►
From YouTube: IETF102-I2NSF-20180718-1330
Description
I2NSF meeting session at IETF102
2018/07/18 1330
https://datatracker.ietf.org/meeting/102/proceedings/
A
A
Here's
the
the
milestone!
Okay,
we
have
adopted
quite
a
few
working
group
drafts
and
our
working
group.
The
primary
goal
is
to
define
the
data
models
to
network
security
functions
and
we
have
achieved
quite
a
lot.
There
are
quite
a
few
there's
some
left
over
work
and
ad
wanted
us
to
finish
them
as
quickly
as
possible
by
next
April.
No
next
February.
A
B
B
In
this
eckerton
we
implemented
the
registration
interface,
security
policy,
translation
and
automated
police
provisioning,
first
registration
interface,
I
Tennessee
Futurecast
and
as
their
capabilities
to
scourge,
controller
security
controller,
the
high-level
policy
into
low-level
policy.
If
his
security
controller
cannot
find
the
proper
NSA
security
controller
cast
the
instantiation
of
NSA
to
developers,
management
system
and
then
develop
developers,
management
system
registered
an
sf2
switch
controller,
and
this
is
the
young
data
model
of
a
registration
interface.
B
B
B
Is
the
example
of
making
the
low-level
c4
firewall
and
right
blue
boxes,
though
example
making
low-level
policy
for
web
filter?
This
is
the
hexagon
topology,
and
this
is
this:
is
the
environment
team
in
Paris
I.
This
is
implementing
environment,
we
unloaded
our
source
code
and
you
get
hop
and
you
can
see
the
demo
and
YouTube.
B
A
So
this
next
one
is
armor
STM,
controlled,
IPSec
configurations,
so
the
presenter
will
be
talking
remotely
afterwards
since
there's
another
model
in
this
particular
model
that
defined
two
cases
like
where's
the
controller
only
sending
down
the
configuration.
Another
one
is
element
network
service
function.
Doesn't
security
function,
doesn't
support
a
key
and
actually
there's
a
sir
model.
So
after
this
presentation
or
like
Carol
to
to
talk
about
the
sir
model
and
then
see
how
that
could
be
made
me
integrate
it
together.
Okay,
so.
A
D
C
So
we
think
we
are,
we
are
trying
to
define
as
an
architecture
for
the
management
of
IPSec
security
Association
using
an
SDM
model.
So
we
have
a
centralized
controller.
Providing
the
information
are
to
establish
dynamically.
All
these
IPSec
security
Association.
We
define
two
cases
in
the
first
case.
The
assumption
is
the
network
security
function
will
have
a
night
person
to
implementation,
so
the
controller
will
need
to
configure
that
I'm
implementing
on
other
pieces
of
different
databases
and
relating
with
IPSec
and
then
the
case
to
where
the
assumption
is
the
nerd,
more
security
fashion.
C
Anderson
has
any
version
of
implementation,
so
the
only
thing
we
have
is
the
kernel
to
board
for
Ivy
set.
So
the
goal
behind
the
draft
is
to
define
the
interface
interfaces
required
to
manage
and
monitor
all
the
Ivy
sex
again,
the
Association
in
the
NSF,
taking
into
account
these
two
gates
is
case,
one
and
case
two
for
case
one.
We
will
need
a
jump
model
for
Ike
version,
two
SPD
d
ad
and
models
that
allows
to
collect
state
data
for
aggression
to
and
the
sa
ID
for
the
IPSec
security
associations.
C
Of
course,
in
the
case
we
don't
have
Ike,
we
don't
need
PA
D,
the
only
thing
we
need
to
be
fine.
There
is
this
in
the
NS
ad
and
actually
our
dev
already
passed
the
jump
model
for
all
these
cases,
and
all
these
are
required
information.
So
next
one
so
here
just
a
summary,
you
can
find
the
explanation
in
the
internet
draft
case
100,
as
you
can
see
in
the
safe
I,
can
type
e6
support,
so
they
controlling
will
need
to
provide
that
information.
Based
on
the
jumbo
that
we
have
defined
the
case.
C
There's
no
key
management
protocol
in
an
NSF
so
in
the
staff
is
simpler.
So
this
security
controller
following
the
typical
Sdn
controller,
has
everything.
So
you
need
to
create
all
the
state
and
create
a
VIP
security
associations,
because
actually
the
NSF
doesn't
have
our
IQ
implementation
migration
to
implications
next.
D
C
Actually
related
with
that
I
just
execute
the
Association.
The
only
thing
you
need
is
to
get
a
black
plastic
data
because,
after
all,
like
version
2
will
create.
That
is
actually
with
the
association
for
you,
based
on
the
information
on
this
ID
and
the
rest
of
the
information
in
case
there's
no
I
person.
C
So
the
only
thing
we
need
to
deal
with
his
SPD
to
include
I,
detect
policies
and
collects
on
the
state
data
and
then
to
create
to
configure
to
the
latest
data
about
the
basic
security
associations
that
they
are
controlling
has
created
based
on
the
information
are
provided
by
the
administrator
you
seen.
Typically
the
northbound
API.
C
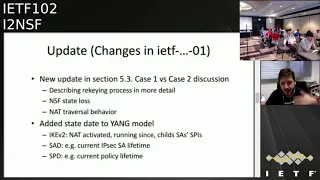
So
from
the
last
version
we
provide
a
nice
idea.
We
didn't
have
any
presentation,
because
it
was
a
minor
modification
that
right
now
and
I
have
an
update
in
Section
803
in
the
discussion
about
case
one
on
parcel
case
2,
where
we
describe
a
little
bit
the
recurring
process
and
now
in
more
details.
We
have
several
step
there
like
an
algorithms
explaining
how
to
do
it
in
case
in
case
or
what
happened
with
the
NSF
crashes,
and
then
it
doesn't
have
any
state
about
IPSec
or
what
having
the
naturally
so
behavior.
C
C
So
here
a
few
slides
about
is
their
natural
muscle
burn.
So
it's
this
is
update,
let's
not
run
okay,
so
the
configuration
in
case
one
basically
is
fairly
easy,
because
the
only
thing
you
need
to
I
mean
I
Gresham
to
is
in
the
NSF
and
has
a
mechanism
to
detect
McRoberts.
Also
little
configuration
there
in
case
to
it
relates
on
the
assumption
that
the
security
controller
knows
it
comes
on.
So
you
can
know
this
where
the
network
devices,
based
on
that
the
controller
you
to
starving.
C
Udp
or
ESP
over
TCP
etc,
and
we
have
that
information
in
there
in
the
young
model
next
one
about
the
regime
again
case.
One,
of
course,
is
one.
We
have
ignition
to
make
version
two
already
handles
there.
We
keep
the
ringing
part
like
this.
We
don't
have
that,
and
everything
is
saved
to
the
security
control.
