►
From YouTube: IETF101-HRPC-20180322-1550
Description
HRPC meeting session at IETF101
2018/03/22 1550
https://datatracker.ietf.org/meeting/101/proceedings/
A
Yes,
I
can
be
heard,
so
we
should
start
because
we
have
a
very
full
agenda.
I
was
fortunate.
We
have
Mallory
doing
jabber
scribe
and
we
have
Korean
doing
note
taking
the
notepad
is
there
for
other
people
to
add
and
of
course,
others
can
add
to
the
jabber,
but
thank
you
very
much
so
moving
forward.
This
is
the
IRT
F
research
group
on
human
right
protocol
considerations,
HR
PC
and
yeah
the
administrative
we
have
a
mailing
list,
there's
github,
there's
meet
echo,
there's
minutes,
there's
a
website
the
agenda
and
the
agenda
are
bash.
A
A
Hearing
nothing
will
go
on
with
it
so
now
to
then
we'll
go
to
the
assorted
there's.
The
note
well
read
the
note.
Well,
I
was
actually
in
a
meeting
today
where
somebody
read
it
out
loud
I
will
not.
Is
this
a
new
one
or
the
old
one?
No,
it's
the
new
one!
Sorry,
sorry
that
it's
a
new
one,
so
you
really
ought
to
read
it.
If
you
haven't
read
it
since
you
read
the
old
one:
okay
document
review
document
quality
relies
on
reviews.
A
B
A
Do
that's
good,
okay,
so
please,
but
also
we
need
people
to
review
our
documents
more.
The
status
of
the
group,
basically,
where
we
are
now
is
March
2018
I
will
not
read
through
all
that.
What
has
changed
is
we
had
no
research
group
documents
accepted
as
of
ITF
100
we
had
finished
80
to
80.
Did
a
call
on
the
group
on
the
group
list
to
see
which
ones
should
be
be
made.
A
Research
group
documents
two
of
them
there
was
general
consensus
that
they
should
be
there's
a
couple,
others
where
there's
still
open
discussion
and
I
think
they're
on
their
way
there,
but
but
the
group
itself
didn't
quite
have
comfortable.
We
can
check,
after
the
discussed
here,
to
see
whether
people
feel
they're
ready
to
become
research
group
documents,
but
if
not
we'll
keep
working
to
that,
there's
no
great
win
in
having
it
be
a
research
group
document
than
your
private
document,
but
perhaps
it
looks
better
yeah.
A
A
If
we
can
reach
that
status
with
the
work
we're
doing
so
that
that
work,
our
work
becomes
as
solid
as
that
work
is
we'll,
have
done
really
quite
well
to
increase
the
awareness
in
both
the
human
rights
community
and
the
technical
community
on
the
importance
of
the
technical
workings
of
the
Internet
in
its
impact
on
human
beings.
Oh
no,
first
we
had
the
the
hackathon
correct
in
the
in
any
agenda.
We
can
go
first
with
this,
but
I
thought
we
had
the
hackathon
first.
A
C
A
C
So
good
morning
to
everyone,
Thank,
You
mill,
salary
for
the
kind
invitation,
I'm,
Luca
belli,
I'm
senior
researcher
at
the
Center
for
technology
and
society
of
fgv
degrees
from
the
surgical
Vargas
is
one
of
the
main
academic
institution
in
Brazil.
It's
currently
ranked
as
the
seventh
most
influential
think-tank
worldwide,
and
it
has
been
ranked
as
the
most
influential
think-tank
in
Latin
America
over
the
past
eight
years.
C
The
work
I
would
like
to
speak
about
with
you
today
is
this
work
on
Network.
Seventh
rumination
is
part
of
my
work
at
fgv,
I
am
I,
had
the
Internet
Governance
project,
which
deals
primarily
with
connectivity
in
data
governance,
and
this
work
actually
has
a
little
bit
of
both.
So,
first
of
all,
all
the
information
I'm
going
to
share
with
you
today
are
taken
from
an
article
I
published
in
this
book.
C
The
name
of
the
article
is
network
determinations
and
the
positive
externalities
of
community
networks,
and
this
book
that
has
been
officially
released
at
the
IGF
in
December
is
the
official
outcome
of
the
dynamic
coalition
community
connectivity
is
a
group,
a
multi-stakeholder
open
group
of
the
IGF
that
analyzes
community
networks
and
the
community
network
mode,
and
you
can
freely
share
it
and
download
it
and
do
whatever
you
want
with
the
book,
so
network
server
termination.
What
am
I
speaking
about?
C
It's
a
right
to
develop
your
own
network
infrastructure
and
it
is
what
I
think
could
be
conceived
as
an
instrumental
condition
for
people
to
enjoy
and
truly
exercise
their
fundamental
rights.
This
is
the
definition
quite
long
that
I
provide
is
the
right
to
free,
assemblé,
associate
sorry
and
to
define,
in
a
democratic
fashion,
the
design,
the
development,
the
management
of
the
network
infrastructure
as
a
common
good,
and
this
is
to
freely
seek
impart
and
receive
information
and
innovation.
C
Those
who
are
familiar
with
human
rights
law
I
think
have
already
spotted
some
elements
that
we
will
analyze
in
second
part
of
the
presentation
and,
first,
why
this
is
relevant
here.
Well,
I.
Think
it
resonates
with
the
work
the
HR
PC
has
been
doing,
particularly
with
RFC
82
80,
and
the
fact
that
you
explicitly
say
that
the
design
and
development
of
the
network
infrastructure
has
a
growing
impact
on
society
and
the
Internet
should
I
mean
can
be
considered
as
an
enabling
environment
for
Human
Rights.
C
C
So,
let's
start
with
the
facts
with
the
observable
phenomena
that
allow
me
to
state
quite
confidently
that
Network
self-determination
actually
already
exists
de
facto.
So
as
of
Monday,
the
world
population
was
about
seven
point:
six
billion
individuals
and
the
internet
population
was
3.87,
so
more
or
less
fifty
percent.
According
to
this
more.
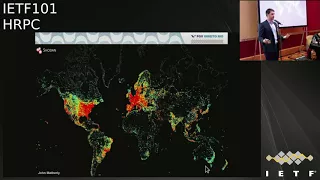
C
Visualization
is
the
global
average
is
53
percent,
and
then
you
have
these
average
of
the
various
region,
which
is
well
it's
nice
to
see
as
a
visualization.
But
it's
not
really
useful,
because
the
problem
with
this
kind
of
visualization
is
that
you
always
find
only
the
average.
This
kind
of
visualization,
on
the
other
hand,
is
much
more
in
and
interesting
because
it
allows
us
to
understand.
Where
are
those
3.6
billion
individuals
connected
to
the
Internet?
C
C
This
is
particularly
evident
if
we
narrow
down
to
Brazil
this
Brazil.
You
see
that
in
the
cost
where
the
major
cities
are,
you
can
spot
all
the
red
and
yellow
which
are
the
connected
people
and
all
the
rest.
The
rural
areas
are
much
less
connected,
but
this
is
not
only
a
problem
of
developing
countries
or
non
developed
countries.
Of
course
it
is
much
more
relevant
in
developing
or
non
developed
country,
but
in
highly
developed
countries
such
as
the
you
remembers,
the
problem
is
not
that
different.
C
Well,
of
course,
is
less
intense,
but
you
still
have
rural
areas
that
have
half
of
the
average
of
the
total
European
Union.
And
if
you
see
this
graph
with
all
the
Member
States
in
rural
areas,
there
are
countries
well,
more
than
half
are
have
less
than
50%
of
rural
areas
are
connected,
and
some
countries
like
Italy
with
60
65
million
inhabitants,
rural
areas
only
have
15
percent
of
the
territory
that
is
connected,
so
it's
actually
quite
quite
telling
of
how
the
lack
of
connectivity
may
also
impact
developed
country
in
so.
C
The
conclusion
that
I
start
to
draw
from
this
is
that
mainstream
networks
are
not
so
mainstream
and
when
I
speak
about
mainstream
networks,
I
refer
to
what
the
request
for
comment.
79
62
calls
mainstream
network,
so
the
authority
network
deployment
RFC
provides
the
economy
of
an
in
identified
mainstream
networks,
as
usually
I
mean
the
traditional
networks
large
network.
They
span
large
areas
controlled
by
traditional
operators
in
a
top-down
fashion.
C
They
require
substantial
investment
to
be
deployed,
and
there
is
no
user
participation
in
the
government's
deployment,
the
operation
of
the,
and
so
here
we
can
start
to
think.
Why
are
people
not
connected
to
this
mainstream
network?
There
are
several
explanations,
several
factors
and
if
they
depend
in
different
countries
in
different
countries,
you
can
have
a
completely
different
importance
of
these
factors,
but
they
are
primarily
this
for.
First
of
all,
connectivity
is
not
available.
C
So
the
lack
of
competition
may
keep
the
price
is
very
high
and
there
are
some
studies,
for
instance,
by
Carlos
ray
Moreno
in
South
Africa
that
explain
that
people
have
to
sacrifice
food
to
buy
connectivity,
and
then
there
is
the
lack
of
interest
which,
if
you
think
about
it,
we
see
the
entry
interest
of
the
internet.
But
if
you're
in
a
rural
community,
you
may
need
local
government
services,
local
e-commerce
platform
to
trade,
local
goods
and
local
services
news
in
local
languages.
C
If
you
don't
have
them,
you
don't
really
see
an
interest
in
connecting
to
internet
and
again
the
low
level
of
literacy
and
numeracy
is
in
specially
in
developed
continuing
countries,
one
of
the
main
causes,
because
if
you
don't
really
understand
how
the
internet
works-
and
you
really
not
have
basic
skills,
it's
quite
hard
to
understand
what
are
the
benefits
that
you
may
have
by
connecting
to
internet.
