►
From YouTube: IETF101-PALS-20180319-1550
Description
PALS meeting session at IETF101
2018/03/19 1550
https://datatracker.ietf.org/meeting/101/proceedings/
A
A
C
D
C
In
here
well,
he's
ready
sittings
happy
with
it,
hello,
everybody,
I'm,
Andy
malice.
This
is
Stuart
bright,
that
is
Dave
Schoeneck
rope
and
we're
here
for
what
may
in
good
probability,
be
the
last
meeting
of
the
pals
working
group,
swish
I'll,
see
so
as
I'm
sure
you've
you've
you've
heard
by
now.
Unless
this
is
your
first
meeting
today,
there
is
a
new
note.
Well,
so
this
is
the
grand
new
note.
C
C
So,
first
of
all,
we
have
had
one
new
RFC
since
the
last
IETF,
which
is
our
C
8
3
3
8,
since
we
reformed
pals
out
of
p3
in
November
of
2015,
we've
published
17
RFC's,
so
we've
done
a
good
job.
Clearing
out
our
our
cue
and
our
Charter
and
I
would
like
to
give
a
huge
round
of
thanks
to
Deborah,
because
none
of
that
would
have
been
possible
without
her
help.
So
thank
you,
Deborah
and
and
as
I
said,
and
we
also
have
one
of
the
draft.
C
That's
still
on
the
air
see
under
this
cue-
that's
pals
pizza,
MPP,
wls
beeping,
so
that
one
should
be
popping
out
shortly
and,
as
I
said,
we
have
one
working
group
draft.
That's
the
draft
IHF
pals!
Even
the
control
word!
That's
on
today's
agenda,
so
I
won't
say
anything
else
about
it
and
there's
one
other
thing
to
bring
to
the
working
groups,
attention
which
is
actually
something
which
is
going
to
be
discussed
more
in
the
MPLS
working
group
session
on
Thursday
and
lower
is
available
here
to
take
any
questions
that
you
might
have
on
this.
C
This
is
a
draft
which
is
co-authored
by
the
MPLS
Wiccan
Group
co-chairs
and
the
PALS
Working
Group
co-chairs
and
has
to
do
with
the
fact
that
LDP,
the
LDP
specification
still
specifies
the
use
of
md5
for
authentication.
However,
the
security
area
loves
to
point
out
to
us
whenever
anything
comes
up
that
that
references
LDPE
in
a
draft,
the
fact
that
they
don't
like
md5
anymore
they've,
they
basically
told
us.
C
In
fact,
they
tell
us
a
while
ago,
back
in
RFC,
59
25,
that
md5
is
really
no
longer
the
considered,
secure
and
protocol
should
be
looking
to
alternatives
to
md5.
So
BGP
has
already
taken
care
of
this
and
some
number
years
ago,
I
think
it
was
like
seven
years
ago,
we're
already
BGP
specified
the
use
of
TCP
AO,
which
is
the
TCP
authentication
option,
as
a
replacement
for
md5,
and
what
we've
been
looking
at
is
for
LDP
is
following
in
beach
B's
footsteps.
C
In
fact,
those
of
us
who
are
in
the
leadership
in
the
routing
area
are
kind
of
struggling
to
try
to
find
actual
implementations
and
deployments
of
TCP
a
Oh,
even
one,
some
number-
you
know
a
good
number
of
years
after
it
was
written
and
specified
and
specified
for
PGP,
so
we're
trying
to
coordinate
this
across
the
routing
area.
You
know
this
is
an
issue.
That's
not
just
an
LDP
issue.
It's
it's
a
lot
bigger
than
that.
C
D
Discussions
and
Jeff
has
been
doing
some
good
work
and
had
a
discussion
with
the
operators
on
something
yesterday
and
we're
kind
of
getting
the
impression
that
actually,
the
operators
don't
really
care
and
they
just
use
md5
as
a
checksum
and
the
security
ADEs
didn't
really
quite
understand
what
we
were
trying
to
do
far
as
I'm
concerned.
