►
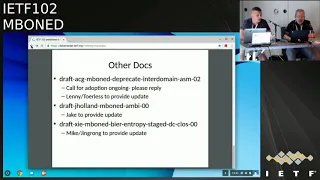
From YouTube: IETF102-MBONED-20180717-1330
Description
MBONED meeting session at IETF102
2018/07/17 1330
https://datatracker.ietf.org/meeting/102/proceedings/
B
A
B
B
E
B
E
A
B
A
A
F
B
B
B
G
B
D
B
Right,
please
sign
the
blue
sheets
Toshi's
here
to
talk
about
em
trees
and
he
has
some
late-breaking
news
that
we're
excited
to
hear
about.
I'm
sure
mike
has
a
couple
presentations
on
update
and
new
beer.
Entropy
Jake's
gonna
be
presenting
remotely
we're
probably
going
to
move
Natalie
up
right
before
Jake
to
promote
true
Pro
to
present
remotely
and
then
toyless
has
a
couple
presentations.
B
B
H
Like
my
bride,
we
didn't
do
any
update
since
the
last
ITF
on
that
a
I
Triple
E
802
multicast
problem
statement.
So
we
didn't
ask
for
a
slot
this
time,
so
I'm
not
exactly
sure.
Probably
what
we'll
do
is
we'll
probably
do
another
update
before
or
Bangkok
represent
it.
There
I
think
will
probably
be
pretty
close
at
that
time.
To
ask
for
a
working
group
last
call
cool.
B
And
then
the
yang
models
draft
was
adopted
successfully
since
London,
so
sandy
is
sandy
here.
No,
no
sandy,
that's
ready
to
be.
You
know,
reissued
as
a
working
group
document.
So
after
a
while
you
know
took
a
while,
but
now
we're
a
working
group
document,
so
we're
ready
for
that
other
drafts
there's
the
deprecated
draft,
which
is
actually
in
a
current
ongoing
call
for
adoption.
So
we
will.
We
would
really
appreciate
folks
replying
to
that
adoption
call
either
yea
or
nay,
if
you
think
it
should
or
should
not
be
adopted.
B
E
D
E
I
J
B
A
F
K
So
except
media
and
Alec
all
approved
I
believe,
but
we
had
a
still
comments
from
media
and
alec
and
we
leave
ice
based
on
their
comments
and
submitted
a
version
24
on
June
to
August
their
comments
and
media
upload
about
the
eloquent.
So
we
have
been
working
to
fulfill
the
requirements.
Eric
showed
and
so
today,
I
just
briefly
summarized
status
and
the
current
situation
and
they
go
to
the
next.
But
beef
maybe
just
go
to
the
last
Friday's
weather.
The
last
strike
last
try
first.
K
So
actually
this
is
update
on
this
at
this
morning.
So
we
thought
after
Eric's
comment
confirmation
that
blue
ball.
We
will
submit
new
new
vision,
25
and
ask
final
procedure,
but
I
met
him
this
morning
and
finally,
I
got
his
confirmation
of
a
blue
ball,
so
now
I'm
think
I
believe
we
can
submit
to
the
worst
version
and
the
desk
device
body
will
be
approved
by
all
ISD.
K
So
this
is
a
current
news,
but
so
if
there
is
no
consensus-
and
there
is
no
appealable
I
may
want
to
ask
you
how
we
can
address
this
comment
and
how
we
can
stack
the
current
situation,
but
luckily
I
got
a
consensus
and
approval.
So
actually,
as
a
result,
maybe
I
don't
need
to
ask
what
should
I
do
now,
but
anyway,
I
can
summarize
what
we
have
been
working.
So
in
a
previous
ride,
you
have
some
question
or
comment.
Well,
no.
K
J
K
3,
yes,
this
one,
so
the
his
comment,
mainly
his
comment
has
he
has
two
comments.
Why
is
forgery
of
responses?
And
so
it's
mainly
security
related
stuff
forgery
of
responses,
amplification
attacks-
and
he
said
this
product-
does
not
appear
to
verify
that
the
sender
of
the
request
actually
owns
iCal
claims.
D
K
K
Okay,
well,
so
he
required
something
like
a
longer
qle
ID,
but
we
already
replied
that
the
clearly
ID
is
not
intended
as
a
security
protection
mechanism.
So
the
length
of
the
query
ID
is
meaningless
to
protect
something
from
the
security
slits.
So
the
first
part
is
actually
the
main
point,
so
we
updated
based
on
his
comment.
We
updated
the
forgery
of
less
horses
so
well.
He
may
acquire
something
like
encryption
mechanism
for
the
messages,
but
we
don't
want
to
adapt
to
some
special
encryption
mechanism.
K
Maybe
it
can
be,
but
that
kind
of
specification
could
be
specified
in
a
different
documentation.
So
we
don't
want
to
say
the
encryption
making
me
something
like
a
master
assured.
So
we
explained
that
anchor
fix
make
increment.
It
could
be
fine,
but
that
kind
of
party
is
out
of
scope
of
this
document
and
he
understand
this
part.
The
second
part,
this
is
more
sensitive,
so
filtering
of
clients
so
see
this
one
is
a
version
24.
This
includes
that
bird.
This
sections
have
a
section
is
included
in
version
24
and
also
in
25.
K
We
try
to
modify
the
wording
from
24
the
letter.
Let
fonts
explain
the
differences
from
the
24
24
and
the
answer
that
apply
from
us
is
that
we
should
specify
some
configurable
packet.
Filtering
mechanism
is
master
so
because
maybe
it's
better
to
explain
with
this
example.
So
let's
say
we
have
one
client
and
this
client
is
attached
to
allowed
a
and
Lauda
is
upstream
with
Delta,
B
and
larger
C
and
so
on,
and
at
the
letter
C
attached
to
the
sender.
In
that
case,
allow
client
sent
actually
messages
legally.
K
So
he
is
a
very
good
member.
He
sent
a
clear
message
and
Lala
I
accept
his
query
and
translate
this
query
as
a
new
request
message.
So
the
quest
message
is
transferred
from
A
to
B
and
then
B
to
C
and
then
C,
Li
change,
the
header
part
or
the
message
type
from
the
request
tool
apply
and
send
back
to
the
client.
This
is
ordinary
case,
but
his
concerns.
K
If
the
body
receiver
is
attached
to,
let's
say,
luta,
flautas
B
and
the
Delta,
B,
intentionally
or
unintentionally
sends
a
request
packet,
not
actually
packet,
request
packet,
but
louder
B
only
uploaded
his
IP
address.
So
he
sent
that
this
request
message
to
assume
louder's,
but
in
that
case
request
message
may
have
some
problem,
so
example
over
the
empty
you
or
something,
then
the
LMS
egde
is
transmitted
to
the
original
client,
which
is
attached
to
Alta
a
so.
This
is
something
like
a
amplification
attack.
He
said
so
this
this
is
amplification
attack.
He
says
so.
K
B
just
believes
his
request
message,
which
must
be
different
and
it
must
be
strange
and
the
transferred
transferred
to
the
upstream
router.
So,
to
protect
this
kind
of
attacker,
we
should
provide
some
configure
packet,
a
filtering
mechanism
that
supposed
to
verified
IP,
address
port
number
and
also
the
type
value
of
the
messages.
L
L
Basically,
I'm
trying
to
understand:
okay,
it's
it
just
like
when
they're
out
the
processes
and
em
trace
packets,
like
as
part
of
being
a
mem,
trace,
client
or
server
whatever
that
you
can
do
this
filth
Rima.
Do
you
expect
like
a
router
that
forwards
IP
packets
to
see?
Oh,
this
is
an
MJ's
packet.
I
need
to
maybe
drop
it
well.
K
K
In
that
case,
the
current
packet
request
packet
is
transmitted
to
the
original
clients
and
continuously
eliminate
by
eliminating
the
previous
standard
response
blocks.
Only
keeping
the
message
header,
which,
whose
type
is
a
request,
continuously
transmitted
toward
the
center,
but
his
concerns.
If
the
message
itself
is
really
larger
or
the
empty
which
service
is
really
small
along
the
past,
then
the
an
incomplete
Leafly
message
may
be
transmitted
by
each
louder
several
times.
K
So,
even
though
the
the
client
send
a
one
single
query
message,
he
may
receive
the
multiple
replies
which
is
initiating
it,
which
it
is
created
by
intermediate
routers.
This
may
so.
This
is
an
amplification
attack.
He
there.