We
need
some
kind
of
procedure
to
do
the
Ricky.
Actually,
what
we
have
designed
is
something
simple
in
the
sense.
C
What
we
do
in
summary
is
security
control,
we'll
create
the
amount
security
Association
in
both
NSF's
mall
and
that
McGee
will
start
when
we
receive
notification
from
the
NSF.
One
of
the
NSF
may
be
both
saying
some
particular
at
this
executive
session
is
going
to
spires
firing,
and
then
we
grade
the
amount
security
Association.
First,
when
we
have
confirmation
the
inbound
security
Association
out
there,
and
then
we
install
the
outbound
security
associations,
and
then
in
that
part,
after
that,
we
can
remove
the
old
IPSec
security
Association.
C
So,
regarding
the
implementation
we
have.
Actually
we
have
a
NSF
implementation
for
case
one.
We
have
the
Ike
version
two
based
on
Strongsville
and
regarding
to
the
net,
confront
yelling
fermentation
we're
using
metal
beer.
This
is
a
linux-based
implementation
for
case
two.
We
are
just
using
another
beer,
no
need
for
a
version,
two
implementation,
and
we
have
been
able
to
go
very
basic
configuration
about
the
stablishing,
this
IPSec
security
Association,
but
just
using
a
not
compliant
using
the
terminal
from
another
another
machine.
C
So
what
do
we
needs
to
work?
In
the
security
controller
side?
We
have
explored
only
end
of
in
daylight
and
on
earth.
We
have
the
aim.
We
have
be
able
to
configure
in
a
self
in
a
very
basic
mode,
using
both
controllers.
We
have
all
the
Eleanor.
No,
but
I
can
assure
you.
We
still
need
a
lot
of
work
there.
As
you
know,
this
piece
of
solar
are
complex,
so
we
are
fighting
with
them
at
this
point
our
goal.
C
Actually,
we
would
like
to
have
a
complete
proof
of
concept,
at
least
an
autonomous
way
to
receiving
notification.
What
happened
with
one
NSF
is
crap
is
crushing
or
during
the
wreak
a
period,
so
we
are
working
on
that,
so
that
is
part
or
it
related
with
the
next
slide,
please
next
so
to
be
done.
Of
course,
what
we
need
is
review
the
jump
model
in
the
current
stage.
C
We
have
detected
some
minor
correction
that
we
will
update
in
the
next
revision,
but
we
receive
pole
pounders
review
some
time
ago,
but
of
course
we
ever
say
that,
but
we
require
more
reviews
for
an
expert,
of
course,
and
a
little
imitation
level.
It's
clear.
We
need
to
continue
the
work
in
the
controller
side,
we
would
like
to
have
a
complete
or
not
autonomous,
is
scenario
list,
even
if
it's
small
list
to
see
how
everything
evolves.
C
Based
on
all
the
notification
we
have
designed
out
all
the
information
we
have
the
jam
hall
of
the
sitter,
and
we
would
really
appreciate
collaboration
in
this
side
because
I'm
pretty
sure
there
are
more
expert
in
the
road
and
out
there
that
are
working
with
implementation.
We
have
sit
down
in
the
hackathon
and
we
would
need
some
help
on
this
part.
So
that
is
my
presentation.
I
have
been
I
have
tried
to
be
short
just
to
promote
some
discussion.
If
you
have
any
question,
yes,
let
me
know.
Thank
you.
Thank.
F
Frank
Safari
hello.
Firstly,
I
want
to
say
that
I
think
that
that
that
is
a
good
draft,
because
80s
are
proposed
to
our
radical
solution
for
the
industry.
Right
now,
for
example,
for
the
Espeon
management
and
provision
mean
it
is
kind
of
automatic
IPSec,
VPN
Turner
Construction
solution.
So
this
document
is
a
very
good
input
for
second,
a
second.
A
second
comment
is
I.
F
Think
during
our
previous
discussion,
whether
it's
my
main
list
or
by
some
of
language,
scholarship,
I,
think
the
biggest
question
or
biggest
concern
of
current
draft
is
mainly
on
the
case
to
on
the
you
know,
on
the
hardwood
directory,
configure
or
manager.
The
session
key
and
the
related
accession
configure
special
continue,
chattering,
attributes
directory
to
the
CP
to
the
pier
so
I
yeah,
actually
I,
I.
F
Think
your
crystal
solution
is
one
way,
but
there
are
still
other
way
based
on
the
STM
control
decentralized,
the
way
to,
for
example,
where
we
can,
where
we
can
calculated
the
key
and
the
hallway
distributed,
and
so
but
I
I
kind
of
think
this.
These
have
some
trade-off
between
the
security
and
the
provision,
efficiency
or
the
scalability.
F
So
I
would
like
to
hear
more
discussion
and
comments
on
this
part.
Should
shoot
away,
supplanter
people,
ways
to
probation
them
and
how
to
say
aye,
I,
think
I,
think
I
found
my
personal
view.
I
think
her.
The
crystal
solution
has
has
its
own
value
and
its
own
scenarios,
but
we
master
have
a
good
assumption
that
the
controller
and
the
manager
link
between
the
controller
and
the
peer
has
we're
protected
met
madmen
so
to
protect
her
to
protect
her.
F
C
A
the
main
thank
you
think
about
that.
The
main
part
there
is
one
of
the
key
question.
There
was
obviously
the
SDN
controller.
The
security
controller
needs
to
create
all
the
IPSec
security
Association
in
the
NSS.
That's
clear
and
one
of
the
parameter.
Of
course,
the
key
you
will,
you
will
have
to
use
and
that's
the
the
particular
are
common
there.
So
the
concern
might
be
okay.
The
security
controller
is
seeing
in
some
point
at
some
point
anything
the
keys
that
will
be
installed
in
the
NSS.
C
The
question
is
obviously
following
this:
the
Empire
in
the
controller
is,
it
should
be
a
trusted
entity.
Obviously
you
have
security
associations
between
the
NSF
and
the
security
controller
based,
for
example,
you're
using
that
counts,
you'll
have
TLS
or
SSH,
so
the
distribution
itself
is
not.
Is
it's
not
a
problem?
The
problem
or
the
the
comments
we
have
received
is
the
security
controller
will
need
to
create
a
random
key
that
we
finally
be
installed.
It
will
be
finally
installed
in
the
NSF.
That's
the
key
point
so
solutions.
C
There
are
a
recent
draft
as
well
that
written
by
Dave
Carroll.
Well,
they
want
to
or
to
avoid
that,
for
example,
using
some
kind
of
difficult
saying.
Okay,
the
controller
doesn't
see
the
key,
so
the
key
is
generated
by
the
NSF
itself,
so
they
let
the
security
controller
cannot
get
those
keys
from
anywhere
right.
