►
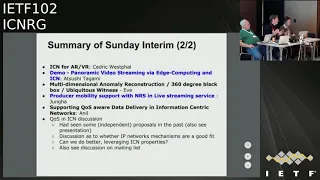
From YouTube: IETF102-ICNRG-20180717-1550
Description
ICNRG meeting session at IETF102
2018/07/17 1550
https://datatracker.ietf.org/meeting/102/proceedings/
A
A
A
B
A
A
I'll
talk
out
a
little
bit
about
this
Sunday
meeting
and
then,
if
is
gonna,
give
us
an
update
on
the
Intel
NSF
sponsored
ICN
Wireless
edge
networking
program,
and
so
we
thought
that
we
could
discuss
mobility
management
a
bit
today
so
recently
and
they
have
been
different
proposals
as
to
you
know
how
to
manage
mobility
in
ICN
like
reduced
mobility,
for
example,
but
also
as
to
you
know.
How
could
this
fit
into
existing
frameworks
so,
for
example,
on
growing
firestation,
ization
and
so
on
and
so
look.
A
I
has
kindly
volunteered
to
give
this
some
soft
parts
and
also
try
to
generate
some
discussion
here
in
the
room.
So
if
you
have,
if
you
are
working
on
this
and
you
have
some
ideas
and
you
haven't
really
followed
up
with
Luca-
please
start
thinking
now,
and
so
we
can
have
a
good
discussion
and
then
we
have
a
block
of
different
draft
updates.
A
So
we
can't
miss
and
later
in
the
session
and
in
the
end,
I
would
like
to
kind
of
give
you
some
ideas
for
what
you
want
to
continue
working
next
meetings
and
so
on
quick
summary
of
the
sunday
meeting.
So
we
had
again
really
interesting
Sunday
like
food
food,
a
meeting
with
an
extended
break
that
made
our
French
participants
happy.
A
So
Yanis
talked
about
mobile
data
repositories
at
the
edge.
So
this-
maybe
you
could
describe
this
as
thinking
about
you-
know,
data
logistics,
useful
services
that
ICN
could
provide
thinking
about,
say,
use
cases
where
you
generate
tons
of
data
and
edge,
for
example,
in
an
autonomous
car,
and
you
need
to
store
this,
but
also
make
this
available
at
some
point.
How
could
I
see
and
help
so
even
Martin
and
Mel,
you
say,
pretended
ideas
for
video
distribution.
A
So
that's
a
local
company
here
in
Montreal
that
is
trying
to
change
the
model
of
a
distribution
and
considering
to
use
ICN
for
that
that
that's
also
highly
exciting
and
Luca
gave
us
an
update
about
the
activities
on
H
ICN
and
specifically,
a
concept
for
transport
layer
and
socket
API.
That
was,
you
know,
designed
to
kind
of
enable
applications
to
to
work
with
an
IC
and
network,
but
also
giving
some
thoughts
on
really
high
performance.
A
So
if
you
haven't
been
at
that
meeting,
I
encourage
you
to
check
out
the
slides
which
actually
interested
in
comparison
comparing
so
they
are
HIC
ends.
Deck
was
a
like
traditional
tcp/ip
stack,
so
it's
really
good
results
and
yeah
that
also
included
a
demo,
so
web
RTC
over
over
h,
IC
n,
so
in
general
sunday,
was
really
cool
because
we
actually
have
three
different
demos
at
that
meeting.
A
In
the
second
part
of
the
meeting,
we
had
a
blog
on
video,
augmented
reality.
So
Cedric
is
working
on
a
draft
and
in
in
this
field
and
then
tag
Amazon
had
a
live
demo
for
360-degree
video,
so
using
ICN
so
leveraging
the
fact
that
if
you
have
say
multiple
users
so
watching
the
same
video
you
can
tile
the
video
and
then
benefit
from
from
caching,
literature,
tiles
and
achieving
performance
or
efficiency
benefits,
and
that
was
demoed
life
at
uni
meeting
and
what's
also
pretty
cool
and
so
connected
to
that.
A
A
A
So
what
is
maybe
what
other
possibilities
that
ICN
provide
to
provide
us,
but
also
maybe
to
arrive
at
slightly
different,
maybe
more
elegant,
more
efficient
solutions
for
that,
so
they
seem
to
be
quite
an
interest
in
that
and
also
I,
think
they'll.
So
they've
posted
a
draft
and
a
flow
label
idea
on
the
menu
list.
A
B
B
A
number
of
the
dress
active,
we're
gonna
have
explicit
updates
from
the
author's
at
the
end
of
the
session,
but
let
me
just
go
quickly
because
some
of
these
men
will
not
be
discussing
actively
at
the
meeting,
so
the
first
is
the
to
see
CNX
protocol
documents
which
are
destined
for
to
expend
on
experimental
RFC
status,
have
passed
irst
review.
We
got
Cox
and
relatively
simple
comments
back
how
to
another
sort
of
pass
through
the
through
the
folks
in
the
RG.
B
There
have
been
updates
posted
of
those
too,
and
this
is
now
an
out
is
Allison
in
the
room.
No
okay,
well
absent
Allison
in
the
room,
it's
in
her
hands
to
do
the
final
IRS
G
poll
on
those
two
documents
and
assuming
that
goes
well.
Those
will
move
directly
to
RFC
publication
once
that,
once
that
poll
completes,
this
has
been
a
very
long
process.
B
Christian
does
what
he
can,
but
he's
also
very,
very
busy.
It
would
be
very
nice
if
there's
some
folks
in
the
working
group
would
like
to
step
up
and
help
work
on
this
and
maybe
take
over
co-authorship
of
that
of
that
draft.
We
really
need
to
move
it
forward,
because
the
actual
extant
implementations
that
are
out
there
in
open-source
actually
implement
slick.
So
we
have
implementation
ahead
of
spec
in
in
that
sense.
B
Next,
another
finished
draft
is
our
disaster
scenarios
draft
all
that
went
to
IRS
Depot
came
back
with
one
set
of
very
nice
comments
from
Vince
all
hookah
and
I'm
waiting
for
comments
from
two
other
IRS
G
members,
who
said
they
wanted
to
look
at
it.
Well,
once
we
have
that
we'll
we'll
do
another
spin
of
that,
and
hopefully
very
rapidly,
that
will
get
through
the
novel
back
through
IRS
depot
and
a
publication
as
an
a
as
an
informational,
RFC.
B
B
B
It
got
submitted
as
an
RG
document,
but
it
isn't
an
RG
document,
so
we
have
a
naming
problem
there,
but
at
some
point
we
would
like
to
look
at
whether
the
RG
wants
to
adopt.
This
is
a
work
item
we're
going
to
hold
off
a
little
while
on
that,
because
there's
IPR
on
that-
and
we
want
to
see
the
IPR
declaration
from
Cisco
before
we
move
too
far
with
that
draft,
it's
submitted.
C
D
B
B
There's
another
one
called
CC
info
I'll
be
talking
to
Toshi,
I,
say
there.
The
author,
one
of
the
authors,
isn't
here
I'll,
be
talking
about
that
briefly
during
the
draft
update
session,
and
we
have
a
document
on
considerations
for
applying
ICN
for
edge
computing,
so
that's
sort
of
the
status
of
everything.
That's
that's
sort
of
like
bubbling
in
the
pot.
We're
pretty
I
think
happier
chairs
is
the
level
of
work.
That's
your
product!
That's
that's!
Coming
out
and
I
hope
we
can
continue
that
way.
So,
let's
go
on
to
today's
presentations
and
I.
Think
images.
E
Okay,
hi
I'm,
Eve,
Schuler
I'm
from
Intel
and
I,
am
on
the
board
of
advisors,
as
is
Dave,
ran
and
Christian
Juden
for
as
well
as
several
other
people
from
Intel,
as
well
as
another
external
Board
of
Advisors
member
from
University
Michigan,
but
essentially
I'm
here.
To
tell
you
it's
a
year
since
the
last
time
I
was
here,
we've
had
a
year
of
research
on
a
program,
that's
jointly
funded
by
Intel
and
the
National
Science
Foundation,
which
is
one
of
the
key
funding
agencies
for
computer
science
in
the
United,
States
and
internal
to
Intel.
E
There
are
a
couple
people
in
our
wireless
lab
who
are
the
program,
the
the
PI
and
the
program
managers
in
our
University
Research
Office,
and,
of
course
these
are
our
partners
at
NSF.
You
probably
recognize
Darlene's
name
and
maybe
even
Manisha,
just
to
give
you
the
high
overview
here
the
high-level
overview,
because
some
of
you
may
not
have
heard
the
previous
presentations.
E
E
Networks
and
what
was
interesting
to
us
about
that
venue
was
really
the
you
know.
If
you
look
at
what's
going
on
with
5g
the
call
for
support
for
ultra-low
latency
and
massive
IOT
applications,
and
we
are
look-
we
want
to
look
at.
We
want
our
researchers
to
look
at
at
least
three
aspects
of
what
we
mean
when
we
say
wireless
networks,
the
endpoint
devices,
the
infrastructure
and
architecture,
as
well
as
the
wireless
data,
security
and
privacy
and
I
I.
E
Don't
know
if
this
is
aspirational
or
not,
but
we
did
put
into
the
call
that-
and
there
were
many
who
said
that
you
know
this
was
also
interesting
to
them.
Your
clean
slate
design
and
as
yet
you
know
people
are
sort
of
right
now.
Some
of
the
implementations
that
exist
are
not
clean
slate,
but
we're
hoping
in
three
years
that
more
will
be
our
research
goals.
E
But
can
we
quantify
as
well
as
qualify
the
benefits
of
an
ICN,
enable
network
and
to
do
this
by
anchoring
this
work
in
realistic,
implementations
and
deployments?
So
that
was
the
goal
last
time
I
was
here,
I
think
it
was
right
after
we
had
announced
the
awardees-
and
this
is
about
a
year
in
the
interim,
we
decided
we
also
got
enticed
to
do
a
little
bit
more
funding
for
another
team
out
that
I'll
talk
to
you
about,
and
we
just
had
our
first
year
review
and
these
slides
I
make
you
know.
E
E
Some
of
these
people
are
not
really
schooled
in
what's
going
on
in
the
ITF
and
they
live
in
other
communities
and
certainly
the
wireless
community,
3gpp
and
elsewhere.
So
I
think
some
of
the
dialogue
I'd
like
to
hear
about
is
really
how
do
I
connect
them
to
people
who
are
doing
similar
work
in
this
environment
and
how
to
get
them
acculturated
around
the
standards
and
the
idea.
These
are
the
three
main
projects.
E
E
So
that
hasn't
really
been
going
long
enough
to
for
me
to
report
out
on
details
except
to
say
that
they're
working
away,
okay,
I,
think
we
do
have
Leisha
here
in
the
audience.
