►
From YouTube: IETF101-CAPPORT-20180320-1330
Description
CAPPORT meeting session at IETF101
2018/03/20 1330
https://datatracker.ietf.org/meeting/101/proceedings/
A
D
E
C
Sad
I
saw
brick
on
the
way
out
and
he's
not
here.
You
must
have
something
else
on
nevermind,
so
apologies
from
Eric,
my
co-chair,
who
is
dealing
with
family
medical
emergencies.
I
don't
see
him
online,
so
we'll
just
have
to
do
this
without
him.
If
there's
any
anything,
we
need
to
decide
concretely
we'll
take
it
to
the
list
anyway.
So
that's
not
a
big
problem.
E
C
Have
the
means,
of
course,
the
slides
didn't
update
the
engine?
The
agenda
has
the
stupid
all
right,
and
so
we've
had
a
request
from
check
to
talk
about
some
of
the
hot
spot.
Light
security
on
properties.
We'll
do
that.
If
we
have
time
it's
been
some
how
we
go
and
the
meaty
issues
that
we
have
in
front
of
us.
Does
anyone
have
any
agenda
great
next,
very
brief
status.
Other
working
groups
do
this.
So
just
around
people
we
have
to
go
to
drafts.
They're
adopted.
C
C
B
F
I'm
Tully,
so
this
is
on
behalf
of
both
Tasha
and
myself,
so
we
do
have
a
working
group
draft
version
of
the
captive
portal
API.
Now,
as
I
mentioned,
it
is
up
on
github.
It
is
also
on
the
main
document,
so
this
is
taken
from
the
one
that
had
been
started
before
and
cleaned
up
with
some
of
the
feedback
from
the
group,
and
it
is
still
very
much
a
work
in
progress
with
open
issues,
but
this
is
what
we
have.
F
So
we
want
to
go
over
is
what
we've
put
in
there
so
far,
it's
pretty
basic
and
what
are
the
open
issues
and
how
we
want
to
see
it
at
all
from
there.
Next
slide,
please
great!
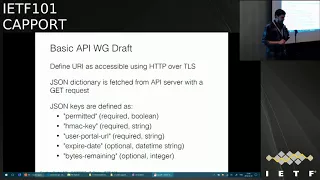
So
it's
a
pretty
basic
API
we
have
here.
We
define
first,
that
we
have
some
URI
that
we
get
by
some
other
means.
That
is
not
part
of
this
document,
and
this
URI
specifies
some
resource
that
is
accessible
using
HTTP
over
TLS,
and
this
resource
is
a
json
dictionary
which
is
fetched
from
this
api
server.
F
Presently,
it
is
with
a
get
request
and
the
json
keys
at
the
most
basic
form
define
whether
or
not
you
are
currently
allowed
to
get
through
the
captive
portal
permitted.
It's
a
boolean,
a
HVAC
key,
which
we
are
going
to
help
discuss
a
little
bit
more,
which
allows
us
to
hopefully
authenticate
other
items
in
the
captive
portal
interaction.
It
has
the
user
portal
URL,
which
defines
here's
the
user
facing
a
website
which
you
can
go
to
to
actually
do
your
normal
interaction
and
it
may
be
the
same
server
as
what
you
have.
F
It
may
be
a
different
one,
the
expiry
date,
which
is
an
optional
field,
our
best
guess
of
when
this
captive
portal
will
close
on
you
and
the
bytes
remaining,
which
is
essentially,
if
the
bytes
driven
rather
than
time,
driven
form
of
the
same
thing
as
the
last
of
when
you're
going
to
get
recap.
T'v
captivated.
F
So
that's
essentially
what
it
has
right
now,
fairly
straightforward,
just
kind
of
the
minimum
set
of
things
we
think
the
API
needs
to
have
it
slide,
please
all
right.
So
there
are
several
open
issues
on
the
github,
so
I
just
thought.
I'd
cover
them
here
and
maybe,
as
we
were,
going
through
them.
If
people
want
to
comment
on
them,
please
come
up
to
the
mic.
Is
there
we
can
kind
of
just
gnaw
on
them?
And
if
you
have
more
thoughts,
please
do
go
to
the
github
and
write
your
thoughts
and
comments
on
the
issues
there.
F
So
first
one
privacy
I
think
Martin
brought
this
one
up.
So
we
want
to
make
sure
that
the
pro
client
information,
such
as
the
HVAC
cave,
this
is
you
know,
is
not
being
stored
and
shared
caches.
If
we
have
some
proxy
and
stuff
going
on,
and
so
the
document
should
specify
that
respond
should
include
cache-control
private,
to
say
you
know,
don't
just
cash.
This
chase
on
information
everywhere.
Do
people
think
this
is
the
right
way
to
do
it
I
think
it
sounds
fine.
Any
objections
that
we're
good
for
this
are.
C
Good
to
be
clear,
this
is
confidentiality
they
absorb
the
privacy
risk
here
would
be
related
to
the
captive
portal,
harvesting
user
information
or
something
along
those
lines
which
I
don't
think
we
to
kill
II
worried
about
I
mean
yes,
we
might
worry
about
that
at
some
point,
but
I'm
not
sure,
there's
anything
we
do
about
it.
This.
G
F
It
is,
admittedly
under
specified
as
of
right
now,
because
it
essentially
needs
to
refer
to
something
in
the
architecture
document
to
say
what
is
this
being
used
for?
How
is
this
being
used
between
the
various
things
last
time
at
the
last
moment,
we
were
talking
about
this
key
as
token
for
validating
ICMP
messages
such
that
ICMP
messages
could
use
this
key
in
some
manner
to
sign
that
hey
I
came
from
someone
who
has
the
same
authority
as
the
API
server
that
you
first
opened
with.
F
H
Kyle
Rose
I
mean
we're
not
sure.
Yet,
if
you're
even
going
to
have
ICMP-
and
if
that's
the
case,
do
we
still
need
HVAC
key,
potentially
not
but
I
mean.
Supposing
we
do
go
of
ICMP
I'm,
not
sure
that
the
API
should
be
specifically
sorry.
The
architecture
document
should
be
talking
about
the
specifics
of
the
API
I
think
it
should
still
be
general
talking
about
a
token
and
then
maybe
the
ICMP
draft,
presumably
and
the
API
draft
would
both
say.
F
Could
imagine
if
you
want
to
in
the
architecture
document
define
very
strongly.
There
is
a
notion
of
a
token
that
can
be
given
from
the
captor
for
law
enforcement
cluster
to
the
UE
to
to
validate
future
communications,
which
may
be
ICP,
which
may
be
other
things
that
come
up
down
the
line,
but
you
don't
see
how
we
get
it
or
how
it's
used.
Api
says
hey:
this
is
how
you
get
it
and
an
ICMP
document
says
this
is
how
it's
used.
C
So
then,
this
is
not
chair,
head
stuff,
I,
don't
know
the
there's
number
of
ways
we
can
cut
this
particular
one
because
it
sort
of
crosses
a
couple
documents.
One
option
would
be
to
if
we
were
to
decide
to
do
ICMP,
do
that
in
an
ICMP
specific
document
and
define
an
extension
to
this
document.
That
did
that.
That
means
we
get
this
document
out
of
out
of
the
critical
path
on
that
decision,
but
I'm
not
necessarily
sure,
that's
really
going
to
help
us
long
term,
because
we
have
the
architecture
thing
that
needs
to
addressed.
C
F
F
F
I
I
Like
a
Pepsi
bottle,
API
server
and
some
routers
devices
that
are
going
to
send
those
ICMP
messages
so
that
that's
pretty
for
later,
but
I
wanted
to
say
it
not
because
we
have
the
list.
You
know
about
the
complexity
of
the
of
the
standardization
of
that
solution.
Maybe
that's
a
hint
that
the
technical
solution
using
that
would
be
actually
complex
as
well.
That's
that's.
F
Fair
I
in
the
case
of
using
ICMP
in
the
most
basic
sense
of
just
saying,
hey,
you
were
blocked.
I,
see
that
as
a
useful
piece
of
architecture
and
anything
that's
doing
that
should
be
validated
I
could
imagine
we
could
end
up
going
some
other
way
than
ICMP,
but
as
long
as
we
have
some
interaction,
that's
not
directly
coming
from
this
client
initiated
connection
to
an
API
server
that
we
want
to
essentially
have
some
other
out-of-band
channel
for
saying,
oh,
you
did
something
wrong.
F
Anything
wouldn't
probably
need
to
be
validated,
and
so
we
could
find
other
uses
for
this
too.
Potentially
so
anyway.
You'll
have
that
discussion
later
next
slide.
Please
all
right,
surfer
authentication,
so
the
EPA
document
does
not
currently
but
needs
to
describe
the
server
authentication
model,
and
specifically,
it
was
brought
up
that
CR,
ELLs
and
OCSP
will
generally
fail
if
you're
captive,
unless
those
things
are
explicitly
whitelisted.
