►
From YouTube: IETF101-6TISCH-20180321-1330
Description
6TISCH meeting session at IETF101
2018/03/21 1330
https://datatracker.ietf.org/meeting/101/proceedings/
A
Of
IPR
in
the
discussions
that
take
place
in
this
room
and
IPR
that
you
have
done
that
belongs
to
your
company
or
something
like
that.
You
are
aware
of.
Please
notify
it
all
at
the
chairs
know.
At
the
end
of
this
meeting
now
there
are
other
policies
which
are
now
presented
in
the
not
well.
In
particular,
there
are
new
policies
which
were
defined
before
harassment
and
good
behavior
code
of
conduct
type
of
things.
A
So
please
have
a
look
at
the
best
practice
documents
which
are
pointing
he
appointed
here
and
there's
also
something
about
the
copyright
statement.
And
if
you,
if
you
are
in
a
bad
situation
about
harassment,
something
like
that-
and
there
is
now
a
group-
the
idea
that
you
can
contact-
and
this
is
this
Ombuds
team-
which
is
very
hard
for
me
to
pronounce.
But
there
is
a
link
here
there
are
people
behind
this
link.
So
if
you
issue
a
face,
a
situation,
which
is
that
you
don't
feel
is
acceptable.
Please
contact
the
unbox
team.
A
A
So
we
have
our
not
takers
there
in
the
room
we
need.
Yes,
I
saw
you
get
you
Nathaniel
there.
Ok,
so
these
are
the
usual
links.
The
etherpad
link.
The
first
link
is
pretty
useful.
This
is
where
our
minutes
are
being
taken.
If
there
is
something
you
did
not
understand,
probably
it's
good
to
look
at
this
iPad
to
see
how
it
was
captured
same
thing.
If
you
came
to
the
mic
and
said
something
your
feelings
interested.
Obviously
interesting,
please
check
in
the
minutes
that
what
she
said
was
captured
correctly.
A
All
your
name
was
captured
correctly,
and
this
is
our
number
of
links
to
documents
that
are
produced
pushed
to
other
working
groups
which,
in
fact
inner
from
the
work
of
six.
So
you
realize
that
60s
does
not
produce
so
many
documents,
but
actually
our
work
is
a
lot
about
integrating
things
and
asking
other
working
groups
to
produce
documents,
and
this
is
a
list
of
things
which
are
done
here
or
in
other
groups
which
are
actually
product.
B
A
A
Just
before
we
continue,
there
is
the
agenda
for
today,
oops
not
very
readable,
so
so
we'll
start
with
the
blue
sheets
and
the
presentation
I'm
doing
then
we'll
go
through
the
chartered
items
so
we'll
have
the
six
top
protocol,
then
minimal
security.
We'll
have
a
small
talk
on
terminology
as
well.
There
was,
there
are
few
dates
to
go,
we'll
talk
about
this
effects
and
thankfully
about
the
mini-mall
SF.
C
D
You
pull
the
agenda,
we'll
have
a
pretty
packed
1
hour
and
a
half.
So
as
a
reminder,
what
I'm
putting
on
here
is
the
the
goal
of
the
presentation.
So
we
start
with
from
charges
items
6
the
protocol
is
in
is
G
last
call,
so
we
want
to
I.
You
know,
inform
our
viewers
about
about
the
revisions.
Charlie
is
going
to
present
this.
We
didn't
have
a
leash.
I
will
present
minimal
security.
I
think
which
is
you
know,
the
goal
is
to
prepare
for
work
last
call.
D
This
is
something
that
has
been
there
has
been
a
pretty
stable
marita
has,
you
know
essentially
two
minutes
to
present
terminology.
It's
just
an
update.
Sfx
Diego
will
present
presenters
the
editorial
updates
with
discuss
redness
for
work
group
last
call,
and
then
we
have
MSF,
which
takes
a
will
present
preparing
for
work
group
adoption
and
then
a
SF
discussing
how
to
best
integrate
a
SF
into
different
lot
of
documents.
So
we
had
a
pre
meeting
just
now
and
Charlie
I
think
you
said
to
the
main
you
list
some
some
proposal
next
slide,
please.
D
The
second
part
is
time
permitting,
of
course,
so
new
work
on
global
time,
and
so
the
goal
is
to
assess
the
importance
for
the
work
group
and,
seeing
you
know
discussing
the
validity
of
these
and
then
to
drafts
by
michael
mullen
the
enrollment
and
has
beacon,
and
one
was
the
roll
enrollment
priority
and
so
I
think
those
are
presented
together
in
one
in
one
set
of
slides,
and
so
we
want
to
discuss
the
different
priority
fields
and
there
are.
There
are
some
follow-up
meetings
following
this
this
this
afternoon.
D
A
D
We'll
obviously
have
to
update
the
PDFs
that
are
on
site,
so
are
the
work
group
stuff,
sixth,
overall
and
core
tomorrow
at
the
six
o'clock
meeting,
we
have
a
40
40
minute
time
slots
dedicated
to
sexual
fragmentation.
There's
a
design
team
will
report
on
that
report
on
two
different
drafts
and
under
they
there's
a
draft
well
deadline.
D
Time,
which
is
has
a
six
specific
I
said
time
to
do
time:
stamping
enroll
we,
you
know
the
discussions
will
have
with
Michael
right
after
this
meeting
will
be
other
words
for
all
as
well,
and
then
we
should
a
liaison
to
the
core
working
group
just
indicating
that
this
draft,
your
minimal
security,
defines
a
new
stateless
proxy
co-op
option.
So
we
just
issued
that
that
statement
next
slide.
Please
a
couple
of
a
couple
of
very
quick
updates.
This
is
more
for
having
this
inside
our
slide
deck.
D
So
there's
a
six-tier
simulator
that
was
released
an
hour
ago.
So
thanks
militia
for
racing
this
right
on
time,
it's
a
pure
I'm
going
to
present
them
because
it
would
be
silly
to
have
somebody
come
up
for
30
seconds,
but
it's
a
high
level
simulator
that
allows
you
to
answer
what-if
questions
and
provide
some
idea
of
the
performance
of
success,
all
written
in
Python,
so
open
source
on
their
BSD
license,
and
it
it
it
it.
It
captures
the
full
sisters
behavior.
D
The
idea
at
least,
is
to
capture
the
full
behavior
so
that
we
can
assess
the
performance
of
a
six
there's.
Network
behavior
means
TCH,
of
course,
minimal
security,
ripple,
6
p.m.
s-s,
etcetera,
ID
can
run
on
multiple
CPU
cores.
You
can
run
it
on
a
on
a
cluster.
You
can
lock
stuff
plot
stuff
and
you
can
replay
real
world
connectivity
traces.
So
if
you
have
long
term
connectivity
traces,
you
can
use
that
rather
than
a
model
for
physical
air
connectivity
militia,
and
so
the
core
team
is
those
three
people.
D
D
112
release
was
released
yesterday
and
runs
on
I'm
sorry,
it
should
be
12
platforms,
including
the
open
mode
B,
which
is
this.
This
cool
little
platform
that
has
both
2.4
and
some
gigahertz
radios
also
a
bsd
implementation
and
the
two
leading
leads,
thankfully,
are
here
as
well,
and
we
actually
will
have
an
open
WN
session
right
after
this.
