►
From YouTube: IETF101-6LO-20180322-1330
Description
6LO meeting session at IETF101
2018/03/22 1330
https://datatracker.ietf.org/meeting/101/proceedings/
A
B
B
C
C
We
also,
we
already
announced
in
the
mailing
list
that
our
secretary
James
Sudhir
has
moved
on
to
other
responsibilities.
I
just
wanted
to
announce
it.
We
wanted
to
announce
it
again
and
we
wanted
to
thank
him
for
his
service
so
going
forward.
We
have
a
very
tight
schedule
today
in
the
agenda
and
if
you
look
at
the
agenda
and
see,
if
you
have
any
comments,
so
we
will
try
to
switch,
but
we
will
start
with
the
6lowpan
and
the
SG
review
presentation
and
then
we'll
follow
up
with
other
two
updates
on
the
nd
related.
C
C
Yeah
I
think
that,
because
everything
is
on
this,
one
take
you
Center,
so
your
last
presentation
in
her
information-sharing
to
the
six
low
working
group
that
will
be
moved
up,
yeah
and
just
spend
five
minutes.
Okay,
so
we
and
also
attend.
We
have
Benjamin
from
Etsy
from
plaque
tests.
I
think
they
are
doing
some
practice.
They
were
here
for
IETF
hackathon
and
they
want
to
talk
about
their
test
cases
and
future
plans.
D
B
B
C
Okay,
so
the
draft
status
for
working
group
since
last
I'll
give
we
have
RFC
6775
update
to
that
is,
is
GED
field
and
the
comments
were
address
backbone.
Router
is
preparing
for
a
working
group
last
call
and
six
low,
AP
and
D
work
is
in
progress
and
really
mesh
Carla,
so
send
the
updated
status
about
the
implementation
and
the
progress
of
the
draft
to
the
mailing
list.
So
with
that
document
also
is
in
progress.
C
C
C
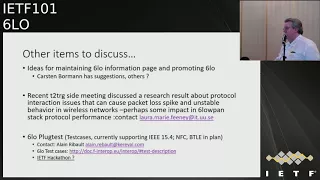
So
that
brings
to
the
last
page
and
we
are
going
to
discuss
some
of
the
some
of
the
items
that
are
probably
miscellaneous,
but
things
are
also
important.
One
of
the
things
is
that
Carsten
mentioned
to
the
chairs
offline,
and
we
also
discussed
in
today's
IOT
directorates
meeting
that
lot
of
the
thing
time.
We
do
develop
protocols
over
here
and
we
don't
see
much
deployment
out
there
and
also
we
don't
have
a
good
6lo
information
page.
C
We
key
to
provide
details
on
the
implementation
or
what
exactly
we
are
doing,
how
it
can
be
applicable,
so
Carsten
used
to
maintain
a
good
6lowpan
page,
but
that
has
now
expired
or
taken
away.
We
are
looking
for
volunteers
to
help
us
out
on
updating
some
of
the
materials.
So
Kirsten
do
you
want
to
say
anything.
D
Yeah
cuz
more,
this
actually
came
up
in
it
in
a
class
when
students
who
had
already
sown
seeing
pages
like
seaboard-
oh
and
quite
a
technology
asked
me,
is
there
something
like
this
for
six
No
and
there
is
nothing
like
this
for
six.
No,
there
used
to
be
the
old
6lowpan
dotnet,
but
maybe
something
that
that's
really
just
a
landing
page
with
lots
of
useful
links
to
implementations
words
and
to
reference
documents
would
be
useful.
D
So
if
you're,
not,
if
you
don't
know
seaboard,
Oh
or
the
Corp,
the
technology
just
just
go
there
and
have
a
look.
It's
pretty
low
effort
to
run
such
a
site.
We
put
this
on
github,
so
actually
we
help
people
have
updates,
they
usually
just
send
apoyo
requester
hints,
you
can
just
merge
that
and
then
you
are
done
so
I.
Think
it's
relatively
easy
for
us
to
do
that.
But
of
course,
will
require
a
little
bit
of
work
to
collect
the
initial
content
of
that
site.
C
Please
contact
the
chairs
and
Kirsten
Thank
You
Kirsten
and
for
the
sake
of
the
time,
I'll
just
go
quickly
for
the
second
and
third
bullet
point.
There
was
recent
t2
RT
side
meeting
where
there
was
a
research
presentation
which
showed
that
there
are
some
issues:
performance
issues
due
to
the
protocol
interruption
in
the
wireless
networks
and
their
lyrics.
They
expect
that
there
might
be
some
impact
in
6lowpan
stack
protocol
performance,
although
nothing
has
been
identified
that
we
know
of
Laura
Mary,
Feeney
I,
don't
know
whether
she's
here
okay.
C
So
she
is
the
contact
for
that
research
and
if
you,
if
you
are
more
interested-
and
if
you
like-
to
provide
some
more
information
to
the
mailing
list,
Laura
please
do
and
so
you
we
will
follow
up
from
there.
So
the
last
point
is
six
low
o'clock,
taste
test
cases
and
they
they
included
in
the
slide
contact.
Primary
contact
is
Alan
reball
and
they
currently
support
eight
or
2.15
dot
for
NFC
and
ET
alien
plan,
and
they
were
are
interested
in
doing
any
participate
in
IETF,
hackathon
and
practiced.
E
So
I
have
about
with
alpha
level
to
discuss
four
drafts,
which
are
really
saying
a
single
story,
and
the
story
starts
with
the
update
of
the
6lowpan
neighbor
discovery
protocol.
The
goal
of
the
whole
story
put
together
is
to
enable
a
large
building
or
large
factory
to
have
small
devices
which
just
support
6lowpan,
6lowpan
and
e,
and
that's
it
and
those
devices
would
be
able
to
move
seamlessly
inside
the
whole
factory
join
different
route
over
the
other,
go
whatever
shape
that
takes
and
maintain
their
routings
without
having
to
remember
the
IP
address,
etc.
E
Yes,
so
so,
basically,
there
are
a
number
of
elements
that
need
to
be
put
in
place
in
order
to
enable
the
whole
story
that
I'm
talking
about
it
looks
simple,
but
actually
it
takes
a
lot
of
effort
to
get
there,
because
you
have
to
have
a
number
of
those
right
over
networks
to
appear
as
a
single
network
for
the
moving
device.
The
device
has
to
be
able
to
move
without
remembering
without
reforming
a
security,
Association,
etc,
and
it
has
to
be,
it
has
to
have
a
very
simple
host
side
implementation.
F
E
So
you
know
what
I
don't
I
stop
my
story,
because
I
just
have
an
hour,
so
I'm
gonna
skip
the
backbone
watery
because
nothing
much
change
there.
I'm
going
to
talk
mostly
about
the
iesg
review
of
the
RFC
6775
update
and
I
have
a
few
questions
and
she
validation
I
need
to
be
made
by
the
working
group,
because
number
of
thing
have
changed,
and
that
also
applies
to
the
address
protection
draft.
There
are
number
of
things
which
have
changed
and
I
want
to
make
sure
that
the
working
group
is
happy
with
what's
going
on.
E
E
So
this
it's
not
a
that's
okay,
I'm
skipping,
the
previous
slide.
You
won't
be
surprised,
so
there
is
a
group
of
three
documents
at
6lowpan
which
are
the
update
itself,
which
tells
you
about
the
changes
we
are
making
to
six
leopard
ND.
Then
the
address
project
project
protection
thing,
which
is
basically
Savi
protection
for
six
weapon.
E
So
how
do
you
protect
address
against
somebody
wanted
to
steal
your
dress
Wendy,
and
how
do
you
prevent
somebody
sending
packets
or
signals
and
dress,
which
is
which
belongs
to
you,
and
the
last
draft
is
the
backbone
router,
which
is
as
I
mentioned
earlier,
as
you
want
to
be
of
this
build
a
big
network
with
multiple.
What
about
you,
dogs
or
whatever,
that
is,
and
of
an
Ethernet
or
some
type
of
I
spin
network
interconnect
with
these
routers
they'll
be
ours.
How
do
you?
E
What
operation
do
you
do
if
you
have
classical
nd
on
the
backbone?
So
it's
really
interaction
of
a
classical
nd
on
the
backbone
and
the
6lowpan
ND
/.
Whatever
protocol
that
you
may
have
on
the
6lowpan
network,
there
is
a
fourth
document
that
I
will
present
at
the
end,
which
is
how
that
works
with
ripple.
So,
at
the
end
of
the
day,
when
you
take
those
four
documents
together,
you
effectively
can
be
out
this
network,
which
spans
this
the
big
factory
with
thousands
and
thousands
of
devices,
and
they
all
reach
the
nearest
gateway.
E
But
they
so,
let's
see
now,
let's
go
through
the
changes
that
we
made
since
the
iesg
review
started.