So
to
avoid
this
kind
of
attack,
intentionally
or
unintentionally,
attacker
request
message
must
be.
L
L
K
L
B
K
B
A
L
K
K
B
K
B
L
It's
in
in
practice,
I
mean
you
could
say:
people
must
implement
some
filtering
to
support.
That
is
that
right
to
be
compliant
with
whatever
they
are
disability,
and
you
can
say:
okay,
if
you
support
your
people,
implements
em
chase,
you
need
to
be
compliant,
of
course,
but
it's
you
know
it's
hard
to
enforce
and
say
that
wall
routers
that
are
deployed
need
to
support
and
trace
filtering,
and
if
that
is
needed,
to
make
it
secure
and
in
practice
it.
You
know,
you
can't
really
expect
that
to
happen.
L
C
B
N
M
N
That's
I'm,
sorry
with
someone
just
talking:
okay,
there's
standard
functionality
that
is
supplementary
to
ACLs,
that's
provided
by
juniper
and
Cisco
and
I
assume
other
vendors
that
provides
generic
packet
filtering
and
it
allows
specification
of
an
arbitrary
field
within
the
payload
which
in
this
case,
could
be
the
M
trace
message
type.
So
this
isn't
a
special
thing
required
as
part
of
the
M
trace
implementation.
It's
just
there
for
current
releases
of
a
number
of
vendors
routing
and
switching
products.
I
N
That's
right,
Troilus,
so
it's
within
that
arbitrary,
but
some
number
of
bytes
of
the
header,
which
in
this
case
will
work
fine.
We
can
differentiate,
request
and
and
reply
from
other
message
types.
So
we
can
say
only
these
ranges
of
IP
addresses
are
allowed
to
send
a
request.
And/Or
a
reply
message
so.
L
N
I
Your
main
clarification,
and
maybe
that
helps
with
mistakes
questions
so
try
to
remind
me
of
these
packets
that
we
need
to
filter
our
guaranteed
to
be
at
the
process
level,
because
they've
been
hunted
by
router
alert
or
something
else
or
it
can
they
be
in
the
aqua
forwarding
thing
and
need
to
be
filtered
there.
So.
N
B
K
K
This
is
a
most,
so
next
one
is
just
explanation
about
what
is
application
attack,
and
this
is
also
related
to
the
such
kind
of
filtering
mechanism,
so
più
itself,
for
example,
TSM
or
pin
D,
and
so
on-
has
mechanisms
to
authenticate
the
neighbor
louder's.
So,
in
addition
to
the
such
kind
of
filtering
mechanism,
router
this
one
says
should
top
any
empty
edge
to
request
all
the
premises
that
is
received
from
a
known
authorized,
be
neighbors,
and
additionally,
this
is
a
today's
agreement.
K
So
this
initially
we
didn't
mention
this
kind
of
a
scenario,
because
MTS
doesn't
rely
on
any
kind
of
multicast
routing
protocol,
but
he
requires
such
kind
of
authentication
mechanism.
As
an
example,
we
explained
about
a
FEMA
authentication
mechanism,
but
not
only
p.m.
we
also
need
to
explain
the
intent
over
this
text
is
to
prevent
non
louder
in
point
from
everywhere
in
village
of
non
pimp.
Loadable
should
employ
some
other
we're
going
to
prevent
this
kind
of
attack.
So
if
you
use
gnome
PM
louder
than
something
like
a
similar
mechanism
must
be
are
considered.
Okay,.
L
B
That
the
hostages
have
been
agreed
to
be
released,
but
we're
not
quite
sure
we
agree
with
the
terms
of
the
release.
Okay,
yeah
I
think
I
think
it
goes
without
saying.
We
should
definitely
send
things
on
list
when
people
have
a
chance
to
really
review
and
and
and
digest
what
was
agreed
to
make
sure
that
it
didn't
change
anything
okay,.
I
K
I
O
J
J
H
Very
good
all
right,
so
some
of
you
may
remember
this
draft
from
thank
you
from
years
ago.
Last
time,
last
ITF
I
mentioned
that
it
was
resurrected.
It
was
already
working
group
draft.
We
thought
it
would
be
good
idea
to
have
a
working
group
draft
here
in
mbone
that
discusses
multicast
as
use
in
the
data
center
last
ITF
I.
H
H
We
just
mentioned
that
in
the
spring
working
group,
for
instance,
they
are
reach,
are
during,
but
multicast
continues
to
not
be
included
in
that
Charter,
and
so
we
need
to
have
a
place
to
address
multicast
in
spring.
We're
addressing
some
of
those
things
in
PEM
within
embo
Andy
it'd,
probably
be
a
good
idea
to
start
at
least
thinking
about
some
ramifications
and
in
beer
right,
okay,
very
good,
and
so
we
were
dressing
that
where
we
meant
we
mentioned
beer
in
this
draft
as
well.
H
B
H
So
maybe
so
cuz
we
have.
We
have,
for
instance,
NPM
a
giraffe,
that's
going
to
be
mentioned
today.
We've
had
some
that
were
discussed
previously
about
different
solutions
for
multicast
in
and
segment
routing,
whether
that's
beer
or
some
new
type
of
solution.
So
maybe
the
some
of
those
things
may
need
to
be
discussed
from
a
deployment
perspective.
Here.
H
L
L
H
Prior
to
this
latest
update
from
Femi,
it
was
just
what's
been
used
today
up
to
this
point
where
March
kids
used,
but
we
added
a
few
just
little
tidbits
that
maybe
we
shouldn't
of
well
just
just
an
FYI.
There
are
some
new
developments
that
are
being
used,
they're
coming
into
deployments,
probably
soon
just
be
aware
of
them,
and
if,
when
that
does
happen,
here's
some
of
the
basic
things
to
be
aware
of.
H
L
H
H
H
E
H
H
H
People
have
something
to
point
to
where
this
is
what
you'll
get.
If
you
do
use
beer-
and
in
this
case
we
we
could
either
have
a
beer,
general
beer
and
a
data
center
draft
here
in
mbone
d
or
beer,
or
we
do
like
what
we've
done
here
and
that
is,
we've
just
chosen
a
specific
feature
of
beer
and
then,
in
this
case
it's
including
entropy
and
beer
for
load,
balancing
and
just
and
create
a
document
about
it.
Yeah.
J
You
should
I
mean
we
normally
do
that
across
across
working
groups
to
make
sure
everyone's
informed.
Clearly,
the
entire
beer
group
is
not
represented
here.
People
might
have
issues
about
how
the
intro
field
is
what
I
mean
I
I
like
where
this
is
going.
I,
don't
disagree
with
all
the
decisions,
because
I've
got
some
some
feedback
into
this
as
well.
Take
a
stir:
okay,.
H
E
H
This
draft
described
in
Jing
wrong,
it's
been
leading
the
and
these
are
his
ideas
and
I've
just
been
kind
of
helping
them
with
some
of
the
details
of
this,
but
we're
describing
how
beer
entropy
can
be
useful
in
data
center
Clause
networks,
so
beer,
entropy,
entropy
in
general,
is
being
used
with
a
variety
of
protocols,
including
segment
routing.
There's
a
draft
on
entropy
I.
H
Don't
know
the
RFC
number
yell
it
out
if
you
know
it,
but
that
allows
you
to
view
load
balancing
and
it
can
be
done
in
a
more
deterministic
way,
rather
than
just
more
of
a
random
hashing
and
ecmp
kind
of
environments
and
beer
includes
the
entropy
as
well,
so
you
can
actually
have,
as
you
look
at
a
packet
and
look
at
the
source,
IP
a
destination
address,
and
maybe
the
port
numbers
you
can
take
that
out
and
create
an
entropy
label,
an
MPLS
environment
and
hash.
On
that.
Just
tell
the
second
sis
question.
I
I
J
You
have
one
no
professional
media,
okay,
we're
like
your
description
here,
the
Greg
Sheppard
Cisco,
it's
not
chair,
had
you
said
long
lived
elephant
flows
in
pmn,
they're,
all
elephant
flows,
and
so
when
you've
got
multi
point
going
up,
multi
point
come
down.
Ecmp
could
create
collisions
based
on
the
addressing
hash,
whereas
you
want
to
make
sure
that
this
flow
takes
this
link
and
the
next
big
flow
takes
this
link
and
there
isn't
collisions
across
that
typically
kind
of
streaming
out
of
the
data
center
or
kind
of
the
always.