D
This
presentation,
as
well
as
tomorrow
from
10
to
2
next
Wireshark
that
sector,
so
just
a
state
of
the
work
they're
different
people
contribute
with
dissectors
for
different
pieces
of
the
sixish
puzzle
and,
and
so
today's
Wireshark
dissector
contains
we
believe
most
of
most
of
the
latest
versions
I
put
in
in
bold
here
the
sixth
of
protocol
10
and
object
security,
7
or
2
dissectors
that
are
part
of
the
official
Wireshark
release.
I
forget
the
number.
D
B
D
In
a
code
lounge,
we
took
advantage
of
this
code
lounge
being
open
to
to
have
a
couple
of
things
lined
up
so
from
2:00
to
6:00.
Today,
a
lot
of
the
people
contributing
to
work
group
are
here
today,
so
we
had
to
pack
today
a
lot
apologize
so
4
to
6
we'll
have
a
discussion
with
Michael
around
the
two
drives
that
you've
presented,
how
they
integrate
sixish
with
core
with
roll
I'm.
Sorry,
six
to
eight.
D
We
have
in
the
code
large
again
in
a
session
about
the
F
and
drop
platform
that
allows
us
to
do
interoperability,
tests
and
so
we'll
be
discussing
and
deciding
on
the
scope
of
the
next
interrupt
test.
The
test,
description
and
implementation,
which
Manisha
Morita
will
Lake
will
take
Ramadi
that
will
late
will
lead,
and
then
we
have
some
side
discussion
about
score
score
and
six.
Lo
han
from
eight
to
ten
will
have
values
and
friends,
I,
say
friends,
because
you
know
everybody
who
works
on
open
source.
D
Six
dish
related
stuff
is,
of
course,
absolutely
invited,
and
so
Charlie
will
present
the
open
multi-platform.
Jonathan
will
talk
about
multiple
interfaces.
Michael
will
talk
about
changing
the
interface
to
PPP
and
Annie.
H
will
be
there
to
talk
to
answer
questions
about
the
simulator
and
then
tomorrow
there
is
an
open
areas
and
write
integration
slot
for
our
slot
in
the
morning,
as
well
in
the
code
lounge
at
the
bottom
of
the
minutes.
So
thank
you
for
the
minute
takers
to
to
to
take
minutes
at
the
very
very
bottom
of
the
minutes.
D
There's
a
there's,
a
highlighted
section
with
a
wish
list.
So
if
you
want
to
discuss
others,
six
dish
related
stuff
at
those
meetings
just
populate
that
they
won't
be
part
of
the
minutes,
but
that's
just
where
we
want
to
capture
some
ideas
that
might
pop
up
during
the
the
the
meeting
now
next
slide.
Please
so
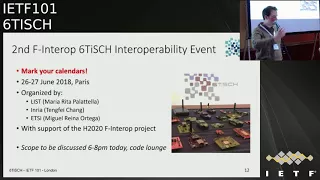
mark
your
calendars.
There
will
be,
and
so
it's
the
official
title
is
the
second
F
and
drop
six
stations.
Reliability
interoperability
event
will
be
organized
Thank,
You
Meredith
reported
putting
this
together.
D
It
will
be
in
Paris
26
27
June
of
2018,
so
those
are
the
people
that
are
that
are
that
are
organizing
it
Meredith
I,
think
Fame
and
miel
and
is
supported
by
some
project.
So
we
will,
the
scope
will
be
discussed
today
between
six
and
eight.
So
you
know
if
you're,
an
implementer
and
and
and
tempted
to
participate,
please
come
to
six
Nate
will
discuss
high
level,
which
are
the
drafts
that
we
want
to
test
during
this
an
event,
and
then
we
can
start
working
on
the
test
description.
D
The
ID
usually
is
to
have
the
dezerter's
already
one
month
before
the
event
and
registration
will
be.
If
it's
not
open
right
now,
it
will
be
open
in
the
next
day
or
so
so
keep
you
know
we'll
keep
you
posted
on
a
six
mailing
list
so
that
you
can
register
this
is
organized
by
this
is
under
youth
under
the
umbrella
of
Etsy
and
that's
I
think
the
end.
D
E
Okay,
so
this
draft
is
in
is
Djilas
group
call
and
we
published
answering
some
of
the
reviewer
comments.
Version
number
ten.
We
addressed.
We
had
several
males
in
the
mailing
list
and
we
provide
responses
to
all
of
them.
But
then
we
come
back.
They
come
back
with
another
questions
or
clarification,
so
I
will
detail
how
I
will
address
them,
not
all
of
them,
but
I
think
the
most
important
one.
E
So
you
know
the
status
so
Ryan,
for
example
at
the
remark
mentioning
that
there's
a
possible
race
condition
in
the
two
way
and
three-way
transactions,
and
would
we
go
to
clarify
in
the
text
in
the
ad
or
in
the
transaction
description
that
in
case
that
this
happens
in
consistence
is
then
handled
by
what
is
specified
later
on
in
another
section,
which
is
mainly
a
pointer
to
another
section.
So
people
know
when
read
the
draft
that
this
will
be
addressed
later
on.
E
F
E
E
For
example,
is
last
in
the
last,
when
we
have
a
cell
list
in
a
packet
in
a
6p
packet
to
know
the
length
we
have
to
know
the
length
of
the
information
element,
so
we
have
to
go
due
to
the
information
element
header
and
through
this
length
we
know
how
many
cells
are
in
the
in
the
in
in
the
list.
So
this
needs
to
be
clarified
and
least
with
the
short
sentence
in
the
in
the
draft.
E
So
if
someone
wants
to
add
many
candidate
cells
for
an
ad,
we,
it
has
to
be
done
in
more
than
one
packet
has
to
be
done
in
multiple
ad
requesting
some
other
simple
clarifications,
and
maybe
one
that's
important
is
the
fact
that,
when
we
do
an
least
command
between
two
nodes,
we
need
to
clarify
that
the
response
for
that
command
is
the
least
that
are
scheduled
between
them.
So
it's
not
at
least
that
involve
other
nodes,
but
it's
only
between
the
two
nodes
involved
in
this
in
this
transaction.
E
E
E
His
proposal
is
tries
to
address
the
fact
that
the
minimal
cell
is
congested
at
the
beginning
when
we
are
booting
and
then
he
tried
to
propose
an
alternative
mechanism.
So
we
don't.
We
cannot
lose
an
acknowledgment
when,
when
we
install
that
cells,
we
think
that
this
is
complicating
the
draft,
because
this
only
applies
to
at
but
is
not
applying
to
the
rest
of
operation.
So
it
would
seem
strange
to
have
one
mechanism
particular
to
add,
while
the
rest
of
mekinese
use
another
another
mechanism
for
for
transaction.
E
D
Okay,
Thank
You
charlie.
So
are
there
any
further
remarks?
I,
don't
know
if
Alex
and
a
lot
are
indeed
in
the
room
or
Nicola,
please
raise
those
now
what
you
know
we've
had
the
meeting
just
before
these
are
all
clarifying
questions,
so
I
think
we
can
address
them
very
easily
in
a
version
11
that
would
be
a
it'll
just
address
them
and
then
pushing
them.
D
G
Not
as
stammering
Mook,
I
I
just
have
one
minor
remark.
Thank
you
for
getting
back
to
me
about
my
interpretation
of
like
when
to
start
actually
using
the
sales
I
was
wondering
if
you
could
also
went
before
you
publish
version
11.
