►
From YouTube: IETF102-6TISCH-20180718-1330
Description
6TISCH meeting session at IETF102
2018/07/18 1330
https://datatracker.ietf.org/meeting/102/proceedings/
B
E
B
B
So
we
are
trying
to
own
that
they
gave
us
so,
let's
see
if
it
works.
So
this
is
a
traditional
80s
meeting,
so
all
the
provisions
of
the
best
practices
and
enjoy
to
property,
entire
restaurant
etc
apply
to
this
meeting.
The
particular
are
aware
of
any
idea
in
technical
subject
in
this
case
in
this
meeting.
Please
let
us
know
after
the
chairs
autonomy.
B
Remember
that,
as
an
hf
meeting
group,
everything
that's
being
said
is
shared,
meaning
that
your
presence
will
be
large.
The
minutes
will
be
recorded
and
kept,
and
people
will
be
able
to
visualize.
The
meeting
after
recording
will
take
the
notes.
The
minutes
of
the
meeting
on
the
etherpad
link,
then
etherpad
link
is
on
this
page
here.
Please
join
for
two
good
reasons:
one
if
you
have
trouble
understanding
what
was
said.
Maybe
somebody
captured
it
that
will
help
you
see
what
I
said
or
fix
it.
B
And
second,
if
you
say
something
of
them,
I
can
say
something
you
may
want
to
check
that
your
words
were
captured
correctly,
but
those
two
reasons
it
makes
a
lot
of
sense
to
join
the
ether
fan.
We
will
pass
on
the
blue
sheets
in
a
few
minutes
just
to
give
a
chance
for
the
late
comers
to
join
the
room
before
we
pass
them
on,
and
that
will
be
the
difficult
time
of
finding
minute
takers
and
most
he
jabber
scribes.
B
B
Thank
you.
Thank
you
all.
Thank
you
very,
very
much.
Okay,
so
the
other
links
for
the
various
materials
we
publish
the
minutes
on
the
ATF
site.
There
is
already
the
agenda
publish
there,
so
you
can
click
on
links
to
to
find
out
all
all
those
websites
and
with
this
let's
do
the
traditional
agenda
batching.
So
today
we
don't
spend
a
little
bit
of
time,
not
too
much
javi
explaining
us
the
latest
on
the
six
top
iesg
work
then
we'll
have
also
remote
thankful.
B
Oh
no
single
you're,
the
one
talking
right,
Simona
compliment
so
yes,
Simone
will
be
representing
us.
Did
the
Mirage
of
MSF,
then
Monisha
for
minimum
security
and
many
sure
there
has
been
a
lot
of
activity
on
minimal.
So
if
you
like,
we
can
actually
compress
the
micro
slots
which
I
intended
to
present.
To
give
you
more
time,
would
you
like
to
have
like
monisha.
A
B
Ultimates
flexible
is
to
put
your
last,
so
you
have
all
the
time
left,
but
I
wouldn't
do
that
either
so
say
what
I
you
have
25
minutes.
But
then,
if
you
I
won't
stop
you
if
you
go
to
35
or
even
40,
ok,
good!
So
we'll
make
a
hot
stuff.
Ok,
all
right!
That's
good
thanks!
So
then
we
have
2
discussions
about
Michael's
draft.
B
He
has
progressed
on
both
drives
on
both
drafts,
but
he
can
not
be
with
us
today,
so
we'll
be
presenting
an
update
and
then
time
permitting
will
have
javi
explaining
us
the
latest
on
global
time,
Jonathan
on
multiple
files
and
subjec
and
then
yatch.
We
had
a
very
interesting
discussion
about
which
the
weary
transmission
works
on
15
for
2015
and
actually
yet
extracted
the
operation
in
a
way
that
we
can
now
understand.
B
So
if
we
have
time
yet,
you
will
present
that
to
us
and
thanks
so
much
for
doing
this
yeah
and
then,
as
you're
aware,
we
are
working
at
6000
and
fragmentation
and
Tomas
presented
status
of
the
design
team
to
sit
slow
and
time
permitting.
You
will
show
us
where
we
are
in
that
respect.
So
this
trench
thing
at
60,
which
is
that
we
are
not
like
a
usual
working
group
just
doing
our
one
RFC's.