So
hopefully,
if
you
have
more
detailed
questions,
he
is
here
afterwards
for
you
to
touch
base
with
she
is
part
of,
and
she
is
the
lead
PI
on
a
program
called
ICN
enabled
secure
edge,
networking
with
augmented
reality,
and
that's
because
the
application
that
they've
chosen
to
anchor
their
work.
It's
not
the
end
result
it's
just
to
drive.
E
E
Now
they
are
trying
to
drive
research
along
multiple
dimensions,
and
fundamentally
it's
all
about
naming
and
in
fact,
one
of
the
most
interesting
conversations
that
we
had
for
me
anyway.
At
the
the
meeting
the
face
to
face
was
all
about
there
is
this
skill
or
this
art
to
the
design
of
naming
and
namespaces,
and
what
is
it
and
how
do
we
school
people
in
it
and
how
do
are
there
best
known
methods
around
it
and
so
I
think
you
know
we
should
come
back
to
that?
Maybe
do
we
need
a
workshop
around
that,
etc.
E
So,
there's
a
big
discussion
going
around
around
that
acceleration
is
a
service
meaning
at
the
hardware
level
FPGA.
What
kinds
of
networking
algorithms
do
we
accelerate
interest
in
local
resource
discovery
at
the
edge
security,
privacy
and
Trust
and
up
clearly
how
does
the
upper
layer
mingle
with
the
lower
layer?
But
how
do
we
interconnect
all
these
disparate
pieces?
Part
of
the
objective
of
this
program
was
to
bring
together
people
who
live
in
adjacent
areas
and
get
them
to
actually
work
together.
E
Not
not
only
on
these
teams
that
you
know
got
the
funding,
but
across
teams,
so
we're
still
hoping
that
that
that's
going
to
happen
and
we're
just
starting
to
see
the
fruits
of
that.
What
have
they
done
in
in
this
first
year?
I
would
say
the
thing
that
impressed
the
folks
at
Intel.
The
most
was
really
that
they
have
a
working
implementation
and
prototype
of
an
end-to-end,
augmented
reality
application.
Oh
there's
Lisa.
E
She
can
hear
me
anyway,
so
we
were
very
impressed
with
that
and
and
that
has
driven
a
lot
of
understanding
about
what
are
the
requirements.
What
are
the
kinds
of
workloads
and
counters?
What
is
the
security
issues,
and
it
has
led
them
to
really
take
a
step
back
and
re-examine
ation
of
libraries
that
are
already
existed
in
their
toolkit
things
like
their
common
name
library,
where
how
do
you
expose
meta
information
across
different
layers?
You
know
what
is
the
naming
and
a
touch,
and
also
some
of
their
real-time,
very
work.
E
So,
as
I
said,
this
is
gonna,
be
a
whirlwind:
I'm
not
gonna,
go
into
tremendous
depth.
Unless
you
ask
me
questions
afterwards,
but
I
just
want
to
give
you
a
feel
for
the
breadth
of
exploration
here.
I
spoke
about
acceleration,
oh
and
by
the
way
these
are,
as
I
said,
these
are
their
slides
that
I've
sort
of
adopted
for
me
to
tell
this
narrative.
E
They
started
looking
at
fph
for
for
networking
compression
and
some
of
their
results
have
led
to
4.7
times
better
energy
efficiency.
Then
I'll
just
state
a
leading
GPU
that
is
out
there
and
to
us
again
quite
interesting.
If
ICN
is
being
used
for
service
distribution,
then
maybe
we
put
those
algorithms
into
our
FPGAs
or
even
for
Network
processing,
and
that
that
is
an
interesting
result
to
us
for
security.
E
There's
quite
a
few
quite
interesting
mechanisms
for
access
control,
and
we
were
pleased
to
hear
that
Jay
and
other
colleagues
are
looking
at
some
of
the
hard
issues
around
the
revocation
of
access
control
and
additionally,
that,
of
course
leveraging
some
of
the
existing
trust
schema
work
that
and
and
other
things
that
already
exist
in
the
tool
suite
so
one
another
interesting
result,
at
least
for
me.
Having
been
that
I,
you
know,
I
haven't
had
my
hands
in
the
wireless
code.
Design
issues
is
just
how
difficult
some
of
these
boxes
are.
E
The
I
think
I
will
simply
state
that
the
intent
of
us,
selecting
these
different
teams
and
you'll
see
two
of
the
teams
are
quite
complementary.
The
UCLA
anchored
team
and
the
next
team
that
I'll
talk
about,
which
is
I
call
our
Midwestern
group
of
universities,
they're
really
nice
at
complementary,
because
they're,
both
using
ndn
and
whereas
the
expertise
in
the
NBN
team
comes
from.
Having
been
you
know,
leading
members
of
the
NSF
FIA
program
and
in
the
u.s.
E
you
know
so
at
the
routing
layer,
that's
where
they
sort
of
start
out
life.
This
other
team
was
in
the
wireless
realm,
so
the
kinds
of
cross-pollination
for
the
co.design
work
is
very
interesting
to
us.
Given
those
multiple
perspectives,
I
also
was
intrigued.
With
this
we
talked
a
lot
about
quality
of
service
and-
and
also
this
you
know
comparison
with
other.
You
know
with
with
non
ICN
kinds
of
frameworks
and
I,
really
liked
the
fact
that
this
team
had
taken
the
time
to
talk
about
what
they
were
trying
to
measure
in
their
comparison.
E
And
here
you
can
see
that
these
are
qualitative
measures,
programmability
ease
of
use
and
so
forth
that
we
need
to
develop
some
metrics
around
so
because
I
do
think
that
that's
really
where
ICN
shines,
that's
my
personal
opinion
and
then
also
them.
They
went
to
the
trouble
to
say
what
are
their
lessons
learned.
On
the
one
hand,
there's
you
know,
naming
is
a
has
two
sides
of
the
same
coin
on
one
hand
in
name,
networking
and
storage
and
processing
all
to
sort
of
come
together
and
into
a
cohesive
design
on
the
other.
E
It
can
be
very
difficult
to
integrate
all
these
pieces
together
because
they
all
have
to
speak.
Naming
so
I
found
that
an
interesting
result
there.
You
know
obviously
design
principles
as
I
said
before
kind
of
what
are
the
best
known
methods
for
doing
this
kind
of
work
and
then
that
the
application
driven
architecture
development
is
has
been
instrumental
in
teasing
out
gaps
that
need
addressing
and
the
challenges
and
I
would.
Second,
that
I
think
also
think
that's
important
I,
don't
know
if
you
can
all
read
this.
E
This
is
a
much
smaller
font,
but
I
deliberately
put
the
publication
lists
in
here
so
that
when
you
download
the
slides
that
you
can
peruse
them,
because
that's
really,
where
I
know,
wasn't
really
at
liberty
to
talk
about
the
work
that
is
underway.
I
really
wanted
to
just
talk
about
the
public
work.
Okay,
lots
of
papers,
oh
and
as
I
said,
there
are
some
very
interesting
ones.
They
span
the
gamut
because
we're
really
trying
to
get
the
architectural
breath.
E
Okay,
second
team:
they
call
themselves
the
splice
team
for
secure
predictive,
low,
latency
information,
centric
edge
for
a
network
generator
for
next
generation,
clueless
networks,
and
you
can
see,
there's
quite
an
interesting
crop
of
schools
here:
Texas
A&M,
otherwise,
tamo
Ohio
State,
you
I,
you
see
Purdue
and
Washington
University
in
st.
Louis
or
wuzzle
and
I
would
say
that
they
what
anchors
their
work
has
been
this
search
for.
How
do
you
assess
quality
of
service?
And,
furthermore,
how
do
you
really
truly
embed
ICN
in
the
wireless
edge
network?
E
As
I
said,
this
was
a
strong
competency
in
this
team
and
when
I
say
you
know
the
wireless
edge
network,
they
are
looking
to
you
know
how
can
they
exploit
you
know?
Dirk
was
talking
a
little
earlier
about
one
of
the
demos
that
we
had
seen
what
kinds
of
in
that
Wireless
local
edge?
What
kinds
of
commonality
is
there
in
the
data
and
the
usage
patterns
and
so
forth
that
we
could
leverage
multicast
and
caching
and
wireless?
How
do
you
know
how
do
those
things
combined
together
and
exploit
predictability,
etc?
E
Okay,
again,
I
need
to
how
am
I
doing
for
time.
Okay,
this
is
the
picture
they
like
to
use.
You
can
see
it
starts
at
that
I,
don't
know
if
you
can
see
the
fonts,
but
you
know
up
here:
is
quality
of
service
applications
use
your
privacy,
here's
in
the
end
right
in
the
center
here
down
below
they've,
but
caching,
but
then
note
it
has
interactions
with
coding,
which
is
a
wireless.
E
You
know
wireless
coding
as
well
as
security,
social
security
and
privacy
sort
of
straddle
these
layers
and
wireless
control
mechanisms,
as
well
as
power
constraints
and
interference
constraints,
which
makes
it
quite
interesting,
and
these
are
again
some
of
their
objectives.
There's
a
lot
of
wonderful
wireless
caching,
interaction
in
terms
of
optimizations,
joint,
optimization
and
I.
Think
I
will.
Oh
one
thing
I
should
point
out
is
that,
in
contrast
to
the
UCLA
team
that
is
looking
at
augmented
reality,
this
team
is
specifically
looking
at
virtual
reality
and.
E
E
And
so
sorry,
that's
pretty
hard
to
do
these
days.
Certainly
when
we
think
about
Indiana
5g,
even
which
is
why
I
think
it's
a
great
context
for
pushing
the
envelope
now
they
had
some
interesting
work
already
on
single
player,
VR
applications
on
mobile
and
that
they
published
last
year
and
what
they
did
was
they
realized
that
they
couldn't
really
do
all
the
processing.
E
In
the
places
that
they
wanted
and
they
needed
to
have
a
split
architecture,
and
this
starts
to
wind
its
way
into
why
it
is
that
there's
these
are
these
discussions
around
edge
computing
and
so
for
the
they
broke,
the
foreground,
processing
to
stay
local
and
the
things
that
they
could
send
across
the
network
they
sent
across
the
network
to
somewhere
else.
That
didn't
need
the
the
quick
updates,
and
so
that
was
some
interesting
work
from
last
year.
But
then
they
decided
well.
E
That
I
should
be
more
familiar
with,
because
I
have
two
sons
who
are
addicted
to
these.
They
think
but
or
myself,
sometimes
look
looking
on,
but
nonetheless
for
these
kinds
of
games,
where
you've
got
groups
of
multi
players
in
the
same
location,
that
about
70%
of
the
frames,
have
commonality
by
some
definition
of
commonality,
and
so
that's
what
they
are
trying
to
exploit
here
and
that
they
also
had
some
very
interesting
results
about.
E
There's
a
student
who's
about
to
graduate
who's.
Patrick
Crowley
student
Gila,
Bend,
Abraham
who's
been
looking
at
specifically.