Add
a
remark
on
I'm
getting
nervous
right
how
to
miss
how
to
react
to
missing
acts
because
I
kind
of
started
wondering
like
at
which
point
do
I
actually
figure
out
if
something
went
wrong
and
I
kind
of
drew
something
down.
I
could
ask
you
after
the
meeting.
D
D
H
I
I
H
The
goal
of
this
presentation
today
is
just
to
go
quickly
through
the
summary
of
updates
since
so
forth,
to
get
everyone
on
the
same
page
and
to
discuss
the
eventual
working
group
Lascaux.
So
first,
the
first
mate.
Let's
call
it
major
change
that
was
done
was
to
resolve
to
mitigate
the
vulnerability
that
was
caused,
that
would
that
would
open
the
network
to
a
resource,
exhaustion
attacks,
but
from
malicious
pledges.
H
If
there
is
a
collision
in
the
routers
between
join
requests
and
the
drawing
responses,
we
declared
out
of
scope
how
individual
scheduling
functions
react
to
to
this
traffic,
but
we
provided
the
recommendation
that,
basically,
they
shouldn't
add
new
cells,
and
with
this
there
was
an
order.
A
new
normative
reference
was
added
to
our
SC
25
97.
H
The
second
change
was
related
to
a
use
case
that
we
previously
did
not
do
not
work
on,
and
it's
basically
a
jrc
that
is
managing
multiple
sixties
networks.
At
the
same
time,
it
is
not
co-located,
obviously
with
the
6lb
R,
and
the
issue
here
is
when
the
join
request
from
a
pledge
comes.
The
GRC
needs
to
identify
the
network
that
the
pledge
is
attempting
to
join
in
order
to,
because
all
these,
not
the
different
networks
will
have
different
link
layer
keys.
H
So
the
when
the
in
the
join
response,
which
contains
the
link
layer,
King
material
to
J
and
J,
are
C
needs
to
respond
with
the
proper
King,
and
the
resolution
was
that
we
are,
we
defined
basically
the
payload
for
the
join
request
and
it's
a
C
bar
array
with
a
single
network.
Identifier
element
where
the
network
identifier
maps,
by
default
to
the
pen
ID
in
the
802,
does
15.4
header
but
can
be
overridden
by
filter
specs
and,
as
the
drawing
request
maps
to
a
co-op
post
it
can.
It
can
carry
payload.
H
H
H
H
D
K
We're
Michael
Richardson
were
if,
if
we're
going
to
define
rekey
there,
then
wherever
we
I,
don't
think
we
should
redefine
rekey
in
this
document.
If
we're
going
to
use
that
mechanism
to
define
the
rekey
it
will,
there
will
be
some
cryptographic
statements
to
figure
out
how
to
secure
that
subsequent
packet
I,
don't
think
it's
complicated,
but
it's
not
a
literal
just
sense
of
our
data,
there's
some
other
there
other
stuff
that
that
we
need
to
do
because
we
have
the
OS
core
layer
there
right
are.
K
K
K
I
I'm
thinking
that
there's
a
that
OS
core
has
some
additional
response.
That's
derived
from
the
thing
that
you
wrote
that
creates
something
so
maybe
I'm
mistaken
and
I'm
thinking,
I'm
overthinking
this,
but
anyway.
So
if
it's
really
simple
and
you
think
we
can
define
rekey
ther,
then
we
should
maybe
think
about
doing
that
to
completeness
but
I'm
hesitant
to
do
anything
that
prevents
us
from
going
to
working
group.
Last
call:
okay,.
H
So
I
see
let's
discuss
this-
is
the
side
meeting
this
evening.
I
think
that
would
be
a
good
starting
point.
I.
The
idea
I
had
in
mind
was
basically
just
to
use,
observe
to
carry
the
key
and
then
with
this
we
would
need
also
to
define
a
timestamp
like
the
ASN
at
which
this
key
will
get
actually
used
in
the
network,
so
that
the
jrc
can
hand
out
the
keys
before
actually
rolling
out
the
new
key
in
the
network,
but
yeah
and
then
so
to
continue
with
my
presentation.
D
H
Nathan,
yes,
yes
with
the
current
mechanism,
there
would
be
a
disruption
on
the
network
and
because
it's
basically
every
node
would
have
to
request
the
key
once
it
identifies
that
it
doesn't
have
the
link
layer
keys
that
are
currently
in
use.
So
it
needs
to
fail
first
before
that
and
then
the
third
major
change
was
editorial.
I,
don't
normally
present
the
de
toriel
changes,
but
I
would
like
just
to
get
around
same
page
Roger
regarding
the
terminology
and
let's
call
it
the
standardization
scope
of
the
of
the
document,
so
the
the
first
part
was.
H
The
first
goal
was
to
clarify
the
terminology
and
to
allow
basically
future
specs
to
override
the
identifiers
that
we
use
we.
So
we
worked
together
with
the
terminology
draft
authors
to
define
better
some
drawing
specific
terms
these.
All
the
definitions
are
in
the
terminology
section
and
in
the
minimum-security
we,
basically
just
we
just
we
just
list
these
terms
with
an
addition
that
is
specific
to
minimum-security,
where
we
use
also
terms
network
identifiers,
generic
terms,
network
identifiers
and
pledge
identifiers,
and
we
map
these
terms
to
pen
ID
and
the
eui-64
by
default.
H
But
we
allow
future
specs
to
other
ideas,
identifiers
for
privacy
reasons
or
also
the
reasons
that
michael
outlines
in
one
of
his
one
of
his
draft,
and
these
two
terms
are
not
industry.
In
the
terminology
section,
I
added
a
separate
section
identifiers,
as
the
text
is
kind
of,
contains
the
standardization
stuff,
not
really
the
precise
definitions
of
the
of
these
terms.
H
The
second
major
editorial
strange
was
to
the
goal
of
the
second
major
toriel
change
was
the
precise
scope
in
the
standardization
scope
of
the
document
and
with
that
I
wanted
to
clearly
stress
out
what
what
are
we
standardizing
and
basically
the
document
is
now
separate
and
separated
into
different
sections.
They
talked
about
the
configuration
of
the
60
stack,
so
we
go
like
link
layer,
802,
15
4.
A
Monisha
for
the
previous
slide,
when
you
say
that
the
network
is
the
fan,
but
the
kind
of
network
where
buildings
are
really
ipv6,
subnets
and
I
was
wondering
if
it
would
make
more
sense
for
us
to
consider
that
the
whole
subnet
has
the
same
security
properties
like
keys,
because
because
people
will
move
from
one
pan
to
the
other
pan
inside
the
subnet,
so
my
wall
guess
is
a
network.
Is
a
subnet.
It's
not
bad.
Okay,.
H
So
a
CRM,
so
basically
we
need
two
different,
I'm
een.
This
is
an
important
question
in
terms
of
the
architecture,
the
link
layer
keys.
If
these
networks
are
not
synchronized,
if
you
get
reuse
of
ASN,
you
have
to
use
the
different
keys
for
each
sixties,
Network
right.
So,
even
though
they
are
part
of
the
same
subnet,
they
need
to
use
different
link,
layer,
keys.
A
They
would
be
synchronized
because
if
you
want
to
move
from
one
tier
dag
to
another,
do
like
different
routes,
but
then
you
need
to
keep
everything
SES.
