►
From YouTube: IETF101-HOMENET-20180323-0930
Description
HOMENET meeting session at IETF101
2018/03/23 0930
https://datatracker.ietf.org/meeting/101/proceedings/
B
C
C
D
E
C
A
Well
can't
do
it
with
my
glasses
or
without
that's
great.
It
must
be
Friday
morning,
so
yeah
I
mean
the.
The
main
draft
that
we
have
that's
active
is
the
one
from
Ted.
On
the
simple
naming
we
have
a
number
of
oh
yeah,
the
the
HomeNet
dot
is
getting
really
close,
really
really
really
really
really
close
to
being
published,
and
that's
great.
The
the
HomeNet
profile
Babel
profile
is
now
on
the
agenda
for
the.
C
A
So
yeah
that
agenda
the
iesg
tell
a
chat
agenda.
It's
in
May,
so
that's
good,
that's
progressing!
We
do
have
these
other
drafts
working
group
drafts
that
are
hanging
around
at
some
point,
we'll
have
to
decide
what
to
do
with
them
and
then
there's
the
other
stuff.
Any
comments
on
any
of
these
good.
Let's
move
on.
E
C
E
E
Wow,
so
there
was
a
bit
of
a
hiatus
for
me
and
not
much
has
changed,
but
the
changes
that
have
happened
have
actually
been
pretty
substantial.
I
really
I
took
a
look
at
the
document
after
kind
of
a
several
month,
hiatus
from
working
on
it
and
realized
that
it
was
really
poorly
organized
and
probably
quite
difficult
to
follow.
I
mean,
of
course,
you
know
anybody
here
could
probably
parse
it,
but
it's
a
lot
of
work
to
parse
and
it
shouldn't
be
that
much
work.
E
So
I
reorganized
and
I
think
the
new
organization
is
better
I'm
curious
to
know
other
people
think
that's
true.
Also
I
didn't
I
was
a
little
rushed
getting
the
document
in
before
the
deadline,
and
so
there
are
some
places
where
it
says
things
that
aren't
correct.
Sorry
about
that
that
will
get
fixed
in
the
future,
hopefully
the
near
future.
E
So
it's
not
the
full
architecture
and
it
doesn't
require
full
service
resolver
and
it
needs
some
work
on
expanding
the
the
new
sections
that
I
added
to
read
when
I
reorganize,
because
when
I
reorganize,
what
I
found
was
that
actually
there
was
a
whole
bunch
of
text
about
certain
things
and
there
was
a
lot
missing
on
the
other
stuff.
Next
slide:
okay,
so
the
new
structure.
Just
briefly,
it's
now
structured
based
on
the
things
that
you
need
to
do
to
make
home
network
at
the
home,
not
naming
architectural
work
in
your
home
net
I.
E
So
name
is
just
a
four
word
domain
name
for
the
home
net
and
in
the
simple
architecture
this
is
always
home.
Darpa
I
mean
you
could
go
into
the
UI
and
change
it
to
something
else,
but
I,
don't
know
why
you
would,
and
you
know
when
I
say
you
could
go
into
the
UI
I'm
saying
speaking
hypothetically
I.
Don't
actually
know
that
you
can
do
that,
so
there's
no
support
for
delegating
a
global
name.
E
If
you
want
you're,
like
you
know,
if
you
want
your
home
net
to
be
Ted,
dot,
home
or
Ted
dot,
it
wouldn't
be
Ted
down-home.
But
you
know
Ted
comm
example.com.
If
you
want
your,
if
you
want
it
to
be
example,
welcome
you're
not
going
to
be
able
to
set
that
up
using
the
simple
naming
architecture,
because
the
simple
naming
architecture
doesn't
really
provide
name
service
in
the
traditional
sense.
Next
slide
so
authority,
every
home.
That
obviously
needs
to
have
an
authoritative,
DNS
server.
E
That's
not
as
complicated
as
it
sounds
in
the
simple
home
net
naming
scenario:
that's
just
a
discovery
proxy.
So
there's
no
stable
storage
and
it's
supporting
locally
served
zone,
so
home
DARPA
FCIP,
six
arca
archa
is
for
you
la's
and
then
ten
dot
in
an
editor
160
at
da1,
8201,
16.7
teen
done
in
our
DARPA,
so
that
you
can
do
reverse
lookups
and
obviously
it's
not
required
to
support
any
of
those
that
aren't
being
used
on
the
home
net.
But
that's
what
needs
to
be
there
and
it'll.
E
Also
answer
for
any
of
the
other
local
locally
surf
zones.
I'm,
not
sure
I,
know
that's
not
an
exhaustive
list,
but
I
can't
think
off
the
top
of
my
head.
What
the
other
locally
serves
are,
but
it
has
to
answer
for
them
too.
Next
slide
that'll
be
fleshed
out
in
the
document,
so
name
resolution.
So
we
need
obviously
something
listening
on
port
53.
That
will
answer
questions
that
any
host
on
the
local
wire
asks.
E
E
It
could
be
a
caching
resolver,
so
it
could
be
doing
full
service,
like
you
know,
recursion
and
stuff
like
that.
But
the
simple
I'm,
not
naming
architecture
certainly
doesn't
require
that
it
doesn't
I,
don't
think
it
forbids
I,
don't
well,
it
doesn't
say
anything
about
it
right
now,
I,
don't
think
it
will
forbid
that
and
I'm
curious
if
anybody
thinks
it
should
so,
but
the
key
feature
is
that
it
has
to
support
diversion
of
locally
serves
own,
so
this
is
sort
of
the
as
we
were
talking
about
split
horizon
and
DNS
ops.
E
E
Publication,
so
the
idea
is
that
services
need
to
be
able
to
publish
information
about
the
service
they
provide
on
how
to
reach
them
and
manage
the
lifetime
of
that
information.
Now
for
for
discovery
proxy,
that's
pretty
straightforward.
They
just
you
know
they
answer
em
DNS
queries
and
the
lifetime
of
those
M
DNS
queries
is
basically,
however
long.
The
thing
sits
answering
in
DNS
queries
as
soon
as
it
stops
at
some
point,
not
too
long
after
that,
the
existence
of
the
server
will
no
longer
be
apparent.
Nextslide.
E
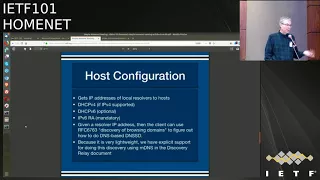
Hose
configuration
so
it
needs
to
get
the
IP
address
of
a
resolver
to
your
host
so
that
you
can
actually
talk
to
the
resolver
and
there's
basically
three
methods
that
I
know
of
to
do
that.
If
anybody
else
has
other
suggestions,
please
let
me
know
I,
don't
think
that
we
should
be
requiring
dhcpv6
stateless,
not
stateful,
but
stateless,
but
we
certainly
could
do
it
that
way.
E
So
let's
see
so
once
once
the
host
has
an
IP
address,
it
can
discover
so
a
little
bit
of
background.
Rfc
67-63
describes
a
way
that
you
can
advertise
service
discovery
and
well
in
in
DNS
and
so
rather
than
using
M
DNS,
and
that's
how
simple
home
that
naming
works.
So
in
order
to
use
that
you
need
to
be
able
to
go
look
in
the
zone
to
find
to
find
what
your
local
zone
is.
That
so
that
you
can
do
service
discovery
and
there's
a
process
called
discovery
of
browsing
domains
in
RFC
67-63.
E
We
in
the
in
the
discovery
relay
document
there's
actually
some
text
that
says,
if
you
get
an
M
DNS
query
to
do
browsing
domain
discovery,
you'll
answer
it,
so
we
don't
normally
the
discovery.
We
don't
normally
do
em
DNS
as
a
service
on
the
home
net.
All
though
it's
present
on
the
local
wire,
if
something's
doing
it,
but
this
particular
thing
we
do
because
it's
a
single
packet
exchange,
whereas
if
you
wanted
to
go
lookup
discovery
browsing
using
DNS,
it
takes
longer.
Yes,.
E
Don't
know
I
guess
that's
an
interesting
question.
I
think
the
right
answer
to
that
question
is
not
for
me
to
make
a
definite
statement,
but
to
say:
let's
talk
about
it,
so
if
he
could
bring
that
up
on
the
mailing
list,
I'd
love
to
have
a
discussion
about
it.
I
think
that's
a
great
question
to
ask
next
slide.
E
Who
trusts
so
on
a
simple
home
net
trust
you
suit?
You
have
to
have
some
kind
of
trust
for
simple
naming.