So
what
Michael
might
make
us
read
is
what,
if
you
could
build
the
internet
yourself,
what
if
people
could
mitigate
at
least
some
of
the
these?
C
These
elements
that
I
was
mentioning
by
building
their
own
internet?
Well,
they
actually
people
are
already
doing
so
since
almost
twenty
years
with
by
building
community
networks
through
crowd,
crowd-sourced
networks,
they
are
built
by
a
group
of
individuals
and
managed
by
them
in
a
bottom-up
fashion,
as
a
common
good.
So
they
are
managed
by
the
local
community
as
Commons,
and
this
gives
rise
to
a
distributed
architecture.
C
Actually,
bringing
us
brings
us
back
to
the
original
philosophy
of
the
Internet,
a
network
of
networks
where
people
can
add
new
networks
and
those
network
will
interoperate
through
open
standards,
started
out
here.
The
ITF,
and
actually
this
is
quintessentially
decentralized,
and
this
architecture
is
usually
put
in
place
using
wireless
technology,
low-cost
Wi-Fi
equipment
and
the
use
of
unlicensed
spectrum
to
Randers
equipment,
or
maybe
TV
white
space
it
with
dynamic
spectrum
and
allocation,
and
but
it
can
also
be
built
on
fibre,
and
there
there
are
some
pretty
impressive
results.
C
Besides
this
benefit
of
the
access
to
information
having
connectivity,
obviously
that
we
all
know
there
are
also
collateral
effects.
External
effect,
it's
a
virtual
circle
of
knowledge
and
innovation
that
is
triggered
by
this,
because
when
the
communities
involved,
there
are
new
services
that
are
developed
by
the
locals
for
the
locals.
So
the
time
the
families,
government,
services
or
local
language
content
that
I
was
speaking
about
before
they
are
developed
by
the
come
by
the
locals
that
are
into
the
community
networks
for
the
locals,
so
it
in
almost
all
community
networks.
C
You
see
this
phenomenon,
the
element
of
maps,
voice-over-ip
local
fora,
health
applications
in
the
Nepal
network
wireless
project.
They
have
developed
a
application
for
pregnant
women
to
receive
information
about
pregnancy.
It
also
has
stimulates
use
of
smartphone
by
people
living
in
Malaya
zones.
So
it's
quite
impressive
result.
So
all
the
positive
externalities
of
the
do-it-yourself
connectivity,
of
course,
freedom
of
expression.
We
know
to
impart,
receive,
seek
information
ideas,
but
also
the
education
that
comes
with
it
and
capacity-building,
because
people
that
are
actually
in
developing
networks
usually
also
provide
training
for
for
the
locals
and
everybody.
C
They
may
be
promoted
by
the
local
command
connectivity
used
as
a
comment,
so
I
think
so
far.
I've
provided
a
little
bit
of
empirical
basis
on
which
we
can
start
to
think
that
Network
self-determination
already
exists.
De-Facto
now,
let's
see
very
quickly
how
it
can
be
constructed
that
you
were
using
international
human
rights
law.
If
we
come
back
to
the
definition
I
provide
at
the
very
beginning,
we
can
decompose
it
in
three
elements
and
the
right
to
freely
associate
the
definition
of
the
network
governance
as
a
Commons
and
the
freedom
to
seek
important,
receive
information.
C
Innovation,
the
first
and
the
third
are
quite
self-explanatory,
meaning
that
the
first
is
simply
the
right
to
freely
associate
it's
already
protected
by
very
explicitly
by
Human
Rights
binding
instrument.
The
third
is
a
simple
rephrasing
of
freedom
of
expression
is
traditionally,
it
is
defined
as
the
right
to
freely
seek
important,
receive
information
and
ideas
here,
I'm
just
substituting
ideas
with
innovation,
because
an
idea
in
the
digital
ecosystem
can
easily
translate
into
a
new
application
of
new
technology,
and
people
should
be
our
actually
are,
according
to
fundamental
human
rights
law,
free
to
fear,
receive
and
access.
C
Those
ideas
in
the
second
part
is
a
little
bit
more
tricky.
Why?
Because
there
is
no
agreed
definition
of
what
is
democracy
in
human
rights
law,
so
the
the
the
the
rights
to
define
the
in
a
democratic
fashion,
the
network
governance.
Well,
one
has
to
understand
what
is
what
does
democratic
means,
and
here
we
usually
international
UN
right.
So
you
will
refer
to
the
right
to
self-determination
and
the
internal
dimension
of
domination.
There
are
two
dimensions:
one
is
external
dimension
of
self-determination.
The
right
to
have
any
depend
territorially
independent
states,
sovereign
states.
C
It
is
not
this.
What
interests
interests
us
and
I?
Don't
want
to
start
a
discussion
about
territorial
independence
in
the
UK,
which
is
not
the
most
advisable
thing
to
do
to
mean
recently,
I
want
to
focus
on
something
else,
which
is
what
really
interests
as
internal
self-determination,
so
the
right
to
define
a
governance
system
according
to
the
will
of
the
people,
it's
really
technology,
they
must
characters.
C
The
government
of
the
people
and
this
right
to
self-determination
is
so
important,
which
is
the
that
is
the
first
right
not
only
of
the
Universal
Declaration
of
Human
Rights,
but
of
both
international
covenants
of
fundamental
right.
The
same
wording
the
same
phrasing
in
article
one
of
the
three
document.
All
people
must
be
free
to
determine
their
political
status.
This
is
external
dimension
and
to
pursue
their
economic,
social
and
cultural
development.
C
This
is
important.
This
becomes
very
important
if
you
consider
your
personal
data,
our
money,
your
personal
data
are
the
digital
currency
that
is
used
to
pay
services,
and
it's
not
only
money.
It's
really
the
most
important
resource
you
have
in
the
world
and
if
you
think
in
internet
terms,
the
main
business.
E
C
You
have
so
far
is
zero
price
model
right.
You
don't
pay
with
money,
you
pay
with
data.
Well,
the
same
logic.
The
zero
price
logic
has
been
transported
over
the
past
four
or
five
years
to
zero
rating
offerings,
which
are
another
strategy
that
has
been
advocated
for
by
some
several
operators
to
provide
subsidized
services
applications
to
unconnected
individuals.
So
this
is
basically
price
discrimination.
You
don't
do
not
count
the
consumption
of
specific
services
against
the
monthly
data
allowance
of
the
user.
But
what
are
the
purpose?
Is
why
or
is
this
way?
C
Are
these
strategies
being
implemented?
It's
not
only
because
of
second
operators
have
magically
become
philanthropist.
Is
it
because
there
is
a
commercial
logic
behind?
First
of
all,
you
attract
new
users.
If
you
give
them
a
gift,
I
will
give
you
a
free
service,
but
if
you
think
about
it,
that
gift
is
only
useful
if
you
have
no
access
or
a
very
reduced
data
cap
every
month.
C
If
you
have
the
possibility
to
create
your
own
network
and
your
own
services,
you
don't
need
a
freeze
for
one
application
as
a
gift,
because
you're
already
having
all
the
applications
that
you
can
do,
which
you
can
connect
through
your
network,
plus
the
one
that
you
really
need.
You
are
developing
them
through
your
community
network,
the
orientation
of
user
choice
and
user
attention
towards
specific
applications
is
also
another.
Another
reason
of
these
strategies
and
user
attention
in
the
eyeball
economy
equals
to
data
data
are
the
most
valuable
resource.
C
So
I
will
give
you
the
example
of
Brazil,
where,
despite
being
this
practice,
illegal
operators
are
providing
integrated
services
so
that
they
can
bypass
the
prohibition
to
harvest
data
on
their
users
through
applications
that
are
providing
that
harvest
data
of
the
users
and
then
all
last
but
not
least,
this
selling
the
preferential
access
to
your
own
customers
to
the
application
providers
that
are
willing
and
able
financially
able
to
pay
for
this
preferential
access.
So
this.
C
Obviously,
this
kind
of
strategy
presents
some
advantage
for
the
consumer,
because
you
have
a
free
app,
but
the
problem
is
that
it
is.
It
is
an
advantage
for
that
app
consumer,
not
from
the
internet
user,
and
it
transforms
actually
all
the
potential
Internet
users
and
presume
us
into
app
consumers,
because
that
is
what
is
free
and
it
is
that
is
particularly
evident
in
developing
country,
where
people
do
not
have
the
money
to
buy
access
and
have
free
access
subsidized
to
specific
services,
and
they
turn
out
to
be
only
users
of
those
applications.
C
Again,
Brazil
is
very
telling.
Only
three
weeks
ago,
the
Brazilian
Institute
for
geography
and
statistics,
which
is
a
public
entity.
Releasing
statistics
on
Brazilians
every
three
months
started
for
the
first
time
to
release
data
on
what
are
the
main
reasons
for
which
Brazilians
access
danger
in
94
percent
94
percent
of
Brazilians
access
the
internet
to
use
messaging
applications.
Now
it
might
be
that
Brazilians
really
love
messaging
applications,
or
it
might
also
be
that
whatsapp
is
the
only
application.
C
If
you
want
to
know
more
about
what
services
are
zero
rate
in
the
world,
with
the
IGF
dynamic
coalition
on
any
Friday,
we
have
built
this
nice
tool
that
allows
you
to
see
in
87
countries.
So
far,
what
are
the
services
that
are
generated
and
what
are
the
does
your
rating
policies,
in
naturally
poetry
and
no
surprise?
The
Facebook
application,
Facebook
group
applications,
meaning
what's
a
primarily
Facebook
and
sometimes
instagrams,
are
those
that
are
zero
netted
in
all
countries,
basically,
and
with
some
rare
exceptions
and
well.
C
This
leads
us
to
what
I,
rather
provocatively,
define
miniaturization
of
the
internet,
which
is
transformation
of
the
internet
from
an
open,
a
general-purpose
network
into
a
centralized
and
predefined
purpose
network,
and
but
that
is
not
the
only
option.