How
do
you
enable
and
en
in
this
context,
enabling
VR
over
ndm
and
as
you
can
imagine,
these
AR
MVR
applications
have
some
requirements
that
we
don't
immediately
meet?
They
are
event
driven
applications
and
they
rely
on
quick
delivery
of
prediction
and
push
notifications
and,
of
course,
ndn
and
some,
some
of
the
other
code
bases
are
pull
infrastructure.
E
So
so
that's
very
an
interesting
abstraction
that
again,
if
you,
if
you
look
at
what
this
says
here
it
her
aim,
was
not
so
much
the
push
notification
say
it
was
twofold:
it's
the
push
notifications,
but
also
to
simplify
the
applications
by
allowing
them
to
be
agnostic
to
the
networking
mechanisms
and
characteristics,
and
it
just
stays
in
the
information
plane.
So
some
interesting
results
there.
As
I
stated
earlier,
this
team
really
excels.
E
I
want
to
point
at
this
because
I'm
reading
it
there's
so
much
said
that
I
don't
know
who
has
you
report
on
other
people's
work,
but
but
you
can
see
that
there's
they
have.
Some
of
the
key
insights
is
that
they've
reduced
the
delay
even
with
small
caches
and
misaligned
content,
and
they
have
what
they
call
moving
window
codes
that
have
also
improved
the
performance
over
traditional
rayless
codes
and
with
very
little
overhead
I
also
was
intrigued
by
their
as
I
said.
E
They
they've
done
some
max
scheduling
because
again
they're
looking
at
supporting
applications
that
have
really
low
latency
or
can
have
low
latency
guarantees,
and
so
they
have
developed
and
there's
a
nice
paper
on
processor
supported
ultra-low
latency
scheduling.
This
is
another
case
where
they
decided.
How
do
we
split
the
processing
between
the
FPGA
in
the
main
CPU
and-
and
this
relates
in
this
case
to
the
Mac.
E
On
a
security
front,
they've
been
very
busy
as
well.
They
are
leading
the
charge
on
trying
to
understand
how
Bakhtin
might
be
incorporated
into
PKI
and
they
have
some
findings
that
state
that
it's
significantly
reduced,
but
the
cost
and
time
at
adding
new
certificates
at
the
server
and
the
IOT
device,
and
they
they
also
have
submitted.
They
have
a
paper
appearing.
That
is
an
approach
for
privacy,
preserving
attribute
based
access
control
for
ndn,
and
finally,
one
of
the
pieces
of
work
that
I
found
quite
interesting.
E
E
So
you
know
that's
what's
on
the
horizon
for
them,
but
they
at
least
have
some
results
in
the
4G
scenario,
and
this
LTE
inspector
is
a
tool
that
they've
created
and
they
also
have
created
some
algorithms
to
identify
under
what
circumstances
you
can
figure
out
that
they're
fake
base
stations
out
there.
So
you
can
see
the
the
work
is
pretty
varied.
They
as
I
stated
earlier.
When
I
was
talking
about
the
UCLA
team.
E
E
They
didn't
even
have
an
Indian
or
ICN
codebase,
so
for
them
they
have
been
doing
their
their
experiments
and
sort
of
you
know,
sort
of
disparate
fashion
and
what's
coming
down
the
pipe
right
now
is
they've
been
they've,
been
hired
a
task
trying
to
design
a
splice
testbed
and
so
that's
launching
and
so
that
they
will
have
a
venue
where
they
can
more
methodologically
systematically
do
their
experimentation
and
for
all
these
schools
to
come
together
and
rally
around
this
test
pad.
So
that's
what's
on
the
list
there
they
are
prolific.
E
They,
as
I
stated.
You
know
in
Hong
was
here
earlier
and
he
you
can
see
he's
doing
all
this
optimal
rate
control
he's
an
optimization
person,
scheduling
to
Central's
a
decentralized
medium
access
protocol
for
real-time
wireless
ad
hoc
networks
with
unreliable
transmissions.
All
sorts
of
wonderful
work
to
explore
here,
I
hope
you
will
take
a
moment
to
peruse
these
and.
E
Again,
kind
of
all
over
the
place
best
paper
award.
You
should
certainly
be
that
one
and
I
okay,
you
know,
and
some
Indiana
related
work
towards
the
bottom
and
the
security
towards
the
bottom.
Okay.
How
am
I
doing
for
time
now?
Okay,
so
I
have
five
more
minutes.
How's
that
perfect
length
and
that's
a
perfect
name
for
five.
More
minutes,
light
speed,
networking
right,
refactoring
the
wireless
networks,
doc
to
dramatically
reduce
information
response
time
and
is
primarily
an
interaction
between
university
of
massachusetts
and
university
of
wisconsin-madison.
E
And
what
I
like
about
this
team
is
that
first
off
their
approach
to
ICN?
Is
they
come
out
of
the
mobility
first
community?
They
have
tremendous
background
in
service
architectures
edge
computing,
their
idea
of
information
centrism
is,
you
know,
there's
a
big
debate,
and
actually
it
is
a
question
like
what
constitutes
information
centrism
and
how
do
you
define
it,
and
how
do
you
know
that
something
is
information
centric
and-
and
some
of
it
comes
from
the
fact
that
they
have
a
really
disparate
worldview.
E
And
so
that
was
another
very
interesting
discussion
at
the
event
itself,
these
colored
items
are
topics
that
I
will
talk
about,
since
I
only
have
five
minutes,
I
will
state
that
you
can
see
they're
big
I'll,
get
there
in
a
second.
Let
me
just
tell
you
what
Ellison
is
in
a
nutshell:
it's
trying
to
really
leverage
the
edge
cloud
drive
down
the
information
response
time
and
that's
where
the
light
speed
comes
from.
E
How
do
you
move
the
services
to
follow
the
people?
How
do
you
move
that
edge
cloud?
How
does
that
mobile
edge
cloud
follow
around
the
application
or
the
person
attached
to
that
application?
So
it's
a
slightly
different
mental
model,
and
so
this
is
a
picture
of
their
service
dispersion
architecture,
and
just
this
what's
meant
to
be
implied
here,
is
that
you
know
when
we
think
of
data
centers,
then
they're
gonna,
be
you
know,
regional
data
centers
and
nano
data,
centers
and
microdata
centers
and
our
edge
data
centers.
E
We
are
data,
centers
and
sort
of
how
does
all
of
that
stuff
get
orchestrated
and
by
the
way
you
have
an
information,
centric
infrastructure
to
support
that.
So
that's
really
where
their
focus
is,
so
their
results
are
and
I
just
have
one
more
slide
after
this
is
there
they
have.
They
have
built
now
a
feasibility
and
proof
of
concept,
of
what
they're
calling
a
gap
axis,
which
is
their
service
to
be
dispersed,
ability,
framework
and
implementation.
E
They
also,
interestingly,
I
think
this
goes
back
to
our
conversation
about
what
is
information
centrism,
and
you
know
how
do
you
even
begin
to
compare
the
different
models?
They
have
a
paper
in
infocomm
this
year
about
ICN
architectural
comparisons.
So
I
would
encourage
folks
to
look
at
that
and
specifically
for
mobility
support
they
also
at
the
lower
layers
of
the
network
they're
looking
at
radio
polymorphism,
because
again,
these
applications
have
such
a
wide
range
of
requirements.
E
One
last
slide:
they
have
some
quite
interesting
work
on
private
information,
retrieval
meaning.
If
you
ask
for
content
over
the
network
of
a
server
that
the
you,
how
do
you?
How
does
the
server
not
know
that
you,
you
know
what
you've
asked
for,
and
so
these
are
some
results
on
that
front
and
additionally,
they
are
in
in
the
throes
of
how
to
limit
personal
information
or
private
information
leakage
in
ApS
and
and
then,
how
do
you
roll
all
of
this
up
into
some
use
cases?
The
UCLA
team
is
focused
on
augmented
reality.
E
E
How
do
you
share
semantic
information
and
so
forth,
and
this
goes
back
to
the
metadata
discussion
and
so
they've
created
this
control
plane
and
it
and
they're
using
it
for
their
dispersed
ability
infrastructure
so
that
they
understand
Oh
their
resources
over
here,
and
these
are
their
capabilities,
and
this
is
how
I
can
map
what
my
job
looks
like
to
those
things
over
there,
and
this
is
why
migrate
it
and
all
of
this
done
using
a
mobility
first
inspired
infrastructure,
so
I
think
that's
it.
They.
E
They
too
have
a
wide
range
of
publications
that
you
might
enjoy
and
I
think
I
did
touch
on
all
of
these
interesting
questions
that
I
think
this
community
should
take
up
at
some
point,
because
I
think
it's
relevant
to
the
whether
or
not
it's
going
on
in
the
ICN
web
program
or
some
of
our
design
discussions
as
well.
Thank
you
for
letting
me
talk
about
other
people's
work.
E
G
H
F
H
You
do
not,
you
may
not
know
exactly
what
you
are,
what
the
functionality
to
put
in
so
fpga
give
you
the
flexibility.
You
can
actually
download
that
fpga
code
in
sub
seconds.
So
what
we
put
into
the
AP
adjusts
the
the
the
chips
and
therefore,
depending
on
the
application
requirement,
you
can
download
that
feature
code
already
compiled
and
then
do
the
execution
there,
but
actually
the
the
power
of
this
is
not
so
much
alpha.
Okay,
you
can
download
a
free
pdf
code.
The
power
is
really
unnamed
the
data.
What
did
that
piece
of
code?
H
H
The
the
execution
in
the
in
the
running
in
the
IPA
just
Otunga
data
code
and
you
can
write-
we
can
I,
definitely
know
on
the
ways
that
I
want
time
here
to
elaborate
for
the
details,
but
we
should
check
offline
how,
in
the
end,
really
realized
this
edge
computing.
You
can
like
here's
that
somewhere
to
say
that
you
can
integrate
the
storage,
harnessing
and
networking
all
together.
Oh
yeah,.
E
E
G
G
E
I
think
that
I'm
at
least
my
understanding
of
the
intersection
of
5g-
and
you
know,
I
see
other
people
who
understand
this
too.
They
sort
of
where
does
5g
and
Indian,
and
it's
really
the
wireless.
So
five
genes,
I'm
gonna
use
as
a
bucket
for
wireless
and
mobile
communication
and
then
the
caching
and
I
think
there
was
a
statement
here.
Maybe
in
this
about.
E
Predictive
caching
and
coding
and
learning
sort
of
these
kinds
of
things
together
or
perfect
for
co.design,
and
so
my
back
to
your
point
about
5g.
My
understanding
is
that
it's
sort
of
aspirational
for
5g
to
want
to
have
low
latency
to
the
levels
that
are
needed
for
this
application,
which
is
you
know
less
than
five
milliseconds
or
less
than
one
millisecond,
and
certainly
for
factory
kind
of
contexts.