So
the
first
thing
was
naturally
consequence
of
the
LSU
review
itself,
but
was
the
consequence
of
the
work
which
is
happening
with
the
address
protection
thing,
something
with
this
case
very
early
in
the
six
up
and
energy
that
was
not
there
for
a
while
and
now
it's
there,
it's
the
capability
to
have
lags
which
is
not
to,
and
that
is
not
backward
compatible
with
the
previous
six
top
anandhi.
E
E
Token
is
actually
very
expensive
on
the
client
side
and
we
thought
that
some
clients
could
not
afford
to
do
that
and
if
they
can't
spend
all
the
cycles
doing
the
cryptographic
things
that
you
find
in
CGI,
then
the
only
alternate
was
to
make
this
thing
feel
bigger,
and
so
that's
why
we
actually
provision
far
ranks
which
is
like
a
larger
than
two.
So
if
there
is
any
problem
with
this
and
anything
any
problem
with
this
and
the
rest
I'm
going
to
present,
please
raise
your
hand.
But
this
is
a
big
change.
Next
slide,
please.
E
So
the
second
thing
which
which
aperture
is
also
a
consequence
of
this,
which
happened
during
the
initial
review
bit,
was
not
an
issue
review
come
out.
It's
the
the
problem
of
telling
the
router
over
world
whether
this
is
also
a
router
or
which
will
under
its
wrought
ability,
later
I'll
participate
in
to
repeal,
for
instance,
or
if
this
device
is
a
plane,
live,
meaning
that
it
doesn't
know
anything
about
the
right
over
doesn't
know
anything
about
anything
else.
E
You
just
want
the
infrastructure,
the
routers,
to
do
their
job
and
make
sure
that
these
packets
will
come
back
to
him,
and
the
original
idea
was
that
the
this
ripple
devices
would
set
a
bit
and
that
the
leaf
would
not
suit
this
spec
would
have
been
transparent,
but
the
discussion
tended
to
say
eh.
There
are
many
report
devices
out
there
which
don't
set
the
bit,
so
the
backward
compatibility
will
be
very
hard,
but
the
plane
6lowpan
in
the
right
of
our
world
don't
exist.
So
this
is
a
flag
day
for
them.
E
Let
them
all
set
the
air
bit
to
odd
okay.
So
the
a
bit
now
is
host
setting,
which
says:
oh
I'm,
a
host
I'm,
not
persuading
two,
twenty
rotting
I,
don't
know.
What's
writing
there
is
I,
don't
want
to
know
I'm
setting
the
bit.
If
there
is
a
router,
please
do
everything.
I
need
to
be
done
because
I
won't
do
it
myself.
You
see
so
basic,
basically
a
six
up,
a
node
which
does
not
participate
the
right
over
us
to
set
a
bit.
E
So
this
has
been
there
for
a
long
long
time.
This
is
the
tid.
So
the
T
ID
is
a
sequence
counter,
and
this
is
how
we
can
do
this
seamless
roaming.
As
you
know,
when
the
device
moves
from
a
place
to
another
place,
the
infrastructure
has
to
figure
out
out
of
the
two
information
which
is
the
most
recent,
and
there
are
two
ways
to
cluster
ways
for
doing
that.
You
have
a
timestamp
of
your
sequence
counter
and
the
timestamp,
when
you
have
a
very
constrained
space
to
put
your
timestamp
is
a
bad
idea.
E
We
don't
know
the
resolution,
will
need,
etc
or
some
things
and
move
very
fast
and
things
can
move
very
slow.
So
what's
your
unit
what's
the
space,
so
the
sequence
counter
is
much
easier
to
deal
with,
but
it
has
to
be
provided
by
the
moving
device.
So
that's
why
it's
one
of
those
two
information
that
6lowpan
is
now
provided
while
providing
to
to
the
routing
protocol
with
easy
repo.
So
this
is
this
tid,
so
that
was
one
of
the
biggest
thing
wanted
to
do
with
this
update
next
slide,
please.
E
Next,
please
so!
This
is
this
is
the
the
most
important
change?
That's.
The
change
is
that
we
don't
necessarily
use
a
new
I-64
as
the
identifier
of
the
device
anymore.
Actually,
if
you
think
about
what
you
want
to
express,
you
don't
want
to
say
who
is
the
owner
with
a
unique
ID
or
something
you
want
something
to
an
able
to
correlate
the
second
registration
for
the
first
for
the
same
address
so
as
to
see
if
the
second
registration
for
the
same
address
is
coming
from
the
same
guy.
E
That
doesn't
mean
that
the
token
that
you
are
using
to
verify
that
as
to
be
a
unique
ID
if
it's
a
unique
ID
one
of
the
ing
commands
that
I
heard
is
that
you
have
privacy
issues
around
that.
That's
good,
now,
you're
leaking
the
UI
64
the
device
there
are
privacy
concerns
with
that.
So
one
of
the
ideas
you
reviews
I
got
is
even
asking
whether
we
should
take
the
path
of
duplicating
the
use
of
UI
64
for
this
purpose.
Okay,
anyway,
the
new
term
insist
on
what
this
exactly
years.
E
It
is
not
an
idle
failure
of
this
source.
Don't
there
is
new
text
which
says
don't
do
we
do
it,
for
that?
Don't
do
it
for
correlating
to
registration
which
have
the
same
identifier,
because
this
is
a
different
thing.
The
scope
of
this
field
is
registering
one
address.
Okay,
that's
that
the
scope
of
it
that's
its
value
it.
The
same
device
can
use
different
further
field
for
different
registration.
Don't
think
that
by
looking
at
all
the
Deva,
the
registration
with
the
same
raga
field,
you'll
get
you'll,
get
everything
from
the
same
yard.
E
It
is
not
the
meaning
at
all.
So
that's
why
the
name
has
changed.
It
is
used
to
verify
that
the
second
registration
for
the
same
address
is
is
about
the
same
guy,
registering
the
same
address,
not
two
different
guys,
that's
what
it's
for.
So
we
had
a
lot
of
new
text
to
clarify
that,
and
the
name
has
changed
actually
two
times
during
the
review
next
slide.
Please
so
I
have
some.
Oh
it's
going
to
be
very
quick.
I
have
some
limited
flows
there.
We
can
go
quickly
through
them.
E
What's
important,
Shira,
that's
the
bootstrap
of
a
network
is
that
now
we
have
mastered
a
six
cio
option,
which
is
an
option
that
customers
actually
standardized
sometime
ago.
We
must
the
presence
of
a
six
cio
india,
rice.
Actually,
that
must
is
inherited
from
from
Justin's
rosebud
and
that's
how
we
know
that
the
sender
of
the
array
supports
this
update.
E
In
the
draft
like
before
the
ideas
you
review,
there
were
two
ways
of
getting
there
and
one
of
the
review
commands
was
a
it's
too
complicated.
We
need
one
way,
I
think
that
was
that
real.
So
now
we
have
one
way
and
we
discussed
with
caste
and
blah,
and
we
ended
up
saying
the
six
CIO
is
the
right
way
here:
I'm
giving
more
details
on
what
goes
into
registration,
so
they
are
option,
is
called
now
an
extender,
oh
just
to
discuss
it
easier.
E
The
source
of
the
registration
is
always
an
ink
lockup,
and
the
address
that
you're
registering
now
is
in
target
of
DNS.
You
know
there
is
Target
Field
in
the
ICMP
header,
that's
that's
where
the
registered
address
goes
and
that's
good,
because
when,
when
you
see
on
the
right,
the
the
registration
goes
between
a
6
lb
arrow
and
the
six
VBR
the
source
of
that
packet
cannot
be
the
6lowpan
note
at
the
end
of
the
network.
It
has
to
be
the
guy
who
sends
the
packet
so
to
do
this
proxy
registration
by
the
6
lb
I'm.
E
E
E
And
yes,
optionally,
in
the
NSC
arrow,
you
can
see
the
AP
and
the
options
that
come
down
next
slide.
Please,
and
there
is
the
the
flow
back.
So
after
a
time
out
on
the
backbone,
the
address
is
unique,
so
that's
the
six
backbone
router
size
in
a
row
to
to
the
6
lb
r
and
that
flows
back
as
previously,
nothing
very
surprising.
That's
pretty
much.
What
thanks
like
so
I
will
give
you
more
about
the
eyes
I.
H
E
Like
four
or
five
slides,
one
per
review
so
I
think
it's
worth
going
through
at
least
my
summary
of
the
review,
because
these
are
were
all
great
great
reviews,
very
detailed,
a
lot
of
comments
so
I'm
just
giving
you
a
short
summary
of
the
main
items,
so
Tim
Shawn
from
interior
told
us
that
that's
that
steam
we
told
us
that
using
UI
64
at
all
was
probably
a
bad
idea,
so
we
have
it
for
backward
compatibility.
The
group
never
discussed
about
completely
des
practically
Despres,
creating
that.
E
E
Yes,
Tim
asked
for
because
you
remember
we
have
we
had
this
document
about
requirements.
We
are
we
used
to
have
a
requirements
right.
These
requirements
is,
is
dead
now
stand
out,
but
I
copied
it
mostly
in
appendix
so
people
would
know
what
we
serve
and
actually
it
was
not
clear
what
this
document
serves
us.