B
A
lot
of
our
work
is
actually
to
aggregate
integrate,
RFC's
from
different
working
group,
find
redundancy
and
say:
ok,
we'll
work
with
this
and
not
that
and
find
holes
and
missing
pieces,
in
which
case
we
go
and
push
off.
Some
work
in
the
work
which
are
responsible
for
that.
So
examples
of
that
are
the
work
that
we
are
doing
at
six
know
on
the
fragmentation,
and
then
there
is
all
this
see
clapping
and
the
update.
We
are
concluding
the
backbone
router,
which
is
part
of
our
architecture.
B
All
this
actually
derives
from
work
at
six
station
and
we
have
the
the
six
loaded
like
time
as
well,
which,
as
a
particular
variation
when
the
time
is
expressed
as
an
absolute
number
in
succession,
then
we
have
all
the
work
that
we
promoted
at
role.
That
includes
the
Software
Defined
Networking
variation
of
role
of
ripple,
which
is
called
our
projection
and
I
know
where
I
live,
which
allows
a
device
which
is
not
aware
of
people
to
get
written.
B
What
abilities
to
ripple
and
then
the
companion
draft
of
the
beacon
that
we'll
be
discussing
later,
but
six
at
role,
is
how
you
actually
propagate
and
help
on
the
geoduck
selection,
very
useful
for
sixty
very
useful
for
role
in
general.
How
do
you
help
select
the
right
ear?
Dag
when
you
see
multiple
networks
around
you,
and
then
we
have
a
relation
or
some
common
work
with
course
called
discussion
for
minimal
security,
which
we
are
working
on.
This
deck
is
proxy.
Our
inter
man
with
this
I,
will
give
you
the
ball
baby.
F
Thank
you.
So
a
couple
of
things
to
add
so
first
I'm
very
frustrated
cannot
be
there.
My
plane
was
canceled
at
the
very
last
minute.
I
wish
I
could
be
there,
but
but
I
think
this
works
well.
So
another
announcement
where
we're
looking
at
here
at
slide
Oh.
So
if
you're,
looking
on
the
link,
that
who
said
is
the
right
one
we've
been
updating
the
slides
with
a
kind
of
recent
work
that
happened.
So
if
you
have
downloaded
yesterday
night,
your
outdated,
so
do
you
should
download?
F
Oh
before
we
get
started
with
the
draft
three
tiny
announcements.
The
first
one
is
that
open
areas
had
114
was
released
a
couple
of
weeks
ago
and
it
implements
the
different
drafts
that
we're
talking
about
today.
Next
slide,
please
there
is
a
Six
stage:
sweet
now
released
1
0-0
as
part
of
elephant
drop.
If
a
drop
is
this
online
tool
that
allows
you
to
do
conformance
and
interrupt
tests
online,
and
so
there's
a
there's,
a
test
suite
that
implements
that
that
covers
the
different
drafts
that
we're
talking
about
today
on
F
and
drops.
F
We
can
test
your
implementation
against
it
anytime.
You
want!
It's
it's
a
free
service.
The
next
item
next
slide,
please
is
an
announcer
I
mean
as
a
reporting
that
we
had.
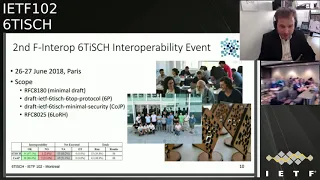
The
second
defender
of
succession
drop
event
held
a
couple
of
weeks
ago
in
Paris,
with
the
scope
that
you
see
here,
lots
of
fun.
We
run
whatever
number
of
88
different
tests
with
a
compliance
of
97.1%,
so
that
that's
good.
F
It
helped
us
tremendously
testing
this,
and
in
particular
we
we
tested
our
CID
180,
which
is
which
we,
you
know,
which
has
it
already,
but
also
the
six
stop
protocol
and
also
the
co
cheap
part
of
the
minimal
security
draft
and
then
six
low
RH,
and
that's
it
for
me,
the
next.
So,
let's
get
started
with
with
what
the
agenda.
E
Hi
everybody,
okay,
I'm
gonna,
present
a
little
bit
the
status
off
of
this
draft
we've
been
working
on
it
since
last
ITF.
