only
be
allowed
for
the
leaf
nodes,
and
that
is-
and
that
is
the
level
one
nodes.
It
should
actually
be
level.
Zero
nodes
actually
form
form
a
daisy
chain.
E
It
may
be
in
fiber
constrain
campus
environment.
It
may
be
in
special
environments
where
a
lot
more
devices
are
deployed
to
aggregate
instead
of
getting
central.
You
know
concentration
points
in
this
kind
of
like
reversal,
super
spine
use
case,
except
except
now
it's
southbound
it
is.
It
is
a
deviation
from
original
rift.
Spec,
as
you
know,
stated
by
Tony,
so
northbound
ties
can
go
in
east-west
direction
and
Leafs
leaves
still
run
south
SPF.
Only
you
know
those
go
east-west
in
both
direction
of
the
daisy
chain.
E
No
need
to
get
through
those
to
get
reflected
back
northbound
to
ensure
that
there's
no
disagree,
negation,
loop
and
obviously
you
know
southbound
eyes-
can
never
be
propagated
if
already
learned
from
leaf
that
creates
of
worried
that,
while
that
creates
a
difficult
situation,
but
if,
if
there,
if
this
is
designed,
you
know
and
the
constraint
carrying
set
up
that
should
that
should
make
that
should
avoid.
They
need
to
start
preventing,
east-west
loops
and
potentially
again
utilize,
the
you
know,
perch
southbound
ties
in
both
directions.
E
She
was
draw
still
the
routes
to
optimize
the
convergence
and
you
know
and
then
pretty
much.
Everything
else
is
standard
and
upstream
no,
its
run.
Northbound
SPF
and
you
know
in
purgable
force
all
the
we've
stood
around
southbound
SPF
and
regard
from
the
break
of
the
daisy
chain.
That's
it
so
anyway.
In
the
conclusion,
these
are
some
of
the
possible.
You
know
things
to
consider.
If
riff
riff
could
be
adapted
for
access
networks,
that
was
only
divorced.
F
F
F
F
F
So
one
thing
I
didn't
understand
why
you
think
that
the
default
route
summarization
kills
the
tunneling.
You
know
the
tunnel
endpoints
and
how
it's
get
forwarded
there.
It
doesn't
matter
as
long
as
you
get
to
the
correct
endpoint
and
if
you
use
default
route
to
forward
to
what
you
care
at
the
end,
you
have
your
tunnel
op,
so
I.
E
That's
not
a
problem,
but
if
we
decide
that
but
but
I
guess
the
bigger
product
but
I
guess
the
bigger
problem
becomes.
Is
that
tunneling
is
wanting
building
a
tunnel?
That's
not
a
problem
forwarding
traffic
into
those
tunnels.
That's
another
thing
since
we're,
since
we're
actually
aggregate.
That's
right,
I,
remember
yeah,
since
we're
actually
aggregating
a
default
downstream.
Only
yeah.
G
E
If
we
have
an
edge
device
and
that
edge
device
needs
to
be
able
to
route
to
some
kind
of
to
some
kind
of
route
that
look
that
long
ago
got
summarized,
it
doesn't
actually
know
that
it
needs
to
go
into
that
tunnel.
It
can
certainly
follow
default,
but
when
it
follows
a
default
that
needs
to
land
on
a
super
spying
somewhere
in
the
little
in
and
then
actually
D
and
then
actually
be
routed
somewhere
southbound.
So
that's
actually
kind
of
like
the
concern
about
braking
was
default.
Well,.
B
F
Next
one,
so
one
thing
that
confused
me
and
that's
probably
the
last
comment
that
I
I
make
is
the
mobility
stuff.
So
there
is
nothing
special.
You
need
to
do
if
the
prefix
moves,
the
guy,
who
lost
the
prefix
floods
up
a
new
tie
which
has
no
prefix
and
a
guy
who
got
the
tie
flats
up
in
you
tied
it
has
the
prefix
and
everything
gets
recomputed
automatically.
So
there's
no
need
to
purge
anything
specifically.
You.
E
F
F
F
F
F
Well,
I
mean
the
introduction
says
it
all
right.
What
is
the
precondition
to
read
the
stuff?
Okay,
so
I
think
people
an
idea
at
least
what
kind
of
mechanisms
are
inside,
maybe
even
they
did
in
the
understanding
detail.
So
this
presentation
is
not
necessarily
like
tearing
the
park
how
the
stuff
works
in
detail.
Okay,
but
more
like:
where
do
we
still
need
to
work
to
be
done
and
what
is
kind
of
well
understood
and
needs
to
know
like
precise
pecking
out
so
I'm
kind
of
laying
out
the
landscape?
F
A
F
This
is
kind
of
a
traffic
light
representation
where
we
are
a
rat
is
like
no,
not
attacked
yet
completely
open.