The
only
trust
the
only
basis
we
currently
have
documented
for
talked
about
for
trust
is
that
you
know
the
thing
is
local
and
it's
not
particularly
trustworthy,
but
it's
you
can
at
least
trust
that
it's
the
local
thing
could
be
nice
to
have
something
better
than
that,
but
for
now
we're
essentially
relying
on
the
local
link,
and
my
expectation
is
that
the
document
when
it's
done
will
be
relying
on
the
local
link.
E
This
is
something
the
working
group
might
want
to
think
about,
but
I
suspect
that
that's
what
we're
going
with
I
have
some
ideas
for
how
to
do
something
better
than
that.
I
think
those
might
go
in
the
advanced
home
that
naming
architecture.
If
people
think
that
we
need
this
in
a
simple
home
that
naming
architecture.
Let's
talk
next
slide.
E
So
speaking
of
advanced
tonot
naming
architecture,
so
the
idea
when
I
propose
the
simple
home
that
naming
architecture
was
that
we
would
have
the
simple
home
that
naming
architecture
which
would
suck
actually
no
it'll
be
awesome,
but
but
it's
not
as
good
as
the
advanced
naming
architecture,
but
they
have
to
coexist.
If
you
have
a
bunch
of
routers
that
implement
the
simple
naming
architecture,
they
have
to
work
with
routers
that
support
the
advanced
naming
architecture.
E
Think
I
believe
that
means
that
we
need
to
actually
define
the
advanced
naming
architecture
before
we
finalize
the
simple
naming
architecture:
I,
don't
think
it
has
to
be
done,
I,
don't
think
it
even
has
to
be
an
adopted
by
the
working
group,
but
we
need
to
have
some
sense
of
what
we're
doing
so
that
we
don't
wind
up,
producing
something
that
doesn't
actually
help.
So
it's
my
intention
to
work
on
that
between
now
and
Montreal
and
hopefully
have
something
fleshed
out
that
we
can
work
with
next
slide.
E
So
next
steps,
aside
from
the
advanced
naming
architecture
bit
I,
need
to,
we
need
to
flush
out
the
the
new
sections
that
I've
added
to
the
simple
naming
architecture.
Assuming
that
everybody
agrees,
that
that
was
the
right
thing
to
do
reorganizing
it.
The
way
I
did
the
authors
so
far
have
not
thrown
any
tomatoes
at
me,
I
kind
of
did
that
unilaterally.
E
We
need
to
finish
the
security
consideration
section
and
once
we
have
a
fairly
complete
version
of
the
document,
I'd
like
to
get
some
review
from
the
working
group.
That's
you
guys
and
I
think
before
we
actually
go
for
a
last
call,
I'd
like
to
have
some
working
implementations
and
Stewart
and
I
are
working
together
on
doing
that.
E
Of
course
yeah,
and
actually
you
you
were
asking
yesterday,
I
think
Indian
SSD
about
whether
this
would
be
something
you
could
just
sort
of
you
know
add
to
your
to
your
list
of
packages
and
I
agreed
that
I
would
make
it
so
that
you
could
actually
add
it
to
the
latest.
If
you
have
the
latest
version
of
open
wrt
the
distribution
running,
then
you'll
be
able
to
add
a
feed
and
just
subscribe
to
that
package,
and
you
should
be
able
to
get
home
nicknaming
working.
F
E
Many
people
in
the
room
are
running
open,
wrt
or
something
like
it.
Okay,
that's
a
lot
of
hands.
How
many
of
the
people
who
raise
their
hand
would
be
interested
in
this
code
and
running
it
on
their
home
network
or
wherever
they're
running
open
wrt,
not
as
many
hands,
but
a
pretty
good
number
great.
So
so,
yes,
I
will
we
will
be
announcing
that
on
the
mailing
list
and
yeah,
it
would
be
great
to
get
some
feedback
Andrew.
Oh.
G
Well,
that's!
Okay,
because
it
you
know
this
is
the
one
that
we
can
achieve.
Yeah
and,
and
now
it
sounds
like
what
you're
saying
is,
but
we're
gonna
need
to
have
at
least
a
plan
for
the
the
full-blown
performance
to
the
original
thing,
which
now
seems
like
a
you
know,
it's
a
it's
a
blocker
once
again
and
III.
Don't
care
and
I
agree
with
you
that
the
advance
thing
would
in
fact
are
the
complicated
or
whatever
we're
going
to
call.
It
is
the
that's
the
thing
that
actually
satisfies
what
we
said.
G
E
So
so
the
motivation
for
the
simple
naming
architecture
was
that
a
bunch
of
folks
got
up
at
the
microphone
about
I,
don't
know
four
or
five
IDs
ago
and
said
we
don't
want
to
implement
anything,
that's
complicated,
so
it
wasn't
actually
that
we
didn't
want
to
that.
We
didn't
want
to
have
an
advanced
home,
that
naming
architecture.
It
was
that
we
didn't
want
to
be
required
to
implement
it.
So
the
reason
for
splitting
them
out
wasn't
really
to
get
rid
of
the
dependency
on
the
advanced
architecture.
G
Okay,
so
I
remember
that
a
little
differently.
Okay,
you
know,
arguing
about
the
past
is
one
of
the
things
that
caused
me
to
get
divorced,
so
I'm
not
going
to
try
to
do
it
here,
but
that
the
I
have
the
impression
that
part
of
the
reason
people
didn't
want.
The
really
complicated
thing
was
Oh
too
complex
to
implement
and
part
of
it
was.
It
will
take.
You
know,
900
years,
to
come
to
consensus
on
on
some
of
these
things,
and
everybody
was
tired
from
the
routing
discussion.
We
didn't
want
to
repeat
that
right.
E
Right,
so
it
will
not
be
good.
So
what
I
said
on
the
previous
slide?
Maybe
I
didn't
say
it
related
work,
so
I
don't
need
the
working
group
to
have
consensus
to
even
adopt
the
advanced
naming
architecture.
Document
I
just
want
to
know.
What's
going
to
be
in
the
advanced
naming
architecture
document,
with
sufficient
clarity,
that
I
know
that
we
haven't
left
something
out
of
the
simple
naming
architecture
document
and
I
think
that's
a
lower
bar
than
what
you're
worried
about
now.
All
right,
maybe
maybe
I,
am
being
unrealistic.
E
Maybe
it
would
actually
be
better
if
we
actually
finished
the
advanced
naming
architecture
document
before
finalizing
the
simple
naming
architecture
document.
But
that
is
not
what
I'm
proposing
to
do
and
that's
a
debate
we
could
have
if
somebody
wants
to
have
it
but
I'm
not
planning
on
having
it
if
nobody's
gonna,
bring.
H
F
F
You
probably
can,
but
it's
like
there
is
no
reason
to
so
most
of
the
devices
they're
shipping
today
have
like
256
Meg's
of
RAM,
and
you
know
sixty-four
banks
of
flash
or
even
more.
So
this
is
less
of
a
problem
that
it
was
three
years
ago
when
we're
having
the
large
discussion
about
how
to
keep
down
the
footprint
to
like
the
bytes,
we
optimize
the
bytes
please-
and
this
is
less
of
a
thing
anyway.
I
when.
E
I
looked
a
couple
of
like
about
a
year
or
two
ago
to
see
if
it
was
possible
to
buy
a
z80
still.
Does
anybody
remember
the
80s
yeah
and
it
turns
out
you:
can
they
still
make
them
they're,
very
small,
and
this
the
slowest
one
I
think
is
like
two
gigahertz
or
something
like
that?
It's,
like
ludicrously
fast,
like
any
program
that
you
had
that
ran
on
a
z80
back
in
the
day.
It
would
finish
before
you
before
you
hit
return
so
anyway,
next
step,
so
is
that
the
last
slide?
That's
all.
A
I
A
I
love
the
reorganization,
Ted
really
did
it
make
things
so
much
clearer.
What
I
was
thinking
about
was
in
the
context
of
multiple
routers,
which
of
course
is
part
of
Hell
Nets
charter
and
trying
to
understand
what
will
be
the
interrelationships
between
the
multiple
routers
who's
going
to
win.
You
know,
you
know
if
there's
multiple
things
delegating
multiple
things:
how
are
they
going
to
decide?
E
A
E
C
Many
people
have
read
this
version,
not
so
many
how
many
people
have
read
a
recent
version
likely
more
so
yeah.
We
clearly
need
to
get
more
more
feedback
and
second
extent
there
was
a
in
in
the
document.
There
was
a
bunch
of
places
where
there's
like
I
still
have
a
bit
of
work
to
do
TBD
kind
of
stuff
yeah.
It
wasn't
clear
to
me
which
of
those
were
difficult
which
of
those
were
reduced
editorial
from
reading
through
it.
So
my
question
is:
would
it
be
possible
to
try
and
flag
the
ones
that
need
more
discussions?