E
It
can
be
less
than
a
millisecond,
and
so
at
least
I
know
some
researchers
and
I
and
I
couldn't
swear
that
you
know
this
is
what's
motivating
the
the
Spice
team,
but
some
researchers
are
looking
for
any
other
ways
to
extract.
You
know
either
one
not
sending
redundant
information
over
the
network.
Caching,
things
closer,
you
know
all
those
kinds
of
things
that
might
shave
off
just
a
little
bit
more
time
from
the
latency
that
that
would
be
encountered
by
traffic
on
the
network.
So
that's
it's
a
little
bit
subtle,
but
I.
E
H
E
G
H
C
E
Also-
and
you
know
well,
we
know
where
Patrick
is
these
days,
but
but
it's
still
there's
a
pretty
sizable
team.
Still
that's
part
of
that
and
they
maintain
the
Indian
Test
bed,
but
that
Indian
Test
bed
isn't
necessarily
focused
on
wireless
wait.
Don't
you
guys
have
a
private
conversation
come
share
with
us
how
it's
gonna,
save
that
base
projects
I.
H
E
But
it's
a
good
question
I
think,
but
we
can.
Let's
follow
up
on
that,
because
that's
a
very
interesting
topic
of
how
do
we
leverage
the
already
existing
test
beds
and
how
do
we
share
some
of
the
code
base
for
testing
using
different
sorts
of
applications
because,
as
you
can
see,
that's
what's
driving
some
of
the
pushing
the
envelope.
Thank
you
for
letting
me
have
so
much
time.
Thank.
C
C
Okay,
okay,
I'll,
try!
So
this
light
that
is
trying
to
provide
feedback
about
some
of
the
work
that's
been
done
in
in
a
space
of
5g
standardization.
So
this
is
essentially
to
to
provide
feedback
to
the
ICN
research
group,
but
also
to
try
to
stimulate
more
research
work
in
this
space,
something
that
we
can
bring
the
first
place
into
the
ice
ecology
and
then
try
to
push
into
other
places
like
the
working
group
or
in
other
places
like
3gpp
as
well.
C
City
for
is
a
study,
a
team
that
is
taking
care
about,
especially
right
now
about
different
users
of
playing
solutions
for
fi
G
and
what
Eva
just
presented.
It
is
actually
a
different
kind
of
applications
that
you
want
to
see
in
5g.
So
it's
really
it's
critical
for
5g
design
and
standardization
work
to
provide
support
for
those
kind
of
applications,
so
we're
talking
about
very
low
latency
high
at
the
same
time.
So
the
requirements
are
going
to
be
are
already
very
difficult
satisfy
in
English.
C
In
this
research
group,
I
think
we
can
provide
support
in
solutions
for
some
of
the
use
cases
that
5g
is
trying
to
solve
in
a
very
different
way
of
respect
to
other
solutions.
So
so
it
is
important
that
this
research
group
is
aware
about
the
different
solutions
that
are
being
considered
in
terms
of
users,
user
playing
solutions,
which
is
the
something
that
city
voice
is
going
to
start
to
study
in
the
following
starting
from
now.
C
So
there
are
several
several
protocols
that
have
been
presented
this
morning
at
the
DMM
working
group.
Some
of
those
are
sr
v6
lease
pieces
are
unaware
in
ila,
so
as
in
other
loci
D
solutions,
NHS
en
is
that
the
the
one
that
represented,
which
is
the
so
for
those
who
are
familiar
with
the
jcn,
is
a
ip6.
Implementation
of
CCN
is
specified
in
the
draft
that
are
in
what
having
this
research
group.
So
the
CC
annex
draft
in.
C
C
I
C
This
right
this
right,
currently
they
are
focusing
the
n9
interface,
we're
going
to
talk
about
that
in
a
second.
But
that
is
an
opportunity.
It's
a
starting
point.
So
I
think
that,
as
a
research
group,
we
should
look
at
that
as
an
opportunity
to
start
showing
the
benefits
of
replacing
GDP
and
the
way
GDP
is
used
in
that
interface.
For
is
a
start
also
to
also
show
how
this
is
actually
what
other
solutions
are
also
trying
to
show
how
that
kind
of
benefits
can
also
be
pushed
in
other
interfaces
like
n3e
and
others.
I
C
C
I
I
Slicing
this
ins
like,
if
you
can
have
multiple
slices
and
then
you
can
give
different
QoS
and
traffic
management
treatment
to
how
different,
okay,
so
I,
think
that
was
the
focus
doing
the
solving
the
endline
problem.
But,
as
I
said,
probably
you
can
leverage
some
of
that
towards
solving
a
mobility
kind
of
entire
mobility
problem.
But
focus
seems
to
be
right,
no
more
well.
The
fish.
C
Go
directly
to
the
what's
in
here,
not
so
efficient
is
a
for
those
who
are
not
familiar
with
the
Phi
G
terminology.
So
basically,
the
n9
is
the
link
between
a
TS
gwgw
for
using
4G
like
a
PC
terminology,
so
that
that
link
a
it's
something
that
is
use
not
much
today,
because
a
co-located.
So
if
you
try
to
distribute
that,
you
have
a
highly
distributed
architecture,
and
this
is
something
that
you
need
for
the
application
we're
talking
about.
C
I
How
do
you
do
that?
That's
the
whole
point,
so
today
it's
gonna
be
gtp
by
default.
It
is
but
what
I'm
saying
is
that
you
still
having
a
tunnel
between
under
in
three
so
that
has
to
Emanuel
know
where
you
have
to
decide.
So
sorry,
so
you're
saying
that
that
that's
really
further
out
then
I
mean
somewhere.
Probably
that
entry
is
extended
to
that
point.
So
yeah.
C
So
it's
not
gonna
happen
in
one
shot
in
the
so
the
point
is
this:
is
these
are
the
opportunities
and
what
city
for
is
discussing,
and
the
point
is,
how
can
how
we
can
help
in
pushing
innovation
in
different
places
to
solve
some
some
of
the
issues
and
support
some
of
the
application
we
are
talking
about?
It's
not
gonna
happen
in
all
at
once
for
sure.
Maybe
it's
not
gonna
happen
at
all,
but
this
is
how
this
is
the
the
path
we
see
already.
Like
you
start
with
the
ni.
You
prepare
something
in
9.
C
A
C
C
E
C
What
I?
That's?
What
exactly
what
I
mean,
so
the
there's
an
opportunity
in
general
for
I
would
say
not
only
this
research
group,
it's
an
opportunity
in
general
for
mobility
management
in
the
solution
that
can
come
from
the
ITF
to
have
something
different
than
gtp
and
provide
real
solutions
for
the
problems
of
the
application
you
mentioned
to
have
oculus
mobility
to
offload
the
core,
the
mobile
core.
C
You
know
you
put
the
constraints
in
the
the
different
requirements
for
the
application
and
we're
talking
about
you
know
which
are
not
just
a
video
distribution.
It's
a
lot
more
real
Thank,
You,
munication
low
latency,
so
in
the
there's
an
opportunity.
So
this
is
the
whole
point
like
you
trying
to
catch
the
opportunity
in
the
first
place.
C
B
One
of
the
things
that's
entangled
with
the
current
tunneling
architecture
is
the
way
authentication
and
authorization
is
done,
because
it
assumes
that
you
can
transparently
carry
the
authentication
authorization
information
way
back
to
some
centralized
place.
In
order
to
let
somebody
under
the
network
and
if
you
I'm
just
on
it
see,
it
seems
like
you,
can't
just
change
away
from
that
and
not
rethink
authorization,
authentication
authorization
and
at
least
some
degree
and
I
didn't
I,
didn't
see
that
the
3gpp
folks
I'm
sort
of
like
understand
that
I'm.
B
Like
you
know,
let
me
interpret
Devi
okay.
If
your
tunnel
doesn't
work,
nothing
works,
that's
right
right,
so
that
says
they
now
exploit
the
tunnel
to
get
you
back
somewhere,
where
there's
where
there's
others
computing
power
and
you've
got
your
authorization,
databases
and
stuff
like
that.
Right
again,
where
did
that
you
may
still
need
to
get
all
your
data
back
to
there,
but
then
you
can't
survive.
You
can't
have
any
local
communication.
You
can't
survive
disaster
scenarios.
B
Often
you
know
some
of
the
low
latency
applications
mayhap
need
rapid
startup
as
well
as
rapid
operation
and
then
so
the
latency
of
just
getting
started
when
you
have
to
go
all
the
way
back
into
the
core
to
do
an
authentication
or
authorization
operation,
I
mean
I'm,
not
sure.
There's
that
I
have
an
answer
here.
This
is
just
a
question
or
are
they
actually
thinking
about
this
at
all?
Now.
C
The
current
study
item
is
about
a
user
plane
only
so
in
this
picture,
for
instance,
you
see
a
control
plane
and
all
the
different
policy
control
functions
which
are
currently
not
considered
in
a
study
item,
so
they
are
mostly
focusing
in
the
user
plane,
but
what
you
said
is
a
absolutely
necessary.
So
that
means
that
this
is
coming
back
soon,
probably
or
maybe
it's
gonna
be
a-
maybe
is
gonna,
be
a
new
thread
very
soon,
but
yes,
assumption
II
is
a
in
this
current
state
yeah.
Then
you
don't
touch
the
control
plane.
C
Control
plane
is
unchanged.
What
are
the
solutions?
Replace
the
gtp
user
planes
only
so
the
the
5g
service
base
architecture
makes
use
of
a
cups
models
where
you
have
user
plane
and
culture
plane
separations,
and
the
current
study
item
is
is
assuming
that
you
don't
touch
the
country
plane,
but
just
try
to
replace
the
control
the
GDP
protocol
with
other
solutions
for
that
specific
interface
or
set
of
interfaces,
but
you're
right.
This
is
to
be
sold.
C
The
the
well-known
is,
of
course,
which
also
support
a
control
plane
which
can
use
for
all
the
other
user
plane
solutions
like
a
LAN
SRB.
Six,
so
I
said
you
see
here.
Sorry,
six
is
being
used,
a
solution
for
ocular
base
and
ideologue
solutions,
because
for
the
flexibility
you
can
have
in
SRV
six
for
this,
the
different
kind
of
semantics
the
service
system
can
bring
can
carry,
and
this
is
one
solution
that
can
already
enable
some
of
these
cases
we're
talking
about
where
you,
basically,
you
can
off
the
model
core.
C
We
are
going
through
a
the
same
as
DW
or
PG
table,
for
instance,
so
this
is
a
first
step
to
world
offshored
in
a
core
by
a
49
core.
You
see,
I
have,
of
course,
mapping
system.
So
that
means
that
you
go
through
the
mapping
system
to
to
resolve
the
ID
lock
bindings,
but
it's
the
first
step
toward
the
use
case.
If
mentioned.