We
got
the
review
from
the
IG
and
we
we
answer
all
of
them
to
the
mailing
list.
On
the
right
side
of
this
light,
you
see
the
different
persons
that
send
us
comments,
and
this
is
the
response.
This
is
now
the
status
of
their
their
their
claims
or
their
questions.
E
F
B
Just
out
of
your
hands
now
it's
between
the
Shepherd
and
the
area
director,
and
so
basically
yeah.
The
only
thing
you
could
do
was
make
sure
that
you've
answered
all
the
question
that
was
asked
and
maybe
chase
the
reviewers
if
they
did
not
confirm
that
they
were
okay
with
your
responses.
But
as
soon
as
you
know
you
you
got
you
okay
and
they
have
to
do
with
what
you
said:
the
body's
the
raw
in
your
hands
mm-hm,
basically
now
for
Suraj
to
ask
for
publication.
C
G
C
A
nutshell:
MSF
now,
after
the
merge
has
three
types
of
cells,
you
have
the
basic
minimal
cell
that
comes
from
the
sixties,
minimal
schedule.
So
it's
one
cell
that
repeats
periodically.
Let's
use
for
any
broadcast,
so
it's
Ronnie
Busan
everybody
wakes
up
at
the
same
time
and
Chandler
upset.
Then
you
have
what
we
call
it.
Animal
cells,
which
are
it's
one
cell,
every
Network
maintained
one
cell
every
node
maintained
once
LT
was
each
of
its
neighbors.
C
You
have
one
cell
to
to
to
receive,
and
you
have
one
cell
for
each
of
you
enable
to
transmit
to
them
and
do
some
antenna
to
numerously,
but
then
the
main
limitation
of
them
is
that
you
have
just
one
it's
just
one
perp
or
any
pair
of
node.
That's
just
one
link
to
communicate.
So
we
in
on
top
of
that
we
have
the
D
D
dedicated
cells,
which
were
already
present
in
msf
of
previous
versions,
which
are
all
negotiated
with
using
6p
with
60,
add
and
delete
commands.
C
So
whenever
there
is
more
traffic
need,
you
can
add
more
cells
between
child
and
parents,
so
I'm
going
to
focus
here
on
the
changes.
Since
last
time,
so
the
one
of
the
major
changes
is
the
addition
of
section
3,
which
is
grab
you
to
normal
cells,
which
could
simply-
or
so
you
have
as
I,
was
mentioning
quickly.
C
So
you
can
also
include
the
hash,
that's
how
this
is
done
now.
The
cells
they
have
is
that
the
TX
or
rx
flag-
and
they
always
have
the
share
option,
because
you
might
have
multiple
transmitter
understand.
Only
given
google
coordinate
and
one
last
thing
was
mentioning
here-
is
that
you
have.
You
may
have
collisions
in
your
schedule.
You
may
have
multiple
cells
executing
at
the
same
point.
C
In
time,
and
when
that
happens,
we
resolve
collision
at
runtime
exactly
as
much
as
define
in
a
cheerily
15.4
2015,
which
is
that
transmitted
cells
take
precedence
over
receive
cells
and
in
we
actually
define
a
bit
more
specifically.
How
we
do
that?
What
we
do
with
that.
You
pick
the
cell,
that
you
have
the
most
outgoing
packets
in
your
q4,
and
then
you
see
you
can
start
flushing
that
queue,
and
only
when
all
the
TX
cells
don't
have
any
transmit
any
packet
in
transmitted
queue,
then
you
can
start
considering
issuing
an
assault.
C
So
that
is
for
how
the
autonomous
cells
work.
Now
the
you
have
updated
the
behavior
of
the
nodes
at
boot.
So
the
way
it
looks
now
is
that,
after
the
next
thing
you
do
is
to
install
the
Unum
cells
that
just
straight
away
able
to
communicate
on
them.
So
you
can
install
your
own
Eric
slot
and
you
install
the
TX
slots
to
body
levels
and
then
you're.
C
For
for
the
registration
of
your
parents,
so
the
join
procedure
which
was
taking
place
before
on
the
dedicated
cells
of
MSF,
which
now
are
not
installed
at
this
stage.
Yet
it
will
be
installed
at
the
later
stage
and
if
there
is
more
traffic
needed
between
a
child
and
a
parent.