C
G
A
H
Hi,
so
thanks
for
bringing
this
and
got
two
questions
well,
the
first
is
well
I
still
don't
see
the
value
in
your
case
too,
because
any
NSF
is
running
on
some
platform
could
be
usually
Linux
could
be
Mac
OS
the
windows,
even
phones,
every
one
of
them
has
an
IP
to
demon.
I
think
you
demons
are
ubiquitous,
there
is
ubiquitous,
is
TLS
implementations,
so
they're
everywhere.
We
don't
really
have
this
tour
and
a
stuff
that
doesn't
have
an
IQ
to
implementation,
and
the
other
thing
is
that
well
it's
a
matter
of
key
hiding.
I
Yeah
good
question:
a
quick
comment
to
the
presenters
equine
wise,
Francisco
I.
Think
the
contribution
of
the
yang
models
is
it's
very
valuable
and
case.
One
is
a
very
valuable
as
well
just
to
put
what
maybe
you
all
have
said
in
a
different
light
or
what
some
people
have
been
saying
when
we
think
of
caen
distributing
configuration
through
a
yang
model,
that's
reasonably
safe,
because
a
third
party
that
would
see
the
configuration
can't
do
a
tremendous
amount
with
it.
I
C
The
thing
can
I
say
something:
okay.
Now
the
thing
is
in
our
view,
in
our
experience,
for
example,
when
when
the
SDM
parenting
started,
for
example,
the
the
routing
protocols
are
not
that
in
the
routing
device
so
are
moved
to
the
head
to
the
Sdn
and
basically
their
routing
device
is
young,
merely
switch
our
processing
flows.
C
Don't
understand
why
NSF
should
be
there.
Is
there
any
requirement
for
NIH
and
NSF
should
be
this
one
or
this
one
or
this
requirements
in
terms
of
CPU
memory
or
everything?
I,
don't
know
here.
We
have
seen
some
comments
also,
and
they
manually
say:
maybe
your
who
we
can
have,
for
example,
thousands
of
nodes
creating
and
then,
if
you're,
saving
some
memory
or
some
CPU
could
be
variable.
So
what
I
see
is.
Obviously,
if
you
have
a
constraint
device,
there
is
a
malleable
thing
there.
C
When
are
we
saying
this
word
is
not
valid
in
general,
I
mean
in
this
working
group
to
or
you
know,
to
provide
that
kind
of
models
to
more
constrained
devices
to
save
memory.
Save
CPU
I
cannot
tell
I'm
working
also
with
IOT
stuff,
and
then
the
Sun
of
this
idea
are
coming
from
there.
Maybe
maybe
you're
not
using
IPSec,
maybe
you're
using
DTLS
or
DTLS,
but
you
know
I,
don't
know
what
are
the
NSF
requirements,
terms
of
capacity
or
capabilities
that
NSF
should
be
should
be,
should
have
in
that
case,
I.
Remember.
A
During
our
interim
meeting
on
this
subject,
we
agreed
that
this
document
should
clearly
writing
down
the
security
risks
associated
with
model
to
write
so
that
for
like
IOT
device
with
very
constraining
resource,
they
can
utilize
that
with
acknowledge
the
risk
they
are
taking.
That's
I
thought
that
was
the
agreement
right.
C
In
fact,
the
ID
has
a
security
section
explaining
precisely
that
in
the
sense,
ok,
of
course,
you
have
a
trusted
entity
which
is
acting
a
key
distribution
center.
Obviously,
that
trusted
entity
is
not
trusted
anymore.
For
some
reason:
Tatian,
that's
clear,
but
I
think
it's
as
you
mentioned.
It's
a
trade-off.
Somebody
I
think
Frank
mentioned
that
it's
a
trade-off.
Obviously,
then
I
say
be
simple.
C
Even
in
terms
of
implementation,
you
need
to
deal
with
just
with
the
SPD
jump,
part
the
immoral
part,
and
this
is
ID.
We
are
sending
that
information
and
it's
simpler.
You
need
to
deal
with
the
kernel
part
and
just
that
then
in
case
one,
the
ninja
need
to
add
the
information
for
the
BA
D.
There
Ike
version
two
information,
the
SPD
of
course
and
I
said
he
just
a
collecting
data,
but
you
know
what
we
see.
What
we
see
is
there
is
value,
even
in
the
case
to,
of
course,
there
is
a
risk.
C
H
Well,
I
understand
that
it's
just
that
I
personally,
don't
see
much
see
the
case
for
IOT
devices.
That's
do
IPSec
there.
Well,
they
might
do
for
themselves,
but
not
a
functioning
as
an
network
security
function
at
any
rate,
I
think
this
debate
is
going
to
continue
at
the
IPSec
me
working
group.
Later
this
days.
Yeah
we'll
see
you
there.
Okay.
J
Okay,
I'll
try
to
do
this
really
quickly,
so
we've
I
work
in
a
SD
Wang
company,
they're,
actually
acquired
by
someone
bigger,
so
I've
been
working
on
this
problem
for
a
while,
and
we
have
a
real
case
where
we
actually
do
want
something
case
to
like.
We
don't
want
to
implement
an
IKE
v2
in
our
end
nodes,
but
we
need
the
security.
You
know,
as
Brian
said
as
your
offset
there's
key
hygiene
and
we
don't
want
the
Anna
or
we
I'm.
J
Sorry,
we
don't
want
the
central
controller
knowing
these
keys,
so
we
put
together
this
controller
IP
and
whether
it's
a
case
or
a
case,
three
I,
don't
know
it
doesn't
really
matter.
There
may
be
a
Rafa
was
saying
that
maybe
a
point
were
you
wanting
really
a
small
IOT
device
that
doesn't
do
any
key
management,
so
what
we
put
together
is
really
a
simple
idea:
can
we
pop
the
first
slide?
J
So
what
is
this
controller
I?
It's
a
key
exchange
method,
and
that's
really
all
it
is
we're
not
trying
to
create
a
protocol
that
manages
the
NSF.
This
is
something
that
would
be
suitable
for
embedding
in
Rafah.
The
submission
or
something
else,
the
concept
is
really
simple:
we're
doing
diffie-hellman,
so
each
each
peer
creates
their
own
diffie-hellman
pair
they're,
going
to
send
their
public
values
up
to
the
controller.
The
controller
will
distribute
out
an
entire
list
of
everybody's
public
keys,
and
now
every
node
can
create
a
shared
secret
with
every
other
node
in
the
network.
J
J
We
don't
want
peer-to-peer
messages
because
we
have
topologies
whether
it's
possibly
only
one-way
communication
we
have
topology
is
where
we
don't
want
the
latency
of
doing
an
Ike
setup,
and
you
know
I
think
people
have
talked
on
the
list
about
how
many,
how
many
RSA
is.