I
think
it
so
long
as
there
is
peace
breaks
out
and
people
don't
hold
our
drafts
to
hostage
I'm
happy
with
any
of
these
any
resolution.
So
in
some
ways
this
is
a
stalking
horse
to
either
producing.
D
No,
so
so,
there's
two
sides
of
this
argument.
The
two
sides
of
this
discussion
are
md5
is
not
good
and
I'll
find
a
better
algorithm,
including
all
of
the
other
bits
and
pieces.
We
really
need
to
use
TCP,
IO
or,
and
actually
we
don't
care.
We
use
Mac
sec
to
secure
all
these
things
anyway.
Md5
is
only
there,
as
is
a
better
checksum,
so
we
don't
need
any
of
this
now
I,
don't
care.
I
will
faithfully
drive
this
piece
of
work.
You
know
we
all
the
work.
D
D
The
they
think
the
key
thing
is
there
are
not
there's
a
spectrum
of
opinions.
The
function
of
this
drop
I
think
is
to
get
us
into
a
position
where
drafts
are
not
held
hostage
over
this
issue
and
I
hardline
concerned
will
worked.
We
should
work
to
whatever
resolution
gets
us
into
a
position
where
we
can
carry
on
publishing
drafts.
F
G
No,
don't
no,
please
so
two
things
about
the
access
or
some
other
types
of
single,
hawk
security
in
any
purple.
That
goes
multiple
hops.
You
know,
obviously
that
doesn't
work
and
the
I
know
of
one
protocol
that
was
recently
a
fruit.
We've
got
the
premise
that
it's
always
going
to
be
used
1aqaq
and
what
went
through
the
security
area
was
that
either
you
have
to
run
it
through
CLS
or
you
have
to
use
the
generalized
CTL
security
mechanisms,
which
is
a
great
name
for
set
it
to
55
and
make
sure
it's
received.
G
I
H
H
But
number
two:
so
what
are
you
forcing
anyone
who
uses
LVP
to
always
go
over
even
if
they
need
someone
to
do
something
else
and
in
any
case
the
LDP
is
not
even
Ethernet
labor
level
protocol.
Therefore,
even
if
someone
uses
it,
it's
completely
irrelevant
and
you
have
to
solve
this
problem
and
if
you're
saying
you
don't
really
want
to
solve
it,
just
political
issue,
that's
fine,
but
I
think
it's
a
problem
which
can
be
easily
solved.
There
are
algorithms
that
can
solve
this
very
nicely.
D
So
next
slide:
please:
okay,
we
just
do
it.
Actually,
no
I
don't
have
mine
here,
I
get
very
good.
So
what
we
did
was
we
took
the
feedback
that
we
got
at
the
last
IETF
and
applied
it
to
the
text.
We
got
a
bit
more
feedback
and
we're
hoping
that
this
is
the
last
opportunity
is
the
last
time
we
need
to
discuss
this
in
the
in
the
working
group.
Okay,
so
next
slide.
D
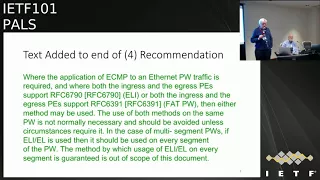
So
we
added
the
following
text
that,
where
the
application
to
the
end
of
section
4,
which
basically
says
where
the
application
will
be
CMP
to
an
Ethernet
pseudo,
a
trapeze
return
with
the
application
of
EDF
of
ecmp
is
required
and
we're
both
the
ingress
and
the
egress
pease
support
the
ill
I
or
both
the
ingress
and
the
egress
pease
support.
Fact.
Then,
either
method
may
be
used.
The
use
of
both
methods
on
the
same
pseudo
wire
is
not
normally
needed
and
should
be
avoided
unless
circumstances
require
it.
In
the
case
of
multi
segment
pseudo
wires.
D
D
Ok,
next
slide,
then
please
they
note
comment.