So
you,
our
discussion,
is
very
early
in
six
issue.
Is
that
you
have
a
backbone,
then
the
time
must
be
synchronized
between
the
routes.
Understand.
G
A
Then
they
are,
they
are
on
the
same
time,
exactly
that's
what
the
goal
was
to
be
able
to
move
freely
to
deploy
as
many
routes
as
you
wanted
to
and
move
freely
from
one
route
to
the
other,
meaning
it.
So
it's
one
network,
you
keep
your
sense
of
time.
You
keep
everything,
so
that
was
the
design
that
I
know.
We
did
not
discuss
that
for
a
long
time,
but
you
know.
K
Michael,
Richards
and
I
think
that
in
the
generic
case,
if
we
say
that
different
pan
IDs
have
different
keys
and
you
need
to
perform
a
joint
process
on
each
then
in
the
case
where
the
keys
are
all
the
same
and
you
can
freely
move
from
place
to
place,
then
that's
it
adjust
a
degenerate
situation.
For
that,
my
tenth
one
career.
K
We
act,
you
know
and
and
oh
and
once
once
you
have
a
mapping
that
says
you
know
for
pen,
one
I
have
key
X
and
for
pen
I
have
key
X
because
they
happen
to
be
the
same.
Then
I
can
move
from
pan
one
to
pan
without
going
through
a
joint
process.
But
if
I
go
to
pan
three
and
it
turns
out
to
have
key,
why
and
I
will
have
a
new
have
to
have
a
new
key.
K
But
the
point
is
that
if
I
have
those
two
keys
already
I
can
move
back
and
forth
with
a
problem,
and
it's
really
just
an
administrative
thing
that
he
says
well:
I've
set
the
same
keys
right,
l2,
l2,
Network,
key
you're,
absolutely
certain.
Even
as
of
Pascal
said,
the
asn.1,
the
ASNs
are
synchronized
such
that
we
never.
L
K
A
L
They're
giving
it
yes,
they
might
be
sucrose
in
the
beginning,
but
because
the
time
time
synchronization
process
keeps
the
network
sync
inside
the
pan.
So
if
you
have
any
kind
of
crime
proof
there
it
they
might
drift
away
from
each
other
and
because
even
if
you
try
to
keep
them
in
sync,
they
might
go
off
and
because
it's
a
fundamental
property
that
the
ASN
is
part
of
the
pan.
So
so
there
is
nothing.
Yes
could
you
could
print
principle
do
that
kind
of
network?
L
But
it
would
be
very
scary
to
do
that,
because
if
you
can
end
up
having
one
x
of
difference
there,
ten
milliseconds
that
then
you
actually
have.
You
know
this
issues
that
you
know
you
even
know
you
don't
even
you
don't
you
fail
to
actually
the
decrease.
You
can
actually
decrypt
the
pockets
of
the
other
network
because
they
are
using
different.
You
know
they're
using
the
same
key
twice
or
the
same
ASN.
A
But
if
you
don't
do
that,
then
you
cannot
move
freely
inside
your
subnet,
which
would
be
ever
so.
The
idea
was
the
the
ripple
root
actually
propagating
the
time
and
they
get
it
from
the
backbone
over
precise
time
or
whatever
a
protocol.
So
so
it's
the
way
we
provide
time
is
a
long
ripple
as
well
so
I'd.
L
Like
to
cut
it,
it's
it's,
it's
actually
very
easy
to
just
put
a
different
Keystone
them.
There's
I
mean
you
have
a
pan.
You
have
the
key
settings
there
actually
and
you
have
a
key
source
you
have.
You
can
have
a
multiple
keys
there,
so
dope
issue
that,
and
you
have
to
understand
that
if
you
actually
part
of
the
multiple
pans,
it's
something
that
is
not
really.
There
is
ways
to
do
that.
L
D
H
H
H
D
So,
let's
so
for
workgroup
last
poll,
I
think
we
are
we're
very,
very
close
I'd
like
to
make
sure
that
this
fetch
get
post
thing
is
well
understood.
Before
we
go
forward
replies
coli
I
would
I
would
hate
to
work
that
the
workgroup
a
school
would
create
a
big
change
like
this.
So
let's,
let's
it
doesn't
have
to
be
long,
but
let's
make
sure
that
that
is
cleared
up,
that
we
understand
what
we're
committing
to
before.
D
N
H
O
O
So
it
does,
it
has
gone,
I,
usually
undergone
review,
and
this
like
currently
being
stuck
and
I
discuss
from
the
security
ad.
So
one
of
the
security
but
eighties
ballot
areas,
another
one
is
holding
a
discus
and,
like
it
looks
very
very
how
do
I
call
it
complicated
like
the
discus
right,
so
I
I
wouldn't
get
on
it.
Just
go
for
it
like
you
know,
whenever
you
are
ready
to
send
it
off,
send
it
off
like
and
we'll
handle
it
at
some
point.
O
P
D
This
to
be
able
to
to
be
used.
Thank
you
so
I'm
going
to
just
just
to
mention
the
fact
when
it
asked
me
to
present
two
slides
essentially
about
the
terminology.
Terminology
is
just
following:
oh
not
this
one.
Just
following
the
different
new
terms
that
pop
up
in
different
drafts,
we
did
a
full
pass
over
it.
There
are
now
next
slide.
There
are
now
48
definitions
in
our
in
our
in
our
terminology
draft.
It's
still
a
workgroup
document,
no
change
requested.
This
is
just
following
Bullington
regular
work.
Next.
D
I
I
Remove
temporary
sections
also
and
corrected
many
typos
and
styling
expressions
which
were
remaining
over
there.
Then
we
other
change
only
the
response
list.
In
fact,
the
error
management
becomes
how
the
response
management
and
we
corrected
the
other
new
new
new
descriptions
which
belonged
originally
to
a6p.
Ok,
so
we
adapted
to
the
new
requirements
on
from
6p.
In
fact,
they
and
of
least
ok
the
one
which
is
added
Kaleigh.
I
The
the
sequence
number
would
replaces
the
generation
a
check
and
the
cell
list
error
from
this
at
least
ok
and
what
do
on
the
locked
and
the
reset
were
which
were
passed,
the
RCR
reset.
Then
we
added
a
security
considerations,
which
is
in
fact
this
only
and
explains
that
we
are
not
defining
the
speed
security
there.
We
are
only.
We
have
an
algorithm
and
way
of
behavior,
and
so
we
are.
We
trust
on
the
a
hundred
to
fifteen
for
security
and
also
on
the
security
firm,
would
describe
on
minimal
security,
which
are
other
complemented
documents.
I
Then
a
we
added
a
section
on
scheduling,
function,
identifiers
which
was
needed,
and
this
is
the
SFX
one
which
has
required
a
on
the
6p
draft,
which
is
figure
five
here
and
finally,
we
like
to
we
are
going
to
address
all
the
all
the
requirements,
all
what
was
commented
on
the
main
list
from
lot
and
since
I
have
it
mean
it's
more
than
five,
which
I
requested
so
I'm
very
happy.
I
will
have
it
on
the
slides.
I
In
fact,
I
will
try
to
mention
a
little
bit,
which
are
the
items
which
are
replaceable
loaded,
first
of
all,
the
education
policies,
okay
and
which
we
find
out
the
number
of
cells
and
second,
in
on
the
number
of
cells
on
the
cell
list.