J
All
within
the
DC,
so
processing
for
exactly
so
you've
got
I
mean
so
even
well.
What
we
call
a
DC
and
that
could
be
in
a
truck,
could
be
in
a
stadium.
It
could
be
in
a
massive
data
center
facility,
but
the
flows
are
the
same
they're
all
4k,
HD
cameras
and,
and
they
stay
that
way.
Uncompressed
flows
I
think
that
the
important.
H
That's
exactly
right
exactly
so
that's
and
that's
what
a
clause
network
is,
and
so
without
going
into
much
of
detail
on
that,
and
we
mention
it
in
this
draft
and
I.
Think
I
may
mention
it
more
in
the
DC
deploy
draft,
and
that
is,
you
know
how
we
used
to,
for
those
of
us
have
been
doing
this
for
a
long
time.
We
used
to
have
the
hierarchical
tree
like
structure,
a
tier
1
tier
2
to3,
which
was
core
distribution
and
access,
and
we've
kind
of
moved
away
from
that.
H
It's
much
more
popular
to
do
these
cause
this
spine
leaf
scenarios
where
you've
got
to
1
to
2,
to
3
the
spine
being
tier
1,
the
leaf
being
tier
2
and
the
top
of
rack
being
tier
3,
and
it's
more
horizontally
scalable.
You
can
add
new
servers
devices
routers
whatever
to
the
spine
as
you
need
them
without
having
to
replace
boxes.
So
it's
just
much
more
scalable
and
that's
for
port
density.
That's
why
we're
doing
it
and
we've!
You
know
kind
of
mentioned
the
the
long-lived
elephant
flows.
H
Whether
and
there's
a
lot
of
them
can
be
non-trivial
due
to
lack
of
determinism
and
so
we're
trying
to
find
we're
trying
to
specify
that
beer
with
entropy
can
give
us
a
level
of
determinism
to
help
alleviate
some
of
these
problems
and
an
operator
may
want
to
have
a
deterministic
path,
and
this
this
is
something
that's
being
used
elsewhere.
There's
a
draft
MPLS
spring
entropy
label,
which
addresses
very
similar
thing.
H
We've
utilized
some
concepts
from
that
draft,
and
so
basically,
a
deterministic
path
can
be
found
by
using
part
of
the
20
bit
entropy
build
that
0
2
bit
2
friends,
for
instance,
that
the
entropy
level
can
be
can
represent
the
value
of
zero
to
seven.
It
can
be
used
to
select
deterministic
paths
from
a
equal
cost
paths.
So
again
it's
something
that's
not
new
to
beer,
but
thankfully
beer
does
utilize
it.
H
H
Okay,
so
I'm
just
gonna
quickly
go
through
the
next
two
sides.
It
just
kind
of
it
just
kind
of
shows
what
I
just
described
in
this,
and
these
diagrams
are
used
in
the
in
the
draft.
So
go
back
up
one
more
great:
it
just
went
down
yeah
there
we
go
stay
there
right
there
all
right,
so
this
kind
of
shows
in
clause
networks,
there's
three
stage:
there's
five
stage
architectures
and
you
have
northward
stages
and
you've
got
southbound
stages
that
have
a
rich
amount
of
equal
cost.
H
And
so
again,
by
using
the
beer
entropy,
you
can
bill
to
provide
more
deterministic
path,
selection
and
you
can
use
like
I
mentioned
in
stage.
One,
for
instance,
use
bit
zero
of
that
twenty
bit
entropy
label
to
represent
red
and
blue
plus,
and
you
can
on
different
stages.
Let's
this
case
stage
to
use
different
bits
of
that
enter
beef
label
to
represent
three
paths
to
each
of
the
different
clusters:
to
be
able
to
provide
a
deterministic,
you
could
cost
multi
path
along
a
data
center,
multi
stage
network
next
slide.
J
Yeah,
cisco,
so
in
this
I
your
showing
how
how
to
potentially
break
up
the
interview
field
to
set
deterministic
paths,
because
the
question
I
have
is
around
where
the
bier
header
gets
written
in
a
way
to
use
these
paths,
so
that
would
have
to
be
I
guess
below
stage
one
or
it
could
happen
either
way.
I
mean
she
had
IP
multicast
at
the
pod
level
and
beer
in
the
DC.
It's
the
first
in
position.
Point
creates
that
field
right,
yeah.
P
J
This
could
be
a
DC
specific
decision
how
the
bits
are
used,
where
I
could
be
just
networks
like
beer
domain
decision
not
necessary.
We
have
to
have
our
architecture
dock
that
specifies
the
bits
to
be
used
in
this
way,
but
here
is
a
particular
way
to
use
those
bits
and
how
you
cut
them
up.
Based
on
how
many
CMP
paths
did
a
complexity
for
topology,
you
can
set
a
beer
wide
specific
configuration.
You.
H
Should
cut
using
controller
or
whatever
tip
that
happened?
That's
right
exactly
right!
Okay,
so
next
slide
yeah,
okay!
Well,
we're
just
about
done!
We're
done
so
go
to
slide
six.
It
just
kind
of
specifies
some
of
the
forwarding
procedure
using
beer
in
tributed,
just
like
the
path
over
equal
cause.
Paths
already
explained
at
this
draft
defines
a
method
to
use
part
of
that
20-bit
entropy
label,
and
it
should
be
easier
and
should
be
more
granular
and
more
deterministic
than
using
just
the
typical
hashing
ecmp
function.
H
So
with
that
I
was
just
going
to
leave
it
at
that
and
just
kind
of
go
on,
but
I
think
it
would
be
good
to
have
a
discussion
about
if
this
is
something
that
this
type
of
weather
it's
just
draft
or
not.
This
type
of
topic
is
that
this
is
something
that
we
think
that
we
should
address
work
on
here
in
an
Bodi
question.
I
Yeah
so
I
think
you
know
the
most
simple,
but
you
know
problematic
reference
example
to
show
you
know
they
have
people
belief
in
the
problem
right
so
I
think,
starting
with
what
you
know,
Greg
was
saying:
maybe
you
know
the
smallest
kind
of
data
center
right,
which
could
be
production
truck
with
a
bunch
of
you,
know
the
small
stuff
and
then
video
whatever.
It
is
right
so
that
dead
set
the
expectation
in
terms
of
yeah.
This
is
a
problem
and
then
the
other
things
are
fine.
I
mean
I
completely
forgot
the
details.
I
So
do
we
have
polarization
in
the
beer
ecmp?
That's
one
of
the
typical
issues
to
deal
with
right,
I,
don't
remember
it
in
the
algorithm.
Obviously
you
know
I
also
stand
out
on.
You
know
behalf
of
this
author
of
beer
te
and
say
that
we
haven't
thought
about
really
that
much
about
the
EC
and
P
stuff.
It
was
obviously
mostly
about
non
ecmp
path,
but
we
could
also
think
about
comparing
this
what
we
can
achieve
with
the
beer
ecmp
with
the
explicit
hop-by-hop
engineering
of
the
path
and
the
data
center
with
beer
te
o
your.
J
I
H
J
Q
Univer,
if
this
involves
defined
methods
of
using
the
part
of
entropy
layer
failed
in
beer
or
the
purely
entropy
label,
were
what
the
came
first
clarified.
As
you
see
on
this
slide,
you
mean
you
mentioned
that
gives
part
of
the
20
bit
entropy
label.
I
talking
about
entropy
label
are
talking
about
entropy
filled
in
the
beer
header.
P
Q
Okay,
so
if
this
involves
pure
entropy
field
and
also
involves
some
specific
beer,
falling
behavior,
then
I
think
ish
should
be
part
of
the
beer
working
group
in
other
comment
is
that
if
you
want
to
control
how
the
that
of
the
past
that
the
packet
follows
another
way
to
do,
this
is
use
multi,
topologies
or
or
just
a
flexor
I'll
go
so
that
you
can
decide
that
some
Packers
follow
so
one
sub
subt
apology,
some
other
Packers
poles
are
differently
sub
topology.
That's
another
way
to
do
it
right.
J
Can
I'm
gonna
address
that
one
in
particular,
because
I
think
the
use
case
that
I'm
thinking
of
that
kind
of
came
up
from
reading?
The
document
is
specific
enough
that
the
multi
topology
it
would
be
very
complicated.
You
would
have
to
have
several
of
them
not
just
a
couple
and
we're
not
really
trying
to
select
topology
necessarily
we're
trying
to
ensure
that
each
of
the
hops
don't
have
collisions.