C
E
That's
yeah,
that's!
Actually
it
might
be
good
to
just
go
through
the
document
like
one
section
at
a
time
and
have
the
list
discussion
on
that
section
of
the
document
and
talk
about
what
the
problems
in
that
section
are
or
solicit.
You
know,
I,
don't
think
there
are
any
problems.
Does
anybody
disagree
with
that
and
see
how
that
goes
because
yeah
I
agree?
There
are
some
things
that
are
hard
and
there
are
some
things
that
are
easy.
It
would
be
nice
to
to
get
a
feedback.
Julia
scrovo.
J
Check
I'm,
sorry,
if
I
repeat
myself,
it's
very
difficult,
at
least
in
my
experience,
or
at
least
I'm,
not
smart
enough
to
see
the
problems
in
a
document
before
I
implement
it.
Okay,
now
we've
been
through
that
before
and
I
think
we
did
not
quite
agree,
but
I
think
it
would
be
a
very,
very
good
thing
to
have
a
third
party
implementation
of
this,
so
that
we
can
know
whether
there
are
any
problems
and.
A
J
K
E
E
Have
any
undergrads
who
might
be
interested
I'm?
Nothing
no!
Have
any
colleagues
ooh
anyway,
yeah,
no
I
absolutely
agree
with
you
and
if
you
know
of
somebody
who's
interested
in
doing
this
work,
I
would
love
to
do
it
with
them
or
I
would
actually
be
better
if
I
didn't
do
it
with
him,
but
I'd
love
for
them
to
do
it.
So
the
problem
is
just
finding
somebody
that
wants
to
do
that.
Only
yeah.
E
Is
that
is
there
are
too
many
bits
to
assemble
there?
There
are
a
lot
of
moving
parts
in
this,
I
mean
if
you,
if
you
really
wanted
to
do
a
serious
implementation
of
it,
you
would
have
to
implement
the
the
proxy
that
I
talked
about.
You'd
have
to
implement
a
DNS
SD
discovery,
proxy
and
you'd
have
to
implement
a
discovery
relay
so
there's
a
fair
amount
of
code.
There
I
mean
the
discovery
relay
like
somebody.
E
Who's
really
gung-ho
could
probably
get
one
working
in
somewhere
between
a
week
and
a
month
that
would
sort
of
limp
along.
Obviously,
it
would
need
some
beating
on
to
mature,
but
it's
definitely
not
a
hackathon
level.
Thing
I
mean
that's
not
to
say
that
you
know
I
mean
somebody
could
could
get
to
get
show
up
at
a
hackathon
and-
and
you
know,
assemble
parts
and
probably
come
up
with
something
and
that
might
still
be
instructive,
but
so.
A
H
E
E
C
L
L
You
may
know
me
from
TV
shows
such
as
anima
and
brewski
and
I've
been
doing
a
lot
of
work
crossed
a
couple
working
groups
between
Netcom,
Panama
and
sixth
ish
in
doing
enrollment.
What
what
we've
often
called
join
and
we've
stopped
calling
it
join
a
little
bit
because
it's
it's
confusing
for
some
things
that
where
you
join
other
things
in
other
places,
so
I'm
gonna
be
talking
a
little
bit
about
the
brewski
protocol.
L
That's
bootstrapping
remote,
secure
key
infrastructure
and
you
can
be
sure
that
we
came
up
with
the
acronym
first
and
how
it
might
work
in
home
net
or
not
work
in
home
net.
So
next
slide,
please
and
Paula
G's
I.
That
slight
numbers
just
never
seem
to
work.
For
me
they
always
I
should
previous
slide
has
six
ones,
and
this
one
has
none.
L
You
can
ship
it
out
and
the
equipment
will
discover
your
network
and
will
join
your
network
and
join
your
domain
and
get
a
credential
in
your
domain
and,
at
the
end
of
the
day,
you'll
see
it
pop
up
as
an
icon
in
your
NOC
Center,
even
though
you've
never
touched
the
equipment,
and
so
this
is
something
that
you
know
is
that
human
operators
used
to
do
through
quote
South
interfaces,
which
often
means
a
laptop
plugged
into
that
piece
of
equipment,
and
that's
just
something.
People
don't
want
to
do
anymore
for
wide
variety
reasons.
Next
slide.
L
So
we
have
three
basic
pieces
of
the
Ani,
the
autonomic
network
infrastructure.
We
have
the
secure
boot
strap,
which
is
brewski.
We
have
a
secure
and
dedicated,
essentially
VPN,
which
is
known
as
our
autonomic
control
plane,
and
we
have
a
generic
single
link
protocol
known
as
grasp
just
not
unlike
hn
CP,
but
has
a
different
goal
in
many
ways
and
is
more
about
the
content
than
of
the
negotiation
than
the
transport
of
it,
and
we
put
them
together
and
we
get.
We
get
a
useful
system
where
we
essentially
get
a
management
interface.
L
What
would
have
you
know
in
times
past
been
a
been
a
phone
line
over
or
some
other
out
of
an
connection
which,
of
course,
that's
all
disappeared,
so
it's
only
the
internet.
So
if
you
don't
have
a
Noda
band
connection,
then
you
have
nothing
to
to
rescue
the
system.
On
top
of
this,
we
run
what
are
called
autonomic
service
agents,
and
if
it
sounds
a
bit
like
voodoo
and
hoping
I
would
say,
it
is
a
little
bit
at
this
point.
L
But
the
idea
is
that
these
are
the
things
that
go
and
configure
things
like
figure
out
that
you
need
address
space
in
a
particular
network
or
that
this
particular
installation
was
intended
to
be
to
serve
residential
customers,
and
it
should
turn
on
DSL
pppoe
interfaces
or
something
like
that.
That's
the
kind
of
thing
it's
supposed
to
be
kind
of
intent-based
next
slide.
L
So
a
little
bit
of
what
the
automatic
control
plane
is.
It's
essentially
a
VPN.
It's
an
IPSec
over
ipv6
link
layer
addresses
we
build
a
tunnel
on
top
of
that
and
we
actually
run
the
rolls
ripple
protocol.
On
top
of
that,
which
is
a
nice
simple,
lightweight
protocol,
that's
not
in
use
and
routers
otherwise,
and
that
one
of
the
reasons
to
have
a
different
one
was
because
it
being
different.
It
wouldn't
be
subject
to
what
vendors
are
already
doing
with
something
and
they
get
confused
and
mixed
their
different
via
refs
around.
L
So
that
was
a
little
bit
there,
but
also
it's
good
it
just
throw
in
felt
relatively
low
impact,
throwing
around
slash
128,
we
could
have
used,
we
could
have
used
Babel
or
Babel.
I
still,
don't
know
how
to
say
it
right.
That
was
a
certainly
possibility
as
well
next
slide.
So
how
do
we
bootstrapped
trust?
So
our
assumption
is
that
the
devices
come
out
of
the
block,
so
the
trust
anchor
linking
them
to
the
manufacturer.
L
That
is,
if
you
wrote
the
code
and
make
the
wrong
you
can
put
a
public
key
in
there,
for
which
the
private
key
you,
the
manufacturer,
control.
Then
the
end-user
convinces
the
manufacturer
that
the
device
belongs
to
them
and
the
manufacturer
issues
what
we
call
a
voucher.
So
that's
the
piece
that
actually
is
across
the
three
working
groups
are
using
the
same
voucher
format
for
between
net
Kampf,
anima
and
sixth
issue
and
its
Ana
document
called
IETF,
anima,
voucher
and
I.
Believe
it's
passed,
iesg
last
call
and
it's
in
the
RFC
editor
queue
the
device.
L
The
end
result
of
the
device
now
now
trusts
the
end
user.
So
you
think
well,
why
does
the
device
need
to
trust
the
end
user
I'm
interested
in
trusting
the
device?
Well,
the
thing
is
that
each
one
of
you
decide
what
network
you're
gonna
with
your
laptop,
what
network
you're
going
to
trust
by
clicking
on
the
little
Wi-Fi
icon?
L
L
The
flea
market
I
will
come
to
that.
That's
a
good
question
and-
and
we
don't
have
a
complete
answer,
but
we
have
a
number
of
different
answers
and
unfortunately,
some
of
it
depends
upon
what
the
manufacturer
wants
you
to
do.
So
it
is
possible
for
manufacturers
to
forbid
you
to
buy
routers
at
flea
markets,
but
it's
also
possible
for
for
systems
to
essentially
once
it
becomes
the
first
owners
router.
L
Then
the
first
owner
essentially
replaces
the
manufacturer's
identity
with
theirs
and
when
they
sell
it
to
you,
they
become
your
manufacturer,
but
which
point
you
of
course
receive
the
device
and
overwrite
that
again,
so
there's
different
models
to
do
that
and
we
haven't.