Okay,
we
can
use
the
new
feature,
which
is
offered
by
6p
to
add
request
to
provide
more
cells
for
further
for
the
negotiation
process,
the
ones
needed
on
the
whitelisting
side.
Okay,
we
are
trying
to
define,
we
tried.
We
will
address
till
this
point.
I
Also,
okay,
then
we
add
the
non
number
of
cells
to
it
or
a
whitelist
after
the
the
ones
which
are
not
add
for
those
which
are
not
added
during
the
out
process.
The
deletion
process
or
the
policy
should
be
defined
also
for
delete
and
our
affordability
and
relocate
and
the
time
measurement
time
time
measurement,
which
is
one
of
the
most
interesting
things
to
define.
Here,
we
find
a
wide.
I
I
C
A
A
Q
Q
So
for
the
MSF
for
the
first
version
is
published
in
the
last
year
during
the
ITF
100
Singapore
meeting.
And
since
then
we
have
the
Commons
many
from
Josh,
who
is
the
one
they
implement
implementer
of
the
MS
dropped,
and
this
draft
is
implement
in
open-open
DeRozan,
which
is
a
form
we're
running
on
the
hardware
and
also
the
secretary
simulator,
which
already
present
by
a
Thomas
before,
and
the
zero-one
working
is
published
in
March
1st
and
is
present
and
today
during
the
60s
entering
at
2nd
March
and
right
now,
I'm
presenting
the
newest
version.
Q
Q
Q
And
besides,
then,
the
nose
need
mass
to
remove
all
the
dedicated
links
which
actually
the
right
term
here
is
the
cells.
So
we
also
changed
that
part.
So
the
second
common
is
a
about
six,
a
time
out.
Calculation,
the
in
the
first
abortion
is
going
wrong
and
the
right
one
is
present
here
and
we
just
as
these
changes
to
the
nearest
of
Russian.
Q
This.
The
third
Commons
is
for
the
clarifying
the
use
of
the
share
cell.
In
the
version
first
version,
we
are
trying
to
clarify
the
package
going
to
transmit
on
the
minimal
cell
and
a1.
The
type
of
package
is
we're,
saying
is
the
first
SXP
packet,
but
in
real
case
is
actually
the
whole
transaction,
which
is
the
6p
package
which
is
used
for
schedule,
the
first
datak
dedicated
cell.
So
we
also
apply
this
changes
to
the
zero
one
version
and
for
the
first
common
in
the
zero
one.
Q
There
is
a
a
section
in
the
MSF
trapped,
seeing
the
implementation
status
of
this
draft.
Currently
we
have
this
too
imputations
open,
double
sandwiches,
affirm,
firmware
and
the
smear
later,
a
60
simulator,
which
I
mentioned
about
so
once
and
the
result
of
those
implantation
will
appear
in
this
section.
Q
A
A
Q
D
M
M
C
M
M
M
Yeah,
thanks
now
to
main
to
main
IDs
behind
a
yourself.
The
first
one
is
that
you
have
autonomous
catering
inside
slot
frames.
That
means
that
inside
a
given
slot
frame,
the
nodes
are
going
to
calculate
the
slot
offset
that
they
want
to
communicate
on
on
by
hashing
their
MAC
address.
So
they
know
where
to
listen
from
the
hash
of
their
MAC
address.
And
then,
when
you
want
to
talk
to
someone,
you
have
the
MAC
address
of
the
destination,
and
then
you
know
who
torch?
That's
that's
one
main
idea
and
the
the
second.
M
The
second
idea
is
that
you
separate
traffic
in
different
slot
frames,
for
instance,
like
your
most
basic
example,
would
be.
You
have
one
slot
frame
that
is
dimensioned
for
your
application,
traffic
or
unique
as
traffic
another
one
that
they
mentioned
for
control
of
the
control
plane
with
broadcast.
M
So
the
difference
is
in
version
one
compared
to
to
the
res
version
were
filled
from
a
based
on
input
from
from
the
last
meeting
and
minimis
discussion,
namely,
we
have
a
full
definition
of
how
to
configure
the
slot
frames
and
we
have
a
way
to
configure
different
hash
function.
To
make
this,
there
was
a
concern
that
was
raised
by
Mike
home
that
we
were
recommending
sax
as
a
hash
function,
that
we
made
that
configurable
and
we
have
a
burst
mode
to
handle
traffic
searches.
M
It's
basically,
you
can
see
it
as
an
extended
version
of
the
standard,
I
Triple
E
search
from
in
link
information
elements,
but
that
adds
a
few
fields
so
that
you
can
define
how
the
that
framed
our
maintained
so
which
node
to
hash
to
help
the
mackerel
eyes
off
when
you
want
to
compute
coordinate
which
hash
function
to
use
from
which
node
that
that
the
one
good
neighbors
for
which
not
to
do
to
do
so
and
how
to
filter
traffic
any
given
slot
frame.
That's
all
detailing
draft.
M
This
is
an
overview
of
the
traffic
filters
that
tell
you
again
how
which
traffic
goes
in
which
slot
frame,
so
you
can
segregate.
For
instance,
you
could
choose
to
say.
Oh
all,
TCP
traffic
goes
to
start
from
five,
but
then
all
I
simply
goes
to
a
different
one,
and
then
your
rules
can
depend
on
different
parameters
that
include
the
frame
type
with
the
rhetoric
as
broadcast
the
IP
protocol,
the
port,
etc
configuration
dissemination.
M
So
the
current
plan
is
that
this
configuration
is
disseminated
using
the
extended
becomes
the
EBS
as
one
more
information
element,
which
is
a
six-piece
signal
command,
and
this
can
be
done
in
two
ways.
One
is
so
it
would
be
done
in
EB
is
one
one
is
to
secure
the
eby's,
but
that
means
those
are
not
the
only
bits,
because
we
need
unsecured
bits
for
the
initial
joining.
So
that's
one
option
is
both
secured
and
unsecured.
It
B's
unsecure
for
initial
learning
and
secure
for
the
ASF
dissemination.
M
H
M
M
H
G
H
Can
you
can
use
a
key,
so
I
mean
in
the
link
layer
requirements
in
minimal
security?
We
say
that
the
pledge
has
to
accept
this
beacon,
even
though
it's
authenticated
it
and
it
does
not
have
the
key
in
order
to
get
synchronized
with
the
network.
It
accepts
this
beacon.
So
this
opens
the
vector
which
we
discuss
in
the
security
consideration.
M
H
M
Even
in
that
draft
is
the
burst
mode
so
that
you
can
handle
peaks
in
traffic.
So
when
you
have
a
given
slot
to
you
in
in
a
SF
start
frames,
you
typically
have
a
single
opportunity
to
transmit
in
a
restaurant
frame,
that'll
be
too
static
from
any
scenarios,
and
so,
if
you
have
friends
in
the
fragmentation,
you
might
have
like
10
packets,
an
imperfect
queue
that
you
want
to
dump
to
a
given
neighbor.
D
D
But
if
the
PD
are
between
a
and
B
is
relatively
low,
then
there's
a
high
chance
that,
on
the
first
transmission,
the
node
a
does
not
get
an
acknowledgment
at
which
point
the
burst
stops
right.
So
this
works
beautifully
well
with
high
PDRs
and
it's
kind
of
a
best-effort
tool
for
for
lower
PDRs.