C
The
third
warning,
which
is
more
related
to
the
work
done
in
this
research
group,
is
using
ICN
is
a
solution
purely
AI
based
so
and
when
I
say
so,
we
have
used
in
working
in
a
working
with
the
term
ID
base,
essentially
to
explain
how
we
move
in
this
classification,
from
locator
to
ideal
of
separation
and
ID,
where
ID
is
a
namespace
she's,
a
location,
independent
and
HSE
n
is
the
one
that
we
we
have
inserting.
The
document,
because
it's
using
ipv6
and
this
is
a
oldest
solution-
are
actually
based
on
activity
six.
C
C
So
this
this
this
picture
allow
us
to
understand
where
functions
are
located.
So
this
is
a
typical
mobile
network
deployment.
We,
the
south
side
access
back
own
core
networks
in
the
upstream
internet.
So
the
whole
point
here
is
to
to
be
able
to
distribute
this
new
user
plain
functions
so
that
application
can
be
can
bypass
as
much
as
possible
the
mobile
core
when
application
or
local.
So
in
in,
like
a
our
VR
Reata
communication,
there
are
local
in
traffic
stays
local
without
going
through
the
court.
J
J
Then,
from
there
you
have
the
first
and
free
interface
that
connects
to
a
set
of
user
plane
functions
that
are
where
the
different
processing
is
done.
It's
a
generic
function
that
can
implement
what
was
previously
the
SDW
and
the
PGW
in
a
typical
deployment.
You
would
find
two
ups,
one
which
is
typically
referred
as
the
intermediate
UPF,
which
was
a
sgw
previously,
which
is
optional
in
5g
and
another
one,
which
is
the
padilla
session
on
Kohan,
that's
typically,
where
the
IP
address
and
the
prefixes
of
the
we
advertised
to
the
internet.
J
J
Between
the
UE
and
the
data
network
dn,
so
one
important
feature
that
was
introduced
like
in
4G
and
then
in
Phase
II,
is
the
separation
of
control
panels
open,
which
are
used
to
distribute
some
of
these
functionalities
really
close
to
the
edge
I
will
skip
this
one
so
in
the
DMM
works.
What
has
been
proposed
so
far
is
two
ways
to
try
to
introduce
new
data
plane
technologies.
J
J
J
So
entry
is
linking
the
run
with
the
mobile
backhaul,
so
it's
different
working
group
I
think
it's
City
to
in
free
GBP,
which
is
responsible
for
that,
and
they
would
need
cooperation
if
they
want
to
extend
this.
So
it's
strongly
recommended
by
the
specification,
because
if
you
have
two
different
technologies
in
a
nine
and
and
three,
you
need
some
internet
walking
between
the
two.
So
it's
likely
that
change
in
entry
will
trigger
most
of
these
afterwards.
J
Okay
and
the
integrated
model
so
is
proposing
the
replacement
of
gtp.
You
buy
those
new
data
planes,
so
I
will
quickly
show
you
some
possibilities
for
the
entire
working
model.
First,
and
there
are
two
option:
the
first
one
is
leveraging
the
mobile
edge
compute
and
the
second
one
is
introducing
some
function
in
the
UPS.
J
So
one
interesting
function
that
we
have
in
5g
is
what
is
shown
here
as
the
you
LCL,
it's
the
amplifier.
So
it's
a
function,
a
UPF,
the
disable
to
split
traffic
based
on
some
filter
on
the
destination
address,
and
that
can
be
interesting
to
be
able
to
divert
some
of
the
traffic
towards
some
function
which
can
be
located
in
a
mech.
J
So
the
problem
with
such
deployments
is
that
when
you
get
out
of
the
network,
you
still
have
the
AP
Encore
point
which
is
situated
in
the
in
the
core
network,
and
that
would
mean
that
any
communication
talking
to
the
Yui
would
have
to
go
through
this
producer.
Unless
you
do
complex
traffic
engineering
to
try
to
redirect
those
prefixes.
J
This
morning,
where
the
discussion
that
3gpp
would
strongly
advise
to
have
a
symmetric
pass
and
that
you
would
like
the
traffic
to
return
back
from
white
exited
the
network,
so
second
possibility
would
be
insertion
in
a
bf.
I
will
skip
this
one
and
then
the
second
option
is
to
really
try
to
leverage
mod
and
such
an
affinity
plane
by
replacing
gtp.
Yes,
just
a
quick
question.
K
J
K
J
What
is
ensured
by
Jayceon
is
that
the
traffic's
go
through
the
rest
pass
through
each
haan
node.
That
was
inserted,
and
we
do
that
by
using
the
writing
of
the
source
address
of
the
packets
that
exceeds
so
that
when
another
response
it
responds
to
the
previous
adjacent
hop
is
done
back
to
the
requester.
Something
like
that.
It's
not
not
it's!
It
can
be
similar
to
address
translation.
J
So
the
replacement
of
a
nine
is
real,
an
alternative
to
GPU
and
it's
mainly
replacing
TTP
you
within
the
DOE
mobile
backhaul
between
ups.
So
what
has
been
proposed
is
to
use
either
some
idyllic
implementation
or
I
see
an
implementation
at
the
different
borders
of
the
node
and
use
those
new
data
planes
to
have
more
optimized
forwarding
and
mobility
in
between.
J
So
if
we
look
at
the
protocol
stack
so
here
we
have
represented
standard
3gpp
protocol
stack
for
Phi
G,
and
you
see
after
the
radio
access
the
the
GD
P.
You
stack,
which
is
built
up
of
UDP
IP,
and
one
of
the
objectives
would
be
also
to
try
to
simplify
this
encapsulation
and
eventually
remove
it,
and
that's
why
we
have
solution
like
ila,
which
tries
to
to
have
to
remove
completely
on
capsulation
and
simplify
mobility
management.
So
we
see
that
food
is
new
data
planes.
K
John
again
just
a
general
comment:
when
you
have
this
new
data
playing
I,
wonder
I
mean
I've,
been
exploring
some
ideas,
a
lot
on
this
space
that
may
use
a
distributed
routing
or
something
like
the
Casa
or
so,
and
some
way
for
it
to
converge.
But
it
looks
like
if
you're
tracking
for
flow,
you
know
if
there
are
and
I
mean
the
communications-
are
going
to
be
like
an
N
square
in
terms
of
complexity.
So
I
wonder
if
you
have
looked
at
the
scalability
and
things
like
that.
K
K
K
A
C
So
the
answer
is
no,
if
the
focus
on
ipv6
but
the
work
that
Robbie's
been
doing
with
other
people
here
in
the
research
group
is
using
the
there's
a
very
small
opportunity
to
do
that
by
using
the
so
called
I'm
structure,
PDU
and
5g,
which
is
a
which
is
an
opportunity
to
do
that.
But
is,
if
you
look
at
the
instruction
specification
in
3gpp.
Documents
can
be
far
four
to
five
lines
without
any
clear
use
case
where
you
can
really
support
the
kind
of
approach.
I
You
think
I'm
gonna
chase
you
in
your
introducing
two
new
parameters,
pretty
much
you're
saying:
there's
an
IP
interest
packet
right.
We
get
a
packet
and,
if
you're
doing
some
kind
of
network
management,
and
probably
you
eventually,
this
sees
the
light
of
day.
You
would
take
it
as
new
kind
of
packets
in
the
network.
That's
right!
New.
I
New
functions
into
the
IP
layer
and
I
mean
you're
overloading
IP
with
some
new
semantics,
and
there
are
two
new
kinds
of
packets
here.
Of
course,
new
transport,
semantics,
and
so
eventually
I
mean
it
would
be
treated
as
some
unstructured
videos,
I
mean
because
it's
it's
it's
enabling
new
network
architecture,
and
it
was
completely
new
definitions.
Yes,.
C
I
Now
you
have
you:
have
the
choice
in
application:
pretty
much
I
see
an
applications
right,
I
mean
they're
just
behaving
like
that,
and
they
are
now
putting
these
new
kinds
of
IP
packets
into
the
network
and
you're,
enabling
some
new
functions
in
the
IP
transport
saying
that
okay,
there
are
few
sets
of
routers
that
are
do
HIC
and
functions
so
from
network
management
perspective.
You
may
want
I
mean
eventually.
If
you
people
are
going
into
the
depth
of
it,
they
would
like
to
separate
these
two
kinds
of
PDUs.
I
There
is
a
regular
IP
PDUs
and
the
ones
that
are
HIC
in
base.
So
in
that
sense,
what
I'm
saying,
even
when
endpoints
are
putting
these
packets
into
your
5g
network,
they
would
would
probably
want
to
take
it
in
a
different
way.
It's
a
different
I,
don't
know
that.
Go
that
way,
but
I'm
saying
that
it
seems
to
be
a
network
management
perspective.
That
seems
to
be
a
problem
by
itself
way.
I
C
C
C
Encapsulation
I,
don't
think
they
D
encapsulation
EEZ
is
a
the
point.
Is
you
have
a
new
a
new
semantics
in
the
in
the
user?
Plane
which
is
lock
ID
so
in
caponata,
is
not
a
point
because
it
can
be
made
using
ila,
which
is
not
doing
cup,
but
the
philosophy
exits
the
same.
So
then,
so
you
need
a
leased
contra
plane
to
enable
the
located
semantics
in
the
user
plan.
I
C
I
B
The
IP
router
cannot
tell
they're
different
and-and-and-and
if
the
well,
no,
no,
the
reason
I
bring
this
up
is
this
is
this
is
the
trap
that
the
mobile
operators
fall
into
over
and
over
and
over
again,
which
is
something
that's
supposed
to
be
general
and
transparent?
They
attempt
in
many
cases
to
differentiate
the
different
types
of
traffic
and
try
to
treat
it
differently
and
every
time
they
try
to
do
this.
They
fall
over
right
because
they
create
black
holes.
They
try
to
accelerate
things
with
proxies
and
slow
things
down.
B
You
know
so
I
mean
whether
you
believe
in
this
whole
approach
of
trying
to
shoehorn,
ICN
style,
routing,
forwarding
naming
into
an
ipv6
context
or
not,
but
that's
an
interesting
discussion.
You
know
some
people
think
it's
great
idea.
Some
people
don't,
but
the
worst
thing
you
could
do
is
turn
it.
Do
that
and
then
sacrifice
the
fact
that
you're
using
ipv6
in
terms
of
it
being
transparent
to
all
the
I
thought
the
whole
of
everything.
That
knows,
it
only
knows
that
it's
doing
ipv6.
I
K
Very
quick
follow-up
question
on
that.
You
mentioned
that
you
wouldn't
end
up
with
the
n
square
problem
because
you're
not
tracking
power
flow
and
going
on
to
what
Dave
said
about
authentication
and
authorization.
Would
you
be
able
to
also
authenticate
and
authorize
users
without
tracking
that
state
left.
K
C
This
nation,
it's
a
mandatory
I
mean
it's,
not
it's
not
adoption.
Now,
whatever
say
my
answer
was
mainly
did
the
current
study
item
is
just
focus
on
user
plain
he's,
not
he's
not
touching
the
control
plane.