So
you
could
build
complete
matrix
of
topologies
to
ensure
that's
the
case,
but
in
a
flow
by
flow
basis.
J
You
may
want
to
make
a
different
determination
that
this
link
was
okay
now,
but
now
at
the
next
hop
down,
we've
got
a
congestion
issue.
I
want
this
to
keep
on
this
hop,
but
take
the
next
one
over
here
to
avoid
that
congestion.
So
it's
that's
something,
but
this
matrix
of
topologies
could
get
very
complicated
quickly,
so
I
think
to
Tauruses
point.
Maybe
a
more
specific
problem
statement
would
allow
to
burrow
into
a
solution
that
is
very
specific
to
that
problem.
J
I
So
TARDIS
it
wasn't
kind
of
clear
to
me.
You
know
if
you're
really
changing
something
in
beer
or
just
basically,
you
know
what
a
application
using
beer
and
setting
the
field
would
be
doing
so
might
be
borderline,
whether
it
should
be
beer
or
in
Bondi,
but
overall,
the
problem
statement.
You
know
describing
the
example
reference
problems,
so
anything
operational
would
be
good
here,
so
I
mean
I,
have
no
strong
opinions
either
way
right.
A
J
J
B
M
E
B
B
So,
just
in
in
London
we
had
William
Jiang
present.
His
experience
in
deploying
an
AMT
relay
one
of
his
pieces
of
feedback
was
that
okay,
the
relay
is
up
and
running.
There
is
content
out
there.
However,
the
state
of
Gateway
implementations
is
not
so
awesome.
You
know
the
best
most
widely
usable
implementation
was
a
VLC
Windows
port
that
was
about
10
to
12
years
old.
M
M
So
the
end
goal
of
the
project
was
to
allow
end
users
to
access
multicast
content
over
the
Internet,
because
it's
out
there,
but
there's
not
an
easy
way
to
get
it.
You
kind
of
have
to
do
a
lot
of
workarounds
and
so
I
made
a
list
of
various
ways
that
we
could
do
this
so
that
in
the
end
it
would
be
easy
for
even
like
my
mom
to
use
whoo
she
kind
of
struggles
with
technology.
Cuz
I
don't
want
it
to
be.
M
She
has
to
enter
an
IP
address
and
like
go
through
all
the
stuff,
because
she,
you
know
something
goes
wrong
with
her
email
and
she's,
like
I'm
done,
I
quit
so
I've
been
doing
that
since
the
end
of
May,
that's
been
my
project
at
juniper
and
I
had
no
idea
what
AMT
was
before
this.
So
it's
definitely
been
an
experience.
M
You
can
go
to
the
next
slide.
So
again,
I
made
a
list
of
a
bunch
of
possible
platforms.
Our
original
goal
was
to
use
a
web
browser
implementation
because
that
tends
to
be
the
easiest
for
people.
I
mean
you
just
go
to
a
website,
you,
like
click
and
it's
there.
That's
really
easy
for
most
people
understand
and
use,
but
I
did
find
some
issues
with
that.
M
So
with
web
RTC,
at
least
from
what
I
found
it
had
no
multicast
support
and
then
webassembly
had
no
UDP
support,
because
amt
works
over
UDP
without
that
it
just
doesn't
work.
So
then
I
looked
into
making
a
plugin
for
a
browser
like
Chrome
Firefox,
and
then
you
know
making
it
available
all
of
them.
But
I
found
out
that
google
apparently
deprecated
plugins,
starting
in
like
2016.
M
They
have
that
had
this
like
movement
and
then
it
kind
of
like
finalized
in
2018,
where
plugins
you
can
no
longer
create
new
ones,
even
though
older
ones
can
still
be
maintained,
so
I
didn't
want
to
start
on
making
a
plug-in
just
to
have
it
be
no
completely
out
of
date.
Soon
after
and
other
issues
arise
with
that,
and
then
I
tried
an
extension
and
the
gist
of
it
was
that
anything
to
do
with
the
web
browser
seemed
there's
no
raw
UDP
access.
So
I'm
sorry
was
there
garbled
speech,
nope.
E
M
M
M
Okay,
but
with
the
browser
implementation,
there
used
to
be
an
API
for
accessing
UDP
sockets,
but
it
has
been
put
out
of
date
or
like
when
I
even
just
started
on
some
of
the
tutorials.
For,
like
writing
a
plug-in
or
something
like
that,
I
kept
getting
all
these
errors
about
like
hey.
This
is
deprecated
you
shouldn't
use
it
like
try
moving,
is
something
else,
but
it's
newer.
So
there's
there's
not
a
an
API
and
it's
understandable
from
a
security
standpoint
just
accessing
raw
UDP
sockets,
but
they're.
M
They
have
a
port
for
basically
everything
and
it's
backwards,
compatible
for,
like
all
their
old
versions
and
stuff,
like
that.
So
and
theoretically,
I
actually
found
this
out
more
recently.
They
also
have
a
plugin
like
that
has
already
been
made.
So
theoretically,
if
the
amt
module
got
added
in
then
you
could
make
a
web
application
that
could
use
that
plug-in
that
as
long
as
everything
gets
flushed
up
straight
and
such
so,
you
can
go
to
the
next
slide.
M
Cool
so
the
other
benefits
of
VLC
it
handles
basically
all
major
media
types.
It
can
play
almost
anything
even
like
corrupt
files,
which
is
really
good.
It's
also
modular,
so
adding
parts
into
it
and
like
developing
on
its
source
car
source
code
is
pretty
easy
because
you
don't
have
to
worry
about
breaking
it.
The
other
functionality
too.
Much
and
again,
it
runs
on
almost
any
platform.
I
found
that
it's
pretty
easy
to
use
from
my
standpoint,
but
then
again
I'm
also,
you
know
computer
science
person.
M
M
So
what
I
did
is
I
started
on
an
access
module.
They
VLC
has
all
these
kinds
of
modules
that
work
for
different
things
like
output,
access,
D,
muxing,
so
most
of
the
D
mixers
are
actually
the
what
decodes
the
streams
and
stuff
like
that.
So
my
idea
was
that
all
create
an
access
module
that,
essentially
you
know
open
supports,
sends
the
correct
messages,
the
discovery
advertisement
and
such
and
then
pass
that
data
onto
a
d'emic,
sir,
because
theoretically,
VLC
can
already
read
whatever
the
data
is
because
it
should
be
a
major
media
type.
M
It
shouldn't
be
something
ridiculously
obscure.
I
did
start
off
using
the
UT
Dallas,
antique
implementation,
I
kind
of
looked
at
that
first,
only
because
it
was
you
know
already
integrated
with
VLC
quote
unquote,
but
it
was
also
from
a
much
earlier
version
of
VLC
that
wasn't
quite
as
modular
then
so
it's
helpful
ish.
It
was
also
mostly
had
a
lot
of
windows
API
specific
stuff,
so
it
wouldn't
work
as
well
for
compiling
with
VLC
J
holin.
M
Both
his
code
and
just
talking
to
him
over
email
was
really
helpful
for
me
to
understand,
and
also
just
where
to
get
started,
because
VLC
is
just
really
big,
even
though
there
is
a
lot
of
documentation
and
stuff
kind
of
confusing
to
get
started.
Cisco
has
an
open-source
library
for
SSM
amt,
so
that
was
also
pretty
useful.
M
So
some
of
the
major
challenges
I
spent
a
couple
weeks
partially
doing
research,
I,
understand,
AMT,
but
also
just
the
appropriate
path,
because
again,
I
would
keep
trying
something
with
a
web
browser
and
then
find
out.
Oh,
it
doesn't
have
this
kind
of
support.
Oh
it
doesn't
do
this,
so
that
was
a
little
difficult.
I
actually
didn't
have
to
duplicate
a
little
bit
of
the
IGMP
and
IP
protocols.
M
In
order
for
AMT
to
work
and
just
getting
my
messages
to
send
correctly
AMT
wasn't
a
understanding
itself,
wasn't
a
huge
challenge,
but
it
was
still
there
as
something
I
had
to
overcome
in
the
beginning.
Right
now,
also,
my
mate,
where
I'm
stuck
right
now,
is
that
I
can
receive
the
multicast
data,
because
I
send
the
messages
correctly
and
like
Wireshark,
shows
me
receiving
the
multicast
data,
but
the
audio
is
garbled
and
there's
no
video
rendering
so
and
I've
tried
synching
it
up
with
the
Windows
VM
I
have
for
the
other.