F
This
could
get
a
little
bit
complicated,
but
we
really
do
want
to
do
HTTPS,
so
it
was
brought
up
that
OCSP
stapling
does
avoid
the
issue
because
it
essentially
puts
the
burden
on
the
server
to
get
the
or
CSP
credentials
and
pass
them
through.
That
seems
to
be
pretty
clean
to
me
as
a
way
of
validating
this
authentication,
so
I
think
the
option
here
would
be
make
OCSP
stapling
mandatory.
As
part
of
this,
that
sounds
fine
to
me.
One
question
is:
what
do
we
do
if
that
stapling
is
not
present?
F
K
Brian
thanks
for
coming,
hey,
Ryan,
sleevee,
Google
so
and
I
was
looking
over
this
wondering
the
same
question.
One
potential
implication:
this
is
going
to
be
figuring
out
intermediates
and
you
know
obviously
TLS.
One
three
has
the
ability
to
staple
intermediates,
but
client
path
building
is
going
to
be
non-deterministic
based
on
their
trust.
K
K
K
F
K
L
L
L
Making
it
mandatory
I
looking
at
the
real
world
I
can't
imagine
that
the
implementers
will
will
agree
to
make
it
mandatory.
So,
like
sure,
though,
this
is
a
nice
idea
but
and
impossibly
even
if
you
want
to
make
something
mandatory,
you
might
mandates
that
implementers.
If
they
choose
to
ignore
the
stapling,
must
present
the
user.
A
message,
something
like
that.
F
C
C
Sorry,
yeah
try
again
one
of
the
things
that
might
happen
in
that
case.
Is
you
someone
there's
a
Mis
configuration
somewhere
and
there's
any
number
of
mr.
miss
configurations
that
are
possible
in
this
context,
and
one
of
them
might
be
that
you
are
actually
hitting
the
captive
portal
is
trying
to
intercept
your
communications,
and
that
suggests
that
you
need
to
go
probing
probing
again
at
that
point,
yeah
I.
N
Think
that
there's
two
different
issues
that
I
think
he
started
to
get
to
them,
which
are
what
do
we
do
if
we
can't
validate
the
certificate
at
all?
And
what
do
we
do
if
we
it's
can,
we
think,
validate
the
certificate
and
find
that
it's
invalid
and
I'm
not
sure
whether
those
should
we
should
any
of
this?
Those
two
cases
or
not,
there's
also
the
question
I
mean
given
the
number
of
sites
but
having
valid
certificates
or
are
not
signed
by
a
certificate
authority.
They
are
self
signed
or
other
things
like
that.
N
I,
don't
know
you
know
one
of
the
goals
and
security
I
think
here
is
to
make
it
no
worse
than
it
is
now.
I.
Also
think
one
of
the
goals
of
the
service
in
this
case
should
be
that
by
inserting
this
we
make
it
no
worse
than
it
is
now
you
know,
and
so
why
you
want
to
try
that
URL
and
just
try
to
log
in
like
we
do
now.
N
N
F
Think
we
can
distinguish
here
between
the
site
that
people,
essentially
users
directly
interact
with
and
this
other
channel,
which
is
more
of
a
system
level
communication
to
get
the
JSON
if
we
essentially
fall
back-
and
we
imagine
that
for
some
time
being
captive,
portals
still
deploy
the
old
I
redirect
you
model,
we
essentially
just
go
down
that
route
and
ignore
everything
that's
in
the
API
right.
So
we
allow
you
to
do
what
you
do
today,
but
we
don't
take
into
account
anything
that
may
have
been
inside
the
JSON.
That
would
say.
F
N
F
H
H
H
F
One
way
that
it
falls
out
is
that
if
people
are
using
a
validated
method
of
discovering
their
captive
portal
that
maybe,
rather
than
shaming
the
ones
they're
using
the
legacy
system,
we
just
kind
of
had
the
little
green
checkmark
or
like
hey.
We
have
a
secure
lock
on
this
new
portal,
which
we
didn't
have
previously.
We
about
to
start
shaming
people
who
don't.
O
There
should
type
of
develops,
so
one
reason
for
kind
of
trying
to
authenticate
right
is
to
at
least
give
an
indication
of
saying
that
there
might
be
a
man,
the
middle
kind
of
attack
right
if
somebody
is
actually
trying
to
do
sleeping
or
something
so
you
still
tell
the
using
you
are
connected
to
and
just
like.
Have
you
get
a
notification
right
now,
you're
connected
to
know
that
anybody
can
look
at
you
right
and
same
message
might
pop
up
in
this
case.
F
All
right,
very
good,
thank
you
for
the
discussion.
Everyone
I
think
we'll
move
on
to
the
next
issue:
Thank
You,
Martin,
right,
media
type.
It
was
brought
up
that,
rather
than
just
requesting
the
application
JSON,
we
should
have
a
specific
media
type
to
allow
better
versioning.
That
sounds
like
a
good
idea.
I
like
it
first
does
everything
that's
a
good
idea,
and
then
second
one
is
this
media
type?
What
should
we
define
it
as
a
bike
shed
warning
you
pick?
Okay,
if
we
decide
to
pick
something
and
if
you.
C
C
Pass
so
one
of
the
one
of
the
standard
problems
that
we
have
with
these,
these
sorts
of
API
is.
Is
that
you
go
to
them
and
there
has
a
particular
format
and
you
develop
expectations
about
those
sorts
of
things
you
can
with
HTTP
use
content
negotiation
to
get
different
media
types.
So
we
say
we
pick
the
first
one
on
this
list
right
now
and
later
on.
We
we
have
a
challenge
of
mind
and
want
to
make
a
backwardly
incompatible
change
to
the
format.
We
could
pick
the
second
one
and
Kaplan.
C
That
support
the
old
one,
which
would
send
nothing
or
would
send
except
the
first
one
and
clients,
addicts
that
accept
the
new
one,
would
send
the
accept
header
with
the
second
one
in
it,
and
the
server
could
use
that
information
to
provide
the
new
one
and
you
can
then
seamlessly
transition
from
one
of
the
other.
Okay.
N
C
F
I
didn't
find
this
approach
compelling
so
I
think
we'll
add
it
into
the
next
version,
all
right
next
slide.
Okay,
I'm,
just
gonna,
follow
up
to
discussion
that
we
had
them
list.
One
of
the
non
published
versions
of
this
was
playing
with
doing
a
well
known
inside
the
URI
that
was
discussed
to
be
an
inappropriate.
F
You
said
well
known,
I
just
wanted
to
discuss
here
with
the
group,
the
approach
that
we
haven't
of
essentially
making
sure
that
we're
getting
the
right
resource
from
this
URI
there's
severe
suggestions
made
about
link
relations,
specifying
also
that
the
UE
could
first
issue
just
ahead.
Requests
to
figure
out.
What's
there,
I
would
like
to
in
the
API
document,
be
a
little
bit
more
clear
about
how
we're
going
to
use
this
year.I
and
exactly
you
know
what
the
contract
is
for
when
we're
fetching
the
API
and
went
or
not.
F
I
Jeff,
you
saw
my
first
so
I
didn't
see.
The
discussion
on
the
mainland
is,
but
my
first
thought
would
be
that
what
the
situation
we
are
trying
to
get
away
from
is
having
to
send
probes
and
issues.
Something
like
that.
Well
known
that
sliced
JSON
API,
maybe
you
will
open
it
all
to
use
probes
again.
So
I
would
say
that
it's
better
if
you
must
have
a
way
to
discover
deterministically
the
the
captive
api
and
so
that
capture
API
can
be
using
any
alright.
So
you
cannot
just
guess
it.
That's.
F
Very
true,
so,
let's
you
have
to
get
it
from
DSP
are
a
PVD
RS
that
so
we
receive
this
information,
we
have
the
URI.
You
know
there
is
a
question
of
like
we
had
in
the
original
document.
This
URI
could
be
the
same
or
very
similar
to
the
one.
That's
actually
the
user-facing
landing
page,
potentially
there
only
differentiated
by
the
type
of
content
I'm
requesting,
maybe
they're
totally
different,
is
essentially
that
relationship
that
needs
to
be
very
clearly
specified,
and
so
it's.
C
Alright,
so
I'm
not
leaving
this
chair
but
I
do
have
a
question.
We
have
7710
and
we're
going
to
talk
about
that
in
a
little
bit
that
only
produces
one
URL.
That's
are
we
going
to
mandate
the
use
of
this
new
media
type
to
distinguish
between
clients
that
support
the
API
and
clients
that
are
ignorant
Lea
hitting
this
URL,
or
are
we
going
to
say
that
that
URL
in
7710
points
to
this
is.
F
Through
the
question
right,
so
if
we
do
get
to
the
7710
equivalent
or
the
theme
from
PVD
or
whatever,
is
that
always
like
if
I
don't
include
any
content
type?
Is
that
the
API-
and
it
just
tells
me
hey,
I'm
application
captive
JSON
or
do
I
specifically
have
to
ask
for
captive
JSON?