That
means
that
any
solution
is
to
support
the
user
plain
the
control
plane
functionality.
Functionality
is
they
are
that's.
That's
the
disappoint.
B
Usual
authorization
by
itself
is
not
order,
N
squared
because
you
authorized
users
to
talk
to
anything
right,
so
you
only
have
one
in
if
you're
attempting
to
do
authorizations
on
a
pairwise
basis.
This
user
is
talking
to
this
thing.
Then
you
have
an
order,
N
squared
problem
and
and
we're
back
yeah
we're
back
in
hell
right
forever.
K
A
Let
me
ask
you
like
they
asked
me
em,
like
you
and
one
question,
so
so,
thanks
for
doing
this,
to
us
in
I
mean
I
know
that
you
are
kind
of
discussing
this
work
and
DMM
and
also
in
the
area
and
so
on.
Is
there
something
that
you
cannot
expect?
I
would
like
to
see
happening
in
icy
energy,
something
that
the
group
should
be
doing
or
any
recommendations
on
your
side.
C
E
Oh
and
there's
like
an
actually
an
interesting
point
about
that.
Around
timeliness,
because
the
3gpp
community
moves,
like
an
you,
know,
breath
day
like
very
fast
speeds,
and
we
have
to
kind
of
keep
up
with
them,
but
they
I
think
we
can
once
we
get
these
proposals
into
shape
and
they
represent
our
kind
of
community
here
that
really
wants
to
see
something
ICN
like
out
in
the
broader
world.
How
do
we
strategically
I
would
infiltrate,
but
I
would
say
influence?
E
C
C
We
showed
scalability
about
the
solution
for
that
use
case
for
that
application,
and
we
see
the
data
and
we
can
use
that
data
to
support
when
you
scale
compared
to
another
and
say
this
is
where
it's
gonna
help
and
we're
gonna
we're
gonna
gain
X
or
Y,
and
the
data
is
there
its
public
and
we
can
use
it.
So
this
is
to
be
the
word
I
expect
from
research
and
so
well.
E
L
Okay,
thank
you.
Okay,
I'll!
Try
to
keep
it
to
my
five
minutes,
so
this
is
for
the
deployment.
Can
its
considerations
for
ICN
draft
I
have
some
background
material
here,
but
more
you
know
you
can
read
it
offline,
but
basically
we're
trying
to
address
the
charter
item
about
giving
guidelines
for
deployments,
as
a
name
suggests.
L
We
basically
first
start
with
sort
of
a
classification
of
the
different
types
of
deployments,
I
think
more
or
less
in
line
with
you
know
the
sort
of
research
and
industry
view
there's
the
clean
slate
overlay
on
top
of
IP
underlay
sort
of
basically
you
being
the
basic
fabric
and
then
as
a
slice.
You
know
originally
motivated
by
5j,
but
it
could
be
applied
elsewhere
and
then
in
the
last
version,
so
I'll
touch
our
bun.
You
know
some
of
the
latest
updates
we
did.
As
I
talked
in
the
last
version.
We
created
this
new
category
composites.
L
So
we
created
this
new
new
category
called
composite
and,
as
you
can
see
from
the
the
the
next
part
of
the
slide,
the
hybrid
ICN
was
really
the
one
that
that,
as
a
trial
that
we
could
clearly
categorize
there,
the
other.
So
that
was
one
major
update
since
the
last
IETF.
For
since
the
last
time
I
presented
the
other
world,
major
updates
were
basically
in
the
I
CNS
and
underlay.
We
got
good
feedback
from
the
community
about
the
end,
ran
and
the
doctor
test
beds.
So
the
n
ran
my
understanding.
L
Is
it's
a
US
base
test
system?
So
we
got
some
good
texts
there
that
from
the
participants
of
Enron,
so
we've
it.
We
put
that
into
the
draft
and
then
the
doctor
test,
but
actually
we
had
a
lot
of
good
feedback
from
that
group
that
the
doctor
test
bed
is
really
it's
concentrated.
On
security,
it's
it's
a
it's
a
French
testbed.
It's
concentrated
on
looking
at
some
security
aspects
of
ICN,
we've
categorized
it
as
an
underlay,
but
it
had
also
some
virtualization
aspects
to
it.
L
It
was
basically
coordinated
sort
of
virtualized
Network
reacting
to
security
threats,
so
it
had
some
aspects
of
that
of
icns
a
slice,
but
we
agreed
that
it
would
be
classified
as
I
seen
as
a
as
an
underlay.
So
really
this
is
one
of
the
key
parts
of
draft.
The
other
parts
that
did
not
have
many
updates
in
the
last
few
revisions
cover
some
other
important
aspects
that
we
think
are
useful
for
people
considering
deployments.
L
So
we
looked
at
okay,
you
know
what
are
the
issues
with
application
or
service
migration
or
migration
of
various
parts
of
the
network,
and
then
we
tried
to
map
it
back
to
those
classes,
and
you
know
which
class
had
which
benefit
for
these
issues,
that
practical
practical
operator
or
somebody
else
deploying
would
be
considering
so
that
that's
what
that
deployment
migration
paths,
part
of
the
of
the
draft
covers,
and
then
we
had.
You
know
for
IETF
an
IRT
F,
an
important
section.
L
We
thought
for
giving
into
future
standardized
to
help
interoperability
of
ICN
systems
when
they
go
into.
You
know
wide
scale
deployments
so
mapping
to
http
exchanges,
dynamic
naming
routing,
etc,
and
then,
finally,
we
try
to
hopefully
add
some
added
value
with
some
summaries.
There
was
two
main
summary
sections
one
after
the
trials
trial,
experience
section
and
then
a
final
summary
so
really
just
make
a
synthesis
of
all
the
key
points,
including
in
the
last
update.
Some
I
think
good
security
considerations
from
the
doctor-doctor
testbed.
L
This
is
small,
but
hopefully
you
can
meet
it.
It's
basically
the
table
of
contents,
so
it
gives
you
a
good.
You
know
view
of
what's
covered
and
then
just
in
quick
summary,
we
started
the
draft
in
Chicago.
We
got
lots
of
interactive
feedback.
Dave
also
did
very
good
with
you.
You
know
in
that
span
between
98,
ATF,
98
and
100.
L
It
got
adopted
in
the
one-on-one
time
frame
and
then
the
chairs
suggested
that
we
follow
the
working
group
to
ask
for
more
deployment,
trial,
experiences
and
and
any
other
feedback,
obviously,
and
so
revision,
one
two,
and
actually
it's
now
revision.
Three,
it's
a
typo.
It's
missing
that
to
me.
We
got
good
input
from
these
authors,
authors,
but
these
contributors
from
different
test
systems
and
Lukas
here
I
know
what
the
other
ones
Michael
and
Misha
do
yeah
I,
don't
think
they're
here,
but
they
gave
good
input
and
we
need
next
steps.
L
Is
there
any
other
trials
that
people
think
we
should
cover
and
that
hopefully,
would
add
some
added
value,
because
we
already
have
quite
a
good
listing
of
trials
way.
It's
not
supposed.
It's
not
meant
to
be
exhaustive,
obviously
was
more
meant
to
be
illustrative
and
then
to
the
chairs
into
the
working
group.
L
Do
you
think
going
or
seeing
if
we're
ready
for
our
G
last
call
is
useful
from
the
author's
point
of
view
we
believe
you
know
if
the
document
is
of
good
quality,
if
people
agree
to
that,
it's
probably
better
to
put
it
in
the
RFC
queue
and
have
it
as
something
published
from
the
working
group
so
that
the
community
at
large
can
reference
it
so
that
that
was
our
thinking.
So
I'll
stop
there
for
any
questions.
So.
B
D
B
Okay
latest
version
all
right,
so
we
kind
of
need
some
more
eyes
on
this.
There
are
two
ways
we
could
go
forward.
One
is
to
plea
for
more
eyes
on
it
on
the
mailing
list
by
itself
or
the
other
was
potentially
acquired.
The
question
by
kind
of
trying
to
last
claret,
which
was
usually
read,
brings
out
the
additional
comments.
So
let
me
get
a
sense
home
from
the
room
or
the
are
there.
People
who
think
this
is
sure
I
speak
this
negatively
or
positively.
B
M
So
hello,
Milan
storage
with
Cisco
Systems.
They
worked
on
this
draft
together
with
Prakash,
tsuita,
doukasen
and
Ravi.
This
was
about
a
native
deployment
of
ICN
in
Normandy
network.
So
specifically,
we
were
looking
at
the
4G
or
LTE,
so
the
idea
behind
the
draft
was
to
prevent
so
as
a
reminder
to
present
the
holistic
view
of
native
ICN
deployments
in
4G
LTE
mobile
networks.
M
So
we
were
looking
at
a
few
specific
use
cases
depending
on
which
of
the
nodes,
if
you
think
of
the
path
between
the
UE
and
the
gateways
and
beyond,
depending
on
which
of
the
nodes
in
that
path,
do
or
do
not
support
ICN,
so
we
were
analyzing
first.
How
would
that
look
in
the
control
plane
and
then
after
that,
in
the
user
plane?
If
you
look
at
the
path
of
the
data
packet,
what
would
happen
if
the
user
equipment
would
be
using
dual
stack,
IP
and
ICN
in
a
device
in
deployment
models?
M
A
similar
thing,
for
you
know,
B,
and
also
in
the
EPC
gateways,
specifically
for
SK
28,
where
we
are
looking
at
the
possibility
if
they
support
ICN?
What
kind
of
protocol
changes
we
will
be
looking
at
and
we
were
discussing
the
introduction
of
the
transport
convergence
layer
in
the
protocol
stack
to
support
this
in
the
summary
of
the
update
since
the
last
time
we
presented
this.
That
was
back
in
London
four
months
ago.
M
So,
first
of
all,
we
want
to
thank
their
chairs
and
all
of
the
reviewers
for
providing
the
input
and
making
this
a
workgroup
draft
and
also
were
the
drafts
we
have
direct
updates.
We
have
implement.
This
is
the
last
time.
Those
were
a
few
review
comments
there
also
regarding
the
QoS,
which
we
vaguely
mentioned
in
the
first
release,
this
there
was
just
a
little
more
clarification
on
the
definitions
of
the
problem
and
the
necessity
of
addressing
them.
This
draft
does
not
get
into
addressing
the
actual
qsr
implementation.
That's
beyond
the
scope
of
it.
M
Then
we
also
discussed
the
further
caps
implementation
discussion.
Basically,
if
the
caps
is
implemented,
what
does
that
mean
for
the
network?
Then
we
describe
the
lab
setup,
which
we
don't
have
the
results
yet,
but
the
website
appears
in
progress
and
we
provide
centralized
some
of
the
text
and
updated
editing.