As
what's
left
to
be
served
by
further
documented
or
what
is
already
served
by
different
documents,
so
I
made
this
table
with
the
state
of
the
art
of
what
I
know,
which
document
do
what.
E
E
E
What
what's
that
value?
What's
the
minimum?
What
is
what
is
a
good
value
and-
and
the
question
is
not
really
for
us,
but
for
six
months,
so
maybe
there
is
an
interesting
work
to
be
asked
from
six
man
about
you
know
when,
when
you
have
a
device
which
has
to
store
information
about
bottles,
to
store
information
about
the
devices,
how
much
space
does
it
need
per
your
device?
At
least
the
many
says,
I
cannot
support
this
amount
of
device
or
something
like
that.
E
E
E
It's
on
yours
as
well,
but
maybe
because
we'll
see
otherwise,
please
come
to
make
anyone.
So
then
we
are.
We
are
joking
and
Chris,
and
so
yes,
some
terms
were
found
to
be
offensive
like
legacy
talking
about
the
original
f
675,
so
we
moved.
We
changed
that
or
FC
675
only
meaning
supports
the
Sierra
6725,
but
not
des.
That
was
the
first
change
of
the
name.
E
So
if
you
look
intermediate
draft,
the
UI
6
2016
4
field,
which
was
the
unique
ID
field,
was
renamed
to
registration,
unique
ID,
to
really
refer
to
the
fact
that
the
scope
of
this
information
is
the
registration
itself,
not
the
whole
world,
and
it
cannot
be
used
for
inferring
things
in
between
registrations
and
the
new
option
came
in
new
requirements
set
on
the
operation
and
management.
So
there
is
a
new
attempt.
Well,
it
has
requirements,
maybe
nothing
matching
them,
but
at
least
we
have
those
requirements
stated
now.
What
was
yoga
next
slide?
Please
Dave!
E
E
That's
this
version
fear
14,
where
the
DF
flag
came
in,
it
was
not
taste
come
out
like
I
say
it
was
the
power
of
discussion
with
all
the
wrong
people.
Tiny
a
the
inflection
had
been
a
rolls
back,
sign
put
it
down.
It
should
be
in
the
six
lows
back
to
put
it
down
so
that
the
role
device,
the
backward
opportunity
with
repo,
still
works
a
lot
of
rewarding
on
the
rover
field,
explaining
what
it
is,
what
its
copies
etcetera
and
yes,
they
comment
stated
here
as
well.
What
is
the
minimum
number
of
addresses.
I
So
Dave
Taylor,
my
question
is
partly
for
Eric
who's
sitting
back
here.
So
if
your
question,
so
this
is
in
response
to
your
point
Pascal
about
saying.
Well,
maybe
this
is
a
job
for
six
men
in
the
normal
neighbor
discovery
right.
The
router
has
some
cash
that
I
can't
forward
about
an
entry
in
there,
but
it
can
evict
entries
in
the
cache
and
repopulate
them
with
new
ones,
just
with
performance
issues,
and
so
you
can
evict
stuff
in
the
cache
whenever
you
want
as
long
as
you're
willing
to
do
the
extra
exchange
to
repopulate
them.
I
My
understanding
is
you
can't
do
that
for
the
for
the
things
that
are
registered
with
aro,
so
my
question
is:
really:
is
there
any
other
case
in
six-man
where
you
can't
evict
a
particular
thing,
the
cash,
or
is
this
really
a
six
low,
specific
problem
that
quite
and
the
answer
belongs
here-
I'm
wondering?
Maybe
it's
not
appropriate
to
throw
it
over
to
six
man
unless
there's
some
case
that
comes
up
outside
the
scope
of
six
well.
J
J
I
Thank
you
for
that.
So
I
believe
that
you
cannot
throw
this
over
the
wall,
the
six
man
it
should
be
addressed,
and
this
working
group
and
potentially
with
review
from
them.
But
it's
your
problem
because
you
created
it
so
you
well,
we
right
create
it,
so
we
should
solve
it
in
this
working
group
and
not
trying
to
throw
it
over
there
and
so
for
what
is
the
minimum?
I
argued
my
email?
Well,
obviously,
the
answer
isn't
zero,
okay
and
I.
I
Think
most
people
would
agree
that
the
answer
isn't
one
because
that
means
you
can't
use
both
local
and
global
addresses
or
something
like
that.
I
think
many
people
will
also
argue
that
the
answer
can't
be
two,
because
that
would
say
that
you
can't
use
privacy
addresses
and
on
privacy
addresses,
and
so
certainly
the
minimum
is
greater
than
or
equal
to
two,
but
is
there
a
higher
number
it
ought
to
be,
and
this
is
the
group
that
I
think
is
the
one
that
actually
needs
to
make
a
recommendation,
because
we
created
the
problem.
I
E
We
can
come
up
with
a
number
which
is
reasonable
for
all
case,
because
we
know
a
number
of
things
yeah,
but
then,
when
you
want
to
port
this
document
for
a
large
of
couples
like
six
men,
they
would
have
to
revise
this
number,
probably
the
world
something
much
higher
use
in
here.
What
we
have
is
we
have
a
link
loco
at
least
one
which
is
derived
from
the
UI
64,
that's
used
for
making
the
registration,
the
reservation,
the
registration.
E
We
have
a
global
address
or
ul8
rice,
which
is
derived
from
the
UI
64,
and
that's
used
for
the
trade
process
and
at
the
end
of
the
join
process,
and
mostly,
we
have
one
which
is
based
on
the
short
address
on
the
pan
ID,
that's
the
three
sixth
of
an
original
15
4.
So
on
15
4,
you
end
up
with
4
or
3
addresses
at
least
right
on.
E
I
Get
that
from
one
link-
local,
maybe
one
ula
and
the
one
regular
global
address
and
for
privacy
addresses.
You
have
the
address
of
the
day
for
the
last
7
days.
Yep,
and
so
you
add
those
together
and
your
minimum
bound
for
normal
behavior
would
be
about
10,
and
that's
assuming
that
you
don't
have
multiple
subnet
prefixes
per
link.
So
if
you
get
into
home
that
cases
we
might
have
multiple
subnets
/
link,
then
just
multiply
that
by
the
number
that
you
want
to
allow
for,
but
it's
on
the
order
of
tens
or
tens,
not
ones.
I
E
And
that's
back
to
your
question:
do
we
serve
this
group,
in
which
case
three
is
a
good
minimum?
I'm,
not
saying
you
only
three
right,
but
it's
a
minimum
of
six,
not
by
only
saying
three
is
good
for
going
anywhere
outside
of
this
constraint
network.
Where
you
comprise
the
IP
address
based
on
the
MAC
address
blah,
then
you
need
a
lot
more,
and
so
should
we
expect
for
just
our
minimal,
minimal,
minimal,
need
or
should
respect
for
something
broader.
You.
K
Can
see
description
you
can
must
for
the
three
and
should
for
something
larger
if
you
want
like
that
would
be
one
way
to
deal
with
it
I'm
here
for
a
completely
different
reason.
So,
like
do
you
want
to
go
through
this
first
I
do
only
like
there's
something
that's
been
bugging
me
and
I
have
to
say
it
like
and
then
kind
of
like
think
about
it
in
the
working
group
as
well.
K
E
K
So
it's
one
or
the
other
so
either
like
we
say
this
is
the
algorithm
we
use
and
just
put
it
in
there
or
we
say
we
use
the
ripple
algorithm
because
the
the
issue
is
like
if
the
ripple
thing
gets
changed
at
some
point
in
the
future.
We
are
gonna
have
an
inconsistency
from
this
document.
It
says
like
hey.
If
you
want
to
do
our
triple
does
and
also
do
this
so
I
I
thought
about
this.
Quite
a
bit
like
ever
since,
like
well
hit
like
I've,
been
thinking
about.
K
It's
like
something
right
from
80
well
time,
but
I
just
wanted
to
like
the
working
group
to
make
a
considered
decision
on
how
to
go
about
this
because
I
really
don't
like
it.
Okay,
I,
just
don't
wanna
push
it
on
the
working
group,
but
I
would
either
like
a
straight
reference.
Saying:
go.
Look
at
65
50,
like
you
know,
take
it
from
there
or
just
put
this
algorithm
copy
and
paste,
but
don't
say
it
60
or
50
say
this.
Is
the
algorithm
and
be
done
with
it?
So
that's
80
hat
off
comment.
E
It
was
a
pointer
to
us
in
65,
50
and
I
took
the
inline
text
of
65
50.
Instead
saying
it
is
inline
text
of
65
50
and
now
it's
suresh
telling
us
he
is
either
I
come
back
to
what
I
was
before
or
I.
Remove
the
fact
that
it's
a
reference
I
just
keep
the
copy
tags,
but
I,
don't
say
it's
copied
from
65
50
right.
That's.
K
Fine
with
me
so
keep
the
text.
Don't
say
it's
165
50,
like
you
know,
IETF
V
Lee.