Do
you
agree
with
that?
That's.
M
D
So
so
we
had
that
we
had
a
meeting
a
little
bit
before.
So
you
know,
as
you
know,
I
think
EF
has
has
a
bunch
of
cool
ideas
if
I
list
them
one
ideas
to
hash
the
MAC
address
of
the
know
you
want
to
talk
to,
and
so
you
have
a
automatic
cell.
You
know
a
rendezvous
cell,
where
you
know
that
that
that
node
is
listening.
D
That
allows
us
to
offload
the
shared
cell
on
the
minimal
slot
frame.
That's
one
second
one!
This
pending
bit
you
so
in
the
15
four
FCF
field.
You
said
the
pending
bits,
which
means
hey
I'm
I,
have
more
for
you
keep
listening
on
the
next
on
the
next
cells.
I
think
those
are
the
and
then
you
have
the
different
slot
frames
and
then
the
whole
configuration
of
it
with
II's.
That
might
be
a
need
not
in
Ibiza
titre.
D
So
I
think
it
is
very
complementary
to
msf,
and
so
we
discussed
the
idea
of
augmenting
msf
with
these
ideas,
but
of
course
it
has
to
be
worked
out
and
then
the
pending
bid,
it
being
such
a
kind
of
powerful
independent
tool
might
be
a
separate
document.
So
I
think
you
know
taking
the
raw
ideas
from
ASF
forking
that
having
one
depending
would
be
its
own.
You
know
document
that
is,
you
know,
generally
usable
and
then
rolling.
The
idea
of
sorry
hashing
mac
addresses
into
the
MSF
draft
I.
D
Think
in
my
mind,
makes
sense
rather
than
having
two
competing
SF's,
because
I
think
that
if
we
do
the
integration
well,
that
will
perform
better
than
if
we
had
the
two
SF's
side-by-side.
So
it's
kind
of
a
win-win.
That's
the
current
state
of
thinking.
We
had
the
discussion.
You
know
this
is
not,
as
almost
you
know,
Hatcher
I
could
sure
hat
off
any
any
comments
about
this.
Any.
H
Input
that
we
should
consider
so
I
just
have
I
was
just
reflecting
about
what
you
said
about
the
pending
bit
and
a
separate
document
I
mean.
So
you
want
the
mechanism
with
the
pending
bit
specified
in
a
separate
document,
but
then
we
will
also
need
to
schedule
the
cells,
so
this
belongs
to
the
SF,
because
it
would
be
perfect
if
it
would
have
the
SF
document
contained
that
contains
the
scheduling,
part
yeah.
So
it's
kinda
interleaved,
you
see,
and
you
see
my
point
I.
M
H
H
A
These
this
idea
of
having
more
burst
mode
was
discussed
a
number
of
times
long
ago
remaining
list.
So
the
I
would
support
that.
We
dig
these
three.
We
have
on
it
and
I
completely
agree
that
it
can
be
separated
for
from
MSI.
For
yourself.
One
thing
you
could
do
to
support
it
in
this
document
in
a
SMSF
is
to
allow
to
come
to
get
more
than
one
cell
in
in
the
slot
frame,
but
then
decide
with
the
more
bit
whether
other
I
used
or
not.
A
You
see
so
that's
my
own
so
to
Manisha
how
you
split
the
work
between
this
document,
which
allocates
the
cells
and
the
more
bit
is
that
you
may
allocate
more
than
one
cell
with
your
mechanism
defaulting
on
using
a
one,
the
first
one.
Oh
yes,
they
don't
have
to
be
in
the
right
order
right.
You
can
have
the
first
one
here,
the
second
one
here
etcetera.
A
So
you
order
them
and
based
on
your
mobile,
then
you
consume
them,
but
at
least
you
can
control
what
is
the
size
of
the
burst
and
how
the
burst
is
distributed
over
channel
and
time.
So
you
don't
have
to
have
them
conceived
contiguous,
which
I,
don't
really
like
so
benefiting
from
jch
is
distributing
them
all
over
the
place
using
one
and
if
the
mo
bit
is
set,
then
the
Bobby
document
will
explain
using
two
three
four
right.
So.
D
M
A
D
E
So
this
idea
comes
from
the
fact
that
we
have
a
synchronized
network
and
the
synchronized
Network
uses
a
let's
say,
virtual
counter
or
we're
12
element
that
provides
seen
relative
synchronization
between
the
nodes,
but
we
don't
have
a
global
preference
in
time
as
an
example.
If
we
have
two
different
sixties
networks,
coexisting
somewhere
and
they
are
sampling
data,
they
are
monitoring
something
and
we
want
to
time
standard
data.
We
don't
have
a
common
source
of
time
for
all
of
them.
E
They
have
different
absolute
seconds
numbers
counting
and
we
can
know
what's
going
on
in
one
network
what's
going
on
another,
but
not
one
to
the
other.
We
think
that
having
level
time
in
a
network
enables
many
other
use
cases
even
for
security,
so
we
thought
okay,
what's
the
what's
the
best
or
what
this
is
way.
We
have
to
transmitted
or
to
spread
global
time
in
the
notes
and
make
sure
they
keep
their
clocks.
With
this
global
time.
Sensor.
E
E
The
summary
for
those
that
have
not
read
it.
It's
a
very
simple
idea.
We
have
an
applied
to
note
that,
when
is
when
joins
the
network
through
the
minimal
security
mechanism
to
join
it
and
it
gets
to
the
GRC
and
the
GRC,
apart
from
giving
back
the
keys
and
the
short
address,
it
also
can
distribute
an
optional
element,
an
optional
object
that
contains
the
mapping
between
the
absolute
sequence
number
and
the
global
time,
and
it
is
what
is
defining
this
part
here.
So
this
extension
enables
no
joining
to
get
from
the
j.
E
Jc
RJ
R
see
an
absolute
sequence
number
as
a
reference
and
era
counter
and
the
same
census
in
NTP
seconds,
which
is
the
number
of
seconds
since
first
of
January
1900
same
as
NTP
and
diffraction,
which
is
the
number
of
Pico
seconds
in
the
last
in
the
last
second,
so
same
same
notion
as
NTP
protocol,
and
then
it
can
transmit
as
well.
Optionally.
E
Address
of
time
source
note
in
case
this
is
not
the
GRC
and
link
format
identifying
the
service
that
is
delivering
the
time
and
then
least
time
in
order
to
refresh
that
information.
So
some
the
note
can
specify
okay,
you
have
to
come
back
again
to
resync
after
that
that
time,
and
then
we
define
a
leap
second
option
as
well
in
case
there's
a
leap.
Second,
we
need
to
correct
it.
E
E
Carsten
asks
whether
what
is
this
link
format,
so
the
link
format
is
saying:
what
is
the
you,
let's
say
the
the
object
in
the
server
that
I
have
to
query
to
get
that
that
update.
It's
like
the
URL,
the
URI
yeah
in
getting
it.
So
this
is
configurable,
so
we
can
decide
if
we
it's
a
fixed
one
or
someone
wants
to
configure
the
name
as
it
is
optional.
My
thing
doesn't
heart.
D
So
this
is
thomas,
I
actually
retract
that
that
recommendation
yeah
yeah,
so
so
the
problem,
the
problem-
and
this
is
very
much
to
terrorists
point.