M
References
in
a
little
more
detail,
so
a
comment
on
the
research
done
so
far
on
QRS
is
what
was
added
and
a
necessity
to
handle
QoS
and
data
packets,
and
that's
pretty
much
where
we
stop
in
this
draft
when
it
comes
to
a
control
and
user
playing
separation,
and
we
were
talking
about
the
implication
of
the
cups
if
the
cups
were
implemented
in
the
network.
What
does
that
mean
specifically
to
the
publisher
placement?
How
does
that
influence
the
publisher
and
its
capabilities?
A
similar
way
was
discussed
for
the
UPF.
M
M
Want
to
have
the
results
from
the
lab
trials
in
the
next
release,
so
we
plan
on
doing
that
for
the
next
for
the
next
IETF
conference
and
areas
for
future
updates
that
we
may
be
that
we
are
considering
for
updating
further
impact
over
over
of
cups
introduction,
because
this
was
just
touching
this
time,
then
also
the
realization
of
transport
convergence
layer.
That
is
mentioned
on
page
14
of
the
document.
M
We
would
like
to
investigate
further
through
lab
trials
in
beyond
what
does
that
mean
really
for
the
protocol,
stack
impact
analysis
or
ICN,
or
mobility
management
messages,
structure
and
flows,
and
also
to
investigate
how
the
interworking
gateway
would
react
or
what
would
be
required
from
interworking
gateway
to
perform
the
conversion
between
ice?
You
know
IP
primitives,
for
data
retrieval.
M
Lastly,
there
are
there's
a
number
of
ancillary
functions
in
any
data
core
in
any
impacted
core.
That
would
have
to
be
analyzed
in
more
detail
if
we
were
to
introduce
ICN
to
it,
for
example,
lawful
interception,
billing
mediation
network
slicing
provisioning
API
as
requirements
and
such
and
that's
all
for
the
update
so
far.
Thank
you
for
your
contributions
and
we'll
be
looking
forward
to
reducing
comments.
N
M
B
So
my
my
chair,
hats
off
for
this
particular
comic.
Could
you
go
back
to
the
previous
slide
for
a
second
I
can't
yeah,
so
the
last
bullet,
just
just
a
piece
of
unsolicited
advice?
Yes,
tread
carefully
on
any
ITF
document
that
talks
about
lawful
interception,
billing
or
mediation.
There
are
constraints
on
what
we
like
to
do
in
the
ITF
that
touch
on
those
things
so
I
can
we
can
give
you
some
guidance
when
some
of
the
previously
published
RFC's
about
about
ITF
stuff,
not
getting
involved
in
any
of
those
things.
So,
okay.
F
B
M
N
A
O
N
O
N
Okay,
so
in
the
IP
world
you
have
this
6lowpan
layer.
If
we
put
next
to
it
the
Indian
or
CCN
layer,
then
these
two
count
in
to
operate
anymore
and
you
will
have
a
clash
on
the
network
so
for
this
we
already
introduced
in
Singapore
I
believe
the
dispatch
and
fragmentation
framework
for
a
lopen
that
jointly
can
operate,
IP
and
Indian
or
CCM,
and
we
discussed
first
steps
of
header
compression
and
I
will
give
you
an
update
on
this.
So
this
is
actually
the
port
where
we
had
an
update,
whoops.
N
So
I
have
already
presented
or
saying
I
guess
presented
in
London
about
stateless
header
compression
rarely,
but
you
basically
take
condense,
the
Tia
visto
to
a
more
efficient
format,
and
if
you
do
so,
you
gain
for
this
example.
It's
just
a
simple
example:
you
send
an
interest
for
this
ACM
ICN
Boston,
blah
blah
blah,
get
a
content
of
21.2
degrees
and-
and
if
you,
if
you
just
do
this
for
this
simple
example,
you
save
about
25%
and
what
we
introduced
now
is
to
state
4
header
compression
mechanisms.
N
N
So
what
is
what
is
the
no
local
states
or
what?
If
you
look
in
the
document
now,
if
you
remember
there
was
a
there's,
this
there's
this
dispatch
field
and
this
dispatch
field,
that's
basically
the
the
compatibility
layer
in
the
lopen
that
distinguishes
between
the
payloads
and
vistas
pledged
field
had
an
indicate
a
bit
on
on
that
you
could
have
compression
contexts.
You
could
set
compression
context,
and
this
is
now
defined
here.
You
have
a
compression
context
that
actually
represents
a
shared
state
and
in
the
network,
for
instance,
there
could
be
a
common
prefix.
N
The
along
the
path
or
a
route
state
is
something
that
is
specific
for
a
particular
request
response
and
actually
goes
back
to
an
to
an
inspiration
by
Dave.
You
gave
in
Singapore
if
I
remember
correctly,
and
that
is
basically
the
idea
that
you
I
mean
your
request
carries
the
name
and
the
response
carries
the
name,
the
same
name
again.
So
what
you
can
do
is
you
can?
N
If
you
send
your
interest,
you
can
distribute
local
link,
local,
a
short
identifiers
and
put
add
them
to
the
to
the
pit,
and
if
you
that
is
basically
done
here
so
you
you,
you
communicate
the
link
local
state.
It
is
editor
of
the
pit
and
if
you'll
come
back,
then
you,
then
you
simply
communicate
these
link
local
states
and
you
elide
the
name.
So
you
don't.
Your
data
doesn't
carry
the
name
anymore,
and
that
makes
it
just
shorter.
N
N
The
next,
basically,
what
we
want
to
do
is
say
we
want
to
add
stuff
that
this
actually
goes
to
other
link
layers
like
ble
and
stuff
or
a
lower
one.
That
is
not
part
of
the
drafts
yet
and
probably
do
some
more
homework
on
the
play
on
the
packet
formats
and
on
the
details
and
then
probably
will
ask
for
vocal
production
or
research
group
adaption,
soonish.
O
D
Yes,
this
is
Jonathan
from
a
tree,
and
this
is
a
update
on
a
nurse
trapped.
I
have
a
tree
trapped,
which
is
related
and
being
resolution
service
and
I'll
go
over
here,
EB
up
to
each
and
keep
the
short
update
and
the
first
one
is
the
requirement
for
an
iris
in
ICN.
This
is
the
first
revision
and
this
document
discusses
the
motivation
and
requirements
of
an
arrest
in
ICN,
and
we
hadn't
represent
a
number
of
use
cases
in
this
draft.
We
in
this
revision
we
added
another
use
case,
manifests
support
44,
another
use
cases.
D
D
We
have
updated
the
description
in
details
and
what
haven't
changed
much
for
the
structures
or
contents
of
tables,
and
the
last
one
is
the
architecture
consideration
of
the
ICN
using
NRS.
This
is
the
first
revision
we
just
updated
the
introduction
part
as
violence.
The
Ana's
has
been
discussed
in
ICM
focused
on
the
considerations
in
the
requirements
or
EMRs
itself,
and
also
there
are
a
few
and
our
systems
implementing
has
been
introduced
in
ICM.
D
We
had
the
blue
feet
based
in
a
system
before
for
platinum
based
robbing,
and
now
we
have
a
CCX
exchanger
for
an
arrest.
However,
it
is
necessary
to
discuss
the
an
IC
and
architecture
issues
to
be
considered
when
another
system
is
used
or
implemented
in
ICS,
so
this
document
discusses
the
IC
and
architecture
considerations
for
an
arrest,
and
this
is
the
shirt.
This
was
the
shirt
updates
for
three
documents,
and
this
is
a
summary
of
analyst
talk
that
I
presented
in
last
Sunday
meeting
as
I
just
talked.
D
A
Yes,
thank
you
John
hi,
so
so
the
chairs
have
been
you
know,
thinking
about
so
what
to
do
with
with
this
work
so
as
Jonah
and
colleagues
have
worked
on
this
for
quite
some
time
and
has
been
quite
a
journey,
and
so
now
they're
at
a
state
where
they
and
have
achieved
good
results
and
sample
also
shown
in
the
demo
on
on
Sunday
and
so
name
resolution
sometimes
comes
up
in
our
discussion
I'm.
So
it's
not
only
John
has
team.
That's
looking
at
that.
A
So
we
are
we're
thinking
about
what
would
be
a
good
output
of
icy
energy
on
this
topic,
and
so
Trina
has
this
sweet
draft
that
she
just
mentioned?
Is
there
any
immediate
feedback
or
comment
from
from
the
book?
So
do
you
think
we
should?
We
should
have
a
say,
published
document
on
name
solution
at
some
point
or
in
the
near
future?.
B
Chair
had
off,
they
were
on
just
a
couple
of
thoughts.
One
is
that
you
know
we
as
a
research
community
are
trying
to
capture
the
output
of
good
work
and
and
whether
we,
when
we
carry
something
forward.
It's
not
necessarily
saying
this
is
the
final
answer,
or
this
is
the
right
approach
for
everybody
to
take
toward
toward
doing
a
particular
function
in
in
the
ICN
world.
So
I'd
like
to
sort
of
frame
the
question
of
the
ICN
RG,
which
is
that
there's
a
ton
of
work
that's
gone
into.
B
This
is
the
assessment
of
the
group
that
it's
mature
enough
to
capture
as
publishable
material
out
of
the
IC
energy,
because
it's
it's
it's
been
done.
There's
a
lot
of
work,
we've
talked
about
it
a
lot
and,
and
it-
and
you
know
if
people
think
that
it's
valuable
in
informing
our
future
work,
whether
it
just
turns
out
to
be
the
right
way
necessarily
to
to
design
the
architecture.
There's
a
certain
argument
for
for
pushing
this
fairly
toward
toward
publication.
B
The
people
think
that
it's
kind
of
a
sideshow
and
maybe
not
something
that
will
help
us
move
other
stuff
forward.
Then
you
reach
a
slightly
different
conclusion,
so
I'd
like
to
sort
of
frame
the
question
in
terms
of
the
clarity
and
the
maturity
of
the
work,
as
opposed
to
trying
to
come
to
some
realization
that
you
know,
NRS
is
a
way
to
do
particular
things
in
the
architecture,
in
contrast
to
doing
in
another
ways.
So,
but
but
that's
the
way,
I'd
recommend
you
frame
this
and
with
chair
hat
off
right.
E
So
before
you
came
out
here
and
and
spoke
to
us
I,
my
question
back
to
the
co-chairs
and
other
people
was
going
to
be
well,
what's
the
hesitancy
and
if
there
is
a
hesitancy,
because
that
was
the
way
it
was
sort
of
asked
like
we're,
hesitant
I,
don't
know
that
was
how
I
interpreted
it.
I
would
ask
why,
and
could
we
frame
some
of
the
hesitancy
as
the
intro
to
the
documents
so
that
we
capture
whatever
the
you
know
prevailing
sentiment,
is
in
the
in
the
proper
language.
A
Well,
the
so
the
consideration
that
I
had
was
more.
That
I
mean
there
are
there's
no
more
than
one
draft,
and
so
we
journalist
thought
it
was.
You
know,
requirements,
and
so
now,
lately
they
focused
more
on.