This
is
the
probably
the
most
advertised
option,
but
I
as
I
was
explaining
the
first
part
people
can
develop
they
on
their
own
network,
so
why
shouldn't
they
be
allowed
to
do
so.
Thank
you
very
much
for
your
attention
and
all
information
are
here.
F
C
G
Please
Nick
Terry
UC
Berkeley
thinks
your
talk
is
very
interesting.
I
was
curious
about
the
early
set
of
slides
about
access
in
rural
areas,
so
I
guess
I
had
sort
of
one
clarification
and
one
sort
of
open
question.
So
I
I'm
curious
when
we
were
describing
these
percentages,
whether
the
percentages
yeah.
This
show
that
chart
yeah
whether
these
percentages,
if
I,
put
the
percentage
of
people
in
rural
areas
who
have
access
or
is
it
the
percentage
of
areas?
That's.
H
G
C
G
Okay
and
and
then
the
sort
of
more
general
question
was
yeah.
You
were
pointing
out
that
we
should
be
thinking
about
self-determination
and
that
the
creation
of
our
now
like
that,
the
sort
of
DIY
creation
of
networks
might
might
speak
specifically
to
self-determination.
I'm
curious.
If
we
have
any
idea
about
how
many
people
are
not
connected
to
the
internet,
because
they
don't
want
to
be
versus
how
many
are
not
connected,
because
they
don't
have
the
capability
or
financial
success.
C
So
I
have
a
double
reply.
The
first
one
is,
it
I
mean
when
you
have
the
even
your
freedom
of
expression,
you,
a
fundamental
right.
Freedom
of
communication
is
a
elemental
right,
but
it's
not
an
obligation,
you
don't
have.
You
don't
have
to
be
connected
and
if
your
choice
is
not
to
be
connected,
it's
a
perfectly
respectable
choice.
C
Yeah,
but
if
you
are
not
connected
because
no
one
is
investing
in
your
area
or
because
the
price
is
too
high
or
simply
because
you
would
want
to
do
it,
but
you
don't
have
accessible
information
well,
this
may
solve
some
of
the
problems
is
obviously
it
is
not
a
silver
bullet.
It's
it's
not
going
to
the
committee
networks
are
not
going
to
bring
high
quality
connectivity
everywhere
in
the
world,
but
it
is
part
of
a
solution,
I
think,
and
there
is
no.
They
do
not
limit
the
right
of
everyone
of
anyone,
sorry
by
being
constructed.
C
C
I
One
thing
you
were
talking
a
little
bit
about
about
subsidy
subsidization
of
in
zero
rating
and
so
on
and
and
the
way
that
that
promotes
certain
kinds
of
applications,
but
I
wonder
to
what
extent
you
think
the
logic
of
applications
makes
for
winner-take-all
anyway,
because
an
application
layer
in
a
in
a
web
environment
there's
there's
basically
no
bit
no,
no
advantage.
Standardization
right,
everybody
can
just
use
the
application
as
it
is,
and,
and
so
what
this
means
is
because
of
the
way
network
effects
work.
I
It's
it's
better
to
be
on
the
application
that
everybody
else
is
using
than
not
now.
This
also
promotes
the
mini
tail
ization
that
you
were
talking
about.
That
is
it.
It
turns
the
Internet
into
like
a
sort
of
boring
substrate
for
on
these
monopoly
applications,
but
it
it
also
means
that
there's
literally
no
like
there's
no
subsidy.
So
there
isn't
really
a
lot
of
there's,
no
a
lot
of
public
policy
tool
that
you
could
use
to
try
to
try
to
discourage
that.
Just
because
the
advantage
accrues
to
the
users.
Well,.
C
C
And
that
has
a
benefit
I'm,
not
saying
I'm,
not
rebuttal
in
that
point,
I'm
I'm.
Taking
that
the
other
point
of
view,
which
is
the
point
of
view
actually
of
the
3.6
billion
that
are
not
connected,
and
maybe
don't
even
know
what
are
those
monopolistic
apps.
So
if
you
don't
even
know
what
they
are,
if
someone
is
giving
you
for
free,
as
you
are
saying
that
it
creates
some
sort
of
I
mean
I,
know
if
you're
not
we're,
not
saying
it
explicitly,
but
it
creates
a
sort
of
dependency.
So
you
start
using
that.
C
It's
like
I,
mean
I,
know.
I,
know,
I,
know
that
I've
been
enough
provocative
today
to
have
another
proof
occasion.
So
it's
like
I
know.
If
you
remember
in
the
90s
those
candles
about
tobacco
company
giving
to
kids
in
Africa
free
cigarettes
right,
it
creates
a
sort
of
dependency.
Again.
I
was
mentioning
behavior
design,
because
a
good
application
is
the
one
that
creates
addiction.
If
you
don't
create
an
addiction,
you
have
failed
with
an
application.
C
So,
if
you're,
giving
that
for
free
to
people
that
don't
even
have
basic
literacy
skills,
well,
a
very
good
chance
of
creating
a
good
addiction.
So
if
I
mean,
if
you're
in
an
individual
and
unconnected,
maybe
literate
individual
you're
excused-
you
don't
know
this,
but
if
you're
a
government
that
also
see
all
the
world's
most
valuable
resource
of
his
citizens
being
drained
away.
You
not
be
excused
for
this
got.
B
It
thanks
Neilsen
uber
for
the
wreck
thanks.
So
much
really
interesting
and
I'd
like
to
pick
up
exactly
where
you
just
left
with
the
final
answer.
What,
and
would
you
like
comment
on
why
you
think
that
the
right
to
network
self-determination
is
more
useful
than
a
governmental
obligation
to
network
provision?
So
why
do
you
put
the
obligation
for
the
gathering
of
the
social,
financial
and
cultural
capital
with
the
individual,
whereas,
whereas
they
would
already
be
disenfranchised.
C
I
mean
again
I'm
not
putting
any
obligation
I'm
putting
the
right
to
do.
It
doesn't
mean
that
again
it's
same
think
of
communication.
You
have
a
right,
not
an
obligation,
meaning
that
what
I'm
just
pointing
out
is
that
if
you
and
your
community
members
want
to
develop
infrastructure,
you
should
be
free
to
do
it.
So
paulien
governmental
policy
should
allow
you
to
do
so
without
restrictions,
but
no
one
will
oblige
you
to
do
so.
I
mean
again,
it's
not
a
silver
bullet.
It's
part
of
a
bigger
solution
that
has
multiple
different
strategies.
C
There
is
I'm,
not
arguing
that
there
must
be
an
obligation
on
the
individual
to
build
its
own
network
on
the
government.
An
example
again
from
Brazil
is
incredible
source
of
thoughtful
examples.
So,
over
the
past
10
years,
universal
access
funds
collected
20
billion
reais
20.
Billions
realize
that,
with
the
current,
not
very
favorable
change
exchange
rate
means
roughly
5
billions
dollars
right,
5
billions
dollars,
it's
good
money.
C
There
is
a
an
inquiry
going
on
from
the
High
Court
of
Auditors,
because
only
1%
of
the
that
money
from
the
universal
access
fund
has
been
used
for
connectivity
and
76
percent
is
unknown.
It
is
not
known
the
no
one
can
tell
you
how
it
has
been
used.
It's
at
76
percent
of
5
billion,
it's
really
a
lot
of
money
and
that
money
I'm
telling
you
I
mean
obviously,
if
the
we're
really
interested
and
efficient.
In
doing
so.
C
We
were
not
being
speaking
about
this
here,
but
if
there
are
three
point
six
billion
people
still
unconnected.
It
means
that
the
traditional
solution
we
have
been
using
mainstream
network,
be
them
there
by
traditional
operators
or
by
the
government,
have
not
been
affected,
effective,
sorry
and
from.
C
A
J
A
J
I'm
from
a
rural
place
where,
like
community
networks,
have
struggled
for
legitimacy.
But
I
do
think
that
if
we
I
think
one
of
the
issues
is
we
put
connectivity
in
its
own
context
when
we're
trying
to
when
governments
are
trying
to
incentivize
building
of
connectivity
into
infrastructure
and
they're
incentivizing
companies
to
do
and
companies
don't
feel
like,
there's
profit
to
be
made.
So
they
don't
even
take
the
incentives
that
are
offered
to
them.
J
Sometimes
I
think
it's
because
we're
not
thinking
about
the
underlying
issue
with
that,
because
if
it's
just
in
connectivity
equals
Facebook,
then
I
can
really
understand
why
people
that
have
not
already
been
connected,
maybe
don't
have
an
interest
in
connecting.
That
was
something
you
said
early
on
the
slides.
J
Then
then
perhaps
that
could
change,
because
I
think
what
what
we
risk
with
not
putting
the
onus
on
government
and
companies
is
that
yeah
you're
you're,
basically
disenfranchising
people
twice,
because
one
they're
not
connected
to
the
internet,
but
then
two
they're
also
not
able
to
get
the
services
that
they
were
previously
able
to
get
in
an
analog
situation,
because
everything
is
moving
online.
So
now
they're
doubly
sort
of
stranded
right,
I
just
wanted.
A
C
C
B
B
Although
the
IETF
mainly
archive
we've,
done
some
Bayesian
statistics
from
words,
analysis
and
some
network
analysis
for
the
use
of
Jupiter,
notebooks
and
Python,
we
found
a
lot
of
issues,
namely
with
a
lot
of
encoding,
and
the
thing
happen.
When
people
run
their
own
mill
servers,
you
can
find
the
code
in
on
github.
So
please
contribute
we
did
it
with
a
bunch
of
people,
and
we
think
it
might
be
really
interesting
to
analyze
the
participation
in
ITF
and
see
how
that
impacts,
the
kind
of
decisions
that
are
made
and
how
it
influences
the
process.