You
know
the
question.
O
So
my
my
opinion
on
this
one
is
maybe
what
we
should
do
is
that
if
we
can
say
that
if
the
7710
URI
is
a
HTML
and
just
should
on
a
recommendation
saying
if
you
are
doing
now,
if
you
have
the
cassava
last,
you
pointed
HTML
page
then
in
there.
If
I
do
a
get
on
that,
maybe
we
use
the
moon
creation
in
there
to
point
to
the
capture
photo.
I
C
F
P
C
C
J
C
O
O
I
P
C
P
What
am
I
doing
on
the
first
one
if
we're
doing
the
site,
that
7710
just
never
happened
and
we're
like
this
isn't
say?
If
now
always
this,
then
there's
no
point
in
using
any
negotiation
at
all.
There's
one.
Your
eye
is
the
API.
No
one's
ever
use
a
human
under
Inc
text.
That
would
also
be
very
clean.
F
F
C
C
C
When
you
connect
to
it,
so
that
would
be
helpful
there,
the
third
ones,
an
interesting
one.
7710
has
a
requirement
for
euro
le
the
URI
URL
to
contain
an
an
address
literal.
This
is
one
paragraph.
Just
you
know
do
this,
and
it
turns
out
that
runs
counter
to
the
discussion
we
had
previously
about
it
actually
authenticating
things
so
we'd
remove
that
and
there
might
be
some
other
things
but
I'm
not
aware
of
anything.
It's
actually
a
pretty
short
document
and
it's
pretty
hard
to
find
faults
in
the
document.
B
C
R
Many
were
there
a
four
of
them-
oh
my
god,
so
yeah,
one
kumari.
Sorry,
one
of
the
original
authors
of
this
so
under
this
state
said
that
I
thought
two
was
a
bad
idea
and
then
somebody
replied,
and
it
now
seems
like
a
good
idea,
but
I
forgot
to
mention
that
so
yeah,
where
I
said
that's
a
bad
idea,
I'm,
sorry
and
then
for
number.
Three
I
think
that
the
addressed
literal
requirements
was
one
of
those
things
that
was
put
in
because
we
kind
of
had
to
with
the
assumption
that
nobody
would
ever
do
it.
R
That
was
one
of
those
yeah.
I
know
I,
know
yeah.
Somebody
asked
for
it,
but
we
didn't
think
it
would
actually
in
the
real
world,
be
used
that
way.
I
know
yeah
somebody
they
couldn't
do
anything
else,
but
you
know
so
we
stuck
it
in
with
the
assumption
that
most
sane
people
would
put
in
non
address
literal
URLs,
so
yeah
I'm,
sorry
it
all
sucks.
That's.
D
I
So
if
you
sell
again
as
a
PDF
thought
again
obviously
trying
to
push
my
stuff
I
just
want
you
to
understand
if
there
is,
if
it's
either,
that
all
the
PBE
or
if
there
any
scenario
where
both
are
in
the
question,
my
question
is
as
well,
so
the
PvE
option
no
has
an
option.
Number
it's
showing
good
progress.
Do
you
want
to
go
that
way
or
try
to
piggyback
what
we
are
doing,
which
seems
for
me
at
least
you
have
a
good
traction
and
could
be
a
I
mean
I.
S
If
there's
no
captive
portal,
that
nothing
should
be
broadcasted
and
included
in
the
options
and
also
if
we
I
think
that
I
Triple
E,
you
have
an
eight
eight
eight
zero
to
Dottie,
we're
being
you
has
some
kind
of
option
that
tells
that
I
verify
client.
That's
they
have
this
network
is
a
restricted
or
this
network
is
open.
So
we
haven't
as
a
choice
to
tell
that
this
network
is
not
not
no
captive,
poker.
I
thought
I,
don't
think
that
option
tears
should
be
included.
So
hello.
F
S
H
H
F
Totally
Polly
Apple
right
just
try
me
and
that
I
think
it's
we
want
to
do
something.
That's
beyond
just
Wi-Fi
we're
on
do
something
that
is
at
kind
of
layer
three
and
up
in
this
case.
As
far
as
the
main
portal,
even
in
the
Wi-Fi
case.
As
far
as
I'm
aware,
you
can
indicate
that
there
is
blocking,
but
there's
no
explicit
indication
that
there's
not,
and
so
as
a
you,
a
developer.
F
Well
thinking
about
7710,
because
people
can
look
at
this
today,
I
think
we
should
update
it
or
visit
or
something
just
to
point
people
to
whatever
we're
now
thinking
and
how
this
is
going
to
play
with
the
overall
architecture.
It
essentially
could
become
the
captive
portal
discovery
draft
part
of
the
architecture.
I
would
not
I
I
would
love
to
see
the
Peabody
stuff
be
used
here.
I
can
also
see
a
very
strong
reason
not
to
tie
the
fate
of
deploying
any
captive
portal.
F
T
F
One
document
that
updates
this,
which
is
like
here's,
how
you
do
discovery
I've,
kept
a
photo
thin.
Here's
how
you
interpret
it
when
it's
just
directly
in
DHCP,
and
it
could
also
be
inside
an
already
extension
called
a
PVD
that
gives
you
this
other
data.
So
like
here's,
the
DHCP
and
Ra
based
ways
of
getting
this
to
your
eye,
and
it's.
C
Kind
of
one
story
there
so
now
I
have
to
ask
the
question
how
how
how
close?
How
were
you
getting
that
PVD
doc,
because
this
could
be
done
theoretically
in
months,
if
not
weeks
with
basically
lost
calls
and
whatnot?
We
could
do
this
reasonably
quickly,
and
could
we
couldn't
do
the
same
affinity
was
in
that
makes
could
be
I.
Don't.
I
T
C
E
T
C
T
T
T
N
Don't
object
to
any,
but
I
think
you
know
original
before
this
version
of
the
API
there
had
been
a
mechanism
to
allow
it
to
be
both
and
I.
Don't
know
if
there's
a
desire
to
do
that
where,
when
you
just
do
a
get,
you
actually
get
the
login
page
and
we
were
doing
a
set
I
think
it
was
in
order
to
enter
into
the
API,
and
that
would
allow
it
to
be
both.
Not
you
figure
it
out
yourself.
So
I
guess
I'm,
saying,
there's
actually
a
fourth
option
as
well.
If.
C
H
Today's
be
just
the
reiterate
Mary
this
point:
you
know
the
word
I
know
we
trying
aren't
trying
to
solve.
The
IOT
is
as
color
as
I
know.
We
are
trying
to
solve
the
IOT
use
case,
but
our
Charter
does
hint
that
we
should
think
about
it
and
I
wouldn't
want
to
go
out
of
our
way
right
now
to
preclude
us
from
doing
an
IOT
solution
in
the
future.
C
Or
D
so
so
to
be
clear,
the
in
the
discussion
on
the
mailing
list-
I,
don't
know
who
it
was.
The
point
of
this
out
might
have
been
Adam
that
if
you
do
the
point
to
the
login
page,
you
can
still
make
a
head
request
to
that
one
as
an
IOT
device
harvest
the
link
relation
and
then
make
your
way
across
to
the
API.
It
just
takes
more
steps
and
more
code,
and
maybe
we
aren't
doing
the
IOT
folks
very
much
of
a
service
by
doing
so,
but
it's
still
possible
yeah.
So
one.
R
Kumari
I
mean
I,
kinda,
think
hey
for
B
or
C
or
D,
because
there
are
a
lot
of
people.
You
know
you
could
currently
deploy
this
in
point.
An
existing
capture
photos
not
the
ones
that
are
being
upgraded,
and
you
know
we
have
no
idea
if
there
will
be
API
is
deployed
on
them,
so
the
advantage
to
be,
and
then
you
know
you
could
fetch
something
from
that
point
to
the
API,
provides
you
some
backwards
compatibility
or
option
e.
F
Tell
me
kind
of
opposed
to
your
point,
so
I
agree
that
if
you
do
something
like
B
or
the
other
derivatives,
then
you
definitely
could
essentially
stay
with
the
existing
model
and
all
you've
added
is
a
way
to
not
probe
on
the
initial
thing.
That
makes
me
sad,
though,
is
that
we
essentially
don't
get
any
of
the
other
benefits
that
we
could
imagine
with
this,
and
it
actually
kind
of
harms
the
deployment
of
something
that
we
well
potentially.
If
we're
talking
to
something
that
is
over
htps,
that
gets
us.
F
Of
this
really
becomes
people
just
ignoring
all
the
other
documents
other
than
a
way
to
find
your
landing
page.
I
could
see
that
as
regards
to
kind
of
what
we
had
in
the
original
API
raft,
what
Margaret
was
bringing
up
I
think
I
was
trying
to
go
for
a
little
bit
simpler
approach
here,
rather
than
having
kind
of
like
the
multi-step.
F
It's
a
lot
more
straightforward.