The
green
stuff
is
fairly
well
understood
there.
Really,
you
know,
deep
green
stuff
is
really
well
understood
and
already
Specht
out
and
the
orange
savvy
somewhere
in
between
and
those
are
kind
of,
the
elements
that
represent
the
protocols.
Some
of
the
eruption
on
some
of
them
are
like
basic
mechanisms
so
going
from
the
left.
F
The
whole
thing
is
like
a
mind,
map
right
a
little
bit
just
thrown
out
there
on
purpose,
so
the
formation
of
adjacency
the
lie
rules,
are,
you
know,
that's
really
wellspect
out
in
lot
of
detail,
but
you
know
we
still
I
will
I
will
break
it
down
there.
What
are
the
component
of
each
of
those
and
how
far
are
we
and
what
still
needs
to
be
done?
The
shame
over
the
schema,
versioning
and
sharing
and
possibly
put
doing
the
schema
another
ideal.
F
You
know
like
G
RPC
is
somewhere
in
orange
and
I
think
there's
a
lot
of
interesting
work
that
can
come
out
of
this
working
group
that
will
carry
forward.
If
we
decide
to
build
more
scheme
oriented
protocols,
we
will
face
the
problems
that
we
will
be
facing
here,
like
how
do
you
version
the
schema
right?
It's
the
schema,
separate
document.
What
happened
if
multiple
people
work
at
the
same
time
on
the
schema?
How
do
you
reconcile?
Would
we
rely
on
optional
elements?
F
We
will
have
some
kind
of
a
capability
field
or
we
will
like
periodically
release
like
combined
version.
Those
are
kind
of
unresolved
things
right,
because
we
have
this
kind
of
mandatory
up
indication
like
auntie
Elvis
is
a
mandatory
optional
element.
But
how
do
you
reconcile
all
these
words
into
a
schema
versions
when
I
open
a
protocol
and
appearing
I
know?
Which
scheme
are
we
talking
about?
What's
in
the
schema,
the
route
redistribution,
which
was
a
lot
of
dislike
yen
stuff,
is
kind
of
not
attacked
yet
I
have
some
ideas,
but
nothing
has
been
written
right.
F
So
how
do
you
redistribute
interest
and
how
is
rift
registry
being?
How
is
that
work
in
deployment
scenarios?
An
interesting
thing
is
the
fabric
bandwidth,
balancing
which
came
in
in
2:05
draft
and
I
have
newer
ideas
and
I
will
present
in
details.
What
I'm
seeing
is
requirements?
Rift
seems
to
allow
to
load
balanced
bandwidth
on
the
fabric
without
any
traffic
engineering
in
a
coarse
way
very
cheaply.
F
So
that
looks
like
something
that
appeals
to
a
lot
of
people
who
have
a
lot
of
asymmetric
bandwidth
on
their
on
the
fabric,
because
they're
losing
like
constituents,
the
provision
links
whatever
not.
We
have
to
transport,
which
right
now
is
basically
flooding
over
UDP
and
people
desire
to
run
maybe
TCP,
maybe
quick,
maybe
run
it
over
l2.
The
work
is
possible
there.
F
We
could
do
this
kind
of
stuff,
but
right
now
you
know
there's
basically
one
version,
you
find
the
PGP,
the
PGP
is
written
down
and
there
is
you
know
some
work
on
policies
and
communities
and
so
on.
But
the
stuff
is
still
not
very
firm.
The
flooding
scopes,
the
flooding
reduction,
is
actually
I,
think
quite
well
specified.
F
It
will
need
firming
up,
but
the
problem
is
understood.
Right
I
mean
you
can't
do
much
better
than
I,
as
is
frankly,
the
CTP
is
fairly
well
understood.
The
procedures
are
very
firm
in
the
spec
on
the
the
implementations
and
the
leaf
and
the
open
source
kind
of
like
you
know.
This
is
not
the
traffic
light.
It's
something
that
people
should
attack.
Something
is
happening,
but
not
much.
F
Security
schema
element,
so
I
mentioned
something
about.
How
can
we
make
this
protocol?
The
security
support
easy,
because
link
states
will
start
struggling
with
security
in
a
couple
of
play
and
we
know
the
pain
points,
but
you
learn
the
pain
points
after
the
programs
have
been
designed
and
deployed.
So
I
say
something
about
that
in
more
detail.
So
there's
some
SR
and
beer
support.
That's
something
that
is
optional
sideways
right,
but
those
things
have
been
attacked.
F
Yet,
though,
so
there's
some
beer
work
going
on,
and
there
is
some
talking
about
SR
I'm,
not
convinced
about
the
SR
use
cases
in
the
fabric
right,
so
that's
something
that
maybe
should
be
attacked,
sideways
and
people
talk
about
what
are
the
real
use
cases
and
whether
we
should
support
SR
at
all
the
key
value
stores.