We
haven't,
said
a
specific
thing,
but
we
were
very
sensitive
to
the
that
we
want
to
support
resell.
L
L
L
So
next
slide,
please!
So
why
didn't
we
use?
Eap
people
have
asked
us
this
all
the
time
that
sounds
like
an
EAP.
Does
this
yeah
and
it
does
a
great
job
if
you're
already
a
member
of
the
domain,
the
problem
is
they're,
not
a
member
of
the
domain
at
this
point,
and
so
you
wouldn't
even
know
which
EAP
network
to
use
and
which
credential
to
use
on
that
network,
and
so
you
get
into
enrollment
problem
of
the
there.
L
Secondly,
it
appears
that
a
number
of
architectural,
a
number
of
switching
equipment,
just
the
concept
that
they
would
be
in
one
X
client,
rather
than
a
an
Authenticator,
it's
too
confusing
to
them.
Okay,
so
we
just
said
you
know
what
we
don't
want
to
go
that
way,
we're
just
gonna
step
aside
from
all
this
next
slide,
so
just
a
little
bit
a
little
bit
more
high-level
I
want
to
deep
drip
jumped
into
a
little
bit
of
stuff
pretty
quickly.
So,
as
I
said,
we
started
with
three
working
groups.
We
won't.
L
We
have
two
methods
in
six
Tish,
a
minimal
version
which
is
a
OneTouch
version
and
a
zero
touch
version,
and
then
we
grew
this
yellow
slide
and
beat
this
yellow
group
in
the
who
wanted
a
bit
from
the
sixth
ish
side
and
a
bit
from
the
brewski
side,
and
so
we
have
that
so
then
I
put
another
box
here.
You
know:
let's,
let's
have
another
another
member
of
the
wedding
party
here,
the
red
home.
L
L
So
the
essential
thing
is,
you
start
with
the
device.
We
call
it
a
pledge
if
you're
Animal,
House
fan
you'll
understand
immediately.
Why
they're
called
that,
but
essentially
a
pledge
is
someone
who
comes
along
and
says
I
I
agree
to
do
everything
that
you
tell
me
if
you
let
me
into
your
club
and
they
possess
a
certificate
and
they
come
along
some
network
next
line
slide.
So
we
have
a
couple
of
other
terminology
that
I
thought
I
throw
here.
So
we
have
pledged.
L
We
have
a
proxy
proxy
as
a
joint
proxy
as
device
that
helps
the
pledge
get
on
line,
and
then
we
have
a
registrar
and
we
started
using
joins
that
have
enrolled.
Sorry
start
these
enrollments
and
joined
because
join
had
a
different
context
for
a
number
of
people
and
that
different
meaning
and
people
got
confused
next
slide.
L
So
it
reaches
out
I,
P
link-local.
We
actually
have
a
grasp
multi
CASP,
that
happens
at
link
layer.
It's
not
unlike
the
HNC
p
meetup
messages,
but
it's
slightly
different,
of
course,
and
the
pledge
learns
about
the
proxy
next
slide
and
then
you
can
see,
there's
a
it's.
Not
so
maybe
should
have
made
a
deeper
line,
but
the
from
the
proxy
it
goes
through
the
pink
lines
to
get
to
the
registrar,
so
the
pink
lines
are
our
ACP
tunnel
and
and
that's
how
it
works.
L
The
proxy
can
be
stateless,
in
which
case
there's
enough
information
in
the
forwarding
such
that
the
traffic
can
get
back
without
doing
anything.
This
turns
out
to
be
pretty
important
in
constraining
networks,
because
nobody
wants
to
build
a
state
table
and
a
device
that
has
only
120.
You
know
neighbor
entries
or
less
sometimes
eight
or
it
can
be
stateful.
So
typically,
a
bigger
equipment
essentially
is
running
a
kind
of
port
forward.
Okay
and
we
use
est
so
next
slide.
L
Now,
there's
some
stuff
in
there
that
we
do.
We
have
a
provisional
state
in
the
TLS
connection.
We
have
both
client
and
server
certificates
involved.
Neither
party
can
immediately
validate
them,
and
so
we
have
a
period
of
time
when
the
connection
is
as
we
call
provisional
and
then
what
happens
is
that
the
manufacturer
issues
a
voucher,
so
the
voucher
says
essentially
to
the
device.
L
This
network
is
your
owner,
so
it
connects
the
the
the
pledge
can
validate
the
voucher
because
they
have
an
anchor
from
to
the
manufacturer,
and
the
manufacturer
of
the
network
has
a
public
key.
That's
been
been
referenced
by
the
voucher,
so
essentially
created
on
doing.
Do
we
create
on
is
almost
auditing.
Okay,
we
have
a
lot
of
text
that
decides
whether
or
not
you
can
write
vouchers
that
expire,
because
new
devices
may
not
have
valid
clocks.
L
Get
that
voucher,
so
I
want
to
get
it
now
when
I
put
it
in
the
warehouse.
So
a
lot
of
discussion
around
that
stuff
and
oh
and
at
the
end
of
the
day
everyone
will
be
offline
in
a
base
in
you
know,
Iraq
or
something
right
when
you
turn
on
the
light
bulbs.
So
we've
had
a
lot
of
a
lot
of
thought
about
how
that
works
and-
and
we
have
I-
think
a
reasonable
set
of
mechanisms.
L
We
have
to
date
explicitly
excluded
bearer
vouchers,
where
the
pins
domain
cert,
which
is
the
name
of
the
the
domain
owner
is,
would
could
be
blank
right.
So
we've
ruled
that
out
for
now,
because
we
think
we
don't
want
to
do
the
security
analysis
of
it,
but
there's
some
awfully
good
arguments
where
why
that
would
be
a
good
thing.
Next
slide,
oh
yeah
and
and
so
we're
right
now
it's
signed
with
CMS,
ok
pkcs7,
if
you
like,
but
there's
a
version
that
will
come
out.
L
That
is
probably
going
to
be
daunted
by
anima
this
week
that
will
sign
with
C
Bohr
and
cozy
and
sorry
encoded,
C
bar
sign
with
cosy,
so
things
at
home
at
does
not
need
the
ACP
is
overkill.
You
don't
need
that
you're
already
building
a
network,
you
don't
need
to
build
a
network
on
top
of
the
network
to
build
a
network
that
doesn't
make
any
sense.
L
Ok
in
the
anima
case,
you
know
we're
talking
about
equipment
that
is
in
multiple
cities,
with
many
pieces
of
potentially
Bart
dart
fiber
between
them
and
the
goal
is
to
have
a
management
network
that
connects
back
to
a
NOC
home
that
doesn't
have
that
that
requirement,
so
you
just
use
brewski.
Ok,
we
have
this
intent
based
policy.
That
is
a
bit
I'm
going
to
say
fairy
dust,
and
we
had
a
super
working
group
which
was
going
to
make
it
all
concrete
and
yeah
when
we're
kind
of
predictably.
L
But
in
anyway
the
intent
which
is
what
does
the
network
for
is
a
bit
implicit
in
home
net.
The
network
is
for
connectivity
of
the
user,
it's
really
I
mean
if
you
can
say
anything
more
complicated
than
that
I
think
you
got
it
right
wrong.
It's
possible
that
the
PKI
is
unnecessary.
Although
I'm
prepared
to
argue
that
point,
you
could
just
use
the
secure
transport
that
we
create.
You
could
just
use
it
to
exchange
PS
KS
if
you
wanted
to
Network
wide
PSK.
That
would
be
acceptable.
L
I,
don't
think
it's
I,
don't
think
it's
a
great
thing,
but
you
could
do
that.
You
could
just
change
route,
public
keys,
all
I'm,
not
sure.
Ultimately,
how
that
benefits
you-
because
you
have
to
you
just
have
everyone-
has
to
have
a
complete
set
and
brueski
with
the
vouchers
allows
you
to
make
that
secure
transport
allows
you
to
keep
it
around
as
well.
If
you
need
to
next
slide
what
you
probably
want,
you
probably
want
the
vouchers.
L
We
have
thought
a
lot
about
how
you
are
going
to
buy
a
device
at
fuchsia
shop
or
Walmart
or
Amazon,
bring
it
home
and
convince
the
manufacturer
that
it's
your
device.
So
we
have
these
things.
That's
called
audit
audit
logs
and
essentially
what
the
manufacturer
says
is
the
first
person
that
comes
along
to
claim
this
device
is
its
owner,
simple,
and
if
someone
else
comes
along,
we
like
to
claim
that
device.
What
they
will
find
out
is
it's
been
previously
owned.
L
Is
that
okay?