So
that
is
over
the
boot
sequence.
No
exact.
C
But
when
we
have
short
term
bursts
of
packets,
we
to
be
able
to
handle
them
as
well
without
having
to
install
new
slots,
because
if
he,
but
suddenly
I
get
ten
packets
to
send
to
a
given
neighbor
or
I,
don't
want
to
insert
more
slots
for
just
these.
So
instead
we
use
the
we
use,
something
that
actually
was
already.
Finally
15.4
2015
t
SCH,
which
is
that
use
the
the
one
of
the
header
a
bit
called
the
frame
painting
bit
to
signal
that
you
have
more
traffic
to
come.
C
So
whenever
you
start
sending
to
your
neighbor
or
you
said
that
beats
that,
and
that
means
there's
more
data
to
come
and
then
the
next
time
of
offset
and
the
same
frequency
not
channel
offset
but
frequency.
So
you
stick
to
the
same
physical
frequency,
then
at
the
next
time
the
times
thought
you
send
the
next
packet
and
you
can
as
long
as
you
keep
setting
that
bit
pending
that's
frame
pending
bit.
C
C
One
is
terminology:
the
the
cells,
the
unicast
cell,
that
have
maintained
by
MSF
between
child
and
parents.
They
are
called
dedicated
in
the
draft,
but
we
think
it's
not
the
best
word
for
that,
because
dedicated
means
nutshell
and
the
seller
shop.
So
we
want
to
change
that
who
installed
or
managed
we
want
to
define
here
are
the
list
of
packets
that
go
to
the
minimal
soul.
We
want
to
discuss
a
bit
more
about
the
length
of
social
0
which,
with
the
minimal
slot
frame,
end
frame
1,
which
is
this
not
frame
use
for
unicast.
C
We
want
to
separate
transmit
in
our
X
counter
so
that
when
we
manage
the
number
of
links
or
all
of
cells
that
we
need
between
Italian
parents,
we
can
manage
separately
the
arrives
in
the
TX.
We
can
adapt
the
to
the
load.
We
want
to
discuss
a
bit
more
6p
time
out
for
the
back
of
mechanism
that
we
have,
and
so
the
last
one
is
really
a
variable
name
change.
B
C
B
C
Yeah
yeah
and
that's
defined
in
15
in
I,
Triple,
E
15,
that's
already
like
this,
so
all
we
do
here
is
that
we
point
to
the
HIV
document
and
we
mandate.
It
say
we
need
to
use
that
mechanism,
but
we
don't
change
anything
to
the
return
mechanism.
So
to
summarize,
we
have
integrated
a
SF
into
MSF.
We
have
a
number
of
issues,
all
of
them
quite
minor-
that
will
be
fixed
in
the
next
version
and
wanted
to
discuss
a
possible
call
for
adoption.
F
F
B
B
Confirm
well
well,
will
confirm
the
call
on
the
list
and
check
that
nobody
opposed
we
can
have
a
short
period
just
to
validate
it
like.
Let's
give
us
give
people
a
week
or
something,
you
have
a
good
reason
why
it
should
not
be
adopted,
because,
if
no
expectation
that
anything
will
show
up,
we
don't
have
to
give
it
a
month.
So
that's
just
you
know
under
the
mailing
list
at
that
meeting.
To
do
for
us
confirm
the
call
for
adoption
and
give
people
a
week
and
next
week,
next
Wednesday.
B
B
F
B
B
A
Alright,
thank
you.
Can
you
confirm
you
hear
me?
Well,
yes,
okay,
great
yeah,
so
we
published
those
six
I
mean
it's
been
I.
Think
like
two
months
sometime
in
May
with
this
is
this
was
mainly
the
input
during
ITF
101
in
London,
and
then
the
two
reviews
that
we
received
on
the
mailing
list.
One
worse,
one
was
from
Java
villages,
Anna
and
the
other
one
was
from
Piscotty
over
at
the
in
London.
We
discussed
heavily
the
data
structures
in
their
extensibility,
and
this
is
the
main
change
that
we
implemented
it.
A
Lo
six
ever
since
we
worked
heavily
on
the
on
the
on
the
running
code,
we
have
an
open
source
implementation
in
open
WSM
of
the
constraint
joint
protocol,
which
is
how
we
call
the
the
secure
joint
protocol.