Something
has
been
written
down.
So
that's
in
some
orange
stay,
the
yang
configuration
operational
state
models,
that's
being
attacked,
I
put
it
right,
because
you
know
nothing
has
been
done
until
today.
F
They're
southbound
default,
origination,
I
think,
is
fairly
well
written
down
and
we
understand
it.
You
know,
modular
all
these
desires
of
people
to
support
east/west
links
in
different
ways,
but
this
s,
east-west
link
stuff,
is
delicate
because
the
moment
you
start
to
use
them
by
directionally,
you
start
to
build
loops
and
you
lose
a
lot
of
these.
You
know
loop,
free
properties
of
the
protocol.
There
you
know
quickly.
F
The
moment
you
use
the
loop
free
properties,
lot
of
the
goodness
goes
out,
and
you
start
to
slosh
a
lot
of
topology
information,
different
places
of
the
fabric,
so
also
this
minimal
blast
residue
starts
to
go
away,
but
that's
an
ongoing
discussion.
How
far
we
get
there
I
think
the
requirements
has
been
fairly
firmly
set
down
and
they
didn't
seem
to
like
if
all-father
over
the
last
couple
of
months.
The
automatic
desegregation
is
pretty
well
understood,
but
there
is
a
whole
piece
which
hasn't
been
written
down,
which
I
call
the
transitive
piece.
F
The
computation
is
somewhere
in
between.
So
we
should
write
a
proper
all
paths,
computation,
which
is
not
too
difficult,
but
today
we
basically
put
just
an
SPF
into
the
spec,
because
that
is
something
that
people
grasp
very
easily.
But
what
we
really
should
have
is
all
paths
on
the
fabric
or
Kay
best
pads
on
the
fabric
and
the
BFGS
bas.
F
Bfd
procedures
are
kind
of
decently
well
written
down,
but
that's
also
something
which
is
more
like
an
orange
state
I
consider
like
deep
green
when
we
have
firm
procedures
and
FS
abs
right,
so
an
implementer
can
set
without
thinking
much
just
hack
this
out.
So
this
no
BFD
support
is
not
in
a
green
stage
without
consider
alright,
so
now
I
basically
take
each
of
these
pieces
and
start
to
go
a
little
more
detail
because
I'm
giving
you
less
this
mind,
map
like
what
needs
to
be
done.
Where
are
we
with
the
whole
thing?
F
So
requirement
should
be
possibly
split
in
two
completely
different
document
and
still
being
discussed
out.
I
think
they're
fairly
firm,
but
it's
just
not
part
of
the
protocol
spec.
As
far
as
I
see
it
I
mean
I'm
talking
right
now
about
the
riff
thing,
which
is
like
big
container.
It
had
everything
you
know
carried
in
it.
F
So
now,
let's
talk
about
the
schema,
a
little
more
detail,
the
roundest
schema
management
and
that's
kind
of
larger
than
the
rest
discussion
like.
Will
we
go
towards
something
like
schema
defined
protocols
for
all
the
benefits
we're
getting
will
be
facing
we're
being
faced
with
new
problems
right?
How
do
we
progress
standards
along
something
like
a
schema,
defined
protocol
and
coding
on
the
wire?
So
the
first
thing
is:
how
do
you
version
this
stuff
and
that
I
think
is
like
oranjee?
F
So
we
understand
how
to
version
a
schema
and
things
change
on
a
schema
and
we
can
actually
automate
it
it
fairly.
Well,
I
mean
you
also:
do
it
with
yang
models
and
so
on
so
I
don't
think
there
is
a
lot
of
magic
there,
but
then
we
have
to
ask
ourself.
How
do
we
share
this?
One
schema
when
multiple
drafts
start
to
evolve
in
a
working
group
and
add
elements
right
and
there's
multiple
approaches.
F
You
know
on
this
checkpoint
and
schema
should
probably
be
a
separate
document
from
the
spec
now
support
for
the
schema
language,
because
some
people
are
talking
about
it,
nothing
has
been
done,
can
be
easily
done,
I
mean
you
can
write
it
in
schema
language
of
your
choice.
They
are
not
that
different,
how
much
value
it
represent?
I,
don't
know,
and
a
problem
that's
coming
up
is
that
stuff,
like
thrift
of
G
RPC,
is
not
strongly
standardised
as
we
understand
it
right,
so
they
don't
have
iso
documents.
We
can.
F
We
can
reference
to
and
are
very
stable
the
reference
implementation.
There's
some
documents
you
know,
but
those
are
not
strongly
standardized
things.
So
how
will
we
progress
protocol
spec
if
this
kheema
language
in
itself?
Isn't
it
not
really
well
no
strictly
frozen?
Those
are
kind
of
open
questions
where
we
face.