Do
the
previous?
Did
the
person
at
the
flea
market
load
it
with
Trojan
software
I,
don't
know?
Okay,
if
you
did
a
factory
reset,
the
manufacturer
is
still
going
to
have
a
record
that
it
was
owned
before.
Are
they
going
to
issue
a
second
voucher
because
they
for
it
for
a
different
person,
because
they
say
hey,
you
know,
maybe
the
device
is
stolen
or
maybe
I
don't
support
reselling.
Well,
that's
something
we
didn't
decide,
but
we're
enabling
all
of
those
decisions.
L
If
you
want
to
make
the
manufacturer
wants
to
make
them
I,
don't
know
if
you
familiar
with
with
mud,
so
I
believe
it's
in
iesg
Terry.
Do
you
know
I
think
it's
fast
iesg
yeah.
So
this
is
a
ops
area.
Submission
manufacturer,
uses
description
specification
and
essentially
allows
the
device,
such
as
a
printer
to
say,
I'm,
a
printer
and
I
have
absolutely
no
business
talking
to
an
IRC
Network
right
at
most
I
will
talk
to
this
one
one
host
at
one
place
to
get
to
get
my
firmware
updates
and
everything
else
is
nonsense.
L
So
please,
mr.
firewall,
if
you
see
anything
suspicious,
I'm
I'm
a
it's
a
problem,
so
that's
something
that
the
that
the
that
I
think
is
going
to
have
some
traction
and
we
have
some
integration
back
and
forth
where
the
mud
URL
specifies
our
masa,
which
is
our
manufacturer,
URL
and
there's
some
connectivity
back
and
forth
there.
If
long,
is
that
the
the
the
router
the
edge
router
is
going
to
acquire
somehow
the
information
well
in
the
process
of
doing
that,
you
can
essentially
do
all
the
enrollment
as
well.
L
You
know
I
know
it's
so
hard
to
get
them
to
ship
firmware
period,
but
you
know
if
they're
gonna
support
any
of
these
protocols
that
we're
gonna
finding
right
now.
I
think
that
that
it's
gonna
it's
going
to
be
helpful.
If
we
have
ongoing
involvement,
we
do
have
some
push
button
type
extensions
where
you
could
do
some
reduced
operations.
You
know
the
whole
I
push
two
buttons
in
this
kind
of
stuff.
We
wouldn't
describe
those
mechanisms,
the
specifics
of
them,
but
rather
how
they
fit
into
our
protocol.
Where
do
they
go
into
the
process?
L
So
there's
a
reduced
security
process
next
slide,
please.
So
what's
the
challenges
right,
so
Holman
etics
explicitly
a
non
professionally
managed
Network?
Oh
you
know
so
in
anima
we
said
we
only
deal
with
professionally
managed
networks,
and
that
was
to
exclude
us
trying
to
boil
the
ocean
of
the
whole
net
problem
as
well,
and
so
what
is
home?
That's
really
problem.
Is
it's
it's
unprofessional
so
that
the
opposite
of
professionally
managed
or
amateur
or
just?
Is
it
unmanaged?
It's.
L
You
know
you
can
pick
different
words
for
that,
but
they
have
actually
the
one
that
you
probably
matters
is
that
if
there's
infrastructure
required
in
the
home
net,
it's
probably
very
hard
to
get
it
independently,
funded,
whereas
in
an
enterprise,
if
someone
says
to
deploy
these
thousand
phones,
I
need
to
have
this
infrastructure
this
this.
You
know
other
system,
good,
look,
oh
yeah.
Okay,
that's
amortized!
Over
a
thousand
phones,
it's
okay!
It's
cool
I
got
that
right.
I
need
to
have
servers.
L
I
need
to
have
back
any
directory
act
as
that
stuff,
but
the
home
that
you're
like
well
I
just
want
some
more
disk
space
on
my
network.
Why
do
I
have
to
buy
this
other
thing?
I
just
want.
You
know
better
connectivity
in
the
upper
bedroom
right.
Why
am
I
buying
anything
else?
So
I
think
that's.
The
real
challenge
is
getting
this
piece
and
I
think
it's
the
same
problem
for
the
DNS
and
the
other
stuff
is
how
do
we
get
that
and
I
know?
L
That's
a
layer,
9
issue,
and
we
you
know
so
we're
not
supposed
to
talk
about
those
at
some
times.
But
if
we
don't
know
who's,
gonna
run
the
system
and
we
I
don't
think
we
can
design
it
properly
and
I.
Think
that's
really
important.
So
is
there
a
PKI?
Is
it
randomly
replaced
because
people,
just
you
know,
pick
equipment
off
the
network
and
shove
it
in
the
garbage
and
buy
something
new
right?
That
happens
right
I,
don't
like
it
watch
people's
perfectly
good
TVs
go
onto
the
curb
that
way!
L
Well,
what
if
the
PKI
was
in
their
TV,
because
that
was
the
machine
that
had
the
best
user
interface
the
biggest
screen
right
at
and
and
the
TV
doesn't
leave
the
house.
It's
a
really
good
place
to
put
new
PKI.
It's
not
supposed
to
leave
the
house.
All
of
your
other
devices
are
mobile
right.
So
maybe
that's
a
problem
isn't
Herge
our
sees
right.
L
Finally,
we
have
interactions
with
so-called
smart
home,
so
I
think
that's
going
to
be
a
problem
going
forward.
We're
gonna
we're
gonna
butt
heads
against
the
other
people
that
also
uninvaded
the
home
and
do
things
and
put
infrastructure,
and
it
might
actually
be
good
if
we
actually
have
an
answer
that
says
well,
actually
there's
an
IETF
spec
on
how
to
do
the
rest
of
the
stuff
and
you
are
actually
already
doing
it
so
either
you
have
you.
Have
your
registrar
or
the
home
net?
L
Has
it
and
you
pick
one
or
the
other,
and
that's
it
and
everyone's
happy
at
that
point
so
and
then
it's
possible
to
put
the
Registrar
in
the
cloud
I
don't
know
exactly
how
to
do
it,
but
I
have
some
ideas
and
I
think
it
could
work.
What's
the
next
the
next
slide.
Please
I
talked
about
that.
Let's
go
on
so
one
idea
is,
you
may
have
heard
the
hub
of
all
things.
It
was
an
attempt
or
it
is
an
attempt
to
bring
all
of
your
IOT
data
in
one
place.
L
They've
in
the
last
four
years
had
some
pragmatic
things
that
they're
now
doing
some
other
type
of
privacy,
your
private
data
collection,
but
they
want
to
get
back
to
this
and
fundamentally
they
want
to
put
a
box
in
everyone's
home
that
collects
everyone's
their
data
for
them
so
that
they
own
it
rather
than
other
people.
So
there
may
be
some
interesting
places,
some
other
movements
to
where
we
would
find
that
suddenly,
there's
something
something
interesting
happens,
next
slide
in
your
Nazz,
so
the
one
on
the
top
is
one
I.
L
Have
it's
a
hard
drive
with
a
very
like
almost
a
thing:
that's
just
barely
big
enough
for
the
bloody
connector
to
the
hard
drive
and
it
operates
as
an
as
you
can
buy.
These
things
now
called
newbie,
a
parent,
that's
gonna
change
name
because
they
don't
like
the
name
but
there's
five
or
six
kinds
of
things
like
that,
that's
more
than
enough
power
to
run
a
PKI
or
a
DNS
server
or
a
bunch
of
other
stuff.
The
question
is
who's
gonna,
maintain
it
for
the
next
10
years,
and
how
is
that
going
to
happen?
L
Where
is
there
where's
the
revenue
stream
out
of
the
home
to
get
that
paid?
For?
If
it's
not
going
to
happen,
then
I
don't
think
we.
If
we
can't
figure
that
out,
then
I
don't
think
our
technology
will
get
deployed
next
slide,
please.
So
what
do
I
suggest?
We
do
lots
of
layer,
9
problems.
Well,
you
could
help
us
finish.
The
current
work
reviews
are,
of
course,
welcome.
You
could
read
it
and
see
if
we
have
mutts
not
must
nots.
L
That
would
upset
you
that
if
you
were
going
to
apply
the
document,
this
would
be
a
problem.
Sheds
are
not
a
big
deal,
because
you
know
if
you're
writing
a
profile
for
home
net.
That
says
do
this
and
we
said
you
should
show
it
don't
do
this
and
we
said
you
should
do
that.
I,
don't
think!
That's
a
problem
next
slide,
so
we
could
write
a
profile,
a
brewski
for
home
net
I.