If
we
just
have
oh
I
just
do
again,
and
this
is
the
one
thing
that
this
URI
means,
and
it
is
a
little
bit
optimistic,
hoping
that
someday
we
can
get
to
a
point
where
we
don't
necessarily
need
any
user
facing
web
portal
that
we
have
today
and
so
baking.
This
into
mean
that
oh
yeah,
that
login
page
is
the
thing
that
you
get
with
the
get
means
that,
if,
in
the
future
we
don't
have
that
page,
do
what
do
you
have?
What
do
you
get
in
response
to
that?
N
O
Think
it's
a
personal
preference
I
think
I
would
say
like
II.
But
my
comment
is
the
same
thing
as
what
you
mentioned
earlier
is.
We
are
not
sure
that,
like
there
is
no
deployment
of
7071
by
while
we're
discussing
somebody
else
by
deployed
so
I'm
not
sure
how
we
can
really
actually
say
it's
just
going
to
be
a
API
when
somebody
and
then
you
actually
breaking
things
right,
because
the
client
is
expecting
Jason
dark
and
then
it
gets
a
mess
here
and
it
goes
blah
right.
So
yeah.
S
Yeah
I
believe
isn't
working
that
idea,
because
the
currently
there
is
very
limited
deployment
with
a
seventy
to
seventy
seven,
seventy,
seven,
ten,
so
yeah
and
also
we
made
we
met.
We
might
consider
the
vacancy
between
the
API
a
captive
portal
and
the
client
because,
like
especially
in
the
virus
type
the
cap,
that
there
is
some
vacancy,
we
can
reduce
communication
between
the
API
and
the
API
and
user
agent
user.
You
a
user
equipment,
so
my
opinion
is
be
alright.
R
O
So
the
other
option
just
tells
whether
so,
if
you
have
another
option,
also
right,
then
we
tell
you,
maybe
that's
the
same,
that
whether
it's
JSON
all
option
so
then
I
get
the
URL
from
7710
like
I
get
the
other
thing
that
tells
me
whether
it's
a
JSON
or
an
HTML.
If
there
other
thing
doing
show,
I
can
just
assume
it's
a
nasty
ml
page
all.
H
C
C
Don't
think
we're
going
to
get
a
real
sense
of
where
we're
at
I
think
we'll
take
this
to
the
list
and
try
to
come
to
some
conclusion.
There
I
got
a
sense
that
we
have
roughly
and
even
split
between
those
people
who
would
like
to
do
the
just
just
the
API
and
those
people,
maybe
a
little
bit
concerned
about.
Maybe
maybe
there
is
some
use
out
there
and
maybe
sort
of
retconning.
This
whole
thing
might
not
be
a
good
idea,
so
we.
P
Almost
know
again,
we'll
cook,
if
I
could
so
then
warns
that
actually
I
think
was
suddenly
different
than
that
and
in
a
very
important
way,
which
is
not
that
there's
like
currently
deployed
stuff
out
there.
It
doesn't
turn
on
that.
It
turns
on
whether
there
might
be
deployments
of
this
with
new
dhcp
new
client
portal,
and
that
was
a
combination.
I
don't
think
we
have
considered
before,
and
I
think
it
actually
is
relevant
it's
that
was
it's
after.
P
U
Thank
you
very
much
hope
Loffler.
When
we're
old,
77
ten
bits,
we
would
just
only
go
up
a
trial
balloon
its
assad
that
I
was
taking
this
long
to
get
to
abyss.
If
what
I
would
like
is
if
I
go
into
as
a
user
go
into
a
portal,
is
I
have
been
able
to
tell
my
computer
negotiate
if
the
policies
are
bra,
so
I
don't
want
to
see
another
cap
default
page
ever
unless
they
want
my
payment
or
they
want
to
steal
all
my
information,
so
API
is
where
we
should
be
going.
U
C
All
right,
so
the
last
question
was:
does:
does
anyone
want
to
stick
their
hand
out
for
this
one?
What
Warren's
already
done
that
anyway?
If
you
can
unstick
your
hand,
it
seems
like
there
is
the
potential
for
some
more
work
than
this
would
imply,
which
makes
me
a
little
sad
but
nonetheless,
so
maybe
what
we'll
do
is
we?
We
will
resolve
that
question
and
then
try
to
now
someone
to
the
wall
for
this
particular
one.
So
so.
M
F
Tommy
parley
Apple
I'm
happy
to
help
work
on
this.
Whichever
way
we
end
up
going
as
far
as
scheduled,
I
appreciate
that
we
do
want
to
get
this
done
quickly,
because
it
should
be
short.
However,
especially
if
this
is
pointing
to
things
like
the
API
etc,
it
does
seem
like
it
should
be
aligned
with
the
other
documents.
These
it'll
be
a
lot
stronger.
If
you
can
point
to
those,
so
I
mean,
were
you
thinking
that
this
would
actually
come
before
other
documents
end
up
getting
pushed
so
one
of
the.
C
C
H
Hello,
unarmed,
caller,
Oz
and
I'll
be
talking
about
some
updates.
We've
made
to
the
character
board
architecture
since
Singapore
next
slide.
Please
alright!
So,
as
Martin
nicely
pointed
out,
I
missed
the
deadline
to
upload.
However
I
have
uploaded
it
since
then,
so
if
you've
managed
to
look
at
it
in
the
last
few
days,
it's
great
the
editors
copy
I
mentioned
I
mean
unless.
H
But
it
is
what
it
is
all
right.
So,
let's
change
to
major
things.
Changed
first
I
tried
to
make
the
Security
section
relating
to
the
guys
old,
stronger
and
then
I
added
a
very
large
section,
which
attempted
to
summarize
the
majority
of
the
discussion
we
had
in
Singapore
and
what
user
Equipment
Identity
and
then.
Finally,
on
lists
and
github
we've
been
discussing
quite
a
few
issues
related
to
the
architecture
and
also
go
over
these
during
the
presentation
here
next
slide.
H
Alright,
so
security
of
the
API
I've
kept
this
pretty
short.
I
basically
mentioned
that
the
privacy
and
integrity
of
the
information
exchange
with
the
API
is
a
must.
We
must
use
TLS,
I
didn't
specify
HTTPS
so
because
I
wasn't
sure
we
wanted
to
get
into
HTTP
versus
other
applications,
but
I
left
it
at
that.
H
H
H
H
In
particular,
we
have
two
distinct
components:
the
VI
server
and
the
enforcement
device
that
need
to
act
on
the
identity
to
use
equipment
devices
that
decide
whether
or
not
the
packet
needs
to
be
allowed
through,
based
on
where
the
packet
came
from,
who
belongs
to
essentially,
and
the
API
server
needs
to
be
able
to
tell
the
equipment
whether
or
not
it
is
blocked,
as
well
as
interact
with
user
equipment
to
tell
it
to
allow
the
the
packets
through
so
the
enforcement
device.
So
how
do
we
do
that?
H
Well,
we
discussed
it
and
I've
tried
to
capture
some
of
the
thoughts
we
had,
in
particular
I,
think
from
the
mailing
list
and
from
those
discussions
that
there's
some
requirements
on
the
identity
that
need
to
be
met.
In
order
for
this
to
work,
and
so
I
try
to
capture
those
in
particular
that
if
I
should
be
unique,
so
only
one
person
or
equipment,
it's
a
little
vague
there.
But
basically
one
thing:
that's
allowed
the
device
at
the
time
can
have
the
identifier,
otherwise
things
might
not
work.
She
had
to
spoof.
H
H
Why
is
the
enforcement
device
needs
to
be
able
to
infer
than
get
it
and
I
didn't
mention
here
on
land
of
action
forgot
to
mention
in
the
architecture,
but
they
also
need
to
agree
on
the
identity,
so
the
API
can
think
the
identity
is
a
source
ID
and
the
person
device
can
think
it's
MAC
address
and
that's
not
very
useful
unless
they
have
some
way
of
correlating
it
to
you
together.
So
I
should
make
that
if
I
haven't
I
need
to
make
that
clear.
So
it's
probably
an
issue
with
the
document
right
now.
H
Next
slide,
please
so
beyond,
actually
specifying
what
I
think
what
we
should
think
the
identity
should,
but
probably
that
any
should
have
I
talked
about.
I
didn't
want
to
get
into
suggesting
a
specific,
because
I
I
think
that
different
deployments,
different
networks
are
going
to
have
different
requirements
and
those
requirements
might
preclude
you
from
using
a
particular
identity
over
another,
and
so
I
gave
some
recommendations
on
how
to
actually
evaluate
to
the
identity
our
potential
identity
against
another,
so
that
you
can
choose
the
best
possible
one,
and
then
I
gave
two
examples.
H
I
gave
the
physical
interface
to
which
the
device
is
attached
as
a
possible
identity
and
I
have
the
IP
address.
Local
device
is
another
possible
identity
and
then
I
evaluated
them.
So
much
now,
when
I
talk
about
these
two
examples
here,
because
I
had
a
bunch
of
discussions
with
people
this
week
and
I
also
worked
on
this
jacket
on
a
bit.