M
The
working
implementation
and
the
audio
lines
up
is
just
dropping
like
packets
randomly
and
the
output
from
VLC
is
like
skipping
30
bytes
of
garbage,
so
I'm
just
stuck
right
there,
because
it
seems
like
I'm,
not
unpacking.
The
packet
correctly
VLC
seems
to
be
confused
by
some
of
the
headers
I
will
say
it
was
much
easier
than
expected
for
me
to
compile
VLC
and
actually
start
on
writing
the
module,
because
I
haven't
actually
contributed
open
source
before
I'm
still
in
college.
M
So
it's
just
I
haven't
done
it
yet,
so
that
was
much
easier
than
I
expected.
So
next
slide,
so
I
still
have
it
to
do
this
for
the
rest
of
summer.
I
have
some
weeks
a
couple
weeks
left
I
do
want
to
add
in
IgM
V
to
support,
because
I've
been
focusing
on
IGMP
v3
I.
Don't
think
it
should
be
a
huge
leap
from
what
I'm
doing
now.
I
need
to
make
sure
I
have
no
memory
leaks
because
VLC
most
of
their
modules
are
in
and
C,
so
I
just
need
to
make
sure.
M
There's
no
memory
leaks,
I,
don't
currently
have
the
timers
fully
working
just
because
of
the
way
I'm
receiving
data
right
now
and
I
was
mostly
mostly
focusing
on
the
actual
functionality,
rather
the
timers.
Just
yet
I
mentioned
before
VLC
looks
like
it
does,
have
a
browser
plugin,
so
I
could
once
provided
this
module
would
be
like
accepted
into
their
access.
You
can
make
a
browser
plugin.
M
The
end
goal
is,
of
course,
to
successfully
stream
full
video
and
audio
because
of
there's
a
relay
already
set
up
at
Thomas,
Jefferson
High
School
near
here
so
and
then
later
on,
submit
a
patch
request,
feature
request
to
VLC
so
that
this
module
will
be
in
there
full
thing,
yeah.
So
next
slide
I
know
Oh.
M
There's
also
like
not
an
audience
because
there's
no
content,
but
there's
no
content,
because
there's
no
audience
so
I
think
it's
a
really
useful
way
to
help
transition
into
hey.
Let's
have
more
multicast
content
available
for
as
many
people
as
possible.
I
did
think
the
RFC
7450
was
pretty
well
written,
very
thorough.
The
diagrams
were
great,
so
VLC
itself,
just
briefly,
their
documentation
is
better
than
some
of
the
other
open
source
projects
that
I've
looked
into
before
or
had
to
like
glance
at
for
school
and
their
chat
and
forums
were
okay.
M
B
A
good
case
study
for
this
working
group
because
amt
the
spec
was
essentially
written
for
someone
like
you,
somebody
who
doesn't
necessarily
know
multicast
but
can
walk
in,
and
and
so
it
is
good
to
hear
that
you
were
able
to
pick
up
the
spec
and
figure
out
how
to
start
writing
and
implementation.
So
that's
actually
great
feedback
for
this
working
group.
M
Right
now,
I'm
still
trying
to
finish
up
and
actually
get
the
video
stream,
in
addition
to
the
audio,
because
it's
not
fully
synched
up
right
now,
like
I'm,
definitely
receiving
the
data.
I
just
don't
think
I'm
processing
the
packets
correctly.
So
it's
kind
of
a
matter
of
like
checking
my
sockets
and
checking
that
VLC
is
actually
getting
the
data
correct.
Since
again,
it
kind
of
jumps
through
a
lot
of
Hoops.
So
the
most
immediate
one
is
fixing
that.
O
O
Though
I
held
my
comments,
cuz
I
know
I
was
going
but
Thank
You
Natalie,
that's
exciting
work!
That's
I'm
interested
in
hearing
more
about
your
progress,
see
your
end
up,
work
great,
so
I'm
going
to
talk
about
our
new
proposal
for
asymmetric
manifest
based
integrity.
This
is
meant
to
provide
integrity,
guarantees,
cryptographic,
integrity,
guarantees
for
for
multicast
instrument.
There
I
think,
there's
no
reason
you
can't
use
it
for
unicast,
but
it
particularly,
maybe
like
AMT,
would
be
a
potentially
useful
case
to
do
that,
but
you
know
so
you're.
O
Looking
for
multicast
yeah
inter
domain
multicast,
we
think
that
one
of
the
issues
it
may
be.
It's
not
the
only
issue
but
I
think
it's
a
blocking
issue
that
we're
not
going
to
have
a
real
and
bone
with
inter
domain
multicast
that
you
know
it
is
friendly
and
hardly
available
if
we
can't
make
good
integrity,
ultimately,
I
think-
and
so
this
to
me
we're
trying
to
fill
a
hole
in
the
what
we've
got.
O
B
O
All
right,
no
revolt,
all
right,
so
so
our
goals
here
are
about.
We
want
a
hat.
Mostly.
What
we're
trying
to
solve
is
live
video,
that's
kind
of
the
main
use
case
we
want
and
we're
looking
for
asymmetric
crypto.
So
we
mostly
want
integrity,
because
when
we're
talking
about
live
video,
especially
to
a
wide
audience,
you
know
symmetric
keys,
just
not
like
there's
a
point
right
and
we
basically
want
to
be
able
to
do
it
it
and
handle
lots
of
work
really
in
the
next
slide.
O
O
There
we
go
so
let
me
preface
this
the
next
three
slides,
including
this.
We
got
some
great
feedback
yesterday
from
psych
dispatch.
Eckhart
pointer
does
pointed
us
at
a
really
interesting
paper
that
I
think
might
be
able
to
this
or
help
us
improve
on
on
the
schema
that
we
have.
But
what
I'll
describe
here
skin
in
the
draft
now
and
just
take
hope
that
we
might
be
able
you
a
little
better.
So
the
basic
idea
is,
if
there's
an
anchor
message
up
on
the
top
left.
O
O
Riya
has
hashes
of
the
data
packets
that
it's
authenticated,
so
this
provides
a
proof
that
cryptographic
proof
that
he
sent
her,
that
the
owner
of
the
private
key
listed
in
a
securely
transfer
to
anchor
those
the
most
the
data
packets
that
were
part
of
this
data
string.
Okay,
so
next
book
next
slide.
O
Necessarily
if
you
want
to
use
RSA,
if
you
want
to
you,
know
a
big
RSA,
then
and
you're
gonna
take
a
chunk
out
of
that
as
well.
So
by
making
a
treaty
we
can
so.
This
is
kind
of
like
a
Merkel
tree
structure.
Here.
By
making
a
tree,
we
can
have
a
signature
at
the
root
of
the
tree,
which
then
provides
integrity
for
child,
manifests
that
don't
have
to
look
themselves
hold
a
signature,
and
the
child
manifests
then
have
the
hashes
of
the
of
the
data
packets.
O
So
for
redundancy,
of
course
we
need
you
can
either
retransmit
the
manifests
that
you
want,
or
you
can
send
the
data
packet
hashes
multiple
different
times,
signed
by
a
different
tree
different
times
it's.
So
this
is
a
trade-off
of
a
signature
rate
versus
you
know:
redundancy
versus
latency
of
the
history
you're
trying
to
secure
right.
O
So
that-
and
so
this
is,
these
are
all
configurable
as
part
of
the
anchor
message
to
decide
to
determine
like
what
is
it
that
you're
going
to
be
sending
and
and
send
it
in
a
manner
that
it
matches
and
as
long
as
you're
getting
the
assigned
hashes
of
data
packets,
you
can
verify
that
all
the
data
packets
receiving
are
the
ones
who
expect
or
reject
Billingsly.
Yes,
the
next
level.
O
So
one
important
piece:
that's
all
these
things,
I've
said
so
far.
You
can
sort
of
get
by
Tesla.
All
right
test
was
a
spec
from
a
while
back,
which
provides
the
way
they
good
is,
is
a
symmetric
key,
but
they
don't
release
the
key
until
after
everybody
is
data
packets,
and
then
they
send
the
key
note,
and
then
you
can
tell
they
is
the
key,
the
data
packets,
that
we
had
the
ones
that
were
assigned
by
the
key
that
just
explodes
on
very
signature.
O
O
So
the
way
we
do,
that
is
that
the
intermediate
ambi
system
has
to
get
the
anchor
and
be
able
to
process
these
these
packets
and
authenticate
them
before
forwarding.