B
So
we've
been
looking
at
almost
2
million
emails
from
190,000
email
addresses
from
over
955
analyzed
mailing
lists
and
of
which
one
mail
address
and
eight
more
over
80,000
of
the
messages,
but
most
contributors
and
one
or
two
messages
so
that
might
be
spent.
If
you
look
at
the
whole
community,
it
is
actually
quite
modular
and
integrated
at
the
same
time,
which
integrates
with
only
a
few
outliers,
and
some
people
might
expect
that
early
participant
of
state
a
long
time
might
dominated
in
discussions,
and
this
is
actually
not
the
case.
B
We
got
from
the
statistics
and
also
it's
not
just
a
few
people
that
send
most
messages.
There's
quite
a
long
tail.
Also,
recent
threat
threats
on
I.t,
the
longest
threats
on
I-80
effort,
IETF,
the
org-
are
actually
long.
Threats
are
actually
quite
recent
and
are
also
about
issues
that
are
relevant
to
to
discussions
that
we're
having
here
in
HR
PC.
So
that's
actually
quite
interesting,
but
it
also
shows
that
these
topics
are
very
alive
within
within
the
community.
B
The
centrality
shows
you
how
many
people
are
applying
to
who
the
the
most
central
note,
the
the
redder,
the
note
the
more
they
reply
to
messages
and
the
people,
the
whites
and
the
whites
are.
The
note
is
the
more
the
less
they
reply
to
people.
So
if
you're
at
a
big
note
in
the
middle
and
your
whites,
that
means
that
you're
a
rock
star
that
never
talks
back
to
people
that
really
likes
you,
we've
been
looking
at
word
trends
and
everyone
can
do
the
word
trends
for
all
the
lists.
B
So
we've
been
looking,
we
see
you.
We
just
took
three
random
concepts
here,
where
you
see
that
there
is
an
increase
in
discussion
of
a
security,
a
slow
increase
in
the
discussion
on
privacy.
But
actually,
when
you
look
at
excess,
there
was
a
it
was
building
up
to
a
peak
of
the
around
2007,
but
it's
it's
falling
off
right
now.
So
if
we
want
to
understand
more
how
these
discussions
are
held
in
our
community
and
also
how
they
travel
between
mailing
lists,
have
a
look
at
the
code
and
police
contributes
a
hero.
Will
you.
K
K
Yeah,
so
during
hakonsen
we
we
made
a.
We
improve
the
click
web
crawler
to
collects,
which
website
actually
returns
HTTP
service
for
4-5-1,
because
we
already
have
the
receipt.
But
not
we
don't
see
not
not
lot
of
lots
of
the
deployment
on
about
HTTP
for
5-1,
say:
let's
call
4
by
1.
So
from
last
ITF
like
no
that's,
ok,
yeah
we
can
we
can.
K
We
can
take
a
look
visitor
yeah
so
from
the
last
couple
ITF
and
we
create
we
collected
it's
the
web
crawler
to
create
clothes
which
websites
returns
a
4
by
1,
and
this
time
we
made
block
collector
so
which
collects
the
statistical
information
that
which
website
actually
turns
4
5
and
took
from
the
clutter
and
also
we
have
the
web
browser
extension
like
Google,
Chrome
extension
so
which
that
we
made
during
the
hexam.
So
this
is
a
screenshot
of
the
4.1
reporters.
K
Yep,
so
now
we
have
the
data
corrector,
so
we
can
so
if
you're
interested
in
you
can
check
you
can
pick
you
can
get
so
source
code
from
github
and
which
we
talk,
show
right
now
that
crowing
reddit.com,
that
which
potential
returns
for
advanced
4-5-1
status
code
from
the
Germany,
but
but
unfortunately,
I
couldn't
find
any
for
five
and
status
code.
I
actually
finished
calling
yesterday
and
there's
no
for
abandoned
status
code
at
this
moment,
but
if
you
think
there's
any
potential
for
five
once
it's
called
web.
K
The
website,
which
returns
for
five
sets
code,
please
use
that
data
corrector
and
also
a
color
and
also
collector
and
so
I.
Think
next
step
is
we
can
we
can
use
that
data
if
we
found
some
so
we
can.
We
can
put
some
input
to
this
working
group
and
also
that
improves
aged
4.1
status,
called
draft.
Thank
you.
A
Just
want
to
mention
that
all
the
slides
are
on
the
the
you
know
in
in
the
data
tracker.
So
so
please
go
through
the
I'll
stop
and
take
if
anybody
would
like
to
ask
a
question
on
any
of
because
this
was
the
end
of
the
the
hackathon.
Oh
there's
one
more!
Ok,
please
sorry,
and
then,
after
that
we
can
take
questions
on
all
of
the
the
hackathon
before
moving
on.
E
Hey
everyone
yeah,
so
my
name
is
Shalon,
so
for
the
hackathon
Christine,
ALP
and
I,
we
worked
on
examining
how
different
browsers,
implement
WebRTC
or,
in
particular,
how
they,
how
they
get
the
local
IP
address
so
about
TC
is
a
technology
which
is
basically
used
to
do
real-time
communication
in
browsers
and
especially
peer-to-peer,
and
for
this
they
need
the
local
IP
address.
So,
but
the
thing
is
that
we
found
that
Firefox
and
Chrome.
E
D
E
This
is
the
website:
it's
netlog
github,
that
IO
slash
WebRTC
privacy,
and
this
is
Safari.
So
if
I
don't
allow
so
then
you
know
we
did
not
get
user
permission,
nobody
support
it
and
it
doesn't
reveal
any
local
IP
addresses.
But
if
I
do
give
it
permission,
then
it
does
see
all
of
my
my
IP
address
my
local
IP
address.
But
if
I
go
to
Firefox
and
I
click,
don't
allow
it
doesn't
care
yeah.
E
So
that's
it
so,
basically,
like
the
idea
is
showcase.
How
different
browsers
have
like
a
different
implementation
of
web
Odyssey,
but
so
this
is
not
ideal
either
because,
like
Safari,
the
permission
it's
asking
is
microphone,
but
so
it's
not
clear
that
this
is.
You
know
related
to
your
like
the
fact
that
it's
revealing
your
local
IP
address,
but
at
least
it's
some
kind
of
user
consent,
but
so
it
says,
I
think
it's
just
a
place
where
more
research
should
be
done
and
more
work
should
be
done
and
yeah.
That's
it.
F
E
The
VPN,
like
that's,
we
didn't
look
into
that
too
much
like
for
for
the
purposes
of
this
hackathon
you're,
mainly
focusing
on
another
case
where
you
have
like
you
know
a
whistleblower
in
an
organization
who
does
not
wish
to
be
identified.
So
the
local
IP
address
is
more
important,
but
yeah
I
mean
I.
Think
I
really
try
out
so
I
can't
really
say
too
much,
but
I
would
imagine
that
it's
the
same
issue
with
respect
to
that
as
well.
Thanks.
A
L
K
K
So
I
think
that
Roberti
stuff
I
think
it's
a
user
agent
issue,
so
I
think
it's
it's
it's
great
ear
to
talk
to
the
web.
Cc
see
people
in
WCC.
They
might
be
have
some
privacy
privacy
consideration
on
their
standards
so
properly.
It's
the
very
good
information
to
input
them
up
to
to
have
a
discussion
about
a
privacy
issue.
Yeah.
E
I
mean
so
Mozilla
and
Google
I
think
have
been
pretty
clear
that
they
don't
want
to
do
this,
at
least
in
the
privacy
discussion
that
have
been
happening
up
to
this
fight,
and
you
know
the
web
RTC.
The
ITA
button
group
doesn't
exist
anymore,
but
yeah
I
think
it's.
Maybe
we
can
talk
to
the
VC
PI.
We
see
a
group
like
I
said.
Thank
you
thanks.
A
M
From
w3c
to
say,
thank
you
for
putting
together
that
this
demo
and
I
very
much
hope
that
you'll
share
that
with
the
WebRTC
yeah
working
group,
because
that
kind
of
input
is
very
helpful
to
us
and
making
sure
that
we
have
the
right
privacy
considerations,
which
is
our
aim
and
all
the
work
that
we
do.
Thank
you
thank.
B
Yeah
so
as
aviary
mentioned,
there
is
RG
adoption
of
the
draft.
So
oh
yay,
there
is
one
small
change,
and
that
is
a
change
in
relation
mentioned
by
mark
Perkins
in
a
in
a
reference.
We
refer
to
intellectual
property,
but
intellectual
property
was
not
thus
described
in
in
the
Universal
Declaration
as
we
refer
to
it.
So
we
we
changed
it
into
the
original
text.
After
that,
I
got
a
email
I'm,
not
sure
if
it
was
on
a
list
or
directly
to
me,
yeah.
E
B
Teresa
that
it's
a
bit
unhappy
that
there
is
that
there
is
only
a
masculine
tense
here,
so
we
changed
it
between
square
blocks
into
place.
He
is,
they
are
I
made
it
clear
that
what
did
not
come
from
from
the
UDHR,
that's
its
I
think
we
will
work
with
this
more
and
we'll
see
more
changes
in
relation
to
the
review
team,
but
we
have
that
later
on
the
agenda.
So
if
there
are
no
questions,
yeah.
A
I
wanted
to
ask
a
question,
so
is
the
review
team-
or
maybe
you
can
cover
this
later
using
this
one
and
is
there
sort
of
a
feedback
loop
or
we
need
to
make
sure
that
there's
a
feedback
loop
I
see
a
head
nodding,
so
there
will
be
a
feedback
loop
on
this.
This
is
one
of
the
things
where
I
am
personally
very
concerned
that
we
get
a
certain
amount
of
rigor
in
in
these
guidelines,
so
that,
as
time
goes
by
we'll
have
things
that
people
can
really
count
on.