H
I'll
start
the
IP
address.
So
we
e
IP
address
it's
nice
because
it
should
you
need
to
identify
these
equipment,
or
maybe
you
know
if
you're,
behind
an
ad
or
something
inside
I
mean
it's
okay.
But
it's
pretty
easy
to
smooth,
so
what
you
need
is
you
need
some
way
of
the
network
and
foreseen
that
only
one
user
has
an
IP
address
at
a
time,
and
not
only
that,
but
if
the
ownership
of
the
IP
address
changes,
maybe
notifying
the
enforcement
device
and
the
API
server
that
that
has
changed,
so
they
can
invalidate
their
records.
H
You
had
the
section
of
the
enforcement
on
link
with
the
user
equipment,
and
then
you
had
upstream
with
the
enforcement
of
ice,
the
enforcement
device
was
doing
the
couch
for
mortal,
and
that
made
me
think
that
mainly
and
Erica
textured,
we
should
be
splitting
enforcement
in
the
two
modular
components,
a
component
that
is
responsible
for
ensuring
the
uniqueness,
validity,
etc
of
the
identifier
on
link,
and
then
the
actual
enforcement
device
is
responsible
for
doing
deciding
whether
or
not
to
allow
the
packet
outside
to
the
external
Network
and
what
pretty?
Well
what
I
did?
H
H
I
was
talking
to
Pierre
about
this,
and
you
know
this
bit
this
like
we're
saying
you
know.
Well,
if
you
just
if
you
can
communicate
the
physical
interface
to
which
the
device
is
attached,
all
the
way
up
to
the
other
point,
I'd
be
a
personal
device
it
doesn't
is.
It
doesn't
actually
have
to
be
on
link,
it's
possible
that
you
use
a
tunnel
to
make
it
super
Wan
link,
or
maybe
you
tagged
the
packet
somehow
with
maybe
so,
every
six
or
something
to
indicate
the
the
origin
of
the
packet
in
the
network.
H
I
Esther
I
just
wanted
to
mention
one
aspects
that
is
that
you
didn't
mention
is
that
the
user
equipment
identifier
doesn't
need
to
be
known
by
the
device
itself.
It's
something
that
is
decided
by
the
by
the
network,
and
we
just
did
that
to
be
a
thing
that
the
EAP
or
the
wireless
controller
or
the
the
first
switch
or
the
first
water
is
able
to
to
know,
and,
as
you
mentioned
then,
which
receives
a
packet
tag.
I
H
C
H
C
J
H
J
I
mean
that
that's
something
you
could
you
could
go
different
directions
of.
That
I
mean
if,
if,
if
we
actually
think
like
people
will
follow
like
a
fairly
specific
recommendation,
then
maybe
we
should
be
specifically
providing.
This
is
how
you
insulate
some
identifiers
so
that
it's
different
when
users
connect
to
different
portals.
I
J
C
Of
that
information
is
certainly
important.
I
would
like
to
so
so
for
background
on
Finnick.
The
part
of
the
point
of
this
is
is
how
does
this
particular
network?
Think
of
this
particular
user
equipment?
And
yes,
we
don't
want
that
identifier
escaping
that
their
network
and
part
of
part
of
that
I
think
is
making
sure
that
the
user
equipment
doesn't
actually
know
what's
how
it's
being
identified
to
so
then
it's
not
propagating
that
identifier
through
the
network
in
indirectly.
C
So,
for
instance,
if
you
had
a
situation
where
you
you
went
from
there
portal
and
the
URI
of
that
portal
contained
the
identity,
I
can
contain
the
identifier,
then
you
know
suddenly
sprang
referrer
headers
all
over
the
Internet
as
a
result
of
those
those
interactions.
They
have
to
be
real
hit.
Be
careful
about
that
sort
of
thing,
but
IP
address
is
really
something
you
just
you
just
can't
avoid
having
sprite
all
over
the
Internet
in
you
know,
Internet
as
we
know
it
yeah.
I
I
To
answer
your
question
whether
this
should
whether
the
architectural,
even
the
working
group,
should
specify
a
specific
tip,
I
think
not
because
this
is
really
specific
to
the
type
of
link
the
device
is
attached
to
so
I
think
the
this
could
be
many
different
things
and
even
for
one
capture
photo.
If
that
Porter
is
providing
a
service
to
Wi-Fi
link,
my
link
might
be
to
use
different
identifiers
I.
J
Oh,
you
have
to
login
on
Facebook
and
and
posa
so
like
where
there
are
definitely
options
that
are
like
on
the
internet
through
a
particular
social
network
before
so
I'm
concerned
that,
like
we
would
need
to
specify
kind
of
directly
what
what
the
woman's
on
an
identifier
is,
because
just
saying,
oh
well,
the
enforcement
point
one
take
care
of
it
or
the
like
that
and
enforcement
point.
They,
like
might
already
be
too
late.
At
that
point,
you
know.
M
H
I,
just
you
know
if
you
were
select
here,
I'm
just
going
over
the
open
issues
that
we
have
so
we've
discussed
a
few
we're
discussing
here
and
we
discussed
a
few
elsewhere,
so
we
can
produce
go
through
the
next
few
slides
next
slide,
something
that
was
raised
in
in
a
github,
repo
and
I.
Don't
know
why
he
decided
to
do
it
but
there's
a
question:
does
he
give
the
state
of
your
captivity
the
API
or
both
I?
H
I
The
beauty
draft
again
and
I,
don't
think
kind
of
yeah
I
think
it
cannot
leave
the
state.
It
cannot
give
the
state
it's
not
designed
for
that
purpose,
to
do
something
instead
designed
to
get
something
that
depends
on
the
user.
It's
not
designed
to
give
something
that
is
private,
and
it's
not
designed
to
give
something
that
changes
all
the
time.
Okay,
so
it
can
give
the
API
that's
really
clear,
but
not
the
state.
So.
C
Like
it
is
pretend
to
be
alone
well,
no
check
would
tell
me
whether
he
has
an
objection
to
that,
but
I've
recorded
that
the
three
points
that
you
made
that
it's
not
very
good
at
dynamic
things:
it's
not
very
good
at
user
things
and
it's
not
very
good
at
confidentiality.
So
maybe
it's
not
a
little
exactly
the
thing
we're
looking
for
so
we'll
see
what.
H
H
H
H
So
we
have
something
we
can
do
here.
Do
we
go
with
ICMP
at
all
and
if
we
do
which
of
the
two
mechanisms
do
we
use
a
simple
one
of
the
more
complex
one
where
you
have
a
lot
more
flexibility
and
how
you
signal
the
user
equipment,
or
do
we
just
say
no
ICP
is
out?
Are
these
for
now?
I
would
personally
prefer
to
have
some
ICP
mechanism,
because
I
think
it
is.
It
is
nice
for
cases
like
where
you're
not
necessarily
denying
all
it's
not
an
all-or-nothing
type
of
captive
portal.
O
C
R
H
C
J
You
know
it'd
be
really
nice
if
I
knew
that
I
was
gonna,
be
locked
down
before
I
get
locked
down.
You
know
because
that's
like
to
me,
the
only
literally
the
the
thing,
that's
the
most
important
that
we
can't
do
today
and
that
we
need
a
way
to
do
is
like
to
log
in,
and
we
up
your
re-up
your
time
before
it
expires.
J
It's
like
you
know,
because
everything
else
you
know
302s
work
right
like
stupid,
plain
text
here
to
work
for
everything
else,
but
not
for
this
and
so
I,
don't
think
the
ICMP
messages
is
particularly
useful.
I
think
it's
basically
security
wise
is
very
difficult,
but
but
I
think.
Most
importantly,
like
you
know,
we
want
something
to
tell
us
in
advance
and
I
think
if
we,
if
we're
gonna,
have
an
API
anyway,
then
this
is
kind
of
useless
one.
H
Day
it
helps
you
with
is
where
you
are
doing.
For
some
reason:
there
is
a
problem
in
the
network
and
you
or
or
the
captive,
or
maybe
you
hate
this
even
more.
The
captain
walls
decided
that
you
are
not
to
go
here
right
now,
because
there's
not
in
the
walled
garden.
That's
fine
destination
unreachable!
That's
what
that's
for.
H
V
N
Wondering
it
would
have
obviously
IC
and
PL
together
there
are
going
to
be
times
when
a
destination
is
unreachable
and
so
you're
going
to
get
a
destination
unreachable,
and
you
need
to
know
what
to
do
and
what
you
do
when
you
get
a
destination
unreachable.
Is
you
stop
trying
to
go
to
it?
Okay,
and
if
you
do
something
else
with
the
destination
that
you're
going
to
start
screwing
up
what
this
I
mean,
we
don't
screw
up
what
basic
networking
stuff
is
already
for.