Now
during
the
sixties,
plug
test,
as
Thomas
mentioned,
that
was
held
in
Paris
end
of
June.
We
tested
this
with
an
implementation
from
one
SME
that
was
based
on
a
Kentucky
operating
system
and
we
successfully
achieved
the
interoperability
of
the
constraint
joint
protocol.
Working
group
last
call
was
on
for
a
couple
of
weeks
in
June.
A
If
I
remember
correctly-
and
there
was
a
lot
of
activity
about
the
draft,
we
received
seven
reviews
from
the
people
listed
here
and
one
of
these
reviews
I
was
completely
neglected.
It
was
from
Klaus
that
ended
up
in
my
in
my
spam
folder,
so
I
just
saw
it
today,
basically,
but
I
updated
this
little
slides
as
fast
as
I
could
with
with
these
changes.
A
So
the
goal
of
my
presentation
for
today
is
to
do
a
quick,
really
quick
summary
of
updates
for
us
since
all
five
and
then
to
spend
a
good
chunk
of
my
time
discussing
the
issues
that
have
been
opened
during
the
working
group
Lascaux.
You
know
yeah
thanks.
So
the
the
first
change
was
related
to
the
read
definition
of
Siebert
structures.
A
We
had
a
couple
of
drafts
published
mainly
the
Travis
Draft
on
global
time
that
want
to
extend
the
structures
that
we
use
in
minimal
security
and
the
previous
in
all
five,
what
we
were
quite
rigid
with
the
sibour
arrays
as
the
top-level
struct.
So
what
we
decided
to
do
is
to
switch
the
arrays
to
maps
maps
and
then
to
add
registries
in
the
draft
for
registering.
Basically
see
board
parameters
and
right
now
there
are
two
registries,
if
I
remember
correctly,
one
for
the
labels
of
the
top-level
parameters
that
end
up
in
this
configuration
object.
A
That
is
returned
as
the
drawing
response.
Payload
and
then
another
registry
is
actually
for
the
values
for
one
of
these
parameters
and
as
an
example.
Now
what
we
have
as
an
example
of
these
parameters,
we
have
like
the
link
layer
key
set.
We
have
the
short
address,
J,
RCS,
address,
etcetera,
etcetera.
A
In
order
to
decode
to
decode
the
element
or
the
parameter,
basically,
so
basically
what
you
will
typically
have
in
your
drawing
response,
you
will
have
an
array
of
these
sequences
and
based
on
the
type.
If
it's
an
unsigned
integer,
you
can
tell
that
this
is
key
index
that
should
be
signaled
in
the
15
for
auxiliary
security,
header
or
if
it's
a
byte
string.
You
know
that
this
is
the
key
value
and
then
we
have
defined
a
special
semantics
for
processing
these
parameters.
In
case
of
802,
the
15.4
you.
H
There
are
cue
minute
one
other
question:
I
have
because
you
have
only
key
index
here
and
in
15,
for
you
can
have
you
know
different
key
ID
modes
where
we
can
actually
have
a
this
key
next
means
that
you
have
a
global
key
is
256
at
Sakura
54
in
the
whole
network.
There
is
also
a
way
of
having
this
kind
of
keys
that
are
not
owned
by
the
controller
but
owned
by
somebody
else.
H
H
Those,
and
if
so,
do
we
actually
want
to,
you
know,
specify
how
they
are
transmitted
here
in
case
we
actually
some
at
some
point,
especially
if
you
think
about
we
don't
have
a
it's
a
coordinator,
and
you
know
the
a
or
C
are
separated,
it
might
actually
be.
You
know,
have
a
keys
that
are
actually
owned
by
the
you
know.
Jrc
is
different
and
that
you
might
have
actually
have
a
broadcast
keys
that
are
used
in
other
one
and
they
are
not
necessary,
coordinate
together
same
address,
pool
okay,.
A
H
Of
ASCII
sucks,
yes,
actually
Pulaski
sees
other
thing.
Yes,
but
I
mean
if
this
is
the
other
type
of
you
know,
because
I'm
missing
two
fives,
for
you
know
keys
you
have.