If
we
go
into
this
direction,
then
there
is,
of
course,
the
idea
of
doing
some
comparison
between
different
schema
languages
and
what
would
be
best
to
actually
implement
you
know
a
scheme,
oriented
protocol
and
so
on.
F
This
is
all
kind
of
larger
than
rift,
but
those
are
the
things
that
start
to
emerge
when
you
start
to
go
in
this
direction,
all
right.
So
where
are
we
on
the
hello
formation
on
the
lies
and
adjacent
information,
so
on
the
FSM
we
have
nothing
written
I.
Did
it
kind
on
purpose?
I
mean
I:
don't
want
to
firm
up
the
protocol
too
quickly,
it
should
be
still
discussed
and
while
when
this
FSM
is
being
strictly
written
down,
a
lot
of
details
may
still
emerge.
So
that's
a
call
to
action.
F
Somebody
can
start
I
provide
the
first
FSM
and
they
start
to
gather
the
procedure
and
write
the
FSM
and
start
to
firm
the
stuff
up.
The
zero-touch
provisioning
negotiation
is
kind
of
fairly
precisely
written
down
and
it
should
sink
into
those
procedures
of
the
FSM
in
the
actions
on
the
FSM
transitions
and
we
have
security
hooks.
So
that's
orange
right.
F
F
Alright,
so
transport
again,
a
bunch
of
things.
So
the
UDP
transport
is
pretty
well
defined.
Okay,
that's
not
the
hard
things
that
we
basically
flood
over
UDP
and,
of
course
that
marries
a
discussion.
So
we
don't
have
an
l2
snap,
we
don't
have
an
l3
IP
protocol.
I,
do
not
consider
the
desirable
direction
from
you
know,
having
learned
what
that
all
means
in
terms
of
implementation,
so
I
consider
the
UDP
for
data
center
use,
which
is
what
I'm
aiming
at
good
enough,
and
it
has
a
lot
of
very
elegant
properties
like
a
normal
time.
F
Situation
is
almost
trivial,
but
maybe
we
should
be
doing
other
things
and
in
a
sense,
rift
has
been
laid
out.
That
is
agnostic.
So
when
you
build
the
adjacency,
you
could
negotiate.
You
know
what
you
flock
over
well
flood
over
TCP.
If
your
neighbor
supports
that
it's
a
lot
of
value-
I
don't
know,
but
those
are
indeed
the
things
on
the
table,
so
we
don't
have
the
TCP
support
and
right
now
we
don't
have
this
transport
security.
We
just
have
the
hooks
and
how
far
should
we
take
the
transport
security?
F
We
have
all
those
discussion
from
the
security
area
coming
out
like
do.
We
need
confidentiality
and
routing
protocols
and
I
don't
have
the
answer
but
I'm
just
saying
that's
like
an
orange
area.
Right
hooks
are
in
some
studies
here.
How
far
should
we
take?
It
should
know
who's
willing
to
work
on
all
right,
so
ties
and
flooding.
So
here
it
gets
interesting,
so
the
flooding
percentage
copes
and
the
procedure
is
pretty
well
understood.
It's
all
stolen
from
aya,
sighs
I
mean
the
Scopes
are
novel,
but
you
know
otherwise,
flooding
is,
is
pretty
much
nailed.
F
You
know
what
can
be
done.
We
don't
have
cross
the
final
state
machines,
the
finite
state
machines
in
the
procedure.
So
that's
something
that
could
be
poured
in
concrete
nicely
right
to
make
it
like
a
grown-up
spec
and
when
we
start
to
serialize
and
deserialize
and
especially
start
to
talk
about
purity,
we
start
to
observe
that
we
can
do
things
that
we
did
with
flooding
on
the
traditional
protocols
better.
F
So
what
we
really
want
is
to
take
somebody's
flooded
packet
and
use
the
binary
form
without
even
this
surge
deserializing
in
serializing,
and
what
forces
us
to
deserialize
and
serialize
are
basically
in
case
of
tie
the
lifetime
right.
That's
where
we
always
struggle.
So
we
have
this
funky
checksum
that
don't
protect
it,
and
then
we
have
this
binary
form.
We
always
flip
the
lifetime
and
then
push
it
forward.
Now,
if
you
serve
this
sir,
you
cannot
take
a
serialized
version
of
the
model
and
say:
oh
I
know
where
the
offset
is
of
this
field.
F
Let's
flip
it
on.
So
you
have
to
deserialize
change
the
life.
That
means
you
realize
this
is
tricky
in
a
couple
of
ways,
because
you
see
realize
I
may
produce
another
form,
which
is
perfectly
valid.
So
I'll
give
you
an
example.
If
you
have
an
optional
element
with
the
default,
I
may
receive
this
element
being
omitted
in
the
encoding
when
I
deserve
it.