We
call
architectural
considerations,
and
so
my
question
was
more
so
what
type
of
do
we
actually
want
to
see,
and
so
I
admit
today,
if
that,
so
when
we
publish
something,
we
wouldn't
we
say,
if
you
you
know,
if
you
do
ICN,
you
need
to
have
an
NRS
and
has
to
look
like
this.
I
Yeah
without
being
unnamed
is
generally
I,
mean
that's
a
research
challenge,
and-
and
that's
we
had
one
draft,
which
is
also
which
is
looking
into
a
I
and
I
split
application
identifies
a
net.
Prevent
fans
requires
some
kind
of
baptism
and
that
fundamentally
dictates
how
you
do
routing
and
mobility
management,
and
things
like
that.
So
I
think
this
is
a
very
useful
component
function
to
investigate,
but
I
would
see
it
in
that
larger
perspective
of
how
do
you
handle
named
days
routing
in
ICN.
O
A
B
So
I'm
practicing
for
Hitoshi,
say
the
engine
channel
from
kit
for
maken-ki
t
so
there's
a
draft
that
discusses,
maybe
one
of
the
first
attempts
to
really
integrate
network
management
types
of
functions
into
the
ICN
architecture
and
deals
with
how
you
discover
the
state
of
content,
routes,
caches
and
other
things
in
an
ICN
network.
So
if
we
look
back
a
little
bit
of
the
history,
those
of
you
have
been
around
primer
clevis.
B
This
started
out
as
one
of
two
approaches
to
doing
the
equivalent
of
IP
traceroute
in
an
ICN
world,
and
this
proceeded
in
parallel
with
another
draft
called
ICN
traceroute
I
may
not
be
a
co-author,
but
I
contributed
to
PhD
students.
Interns
did
the
work
and
we
we
sort
of
went
off
in
a
funny
directions
there.
Well,
maybe
we
can
put
these
things
together,
so
we
don't
have
to
drafts
and
if
they're
talking
about
it
for
a
while
and
thinking
pretty
hard
about
it,
we're
all
eyes.
No,
no.
No.
B
We
want
to
drive
these
things
apart.
We
don't
put
them
together,
because
they're
really
doing
different
things.
One
is
sort
of
like
an
in
band,
very
simple
tool
or,
like
I,
see,
are
like
IP
traceroute
and
the
other
ones
are
sort
of
heavier
weight,
but
much
more
powerful
hammer
for
instrumenting
and
debugging
I
see
in
networks.
So
we've
ringing,
it's
been
renamed
CC
info,
so
it
doesn't
look
like
trace
child
anymore
and
it
does
a
whole
bunch
of
things.
B
I
don't
want
to
go
through,
because
this
is
a
draft
update,
but
it's
a
hefty
draft
and
I
really
recommend
those
people
who
haven't
read
it
read
it.
So
it
deals
with
things
like
reach.
Ability
of
publishers,
reach
ability
of
caching,
routers
contents
of
caches
helps
you
compute
popularity
and
cash.
It
ratio
things,
it
doesn't
actually
carry
it,
but
it
helps
you
compute
that
and
a
bunch
of
things
that
are
worrying
kind
of
potentially
important
in
your
production.
B
I
see
any
network
so
since
the
last
time
there's
a
there's
a
conflict
between
wanting
to
make
one
request
and
get
back
information
from
all
over
versus
issuing
individual
requests
and
trying
to
steal
them
to
gather
the
information
you
want.
So
we
have
sort
of
like
a
default
and
an
option
for
how
to
do
that.
The
motor
casted
version,
which
is
option
2,
has
some
very
interesting
congestion
control
challenges.
B
So
you
know
I,
think
that
would
somewhat
less
mature
and
probably
need
some
more
work.
So,
from
the
last
meeting
there
were
some
questions
that
were
brought
up
in
the
mailing
list
and
the
current
version
of
the
draft
pretty
much
addresses
it,
gives
those
answers
and
addresses
them.
So
here
we
are,
we've
split
them
apart.
We
have
a
substantive
document
that
that
forms
the
basis
for
sort
of
baseline
instrumentation
and
management
capabilities
works
for
CCN
today,
probably
could
be
crafted
to
work
for
him.
B
Indian
others
want
to
do
that
and
I
think
we'd
like
to
raise
the
question
as
to
whether
this
is
mature
enough
enough
interest
to
the
research
group
and
again
on
my
chair
off
here
to
adopt
it
is
energy
you
asked
so
I'll
turn
you
over
to
the
other
cheers
to
sort
of
clear
the
question
here.
Thank
you.
Thanks.
B
C
A
very
short
question,
which
is
well
remark,
first
question
later:
we
need
these
count.
Rules
in
especially
now
as
an
implementer
of
these
kind
of
things.
I
feel
like.
We
are
missing
these
kind
of
tools
for
a
very
long
time
and
it's
kind
of
critical,
so
it
would
be
really
nice
to
dis
adopted
by
the
research
group,
and
the
other
thing
is:
do
you
think
these
kind
of
things
can
also
be
worked
out
and
adapted
to
use
in
hoc
and
as
well
all.
B
B
A
I
Yeah,
this
is
going
to
be
shot
because
the
updates
are
not
very
significant,
this
time
compared
to
last
time,
so
the
basic
goal
of
this
hi.
This
basic
goal
of
this
draft
is
to
basically
look
at
deploying
ICN,
considering
the
5g
5
DC
core
network
architecture
that
is
being
proposed
in
3gpp,
and
you
know
we
have
several
motivations
for
this
Luke
Milan
and
all
referred
to
these.
I
In
the
context
of
these
networks
flat
architecture
we
have
to
transport,
storage,
caching,
seamless
mobility,
so
on
the
more
important
challenge
is
whether
you
could
solve
some
of
the
problems
related
to
the
different
key
scenarios
for
a
movie.
Once
you
see
it
effectively,
then
what
could
be
done
using.
I
I
So
that
you
could,
you
can
do
all
the
things
like
authentication
and
session
management
and
when
you
introduce
I,
see
things
we
leverage
is
the
use
of
unstructured
video.
So
we
had
the
discussion
here
or
what
is
known:
IPP
teams
for
IC
and
deployment,
and
some
we
have
some
education
and
then
we
also
have
a
people
that
was
presented
for
a
couple
of
weeks
back
I
try
to
provide
G.
I
So
this
is
the
outline
of
the
draft.
So,
as
I
said,
like
we
discussed,
the
motivations
I
mean
look
into
the
Phi
G
Co
network
architecture
then
propose
certain
extensions
to
it
from
the
control
in
perspective,
European
function
perspective,
and
then
it
basically
gives
different
use
case
scenarios
for
for
how
this
architecture
could
be
useful,
and
we
also
kind
of
I
mean
the
most
initial
versions
were
mostly
looking
from
the
CCM
Indian
architectures
perspective,
but
we
have.
We
also
included
discussions
related
to
other
ICN
architectures
that
is
working
within
this
5
GC
framework.
I
The
main
updates
in
the
draft
is
Gregg,
as
he
basically
had
a
draft
last
time
on.
Ipod
was
basically
looking
at
how
IP
services
can
benefit
from
ICN
deployments,
and
since
we
had
a
section
for
for
basically
a
native
IC
and
support
in
5g,
so
the
work
that
he
complements
to
what
we
were
discussing.
So
he
has
contributed
bit
to
this
job,
and
then
we
have
some
another
use
case
scenarios.
What
trussing
has
been
working
on
and
looking
into
how
his
architecture?
I
That
is
mostly
what
he
calls
IP
or
ICN,
was
demonstrated
for
basically
supporting
5g
computing
functions
again
within
the
context
of
this
framework,
also
that's
prosecuted
after
updates.
So
again,
this
is
mostly
about,
as
I
said,
like
at
least
in
the
context
of
my
D.
We
don't
have
another
job,
so
this
becomes
a
good
job
to
take
related
contributions.
If
you
have
architectures
that
are
looking
into
these
frameworks
or
more
research
insights
into
be
actually
in
the
dark
we
have
left.
I
But
if
only
two
deployments,
we
have
kind
of
listed
several
challenges
of
how
you
can
handle
things
so,
and
they
mentioned
did
mention
about
all
the
other
policy
charging.
And
but
these
are
like
important
issues
you
cannot
escape
out
in
3gpp,
but
all
we
are
saying
is
that
how
can
you
do
this
in
some
rural
ways
in
a
more
distributed
context
in
the
quantity
of
doing
something
like
I,
CN,
n
5g?
I
So,
let's
see,
the
other
thing
is
to
of
course
see
whether
there
is
enough
interest
to
take
this
as
an
RG
item.
There's
good,
a
kind
of
industry
participation
in
this
job
and
I
think
it
would
be
quite
valuable
to
and
considering
that
5g
is
happening
and
you
have
really
16
and
17
happening.
So
it
could
be
a
good,
valuable
inputs
in
for.
I
L
This
Ackbar
I
think
it
would
be
something
good
to
to
adopt.
I
did
notice.
The
previous
discussion
slash
debate,
Ravi
that
you
had
with
Luca
and
somehow
at
least
the
topics
seemed
to
overlap.
Somehow
so
maybe
one
good
thing
you
know
for
the
community
point
of
view
would
be
to
try
to
see
if
there
could
be
some
alignment
or
I
don't
know
if
they
were
completely
orthogonal
I,
don't
think
they
are,
but
so,
in
addition
to
supporting
adoption
as
RG
item
that
could
be
one
area.
I
would
like
to
see
maybe
some
improvement,
but.
I
Yeah
I
mean
what
look
and
team
has
been
looking
at.
I
mean
that's
mostly
from
an
ipv6
transport
perspective,
and
this
is
mostly
looking
into
kind
of
native
ICN
perspective.
I
mean
so.
The
key
thing
is
here:
the
main
challenges
about
you
need
the
ICN
function.
Where
do
you
place
that
ICN
function
either?
What
V
Architecture
says
you
could
place
it
in
the
run
or
you
could
place
it
crossing
the
IP
town,
so
I
mean,
but
here
it's
not
really
kind
of.
I
A
Okay,
so
wrapping
up,
we
just
like
to
point
you
to
some
exciting
events
that
are
coming
up
so
in
September.
So
there's
going
to
be
the
right
summit,
September,
13
and
14
in
Amsterdam
right
is
the
IOT
operating
system.
That
also
has
an
ICN
stack
and
should
be
pretty
interesting
event
if
you're
interested
in
in
IOT.
A
So
the
the
program
of
that
conference,
it's
going
to
be
published
pretty
soon
if
you
still
want
to
get
involved.
So
just
today
we
published
the
the
call
for
papers
for
four
panels
and
posters.
Those
please
check
that
and
on
the
Monday
after
that
conference
we
are
holding
in
an
icy
energy
interim
meeting
us
also
in
person
and
just
let
you
know,
I
think,
there's
also
an
Network
code
and
research
group
meeting
on
the
Tuesday.