Can
you
do
in
a
second
there's,
a
little
more
to
it
than
that
so
anyways?
If
you
look
at
it,
that's
all
we
did
now.
We've
got
our
keying
up.
J
It
sounds
like
that
was
really
easy
and
now
we're
done,
but
the
problem
is
synchronized,
so
we
have
to
rekey
all
these
devices
fairly
often
right
keys
gets
stale.
We
don't
want
to
use
these
keys
forever.
So
what
happens
when
one
purely
keys
they're
going
to
send
a
new
key
up
to
the
controller?
The
controller
now
has
to
distribute
that
to
the
other
peers,
they're
all
going
to
get
it
at
a
different
period
of
time,
and
so
keeping
this
all
synchronized
is
an
issue.
That's
something
you
have
to
worry
about.
J
J
So
synchronization
is
where
it
comes
down
to
I'm,
going
to
speak
a
little
more
to
this
and
I'd
be
sick
of
me,
so
I'll
be
really
quick
in
the
draft.
We've
got
four
rules
that
you
have
to
you
have
to
follow.
We
spent
a
lot
of
time
kind
of
proving
this
out
and
reducing
it
down
to
four
simple
rules.
If
we
follow
those,
we
have
state
machines
that
now
can
support
all
of
the
synchronization.
We
can
very
large
networks,
even
with
you
know.
J
In
our
cases,
tens
of
thousands
of
nodes-
and
it
all
works-
everything
can
be
done
simultaneously
if
it
needs
to,
but
that
synchronization
is
very
loose,
so
one
one
person
can
rekey
at
one
point
in
time.
Another
peer
can
receive
those
keys
at
a
later
point
in
time.
In
fact,
they
can
receive
those
keys
and
decide.
I,
don't
have
the
time
to
deal
with
it
right
now
and
I'll
react
to
it
later
it's
loose.
If
all
works
everything
comes
out.
Security
needs
the
big
thing
in
this.
J
A
J
We
had
methods
so
we've
we've
indicated
what
needs
to
be
in
that
message
message.
Well,
you
know
what
are
the
fundamental
units
but
I'm,
assuming
that
a
night
to
an
ACEF
protocol
or
somebody
else's
protocol
is
what's
in
preparing
this?
Okay
and
there
are
requirements
on
there.
You
need
to
have
a
trusted
authenticated
connection
to
your
controller.
You
don't
trust
your
connect,
your
controller
all
bets
are
off.
This
would
be
pointless.
Thank
you.
I
have
I,
have.
C
Yes,
basically,
the
thing
is
assuming
we
are
using
V,
V
helm
and,
of
course,
if
the
SDN
controller
is
attacked,
then
we
may
have
a
mug
in
the
middle,
possibly
mine,
the
middle.
But
obviously
this
is
better
because
in
the
end,
you
don't
see
their
kids,
the
final
kiss
but
I
thinking
that,
for
example,
looking
at
the
case
two
we
have
where
we
send
all
the
IPSec
security
Association
information.
C
Instead
of
sending
the
key,
you
could
stand,
for
example,
or
the
public
key,
the
diffie-hellman
public
key
right,
correct,
that's
right
in
the
end,
in
the
end,
what
we're
it's?
It's
we're,
keeping
the
same.
There
may
be
a
little
something
we
need
to
change,
but
what
I
see
is
if
I
send
that
information.
This
is
the
IPSec
security
Association
you
I
won.
We
want
you
to
configure,
but
instead
of
sending
you
the
key
that
I
again
already
I,
meaning
security,
controller
I'm,
sending
you
the
public
key
of
the
other
side
correct
so.
J
C
That
only
the
peers
ago,
so
so
that
that's
that's
fine,
because
in
the
end,
there's
still
to
me
to
me
I
think
your
presentation
is
saying
that
and
I
and
I
agree.
This
case
too
is
I.
Don't
I,
I,
don't
say
case
three
or
what
I
see
is
case
two,
but
with
a
modification
that,
instead
of
sending
the
the
wrong
public
key
sorry,
there
are
all
session
key
you're
sending
the
public
key.
So
the
NSF
is
generating
the
year
correct
and
we.
J
L
At
you,
sorry,
this
kentley,
I
chide
someone
break
the
tie
here.
I
think
there's
a
distinction
what's
being
mentioned
right,
so
I
think
the
way
Rafael's
merchants
are
similar
to
the
scheme
that
you
guys
proposed,
but
that,
in
the
sense,
this
controller
is
the
man
in
middle.
Ask
that
right,
so
I
think
I
think
that's
a
wrap.
I
was
saying
that
and
that
it
is
using
your
Duffy
helmet,
but
then
is
generated
by
the
controller
versus
having
one
side
generating
and
passing
it
through
the
controller.
That's
my
understanding.
The
difference.
F
Two
questions:
first,
one
through
your
way
through
your
mentor,
though
you
achieve
what
you
achieve
the
user,
you
you
calculate
either
the
pairwise
session
key
among
among
each
each
pair
of
the
pier
right
like
that
classical
I.
Okay,
he
was
in
right,
correct,
okay
and
okay.
This
is
a
rank.
One
question
for
credit
kitchen.
Secondly,
in
addition
to
the
session
key,
how
about
SAE
tributes?
Other
si
attributes
to
use
share
the
same
attributes
among
other
communication
peers
or
still
the
pairwise.
J
Supposed
to
be
communicating,
okay
in
our
in
our
method,
we
added
some
ability,
for
you
could
almost
call
it
negotiation
when
you
have
cases
typically,
an
SDN
Network,
you've
just
told
everyone
you're
running
a
SGC
m256
period
and
nobody
has
to
negotiate
anything.
But
there
are
times
where
you'll
be
doing
migrations.
J
You
may
be
moving
too,
you
know
from
aes-128
KS
256,
and
you
can't
you
don't
want
a
red-letter
day
where
traffic's
gonna
stop
you're
gonna
want
to
tell
people
to
migrate,
and
so
how
do
you
then
have
people
figure
out
when
there
is
no
like
between
them?
That
hey
I
can
only
do
this,
but
I
can
I
can
only
do
a.
J
F
I
Brian
Weiss
so
I
think
Rafael.
What
you're
saying
is
the
the
state
machine
by
which
you
today,
in
case
to
when
you
push
down
keys,
could
be
the
same.
State
machine
is
used
for
pushing
tentatively
humming
Keys,
as
opposed
to
our
draft
kind
of
implies.
A
broadcast
model
by
the
controller
is
that
right,
yeah
that
the
thing.
J
But
it
doesn't
anything
I
guess
a
peer
sends
its
public
key
to
the
controller.
Oh
all
right,
then
the
controller
sends
it
out
to
all
the
other
peers,
how
it
sends
it
whether
it's
in
an
individual
message
to
each
other
peer
by
the
way.