My
deserializing
may
choose
to
insert
the
element
with
the
d4
value,
so
when
I
serialize
it
I
get
a
different
binary
right.
F
So
ideally,
I
want
to
just
propagate
the
binary
versions
and
I
have
to
take
the
lifetime
out
so
I'm
thinking
that
there's
some
laser
thing
here
that
stuff
that
we
basically
need
to
frame
serialize
object
to
do
routing
well
into
its
own
envelope,
which
holds
multiple
things.
So
let's
say
we
do
it
over
UDP
header,
but
it
really
doesn't
matter
some
kind
of
transport
and
we
want
to
take
the
security
fingerprint
out
of
the
packet
right.
F
So
here's
a
security
fingerprint,
so
we
basically
say
I
may
have
a
security
fingerprint
I
have
some
length
which
indicates
I
have
a
security
fingerprint
which
comes
later,
which
is
a
sha
which
protect
this
whole
thing.
The
object
plus
something
I'll
talk
about
and
the
tie
lifetime.
We
never
show
them
right
today.
F
They're
like
this
funky
thing
like
set
them
to
zero
and
then
compute
the
checksum
and
dollar
load,
or
do
a
lot
of
you
know
funky
stuff,
we
actually
shouldn't
even
have
it
in
the
serialized
object
in
the
tie
that
that
should
be
carried
on
the
envelope.
So
when
I
get
something
like
this
I
can
there's
very
easily
just
update
the
tie
lifetime
and
just
push
it
out
the
box
again,
I
don't
have
to
touch
the
shower
or
anything
or
any
of
this
utilized
object.
I
don't
even
have
to
deserialize
the
object.
F
If
I
choose
right
because
think
that,
if
I
have
to
deserialize
change
the
life
times,
you
realize
and
then
flaunt
it
on
I
encourage
a
delay.
What
I
want
is
to
really
push
this
thing
by
just
changing
the
day.
The
lifetime,
the
other
thing
that
you
should
we
should
be
taking
out
the
envelope
is
the
line
once's.
So
what
does
it
mean
when
I
producing
a
shower
on
my
hello
packets?
On
my
lies?
F
It's
very
it's
trivial
to
mountain,
a
replay
attack
right,
so
what
I'm
doing
is
I'm
basically
I
have
to
show
my
knowns,
which
is
randomly
chosen,
and
my
neighbor
nonce
that
son,
basically
reflecting
and
I'm
doing
a
char
every
time
over
the
whole
thing
so
I
think
this
is.
This
is
a
work
that
needs
to
be
done
if
we
want
to
do
the
maximum
speed,
flooding
and
good
security
support.
F
Okay
and
I'm,
not
even
talking
whether
this
is
encrypted
I
mean
we
could
also
encrypt
that
stuff.
As
long
as
we
don't
touch
the
bite,
okay,
so
local
flooding,
reduction,
I,
think
that
has
been
written
down.
That
is
in
kind
of
an
orange
stage.
We
understand
it.
Actually
advised
us
quite
a
lot
on
the
fabric.
The
global
flooding
reduction
is
a
long
discussion
here
with
Pascal,
yes,
they're,
like
four
hours.
I
think
we
understand
how
to
do
on
the
whole
fabric.
F
Global
frogging
reduction-
very
well,
okay,
but
that's
a
very
interesting
topic,
because
we
can
literally
squeeze
flooding
to
a
trickle
all
right,
so
pgb
I
think
we
we
don't
have
to
share
a
schema
definition.
Yet
we
have
some
of
the
policy.
Definitions
of
the
PGP
is
kind
of
work
in
progress.
Some
stuff
has
been
written
down.
F
How
hard
this
thing
will
be
driven
will
depend,
of
course,
on
the
deployment
scenarios
use
case
in
customer
demand,
ztp
sauce,
your
touch
provisioning,
so
we
are
lacking
the
final
state
machine
proper
right
on
all
that
stuff,
but
I
think
in
terms
of
understanding
the
rules
and
elements
that
we
put
on
the
lies
and
the
level
selection
procedures.
That
stuff
is
all
very
firm.
Well,
understood
is
actually
running
automatic
system.
Id
selection,
I
think
he
saw
fairly
well,
would
benefit
from
another
look
over
it.
F
Automatic
interface
addresses
it's
something
that
right
now
in,
for
all
practical
purposes,
looks
like
in
the
only
local
v6
is
about
what
you
want
to
do
on
a
fabric,
but
that's
something
that
may
merit
further
discussion.
You
know
riff
doesn't
need
any
addressing
whatsoever
except
to
somehow
get
transport
transport
over.
Something
which
possibly
preconditions
address
is
unless
it's
some
kind
of
point
apart.
F
The
reachability
computations
are
what
we
missing
is
the
proper
write
down
off
the
old
path
computation,
because
you
know
if
rift
is
loop,
free
I
can
actually
use
all
possible
paths.