G
Nikto
UC
Berkeley
I
I'll
certainly
follow
up
on
the
list
with
with
some
comments,
but
I
thought.
One
useful
thing
to
discuss
in
person
would
be
how
we're
coming
up
with
the
list,
like
there's
19
things
and
the
in
the
in
the
table
of
contents
and
I'm
curious
how
we're
coming
out
with
that
list
because,
for
example,
there's
a
lot
of
things
like
confidentiality,
integrity,
authenticity,
anonymity,
pseudonymity
that
that
are
also
covered
in
the
privacy
and
security
considerations,
recommendations
and,
and
so
I
was
just
quite
confused.
G
B
So
the
reason
why
they
got
there
is
that
they
are
important
from
importers
from
RFC
80
to
80,
whereas
also
the
methodology,
why
why
why
they
got
there
so
leaving
them
out
would
in
will
be
problematic.
But
what
we
try
to
do
is
cross-reference
as
much
as
possible
to
RFC
69,
73
and
49
49,
or
what
is
the
security
considerations?
One
so
I
think
we
could
largely
import
the
work
that
is
being
done
or
respect
the
work,
that's
being
done
by
the
security
and
privacy
work
and
work
around
that
where.
G
A
G
A
Perhaps
something
like
and
and
and
and
pardon
me
is
to
it
just
to
add
something
that
sort
of
says
if
you're
doing
a
privacy
review-
and
this
is
already
covered
there,
then
you
could
skip
this
one,
but
for
the
purpose
of
testing
the
guidelines
and
as
what
we're
looking
at
in
the
review
team
is
for
people
to
test
the
guidelines.
They
may
not
be
doing
the
privacy
review
or
or
it
may
be
done
separately,
so
so
having
them.
A
N
Not
only
for
the
reviewers,
it's
also
before
everything
for
the
internet
draft
authors,
so
they
can
check
their
own
protocol
in
the
spirit
of
fc-69,
73
and
privacy
on
the
one
on
security.
Consideration.
I,
don't
remember
the
number,
but
this
to
MFC
are
actually
used
by
a
lot
of
internet
draft
hours
up,
because
if
they
don't,
if
they
don't
use
them,
they
will
be
cut
later
on
by
the
Esley.
So
the
idea
is
in
the
future
that
maybe
that
will
use
these
guidelines
as
well.
A
But
since
it's
still
just
a
research
document,
it
can't
make
assumptions
about
how
it's
being
used.
Okay,
any
other
questions.
Thank
you,
but
let's
so
maybe
we
can,
though,
just
sort
of
out
of
line
if
you're
actually
doing
this,
for
a
review
and
doing
a
privacy
review
cut-and-paste
or
ignore
okay,
so
yeah
that
one's
you
too
right.
Oh,
no,
that
one's.
B
N
So
please
we
don't
review
and
I
also
noticed
that
if
you
care
about
the
document
and
what
reviews
you
have
to
do
with
you
for
all
the
documents,
that's
why
we
a
few
open
questions.
If
you
read
it,
you
will
see
that
there
are
several
places
where
there
is
a
to
do.
G
audio
is
things
that
should
be
improved,
really
should,
for
instance,
there
are
some
examples
of
why
it's
good
to
have
anonymity,
but
not
a
lot.
N
N
N
This
is
a
sort
of
thing
that
that
should
be
read
in
the
context
of
the
discussion
and
anonymity,
so
I
think
up
to
now,
all
that
have
been
little
interest
as
a
scene
is
in
reviews
in
commands
in
etc.
So,
in
my
opinion,
if
the
draft
for
for
the
draft
to
go
somewhere,
we
need
much
more
involvement
from
the
wizard
group
and
so
I
just
asked
to
read
it
to
command
to
review
on
it's
maintained
on
github.
So
you
can
also
send
the
pull
request.
You're
welcome
thanks.
A
First
I
wanted
to
apologize,
I,
read
it
and
never
got
around
to
writing
down
the
questions
that
I
wanted
to
ask.
But
a
couple
of
things
that
occurred
to
me
while
I
was
reading
it
is,
is
the
anonymity
and
the
right
issue,
and-
and
so
in
other
words,
how
is
it
a
right
describing
its
relationship
to
rights?
Is
it
derivative
in
some
sense?
Is
it
an
enabler
of
right,
so
some
discussion
on
that
and
you
know
anonymity
seems
a
good
thing,
but
that
discussion
doesn't
seem
highly
developed.
A
I
was
wondering
whether
there
were
levels
of
nanana,
MIDI
and
I
was
thinking
about
that
and
I
was
looking
at
things
like
you
know.
One
of
the
things
that
worries
me
DOS
now
is
we're
identifying
ourselves
we're
all
going
out.
Actually
I
don't,
but
we're
all
going
down
and
identifying
ourselves
with
our
biometrics
so
that
we
can
use
our
things
easily.
How
does
that
relate
to
anonymity?
Does
that
blow
it
out
of
the
water
completely
or
or
you
know,
or
is
there
a
warning
to
be
put
in
there?
A
M
Wendy
Seltzer,
thank
you.
I.
Do
think
that
this
is
an
important
area
and
I
will
offer
a
review
and
some
comments.
One
thought
I
had
on
the
framing
is
that
anonymity
is
valuable
as
a
compositional
issue,
that
you
can
build
identity
on
top
of
protocols
that
start
from
anonymity,
it's
much
more
difficult
to
build
anonymity
on
top
of
protocols
that
start
with
strong
identity.
O
Hi
Brian,
wouldn't
I,
want
to
echo
the
thanks
for
this
important
work
on
anonymity,
defining
the
protocol
considerations.
One
of
the
things
that
strikes
me,
though,
is
most
of
the
places
we
go
on
the
web.
If
we
show
up
is
completely
anonymous,
we
stick
out
like
a
sore
thumb
and
it
to
be
believably
anonymous.
We
need
some
sort
of
a
persona
that
might
be
crafted.
It
might
not
even
be
true
and
so
a
lot
of
people
when
they're
trying
to
be
anonymous.
O
They
have
a
phone
number
for
one
persona,
an
email
address
for
one
persona
and
then
in
their
other
personas
they
have
other
phone
numbers,
other
email
addresses
and
other
characteristics,
and
they
keep
these
identities
separate,
and
it's
just
that
aspect
of
anonymity
or
pseudonymity
I,
just
didn't,
seem
well
developed
in
the
draft
and
I
I
wanted
to
throw
that
up
for
discussion
to
see
if
there
was
sort
of
alignment
in
principle
and
if
so,
I'm
happy
to
help
flush
out
that
text.
One.
N
N
So
it
seems
to
me
that
there
have
been
a
lot
of
discussion
outside
of
IETF
about
things
like
the
rights
of
the
user,
to
some
anonymity
of
pseudonymity
when
using
services
like
Amazon,
Facebook,
etc,
but
little
discussion
about
consequence
for
identity
of
the
infrastructure
of
the
internet,
for
instance,
IP
itself
on
this
is
clearly
some
things
that
could
be
done
in
the
IETF
III
RTF,
while
other
issues
such
as
anonymity
in
database,
for
instance.
We
are
not
the
best
experts
on
it's
already
Endel
by
other
people,
I
think
so.
O
I
would
say
coming
from
the
security
group.
There
is
a
lot
of
work
there
in
authentication
of
various
kinds,
PKI
based
as
well
as
Kerberos
based,
and
so
it's
not
just
a
cookies
in
CSR
auth
tokens.
But
these
things
all
have
relationships
with
each
other,
and
then
they
get
tied
to
IP
addresses
and
then
they
get
used
to
linked
IP
addresses
together.
So
I
would
recommend
that
we
broaden
the
scope
a
little
bit
in
that
regard.
O
N
Not
but
there
is
also
a
simple
practical
problem.
As
I
said,
we
had
very
little
activity
on
the
draft,
so
I
would
suggest
instead
that
maybe
it's
better
to
focus
on
the
few
things
we
really
know
about,
because
the
entire
issue
of
anonymity
I
don't
eat.
The
authentication
is
extremely
wide
on.
We
clearly
have
limited
limited
workforce
in
the
group
test.
A
O
J
No,
no
one
idea
is
you
have
pseudonymity,
which
is
quite
good,
but
you
might
us.
We
could
also
talk
about
randomization,
it's
kind
of
related
like
sometimes,
if
you
don't
certain
values,
you're
not
allowed
to
connect
to
the
protocol
won't
work,
but
you
can
randomize
certain
things
so
there's
some
ideas
there
and
my
second
comment
was
about
the
section
I
think
that's
new
about
objections
against
anonymity.
J
I
would
recommend
just
killing
that
section
and
using
it
to
basically
enhance
your
introduction
or
your
your
arguments
that
you
make
further
up
in
the
document
rather
than
presenting
the
opposition.
You
just
sort
of
you
know
what
the
opposition
is,
and
you
write
your
introduction
and
your
supporting
arguments
with
those
in
mind.
That's
just
where.
N
You
at
the
plenary
yesterday
because
I've
been
a
discussion
about
this
about
the
draft
on
this
left
and
what
an
effect
on
encryption
with
the
supporters
of
this
draft
that
we
have
to
lay
down
to
write
down
the
reason
people
don't
want
or
don't
like
encryption,
so
we
can
once
it's
documented.
We
can
do
something
about
it
on
other
people
like
me
said
that,
while
writing
it
in
I've
seen
no
official
RFC
will
probably
have
exactly
the
opposite
effect,
giving
them
some
credence.
So
it's
probably
more
or
less
the
same
problem.
Okay,.
G
Nick
Nick
Terry,
UC
Berkeley,
first
of
all,
I'll
commit
to
sending
review
comments.
I
hadn't
gone
to
that
yet
and
I
have
a
lot
of
comments
that
can't
work
right
now.