We
provide
outgoing,
writes
for
every
RFC,
so
we
can
take
freely
from
any
IETF
document
and
copy
and
paste
write
like
because,
like
you're
kind
of
putting
in
the
expectation
of
being
in
sync
because
I
don't
know
why
it
needs
to
be
in
sync
with
ripple
right.
That's
like
personally
may
or
may
not
be
an
implementation
thing,
but
you're
putting
in
like
a
false
expectation
that
will
be
in
sync
because
ripple
might
change
independently.
That's
really
my
concern.
E
K
E
K
K
B
B
E
B
B
J
Mark
agreed
to
be
self-contained,
but
if
you
worked
in
this
room,
you
wouldn't
know
this,
so
you
should
actually
capture
this
in
the
document
which
has
at
the
time
of
this
writing.
This
is
the
same
as
in
repo.
Have
a
rapport
might
change
and
we
might
not
that's
what
an
implementer
needs
to
know
saying
that
when
ripple
changes,
because
he
compared
the
command
say
it's
the
same
right
and
Angele
use
a
library
for
that,
and
then
someone
goes.
The
changes
like
no
provide
the
information.
Don't
have
them
guess.
J
K
J
The
implementers
life
easier,
you
should
then
make
it
explicitly
be
different.
It's
like
saying,
you're
using
TCP
sequence,
numbers
arithmetic.
Well,
does
that
mean
that
if
TCP
were
to
change,
does
this
thing
change
or
not?
You
need
to
be
explicit
about
what
happens
when
change
happens
as
opposed
to
saying
well,
the
words
are
the
same:
if
I
read
it,
does
it
mean
it's
the
same
or
not?
I
have.
J
B
C
B
J
E
E
E
E
I
want
a
working
group
to
be
very
very
aware
if
there
is
any
problem,
because
we
have
very
short
time
in
front
of
us,
60
IO
is
the
only
option
to
discover
the
only
way
to
discover
whether
we're
in
the
backward
compatible
world
or
if
we
can
use
this
back
in
the
full
capability
name
of
the
unique
ID
is
now
rather
because
it's
how
we
verify
the
ownership
of
one
registration,
then
Peter
again
gave
us
very,
very
good
and
deep
review
a
lot
of
help
for
my
French.
Even
after
Dave.
There
was
a
lot
left.
E
E
The
sea
flag
indicates
that
the
rover
is
a
crypto
token,
as
specified
by
this
specification,
which
allows
us
to
basically
obtain
a
proof
of
ownership
of
the
address
later
so
the
first
come
first
serve
first
time
your
register,
latrise,
you
provide
the
rover
whatever
that
is,
but
then
later
we
can
use
that
to
do
a
cryptographic,
verification
that
you're,
the
one
who
did
it
in
the
first
place
yeah.
So
the
challenge
in
the
flow
is
like
this
right.
When
there
is
a
crypto,
ID
and
I
will
need
my
laser.
E
Oops,
obviously
the
resident
working.
So
when,
when
the
CBT
said,
the
rover
is
of
type
crypto
idea
right,
the
Lance
tell
you
tells
you,
it
is
64
bits
or
more.
So
if
the
six
Allah
doesn't
add
the
crypto
information
and
the
first
time
that
will
happen,
then
there
is
status,
saying
validation
requested
in
the
notes
and
basically
that
nonce
was
missing
in
the
specs
like
somos
ago.
So
it's
very
clear.
The
nonce
is
there
and
we
have
a
router
announced,
but
we
don't
have
a
600
knots.
E
E
Then
we
actually
changed
a
little
bit
the
content
of
the
second
and
s,
because
we
wanted
to
reuse
options
which
we
are
present
in
CGI.
But
the
problem
of
this
options
in
RC
39
31
32,
is
like
the
we're
cold,
for
instance,
eres
a
option
and
we
don't
do
anymore
Oh
si
right.
We
are
doing
ECC,
so
I
could
not
really
keep
the
name
of
the
option
we
have
to
so.
E
The
proposal
here
is
basically
to
use
the
same
formats,
the
same
code,
but
kind
of
extend
the
name
and
the
meaning
of
the
option
so
that
we
can
do
other
things.
Then
there
is
a
pretty
much,
and
so
the
sepal
is
is
the
parameter
option
and
the
ndpa.
So
is
the
NTP
signature
option
and
they
are
both
derived
from
existing
options.
So
we
are
not
consuming
more
option
space
and
well
that
enables
the
six
allow
basically
to
reconstruct
the
public
key,
because
basically
the
crypto
ID
is
nothing
more
than
the
ash
of
the
public
key.
E
So
to
make
it
shorter
right
and
the
the
ndpa
option
is:
is
the
public
key
Li
in
the
clear
press,
small
parameter
which
allows
you
to
build
more
than
one
token
with
just
one
private
key
and
the
result
of
that
is
signed
by
the
public
key
but
by
the
private
key?
So
so
you
have
the
public
key
which
validates
from
the
token
and
sign
with
the
private
key
you
validate
the
signature.
Okay
is
really
honor
that
that's
how
it
goes
now.
This
flow
as
we've
designed
it
and
that's
my
big
big
question
to
this
group.
E
E
So?
Let
me
go
back
to
the
first:
we
we
had
a
64
UI
64
field.
We
are
extending
the
legs
or
that
field.
The
reason
is
in
CGI
or
a
season
and
72
there
was.
There
were
three
bits
which
were
actually
meant
to
make
the
computation
of
the
whole
thing
very
intensive,
because
you
were
building
sha
ashes
many
times,
but
until
some
bits
we
are
already
well
ten
with
a
zero.
E
You
had
to
add
a
to
counter
and
we
do
the
ash
again,
so
that
created
a
huge
number
of
ash,
computation,
TL
und
that
we
a
token
of
64
bits
which
had
this
number
of
bits
that
you
wanted
with
the
right
value
that
was
highly
highly
compute-intensive
on
the
device.
If
we
do
that,
we
can
live
with
the
rough
token
of
64
bit,
but
that's
highly
compute-intensive
on
the
device
can
still
do
it,
but
the
spec
has
removed
that.
E
So,
if
you
want
to
come
back
to
a
model
like
that,
you
have,
we
have
to
talk
about
the
mailing
list.
What
we
have,
instead,
noise,
don't
do
any
of
this
complex
operation.
We
remove
the
field
which
allows
you
to
do
that.
Instead,
we
say
a.
If
you
want
more
security,
then
you
put
more
bits
in
the
rubber.
So
remember,
the
rover
is
a
hash
of
the.
E
So
the
Fela
was
talking
about
what's
called
the
modifier,
so
there
is
a
huge
modifier
field
in
CGI
which
allows
you
by
incrementing
incrementing
to
go
all
the
way
till
you
generate
a
hash
which
has
those
bits
that
to
zero,
but
that's
a
big
field.
But
if
I
go
as
long,
we
made
the
modifier
much
shorter.
Why?
Because
if
it
was
kept
very
long,
it
could
be
used
as
an
attack
against
what
we
are
doing.
You
have
any
key
and
you
update
the
modifier.
E
L
Disclaimer
so
I
don't
have
tons
of
six
load
deployment.
Experience
and
I
am
one
of
the
authors
of
this
I
think
it
would
make
sense
to
make
it
longer.
But
how
to
do
it
is,
is
for
the
group
to
decide
so
do
we
just
do
128
and
that's
it?
Do
we
allow
128,
256
longer
short
or
something
in
between
personally
I
think
128
and
then
just
live
with
it,
but,
as
I
said,
I
don't
have
tons
of
deployment
experience
so
I,
don't
know
how
that
affects
backwards.
Compatibility
and
if
somebody
wants
to
comment
on
that.
L
E
There
is
a
lot
of
text
now
in
the
draft
about
this,
and
the
backward
comparative
compatibility
is
not
a
problem
with
a
PNG.
That's
why
I
mean
it's
a
prime
with
the
RSC
6775.
There's
a
lot
of
discussion
about
that.
So
remember.
With
a
six
year
yo
we
discover
with
all
the
six
LVR
and
the
six
raf
support
this
back
and
in
this
RC
6725
allows
all
the
way
to
I
think
255
256.
Now
it's
a
matter
of
deployment.
It's
not
us
right.
We
know
already
256
is
being
used.
E
Some
people
are
talking
about
512,
so
should
we
increase
the
lag
I
mean
we
I
have
put
a
boundary
to
the
line,
I
guess
to
five,
something
like
that
which
gives
us
256.
So
your
complete
part.
Might
we
have
to
to
check
whether
the
boundary
I
gave
is
high
enough
I
mean
a
recommendation,
could
be
128
doesn't
mean
we
have
to
bar
it
2-2
against
longer,
right,
I.
Think
at
least
allowing
256
is
seeing
a
future,
but
you
could
tell
me,
go
all
the
way
to
1k
I
mean
it's
not
hard.
E
It's
just
setting
the
boundary
to
the
ranks
field,
but
we
have
to
decide
that
note
that
it
impacts
the
dark
deck
exchange.