When
you
want
to
talk
today,
if
here's
his
key
or
whether
it
broadcasts
it
out
as
one
big
ears
day's
key,
that's
protocol
dependent.
So.
C
We're
not
my
hug
a
my
my
my
comment.
My
previous
comment
was,
of
course,
in
some
point.
The
controller
needs
to
say
an
IPSec
security,
an
IPSec
security,
Association
inbound
outbound
to
the
different
two
different
NSS
right,
for
example,
for
every
gig,
correct
you're,
sending
the
information
what
we
are
doing
right
now
in
case
two,
we
send
all
the
information,
including
the
key
for
the
inbound
and
the
key
for
the
outbound
okay.
C
So
so
what
we
see
is:
okay,
let's
not
send
that
session
key
just
sent
some
key
material,
diffie-hellman
key
material,
so
the
NSF
just
need
to
create
the
session
key.
So
the
session
key
is
not
seen
by
the
security
controller,
but
the
security
controller
still
has
all
the
information
about
the
IPSec
security
Association
as
Sept
the
key
material
that
will
be
used
in
the
inbound
and
outbound
correct.
J
So
so
a
slight
difference,
sir,
to
your
state
machine.
You
were
talking
about
doing
synchronization
sending
out
the
inbound.
Si
is
first
in
the
outbound.
Si
is
later
that
would
not
be
needed.
With
this
method,
you
could
simply
send
out
the
si
information
with
the
public
keys
and
the
convenient
NSF's
can
then
complete.
They
can
handle
the
synchronization
of
knowing
how
to
install
the
inbound
and
waiting
for
the
appropriate
time
to
install
the
app
app
that.
C
You
know
when
we
thought
about
the
that
algorithm
we
have
in
our
ID
was
you
know
to
be
pretty
sure
that
we
have
the
inbound
first
and
then
the
outbound?
So
when
the
unbound
is
installed
in
the
kernel,
everything
goes
there.
I
mean
the
flow
will
go
using
the
the
new
outbound,
so
the
inbound
in
the
other
side
will
really,
but
we
also
thought
about
saying.
Okay
here
you
have
outbound
are
inbound
to
one
and
a
set.
C
Obviously
you
will
optimize
the
number
of
messages
between
the
the
security
controller
and
the
NSS,
because
you're
sending
all
the
information
they
are
violent
bow,
but
we
our
approach.
We
consider
that
approach
a
little
bit
safer
in
the
say.
Okay,
we
have
the
inbound
there.
So
nothing
happened.
The
old
one
is
still
used,
and
then
we
install
the
outbound
in
the
kernel
and
then
everything
is
really
multi,
but
I
mean
Donnell
garden
can
be
a
yes,
we
also
as
I
mention.
J
C
The
biggest
thing
is
your:
what
you're
negotiating
is
unique:
got
security
associations
yeah,
it's
a
if
unicast,
which
means
you
need
a
secure
station
between
this
point
and
this
point,
even
if
we
have
a
thousand
nodes
right,
but
those
are
if
this
node
has
security
association
with
different
nodes.
Those
are
unique
up
security
Association,
so
it's
one-to-one.
C
So
if
something
happened,
for
example,
you
receive
expired
notification
from
the
NSF
from
the
kernel.
Actually
we're
transforming
that
in
a
drift
occasion,
using
that
conferring
Jam
model,
the
security
controller
will
need
to
react
will
need
to
install.
Maybe
the
policies
has
changed
for
some
reason
and
apply
another
different
way
in
that
particular
moment,
and
then
it
needs
to
send
a
basic
security
Association.
The
difference
here
is
whether
we
send
the
session
key
from
the
security
controller,
meaning
the
security.
No
dollar
generates
a
random
value,
which
is
the
session
key.
C
So
the
significance
unless
sees
that
key
or
we
send
a
public
key
diffie-hellman
public
key.
We
send
that
and
then
the
the
NSF
will
create
that
the
session
key
by
the
zone,
which
is
fine,
terminal
security,
because
the
security
control
doesn't
see
that
key,
but
their
procedure,
all
the
information
about
the
IPSec
security
Association,
all
the
policies,
all
information
is
in
the
security
controller.
The
security
controller
has
the
picture
of
the
different
nodes
in
the
Indian
work.
C
So
to
me
trying
to
move
that
I
I'm
talking
about
the
case
to
so
creating
the
students
NSF
creates
understate
about
the
inbound
outbound
I
in
our
comes
to
the
NSF
in
case
two
is
even
with
simpler.
Everything
is
coming
all
the
configuration
IPSec
configuration
is
coming
from
the
security
controller
internal
office
scalability,
as
the
imperative
is
designed
to
support
that
kind
of
scalability.
It
can
control
many
devices,
routing
information,
now
security,
so
I,
don't
see
I,
don't
see
a
problem
there.
What
I
see
all
the
discussion
here
was.
We
may
have
a
security
problem.
C
The
security
controller
may
see
those
keys
and
somehow
this
part
feels
people
uncomfortable
and
I
understand
that
we
have
that
in
Security
section
part.
Your
idea
is
fine
because
solve
that
particular
fact.
But
not
sure
about
what
is
the
scalability
problem,
because
in
the
end
the
security
controller
needs
to
take
actions
based
on
events
coming
from
the
NSF
for
anything.
Okay.
C
C
A
A
M
K
We
have
don't
have
enough
time
I,
just
particularly
reporter
status
and
the
domaine
in
content.
Please
take
a
look
so
a
probability
I
to
NSF
to
network
security
and
services.
This
document
updated
okay
added
to
ourselves
our
sections,
the
first
one
is
I
to
NSF
or
with
except
she
architecture.
The
second
one
is
I
to
Ana's
that
will
weigh
the
an
apple
we
reference
architecture.
K
So
the
a
separate
cases
we
implemented
the
hackathon
project.
We
are
ruled
on
concept.
Secondly,
a
Nepali
that
runs
architecture
case
my
university
skq
and
then
our
colleague
university
summer
university.
We
are
working
for
improvement,
I
to
NSF
on
top
of
an
apple
we
using
acoustic.
So
this
coming
November
meeting,
we
try
to
probe
concept
using
hackathon
project,
so
I
mentioned
so
mainly
the
a
probability
case
how
to
apply
I
to
NSF
to
do
network
system.
So
you
can
see
the
three
earlier.
K
Our
address
that
the
first
one
is
a
Sdn
with
iTunes
app
other
case
SPC
enough
of
me,
okay.
So
next
please
slide!
So
let
me
show
you
so
this
is
the
structure
for
now:
I
Taurus
apple,
with
a
surface
ship
framework.
So,
in
order
to
power,
we
enforce
get
the
policy
into
the
truck
we
have
to
configure
classifier
or
the
established
families
on
polder
with
traffic
flow
information
and
security
policy
together,
so
that
kind
information
can
be
configured
to
using
NSF,
OPC
interface.