We
got
was
that
we
didn't
actually
specify
I
where
we
put
some
of
these
labels,
so
I
added
the
text
that
the
PW
label
is
pushed
before
the
LSP
label
as
the
ERI
entropy
li
labels
are
part
of
the
LSP
layer
rather
than
part
of
the
PW
layer
they
are
pushed
after
the
PW
layer
has
been.
You
know,
leg
has
been
pushed
the
little
diagram
under
there
is
to
illustrate
it
for
the
room.
It's
not
part
of
the
text.
D
I
think
it's
quite
clear
that
if
you
say
something
is
pushed
after
something
else
where
it
goes.
Apparently
there
was
a
comment
on
the
list
about
us
not
specifying
which
order
we
would
push
these
labels.
Yes,
yes,
the
SDS,
yes,
and
that
I
think
the
text
is
agree.
Just
the
text
agree
with
what
you're
pretty
obvious
is
yakov
I'm,
not
picking
on
you,
these
weren't
here
last
night.
H
D
Slide
please
so
the
old
text
at
the
end
of
operation.
This
was
because
some
people
were
concerned
about
us
saying
to
remove
this
in
the
long
term
and
hence
reduce
the
operational
cost
of
investigating
problems
associated
with
the
incorrect
forwarding
of
packets
with
over
PWS,
not
using
the
CW
control
word.
It
is
recommended
that
the
equipment
does
not
support
the
youth
that
does
not
support
the
control
where
we
phase
out
of
operational
use.
There
were
a
number
of
people
who
objected
to
this.
D
D
D
D
B
D
H
D
D
D
D
H
D
D
However,
deduction
of
the
payload
type
in
this
way
is
not
an
exact
science
and
where
and
where
a
packet
that
is
not
I'd,
be
mistaken
for
an
IP
packet,
the
result
can
be
package
delivered
out
of
order
yeah
next,
please
miss
ordering
of
this
type
can
be
difficult
for
an
operator
to
diagnose.
That's.
Why
we're
here?
That's
why?
Having
this
whole
conversation
Ignace
isn't
here,
but
he
has
spoken
to
lots
of
operators
about
it.
D
Operators
therefore
need
to
be
careful
in
enabling
care
capability
that
allows
the
information
gleaned
from
packet
inspection
past.
The
control
word
to
be
used
for
any
ecmp
calculation,
so
this
is
not
as
hard
and
fast
as
get
rid
of
the
stuff
that
doesn't
that
behaves
like
this.
It
is
saying
just
be
careful.
We
have
warned
you
your
honor.
H
You
know
the
original
sin
having
to
do
with
this
control.
Word
came
from
another
large
vendor
who,
when
look
at
I
said
the
control
word
should
be
mandatory
said
no.
We
can't
do
that
because
the
implementations
and
now
we're
stuck
with
it.
So
why
are
we
going
to
the
same
problem
again?
We
should
say
what
we
recommend
should
be
done,
and
if
someone
wants
to
do
something
else,
it's
their
father.
D
H
K
K
D
K
H
D
They
have
to
turn
the
feature
on.
If
you
know
it
is
absolutely
benign
in
your
application,
and
it
is
the
way
to
get
the
extra
bandwidth,
then
you
know
I
mean
what
we're
gonna
do
you
know,
so
we
I,
don't
there's
any
text
we
could
write
in
here.
That
would
stop
vendors,
putting
such
things
in
the
in
their
equipment.
If
that,
if
that's
what
their
customer
asked
for
well,
do
anything
that
their
customers
will
pay
the
money
for
yeah.
H
In
there,
since
we
know
that
vendors
will
do
anything,
their
customer
is
for
then
don't
bother.
Writing
RFC's,
because
there's
no
one's
gonna
read
them
anyway.
Where
should
we
should
be
saying
what
we
believe
is
the
right
thing
to
do?
If
someone
thinks
that
they
have
a
local
optimization,
which
is
not
compliant
to
the
IEF
way
of
looking
something,
then
they
do
it
at
their
own
risk
and
be
done
our
saying,
you
should
be
very
careful
because
you're
doing
silly
things.