So
the
idea
is
this
is
an
idea
we
stole
from
from
the
ante
relay
discovery
from
a
couple
years.
Back,
that's
still
languishing
might
be
worth
looking
at
again,
but
the
the
idea
is
an
SG
joint
is
issued
and
because
we
have
the
source
as
part
of
the
SGA,
as
the
RPF
signal
goes
back
to
the
to
the
ambi.
O
An
intermediate
system:
it
now
can
do
a
DNS
lookup
on
the
universe,
I
the
reverse
source
IP
and
we
are
I-
think
it's
not
in
the
draft
yet.
But
the
plan
is
to
make
a
the
NS
type
here
and
to
use
that
to
expose
the
URL
for
the
anchor
message
and
then
the
anchor
message
provides
all
the
information
necessary
to
authenticate
all
the
source
source.
All
the
traffic
from
this
source
is
being
authenticated
through
next
time.
O
O
So
it's
really
hoping
that
this
audience
would
be
universally
interested,
uh-hum
or
close
to
I
and
I
understand
some
people
may
not
think
that
inter-domain
multicast
is
one
thought,
but
my
opinion,
that
is
the
essence
of
Engram
and
so
I'm,
hoping
that
we
can
look
for
ways
to
move
this
forward,
and
you
feedback
of
course,
is
very
welcome.
Next
slide,
it's
just
more
asking
for
two
things
and
yeah.
O
Right,
the
DNS
thing
I
haven't
seen
it
a
lot
I'm
interested
in
hearing.
If
people
do
have
problems
with
that
idea,
this
figure
we
can
understand
better.
Obviously,
if
this
whole
idea
is
it's
just
not
worthwhile,
I
would
like
to
understand
that
as
well
and
walk
away
before
I
spend
too
much
time
on
it
and
outside
that
yeah
I
would
like
to
make
it
just
as
solid
as
we
can
were,
depending
on
the
feedback
we
get.
We
are
probably
looking
at
taking
a
stab
at
at
an
implementation.
J
O
So
I
address
that
a
little
bit
in
the
draft.
It's
the
under
the
heading
of
comparison
with
Tesla.
The
basic
problem
is
that
Tesla
doesn't
provide
non-repudiation,
you
can't,
and
so
the
issue
is
that,
if
we
want
to,
if
we
want
to
let
both
the
receiver
perform,
authentication
and
a
network
element
perform
authentication,
then
Tesla
can't
do
it
because
by
the
time
by
the
time
you
release
the
key
either
the
the
intermediate
network
node
has
forwarded.
J
J
B
The
last
one,
the
feedback
on
the
DNS
thing,
I
think
real
a
discovery.
Amt
real
a
discovery
is
a
long
overdue
topic.
Like
you
said
there
was
the
eighteen
t
guys
came
up
with
a
draft
using
DNS.
Actually,
maybe
fifteen
years
ago,
someone
from
Sprint
came
up
with
a
similar
way
of
using
DNS
and
I.
Think
it's
worth
reopening,
not
just
DNS,
but
just
generally
speaking,
how
do
you
pick
a
relay
when
there's
a
bunch
of
them,
some
of
them
being
any
caste?
B
O
So
that's
another
point:
if
there
is
feedback
on
the
DNS
thing,
there
are
at
least
one
that
being
the
anti
relay
and
possibly
two
possibly
another
thing.
I
want
to
consider
using
the
fourth,
but
I
think
the
trick
is
pretty
good,
we're
finding
a
you
know:
RPF
source
related
thing
from
an
intermediate
node,
so
yeah.
If
you.
B
B
R
I
A
I
So
lost
without
you,
okay,
so
anybody
still
remembers
ITF
101.
So
we
discussed
basically
at
that
point
in
time
the
kind
of
revised
new
draft
that
came
out
of
prior
drafts,
in
which
way
you
know,
started
trying
to
deprecated
ASM
completely,
and
so
we
wound
that
down
to
deprecating
ASM
in
the
inter
domain
space,
not
but
not
in
the
intradomain
space.
I
So
that
was
the
agreement,
hopefully
basically
with
101
the
0-0
draft
of
that,
eliminating
the
resistance
that
we
had
in
terms
of
trying
to
get
all
the
way
into
deprecating
ASM
all
the
way-
and
you
know
one
of
the
reason,
of
course,
is
that
ASM
intradomain
is
still
widely
used
right,
so
there
is
really
no
replacement
for
the
best
form
of
ASM
by
dripping
in
enterprises.
You
know
to
replace
you
know:
20
thousands
s,
kimochi
state
with
a
few
group
states,
and
we
can
still
think
about.
You
know,
starting
to
retire
more
intradomain
I.
I
Think
operationally.
But
you
know
really.
The
primary
issue
from
the
operational
perspective
is
that
it's
a
really
good
thing
to
start
deprecating
on
the
service
provider
side,
because
that's
where,
basically,
the
service
providers
have
a
good
impact
on
getting
the
applications
to
move
to
SSM
right,
they
run
their
IPTV
shop.
They
basically
are
in
much
better
position
to
get
the
SSM
adopted,
while
in
the
enterprises
we've
seen
that
for
20
years,
it's
really
very
hard
for
them
to
force
applications
to
support
SSM
if
we're
lucky.
I
Basically
the
stuff
that
happens
on
the
service
provider,
side
SSM
wise
will
trickle
in
the
enterprises
as
well.
I
mean
these
days.
What
new
applications
exist,
they're,
all
the
ones
that
are
being
used
in
the
internet.
Now
the
enterprise
isn't
really
the
place
where
innovation
happens.
So
that's
why
I
think
we're
going
the
right
order
of
you
know
not
touching
the
enterprise's
inter-domain
right
now,
but
you
know
even
something
like
internet
to.
If
you
remember
the
discussion
we
had
in
before.
I
I
I
With
you
know,
explanations
like
the
one
I
had
on
the
previous
slide,
adding
text
to
discuss
the
MSTP
challenges
and
why
there
is
no
MSTP
for
ipv6,
so
kind
of
a
bunch
of
the
background
providing
further
evidence
of
you
know
how
really
dead
ASM
in
real
inter
domain
actually
already
is,
and
so
you
know,
maybe
we
can
still
rephrase
that
we're
really
not
killing
it
right.
It's
basically
already
dead.
Mstp
is
really
used
in
very
few,
inter
domain
deployments
already
only
so
yeah.
So
please
read
through
the
101.
I
Was
there
anything
No,
so
I
think
the
the
key
part
of
that
was
at
the
bottom
point
right:
expanding
the
scope
of
inter
domain,
so
one
of
the
tricks
was
what
is
it
actually
intra
and
Inter
domain?
And
you
can
have
different
views
on
it
right.
One
is
for
the
product
called
site,
so
app
in
person
will
tell
you
Oh
inter-domain.
I
We
really
want
a
SM
out
of
the
picture,
and
that
is
the
service
provider
offering
IPTV
services
that
goes
to
a
million
homes
and
where
you
definitely
don't
want
to
muck
around
with
in
sparse
mode
service
provider
tried
it.
It
took
them
in
many
cases,
six
years
to
get
the
bloody
IPTV
application
vendors
to
support
SSM.
In
many
cases
they
had
to
change
their
vendors
to
others,
but
now
we're
really
in
round
two
around
three
of
these
IPTV
deployments
and
I
would
hope
they
are
pretty
much
as
the
same
everywhere.
I
Why
don't
you
signal
a
source
address
together
with
it
right?
So
that
would
be.
You
know,
added
work,
we're
suggesting
to
be
done
here,
yeah
and
then
oh
to
was
just
a
fixes
right
nope.
So
this
light
so-
and
this
is
basically
the
stuff
that
I
primarily
wanted
to
talk
about
in
in
the
PIM
working
group,
so
the
associated
candidate
work
would
really
be
figuring
out.
I
How
can
we
get
the
classification
of
our
standards
into
shape
because
right
now,
older
standards
that
no,
but
he
should
use,
have
a
better
standard
level
than
what
we
want
them
to
use
like
IGMP
v2?
So
that
isn't
a
different
different
presentation
and
then
also?
How
can
we
get
completely
rid
of
em
SDP
right,
deprecating,
ASM
inter-domain
almost
gets
the
job
done.
I
Unfortunately,
MSTP
is
already
more
or
less
retired,
as
I
said
into
the
domain,
but
it's
heavily
used
in
Trudeau
main
for
the
MSTP
mesh
group
and
it's
actually
doing
a
pretty
decent
job
for
that
right.