There
is
global
to
the
whole
network,
but
anyone
actually
have
you
know
this
kind
of
longer
identifiers
for
the
key
meaning
the
owner,
plus
the
key
index
at
the.
H
Are
something
that
they
use
played
around
but
I
understand?
This
is
also
for
rekeying
and
activities
for
most
likely,
the
same
structure
is
going
to
be
used
for
all
kind
of
keying.
So
that's
why
I
was
thinking
part.
Should
we
think
about
here
how
to
extend
this?
Even
if
we
say
now
that
we
always
use
key
index
and
the
critical
parties,
but
in
a
future,
especially
with
the
Seaboard
stuff,
to
make
sure
that
you
actually
you
know,
can
make
so
we
don't,
we
don't
end
up
Oh.
Suddenly
we
have
this.
H
A
No
I
mean
no
just
to
be
clear,
I
mean
this
is
something
that
I
already
considered
when
I
was
defining.
This
link
layer,
key
structure,
and
my
intention
was
at
first
to
mimic
the
data
structure
that
you
have
defined
in
802
2015,
for
in
order
to
allow
full
support
for
any
kind
of
king
that
is
enabled
in
15-4.
But
then
the
best
driver
had
was
huge
and
I
decided
that
for
the
link
layer
key
we
should
just
take
for
the
key
index.
A
Maybe
it
would
be
better
to
maybe
then
we
could
rename
it
to
be
more
appropriate
that
it
reflects
that.
This
kind
of
object
is
only
for
from
the
index
mode
and
we
could
define
other
objects,
other
structures
that
would
carry
the
parameters
needed
to
set
those
kind
of
keys.
If
there
is
interest
in
the
working
yeah.
H
Actually,
I
always
think
about
one
of
the
GU
that
actually
was
to
say
after
a
key
value,
because
that's
always
there
so
now
that
there's
one
in
butter
string.
But
after
that
you
could
have
a
key
owner
which
would
be
a
debate.
It
will
be
string
that
will
either
be
four
octet
or
eight
doctors
depending
if
it's
you
know,
Quixote
IDE
mode,
one
or
two.
They
want
that
if
they
are
missing,
you
are
using
tid
mod
0.
So
that
will
actually
be
great.
H
A
D
A
A
Let
me
let
me
get
back
to
you
on
that
I'm,
not
sure
if
we
want
to
do
that
right
now
for
minimum-security,
this
would
be
the
fully
blown
our
support
for
all
the
security
features,
since
this
is
the
kind
of
like
the
idea
of
this
is
minimal
and
with
the
changes
to
the
to
have
the
top
level
structure,
as
Maps
I
mean
this
can
easily
be
extended
in
another
RFC,
so
I'm
looking
here
mostly
for
the
input
from
others.
If
there
is
interested
in
supporting
other
key
modes,
then
index.
C
B
It's
not
actually
needed
for
this
work
anyway,
so
it
could
be
actually
trouble
if
you
define
something
that
you
don't
choose.
People
later
in
the
review
process
will
say:
hey.
Why
do
you
define
this?
People
may
use
it,
and
then
you
don't
need
it.
So
addressing
you
know
at
the
RSC
which
needs
it
extend
this
one
for
putting
it's
this
option
that
you
do.
A
But
let's
continue
that
under
male
can
I
have
the
next
slide,
yeah
thanks,
yeah,
so
ii
trained
major
change
was
that
we
homogenized
the
protocol
to
support
the
joining
of
the
six
lvr
or
the
coordinator,
and
basically
I
went
through
the
trouble
of
checking
in
the
document.
What
text
applies
equally
to
the
node
to
the
pledge
that
is
joining
as
a
non
6lb,
our
node
and
to
the
6lb
our
pledge-
and
there
are
quite
some-
there
are
some
changes.
A
A
Response
are
different,
of
course,
from
those
that
non
6lb
our
pledge
gets,
and
there
was
some
discussion
on
the
mailing
list
and
changes
were
not
heavy,
but
there
were
some
changes
and
special
in
the
terminology
part
where
I
had
to
differentiate
between
pledge
that
only
means
non
6ob,
our
pledge,
six
lbr,
etc.
Yeah.
F
F
A
Can
you
hear
me
yep
yeah
in
the
join
request?