Remember
the
dark
as
the
the
same
rubber
field
in
it
and
today,
since
the
doubt,
doesn't
have
an
option.
There
is
another
consequence
here,
since
the
DA
doesn't
have
an
option,
we
don't
have
an
option
Lux.
So
the
only
way
to
infer
that
the
dark
is
the
new
dark
is
the
length
of
the
whole
message,
meaning
that
if
we
have
a
longer.
E
Unless
we
change
something
in
the
header,
like
you
know,
a
new
cmp
code
or
something
the
currency
simply
simply
code,
the
only
way
to
ensure
the
size
of
the
rover
is
by
the
size
of
the
whole
message.
So
we
cannot
add
a
new
field
and
say
because
the
lines
have
changed,
you
have
a
new
field.
If
we
say
the
the
length
of
the
rubber
is
derived
from
the
length
of
the
message,
which
is
what
we
do
now,
the
dhadak
is
recon
strained
in
its
current
format.
E
E
Okay,
so
think
about
the
strikes
that
we
need
think
about
whether
we
can
use
64
bits,
meaning
we
have
a
lot
of
power
or
the
device
to
compute
the
CGA,
the
way
cg8
in
it
or
whether
it's
a
better
idea
to
make
a
rover
field
longer.
How
long
it's
mostly
a
deployment
issue
I
mean
what
is
the
upper
bound
that
we
can
give
today?
But
no,
it's
mostly
a
deployment
issue,
but
then
is
it
the
right
way
to
do?
I
mean
that's
what
we
have
now.
E
We'll
have
to
discuss
the
workgroup
last
call
of
the
backbone
router.
There
is
one
thing
that
they
can
mention
about.
A
barber
by
one
water
is
I,
gotta
feel
bad
feedback
from
implementers,
and
they
tell
me
a
we're
using
that,
but
we're
using
it
in
a
slightly
different
context,
because
what
we
do
and
that's
kind
of
command
in
intercloud,
etc.
We
are
using
a
list
type
of
operation,
a
resolver
so
that
we
don't
have
to
broadcast
DNS
on
the
backbone
or
whatever
it's
not
the
backbone.
But
it's
what
serves
as
a
backbone.
E
They
actually
look
up
a
resolver,
meaning
that
they
don't
need
to
broadcast
and
the
just
go
unicast
from
the
new
location,
the
new
backbone
router
to
the
old
backbone
router.
That
makes
life
a
lot
easier
on
a
large
fabric,
mostly
issue,
do
something
with
ex9
or
no
siree.
So
the
result
of
that
is
you
don't
want
a
broadcast
message
like
and
then
that's
dad
to
figure
out
where
the
guy
was
or
something
if
the
ones
duplicate.
E
What
they
really
want
is
a
unicast
from
the
new
location
to
the
old
location,
and
so
they
looked
at
out.
Spec
and
they
said:
ok,
I
will
do
it,
but
I
will
use
a
data
exchange
for
unicast
and
I
actually
think
it's
it's.
Ok,
it's
a
good
idea
and
some
people
are
doing
it.
So
can
we
call
that
in
our
spec
say
you
know
on
the
backbone
router?
If
you
know
Reggie
well,
the
old
location
was
because
you
have
a
resolver
or
something
just
go
unicast
and
you
should
go
unicast
and
use
a
data
exchange.
E
C
C
E
C
E
D
E
So
so
it's
it's
actually
attached
to
ripple
Network.
So
if
you
say
host
you're
losing
that's
that
meaning
now
it
doesn't
mean
the
exceptions
where
a
leaf
is
actually
a
router,
for
instance,
if
it
doesn't
know
the
instance
ID
you
I
sitting
on
so
it
doesn't
know
how
a
ripple
is
operated
there.
I
can
still
inject
packets.
Then.
C
E
Yes,
it
is,
it
is
because
I
was
presenting
a
roll
presentation
for
the
interest
of
this
group.
That's
what
that's
why
it's
here,
I
think
we
agreed
yeah.
So,
okay,
there
is
a
new
draft
now
a
triple,
and
because
now
we
have
our
CC
735
update
and
all
this
work
that
we
just
served
so
now
we
can
have
a
real
host
doing
only
6lowpan
attaching
to
a
repo
network
and
getting
all
the
good
benefits
of
ripple
rotting,
of
seamless,
moving
morbidity
between
do
dogs,
etc,
etc.
E
C
C
M
Good,
my
name
is
Jung
Hwan
choi
from
a
tree.
I
show
you
I've
got
just
quite
cake
presentation
for
this
time,
and
this
is
the
first
story
on
status
of
my
happy
bestow.
Nfc
I
should
have
got
me
to
eight
times
our
division
at
this
time
is
the
ninth
revision,
the
photon,
that
the
nine
is
about
the
end
and
the
issue.
M
Actually,
there
was
a
meeting
of
fry
meeting,
miss
Pascale
in
the
previous
meeting
in
Singapore,
actually
at
a
time,
I.
Just
almost
all
reflect
the
comment
from
the
comment
and
but
I
just
miss
one
thing:
there
was
from
the
paschal
6ln
to
T
cell
and
how
to
exchange
or
their
own
information
each
other,
but
I
just
put
four
there
I
just
put
just
the
last
sentence:
fool,
but
the
new
Lesbos
just
that
just
take
they
used
it.
M
M
B
B
If
you
have
looked
at
this,
if
you
care
about
this
document,
please
send
in,
doesn't
have
to
be
a
deep
comment
if
you
just
think
it's
in
reasonable
shape
and
it
should
go
forward.
Please
do
say
that,
but
positive
AK
is
very,
very
useful
by
the
way.
We're
hope.
Let's
call
us
over
on
Monday
right,
but
please
still
go
ahead
and
send
your
positive
X
or
more,
but
at
least
positive
acts
would
be
very
different.
Thank.
N
N
How's,
that
okay,
all
right
so
I'm,
Charlie,
Perkins
and
I'm
here
to
tell
you
about
the
deadline,
time,
routing
header.
This
document
has
gotten
pretty
good
comments
for
the
last
previous
IDs
and
I.
Think
we've
made
good
progress
on
it.
Basically,
what
it
does
is
and
allows
you
to
tell
what
deadline
time
is
for
packet
delivery,
and
if
a
packet
is
not
delivered
in
time
to
meet
the
deadline,
then
you
can
drop
it.
N
You
can
also
include
the
origination
time
so
that
devices
along
the
path,
the
routing
path,
can
determine
how
long
the
packets
actually
been
going,
and
this
enables
you
to
do
some
digital
indecision.
So,
for
instance,
if
you
see
a
packet,
that's
just
as
an
example.
If
you
see,
if
you
receive
a
packet,
that's
sort
of
getting
close
to
the
deadline,
maybe
you
allow
it
to
be
routed
in
preference
to
other
things
that
have
less
urgent
delivery
deadlines,
as
it's
assumed
that
the
networks
are
the
devices
that
are
looking
at.
N
This
header
are
in
time,
synchronized
networks.
Otherwise,
they
can't
really
know
what
the
deadline
time
actually
means
and
then
there's
a
simple
mechanism
for
allowing
you
to
make
sense
for
the
deadline
time.
Even
if
you
cross
over
time
zone
boundary
so
drafts
been
around
for
more
than
a
year
and
we've
presented
it
and
got
some
good
comments
and
they
included
the
origination.
Time
made
sort
of
compression
mechanism
for
representing
the
time
in
the
header,
and
then
we
for
the
next
revisions.
N
We
included
the
slot
number
as
a
time
unit
and
made
some
slight
improvements
in
the
header
compression
all
along
there's
been
implementation
and
that's
available
for
open,
WS
n,
and
you
can
look
on
github
and
you'd.
Look
in
the
presentation
materials
for
the
for
the
URL
I
wouldn't
expect
you
to
want
to
read
those.
So
then,
after
after
all
that
the
draft
was
adopted
as
a
working
group
document,
there
was
a
lot
of
interest,
and
now
we
have
our
last
update
is
actually
quite
a
minor
updates.
N
It
was
requested
that
we
put
in
some
information
about
how
the
time
synchronization
can
be
achieved
between
the
networks
and
it's
not
I-
think
it's
clearly
out
of
scope
for
this
document
to
make
a
normative
requirement
for
that.
But
we
did
borrow
language
from
another
draft
that
had
a
similar,
similar
goal
and
we
just
put
in
the
time
synchronization
mechanisms
that
were
appropriate,
or
at
least
feasible
and
the
or
was
in
the
previous
draft
reference
to
the
OEM,
which
has
been
in
the
meantime,
been
adopted
as
a
working
group
document
in
IEEE
ppm.
N
Actually,
I
still
think
it's
a
little
bit
in
the
middle
somewhere
and
like
strongly
should,
but
anyway,
it's
now
says
must,
and
the
last
thing
we
did
was
according
to
a
comment
received
on
the
mailing
list,
is
to
describe
what
kind
of
delays
are
observable
in
the
network,
and
this
is
purely
informative
and
I
don't
well
anyway.