So
some
of
those
look
of
an
email,
I
I,
was
sort
of
a
plus
one
on
the
idea
about
perhaps
broadening
this
to
pseudonymity
or
or
I,
guess,
maybe
more
to
the
point.
I
I
think.
Maybe
we
can't
I
don't
think
we
can
do
a
very
good
job
describing
the
protocol
considerations.
If
we're
just
talking
about
anonymity.
N
G
P
To
this
way,
first
I,
like
the
draft
and
I,
really
like
the
definitions
and
I,
want
to
add
something.
We
are
actually
implementing
anonymity
features
in
our
apps
and
we
have
another
thing
which
I'm
a
little
missing.
I
can
combine
it
all
of
the
other.
Half
definitions,
I,
think,
but
likely
using
them
like
a
toolbox,
which
is
what
definitions
are
for.
We
are
differing
between
a
person
talking
to
another
person
and
no
attacker
can
even
know
who
is
talking
to
whom
even
not
know
that
people
are
actually
talking.
P
P
The
applications
for
the
second
one
is
obviously,
for
example,
for
Lee
King
things.
We
call
it
internally,
the
WikiLeaks
feature
you
want
to
and
I
think,
because
that's
very
different
from
implementing
and
a
ITF
draft
has
usually
the
intention
to
help
implementers
getting
things
done.
I
think
that
could
be
something
you
could
add.
Unfortunately,
I
don't
have
a
good
name
for
it.
So
beside
WikiLeaks
feature,
we
call
it
full
anonymity
against
anonymity,
but
perhaps
have
a
better
name.
Thanks
and.
A
A
A
Q
Neil's
loves
this
quote
and
I'm
starting
to
love
it
as
well.
We
changed
a
little
bit
the
arrangement
of
everything
and
just
trying
to
think
how
the
architecture
itself
impacts
and
enables
her
in
our
or
inhibits
their
right
to
association,
but
also
vice
versa.
If
we
could
apply
the
right
to
association,
legal
standards
to
the
internet
itself
as
an
infrastructure,
and
what
would
it
mean
so
a
quick
overview
of
the
changes?
Q
We
ditched
the
right
to
protest
as
an
angle
of
analysis,
because
that's
where
the
your
idea
came
from,
but
we
later
realized
that
just
association
and
assembly
by
itself
were
way
more
interesting
and
protest
was
just
making
a
lot
of
noise.
So
we
ditched
that
we
removed
the
filter
bubble
section
in
the
literature
review,
because
there
was
the
opposite
of
consensus
on
that.
We
were
discussing
a
lot
about
the
approach
towards
that,
so
we
just
removed
it
as
well.
So
we
can
unban
some
building
this
consensus.
We
have
new
vocabulary.
Q
We
were
taking
vocabulary
from
the
past
RFC
that
I
don't
know
the
RFC
numbers
by
heart,
but
maybe
Niels
and
all
the
rest
of
you
do.
We
have
different
research
questions
as
well.
That
I'll
show
in
a
second
changes
the
structure
and
we
added
to
discussions
in
the
end
protocols
versus
platforms
and
the
internet
assess
an
association.
So
the
first
research
question
you'll
see
it's
pretty
much
the
same.
That's
basically
what
the
guidelines
have
been
building
upon
and
the
second
one
we
change
it
just
like
this.
Q
B
Iso,
what
happens
in
in
several
of
these
discussions
has
happened
during
RFC
80
to
80,
so
it's
starting
to
become
a
familiar
thing
that
we
need
to
have
technical,
legal
and
some,
what
sociologists
explanations
for,
or
concepts
from
Science
and
Technology
studies
to
come
to
the
same
thing.
So
an
example
here
is
where
we
look
at
internet.
B
So
there
we
have
the
standard
technical
one
of
the
network
of
network
that
consists
of
a
asses
that
are
connected
through
IP,
but
then
we
also
have
other
beautiful
ones
with
it
that
it's
a
persistent
socio
technical
system
over
which
services
are
delivered,
but
also
a
techno
social
assemblage
of
devices,
user,
sensors
network,
routers
governance,
administrators
operators
and
protocols,
and
then,
as
last,
because
and
rule
of
the
emergent
process.
So
much,
we
have
an
emergency
press
driven
thing
that
is
born
from
the
collection
of
the
ASA's
that
happen
to
be
together
at
a
given
time.
B
The
fact
that
they
tend
to
interact
at
any
given
time
means
it
is
an
emergent
property
that
happens
because
they
use
the
protocols
defined
at
the
IETF.
So
I
think
this
this
this.
This
definition
is
somehow
a
bit
the
it's
yeah,
it's
a
bit.
What
we
do
here
is
I
I,
really
like
the
beauty,
we've
added
the
new
structure,
so
we
added
a
part
on
IRC
which
we
did
not
have.
B
We
Giselle
and
I
first
talked
about
XMPP,
but
XMPP
was
already
extensively
discussed
in
RFC
82
80,
so
we
looked
at
IRC
found
some
interesting
things
in
the
grouping
together
we
ditched
the
process,
but
looked
a
bit
better
at
a
SS
and
had
a
lot
of
discussion
about
that
and
on
suggestion
of
Steven
Ferrell
he
said
we
had
after
a
thorough
review.
We
said
we
said
initially
said
we
do
not
look
what
happens
on
top
of
the
network,
but
we
do.
B
Q
Can
take
over
just
to
explain
the
difference
between
this
and
then
be
great
if
you
could
continue
so
in
the
beginning,
was
that
the
internet
constituted
an
assembly
but
Sandra
Brown
and
gave
us
great
comments
at
last
ITF
session
regarding
the
lack
of
accuracy
in
our
definitions,
but
because
assemblies
are
a
temporary
nature,
we
change
to
the
Internet
as
an
association,
and
we
argue
that
that
is
exactly
the
point.
So.
B
Then
we
come
to
the
conclusion
that
the
internet
is
made
up
of
interconnected
guesses,
which
jointly
form
an
association
and
that
Association
should
be
protected.
But
what
does
that
mean
because
it
might
not
be
the
only
Association,
because
if
every
network
isn't
an
association
within
the
Association
that
the
Internet
is,
does
it
hat?
Does
the
a
s
have
an
absolute
freedom
to
implement
its
own
rules,
or
should
it
rather
have
commitment
to
the
larger
Association?
B
So
does
the
importance
of
a
functioning,
larger
Association,
the
Internet
prevail
over
a
preference
of
a
smaller
Association,
and
how
does
it
then?
What
does
that
happen?
If
there
is
an
assembly
of
two
people
that
associate
over
to
a
SS?
That's
then
over
to
one
Association,
that's
the
Internet.
So
what
is
the
relation
between
these
assemblies
and
associations?
And
how
is
that
prioritized?
And
what
does
that
actually
mean?
B
So
one
could
arguably
say
that
that
the
largest
Association
enables
the
most
assemblies
so
that
one
should
be
most
protected,
but
in
the
human
rights
practice
one
normally
argues
from
starting
from
the
end
user
from
the
rights
holder.
Sorry
in
which,
in
this
case
would
be
the
end
you
that
are
assembling,
so
that
would
mean
it
from
the
other
way
around.
So
that
is
something
that
we
would
really
like
to
discuss
with
you,
because
that
really
changes
the
the
conclusions
and
then
also
there
was
a.
B
There
was
a
thing
that
we
all
Tercel
like
when
do
it
when
doesn't
a
s
become
part
of
the
Association
of
the
Internet's?
Is
it
when
it
receives
an
autonomous
system
number?
Is
it
what
in
ounces
it
routes
or
when
it
starts
shipping,
shipping,
packets?
And
if
it's
only
routes
with
with
another
IAS
over
the
Internet?
Is
it
still
part
of
that
association
and
what
are
the
implications
of
stating
that
the
Internet
should
be
protected
as
Association,
so.
Q
Just
one
quick
comment:
since
the
beginning,
we
started
discussing
about
like
private
networks
having
public
impact
there
for
aligning
towards
the
larger
public
ensemble,
and
we
kind
of
left
it
over
in
the
middle
of
very
many
other
super
interesting
discussions
and
recently
in
the
mailing
list.
We
went
back
to
it
and
it
is
also
reflected
on
the
draft
itself.
B
A
I'd
like
to
ask
how
many
people
have
actually
read
the
the
reworked
version?
That's
a
good
number,
that's
good!
So
we
don't
have
anybody
at
the
line.
Yet
is
that
just
because
there
are
no
comments?
Okay,
at
the
end
of
this
I'm,
also
going
to
ask
after
we've
gotten
the
line
whether
this
has
progressed
and
changed
enough
since
I
assume.
You
still
want
this
to
become
a
research
group
document,
so
at
the
end
of
the
discussion,
I'll
ask
if
we're
there
yet
and
then
go
on
from
there,
but
please
hi.
H
This
is
Karen,
hey
Sheila,
future
now
bug
so
I
had
a
question
in
terms
of
where
you
want
this
to
go
in
a
sense
that
I
think
the
discussion
has
been
really
interesting
on
the
list,
but
especially
for
people
who
aren't
very
well
versed
and
like
the
kind
of
stuff
that
HR
PC
does.
It
might
be
a
little
hard
to
understand
why
we're
having
this
conversation
and
like
what
the
problem
is,
it
is
trying
to
solve
by
trying
to
figure
out
whether
this
is
an
association
or
an
assembly.
Q
Can
take
the
association
and
assembly
part
legally?
They
have
different
implications
because
one
has
a
more
formal
and
established
nature
and
the
other
one
is
rather
temporary.
The
assembly
is
temporary
and
the
Association
is
a
forma
thanks
for
your
question
crane
by
the
way,
so
the
it
has
different
legal
implications
that
could
replicate
as
well
in
the
technical
and
infrastructure
level
and
regarding
the
research
group.