K
H
K
The
last
one
is
I
to
NSF
are
with
an
employee,
so
currently
we're
thinking
security
controller
can
be
implemented
using
en
element
management
and
also
develop.
A
minimal
system
can
be
also
implemented
as
element
management
and
then
the
life
of
cycling
case.
We
just
take
advantage
of
existing
and
after
we
interface
at
3e
and
whenever
manager
interface,
okay,
shot
for
yet
yeah.
Thanks.
K
Okay,
so
basically
we
also
using
MSH,
so
we
try
to.
For
example,
we
consider
what
scenario
is
a
chain
of
I
were
a
dpi
or
a
technician
case.
Especially
power
is
at
the
first
NSF.
If
there
is
a
something,
some
messages
should
be
delivered
to
dpi
we
can
using
ns8
metadata
filter
and
then
the
next
tip
here
MSF
can
take
advantage
over
that.
So
we
can
surely
use
yeah.
N
Okay,
that
that's
good
I
think
you
should
maybe
add
an
explanation
in
your
draft
okay
and
then
on
the
next
slide
in
a
in
a
NFV
system,
especially
a
man''ôs
system.
You've
called
out
one
interface,
just
ensure
that
it's
obvious
that
that's
a
man,
oh
interface
and
I,
think
there's
some
others
that
might
be
involved.
So
please
take
a
look
at
the
latest
mono
drafts.
N
I'm
sure
Diego
can
help
you
if
you
need
some
help
there
and
make
sure
that,
because
I
think
that
we
mono
is
established,
so
it's
important
that
we
are
compatible
with
the
mono
reference
points.
That
doesn't
mean
that
we
don't
need
our
own.
Of
course
we
do,
but
compatibility
I
think
will
be
a
big
thing.
Thank
you.
Okay.
Thank
you.
K
A
G
A
G
A
N
N
Basically,
a
capability
is
a
function
or
a
set
of
functions
that
are
advertised
by
an
NSF.
They
can
be
vendor
independent.
They
could
possibly
be
vendor
dependent
as
well
and
with
that
the
security
controller
can
realize
the
security
functions
desired
for
a
given
domain
by
putting
together
different
capabilities
from
one
or
more
NSS
there.
In
normatively
we
say
that
n
every
NSF
should
be
described
with
the
set
of
its
capabilities.
N
N
There
is
the
notion
of
a
capability
algebra
now.
What
that
algebra
is,
is
a
template
to
provide
a
mathematically,
formal
definition
of
which
capabilities
are
actually
active.
So,
if
I,
if
I'm
the
security,
controller
and
I,
have
sets
of
capabilities
from
different
NSF's,
then
using
set
theoretics,
I
can
construct
a
algebraic
definition,
a
template,
if
you
will,
of
the
final
set
of
capabilities
that
are
applicable
for
that
NSF.
N
N
So
thank
you
Linda
right
now,
the
draft
is
received
is
restricted
to
imperative
policies.
So,
basically,
when
an
event
fires,
if
the
condition
of
the
policy
is
true,
then
you
may
execute
actions.
Otherwise
you
do
nothing.
I
say
may
because
there's
both
metadata
as
well
as
other
restrictions
that
control,
for
example,
the
execution
order
of
policies.
Remember
this
is
an
imperative
system.
So
order
is
important
right.
You
can
also
control
side
effects.
So
what
happens?
If
a
policy
fails,
do
you
continue
executing
other
policies?
Do
you
stop?
Do
you
rollback,
etc?
N
N
N
This
draft
was
built
to
be
compatible
with
as
many
external
projects
as
possible,
so
it
does
not
define
an
information
model
from
top
to
bottom.
Rather,
it
defines
a
fragment
specifically
two
fragments
one
for
representing
capabilities
which
are
a
type
of
security
and
the
second
for
representing
policy
rules,
and
if
the
external
information
model
doesn't
have
it,
then
a
third
fragment
can
define
NSS.
So
the
way
to
read
this
is
that,
starting
with
an
external
information
model,
you
build
a
an
NSF
object
or
set
of
aljex
this
funny
little
symbol
is
UML
for
an
aggregation.
N
This
funny
little
symbol
means
an
association
class,
so
that
means
that
I
have
the
power
of
a
class
attributes
methods,
other
relationships,
etc.
To
realize
the
semantics
of
this
association.
So
simple
example:
I
have
employers
and
employees,
and,
let's
assume
that
zero
or
more
employees
can
work
for
an
employer
and
an
employer
can
have
zero
more
employees.
Where
do
you
put
the
salary
attribute?
By
put
it
in
the
employee
at
class,
then
every
employer
pays
every
employee
that
salary-
that's
bad,
if
I
put
it
in
them
the
employer
class.
N
That's
worse,
if
I
put
it
in
a
Association
class,
then
the
salary
becomes
an
attribute
of
the
relationship
between
employer
and
employee
and
notice
that
this
is
now
powerful.
I
can
use
that
relationship
to
figure
out,
raises
bonuses,
etc
same
thing
here
with
security
and
well
we'll
talk
about
gaming
in
a
minute.
So
this
is
an
example
of
a
fairly
complex
industry
standard.
This
is
from
the
meth.
Mcm
stands
for
the
meth
core
model
and
I've
used.
N
These
little
highlights
to
show
points
where
NSF
could
attach
so,
for
example,
in
the
meth
we
have
not
just
imperative
rules,
we
have
declarative
roles,
we
have
intent
rules,
we
have
utility
functions,
they
have
lots
of
things.
So
this
class
says
I
am
a
policy.
This
sub
class
here
says:
I
am
an
EC,
any
policy
rule
simple
and
arrogance.
N
D
N
Decorator
contains
events,
conditions
and
actions.
A
decorator
is
a
software
concept.
It
was
defined
in
1995,
it's
used
in
pretty
much
every
windowing
toolkit
I've
ever
come
across,
it's
used
in
Java
and
what
it
does
is
it
allows
you
to
use
delegation
to
assemble
a
new
object
by
putting
all
our
parts
of
existing
objects
together.
So
think
of
it.
This,
if
I
want
to
extend
functionality
of
a
model
and
I
create
a
new
subclass.
N
That
subclass
is
not
known
to
anything
else.
So
I
have
to
recompile
redeploy,
do
all
the
horrible
things
that
operators
hate
if,
instead
of
using
the
decorator
model,
I've
already
defined
all
my
objects
right,
data
is
code,
code
is
data,
and
so
then
all
I
have
to
do
is
to
say
to
make
this
new
function.
I
want
one
of
a
two
of
B.
This
part
of
C.
Add
them
together
and
boom.
I've
got
my
new
objects.
It.