N
H
T
N
T
N
You
have
to
expect
that
99.9%
of
those
for
a
long
time,
I'm
not
going
to
implement
this
and
they're
going
to
get
a
destination
unreachable
with
a
code
they
don't
understand
and
before
you
do
anything
at
all,
you
need
to
understand
what
they
do
at
that
point
and
whether
that
is
what
you
wanted
them
to
be
doing
and
I
I'm
guessing,
probably
not,
but
we
could
talk
about
that.
So
it's
what.
B
N
N
Of
each
of
us
are
cached
with
IP
level,
and
what
you're
really
wanting
is
the
UI
from
the
nodes
throughout
that
right
now,
the
user
needs
to
figure
out
what
his
time
has
expired
and
go
back
into
web
browser
and
hook
back
up
and
I'm,
not
sure
they're
sending
a
destination
unreachable
is
for
them.
The.
H
H
N
The
99%
of
No
we've
never
read
this
document
like
the
implementers
another
word
lease
document
or
the
OT
out
there.
What
are
they
going
to
do
right,
they're,
going
to
cash
it
that
this
nation
is
unreachable
when
I
try
to
go
into
the
web
browser
to
get
to
it
to
renegotiate
and
I
need
it
to
get
to
it.
N
H
Started
that
way
as
well
like
if
you're
talking
about
the
case,
where
it's
not
all
or
nothing,
it's
you
know
which
one
is
bad.
How
does
the
user
know
which
one
is
bad
and
one
thing
is
I
thought
maybe
be
used
it?
The
Forsman
device
could
signal
the
API
server,
somehow
immunising
awful
races
there.
It
does
seem
a
little
complicated
so.
R
One
Kumari
I
have
some
sort
of
background
on
this
or
some
of
Margaret's
questions
so
I
mean
it
could
be
that
if
you
only
have
access
to
certain
sets
of
things
because
you're
in
the
world
garden,
you
will
try
and
reach
outside
the
walled
garden
and
you
will
get
back
a
normal
ICMP
reachable,
which
is
normal
device,
would
treat
this
unreachable.
However,
it
would
also
have
an
extension
so
that
it
could
provide
information
to
the
user.
You
know
in
their
web
browser
or
whatever,
and
so
just
be
like
you
can't
get
there.
R
You
can't
get
there
because
something
something
captured,
port
or
a
hand
wave
hand
wave
and
are
actually
supporting
this
interest.
You
know
the
background
and
then
there
was
also
some
other
discussion
on.
You
could
use
a
different
ICMP
type,
just
as
a
signal
to
you
should
probably
come
back
soon,
because
your
time
is
about
to
expire.
Not
your
time
has
already
expired,
so
more
of
just
a
sort
of
notify
type
mechanism,
just
some
background.
T
T
H
T
C
O
H
G
G
J
J
J
So
it
was
being
discussed
over
the
weekend
that,
like
there
are
some
HTTP
451
cases
where
someone
else
along
the
way
is
interfering,
but
we
and
some
people
might
say:
oh
well
but
perfect,
you
can
use
HTTP
451,
except
that
means
you
have
to
impersonate
the
end
server
and
and
obviously
we
don't
want
to
tell
people
to
do
that.
So
I'm
just
curious.
If
we
like
and
then
maybe
it
is,
I
need
to
look
more
at
icmp,
but
and
if
we
can
have
a
code
saying
you
can't
get
to
this
so.
E
S
Just
a
quick
comment:
I
am
currently
I
could
on
the
considering
the
network
deployment.
So
I
could
send
a
are.
That's
my
speed,
just
poking
ICMP,
an
entire
ICMP
packet,
so
I,
don't
think
that
we
have
another
extension
to
ICMP
I.
Think
it's
a
little
bit
hard
to
deploy
because,
like
I,
we
have
a
API
server,
api
server
and
a
new
client,
but
the
middle
network
is
like
old
network
in
this
case
like
if
even
the
Internet
has
a
new
extension.
But
you
know
switches,
all
those
things
may
block
the
pockets
I.
H
Guess
there's
a
question
of
you
know
how
much
control,
how
far
away
if
he
is
the
enforcement
device,
if
the
operator
had
if
whoever's
operating
the
captive
portal
has
full
control
of
the
entire
network
and
it's
not
too
complex
for
them
to
change
it.
To
support
this
sure.
But
it's
a
good
point:
I
mean
having
to
enable
either
a
specific
ICMP
message
or
or
allow
all
I
see
the
message
or
something
might
be
cumbersome
to
some
operators.
H
S
I
That
this
message
could
be
hard
to
operate
and
also
opportunity
to
make
as
Margot
mentioned.
This
is
this,
if
it
exists,
would
be
a
new
thing
that
would
be
implemented
by
hosts
alongside
the
API,
so
I
think
for
now.
The
answer
is
that
we
shouldn't
do
that
and
try
to
solve
the
issues
we
find
using
the
API,
and
if
we
ever
fail
to
address
all
the
problems
with
the
API,
then
we
can
ask
ourselves:
do
we
need
a
new
tab
and
you
type
a
destination?
Unreachable
is
enough
so.
H
Going
in
maybe
you
know
for
thinking
among
one
possibility
to
keep
the
architecture
open
to.
This
is
to
mention
that
there
may
be
some
on
path,
signaling
that
doesn't
interfere
with
the
actual
HTTP
transactions,
real
customer
traffic
at
a
inappropriate
layer
and
just
leave
it
at
that
in
the
future.
We
got
more
but
yeah
as
far
as
the.
N
Think
that
if
I'm
you
try
to
out
to
somewhere,
you
can't
get
new
argument
like
we
get
it
well.
If
it
comes
all
the
way
back
to
you,
an
ICMP
destination
unreachable,
and
that
doesn't
tell
you
that
much
the
assumption
that
we're
going
to
figure
out
when
we
are
the
garden
from
that
it
just
doesn't
make
sense.
It
could
be
that
a
routers
down
we
have
a
temporary
routing
issue,
I.
Think
that
what
there's
good
ways
to
find
out.
N
You
know
a
garden
like
we
could
add
to
this
or
we
could
have
you
use
pvd's
and
you
get
you're
in
a
world
garden.
You
could
even
get
what
address
ranges.
You
can
reach
you
this
world
garden
or
some
other
information
that
tells
you
when
to
use
this
world
garden
and
when
to
use
another
interface.
If
you
have
one
and
that
right,
CMP
unreachable
is
not
really
going
to
tell
you
you're
in
a
walled
garden,
it's
it's
having
stuff
happen
where
you
try
to
go
to
a
website
when
you
get
a
death
station.
N
Unreachable
just
seems
wrong
to
me
I
just
like,
because
they
may
there's
a
lot
of
times
when
you
give
the
destination
unreachable
and
that's
not
what
you
want
to
do,
and
so
I'm
I'm
concerned
about
that.
And
yes,
you
could
say
the
only
if
you
go
destination
of
each
word,
this
option
in
it
and
the
HVAC
matches
this
and
all
that
but
you're
kind
of
taking
ICMP
out
of
what
it's
supposed
to
do
at
that
point,
because
you're
you're
doing
using
it
as
a
signaling
protocol.
F
Kind
of
do
like
the
ICMP
model
for
at
least
letting
you
know
that
something
has
closed
on
me
because
I
they
said
well,
we
have
right
now
the
API
can
indicate
to
you
if
you
grab
it
once.
Oh
here's
your
expected
lifetime
in
time.
Here's
our
expected
lifetime
in
bites
the
Yui
estimating
the
number
of
bites
it
is
sent
is
not
necessarily
deterministic.
It's
going
to
be
wrong
right
like
so.
F
You
know
what
happens
if
I
think
I
have
more
life
time
left
on
my
portal,
unless
we're
mandating
that
you
have
a
long-lived
push
connection
to
your
API
server
at
all
times,
which
sounds
Ruby
fraught
go
that
direction.
If
we
wanted
to.
Essentially
what
happens
is
like
do
we?
We
should
recommend
some
behavior
when
the
captive
portal
closes.
F
Is
it
just
redirecting
us
like
it
is
today
because
I'd
like
to
get
away
from
that,
and
so
some
rejections,
maybe
sorry
I
assume
he
maybe
is
the
your
captive
HTTP
error
or
something
else,
but
that
only
works
our
HTTP.
So
there
are
some
benefits
to
I
simpiy
here
and
just
just
for
that
model,
not
signaling
your
anawalt
go
to
now.
Your
captive
now,
but
you
already
knew
you
were
captive
and
it.
H
Closed
that
raises
something
in
my
mind
that
dear
bird
I
mentioned
a
while
back
I
mean
if
you
wanted
me
on
mr.
personally,
but
the
enforcement
device
is
ultimately
the
truth
for
whether
or
not
attack
can
make
the
network
and
if
something
happens
or
maybe
crash,
maybe
it
rebooted.
Maybe
someone
pulled
the
cable
or
something
things
are
bad
and
the
API
might
not
know
I
mean,
which
might
that
raise
a
whole
other
series
of
concerns.
What.