Basically,
there
is
a
parameter
called
the
role
that,
if
it
is
not
that,
if
it's
not
present
means
not
sick,
so
we
are
just
regular
part
if
it
is
set,
it's
the
six
lbr
and
then
there
is
a
cent
and
just
saying
that
this
communication
happens
are
over
another
network
interface,
just
not
not
15.4,
but
it's
the
same
protocol,
it's
the
same
yeah
that
is
used
on
any
other
pledges
yeah.
So
you
see
the
join
request
here.
You
have
the
role.
A
If
the
role
is
not
present,
the
the
value
of
non
6lb
are
is
assumed,
meaning
just
regular
proj
joins
and
then,
if
600
on
its
at
it,
sets
it
to
one.
Thank
you
yeah,
okay
and
then
the
turn
major
change
is
on
wreaking
and
basically
we
added
here
a
mechanism
that
was
discussed
heavily
after
ITF
101
in
order
to
allow
the
jrc
to
update
any
of
the
parameters
during
network
lifestyle
and
with
this
mechanism,
basically
me
also
implement
wreaking.
A
Now
jrc
is
aware
of
the
ipv6
address
of
the
node
implicitly,
because
it
knows
the
network
prefix
and
the
network
short
address
and
the
extended
agora,
so
it
can
construct
it
and
it
is
able
to
reach
out
to
any
of
the
network
nodes
to
send
a
co-op
message.
So
now,
this
co-op
message
is
is
completely
a
different
conference.
It
from
the
one
that
was
using
in
terms
of
joining
when
pledge
was
joining
in
terms
that
it
does
not
contain
same
options,
and
it's
just
pure
co-op.
It's
confirmable.
A
There
are
less
security
issues
compared
to
those
were
joining
and
what
they
are
see.
Basically
does
it
just
sends
a
post
request
where
it
encapsulating
the
payload.
The
configuration
object,
configuration
c
bar
object
with
the
parameters
and
now
for
every
parameter.
There
is
semantics
on
how
it
should
be
handled
when
received
as
part
of
this
update,
parameter,
update,
request
message.
With
this
mechanism.
A
The
node
follows
when
it
receives
a
link
layer,
key
of,
for
example,
as
part
of
this
parameter
update
request
and
there
there
is
a
differentiation
between
regular
network
nodes
and
the
6lb
are
to
implement
drinking,
and
what
happens
is
that
basically,
6lb
R
will
install
the
new
key
immediately
once
it
drizzle
once
it
receives
it
and
starts
using
it.
All.
The
other
nodes
will
install
the
key,
but
they
will
wait
and
before
using
it
for
outgoing
traffic
until
they
see
encrypted
or
protected
frames.
A
The
passed
layer,
2
security
verifications
with
the
new
key
at
that
moment
when
they
see
traffic
encrypted
with
the
new
key,
they
just
switch
and
start
using
the
new
key
for
all
outgoing
traffic.
Now
there
was
a
comment
by
Tara
on
this
I'll
get
back
to
that
later,
and
the
same
mechanism
here
is
used
what
the
short
addresses
or
basically
any
other
parameter.
A
A
This
was
the
first
attempt,
but
then,
since
the
drawing
request
was
opposed,
we
cannot
observe
a
post
and
that's
where
fetch
came
in,
but
then
there
were
problems
in
observing
from
an
endpoint
that
has
a
different
ipv6
address,
because
pledge
used
a
link
local
ipv6
address
for
joining.
That
goes
over
proxy
when
it
becomes
a
network
node.
It
just
goes
straight
to
the
jrc.
So
then
there
were
difficulties
in
the
co-op
in
being
compliant
with
co-op
and
doing
this.
A
So
finally,
what
we
resorted
that
the
pledge
exposes
/je
once
it
joins,
and
then
jrc
does
a
post,
a
simple
post
on
this
resource.
Thank
you,
yeah
and
then
the
for
change
is
just
editorial.
I
mean
we
aligned.
There
are
many
editorial
edits
and
clarifications.
We
align
the
key
derivative
derivation
with
oscar
13
registries,
etcetera,
etcetera,
and
then
we
rebranded
the
drawing
protocol
as
constraint
or
and
protocol
with
abbreviation
kojic
yeah.
So
with
that,
I
will
switch
to
the
working
group
last
comments.