As
far
as
I
know,
the
draft
was
already
pretty
close
before
we
made
these
changes,
and
now
it's
extremely
close
so
and
like
to
have
requests
any
comments
or
suggestions
about
the
draft
just
to
briefly
review
here.
N
The
changes
you
can
see
as
there's
a
must
is
in
red
and
there's
a
slot.
I
mean
there's
a
time
unit
for
the
network
slot
number
and
then
other
than
that.
Oh
one
thing
about
this
could
be
slightly
misleading,
and
that
is
that
the
fields
for
the
a
delay
time
in
the
origination,
time,
which
are
called
DT
and
ot.
They
are
not
mandated
to
be
16
bits.
They
can
be
optional
lengths
and,
according
to
let's
see,
do
I
get
a
pointer
here.
N
O
Good
afternoon,
ladies
gentlemen,
my
name
is
Jung
Geun
hyung
working
for
ETL
I.
So
this
is
the
presentation
of
update.zip,
throw
up
credibility
and
use
kiss
threat.
Okay,
this
is
the
history
of
this
trip.
So
this
this
time
is
the
first
revision.
So
I
would
like
to
emphasize
the
goal
of
this
document.
The
goal
of
this
document
is
help
zip,
troll,
g-proteins
tech
adaptation
by
air
to
contain
technology
and
help
a
newcomer
understand
how
she
pretends
there
can
be
a
global
in
practice.
So
we
onto
this
trapped
could
be
useful
for
new
adapter
over
IOT.
O
Over
you,
so
after
all
the
update
since
the
last
meeting,
so
we
add
to
a
practical
six
row,
deployment
scenario:
one
is
g3
Piercy
uses
and
another
is
net
ways
to
use
easier
and
we
update
MSTP
part.
So
thanks
to
Carolyn
and
they
were
loving,
so
they
have
to
obey
the
MSTP
part.
And
we
add
the
sixth
row
bluetooth
matched
on
draft
in
this
document,
and
we
made
some
editor
of
the.
O
So
I
concert
eight
and
the
check
that
the
one
of
the
author
of
this
rep
to
Nyong'o
of
who
he's
working
for
SK
Telecom
in
South
Korea,
the
largest
number
one
mobile
operator.
So
they
have
a
friend
to
deploy.
Ipv6
on-air,
t
and
l
TM
t
she.
But
importantly,
in
this
case
the
cipro,
the
patient
layer,
is
not
needed
because
the
LT
LT
empty.
She
can
provide
transmission
ipv6
without
the
help
of
the
six
role
technology,
so
I
want
to
remove
in
the
extra
vision.
O
O
O
So
in
this
draft
we
have
the
guideline
product
in
IP,
which
tests
that
you
can
check
that.
Yes,
I,
think
that
the
most
important
part
in
this
rep
is
to
sit
row
deployment
scenarios.
So
in
this
doctoral
working
group
we
are
talking
about
the
Trotec
analogy
or
more
interesting
is
the?
Is
there
any
real
world
to
adopt
isotropic
analogy?
So
until
now
we
found
the
poor
area,
one
is
Jupiter
mesh
and
why
son
disrepair
see
and
yet
risky.
O
O
Okay,
so
in
this
revision
we
add
g3,
Piercy,
G's
repair
see
is
narrow,
PNP
analogies.
So
now
it
support
ipv6
and
ipv4
at
the
paint
layer,
so
Jin
Cong
Hui
at
Hawaii
to
help
to
prepare
these
texts
also
the
aresty
program
in
home
flow
of
powerline
Alliance.
They
also
have
a
some
diploma
Janerio
pasted
on
door.
Six
rostec.
These
texts
also
come
from
the
Qin
Qin
Hui
at
Hawaii.
O
So
this
is
the
design
space
dimension.
You
can
see
it.
There
are
some
a
couple
of
the
design
space
dimension.
Okay,
so
in
the
appendix
section
we
have
a
couple
of
the
600
use
cases.
So
each
of
the
six
wrote
canal
ad.
So
we
update
our
use
case
of
MSTP
in
this
division.
We
describe
the
building
automation
network
based
on
MST,
Aitken,
allergy,
so
edges
test
to
Carolyn
and
they
were
live
in
to
apace
to
dispersal
thanks
to
and
the
other
Li.
O
The
same
as
the
previous
version
so
picture
so
I
think
that
this
draft
is
a
kind
of
the
stable
version,
so
what
we
will
want
to
or
caterer
will
track
other
the
useful
information
to
deploys
a
6-row
technology
in
the
real
world.
So
if
you
have
some
deployment
scenario
in
real
world,
don't
let
us
know
that
we
can
add
world
obtain
this
threat,
so
teacher.
B
Now
in
Montenegro,
so
I
like
what
you're
saying
about
removing
something
that
is
not
really
related
to
stuff
we've
done
here
in
six,
the
working
group,
this
LT
think
we
have
no
document
that
points
that,
like
the
work
we've
done
here
for
to
I
to
adapt
that
so
we
should
delete
it.
Definitely
along
those
lines.
New
tricity,
I
couldn't
I.
O
B
O
O
B
P
B
O
Q
R
Q
Have
a
slide
on
that,
so
there's
six
of
us
looking
at
added
what
we
believe
is
a
rather
old
problem
which
is
fragment
forwarding,
and
we
believe
that
we
have
some
elegant
way
of
dealing
with
it.
So
this
is
the
context
so
pre
IT
f99
fragmentation
has
been
brought
up
a
number
of
times
in
these
meetings,
and
so
we
decided
to
to
look
at
it,
and
so
the
sexto
chairs
asked
us
at
ITF,
99,
there's
four
volunteers
to
create
a
design
team.
The
design
team
met
for
the
first
time
at
ITF,
100
Singapore.
Q
We
formally
created
the
design
team,
and
so
here
we
are
four
months
later
to
present
a
number
of
things
I'm
going
to
present
problem
statement
and
goals.
It
will
take
me
about
10
minutes.
Carsten
will
then
present
a
draft
on
minimal.
You
know
an
implementation
technique
to
do
fragment
forwarding
without
changing
anything
due
to
protocols.
It's
a
kind
of
elegant
thing
and
the
Pascal
will
present
fragment
forwarding
now.
I
need
to
say
that
we
have
been
discussing
this
quite
a
bit
for
the
last
couple
of
days.
Q
This
has
already
been
presented:
l
wig,
so
some
of
these
slides
are
a
little
bit
outdated
and
some
of
these
sides-
you
might
have
seen
already,
but
we
wanted
to
to
do
a
full
report
during
these
40
minutes
that
we
have
now.
So
this
is
the
this
is
the
goal
of
the
40
next
of
the
30
next
minutes,
I'm
going
to
start
by
giving
a
overview
of
what
the
problem
is
and
what
the
goals
are
and
I'll
hand
it
over
to
to
talk
about
the
implementation
technique.
Q
Minutes
seems
sounds
good.
That
should
be
good,
so
problem
statement.
We
have
had
fragmentation,
part
of
RFC
49,
forty
four
and
six
to
eighty
two
for
a
while,
and
so
the
naive
way
of
implementing
it
is
doing
per
hop.
Reassembly
and
I'll
show
you
that
that
has
some
some
problems.
There
are
some
candidate
solutions
that
will
do
fragment
forwarding,
including
Karstens
book
and
carson
renamed
it
to
jackson
person's
book.
Sorry
I
will
correct
this
orally
and
then
Pascal
has
had
this
draft
for
fragment
wording.
Q
That
also
provides
a
piece
of
the
answer
to
that
to
that
problem
and
I'll
finish
these
three
or
four
slides
by
the
goals
of
the
design
team,
so
that
everybody's
up
to
up
to
speed
so
in
49:44
what
is
defined
as
a
link
layer,
fragmentation
technique
which
which
is
used
in
route
over
which
allows
you
to
reassemble
at
every
hop.
That
means
that
the
packet
that's
too
long
is
fragmented,
too
many
little
pieces.
Q
These
little
pieces
are
sent
to
the
next
hop
and
then
the
next
hop
you
reassemble
them
in
a
recently
buffer,
and
then
you
either
have
raised
level
that
completely
form
a
new
ipv6
packet
and
then
and
then,
and
for
that
further
on
or
you
weren't
able
to
resettle
everything
and
there's
some
time
out
that
will
cause
that
reassembly
buffer
to
be
to
be
dropped.
So
the
naive
one
remaining
in
this
is
to
do
per
hop
reassembly,
that
is
at
1/2,
pi,
fragmented
I
said
it
to
my
neighbor.
My
name
resembles
resembles
everything.
Q
Reef
Ragman
sit
sends
it
to
its
neighbor,
a
teacher,
etc.
This
has
not
changed
in
RFC
six
to
eight
two
there's
a
one
sentence
about
reassemble.
It
says
basically,
six
to
eight
two
does
not
touch
the
fragmentation
part
of
4944,
so
the
problems
are
that
if
you
do
pro
pre
fragmentation
and
reassembly,
you
have
two
major
issues.