Sorry,
the
HR,
PC,
bigger
perspective,
I
think
meals
can
be
better
suited
to
answer
that
yeah.
B
So
I
think
your
question
is
about.
Why
are
you
sparing
my
mailbox
with
this
theoretical
discussion
and
relevance,
etc?
Well,
I
think
the
answer
can
be
found
in
the
Charter.
Is
that
we're
trying
to
understand
the
impact
of
writes
on
protocols
and
protocols
on
writes
and
that's
exactly
what
we're
trying
to
do
so,
even
though
that
sometimes
needs
a
significant
layer
of
extraction?
B
J
Malory
noodle
I'm
just
a
suggestion
and
how
you
tackle
some
of
these
questions
like
round
is,
and
witness
and
a
s
become
associated
rather
than
maybe
asking
the
determination
like
that
question.
A
friend
just
exploring
and
the
nature
of
that
activity
is
that
Association,
June
and
I'm
saying
like
so
instead
of
asking.
Does
this
make
a
s?
J
I
All
the
time
versus
you
know
the
individuals
themselves,
and
it
seems
to
me
that
the
individuals
have
rights,
but
I,
don't
really
see
how
you
get
from
from
those
individuals
to
the
a
SS
or
the
internet
or
any
of
these
underlying
things
being
an
association
or
an
assembly
or
any
of
that
stuff.
It's
just.
It
might
be
a
forum
for
this
thing,
although
I
feel
uncomfortable
with
X.
It's
not
really
a
space.
So
there's
a
whole
really
I.
Think
what's
happening.
I
The
the
difficulty
that
are
having
with
the
terms
here
and
and
so
I'm
just
afraid
that
there
isn't
a
way
to
make
this
work
because
the
because
the
concepts
don't
really
fit
the
the
underlying
mechanism.
It's
it's
like
you
know.
Sometimes,
when
I'm
reading
this
I
I
feel,
like
you
know,
you're
saying
you
know
well,
if
I
put
a
whole
bunch
of
cars
together,
is
it
an
assembly
or
an
association?
Well,
neither
it's
just
a
pile
of
cars,
it's
traffic
or
it's
a
parking
lot,
or
something
like
that
and
and
I.
I
B
I'm
I
think
the
I'm
trying
to
think
of
it.
It
may
be
you're
right
right,
but
III
haven't
come
to
the
same
conclusion
as
you
yet,
but
I
think
a
newspaper
or
a
media
house
or
a
radio
station
is
itself
also
a
technology,
that's
enabling
freedom
of
expression
and
it's
actually
the
people
that
are
doing
it,
but
still
the
the
whole
licensing
scheme
and
the
way
people
work
in
the
labor
laws
and
etc
the
they
are
a
specific
ordering
that
enable
or
disable
a
kind
of
enabling
of
Rights.
B
So
the
same
is
true
for
the
Internet
infrastructure
and
people
do
associate
over
the
Internet.
So
I
think
it's
important
that
we
try
to
understand
what
the
structure
and
potential
consequences
are
of
that
and
the
reason
for
doing
that
and
to
go
through
it
as
nauseum
is
because
else
someone
else
might
do
it
for
us.
So
I'd
rather
have
this
this
this
this
may
be
sometimes
confusing
or
irritating
discussion
here
then
that
other
someone
comes
up
with
with
it
elsewhere,
because
we
keep
on
saying
that
if
non-technical
people
make
decisions
about
this,
then
it's
shitty.
I
I
Is
it
on
the
internet
or
not
well
kind
of
yeah
kind?
Of
no,
and
that's-
and
that's
not
a
thing
you
can
say
about
like?
Is
this
an
employee
of
the
radio
station?
Yes
or
no?
Well,
you've
got
an
answer
to
that.
It's
a
legal
answer
and
I
think
that
those
I
think
that
the
III
I
believe
that
that
fuzziness
in
one
case
and
the
lot
and
the
non
fuzziness
in
the
other
case,
is
part
of
the
problem
here
now
I
agree
with
you
that
you
know.
O
Wooden
again,
so
I
would
agree
that
the
document
is
not
yet
ready
for
adoption.
I
would
also
echo
the
importance
of
the
area
France
when
I
think
of
the
social
credit
system,
that's
emerging
in
China
and
I
think
for
the
potential
for
that
system
to
actually
hurt
people
just
based
on
who
they
associate
with
having
a
lower
social
credit
score
than
them,
and
the
many
different
ways
that
that
can
hurt
them.
R
B
A
B
B
I
Q
Yeah,
and
also
like
on
a
really
quick
note,
I
think
the
effort
here
is
also
trying
to
stop
separating
its
side.
Michael
from
the
social
and
the
political
looks
more
and
more
they
come
intertwined,
so
I
mean
we
could
argue
it
towards
there,
but
yeah.
Maybe
we
can
from
this.
We
can
take
a
way
forward.
I'd
be
happy
with
that.
Are.
A
L
A
B
See
how
political
diskettes,
so
the
HRP
see
political
we're
doing
this
work
cuz
in
RFC.
Eighty
two,
eighty
we've
been
trying
to
research
the
protocol
impacts
on
human
rights
and,
with
this
draft,
were
also
understanding
the
dynamics
impact
impacting
protocols
and
architecture
development,
so
we're
trying
to
describe
the
political
aspects
of
protocols,
also
because
these
came
up
time
and
again
as
discussion
in
his
research
group,
and
it
is
because
the
internet
is
a
part
of
the
basic
infrastructure
of
information
societies
and
protocols
that
are
being
developed
here
in
the
ITF
influence.
B
So
the
latest
changes
a
lot
of
typos
thank
to
mark
Perkins
for
going
so
so
thoroughly
through
three
drafts.
That
was
really
appreciated.
Lots
of
work,
a
lot
of
people.
Several
people
contacted
me
about
this
off
list,
and
this
resulted
actually
really
good
discussion.
Editor
position
that
all
protocols
are
political,
sometimes
and
is
largely
based
on
the
law
of
unintended
consequences,
improved
examples
in
the
field
of
competition,
also
by
separating
standards,
general
and
IETF,
specific
parts
added,
more
dynamics
about
standard
development,
general
and
ITF
in
specific.
So
where
do
we
go
with
this?
B
O
So
for
Brian
wooden
again
so
for
political
I
thought
one
seminal
work
that
could
add
value
if
just
mentioned
cited
and
maybe
even
pull
a
little
bit
from,
is
a
seminal
paper
by
a
rogue
away
on
the
moral
character
of
cryptographic
work
because
it
really
speaks
to
the
heart
of
how
what
we
do
with
protocols
really
really
matters
ethically,
morally,
politically
in
people's
lives
etc.
Could
you
share
that
one
on
the
list
and
I'll
make
sure
that
I
sure
well
as
soon
as
I
get
permission
post
to
list?
Thank
you
thank.
A
O
L
Please
come
to
the
microphone
and
introduce
yourself
into
that
very
health
and
inner
area,
so
I
think
it's.
This
is
a
very
important
topic
and
I
think
that
the
the
the
the
question
which
I
have
to
I
guess
the
chairs
and
stuff
is
what
is
the
criteria
for
Rjay
adoption?
So
obviously
we
need
to
understand
the
politics
of
standards
for
offering
a
standards
body.
There
will
be
political
ramifications.
The
standards
we
create
having
doctrine,
which
explains
this
background
very
very
well,
is
very
useful.
Do
we
imagine
this
being
operationalized
somehow
in
a
future
process,
not.
A
Necessarily
I
mean
this
is
a
research
group,
so
I
think
you
know
the
criteria
has
been
that
there's
a
consensus
in
the
group
that,
yes,
we
want
this
to
be
our
document,
as
opposed
to
just
his
that
they
are
ready
to
give
up
their
control
of
it
and
make
it
our
document,
but
operational,
not
necessary.
I
mean
some
of
the
things
with
considerations
in
them
like
like
80
to
80.
Yes,
that
was
meant
to
be
operationalized
once
it's
once
it's
you
know,
verified,
etc.
This
not
necessarily
it
doesn't
need
that
to.
B
As
author
I
think,
I
really
want
to
understand
to
map
the
problem
space
before
and
then
maybe
consequences
of
that
or
or
specific
problems
arising
for
that
might
come
into
a
new
draft,
but
I
think
if
we
first
have
this.
If
we
first
can
agree
on
this,
I'm
already
really
happy
with
having
that
in
a
document
section
in.
S
Teresa
had
I
read
the
draft
and,
to
be
honest,
I
was
a
little
confused
by
everything
basic
by
the
structure.
From
section
four
onwards,
like
section
three
I
can
understand
its
different
positions
that
some
people
have
and
then
four
until
the
end
I'm
like
what
are
these
headings?
What
are
these
sections
supposed
to?
Tell
me?
I
just
went
back
to
the
abstract,
and
it
says
here
we
are
mapping
different
positions
and
I'm
like
okay,
that's
section
three,
but
the
rest
like
what
is
the
focus
but
I've
only
read
it
once
and
then
got
really
confused.
B
G
A
I
think
I've
gotten
clue
without
asking
a
general
question
that
it's
not
quite
ready
and
I'm
getting
a
head
nod:
okay,
great
thank
you
and
so
you'll
keep
working
on
it
and
we'll
keep
coming
on.
Okay.
So
we're
now
up
to
update
on
implementation
of
451,
or
did
we
already
do
that?
No,
we
did
the
we
didn't
do
the
we
did
part
of
it
right
right.
E
E
It
is
an
individual
draft
and
the
recommendations
I
was
making
were
based
on
feedback,
and
the
research
done
was
that
we
should
have
a
geographical
scope
to
the
response
that
we
get
to
so
that
if
because
blocks
are
often
nationally
scoped,
so
if
you
are
getting
an
HTTP
451
response,
then
you
probably
want
to
know
where
it
was
blocked.