O
D
O
Away
the
tactical
question
is
probably
to
ask
you
to
provide
your
summation
where
you're
heading
for
just
a
moment.
So
I
can
get
my
mind
into
the
right
concept.
We
have
the
information
model.
We
have
the
data
model.
I
met
real
peace.
Maybe
you
aren't,
and
that
may
be
your
summation
with
having
the
information
show
all
model
for
these
capabilities
show
these
really
cool
ideas
and
the
data
model
over
here
have
substantively
less
because
we
can't
really
do
all
these
cool
things
and
yang
yet
they're
making
progress
toward
it,
but
they're
not
there.
Yet.
N
Know
the
answer
is
yes,
and
no,
so
I
would
absolutely
agree
that
any
self-respecting
data
model,
what
at
least
should
not
and
possibly
must
not
contain
everything
that
parent
information
model
has
that's
like
shipping,
a
relational
database
in
third,
normal
form
or
higher.
You
have
zero
performance
that
way
in
speaking
generally
right
and
you
have.
D
N
Bunch
of
things
that
your
implementation
might
not
use,
that
is
not
my
quarrel.
What
my!
What
I
worry
about
is
how
we're
constructing
our
yang
you're,
absolutely
right.
That
yang
is
not
the
best
implementation
language
for
policy.
One
reason
that
we're
using
Association
classes
is
to
get
around
some
of
the
limitations
in
semantics
for
game,
and
that's
also
why
we're
using
the
decorator
pattern
to
enable
a
more
flexible
construction
of
objects
to
get
around
these
yang
problems,
so
the
punchline
is
coming
in
the
next
couple
of
slides.
Okay,
where.
B
O
N
You
you're
welcome
so
any
questions
on
this,
so
in
summary,
just
in
case
people
got
confused
if
I
was
building
I
to
NSF
in
the
MCM,
which
I
happen
to
be
then
for
the
event,
condition
and
action
classes
defined
in
our
information
model.
They
would
subclass
here
under
gonna,
see
on
policy
event,
policy
condition
and
policy
action.
If
I
was
defining
metadata
to
better
explain
policy
or
other
objects,
they
would
subclass.
N
Metadata
isn't
shown
on
this
one,
but
it's
probably
about
right
there
they
would
subclass
from
the
MCM
metadata
class,
are
I
to
NSF
security
rule
is
a
subclass
from
MCM
EC,
a
policy
rule.
So
just
as
I
said,
an
answer
to
this
question
do
I
have
to
use
all
of
the
structure.
No,
but
it's,
but
if
I
want
to
I,
can
that's
the
advantage
of
building
a
modular
object,
ran
it
info
model?
Okay,
so
now
the
game.
N
N
Two
is
the
concept
of
inheritance
or
subclass,
and
if
you
will
and
three
are
relationships
now,
yang
cannot
really
differentiate
between
an
association
and
aggregation
and
a
composition
and
that's
fine,
but
we
can
still
build
relationships
in
yang
and
we
can
get
around
that
problem
by
implementing
every
relationship
as
an
association
class.
So
in
our
model,
that's
exactly
what
we've
done.
If
we
have
a
relationship,
it
is
always
implemented
as
an
association
class
that
makes
coding
and
implementation
for
all
students
much
easier.
N
Now,
when
we
build
a
class-
and
these
this
is
a
summary
from
the
work
that
we
did
in
supa,
so
what
we
do
is
we
use
an
identity
and
a
group.
Why
well?
How
else
can
you
tell
whose
parent
this
current
gang
letha's
right,
so
every
class
has
a
grouping?
Every
grouping
has
one
leaf
that
has
a
unique
system-wide
identifier
that
identifies
this
instance
and
then
the
second
leaf
is
just
an
identity
rep,
and
what
that
allows
you
to
do
is
a
very
simple
form
of
reflection.
N
And
it's
the
important
thing
here
is
that
reusing
inheritance
of
the
identity
itself
to
emulate
the
sub
classing
that
we
do
in
the
mall,
because,
remember
yang,
is
a
flat
model
right
yang.
You
cannot
represent
hierarchies
of
hierarchies
unless
you
do
special
things.
This
is
one
of
those
special
things.
The
third
point
is
associations.
These
are
a
little
more
complex,
but
and
again,
if
you
want
to
talk
to
me
on
making
myself
available,
but
what
we
do
is
basically
combine
the
first
two
steps,
so
we
define
a
new
that
represents
the
association
class.
N
We
use
instance
identifier
for
each
end
of
the
Association
and
the
Association
class,
and
then
we
have
instance
identifier
is
that
basically
point
from
the
source
to
the
Association
class
and
from
the
Association
class
to
the
destination,
it's
very
simple
to
implement
as
a
software
pattern,
and
it
will
make
your
life
easier.
I
can
skip
the
rest
of
this
since
we're
out
of
time,
and
this
is
just
an
example
of
what
something
like
this
would
look
like
following
these
rules.
N
O
G
G
Anything
no,
no,
you
know
I
have
come
to
the
idea
that
we
should
try
to
find
a
way
in
which
we
could
create
some
kind
of
actionable
mapping
between
this
and
the
other
data
models
that
are
around,
so
we
can
allow
them
to
it
to
refers
to
capabilities
inside,
and
this
is
the
only
thing
that's
just.
We
have
had
no
time
to
talk
about
this
because
it
it
has
been
complicated.
G
A
A
G
A
K
Okay,
this
is
a
poor
attempt
from
skq
Korea,
so
certainly
I
cannot
deport.
My
group
tried
to
address
the
John
and
the
prank
information
a
model
to
our
a
young
model.
So
almost
yes,
stop
I,
believe
or
neglected,
but
we
tried
to
more.
Our
young
model
looked
like
object,
oriented
using
identity
John
mentioned
so
my
team
tried
to
finalize.
So
let
me
shortly
just
because
we
don't
have
a
time
I
scroll
down,
so
you
can
see
there
are
a
model.
Our
working
group
case
capability.
K
This
is
a
Sue's,
the
page
based
our
young
model,
based
on
that
we
make
the
consuming
pacing
and
as
a
facing
and
iteration
also
monitoring.
Also
the
Frank
is
working
for
information
model,
so
this
is
very
important
to
monitor
NSF
okay.
So
so
we
implement
all
of
the
during
hackers
on
projects
or
be
proconsi.
We
try
to
make
final
right.
So
currently
the
legislation
and
the
monitor
model
are
are
also
trying
to
work
in
your
adoption
code.
Okay,
this
time
so
Lester
slide
I
believe
just
update.
K
D
O
I,
instead
of
just
having
a
right
common
illness,
I
realized
this
in
the
middle
of
reviewing
this
with
the
co-author,
so
I
sent
a
slide,
I
tried
to
be
effective,
okay
and,
and
you
notice
it's
not
in
the
form
of
a
drafts.