The
problem
is
that
you're,
ten
millisecond
time
slots
are
not
always
exactly
ten
millisecond
fine
shots.
If
you
have
a
very
fancy
dagger
root
which
is
linked
to
gps
or
something
even
better,
then
you
can
make
them
ten
milliseconds,
but
usually
those
things
are
implemented
on
cheap
microcontrollers
that
have
a
32
kilohertz
crystal.
D
Maybe
you
know
my
10
millisecond
types
of
is
10
point:
oh
two
milliseconds,
and
so
yes,
if
my
network
started
two
years
ago
and
at
the
your
system
tells
me
at
a
SN
0
that
what's
that's
what
time
it
is
my
a
SN
now
is
not
a
SN
times:
10
milliseconds
it
a
seven
times,
ten
point:
zero,
two
milliseconds
and
so
I'm
completely
off
so
I
completely
retract.
This
is
was
a.
D
This
was
a
error
I
I
made
so
so
I
think
it
makes
total
sense
for
the
update
to
contain
both
at
da
SN
that
much
it
is
that
time
and
then,
given
that
the
SN
is
not
always
I'm,
sorry,
the
slot
length
is
not
always
perfectly
is
10
milliseconds.
You
want
to
read
this
over
and
over.
So
if
you
go
back
to
your
previous
slide,
what
I
understand
is
the
Pledge
joins
the
network,
the
network
it
sends
it.
D
E
Sorry,
okay,
yeah.
The
second
point
was
what
you
mentioned
about
the
drift,
so
how
we
cope
with
the
drift
and
I
think
we
have
to
do
it
through
periodic
updates.
Unless
the
node
is
like
the
dark
root
is,
has
a
GPS
and
it
can
ensure
perfect
timing
and
then
through
the
optional
fields.
You
can
indicate
that
so,
if
you
don't
send
the
lizzie
time,
for
example,
you
can
assume
that
you
will
never
synchronize
again.
F
E
Three
times
ton
data
you
mean
area,
so
what
you
want
to
avoid
is
time,
stamping
based
on
a
SN,
imagine
a
wireless
seismic
data
acquisition
system.
You
know,
reading
vibration,
to
look
for
water
or
oil,
and
you
you
tak
every
reading
from
the
ADCs,
and
you
want
to
transmit
that
you
can
tag
them
with
the
SN,
but
then
at
the
server
side
you
need
to
map
a
send
to
time
and
do
this
conversion
with
a
post
processing
in
this
case
having
local
time
I
think
is
useful.
Okay,
thank
you.
D
This
is
a
use
case,
does
not
pull
out
of
thin
air
right.
This
is
a
real
use
case
that
I've
come
across,
so
Seesmic
acquisition
systems
where
you
want
to
measure
at
the
same
time,
so
you
want
to
have
them.
You
know
a
bunch
of
those
that
want
to
measure
the
same
time.
Unfortunately
they're
part
of
different
networks
right,
and
so,
if
those
networks
are
not
somehow
coordinated,
if
the
nose
will
know
what
real
time
it
is,
they
will
not
trigger
the
area
TC
at
the
same
time.
So
this
is
a
trivial
trivially.
H
Melissa
so
I,
just
just
to
add
to
the
last
point.
I
think
this
is
also
very
useful
for
security
for
the
validation
of
certificates,
as
we
don't
want
to
rely
that
like
when
we
receive
a
certificate
from
an
Internet
client
or
a
server,
depending
on
what
to
know
the
act
that
it
has
to
contain.
The
SNSD
in
the
expiration
date.
D
Thomas
again,
if
we
start
going
into
that
route
to
validate
certificates,
it's
really
important
that
we
trust
that
information,
because
now
it's
a
vector
for
attacking
the
whole
thing.
So
what
this
means
is
that
that
you'd
better
be
sure
where
you
get
the
information
from
and
so
as
part
of
the
minimal
security
solution.
We
have
a
secure
session,
that's
open
to
the
jrc.
That
is
that
we
trust
right.
H
Militia
so
just
plus
one
on
Thomas's
response,
also
just
I'm.
Looking
at
the
this
support
structure,
now
I
mean
in
the
you
have
the
mandatory
parameters.
Basically,
the
first
time
when
the
pledge
joins,
you
get
the
time
you
get
the
global
time
from
the
DRC
yeah,
so
it
means
in
this
case
I,
don't
see
the
purpose
of
having
the
the
optional
parameters
of
having
the
node
now
contact
a
different
server.
H
If
you
had,
the
jrc
already
take
care
of
that,
so
it
could
have
just
a
separate
session
with
the
network
server
and
that's
authenticated
TLS
whatever,
so
you
just
need
in
the
trust
model.
You
just
need
to
trust
the
DRC
and
not
now
to
extend
it
to
the
to
the
time
server.
Okay,
so
you're
saying
that
it's
always
these
years,
I
I
think
so
I
mean
we
need
to
work
this
out
a
bit
more,
but
I
think
it's
I
think
it
makes
sense.
Can.
A
We
sorry
guys,
can
we
this
great
discussion
and
we
really
want
to
follow
up,
but
we
have
only
ten
minutes
left.
So,
oh
I'm,
sorry
I
would
like
to
cut
the
line
and
let
Michael
speak
but
yes,
I
mean
we'll,
have
a
great
discussion,
the
meaningless
than
that
and
we'll
have
insurance.
So,
let's
wrap
yes.
D
So
to
wrap
up
officially
so
I
think
Charlie
I
think
it's
it's
it's
too
early
to
call
for
group
adoption,
because
it's
a
load
of
charge,
it's
very
simply
but
I-
think
there's
clear
interests
about
this
work.
What
this
means
from
us
as
Kyle
is
that
we
need
to
figure
out
how
this
can
be
rolled
in.
There
are
some
security
things,
and
but
so
it
might
mean
adding
an
item
to
our
Charter
to
just
deal
with
that
and
then
but
I
think
you
know
I
incur.
D
K
K
The
joint
process-
we
have
this
issue
that
you
have
to
be
able
to
find
a
machine,
another
node
in
which
to
join,
and
so
we
have
beacons
that
are
sent
out
by
anything
lots
of
machine
lots
of
nodes,
and
we
want
to
be
able
to
indicate
which
ones
actually
support
the
join
functionality.
And
then
life
is
grown.
So
what's
the
problem,
we
have
a
big
network,
possibly
many
pans.
K
We
have
blue
networks
that
have,
you
can
see,
are
connected
on
a
backbone
and
we
have
a
green
network
which
may
or
may
not
be
friendly
and
the
nodes.
There's
two
brown
nodes
there.
They
hear
many
many
beacons
from
many
places
when
they're
doing
the
join
process.
If
they've
tried
the
blue
network,
it
would
be
nice
if
they
didn't
try
the
blue
network
six
times
in
a
row,
thinking
they're
all
different
blue
networks,
but
in
fact
went
on
to
try
the
green
network,
because
maybe
the
green
network
has
really
the
better
network
or
vice-versa.
K
We
don't
know.
So
that's
one
of
the
issues.
The
second
issue
is
well.
It
might
be
that
attaching
at
certain
points
to
the
network
arm
from
it.
For
doing
the
joiner,
enrollment
process
would
be
better
than
other
ones,
because
there's
more
bandwidth,
because
there,
the
mission
that
note
the
neighbor
has
more
untrusted
neighbor
cache
entries
available
a
variety
of
different
things.