L
L
We
could
easily
get
to
a
point
of
you
know
doing
something
interesting
at
a
at
at
one
of
the
hackathons,
whether
it
produces
useful
code
for
that
could
be
shipped
different
question,
but
we
would
have
to
decide
just
tupple
things
about
the
joint
proxy
and
some
other
stuff,
and
it's
possibly
don't
need
to
join
proxy
that
that
ultimately,
connectivity
in
the
home
net
will
then
home.
That
is
flat
enough,
that
it
doesn't
matter,
but
maybe
that's
not
the
case
next
slide.
L
So
what
do
you
do
if
you're,
a
brewski,
happy
home
net
device
and
you
get
deployed
in
a
net
work
that
doesn't
have
it?
Yet?
What
is
your
fallback?
How
do
you
find
your
get
connected,
so
you
could
go
neck
off?
Is
your
attach
call
home?
That's
that's
fully
in
our
space
and
is
really
aimed
at
this
kind
of
stuff.
L
The
only
problem
is
if
it
works
too
well.
Well,
no
one
will
bother
deploying
their
own
public.
You
know
their
own
and
stuff
at
home,
and
a
lot
of
the
stuff
we'd
like
to
have
happen
won't
happen,
because
ever
the
devices
will
all
be
still
connected
to
the
cloud.
So
we
need
to
think
a
little
bit
about
that.
If
that's
something
we
want
to
solve
next
slide
questions.
E
Deb
lemon
thanks
for
preparing
this
Michael.
This
is
really
great,
so
I
guess
I'm,
I'm
curious,
so
so
I've
had
a
little
bit
of
experience
with
with
devices
of
the
type
that
you're
talking
about
on
my
home
net.
Recently
I
got
a
Wemo
because
I
was
kind
of
tired
of
z-wave,
not
working
and
so
you'd
be
interested
to
talk
about
the
various
problems
with
the
Wemo
registration
process
and
how
this
solves
them.
L
E
L
Where
we
actually
have
a
document
of
other
we
there
is
a
individual
submission
into
anima
about
nine
different
ways
to
do
anima
over
Wi-Fi.
You
know
in
a
zero
touch
way
to
me.
The
most
obvious
way
is
you
join
the
ESS
ID
called
anima,
which
is
unencrypted
and
do
stuff,
and
then
you
get
the
right
credentials
and
join
the
right
network,
but
there's
about
a
hundred
and
fifty
other
802
11
ways
to
skin
this
cat,
and
some
people
have
decided
to
to
at
least
write
them
down.
So
we
can.
L
We
can
taste
test
them
so
at
the
very
least
that
process
that
she
went
through
the
Wemo
would
be
the
Wemo
joining
your
network
you're
joining
network,
whether
it's
not
you
may
not
be
a
real
network
but
and
that
would
be
standard
so
that
it
would
be
real
and
you
wouldn't
have
to
be
oh
I
need
to
disconnect
my
phone
or
my
laptop
from
my
network,
join
their
network
figure
it
out.
But
now
I
can't
read
the
manual
because
I
don't
have
internet
anymore,
I
have
to
switch
back
again.
I
went
through
that.
L
E
F
Michael
Abramson
go
back
one
slide
just
since
I
was
talking
about
the
stuff
that
isn't
open,
TT
0
comes
is
here,
touch
call
home,
so
this
is
almost
done
and
this
call
home
there
is
already
in
open.
Wt
doesn't
have
any
plugins,
but
there
is
already
add
something
can
install
that.
Does
it
called
home
so.
L
F
F
L
F
F
Having
vendor
lock-in
and
someone
owning,
it
is
crucial
to
stop
theft
and
robbery
sazon,
but
for
home
equipment
I'm,
not
sure
that
the
use
cases
there
compared
to
the
downsides
of
screwing
it
up
I
mean
you
can
go
to
the
if
you,
if
you
buy
an
expensive
mobile
phone,
the
vendor
kind
of
supports
you
when
you
go
there
with
your
receipt
as
they
have
a
like.
That's
all
locked,
but
when
you
go
there
with
your
$30
or
something
else,
I
think
the
vendor
is
not
going
to
care
to
try
to
transfer
that
voucher
or
ownership.
L
Reset
this
factory
reset
right.
So
so
that's
exactly
so.
I
think
that
there's
a
wealth
of
different
things
and
I
think
we
can
write.
You
know
we
could
write
what
I
really
layer
eight
documents
about.
You
know
how
this
works
and
that
may
be
valuable.
But
for
the
moment
essentially,
we
support,
whichever
whatever
model
the
manufacturer
wants
to
do,
and
you
can
also
have
the
model
that
once
it
becomes
your
device,
it's
fully
your
device.
You
can
load
any
firmware
at
all.
If
that's
the
model,
then
you
become
the
manufacturer
before
the
next
guy.
K
Chapters
tale
just
go:
I'm,
sorry,
I
haven't
read
to
draft,
yet
it's
it's
a
bit
long
I'll
go
to
that
later.
First
of
the
from
the
from
the
deployment
in
operational
perspective,
I
think
relying
on
the
manufacturers
to
provide
such
service
is
a
bit
optimistic.
I
can
understand
how
it
will
work
when
manufacturers
Cisco
and
you
paid
multiple
thousand
bucks
or
your
device.
So
you
have
a
very
good
support
and
people
operating
it
are
actually
certified.
They
had
hours
of
lessons
to
know
how
to
do
that.
A
K
If
it's
not
so,
then
the
provider
is
going
to
have
a
call,
and
so
either
the
manufacturer
who
sold
the
device,
30
bucks
or
the
ISP,
who
sells
a
service
very
low
cost
as
well,
is
going
to
have
a
call,
and
they
don't
want
to
have
such
calls.
And
then
the
second
point
is
that
we,
few
years
ago,
like
a
couple
of
years
ago,
we
we
had
a
proposal
to
secure
HS
CP.
It
was
certainly
not
perfect,
but
it
held
it
was
implemented
and
it
was
way
shorter
in
terms
of
specification.
L
Expensive,
so
so
that's
why
I'm
saying
that
there's
a
lot
of
the
pieces
that
we've
created,
don't
need,
don't
and
shouldn't
exist.
Secondly,
bootstrapping
the
security
for
H
NCP:
that's
what
our
goal
is:
not
replacing
the
security
just
going
backwards
and
what
you
said:
Cisco
your
company
ships
phones
with
a
system
that
works
almost
identical
to
this,
the
that
and
it's
based
on
this.
You
know
a
lot
of
this
concepts
based
on
that,
so
at
the
phone
level.
L
Now
these
are
not
you
know,
$20,
you
know
sip
phones,
these
are
$150,
sip
phones
or
at
least
that's
the
retail
price,
probably
much
less
when
you
buy
a
thousand.
So
those
are
already
doing
that
and
I
think
that
the
reason
for
doing
that
whole
process
is
to
reduce
the
support
load
of
deploying
that
many
devices,
but
you're,
absolutely
right.
You
know.
So
if
you're
gonna
call
home,
you
need
Internet
up,
you
need
to
be
connected
on
the
network
and
that's
the
whole
problem.
L
K
Is
just
to
clarify
before
let
the
other
people
speak,
the
draft
I
was
talking
about
his
was
taking
care
of
the
bootstrapping
as
well.
I
would
suggest
that
you
explain.
Maybe
the
further
presentation
or
draft
I
don't
know
how
this
could
work
with
something
as
simple
as
a
password
or,
as
you
mentioned,
a
button
to
press,
because
for
now
it
doesn't
look
to
me
that
it's
sufficiently
simple
to
be
used
for
any
kind
of
user.
Okay,.
M
L
L
So
let's
say
I'm
an
ISP
and
I
buy
a
thousand
wrt
equivalents
from
the
market
right,
so
I
hope
tell
me
if
I'm
wrong,
that
they're
gonna
put
them
through
a
thing
and
put
known
firmware
on
them
right.
Are
they
or
not,
I
mean
because
the
end-user
won't
know
the
password
otherwise
right?
How
does
that
get
configured
thing.
L
But
the
point
is
that
if
you
don't
at
least
go
through
a
factory
reset,
so
that
the
path
so
that
they
can
actually
ship
it
and
give
you
the
user.
Well,
if
you've
done
that,
then
you
could
load
your
own
Krone
own
anchor
right.
Okay
and
potentially
this
process
would
allow
them
to
automate
this,
so
they
would
actually
be
able
to
more
easily
buy
the
devices.
L
Then
they
ship
them
out
to
the
customer
who
power
cycles
them,
maybe
does
a
sort
of
factory
reset,
but
him
now
it's
booting
their
image
right
and
enrolled
and
I
mean
we
have,
of
course,
the
question
which
I
don't
think
we
resolved
in
HomeNet,
which
is
you
know,
do
the
CPE
devices
to
belong
to
the
homeowner
or
the
ISP,
or
do
they
have
two
minds
right
and
that's
a
it
doesn't
matter
to
me
to
my
protocol
how
it
works,
but
it
does
matter
whether
which
credential
the
device
winds
up
with
right.