I
don't
have
to
constrain
myself
to
SPF
the
way
the
spec
is
written
today,
just
to
make
it
simpler
to
understand,
and
the
east-west
limbs
in
ongoing
discussion
I
think
the
way
the
spec
is
written
right
now
using
the
east-west
links
for
protection
as
a
lot
of
benefits.
F
It
remains
loop,
free
and
gives
you
a
protection
and
it
does
not
may
have
of
which
you
blocking
probabilities
automatically
Sergei
disaggregation.
So
the
normal
scenario:
why
do
I?
Have
it
I
would
say
it
is
more
in
the
greenish?
We
understand
it
fairly
well,
but
there
is
a
very
poorly
connected
fabrics,
basically
butterfly
designs.
There
is
a
case
we
will
need
the
transitive
desegregation
and
I
will
not
go
far
into
the
left
here,
because
you
know
that
will
take
about
forever.
Stub
is
written
down
understood,
but
it's
not
in
the
spec
southbound
d4
around
origination.
F
F
The
interesting
discussion,
also
in
application
2d
to
the
things
that
yan
was
talking
about
it,
may
become
interesting
if
we
start
to
redistribute
something
like
okay,
here's
my
internet,
reach
ability,
here's
my
d
for
out.
So
then
you
don't
want
on
the
fabric
to
originate
d4l,
because
you
have
to
be
four
out
unless
we
start
to
basically
have
an
external
D
four
out,
and
we
can
do
that.
Okay,
but
that
also
merits
thinking
whether
we
should
have
like
a
fabric
address
range,
which
is
the
internal
range
right
and
use
this
prefix
instead
of
the
default.
F
So
what
happened
on
the
bandwidth
balancing?
So
that's
some
interesting
work.
So
next
draft
update
we'll
have
that
in
so
the
current
draft
has
a
version
of
bandwidth
load,
balancing
which,
after
the
first
experiment,
implementation
has
been
vastly
improved
upon.
So
how
can
we
cheaply
load
balanced
fabric
and
I'm
just
showing
the
northbound
direction?
First?
F
So
if
we
somewhere
at
a
leaf
level-
and
we
have
a
terms
of
like
ten
Meg
links-
and
we
have
a
bunch
of
hundred
Meg
links
at
the
next
level-
we
have
imbalances
right.
So
let's
say
this
link
is
not
here,
so
we
only
have
ten
up
here,
but
we
have
22
this
guy
and
he
has
200
up.
These
guys
is
only
hundred
up,
but
this
guy
has
symmetric
bandwidth.
So
how
do
we
wait
the
default
route
to
give
a
course
load
balancing
right?
F
So
the
way
we
can
go
about
the
stuff
is
that
having
all
the
information
which
we
have
enough
information
flooded
down,
and
we
do
it
from
this
level
to
this
level
and
the
next
level
that's
the
same
kind
of
load,
balancing
we
talked
about
something
which
is
a
bandwidth
adjusted
metric.
So
we
have
two
normal
metric
of
Taral
being
distributed,
but
we
also
have
all
these
bandwidth
information,
so
we
compute
from
a
leaf
a
sum
we
first
we
have
the
bandwidth
from
a
leaf
to
the
next
node.
F
So
here
it
will
be
20
and
here
will
be
also
20,
but
here
will
be
10,
and
then
we
also
have
the
total
northbound
capacity
on
the
node
that
we're
reaching.
So
this
guy
will
have
the
total
capacity
200
and
this
guy
will
have
a
hundred.
So
when
we
receive
a
d4
out
for
each
of
those
d4
outs,
we
basically
look
at
the
sum
of
the
both.
So
when
the
leaf
112
gets
a
default
from
111,
it
knows
that
it
gets
20
and
another
hundred.
So
the
sum
is
120.
F
We
take
this
bandwidth
number
and
we
push
it
to
the
next
power
of
two
and
take
a
look
to
which
basically
means
we
take
the
most
significant
bit
of
what
we
got
in
terms
of
bandwidth
available
right.
So,
as
an
example
leave
111
to
note
111
goes
this
way:
20
plus
another
to
200.
So
what
I
miscalculated?
No
I
didn't
miscalculate.
So
it's
220!
So
when
you
go
push
it
up
to
the
next
power
of
2
is
256,
which
is
the
8
bit
okay,
and
now
from
all
these
available
defaults
that
go
up.
F
We
built
this.
What
is
the
highest
bit?
We
take
the
highest
possible
and
we
basically
subtract.
So
how
does
it
work
if
the
highest
bit
is
8,
then
I'm
taking
the
maximum
which
is
8?
Minus
8
is
0,
I
do
plus
1
and
I
use
the
normal
distance,
which
here
is
1
as
a
multiplier,
so
we
will
end
up
with
1.