You
know
it's
just
a
to-do.
It's
a
discussion
point
you
can
go
to
the
next
slide.
Linda,
okay,
look
when
we
were
looking
at
it.
We
started
to
talk
where's
the
operational
state
for
the
data
model.
O
We've
talked
about
really
cool
capabilities,
but
you've
not
talked
about
where
the
operational
state,
where
the
NSF
address
and
the
transport
it's
not
really
applicable.
To
put
it
in
the
registration.
I
think
Diego
made
that
point.
That's
what
you
get
from
vendors.
It
probably
needs
to
be
in
some
place
toward
the
NSF
nodes.
It's
probably
not
just
straight
a
capability,
but
it's
an
operational
issue.
You
need
you
need
to
know
here.
I
am
a
controller.
I
need
to
know
what
the
NSF
dresses
I
need
to
know.
How
to
transport.
O
K
A
A
P
First,
we
divide
the
section
fall
to
discuss
about
updating
on
existing
NSF
instance,
fire
the
registration
interface.
According
to
the
changes,
the
figures
two
three
and
four
have
been
updated.
We
also
curl
clarify
the
the
Appendix
A
to
discuss
the
use
of
the
registration
interface
related
to
the
lifecycle
management.
P
G
This
is
something
a
half
is
probably
I
pay
every
pity
days
since
we
first
saw
these
information
models,
I
believe
that
we
should
not
have
separate
information
models
documents
with
the
exception
of
the
capability
model,
and
basically
because
the
capability
model
implies
complex
algebra
for
generating
policies
in
the
translation.
I
think
that
to
meet
make
sense
to
have
this
as
an
introductory
discussion
in
the
corresponding
dates
and
model
documents.
Well,
I
have
seen
this
I
have
said
this
several
times
and
I
will
repeat
myself
as
many
times
as
necessary.
G
G
K
So
this
is
a
port
from
skq,
so
I
have
a
different
opinion
on
the
current
consumer,
PC
interface,
information
model
and
laceration
case
address
aspect
or
a
consumer
painting
and
the
restoration.
So
current
capability
information
is
a
very
cool
good,
but
specifically
different.
The
interface
case
I
still
believe
that
the
separate
information
model
also
Palio
or
so
so
we
tried
to
parallel
working.
A
Got
it
so
in
the
interest
of
time
we
are
running
out
of
time
and
there's
a
remote
anticipation
presentation.
So
maybe
you
can
just
spend
five
minutes
to
discuss
that,
so
there
go
I.
Remember
when
we
discussed
this
last
meeting
and
Katherine
said:
they're
gonna
create
a
new
initiative
in
idea
to
do
that.
Okay,
yeah
first.
G
Of
all,
let
me
assist
replying
to
Paul
and
not
same
to
build.
A
single
information
model
document.
Well,
then,
saying
is
to
bring
the
different
information
models
today,
as
justification
of
the
data
models.
When
saying
is
that
is
to
take
the
text
of
the
registration
interface
information
over
to
the
registration
interface
data
model,
but
merging.
D
G
And
DMS,
okay-
well,
it
comes
to
the
trivia
station
does
just
to
the
document.
We
have
added
it
to
the
document.
We
have
idea
that
some
sections
on
topology
at
the
station,
which
is
important
thing
and
please
have
a
look
at
it
because
there's
something
that
is
connected
with
some
ideas
we
are
going
to
discuss
in
SFC,
which
is
about
pilot,
should
go
the
other
way.
G
In
control,
so
what
just
to
go
very,
very
fast
with
news
precisely
this
is
about
having
topology
verification
mechanisms
topology
at
the
station
mechanisms,
including
including
a
proof
of
transits
using
an
assessee
brief
I'll
have
a
look
at
it.
Have
a
look
at
the
the
proof
of
transit
document
in
the
SFC
group,
and
the
important
thing
here
is
that
take
into
account
we're
not
talking
about.
Katherine
was
mentioning
this.
This
is
not
a
general
a
document
or
attestation.
This
particular
one
is
very
much
oriented
to
h1.
G
Sf
is
very
much
connected
to
the
a
of
having
the
security
controller
as
the
points
collecting
the
measurements
of
all
the
interval,
all
the
components
delivering
it
to
the
to
the
client
for
further
purification.
So
it
is,
it
is
a
particular
it's
a
particular
ization
of
any
of
a
general
the
station
flow
for
the
case
of
the
Jonases
environments.
G
As
I
do
in
a
third
level-
and
this
is
why
well
it's
a
call
for
adoption
or
or
let's
forget
about
this
okay
and
finally,
just
if
you
allow
me
tomorrow
at
7:00,
sort
of
serving
I'll
share
with
you,
the
the
announcements
again,
we
will
have
above
a
bar
both
informal
side
meeting,
whatever
you
call
it
to
discuss
precisely
about
the
possibility
of
certain
some
activity
regarding
general
at
the
station.
So.
G
F
Comment,
Darryl
I
agree
that
this
is
very
closely
to
the
item:
a
safe
architecture
based
on
that
architecture
to
tourism.
What
attestation?
So
maybe
we
can
do
this
in
either
a
safe
working
group,
but
I
think
we
should
be
clear
for
that.
We
will
have
another
initial
work
other
place
right
in
the
other
work,
so
how
to
a
client
your
work
with
with
those
work,
because
in
the
family,
maybe
we
will
show
a
way
a
share,
the
same
protocol,
the
same
process.
So
we
don't
do
hope
that
there
are
some
confliction
between
here.
G
Under
there,
so
Frank
I'm
not
saying
that
we'll
go
for
less
coal
or
whatever.
What
I'm
saying
is
that
weather
is
to
check
whether
the
group
is
interested
continuing
this.
Maybe
this
will
even
happen
that
we
closed
the
group
and
it's
not
finished,
because
it's
not
aligned
yeah,
but
if
you
be
and
asking
whether
the
group
believes
that
there
is
a
value
in
that
we
continue
working
for
so
these
here.
If
not
well,
we
can
make
a
particular
case
or
what
simply
that's
know
for
sure
is
there
is
not
what
I'm
not
asking
to
go.
F
A
Thank
you
very,
very
much
I'm,
sorry
for
two
more
drafts.
We
didn't
change,
yeah
where's,
the
blue
sheet.
Can
people
pass
around
and
if
you
haven't
signed
your
name,
please
do
in
the
back
table.
So
please
go
signing
that.
Thank
you
very
much
and
I
think
we
have
two
more
drafts
didn't
finish,
so
we
can
continue
the
discussion.
Your
draft
probably
is
more
part
of
the
data
model
right.
So
please,
working
with
the
data
model.
Authors
see
if
you
can
incorporate
that
into
their
drafts,
so
we
can
finish
our
I
to
NASA
untied.