So,
in
the
process
of
doing
this
work,
a
number
of
people,
including
my
co-author
on
this
I,
believe
got
confused
by
the
word.
Join,
it's
my
fault,
I
think
join
is
being
enrollment.
K
This
is
how
you
get
the
keys
to
the
network.
This
is
how
you
start.
Having
done
that,
you
would
then
decide
how
to
connect
to
the
doe
deck.
So,
for
instance,
I
can
use
this
laser
pointer
on
the
thing
here,
but
no
one
else
will
see
it.
You
know
you
this
node.
Is
you
here
here
here
here
and
once
it's
got
the
keys,
it
could
decide
how
to
connect
many
of
those
places,
malicious,
malicious
just
to.
H
K
That's
what
I
always
thought
it
was
yeah.
So
the
point
is
that
there
are
some
people
in
the
last
couple
months
that
want
to
use
it
in
the
terms
of
parent
selection
and
so
I'm,
urging
them
to
pick
the
word
parent
selection
for
that
that
discussion
and
that
and
that
I
will
use,
join
slash
enrollment
from
now
on,
so
that
it's
clear,
I'm.
H
K
Want
to
point
out
that
there
is
a
distinction
between
that
and
that's
why
I
renamed
the
documents
at
some
point
just
so
that
it
can
be
actually
sure
what's
going
on.
So,
despite
having
done
that,
there
was
still
a
claim
that
we
would
like
to
do.
Parent
selection
in
advance
of
enrollment
and
I
didn't
use.
The
word
join
either
in
either
statement.
Okay,
so,
and
it
with
that,
it
might
be
that
you
would
like
to
join
pan
one
or
green
pan.
K
Then
it's
sorry
you'd
like
to
enroll
in
green
pan,
rather
than
in
blue
pen,
based
upon
some
metrics
that
you
observe
about
these
things.
So
I'm
not
terribly
happy
about
that
I'm
gonna,
say
I!
Think
it's
mixing
too
many
too
many
things
at
into
a
layer
too.
It's
it's
disclosing
a
bunch
of
stuff,
but
despite
that
in
my
document,
I
have
put
these
two
things
rank
priority
and
a
pan
priority,
which
has
something
to
do
with
join
things
and
I
fixed.
K
This
overlap
in
the
in
the
in
the
the
pages,
but
I
know
that's
just
a
little
bit
hard
to
read
so
so
the
question
is,
you
know:
is
this
interesting
to
people
and
what
I've
heard
is
that
there's
a
number
of
people
that
are
interested
in
this
kind
of
stuff
and
I
think
that
you
need
to
make
a
case
for
why
it's
interesting
and
that's
this
part
of
the
problem?
Ok,
what's
there
all
I
care
about?
K
Is
this
proxy
priority
and
the
reason
I
hate
care
about
that
is
because
a
different
different
of
those
join
proxies
may
have
different
amount
of
resources
and
it
makes
sense
for
them
to
say
I'm
not
really
available
right
now
for
for
enrollment
or
I
am
very
available
for
enrollment.
You
get
much
better
service.
K
If
you
connect
to
me
okay
and
then
the
other
thing
is
that
the
network
may
just
want
to
decide
that
there
are
times
in
which
the
network
does
not
have
capability
to
support
things,
in
which
case
it
would
sent
that
proxy
priority
to
127
and
say,
although
you
know
I'm
here,
I'm
a
beacon
if
you've
got
a
conversation
with
me
already
we're
gonna
continue.
You
probably
shouldn't
start
with
me
because
I'm
not
a
good
Ewing,
so
tomorrow
we're
going
to
talk
about
the
role
part,
which
is
how
do
we
fill
in
these
things?
K
How
do
we
communicate
these
things
down,
but
I'm
just
going
to
stick
to
the
jump
to
the
discussion
and
what
are
we
here?
So
what
is
it
we
want
to
put
in
this
in
this
document?
We
need
to
decide
whether
we
actually
want
to
solve
all
of
those
problems
at
once
or
not
whether
we
want
to
adopt
the
document
or
not,
as
I
said
I'm,
not
I'm,
not
enthusiastic
about
doing
that,
but
I'm
listen
to
prepared
to
listen
to
arguments
for
why
goals
and
role
so
questions
discussions.
I
know
we're
pretty
much
out
of
time.
K
D
Yeah,
so
so
Tomas,
if
you
come
back
to
those
slides
to
this
light,
where
you
have
the
different
priorities
I,
you
know:
I
I,
I've
reviewed
this
draft
and
and
sent
you
are
you
on
the
mailing
list?
Yeah
I'd
like
to
have
a
discussion
about
those
three
or
four
different
priorities:
those
three
priorities
and
the
network
ID?
How
exactly
is
it
used.
K
I
would,
for
instance,
take
a
value
which
the
network
might
express
through
the
role
for
the
other
thing,
and
to
that
I
would
add
some
indication
of
how
busy
I
am
whether
it's
based
on
battery
or
the
number
of
neighbor
cache
entries,
untrusted
ones,
that
I'm
willing
to
devote
towards
a
proxy
activity
and
then
I
would
come
up
with
a
number
so
that
the
network
itself
is
going
to
give
me
a
base
number.
Maybe
it's
50,
okay
and
I'm
gonna
add
you
know
the
number
to
that.
K
K
K
Other
people
asked
for
this,
whereas
this
pan
priority,
which
would
somehow
be
set
to
indicate
which
pan
ID
is
more
desirous
for
whatever
and
not
and
I,
can't
speak
a
lot
to
how
that
will
be
used
in
parent
selection
and
then
a
rank
priority
which
would
somehow
be
derived
from
rank
and
I
can't
say
how
that
people
want
to
do
that.
Those
are
the
two
numbers
that
I've
been
told
would
be
valuable
to
have.
K
Finally,
the
network
ID
is
a
truncated
sha-256
of
probably
the
dough
tag
ID,
and
that's
just
so
that
you
can
see
that
all
the
green
networks
are
green
and
all
the
blue
networks
are
without
action,
revealing
the
anything
specific
because
it's
just
a
truncated
hash.
So
it
doesn't
really
say
a
lot,
but
it
does
tell
you
that
that
this
this
transitions
from
a
blue
node
and
this
one's
also
from
a
blue
mode,
because
they
both
went
back
to
the
same
dough
tag
ID.
So
they
both
announced
it.
K
D
B
K
K
Would
be
wonderful
if
you
want
to
tell
me
what
what?
What
is
it
you
would
like
to
do
with
with
with
these
extra
fields
and
and
how
you
think
it's
it's
valuable
and
and
and
I
will
respond
to
to
maybe
the
security
it
doesn't
work
that
way.
So
that's
that's
the
conflict
that
I
think
I've
had.
Is
that
I
think
that
the
security
is
not
doesn't?
If
you
you
can't
you
can't,
you
don't
want
to
reveal
that
information
unless
you've
already
joined
unless
you've
already
enrolled
on
the
network.
D
K
The
conversation
tomorrow
and
role
is:
how
do
we
configure
the
priority
proxy
priority
within
the
ll
within
the
RPL
dough
deck?
Okay?
So
that's
a
different
kind
of
question
because
it
has
it
doesn't
really
matter
what
we
put
in
this
thing
or
there
because
I
know
I
want
a
proxy
party.
We're
done.
Thank
you.
Yeah.