So
when
I
have
220
bandwidth
I
end
up
with
the
8,
which
is
the
highest
bit
and
8
minus
8
plus
1
is
1.
F
But
if
I
go
to
note
111,
ok,
here,
I
only
have
10,
plus
100,
so
I
have
110
total,
which
is
128,
which
is
7
bit.
So
when
I
do
8
minus
7,
the
maximum
I
get
1
plus
1
I
get
2.
So
that
way,
I
end
up
with
the
weight
of
1,
to
the
note
that
there's
more
bandwidth
and
a
way
to
get
a
significantly
less
bandwidth.
Basically,
each
time
I
see
half
the
bandwidth,
I
basically
give
it
and
off.
F
So
where
are
we
with
the
stuff,
so
the
north
wall,
balancing
I,
think,
is
decently
well
understood,
worked
on
the
southbound
balancing,
we
didn't
do
any
work
yet
question:
is
it
even
necessary
I,
don't
know
because
it
leads
to
all
kind
of
like
ugly
fishtail
problems,
it's
much
harder
to
define
what
you
want
to
do
when
you're
going
down
into
the
fabric.
What
is
really
the
available
bandwidth
that
you
have
and.
F
Of
course,
this
depend
of
what
is
your
ratio
of
your
east-west
to
north-south
traffic
right?
If
all
the
traffic
gods
goes
north,
these
works
very
fine.
But
what?
If
the
traffic
turns
around
here
to
a
large
degree,
then
this
bandwidth
really
upstairs
doesn't
matter.
So
it's
very
similar
to
like
the
oversubscription
ratio
on
that
on
the
fabric.
So
should
we
allow
for
a
constant
people
can
configure?
F
You
know,
I
have
no
opinion.
I
think
this
is
a
very
good
first
approximation
of
a
course
load
balancing
and
then,
if
you
need
to
find
your
grain
balancing
that
you
have
to
understand
the
characteristic
of
your
flow,
so
you
either
you
have
to
shape
on
the
edges
or
you
have
to
do
per
flow
traffic
engineering
or
you
have
to
do
some
kind
of
you
know
utilization
measurement
here
and
do
it
real
time
on
the
fast
path.
I,
don't
think,
that's
something
that
lead
itself
lends
itself
to
be
implementing
control
plan
efficiently.
F
F
We
don't
understand
the
maximum
scale
or
what
will
be
this
key
value,
store,
capable
of
and
I
think
we
have
fairly
decent
tiebreaking
rules.
You
know
when
multiple
people
start
well
that
ties
the
same
key
value
combination,
so
other
technology
and
loose
ends
so
the
segment
routing.
So
there
is
some
section
suggesting:
how
could
we
support
segment
routing
but
to
what
are
the
use
case
is
really
right
for
the
segment
routing.
F
The
the
most
realistic
use
case
is
kind
of
pinging
through
the
fabric,
a
fixed
path
to
understand
it
is
the
path
you
know,
operational,
there's
a
bunch
of
other
possibilities.
There
ICMP
extension
a
long
time.
You
know,
define
a
go,
you
could
target
interfaces
and
so
on
so
I
think
it's
a
slightly
contrived
use
case
beside
that
segment.
Routing
except
like
eager
spear
engineering
oddities.
He
didn't
see
any
any
fabric
use
cases,
I
was
convinced
off
and
the
egress
peering
Jian
could
be
done
using.
F
You
know
like
exit
points
prefixes
in
my
opinion,
so
the
beer
something
will
be
presented.
The
BFG
should
we
support
something
like
SPF,
D
I,
don't
know
how
familiar
people
are
with
that
that
preconditions
that
we
basically
have
like
unique
identifiers
on
the
whole
fabric.
Now,
how
do
we
get
those
unique
identifiers?
I
was
thinking
through
that
stuff,
not
clear,
so
the
yank
models
will
be
presented
in
the
router
redistribution.
F
That
also
like
the
kind
of
still
widely
open
fields
that
are
just
being
started
to
know
to
being
looked
at
and
worked
on
cool,
so
the
sugar
at
the
end
is
that
we
will
be
putting
out
publicly
available
binary
that
you
can
be
download.
Well,
actually,
stuff
is
ready,
but
you
know
getting
this
stuff
through
all
the
red
tape
and
put
it
on
a
web
page.
So
people
can
actually
click
it
and
obtain
it.
F
I
mean
the
last
steps,
so
it's
a
standalone
binary
package
runs
on
OSX
and
Linux
I'll
put
the
announcement
of
the
list
when
I
have
the
download
link
God's
willing,
large
parts
of
rift
are
implemented.
In
this
thing,
it
is
an
environment
where
people
can
very
easily
build
fabrics,
so
you
can
build
fabric
of
you
liking
very
easily,
using
using
some
yang
schema
and
just
push
it
up
the
hill
and
run
it,
and
you
run
a
rift
per
switch
and
get
all
kind
of
statistic
and
stuff
out
of
it.