Thanks.
N
Stuart
Stuart
Shara
from
Apple
I
find
this
whole
discussion
a
little
bit
puzzling.
Okay.
It
almost
feels
like
it's
a
parallel
universe,
where
the
facts
are
different:
okay,
I,
when
I
looked
at
atom
where
a
couple
of
years
ago
there
was
this
weird
reaction,
which
is
we're
going
to
pretend
that
DNS
service
discovery
doesn't
exist
and
imagine
how
we
would
solve
this
if
that
didn't
exist.
Well,
you.
N
Okay,
going
to
the
alcohol
on
that,
the
the
issue
we're
talking
right
now
about
how
you
provision
new
devices
are
maybe
was
an
unsolved
problem
five
years
ago,
but
now
nest
is
making
thermostats
and
smoke
detectors
and
belkin's.
Making
the
Wemo
and
apple
has
the
whole
home
kit
line
of
third-party
things,
and
it
kind
of
seems
like
what
what
we're
acting
as
if
this
is
a
big
mysterious
thing.
No
one
knows
how
to
do,
but
you
walk
down
the
high
street.
N
You
can
come
back
with
an
armful
of
products
right
already
doing
this
and
I
don't
stand
here
for
10
minutes
sort
of
explaining
how
they
all
work.
But
there
are
some
that
used
the
Bluetooth
radio
as
a
way
of
doing
the
provisioning
there's
some
that
work
the
way
Ted
described
where
the
device
acts
as
its
own
access
point.
N
There
is
work
that,
where
we're
looking
at
at
Apple
about
maybe
being
able
to
support
joining
two
access
points
on
the
radio,
that's
not
a
product
announcement,
just
something
we've
been
looking
at
because
that's
just
a
matter
of
time.
Slicing
the
Wi-Fi
radio
to
do
double
duty,
they're,
also
peer-to-peer
wireless
technologies,
where
you
can
exchange
frames
with
a
pair
that
is
kind
of
an
I
Triple
E
lay
absolutely.
A
N
To
solve
that
usability,
it's
not
a
fundamental
protocol
issue.
How
do
the
secure
of
bootstrapping
with
the
appropriate
kind
of
encrypted
key
exchange?
The
thread
group
is
doing
a
ton
of
interesting
work
about
how
you
enroll
new
devices
onto
the
network,
so
it
seems
like
we
should
at
least
not
be
ignoring
all
of
that
existing
stuff
and
pretending
it
doesn't
exist
so
actually
we're
doing
the
complete.
L
Opposite,
okay,
which
is,
we
would
very
much
like
to
reference
all
the
thread
group
work,
but
there
are
multiple
people
in
the
ITF
whose
lawyers
won't
let
them
see
the
documents,
because
that
is
not
an
open
standard.
I,
don't
know
about
the
IPR
in
the
apple
homekit,
I
haven't
looked
I
do
remember.
Reading
overviews,
the
Wemo
is
a
you
know,
obvious
way
to
do
it
and
you
mentioned
a
whole
bunch,
other
things.
So
what
you're
really
doing
is
saying
this
is
a
really
good
idea.
Everyone's
already
done
it.
L
Well,
let's
do
it
at
the
IETF
in
a
standardized
way
such
that
we
don't
have
19
ways
of
doing
it.
As
for
the
the
I
Triple
E,
you
know
the
frame
things
all
that
stuff
yeah.
So
I
mentioned.
We
have
this
document.
That
is
an
individual
submission
at
this
point:
how
to
do
how
to
find
the
right
network
to
enroll
for
Wi-Fi
and,
as
I
said,
there
are
about
nine.
L
N
L
The
point
of
this
is:
do
we
want
to
have
a
way
that
allows
you
to
manage
all
of
your
devices
regardless
of
their
origin?
In
other
words,
that's
what
we
usually
do
with
the
IETF
right
Cisco
could
implement
their
own
EGP
and
juniper
could
have
one
and
we
could
have
two
internets
and
what
we
don't
like
that
right.
We
like
one.
So
that's
why
we're
here
so
I
would
love
to
have
all
that
kind
of
technology
come
into
it.
L
But
what
I'm
seeing
is
that
everyone
prefers
to
have
her
own
vertical
and
their
own
thing
and
I
would
love
to
include
whatever
I
can
I
would
there's
a
one
of
the
proxy
mechanisms.
Stateless,
proxy
medicines
I
would
love
to
use
threads
mechanism.
Okay,
it's
not
easy
to
reference
like
it's
not
even
easy
to
get
the
document,
let
alone
to
tell
people.
How
do
you
do
it
so.
N
Just
on
that
last
topic,
I,
don't
know
why
people
have
been
advised
by
their
lawyers
to
remain
ignorant
the
the
thread
specifications
and
it's
big
at
700
pages
yep
there
should
be
clear.
Apple
is
not
currently
member
the
thread
group,
so
we
have
no
special
status
or
influence
there,
but
I
went
to
the
web
page
and
I
damaged
the
specification
and
the
only
restriction
on
that.
It's
a
fairly
short
effectually
end
user,
License
Agreement.
It
says
by
I
I
understand
the
downloading
the
specification.
N
L
The
IPR
that
clicked
through
that
you
went
through
was
a
bit
more
onerous.
Apparently
I
did
what
you
did
right,
but
it
very
also
very
very
strongly
cautioned
me
against
giving
my
copy
the
document
to
you
or
letting
you
see
it.
It
was
water
marked
with
my
name
right
so
so
it
sounds
like
you've
been
through
the
same
process.
N
L
A
skin
I
would
really
prefer
to
use
particular
pieces
of
their
technology,
for
particular
things
and,
and
it
would
be
lovely
to
you
know.
As
you
said,
we
have
to
become
a
member
of
the
thread
group,
but
we
want
to
call
it
that,
but
there
are
some
bits
and
pieces
that
would
be
really
nice
to
reuse,
because
you
know
there's
just
facilities
that
may
be
elsewhere,
so
devices
that
could
operate
in
thread
space
or
not
Bava.
O
Switch
to
HD
consulting,
probably
answer
some
of
the
things
that
Stuart
was
implying
here.
I
was
at
the
beginning.
This
process
in
I
took
a
look
2.1
back
in
2003,
maybe
2004
8o
2.1
AR
was
published
in
2006.
That
gave
us
the
the
route
and
the
basic
structure
here,
but
then
there
was
well
ok
now
that
we
got
the
this
concept
of
device
certificates,
what
do
we
do
with
them
and
that
turned
it
over
to
IETF
at
that
time?
O
O
One
of
the
things
we're
also
doing
here
in
the
IETF
is
that
we're
trying
to
push
this
down
even
into
smaller
devices
of
the
working
Cosi
that
we're
doing
and
trying
to
get
a
lighter
sort
of
certificate
of
of
security
claim
things
that
can
put
it
even
to
smaller
type
devices.
But
how
do
you
consistently
non
industry-specific
because
in
2015
I
work
with
one
vendor
and
to
create
their
proprietary
architecture
and
they're
a
bit
processor
with
32k
of
memory?
So
it's?
O
L
Approach
so
so
known,
it
is
the
most
difficult
Enclave
because
you
know
in
in
the
the
the
enterprise
ISP
anima
space.
We
know,
there's
a
there's,
a
there's,
a
management
and
they
have
a
very
strong
relationship
with
their
suppliers
to
be
able
to
make
to
do
things
in
the
six
dish
space.
It's
yes,
it's
IOT,
but
it's
industrial
IOT.
Where
again,
there
is
a
very,
very
strong
relationship
to
an
a
sales
channel
force
to
make
things
happen,
and
so
we
knew
we
could
solve
server
problems
that
way
so
home
net.
L
Is
this
essentially
Wild
West
right,
you
go
to
any
manufacturer,
including
them
want
the
curb
and
hope
something
to
work.
So
it's
the
most
challenging
space
and
it's
frankly
the
way
we
stayed
away
from
it.
We
said:
look
we
can't
solve
your
problems,
it's
just
gonna
be
boiling
the
ocean,
but
at
this
point
we
have
a
couple
ships
that
you
might
want
to
consider:
okay
in
your
ocean
track
and
they
may
or
may
not
help
you
alright
I.
O
Think
it
really
can
may
I
have
a
strongly
biased
view
in
terms
of
my
home
network,
since
I
sat
down
my
first
breadboard
back
in
1961,
so
I
may
not
be
your
typical
Hulk
user.
My
first
transistors
I
got
back
then,
but
I
really
think
again.