M
M
K
N
N
H
Yes,
all
you
have
to
say
is
for
inflammation.
You
should
know
that
there
are
implementations
out
there
who
do
so,
and
so,
yes,
you
could
even
put
in
parenthesis
highly,
not
recommend
it.
That's
the
hug,
don't
start
saying
be
care.
You
gave
the
information,
people
understand
what
it
says.
Your
dog
I,
don't
like
I,
saying
any.
Even
the
form
of
document
be
care.
M
E
M
D
M
D
C
D
D
This
sentence,
which
is
highlighted
well,
we
were
we
happy
up
to
the
point
where
I
said:
miss
ordering
of
this
type
can
be
difficult
for
the
operators
to
diagnose,
which
is
actually
you
know
why
we
got
it.
Why
we're
here?
Because
the
parents
they
didn't,
find
it
difficult
and
spent
hours
trying
to
do
it.
D
H
H
D
H
M
M
M
C
B
D
D
J
H
M
I
L
B
D
D
So
well,
so
that
you
see
the
next
thing
I
could
see,
we
can
do
and
not
to
do,
there's
a
number
of
ways,
but
it'd
be
kind
of
nice
to
finish
this.
So
one
of
the
approach,
one
things
to
do
is
to
try
and
get
this
text
to
be
what
the
people
in
the
room
would
like
to
see
and
then
ask
Matthew
well
and
then
put
it
in
last
call
when,
of
course,
everyone
will
have
the
opportunity
to
comment
on
it
and
when
we
will
be
bound
to
address
each
of
the
comments.
D
C
D
C
What
I'm
going
to
do
is
I'm
going
to
show
you
some
text
that
I've
put
together
for
a
liaison
which
is
going
to
be
going
out
to
some
of
our
sto
partners
of
the
broadband
forum,
ITT
studying
15
working
party,
3m,
EF,
I,
Triple,
E
802
at
one
TSN
and
I
Triple,
E
rack
and
Glen.
It's
great
that
you're
in
the
room
and
Pat
as
well.
I
have
good
email
contacts
with
the
right
people
to
send
this
to
for
everybody,
but
the
rack
so
do
either.
K
K
J
C
So
what
the
liaison
is
gonna
say
is
on
two
slides
here
and
basically
it's
kind
of
a
long
liaison
just
because
we
figured
that
a
lot
of
the
recipients
don't
have
the
background
knowledge
of
what's
going
on.
So
we
basically
just
wanted
to
summarize
the
contents
of
the
draft
in
a
couple
of
paragraphs
just
so
they're
aware
of
what
was
going
on
it
and
what
we're
asking
of
them
so
Sudha.
Why
encapsulation
well?
Do
people
just
want
to
read
it
or
they
want
me
to
read
it
or
should
they
just
give
people
a
chance?
C
B
C
K
K
O
K
There's
no
way
the
randomisation
people
are
not
gonna
use
our
gonna,
throw
out
one-eighth
of
the
addresses
when
they
randomized
and
choose
another
one
and
there's
no
way
we're
gonna,
throw
out
at
one-eighth
of
what
we
can
assign.
So
it's
just
so
you're
telling
us
that
there's
a
draft
online
that
talks
about
this
and
weren't
people
about
this
and
then
you're
saying
that
we
should
be
aware
of
the
draft
exists.
Yes
exactly
so,
okay,
so
you're,
not
you're,
not
expecting
any
kind
of
response
or
whatever
I
guess.
I
guess.
C
M
C
P
P
P
N
P
D
Q
H
D
C
Okay,
is
there
anything
else,
anyone
would
like
to
bring
up
four
pals
while
we're
here,
we
still
have
a
little
bit
of
time.
If
not,
I
would
like
to
thank
you
all
for
coming
to
what
may
have
been
the
last
meeting
of
pals
and
for
coming
to
pals
and
pee
wee
three
before
that
for
all
these
years
and
I
think
we're
adjourned.