F
You
can
actually
use
it
to
interoperate
interoperate
your
own
things
again
because
it
runs
on
UDP,
so
you
just
specify
UDP
port
that
sticks
out
through
the
yang,
and
you
hook
up
your
own
thing
on
this
UDP
and
you're
in
the
game.
Okay
and
of
course,
open-source
implementation
encouraged-
and
the
important
thing
to
say
here
is
that
the
leaf
version
is
much
simpler
to
build
right.
I
Good
afternoon
everyone
I'm
ginger
from
the
te
you
can
call
me
sandy.
The
first
presentation
is
for
rift
young
in
this
chapter
we
have
co-author
stolen
and
the
chiffon,
and
this
setup
model
is
defined
according
to
the
rift
protocol
chapter
right,
bye,
honey.
This
model
includes
protocol
configuration
study,
information
and
some
notifications
under
to
be
defined
up,
see
some
features.
The
added
to
enhance
the
protocol.
I
Let's
see
the
rift
configuration,
but
we
know
that
chappie
called
drift
is
very
flexible,
so
we
still
like
some
featuring
this
model,
so
we
will
add
at
a
later
version
and
in
existing
yamato
we
can
see
the
configuration
includes
not
in
foreign
interface,
the
information
and
policy
information
the
base.
Now
the
information
includes
nazi
system,
ID
address
not
level
and
other
information,
and
the
policies
include
the
community
and
the
policy
guide.
I
Let's
see
the
rift
state
the
until
now
we
defined
three
kinds
of
studying
this
model,
neighbor
database
and
key
value
store.
This
is
the
neighbor
state
information.
We
can
see
the
neighbor
system,
ID
address
the
level
flag
and
value
and
at
other
information-
and
this
is
the
databases,
data
and
the
p-value
store
information
Stata.
So
from
it,
we
can
know
that
the
deter
of
the
pie
and
such
as
the
originator,
the
direction,
the
link
type
and
the
six
number
of
the
lifetime
and
other
information.
I
It's
the
notification
of
the
rift.
Until
now
we
divided
two
kinds
of
notifications,
for
it
one
is
the
unexpected
pie
and
the
other
one
is
neighbors
layer
arrow.
So
you
can
improve
it
in
later
version,
but
we
think
it
will
help
people
to
understand
drifter
protocol.
Well,
maybe
some
tip
benefited
for
someone.
Okay,
this
is
the
yeah
and
commit.
I
And
the
second
apparent
issue
is
for
PR
is
reached.
We
have
Koster
Jefferey
the
shower
I,
don't
know
how
many
people
understand
the
route
protocol.
Well,
so
I
make
a
brief
introduction
of
lift
protocol
here.
Rift
is
a
hybrid
routing
protocol
for
cloth
and
factory
networks
and
the
furnace
pound.
We
use,
link
state
routing
and
for
such
bond.
We
use
this
thing:
distance,
vector
routing
and
the
inbound.
The
default
route
is
used
most
of
the
time
and
some
specificity.
I
So
they
are
two
different.
The
features
in
ripped
protocol.
You
can
remember
northbound
and
saucepan
so
because
the
there
is
two
different
features
in
Riften,
so
we
use
two
different
signaling
for
peer
information
advertisement
you
know,
spawned
we
use
the
existing
defined
of
peer
was
peer.
Opec
is
like
mechanism
to
advertise
the
peer
information
and
for
sauce
bound.
We
use
the
function.
Defining
perfect
prefix
redistributed
dropped
to
flatter
the
peer,
such
as
PF
ID
added
other
information.
I
I
So
the
about
a
second
online
because
in
I'm
sure,
as
we
just
used
a
label
blocking
employee
as
encapsulation
support,
govt
to
advertise
the
PR
information.
So
we
can.
We
can
reference
the
function
in
not
I'm
curious.
We
can
simply
use
unique,
come
a
combination
of
most
of
the
men,
its
students
and
the
set
a
tenifer,
and
also
we
can
use
a
function
just
like
mtrs
space.
We
use
the
PRF
chip
block
instead
of
labour
block,
so
we
can
advertise
the
BR
information
whether
they
are
in
protocol.
I
So
it's
a
summary
so
for
not
span
that
we
see,
we
can
see
that
we
use
peer
or
SPF
or
you
see,
is
like
function
to
stagger
learning
the
two-second
of
the
year
information
and
for
sauce
panda.
We
use
the
mechanism
define
the
Impe
are
perfectly
distributed
to
advertise
the
peer
information,
so
similar
BFG,
ID,
signaling,
proposed
and
purest
and
non
piercing
absolution,
and
also
we
can
use
shift
Aseema
instead
of
subchief
emerge.