But
if
we
want
to
kill
it,
I
think
we
need
to
basically
make
the
product
call
that
we
actually
would
want
to
use
for
mesh
groups,
which
is
RFC
46:10
ramped
up
with
all
the
operational
requirements
that
we
have
and
that's
reliability,
debug
ability,
troubleshooting
and
control
what
we've
learned
in
MSD
P
over
the
years.
I
So
the
proposal
is
there
one
draft
that
that
we
have
in
PIM
to
basically
get
us
to
the
you
know:
transport
over
TCP
for
the
reliability
flow
control
between
the
RPS
and
the
other.
One
would
be
yang
model
that
somebody
still
needs
to
write
or
hopefully
find
a
young
author,
where
we
can
add
it
to
one
of
the
existing
yang
drafts
or
updating
them.
The
ssme
application
development
recommendations
that
I
mentioned
in
before
I'm,
not
sure
what
other
you
know
outcome.
We
want
to
have
on
really
evolving
the
standards
bases
operationally
and
protocol.
I
Wise
of
you
know
our
you
know
core
framework,
but
these
seem
to
me
to
be
the
most
important
pieces
that
we
could
think
about
next
letter
so
conclusions.
So
the
authors
think
the
document
is
really
in
good
shape
right
all
the
strategic
concerns
for
adoption
should
have
been
eliminated
right,
and
so,
oh
yes,
so
overlooked
that.
So
that's
just
who
was
about
the
process
so
reminders
to
the
list
may
be,
may
be
good,
that's
great,
so
yeah.
So
in
London.
B
We
did
a
in
the
meeting
and
I
think
it
was
every
you
know.
Everybody's
hands
were
raised
in
favour.
We
took
it
to
the
list
last
week.
I
believe
we
still
haven't
heard
from.
There
hasn't
been
much
replies
on
the
list,
so
we
can't
adopt
this
until
folks
speak
up
on
the
list,
so
what
I
would
say
is
so
first
off,
let's
just
retake
a
poll
and
make
sure
nobody's
mind
has
been
changed
in
the
last
four
months.
I
B
So
we
don't
have
a
police
force.
The
best
we
can
do
is
write
drafts
and
BCPs.
That
say,
if
you're
going
to
do,
inter-domain
multicasts,
don't
do
ASM
do
SSM.
So
it
is
direction
to
the
world
that
when
you
deploy
multicast,
so
what
does
that
really
mean?
Because
again
we
don't
have
a
police
force.
You
know
jackbooted
thugs,
that
we
can
send
out
to
knox
everywhere
to
start
turning
off
ms
DP
and
other
things
or
filtering
we're
telling
people
to
filter.
You
know
everything.
That's
not
232
/e.
What
effectively
it
means
is
it
can
help.
B
You
know
the
mbone,
which
we
are
mbone
d.
The
mbone
does
exist,
it
is
the
multicast
enabled
portion
of
the
internet
and
it
is
primarily
i2.
So
i2
is
probably
90%
of
the
mbone
and
they
continue
to
maintain
an
MS
DP
infrastructure.
They
continue
to
support
inter
domain
multicast,
and
so
it
would
give
them
the
ability
to-
and
this
is
one
of
the
drivers
to
turn
this
off
and
explain
to
their
members.
This
is
why
we're
turning
this
off.
You
know
the
the
the
it
is.
B
I
I
Rights
I
mean
that's
I,
think
the
the
simple
pitch
or
so,
and
it's
hard
to
somebody
to
challenge
it
because
I
think
that's
pretty
true
right,
the
second
one.
Can
you
send
an
email
about
this?
You
know
filtering
of
232
I,
don't
think
we
had
that
recommendation,
part
in
it.
So
it's
a
good
one
that
no.
C
B
Remember
to
in
in
London
that
was
one
of
the
things
that
was
suggested
and
it
was
next
okay,
so
yeah
I
know
I,
don't
think
we
want
to
go
that
far,
it's
more
of
a
finger
wag
than
a
a
jackbooted
thugs
coming
to
your
network,
to
turn
it
off.
Okay,
but
another
benefit
Mike,
is
to
give
clear
direction
to
application
providers
outs.
B
People
outside
of
this
working
group,
who
just
think
that,
oh
we'll
just
you
know,
join
a
group
that
you
you
need
to
do,
SSM
that
that
here
is
you
know
a
BCP
BCPs
are
saying
you
know,
there's
an
RFC
that
officially
says:
don't
do
ASM
do
SSM,
so
it
helps
providers.
It
helps
operators
give
clear
direction
to
their
yeah
app
app
developers,
yeah.
I
B
It's
not
for
the
next
few
months.
If
you
want
to
send
an
email
right
now
you
can
so
so
you
know
when
we
took
that
informal
poll.
It
was
you
know
five,
oh,
so
that
was
I.
Believe
five
people
raised
their
hand
to
support
it.
Anybody
against
supporting
this,
this
draft,
who
doesn't
want
to
see
this
draft
adopted?
B
I
I
I
I
You
know
why
I
have
no
idea,
probably
because
we've
all
been
been
asleep
at
the
wheel
and
never
cared
about
processes.
Have
you
been
at
that
RFC
I
on
Monday
evening
kind
of
process
is
really
not
a
nice
thing
to
think
about,
but
you
know
after
decade.
Maybe
you
know
just
investing
a
little
bit
in
this
process
to
basically
make
sure
at
least
that
stuff
isn't
becoming
a
reason
why
people
do
the
wrong
thing.
I.
L
I
L
L
L
So
this
my
thought
would
be
person.
One
should
probably
become
historic
toward
a
prohibit,
but
double
talk
to
these
and
others
to
find
out
and-
and
of
course,
we
need
to
look
at.
Probably
you
know
either
worse
than
tours
and
see.
If
you
want
to
make
something
a
standard
you
generally
need
to
go
through,
like
implementation
report,
make
sure
well.
I
Right
so
yeah,
let
me
quickly
go
through
the
slide,
because
I
also
had
talked
with
operators.
You
know,
after
this,
the
deprecated
stuff
and
about
you
know
we
want
ASM
and
SSM
right.
So
so
the
this
stuff
is
related
right.
So
so
the
operators
think
they
do
not
need
to
go
through
IGMP
version
3
or
ml
db2,
as
long
as
they
do
not
need
SSM.
I
That
is,
you
know,
to
some
degree
true
right,
so
it
would
be
good
enough
to
stay
with
IGMP
v2
and
MLD
v1,
but
they
also
get
other
benefits
from
ml
db2,
as
are
it
from
IG
MPV,
ok,
typos
from
IGMP
v3
and
mo
d,
bad
typo,
ok
right
so
one,
for
example,
is
the
explicit
tracking,
which
is
one
of
these
other
issues.
Where
I
think.
We
also
need
to
point
out
that
you
know
these
latest
versions
to
provide
short
live
latency,
which
an
IPTV
is
extremely
crucial
and
then
run
all
charter.
I
J
Your
bullet
there's
a
little
misleading
as
well.
Craig
Cisco
says
wrong.
Fully.
Backward-Compatible
can
mix
two
and
three
well,
you
can
do
as
a
SM
without
I
mean
v3
supports
ASM.
It's
not
like.
You
have
to
fall
back
to
2
or
1
to
get
ASM
functionality.
V3
supports
ASM
yeah,
of
course
the
well
it's
just
it's
confusing
backward
compatible
can
mix
v2,
v3,
routers
queries
and
arbitrarily,
like
yeah.
You
can,
which
you
don't
need
to.
You
can
do
ASM
with
v3
I'm,
just
right.
I
I
Of
course,
you
can
perfectly
go
through
to
IGMP
v3
and
ml
DB,
even
if
you'd
have
nothing
on
board
with
ASL
with
SSM,
because
your
intro
domain,
you
spider
film,
whatever
good
stuff
you
want
to
do
in
your
domain,
don't
stick
to
the
old
protocol
version
right
and
then
also
any
mix
should
work,
and
now
we've
seen
basically
the
problems
in
the
past,
and
so
I
mean
that's
operational.
Experience
that
we,
you
know,
and
an
embodied
raft
may
want
to
mention.
I
I-
would
think
that
you
know
my
latest
problems
with
IGMP
v3
went
away
in
something
like
2010
when
the
last
snooping
switches
started
to
support
it
right
so
I
mean
if
we
have
some
timeline
to
to
really
give
more
confidence
to
operators.