I'm
biased,
I've
been
involved
in
this
process,
for
you
know
a
long
time
and
that
this
is
a
can
be
of
immense
value,
and
once
we
start
doing
it,
vendors
will
say.
Oh
all,
these
claims
about
how
I
do
security
and
and
and
how
I
get
started
with
it.
A
J
Issue
and
when
reasonable
people
disagree
and
everybody
is
acting
in
good
faith,
it
usually
means
that
they
are
making
different
assumptions
true
and
that
those
assumptions
should
be
written
out
and
I.
Think
the
assumption
you're
making
here
is
that
the
vendor
and
the
user
have
aligned
interests
or
in
other
words,
that
the
vendor
has
the
users
best
interests
in
mind,
which
is
usually
the
case,
especially
among
the
vendors
present
in
this
room.
J
J
I'd
like
to
make
is
that
we
are
living
in
a
world
in
which
free
software
open
source
software
is
becoming
increasingly
important
and
I.
Think
all
of
us
are
struggling
to
make
sure
that
ITF
and
open
standards
remain
relevant
in
a
world
in
which
anyone
can,
just
you
know,
throw
their
protocol
and
github
and
be
done
with
it,
and
secure
booth
has
a
very,
very
bad
reputation.
There
are
so.
L
J
J
L
Agree,
they
are
very
related,
but
I
think
they're,
very
different
pieces,
different
problems
because
of
because
of
what
you
just
said:
the
interests
of
the
vendor
and
the
firmware
maker
and
the
influence
of
open
source
and
things
like
this
I
think
there's
a
very
different
situations
for
the
bootstrap
or
is
the
the
boot.
So
so.
J
If
you
allow
me
to
conclude
the
fact
that
here
what
you're
doing
is
proposing
that
the
vendor
has
a
say
in
how
you
use
the
device
even
years
afterwards
is
something
that
is
a
very
good
way
to
make
sure
that,
in
the
free
software,
community,
ITF
appears
like
the
tool
of
the
vendors
trying
to
regain
control
of
an
internet,
that
the
vendors
no
longer
control.
I
totally.
J
L
Totally
get
you
and
I
think
you're
completely
correct
about
that
that
concern
and
that
potential
space,
and
to
be
honest
it
it
keeps
me
awake
at
night.
I
think
you
know,
am
I
acting
for
the
devil
here
and
and
I
think
how
can
I
moderate
the?
How
can
I
make
options
such
that
users
still
have
some
control
and
retain
ownership
of
their
devices,
and
yet
it's
easy
right.
L
O
Just
real
quickly,
we
discussed
this
and,
and
we
thought
and
discusses
back
in
2004.
This
is,
if
we
had
this
trust
of
anchor
by
the
manufacturer,
because
in
boost
you
have
it
sometimes
you
don't
want
that.
So
the
implicit
part
of
the
L
divide
II,
is
that
if
you
have
a
different
mechanism
in
which
to
enroll
that
does
not
use
the
idea
right,
II
and
it's
kind
of
in
here.
You
can
then
use
the
L
divide,
II
totally
independent
of
the
idea
of
ID,
but
that
this
is
something
that
they
would
have
to
do.
O
C
P
C
Better,
ok,
thanks
for
thanks
for
the
fit
perfect.
Ok,
so
we
had
this
perimeter
security
draft
milestone.
As
of
now,
we
had
a
chat
and
we
talked
to
the
air,
ID
and
I
guess
the
feeling
is,
if
we
don't
have
somebody
who's
gonna,
do
it
and
it's
not
gonna
happen
so
again,
if
you're,
if
you're,
in
a
position
to
be
able
to
do
this,
then
there'd
be
good
to
know.
Hi.
D
C
E
J
So
in
Babel
we
have
two
approaches
to
security:
one
is
simple:
symmetric
King
using
H
Mac
and
the
other
one
is
David's
idea
which
uses
DTLS,
so
they
have
different
trade-offs.
H
Mac
is
something
simple,
something
that
you
have
a
chance
to
review
before
you
retire,
while
in
the
case
of
DTLS,
you
make
crypto
somebody
else's
problem
by
pushing
get
into
DTLS
and
you
get
all
the
features
of
DTLS.
Both
are
happening
right
now.
J
There
is
a
BIST
for
the
H
Mac
that
is
being
worked
on
and
we
are
planning
to
do
an
implementation
this
summer
and
we
have
two
non-interoperable
proof-of-concept
implementations
of
the
DTLS
stuff,
and
there
are
just
two
bits
of
two
bits,
literally
that
are
in
this
agreement
between
the
two
implementations,
one
being
by
David
one
by
altona.
So
this
stuff
is
without
any
go
and
I.
J
Don't
know
there
is
consensus,
but
I
feel
that
there
is,
shall
we
say,
rough
agreement
on
the
fact
that
H
max
should
be
the
strong
Lee
recommended
and
DTLS
the
optional
protocol.
So
both
of
those
things
are
advancing.
Both
of
these
things
are
being
worked
on
and
I'm,
confident
that
we
will
have
implementations
and
drafts
by
the
end
of
the
summer
for
the
right
definition
of
summer.
You
know
sometimes
summer
lasts
until
March
next
year,
so.
C
J
C
J
A
P
Don't
the
Davidson
Ossie
Apple
I,
don't
think
what
is
mandatory
to
implement
in
the
babel
working
group
is
necessarily
important
here.
I
think
the
profile
for
home
net
should
define
what
we're
using
for
home
net,
because
one
of
the
we've
been
building
flexible
things
in
Babel.
So
if
your
use
case
has
single
symmetric
key
for
everyone,
we
can
do
that.
If
you're
used
to
case
as
a
certificate,
/
router,
we
can
do
that.
I
think
own
net
needs
to
define
the
kind
of
the
route
of
trust,
and
that
was
great
previous
conversation.
P
P
K
Sister
I
mean
I
think,
based
on
what
julius
just
said,
we
are
in
a
great
position
to
work
with
babel,
I'm
very
happy
with
the
hvac
option,
because
we
have
that
mean
that
the
working
group
needs
to
focus
on
securing
HNC
anyway
or
improve
the
security
that
is
already
defined
in
the
existing
document.
From
that
standpoint,
it's
a
piece
of
cake
to
just
create
a
key
that
is
shared
between
the
nodes
using
engine
CP
propagate
that
he
using
agency
P
and
provision
Babel
with
that
key.
K
E
E
K
E
The
problem
with
that
is
that
we
don't
actually
so
what
you
actually
said
before
was,
if
there's
a
if
there
was
a
know
that
needs
to
knit
to
leave
the
network
or
if
there
is
a
node,
that's
been
compromised,
then
you
need
to
generate
a
new
key.
But
how
do
you
know
that
a
node
has
been
compromised?
If
you
only
have
one
key
so.
P
C
B
C
E
E
E
There
was
a
little
bit
of
a
clash
in
terms
of
goals
there,
but
but
there
was
actual
work
done
to
solve
the
pairwise
symmetric
keying
problem
that
that
got
I,
think
I
think
the
the
the
outcome
of
that
was
that
we
concluded
that
it
had
been
unnecessary,
but
it
sounds
like
because
they've
already
had
that,
but
now
it
sounds
like
people
doesn't
already
have
that.
So
maybe
we
should
revive
that
document.
J
D
C
C
P
P
E
Right
so
Chris's
draft
actually
used
symmetric-key
for
for
broadcast
and
a
symmetric
key
for
everything
else
and
didn't
really
talk
about
the
HNC
p
part
of
the
equation.
So
the
HNC
p
stuff
is
still
work.
That's
I've
been
talking
about
doing,
but
then
you
know
life
happened
and
it
hasn't
actually
occurred.
But
that's.
E
Hair-Wise
sorry
asymmetric,
he
is
working
in
hn
CP
and
then
have
a
way
to
develop
pairwise
symmetric
keys
using
hn
CP,
which
we
don't,
I
think
currently
have
unless
them
vastly
mistaken.
Yours
shake
your
head,
or
am
I
am
I
we
don't?
We
don't?
Have
it
right
now
right
a
symmetric
keys
using
used
to
generate
pairwise
symmetric
keys.
C
Design
at
the
mic
line-
it's
probably
not
gonna-
be
that
productive,
so
I
mean
I,
guess,
I,
guess
the
chairs
will
try
and
take
action
to
get
those
three
people
in
Huddle's
and
see
if
there
is
an
agreement
that
to
bring
to
the
mailing
list
and
and
I
think
having
it
based
on
code
is
tedious
suggest
would
be
really
good,
so
might
need
to
be
very
immediate
but
I.
Think
making
some
decisions
in
this
place
seems
like
a
sensible
thing
to
do.