So
that's
one.
So
the
other
thing
was
to
disambiguate
so
make
a
difference
between
like
blocking
authority
and
the
implementer
of
the
block.
E
So,
for
example
like
the
like
the
entity
mandating,
the
block
would
be
a
court
or
a
government,
and
the
actual
implementer
of
the
block
would
be
an
ISP
and
it's
important
to
distinguish
between
these
two
things.
So
the
work
done
was
to
combine
this
draft
with
the
draft.
Many
folks
they
charge
see
RFC
seven
seven
to
five.
So
basically,
what
this
draft
now
also
has
is
the
guidelines
from
RFC.
Eighty
to
eighty
as
applied
to
451
and
yeah,
so
I
guess
the
next
steps
would
be
I
spoken
to
mark
nodding
him.
E
A
H
A
N
Again
so
we
now
have
Human
Rights
review
team.
What
does
it
mean?
A
review
team
is
a
team
that
we've
used
basically,
that
we've
used
internet
draft
we've
been
reading
them,
understanding
them
and
then
making
commands
remarks.
Instable
a
lot
of
people
when,
especially
when
they
are
new
to
the
IETF,
believes
that
a
review
team
is
something
very
organized,
very
formal,
requiring
approbation
by
the
IAB,
iesg,
etc.
But
in
reality,
most
of
the
review
team
that
you
can
see
during
discussion
in
the
IETF
are
quite
informal.
N
Even
sometimes
unofficial
I
mean
two
people
can
gather
together
on
declare.
We
are
a
review
team,
it's
a
freedom
of
association,
it's
good.
Of
course.
The
comments
won't
have
any
specific
weight
unless
Java
they
are
good.
The
point
is
that
review
team
are
typically
not
official
part
of
the
process.
I
mean
they
comment.
If
the
command
are
good,
they
can
be
taken
into
account
otherwise
nope.
So
we
view
team
as
to
prove
that
it's
comments
our
worth
it
on.
It
has
to
establish
a
reputation.
N
So
current
state,
the
review
team
exists,
which
means
that
we
have
a
mailing
list
at
this
time.
It's
all
some
review
team
of
more
formal
group
where
software
to
work
together.
It
should
request
things
like
that.
We
don't
at
this
time
at
all
Artie
its
public
because
of
well
like
everything
I
mean
there
is
no
formal
membership
of
the
review
team.
Anyone
can
join
the
list,
but
it's
not
supposed
to
be
a
general
discussion
list.
We
already
have
one
for
this.
N
It's
supposed
to
be
a
list
focused
on
reviews,
so
publishing
reviews
discussing
meta
discussion
about
the
reviews,
a
thing
like
that,
it's
very
recent
no
review
was
done
yet
so
at
this
time
it's
only
vapo
well,
but
we
will
try
to
turn
it
it
into
something
more
concrete.
So
the
reviews
will
be
based
on
what
the
the
idea
is
to
focus
on
draft
which
are
in
IETF,
why?
The
last
call
I
Center
some
examples
to
the
mailing
list,
because
there
was
a
draft
where
iesg
is
asking
for
comment
from
anyone
at
the
IETF.
N
N
It
was
published,
which
is
itself
derivation
of
ofc
80
to
80
section
6,
section
CC
of
the
FFC
80
to
80
is
supposed
to
be
the
list
of
things
at
the
OFC
authors
should
a
check
to
be
sure
that
their
draft,
the
protocols
don't
have
an
intended
on
bad
human
wife
consequence
because
I
have
see
80
to
80
is
bigger.
The
idea
was
to
move
this
part.
The
concrete
part
to
a
separate
shaft
on
the
review
team
will
both
use
as
a
draft
on
guidelines
to
guide
its
walk
on.
N
Also
will
produce
input
about
this
draft.
Does
it
walk?
Is
it
realistic?
Is
it
a
good
thing
or
not?
Maybe
we
should
change
the
draft
on
guidelines
at
whatever.
So
volunteers
are
welcome,
but
not
too
many
I
mean
it's.
The
review
team
is
supposed
to
do
reviews,
so
we
don't
really
need
people
who
just
come
here
for
sending
one
questions
and
that's
all.
We
mostly
need
people
who
will
commit
to
do
reviews
and
to
discuss
reviews
with
other
people
and
with
the
IETF
commands
and.
A
All
I've
got
one
and
then
hopefully
people
will
come
to
a
line
okay.
So
when
I
was
looking
at
it,
I
was
sort
of
saying:
okay,
it's
an
independent
activity,
that's
kind
of
hanging
out
in
the
HR
PC,
but
because
of
the
that
it
would
be
following
the
guidelines
and-
and
we
spoke
before
about
not
only
following
the
guidelines
but
giving
feedback
as
part
of
that
that
it's
also
kind
of
an
activity
of
the
HR
PC.
So
is
it?
A
N
A
J
J
N
Already
went
through
all
the
draft
in
the
ietf
white
last
call
to
get
an
idea
how
many
were
relevant
for
the
review
team.
Many
of
them
are
on
very
specific
and
very
detailed
technical
topics
that
I
understand
nothing
about.
So
it's
very
difficult
to
find
the
human
rights
issues
in
it,
maybe
they'll,
but
it's.
L
N
Difficult
to
dig
them
out,
so
that
could
be
a
first
criterium
on
then
for
your
ID.
Why
not?
But
so,
if
your
team
is
made
of
volunteers,
there
is
no
hierarchy.
So
if
people
want
to
do
a
review
of
this
draft,
even
if
it
does
not
fit
the
meta
guidelines,
there
is
nothing
to
prevent
them.
So
it
could
be
a
good
idea
to
have
this
sort
of
rules
to
filter
the
draft,
but
people
won't
be
forced
to
follow
them.
Of
course,.
R
R
N
Was
more
flagging
of
future
I've
ever
seen
with
doing
this
analysis
for
existing
FFC
could
be
interesting
to
inform
the
discussion
on
the
guidelines
left
on.
It
could
be
interesting
also
if
some
people
want
to
develop
this
version
of
the
RFC
addressing
the
problem
that
we
found,
but
at
this
time
on,
remember
that
we
did
nothing
yet
it
just
took
his
trip
with
at
this
time.
The
idea
is
motor
focus
on
a
last
call
draft,
because
we
could
flag
problem
related
to
human
rights
and
I,
don't
agree
with
you.
A
Me
for
interrupting,
we
have
only
three
minutes:
left
I
want
to
be
very
careful,
we're
a
research
group.
So
it's
fine
for
us
to
do
this,
and
it's
fine
for
us
to
scream
in
the
wilderness
that
hey.
We
found
human
rights
stuff
in
this
review,
but
I
don't
think
we
can
operationalize
it
in
such
as
attaching
it
to
anything.
Ietf,
ish
I
think
we
have
to
be
very
careful
in
that
boundary.
We're
a
research
group.
So
we
can
shout
hey.
A
R
A
L
Is
just
a
quick
non
non-binding
suggestion
I
reviewing
last
calls
is
great.
Everyone
I've
support
more
review.
You
know
the
message
layers
security
group
just
had
their
charter
Vogel.
What's
up
everyone's
going
to
see
me,
go
forward,
lots
of
obvious
human
rights
connections,
the
Indian
encryption
and
group
messaging
and
and
they're
basically
making
a
charter
what
security
properties
and
privacy
properties
so
another
model,
or
something
which
you
can
do.
L
In
addition,
if
people
have
lots
of
time
would
be
the
liaison
with
working
groups
which
are
in
charter
stage
and
talk
them
about
their
threat
models
and
their
charter,
and
that
could
be
informal
or
could
be
done
over
their
mailing
list.
I
think
that
could
be
a
way
to
influence
new
high
profile
work
that
hasn't
quite
got
to
the
last
call
stage.
Yeah.
A
N
H
Current
I
was
wondering
if
I
could
provide
a
little
bit
of
pushback
to
to
what
you
said
ivory,
because
I
understand
that
you
want
everybody
to
stay
in
their
lane,
for
this
work
to
be
effective.
But
at
the
same
time
you
see
people
who
are
in
this
group
going
to
IETF
working
groups,
training,
they're,
standing
there
saying
this
and
I
work
for
the
ACLU,
the
cdtv
article
19,
coming
with
a
very
specific
perspective,
and
that
isn't
frowned
upon
as
such.
I
also
think.
T
Short
suggests
and
how
this
really
a
team
could
be
useful
for
other
groups
and
I
think
especially
advertising
it
as
a
service
and
saying
oh,
if
you're
designing
something,
if
you
have
something
you're,
not
sure
about,
or
you
think
that
might
have
human
rights
considerations
come
to
us,
we'll
review
it,
and
we
look
at
that
and
either
we
make.
You
feel
comfortable
that
you
did
the
job
right
or
we
point
out
things
weird
might
be
problematic,
I
think
the
framing
it
this
way
would
disappoint
nobody
and
help
to
getting
this
stuff
forward.
N
Because
we
don't,
we
cannot
yet
pose
as
the
Human
Rights
review
experts,
because
we
didn't
do
anything
at
this
time-
not
really
so
better
to
start
to
build
things
to
send
reviews.
And
then
we
will
be
able
to
outreach
to
the
rest
of
the
IETF
and
to
tell
them
a.
We
provide
a
great
service,
but
it's
too
early
yeah.
A
Thank
you,
I
think
it's
a
great
idea.
Thank
you
for
the
discussion.
We
got
to
all
the
agenda
items
except
for
open
discussion
and
any
other
business,
but
we
can
have
lots
of
open
discussion
on
the
list
and
I
really
appreciate
the
amount
of
good
discussion
we
had
in
the
meeting
see
on
the
list.
Thank
you
and
anybody
that
did
do
the
blue
signing
thing.
Please
come
up
and
do
the
blue
signing
thing.