The
first
one
is
latency.
You
have
to
wait
for
the
last
fragment
to
four.
You
have
to
read:
wait
to
receive
the
last
fragment
before
you
can
start
sending
the
first
fragment
out
to
your
next
hub.
Q
Q
It
is
very
possible
that
you
run
out
of
RAM
memory,
especially
on
these
little
constrained
devices,
and
so
you
have
no
other
option
but
to
drop
that
packet,
and
so
your
your
you
know
your
your
network
that
you've
been
building
so
so
with
so
much
love
kind
of
don't
deliver
any
type
of
reliability,
and
so
everything
goes
goes
bad.
So
we
want
to
solve
that.
So
the
proposed
solution
is
to
do
fragment.
Q
So,
if
I'm
sending
data
from
a
node
into
a
mesh
onto
the
internet,
for
example,
the
source
node
will
fragment
the
packets
will
send
it
to
the
next
hop
that
will
immediately
for
it
immediate
and
it's
only
at
the
LPR.
At
the
egress
point
of
your
network
that
you
do
the
full
reassembly
before
sending
that
as
of
course,
surely
valid
IP
you
six-pack
it
on
to
the
internet.
So
there's
been
a
couple
of
example
solutions.
There
is
this
paragraph
here
in
Saxon,
Carson's
book,
that
that
shows
you
one
implementation
technique.
Q
I
won't
read
this
because
that's
actually
the
the
purpose
of
the
next
slides
is
to
kind
of
ride
out
how
this
how
this
works.
Another
solution,
RAF
was
Frank
the
fording
fragment
draft
bye-bye
Pascal,
which
not
only
does
fragment
forwarding
but
also
adds
on
top
of
that
fragment
recovery,
meaning
if
I'm
a
source,
node
I
can
as
the
destination
node
whether
how
many
of
my
friends
it
had
received
and
that
the
destination
can
then
tell
me,
hey
you
I'm
missing,
fragment
three
and
five
and
you
resend
it
so
the
goals
of
the
design
team.
Q
So
that's
kind
of
the
context
of
where
we
were
beginning
of
the
Singapore
meeting.
The
context
of
the
design
team
is
to
produce
two
documents
within
the
sixth
row.
Workgroup
one
is
an
informal
document
which
summarizes
the
fragmentation
and
kind
of
critiques.
What
is
going
on
right
now
and
what
the
problem
statement
is.
Q
The
second
bullet
point
we
have
been.
This
is
where
it
when
I
told
you,
those
sides
were
a
little
bit
outdated.
We
have
discussed
this
with
Carson
with
six
or
chairs
to
produce
that
second
bullet
point
to
have
it
be
its
own
standalone
document
that
is
progressing
in
the
El
Whig
working
group,
which
is
the
technical
description
of
the
virtual
recently
buffer,
but
the
informational
6lo
document
will
still
discuss
its
limits
and
how
kind
of
life
is
with
everything.
Q
The
second
sexual
document
is
a
standard
stock
document
which
looks
very
much
like
pascal's,
a
fragment
forwarding
draft,
which
defines
a
new
protocol
that
does,
among
other
things,
fragment
recovery,
which
deep
implementation
that
knee
does
not
do.
Okay,
so
the
philosophy
of
the
design
team
is
to
to
move
fast,
close
it
as
fast
as
we
can.
Let's
discuss
a
little
bit
later,
what
where
we
think
we
are,
and
that's
I,
think
the
end
of
my
slides
Carson.
Do
you
want
me
to
run
through
these?
We
want
to
send
these.
D
D
D
Is
you
a
reassemble,
all
the
fragments
you
get
and
only
when
you
have
all
of
them,
you
actually
forward
the
packet,
which
means
you
would
then
burst
out
those
fragments-
and
that
has
a
few
problems
as
Thomas
noted
and
the
ideas
with
the
virtual
reassembly
buffer
is
simply
to
implement
a
reassembly
buffer
but
will
not
actually
store
the
data
any
longer.
Then
you
absolutely
have
to,
and
normally
this
means
that
as
soon
as
a
fragment
comes
in,
you
can
actually
forward
the
the
equivalent
fragment
of
the
the
new
packet.
D
You
would
have
sent
out
by
changing
the
header
in
the
first
fragment
and
just
copying
out
the
fragment
in
the
rest
of
the
cases.
The
only
thing
you
have
to
do
is
the
thing
you
would
have
to
would
have
done
with
a
winner
recently
buffer
as
well.
Of
course
you
need
to
remember
under
which
Datagram
tag
you
are
sending
out
the
fragments
on
the
outgoing
link.
D
So
on
the
incoming
link,
you
got
a
Datagram
tag
designed
by
the
previous
hub,
and
you
have
to
manage
your
own
Datagram
tags,
because
that
Datagram
tag
might
have
been
taken
that
you
actually
now
get
there.
So
you
essentially
just
have
a
table
that
pairs,
source
and
destination
addresses
and
Datagram
tags,
and
that's
all
you
need
to
stop.
So
that's
really
very
little
information
and
the
nice
thing
is.
You
can
have
many
many
more
of
these
virtual
reality
buffers
then
the
big
rear
ones.
D
Now
what
I
said
is
not
entirely
true
because
too
far
were
the
fragment.
You
actually
need
media
access
and,
of
course,
if
the
media
access
is
under
contention,
you
may
be
in
a
situation
where
you
get
more
fragments
in
that
you
actually
can
can
get
rid
of.
So
you
still
need
to
have
some
some
buffer
space,
of
course,
but
this
is
buffer
space
that
is
measured
in
fragments
and
not
in
entire
packet
buffers
that
you
need
to
have
reserved,
but
that
are
unused
most
of
the
time.
So.
D
Things
apart
from
what
I
just
said
things
you
have
to
consider
is,
you
might
have
to
wait
for
more
than
one
fragment.
If
the
first
fragment
doesn't
contain
all
the
information,
you
will
need
to
make
the
layer
three
forwarding
decision.
For
instance,
if
you
have
a
giant
salt
rotting
table
that
is
not
going
to
work
out
of
order.
Fragments
are
a
problem.
Of
course.
D
The
the
Desertec
situation
is
essentially
the
same
as
with
rear
wheel
assembly
buffers,
except
that
the
resources
consumed
by
every
assembly
buffer
are
much
smaller
now.
So
it's
somewhat
mitigated,
but,
of
course
somebody
who
really
wants
to
over
load.
You
can
still
send
you
tons
of
first
fragments.
There
is
no
fragment
recovery
in
this
technique.
D
It's
just
an
implementation
technique
and
also
just
as
with
with
reassembly
buffers,
you
have
to
send
out
all
the
fragments
on
the
same
link,
so
you
cannot
do
per
fragment
routing
and
as
soon
as
you
need
one
of
these
things,
you
actually
need
more
protocol,
so
you
cannot
just
use
494
for
and
implement
it.
This
way
you
need
additional
protocol.
I.
Just
looked
it
up.
Pascal
submitted
the
the
grandfather
of
trivial
Sixto
fragment
recovery
on
february
6th
2008.
S
I'm,
yes
from
India,
so
this
shows
previous
simulation
result.
I
implemented
both
RC
49:44
resembling
a
fragmentation
mechanism
and
also
the
the
drug
patent
asks
or
the
minimum
fragment
so
that
what
the
court
sent
now
explained
so
I'd
like
so
maybe
you
know
the
the
idea
is.
The
blue
line
is
a
fragment
falling.
That's
using
the
via
the
table,
so
that's
consumed
less
much
much
less
memory
compared
to
the
49
portable,
so
that
the
x-axis
it's
a
number
of
a
fragment
or
pocket.
S
That
means
yes,
no
frame
loss
due
to
the
text
buffer,
overflow
and
also
the
sink
node
at
the
top
of
the
root
node
have
no
memory
limitation
to
try
to
understand
what
happened
in
the
intermediate
node,
so
yeah.
So
that's
very
appreciative
dissolved
and
I'm
I'm
around
there.
So
it's
contact
me
if
we
want
to
know
more
details.
S
F
C
Q
Q
Then
it
gets
a
fragment
from
node
6
and
drops
that,
because
there
is
no
not
enough
space,
and
so
what
you
see
here
is,
and
if
you
had
an
infinite
memory,
everything
would
be
perfect.
Rather
you
do
fragment
forwarding
or
not.
It
would
be
perfect,
but
as
soon
as
you
introduce
the
limitation
of
memory,
which
is
very
real,
you
lose
data,
so
we
have
results
with
one
reassembly
buffer
to
resettle
you,
our
first
really
buffers.
It
gets
a
little
bit
better,
but
but
you
never
get
to
100%
the
way,
the
way
the
minimum
fragment.
Q
Plus
you
see
the
difference
on
ram,
there's
about
a
five
x
factor
of
ram
memory.
I
mean
there's
no
question
this
is
this
is
just
this
is
just
working
better
as
an
implementation
technique
that
everybody
should
use.
Of
course,
this
this
slide
and
this
work
does
not
at
all
compare
this.