N
H
F
Sorry,
yeah
I
would
argue
that
we
do
require
that
a
signal
protocol,
but
some
specified
behavior
for
what
happens
when
your
portal
is
closed,
what
happens
to
your
traffic?
You
could
say
there
is
no
signal
portal
and
you're
just
left
out
in
the
dark
and
no
I
just
have
a
black
hole,
but
that's
not
ideal.
G
Okay,
it
actually
so
changing
the
definition
of
destination
unreachable.
If
you'd
say
that
okay
you're,
you
know
you
know
captive
portal-
decided
decide
to
talk
you
now
it
is
destination
unreachable.
Yes,
we
should
probably
had
a
new
sock
over
there
like
we
have
already
multiple
of
those
we
have
15
bit
selves.
You
know
five
thousand
the
original
RFC
and
then
we
have.
You
know,
fight,
wanna,
fight,
more.
I
G
Could
add
a
new
one
as
I
said,
most
of
those
are
going
to
be
processed
by
the
client
exactly
same
way
that
they
do
everything
else,
except
fragmentation
needed,
which
is
step
one
a
special
case.
That
is
also
there,
but
I
mean
it's
it's
not
it's
not
overloading
that
because
we
are
still
working
the
device
and
the
source
address
of
that
ICMP
is
going
to
be.
The
enforcement
device,
so
actually
know
a
little
bit
where
it
is,
but
it
doesn't,
it
doesn't
have
to
know
it.
G
N
Maybe
I'm
misunderstanding
something,
but
I
thought
I
heard
we
use
destination,
which
reachable
so
I
add
a
field
to
them
to
contain
the
HVAC
that
gets
checked
to
determine
whether
or
not
to
do
certain
things
which
is
defining
destination
unreachable
differently,
and
you
also-
and
you
just
have
to
make
sure
there
are
many
uses
of
destination
unreachable,
for
instance,
a
correspondent
node
if
it
receives
steps,
decks,
persistent
definite
destination
unreachable
well,
as
soon
as
the
mobile
node
might
have
moved
to
the
mask.
Is
that
going
to
you
know
really
cause
any
problems
for
that?
I.
N
N
I
So,
as
I
think
your
argument,
your
points
about
the
fact
that
the
enforcement
points
and
the
API
server
might
be
out
of
think
of
out
of
sync
is
very
good.
So
what
about
something
that
would
basically
tell
the
hosts
something
went
wrong.
You
should
probably
check
out
the
API
server
now,
instead
of
doing
something
that
is
going
to
mess
really
hard
with
the
IP
layer.
Just
do
something
just
a
message
that
tells
you
yeah
III,
don't
you
should
you
should
know
your
captain
and
you
should
check
the
API.
H
G
I
want
to
be,
as
it
is
now,
it's
different,
adding
a
new
fields
there
for
him,
and
his
map
is
completely
out
of
the
question.
I
think
that's
that's
but
I'm
using
the
icpsr
hint
to
say
that
okay,
now
there's
something
wrong
with
the
network.
I
need
to
do
something
for
everyone,
but
I
didn't
IPSec
in
mobike.
If
you
get
an
ICMP
on
host
unreachable,
we
started
okay,
that's
for
fake
or
it
might
be
blocked.
Let's
try
with
right
level
pocket
and
see
if
the
other
one
is
right.
Oh
he's
alive
that
was
fake.
G
Oh
he
I
cannot
get
Englishness
back.
Okay,
I
promise!
You
try
some
mother
out.
Oh
I
found
this
right.
It
works
so
the
ice
amp
is
always
a
hint
there,
and
here
we
can
do
the
same
thing
because
usually
ICMP
under
this
nation
hundred
distillation
unreachable.
Because
of
the
communication,
probably
by
which
the
reasons
that's
really
in
telling
okay,
it
might
be
from
the
captive
football
telling
us
telling
something
using
the
API
what's
going
on
and
that's
that's
just
a
hint
and
there's
no
point
of
you
know
really
try
you
do
all
navigate
it.
G
H
C
Right
so
I
want
to
give
people
to
concentrate
on
the
question
or
when
we
have
it.
I
have
a
signal
here,
rather
than
talk
about
designing
solutions
and
I
know
that's
appealing
to
stand
at
the
microphone
and
spitball
new
ideas,
but
the
question
of
whether
we
want
a
signal
or
not
cus
away
a
lot
of
things
very
simply
if
we
can
decide
not
and
if
we
decide
that
we
need
one.
C
F
F
We
should
clearly
specify
that
if
you
do
use
this
as
a
hint,
if
something
goes
wrong
as
a
hint
make
sure
that
that
is
somehow
rate
limited
that
you're
not
turning
this
into
an
attack
on
the
API
server
dadada,
so
that
becomes
a
security
consideration,
but
beyond
that
I
think
you
can
totally
live
without
having
that
explicit
signaling.
We
may
also
want
to
mention
like
oh
you
shouldn't.
Do
these
other
types
of
signaling
or
redirects
that
are
no
longer
preferred
I.
N
Think
we
do
need
some
sort
of
signal
that
tells
us
to
look
back
at
the
API
I
think
it
might
be
sufficient
to
say
that
captive
portals
that
implement
this
must
send
an
ICMP
unreachable
to
the
administrative
one
or
whatever
it.
Whichever
one
of
the
current
codes
is
the
closest
and
that
clients
when
receiving
an
ICMP
unreachable-
and
they
know
they're
captive,
should
check,
and
you
can
say
well,
this
could
turn
into
an
attack.
N
But
since
the
butt
check
is
a
single
message
and
an
ICMP
unreachable
is
a
single
message
and
we
don't
accept
broadcast
ICMP
messages.
You
can't
do
a
multiplicative
attack
here,
so
you
could
slam
I
mean
if
you're
sitting
there
and
you
can
send
icing
and
pee
messages.
You
also
could
just
access
the
API
over
and
over
again
I.
Don't
think
you're
opening
up
an
attack.
They
couldn't
already
make.
N
J
Right
so
I
criticize
Luann's
ability.
I
have
criticized
the
ICMP
proposal
bitterly
long
and
hard,
but
I'm
not
going
to
talk
about
solutions.
What
I
am
gonna
say
is.
We
should
not
have
something
that's
easy
to
spoof,
unless
it's
just
a
hint
all
right.
You
know
point
one
right.
Otherwise,
even
when
you
have
a
hint
person,
two
people
go
forget
what
who
it
was
you
haven't?
You
have
an
implicit.
You
have
a
boss
attack
against
the
API
server,
it's
not
multiplicative.
So
if
maybe
it's
not
too
bad,
but
like
something
that's
not
authenticated.
J
Like
ICMP
has
this
problem
it
would
be.
It
is
I,
think
a
spectacular
failure
if
we
standardize
a
solution
that
only
works
when
stuff
is
broken
because,
like
I,
don't
want
that
I
want
something
that
can
tell
me
before
it's
going
to
be
broken.
Now,
if
we
say
that
the
API
can't
tell
us
what
time
it
is,
or
we
can't
agree
on
what
time
it
is
where
we
can't
agree
on
how
many
bytes
we've
passed,
then,
okay,
then
maybe
we
need
a
signal.
J
It
would
be
nice
if
we
didn't
but
like
as
long
as
as
long
as
the
signal
is
really
just
a
hint,
because
I
don't
see
how
an
unsolicited
message
like
this
can
be
made
secure
in
any
way
right.
So
it
really
just
has
to
be
him.
So,
yes,
it
has
to
be.
Him
would
be
nice
if
it
showed
up
before
it's
a
problem,
and
you
know,
let's
not
try
to
make
it
secure,
because
if
it
will
never
be
secure.
R
Yeah,
whatever
yeah
you
know,
yeah
Warren,
Kumari
I,
think
it's
good
to
say
something
similar
I
think
whatever
I
mean
yeah
we've
been
talking
about,
like
you
know,
destination
and
reachable
and
stuff
I.
Think
much
better
would
be
something
else
like
a
by
the
way.
Your
time
is
almost
up.
You
should
come
and
talk
to
me.
Cuz.
W
R
P
I
just
wanted
to
throw
in
one
little
bit
thing
when
you're
talking
about
this
not
being
usable
for
an
attack,
it
is
multiplicative
in
a
way
because
single
ICP,
a
packet
is
gonna
cause
since
in
ack-ack
fin
fin.
So
it's
a
5x
right.
You
do
need
to
have
some
sort
of
throttle
on
here.
I
just
want
to
make
sure
that
wasn't
lost
in
the
conversation.
C
C
N
It's
not
exponential
the
if
there's
something
about
having
using
my
cmp
unreachable
and
explaining
how
we
use
it
and
what
we
do
that
stops
us
from
having
another
thing
that
signaling
protocol
that
stops
us
from
having
these
things
are
running
out
signal
which
could
it
could
not
be
an
ICMP
signal,
but
is
not
nice
EMP
unreachable,
an
ICMP
reach
will
says,
stop
trying
to
come
this
way.
Man.