That
would
certainly
be
not
wasted
right
so
and
then,
of
course
also
when
we
are
writing
something
operationally
down,
then
an
MD
document
would
be
the
place
to
state.
I
You
know
here
are
all
the
the
changes
we've
been
doing
and
deprecating
ASM
inter-domain,
but
we
really
want
to
have
you
know
a
full
internet
standard
for
intra-domain
ASM
and
that's
basically
around
you
know
the
the
other
draft
I
mentioned
right,
so
the
deprecation
in
the
domain,
and
then
these
these
recommended
these
discussions
right.
So
intradomain
is
fine
by
their
premise.
Preferred
majority
of
customers
I
would
think
the
majority
of
multicast
deployments.
I
You
know
the
work
that
we're
doing
interdomain
really
touching
whatever
he
is
doing,
and
then
we
got
into
all
the
IGMP
weekly
discussion
that
stuff.
So
how
do
we
make
the
you
know
the
majority
of
what
we're
still
making
money
from
unless
and
operate
a
vendor
is
is
just
selling
to
service
providers
right.
But
if
I
look
at
these
typical
service
vendors
that
sell
both
enterprises
and
service
providers,
we
don't
want
to
really
make
the
the
enterprise's
feel
scared,
and
so
that's
this
part
next
slide
right.
I
So
now
the
the
funny
protocol
list
right
so
RFC,
one
one,
one
two,
and
so
this
is
actually
the
only
interesting
document.
Everything
else
I
think
that
we
have
on
the
list
is
just
changing
the
status
right,
so
the
bad
ones
downgrade
the
good
ones
upgrade
right,
but
RFC
one
one.
One
two
is
two
things
in
one
on
once:
it
is
the
actual
specification
of
the
ASM
service
model
for
which
we
actually
never
built
an
ipv6
document.
I
And,
of
course,
as
we
said,
we
don't
want
to
duplicate
the
whole
ASM
service
model
right,
even
if
the
last
step
would
be
at
some
point
in
time,
say:
intradomain
pins,
our
spot
is
not
good,
but
intradomain
advisor
pin
is
I,
think
always
going
to
be
excellent.
For
you
know
the
applications
it's
built
for
right,
so
you
know
that's.
This
is
the
biggest
challenge
here.
My
proposal
would
really
be
to
ref
this
and
basically
come
up.
I
You
know
just
strip
out
all
the
IgM
p1
stuff,
add
ipv4
ipv6
in
in
the
rest,
and
that's
going
to
be
the
new
normative
full
internet
standard
for
the
ASM
service
model.
My
pet
would
be
my
proposal.
Hopefully
that's
that's
something
feasible,
because
this
is
something
the
holy
grail
of
multicast
right,
so
upgrading
RFC
saw
would
not
would
try
that
we
don't
touch
any
of
the
actual
content
they're.
Just
you
know
v4
v6
and
get
rid
of
all
the
IGMP
v1
stuff.
I
I
J
C
I
Yeah
so
I
mean
the
upgrade
and
downgrade
for
all.
These
documents
is
pretty
obvious
right,
so
the
old
ones
downgrade
the
better
ones
upgrade
so
4604,
that's
SSM!
That's
the
service
model
for
before
and
v6
upgrade.
Then
we've
got
35
90
we'll
have
to
check.
If
that
is
actually
you
know
well
adopted.
So
that
seems
to
have
been
an
addendum
to
I,
Jim,
pv3
or
ml
db2.
I.
Think
so
we'll
need
to
check
that
in
more
detail.
I
If
that
should
become
part
of
you
know
the
Catechism
in
full
standard,
then
we've
got
the
most
interesting
one.
Just
you
know
from
the
status
and
that's
the
lightweight
IGMP
v3
ml
d
v2,
which
is
kind
of
removing
the
nasty
bits
from
IGMP
v2,
IGMP,
v3
and
ml
db2,
which
is
the
exclude
sources
list
which
we
never
really
used.
So
I
have
no
experience
about
deployment
stuff.
I
L
Stick
here
so
yes,
the
interesting
thing
is
when
you
want
to
make
something:
an
Internet
standard,
you
actually
look
at
the
spec
and
you
decide
which
parts
have
like
white
implementation
and
interoperability,
and
all
of
that
you
actually
take
stuff
out
of
the
spec
that
hasn't
had
it.
That
is
not
nature
enough.
In
general,
like
we
did,
I
picked
it
with
him,
with
between
I,
actually
took
some
stuff
out
of
him
off
its
border
border.
J
I
I
I
have
no
strong
opinions
right,
I'm,
happy
if
we
don't
have
to
go
through
the
trouble
of
doing
this
stuff.
Just
if
people
stand
up
and
feel
strongly
that
this
stuff
has
enough
stuff,
then
I
would
obviously
agree
that
we,
you
know,
do
the
job
on
that
as
well.
I'm,
more
interested
in
what
you
were
saying
with
respect
to
what's
the
process,
I
was
hoping
looking
at
all
the
documents
that
seemed
to
have
been
updated
from
proposed
to
full
standard.
N
I
Q
Jeffrey
from
juniper,
this
is
related
to
sticks,
comments
related
to
the
exfoliant
sources.
If
we
upgrade
the
original
itv3
ml
to
be
two
to
four
standard,
then
we
neither
decide
if
we
want
to
remove
the
excluding
sources
function
and
I'm.
I
was
actually
not
aware
of
a
fifty
seven.
Ninety,
if
the
that
I
with
the
RGV
3ml
TV,
is
without
the
exclusion
sources,
then
we
might
as
just
consider
upgrading
that
57
92
for
standard
and.
I
That
would
be
an
interesting
question
right
if
I
just
take
a
GMP,
v3m,
LDV
and
basically
try
to
change
the
text.
To
say
that
you
know
the
exclude
list
must
be
empty
right.
What
difference
would
that
be
over
50
790,
because
I've
50
790
rewrote
everything
right,
and
so
that's
going
to
be
hard
comparison.
Maybe
that's
that's
one
of
the
tough
jobs
to
do,
because
I
would
agree
that
if
we
need
to
arrest
us
that
hasn't
been
used,
it
would
be
exactly
that
you
know
exclude
list
having
anything
more
than
an
empty
list
right.
I
So
if
that's
the
thing
we
could
do
to
basically
say:
oh,
we
don't
need
50
790
we're
just
removing
the
exclude
list,
but
there
may
be
other
product
called
simplifications
that
57
90,
so
we'll
need
to
check
the
authors
list
and
figure
out
if
any
one
of
them
is
willing
to
to
help
with
the
effort,
because
you
know
when
this
stuff
happened.
I
was
on
the
position
of
you
know.
Having
worked
in
the
vendor
that
had
spent
a
humongous
amount
of
time
to
get
the
full
versions
of
the
protocol
is
implemented.
Q
I
But
remember
RFC,
1,
1,
1
2
doesn't
even
talk
about
ipv6.
We
have
no
normative
document
for
the
ASM
service
model
in
six,
so
I
think
it
would
be
definitely
good
to
to
ref.
You
know,
then
you
know
split
one
one.
One
two,
you
know
just
extract
from
one
one.
One
two,
the
service
model,
which
is
the
50%,
then
comes
the
I
gene,
p1
spec,
so
we'll
just
take
the
first
part
at
v6
to
it.
Something
like
that.
Well,.
I
I
L
Running
yeah,
just
a
just
quick
comment
to
Jeffrey,
so
we
don't
have
to
touch
anything
else
in
order
to
move
that
supposed
and
ago
internet
standard,
it's
up
to
us
or
I
want
to
deprecate
or
whatever,
versatile
one.
That's
a
different
discussion
is
what
sorry
do
we
want
to
touch
person,
one
like
deprecated
or
whatever?
That's
a
separate
discussion.
There's
nothing
automatic!
It
can
make
new
one
without
touch.
R
I
Information
on
that
one
wasn't
because
it's
not
widely
deployed
or
so,
but
because
it's
doing
things
implicitly,
it's
not
changing
anything
on
the
wire
and
they're.
Basically,
these
ideas,
policies
that
are
saying
show
me
differences
on
the
wire.
Then
we
can
make
it
standard
now
we're
actually
having
the
same
discussion
with
the
explicit
trekking
where
the
changing
on
the
wire
is
basically
that
traffic
flows
faster
or
you
know,
stops
faster
and
igmp.
Snooping
obviously
does
the
same
thing,
but
you
know
I
jumpy
snooping
has
this
of
a
layer
to
solution.