The
limits
of
minimal
fragment,
with
fragment,
covering
so
just
playing
with
minimal
fragment.
Q
What
we're
working
on
is
is
is
more
big,
bigger
scenarios
with
real
traces
to
to
see
like
large
deployments,
that
we
know
that
we
master
at
least
kind
of
things
kind
of
going
beyond
the
simple
canonical
case
that
you
see
on
the
left
here
to
something
more
real,
but
we
don't
expect
the
results
to
be
very
different.
I
mean
we'll
just
provide
some
fancier
numbers,
but
it
will
be
the
same
bass
message.
Q
We
haven't
thought
about
comparing
the
tool
approaches,
yet
it
will
happen
somewhere.
So
so
one
point
of
clarification-
and
probably
this
slide
here
is-
is
wrong,
but
we
had
this
big.
You
know,
because
we
had
a
decentralization
of
one
day
between
our
different
drafts.
What
we
will
do
is
have
two
6lo
I
mean
what
the
plan
is
is
to
have
two
six
little
documents
and
one
L
wig
document.
The
first
six
will
document
explains
the
context
and
the
limits
of
the
different
implementation
techniques.
Q
C
E
So
in
interest
of
time,
because
we
not
have
it
I
won't
go
through
any
details
about
what
this
drug
does,
but
just
what
the
update
here's
the
main
update
is.
The
title
has
changed,
because
the
draft
was
doing
two
things,
it
was
doing
fragment
forwarding
and
he
was
doing
fragments
recovery
and
over
least
ten
years.
History
of
this
draft
that
Justin
has
been
talking
about.
The
name
has
changed
back
and
forth
between
insisting
on
the
recovery
side
and
and
the
fawning
side
and
I
never
knew
which
one
to
pick
up
for
the
title.
E
But
now
this
is
finally
resolved
because
I
just
took
out
of
the
draft
the
description
of
the
forwarding,
because
now
it's
in
constants
raft,
so
that
that
makes
my
life
simpler
about
finding
a
title
to
it.
That
also
makes
my
life
about
explaining
how
the
forwarding
works,
because
Caston
is
giving
a
lot
more
and
better
details
on
this.
E
So
basically,
the
main
Tiff's
between
this
drop,
zero,
zero
and
the
fragment
forwarding
away
that
was
in
the
original
agenda
is
that
the
details
of
the
mpls
operation,
using
the
data
can
tag
our
god
right,
but
that
doesn't
did
not
actually
take
out
a
lot
of
the
draft.
That
was
a
small
piece.
It
was
a
very
important
piece.
Obviously,
but
it
was
small.
E
Now
we
insist
on
the
fact
that,
because
we
are
doing
the
acknowledgement
back,
we
not
only
have
one
LSP
from
the
source
of
this
nation,
but
as
we
are
forming
this
path,
we
are
also
forming
the
return
path
from
the
destination
to
the
source,
which
labels
us
to
send
the
acknowledgement.
So
conceptually,
if
you
and
that'sthat's
to
be
synchronized
with
Gaston.
But
if
you
see
that
the
VOB,
as
as
part
of
this
constituent
label
switch
path,
they
are
for
my
draft
I
need
two
of
them,
so
it
will
be
better
and
I.
E
E
The
other
thing
is
because
the
description
of
the
three
draft
was
not
exactly
clear
at
the
time
of
the
publication
of
this
draft
I'm
pointing
untrust
batini
for
for
the
forwarding,
and
they
would
have
to
change
that
to
point
on
draft
custom
right
and
that's
that's
how
it's
gonna
work,
otherwise
I
mean
you
know
like
Gaston
say
that
the
operation
there
it's
been
there
for
a
while.
So
if
you
want
at
a
next
session,
I
can
go
into
more
details
about
how
the
acknowledgement
works,
etc.
But
we
don't
have
time
today.
E
So
let
me
just
show
you
the
difference
between
what
we
do
here
and
what,
when
the
value
of
changing
ever
having
the
new
Donna
track,
format
is
first,
we
can
do
selective
recovery
of
individual
fragments.
We
have
a
bitmap
pretty
much
like
we
do
in
help
Iran
and
the
bitmap
expresses
the
individual
fragments.
So
the
acknowledgment
back
all
the
way
well
tell
which
fragments
were
lost.
E
It's
not
the
only
problem
that
we
solve.
If
you
remember
the
presentation
I
made
several
ATF's
ago,
I
listed
like
five
or
six
problems
and
forwarding
and
the
size
of
buffers
were
one
of
two
of
these
primes,
but
some
of
them
were
due
to
the
second
stall,
sending
of
multiple
fragments
which
could
interfere
with
one
another
and
even
if
you
have
the
actual
buffers,
if
you
push
too
many
buffers
too
fast,
I
cussed
and
said
into
a
device,
you
may
still
have
a
right
number
of
buffers
that
it
has
since
the
DCP
days.
E
We
know
that
the
optimal
number
of
things
that
you
can
put
on
the
network
is
at
most
one
per
hop.
So
the
idea
is,
how
can
we
control
the
number
of
fragments
and
how
can
we
face
the
fragments
that
we
send
about
the
networks,
so
we
don't
eat
conditions
to
stay
in
the
condition
of
college
of
congestion
inside
the
network.
So
there
is
some
congestion
control
here.
So
this
goes
beyond
these
benefits
from
everything
that
Thomas
said.
But
this
goes
beyond
into
protecting
the
network
and
preventing
the
loss
of
individual
individual
fragments.
E
B
So,
thanks
to
the
design
team,
I
think
we
have
good
answers
for
some
of
the
at
least
the
initial
questions
that
we
set
up
to
to
to
resolve.
At
this
point,
the
the
question
for
the
design
team,
a
team
is:
are
you,
okay,
with
the
direction
you're
giving
the
work
at
the
drafts
that
you
were
giving
to
the
working
group?
Is
there
anything
else
you
would
like
to
still
attack,
but
before
the
solving
promise,
yeah.
Q
D
B
Q
Design
team
done
so
yeah,
so
that's
exactly
the
point.
I
was
going
to
make
I
mean
in
the
end,
these
are
workgroup
documents,
they're,
not
design
team
documents,
so
III
think
we're
done
once
once
those
three
documents
have
entered
the
pipeline
within
the
different
working
groups,
I'm
asking
actually
asking
for
your
for
your
advice.
Q
If
we
were
in
two
documents,
I
think
we
should
close
the
work,
the
design
team
right
now,
since
we're
talking
about
now
three
documents,
one
elevate
to
six
low
I
think
there's
a
little
bit
of
editorial
work
to
be
done
on
my
on
the
on
the
first
six
real
document,
so
I
would
feel
more
comfortable
if
you
agree
to
to
not
close
the
design
team
right
now.
Just
let
us
do
this
for
a
couple
of
weeks
and
then
once
it's
in
the
pipelines,
we
just
close
the
design
team,
yeah,
I,
think
I.
Think.
B
B
K
I
think
like
suresh
krisshnan,
so
I
think
these
are
like
orthogonal.
You
can
keep
it
going
on
if
you
want
like
you,
can
keep
down
like
for
the
myth
design
team
like
we
had
the
stuff
in
parallel
right,
but
everything
still
goes
through
consensus,
so
we
had
a
call
like
once
every
two
weeks
or
whatever,
it's
just
to
make
sure
that,
like
anything
coming
in
the
working
group
process
is
funneled
in
and
the
results
are
found
back
right.
K
Q
T
Thanks
for
giving
me
some
time
to
talk
so
I'm
Benjamin,
I'm,
Benjamin,
chato
I
walk
for
Kyle.
We
walked
on
the
hunter
platform
to
implement
and
travesties
for
for
this
platform.
So
so
we
provide
them
from.
We
provide
some
test
specifications
from
the
quraan
terraces
of
6lowpan,
for
neighboor
discoveries,
aid,
occupations
and
and
all
suits
on
testes
without
it
occupations.
So
you
can,
we
will
send
we
coming
to
communicate
to
you
through
the
meaning,
many
missed
more
information
from
how
to
access
to
the
platform
and
outperform
the
test
and
etc.
T
For
you
to
be
able
to
use
this
platform,
and
while
using
this
platform
given
giving
giving
us
feedback
on
out
who
to
integrate
more
things
and
ought
to
improve
this
this
platform
also,
we
will
also
organize
a
6lowpan
plug
test
in
the
next
six
months
to
come.
So
during
we
will
send
you
more
informations
about
the
diet
and
the
place
for
those
who
don't
know.
I
will
explain
a
bit
what,
in
short
run
platform
is
girl.
T
So
if
you
have
some
questions
or
comments
to
make,
you
can
you
can,
or
we
can
talk
after
I,
just
unfinished
implementations,
to
share
to
try
to
try
and
test
the
platform
a
bit
more
because
we
only
used
66
depending
fermentation
on
Linux,
on
raspbian
to
test
the
platform.
So
we
could
be
good
for
us
to
have
another
pod
implementation.
If
you
awesome
any
comments.