H
C
Right,
so
what
I'm
gonna
suggest
is
if
anyone
wants
to
actually
do
the
work,
to
define
a
new
signal
that
they
make
a
proposal
until
such
time
as
we
have
that
proposal.
We
assume
that
we
don't
proposal
I
didn't
hear
it
was
as
strong
an
interest
in
having
the
signal,
as
would
demand
that
we
actually
do
something
right
away.
I
heard
that
they
were,
you
know,
Tommy
couldn't
live
without
it.
Lorenzo
probably
doesn't
want
it
at
all,
but.
N
N
C
J
Asana
for
more
work,
I
think
procedure
perspective
right.
If
somebody
starts
doing
work,
there's
gonna
be
screams
of
agony
from
the
people.
Who've
spent
a
lot
of
time
working
on
this,
so
we
would
probably
need
at
least
some
form
of
like
requirements
before
we
say
okay.
Well,
we
don't
want
to
do
this.
We
want
to
build
something
new,
because
we
don't
like
your
standard
right
so
that
that
I
just
wanted
to
say
that
I
mean
like
Soho
asking.
J
H
J
J
R
C
C
It
would
be
because
I
think
that
that
sets
the
bar
for
any
for
any
implementation
and
what
we
will
do
to
Warren's
point
I,
think
and
I'll
have
to
talk
to
Eric
about
this
one
is
we
will
we
will
assume
that
we
don't
have
one
until
we
have
one
and
at
the
point
that
someone
is
interested
enough
to
invest
the
effort
in
describing
this
signaling
protocol,
something
that
meets
lorenzo's
requirements,
then
we
will
talk
about
adopting
it
at
that
point.
I,
don't
think,
there's
any
burning
desire
to
have
that
at
the
moment,
but
nor.
C
Opposition
to
someone
doing
that
work
should
someone
will
be
willing
to
invest
the
effort,
so
I
think
there
might
be
a
way
forward.
Thank
you
can
I
think
you
everyone
for
being
so
constructive.
I
have
nothing
more
here,
but
Jacque
has
something
for
to
share.
We
have
a
little
bit
of
time.
It's
less
time
than
you
asked
for,
but.
O
O
So
here's
kind
of
the
problem
right.
So
we
have
seen
right
now.
Public
Wi-Fi
hotspots
in
public
hotspots
are
usually
open
right
and
if
you
have,
you
know,
wpa2
personal
powershell
passphrase,
and
if
everybody
knows
it,
then
you
kind
of
don't
have
too
much
security
open,
don't
have
any
security
at
all.
There's
always
already
push
going
on
towards
trying
to
make
this
better
right.
I
mean
if
you
see
that
a
new
p3
and
knots
something's
happening
there
and
then
so.
O
The
only
real
solution
is
like
something
like
pass
point
and
hot
to
the
door,
which
are
pretty
complicated
for
most
deployments
right.
So
I
think
this
there's
an
increasing
desire
in
general
to
come
up
with
a
solution
that
actually
doesn't
require.
You
know
having
a
network
administrator
or
any
things
like
that,
but
like
mom-and-pop
shops
and
simple,
and
people
can
actually
just
deploy
something
that
is
relatively
secure
right
and
not
just
completely
open.
So
that's
kind
of
the
problem,
and
so
here's
a
question.
O
This
is
I'm
just
working
with
a
few
other
people
and
we
the
question
yet
that
we
are
asking
here.
Is
there
some
discussions
going
around
we're
thinking
about
coming
up
with
a
solution
that
may
be
there
where
we
may
be
able
to
leverage
the
capture
portal
api's
to
provide
a
mechanism
by
which
a
Yui
device
or
ion
device
that
connects
to
sort
of
a
untrusted
or
open
network
might
be
able
to
actually
authenticate
and
connect
or
figure
out
that
this
is
actually
a
right
network.
O
So
in
the
sense
that
if
you
have
a
right
now,
it's
easy
to
do
a
man-in-the-middle
attack
right.
If
you
have
an
open
network,
you
probably
won't
even
need
to
do
that.
You
can
just
move,
but
even
if
you
have
an
end
of
unauthenticated
encrypted
connection,
which
is
one
of
the
things
that
feature
go,
w/e
provides
right.
This
still
open
to
active
man
in
the
middle
attacks,
so
this
is
just
kind
of
throwing
out
in
the
air
right
now
to
see
would
kept
with
the
working
group
here
right.
O
So
next,
right,
yes-
and
this
is
just
yeah-
this
is
kind
of
just
talking
about
all
the
other
things
that
are
probably
already
being
done
in
order
to
solve
this
thing,
kind
of
I
think
other
organizations
Wi-Fi
land,
specifically
WBA-
are
already
working
on
trying
to
solve
this
problem.
So
it
is
that's,
that's
right,
but
the
problem
is
going
to
be
solved.
O
The
question
to
this
working
group
is
that,
if
part
of
that
there's
something
that
where
we
can
leverage
the
capital
API
to
actually
make
it
make
a
better
solution
right,
what
the
working
would
be
open
towards
entertaining
that
and
adding
that
to
the
captive
portal.
Api
work
right
I
mean
we
charter
explicitly
says
we
don't
do
you
want
to
worry
about
roaming
staff,
onboarding
and
provisioning
stuff,
and
you
know
things
like
that,
but
this
is
not
about
our
use,
our
trying
to
select
a
network.
O
This
is
more
about
helping
a
user
verify
that
they
actually
did
connect
to
the
network
that
they
intended
to
connect
right
as
opposed
to
being
an
evil
twin
network.
So
anyway,
next
slide
I
guess
so
that's
that's
just
my
general
question
is
I
just
wanted
to
see.
If
there
is
interest
in
that
of
this
first
is:
does
this
will
fall
somewhat
within
the
scope
of
the
Charter?
C
C
Whatever
we
produce,
him
may
be
used
by
others
to
do
any
number
of
things,
and
that
would
not
be
our
responsibility
or
would
require
explicit
collaboration
necessarily,
but
I
will
let
the
people
speak
to
see
whether
or
not
they're
interested
in
in
what
they
have
all
whether
they
have
ideas
about
what
what
you
might
do.
Tony.
F
F
To
this
we
view
the
kamcord
stuff
as
a
extension
for
the
cat
port
interaction
itself,
but
the
relationship
between
cat
port
and
your
network,
provisioning,
like
a
PVD
or
DSP
Ras,
seems
to
be
very
similar
to
the
relationship
between
what
you're
talking
about
and
that
same
provisioning.
So
it's
a
parallel
or
parallel
thing,
but
not
the
same
thing.
I
I
S
I
think
that
people
here
is
interesting
that
this
this
work
but
I,
don't
think
this
is
a
scope
of
this
working
group,
but
and
also
I,
want
to
mention
that
I
think.
If
I
understand
correctly,
this
is
kind
of
like
HTTP
upgrade
for
Wi-Fi
the
Wi-Fi
up
for
like
using
the
young,
unencrypted
pathway
in
and
access
points
which
kept
people
hey.
You
may
20
crates
security
or
more
secure,
so
here's
the
things.
S
So
if
it,
if
you
have
a
discussion
like
we
need
to
incorporate
with
because
like
it's,
it's
definitely
to
make
changes
to
the
Wi-Fi
architecture,
because,
like
there's
no
way
no
such
mechanism
to
upgrade
the
connection
between
that's
point
the
clients
so
before
I
think
it's
a
good
idea,
but
I
could
before
starting
the
discussion.
I
think
we
may.
We
may
talk
about
the
HIV
as
well.
Yeah.
O
Q
Think
this
is
great
for
situations
where
you're
for
networks
that
don't
have
captive
prose
as
well
like,
for
example,
your
home
network,
someone
comes
by
and
drowns
out.
The
signal
makes
you
connect
to
their
router,
so,
but
that
goes
to
demonstrate
that
this
is
beyond
the
scope
of
the
program
here.
I
think
by
still
something
really
needed,
because
these
attacks
do
happen.
So
it'd
be
great
for
users
to
do
this
kind
of
work.
Okay,.
O
C
Speaking
with
you
know,
IB
hats
on
if
there's
anything
that
that
one
of
these
groups
wants
to
come
and
talk
to
us
about,
we
can,
we
can
do
formal
liaisons,
we
can
do
people
come
into
the
working
group
and
simply
sending
emails.
I
prefer
the
latter
yeah.
But
if
it
comes
to
that
and
that's
the
way
those
work
groups
need
to
work,
then
we
we
can
accommodate
that
yeah.
O
C
C
T
C
H
Knew
clay
did
all
of
that,
but
if
proposing
actually
make
it
possible
right
now
and
specify
exactly
how
and
I
have
this
IOT
device
will
be
able
to
connect
to
your
captor
portal
that
will
require
changes
to
the
API,
because
the
API
is
only
providing
you
a
place
to
go
to
login.
It's
not
providing
you
the
button
to
login,
and
so
maybe
we
just
need
to
make
make
it
clearer
than
the
architecture.