I,
don't
know
how
much
time
I
have
both
call
plan.
B
A
A
A
But
the
semantics.
This
is
a
new
prop
option
that
we
define
in
minimal
security
and
it's
processing
is
quite
similar
to
the
co-op's
token
coop
token
from
the
base
RFC
72-52.
But
the
problem
is
that
the
value
that
we
need
to
put
in
the
option
does
not
fit
eight-byte
toh
coop
token,
that
is
defined
by
72
52.
A
So
then,
there
were
two
questions:
one
raised
by
your
on
cylinder
about
whether
we
can
use
the
token
is
the
end
of
this
new
or
instead
of
stateless
proxy,
which
is
possible
in
some
cases,
but
not
in
all
and
then.
The
second
comment
comment
was
from
Klaus
who
raised
a
point
about
duplicating
features
in
coop
with
this
option,
since
we
are
defining
a
new
co-op
option
that
can
be
used
for
the
general
purpose.
A
A
We
are
working
together
with
core
with
core
experts
on
this
issue,
and
we
had
a
meeting
this
afternoon
on
trying
to
find
the
best
way
to
proceed,
and
the
attempt
here
is
to
find
something
that
is
both
that
works
both
for
general
purpose
squad
and
for
our
use
case
in
succession
in
minimal
security,
so
I
mean
I
will
keep
the
working
group
posted
will
here.
We
have
some
side
meetings
on
this
and
also
I.
Will
present
the
our
views
case
during
the
core
may
team
tomorrow
evening
tomorrow
evening
yeah?
A
So
the
second
issue
is
was
raised
by
Tara
on
the
decision
on
the
decision
that
is
important
for
the
drapy.
So
let
me
sum
this
up.
Jp
needs
to
accept
frames
that
are
not
secured
at
link
layer
for
the
duration
of
the
joint
process,
but
now
the
duration
of
the
drawing
process
is
vague,
and
we
had
a
couple
of
discussions
on
this.
How
do
we
pass
the
information
that
the
Jaypee
should
enable
the
drawing
process
and
that
it
should
accept
unprotected
layer,
two
frames?
A
This
was
discussed
heavily
during
the
ITF
99
in
Prague,
where
we
explore
different
options.
One
of
them
was
just
to
abuse
the
drawing
metric
that
is
present
in
DBS
and
basically
to
use
one
value
of
the
drawn
metric
to
signal
that
drawing
is
not
allowed
and
when,
for
example,
a
drawing
proxy
would
see
this
zero
zero
hex
FF,
for
example,
in
the
enhanced
beacon
of
its
preferred,
the
ripple
parent.
It
would
not
accept
any
any
unprotected
layer,
two
frames
and
therefore
not
accept
any
new
pledges
into
the
network.
A
So
this
hasn't
been
adopted
yet
I
think
michael
has
a
presentation
afterwards
or
whoever
is
filling
in
for
Michael,
and
this
is
one
part
that
we
are
currently
missing,
as
as
Tara
said
so,
I
proposed
here
three
options
that
we
how
we
can
proceed.
We
can
keep
working
on
this
as
part
of
Michael's
draft.
A
Physical
button
press
would
switch
this
the
drawing
process
so
on
first
on
the
coordinator,
and
then
this
information
will
propagate
down
the
mesh
towards
holdin
all
the
Dre
piece
and
the
plan.
New
pledges
would
the
frames
of
new
pledges
that
are
not
protected
at
layer.
Two
would
be
accepted,
and
then
the
third
of
would
be
to
do
this
at
the
Qadri
player
in
coop,
to
define,
for
example,
a
quadric
parameter
that
would
be
sent
as
the
parameter
update
in
the
parameter
update,
request
message.
H
H
You
know
thing
was
more
or
less
how
the
Jaypee
knows.
If
there
is,
you
know
one
of
these
peers.
Actually
you
know
when
it
starts
doing.
You
know
this
turning
process.
The
joining
node
connects
the
IP
and
then
it
starts
something
and
I
was
assuming
that
the
chip
is
usually
they
stores.
Even
if
you
say
it's
completely
slightest,
you
can
actually
I
didn't
really
understand
if
you
can
actually
make
it
completely
status,
and
so
next
we
are
assuming
that
it
has
some
kind
of
state
and
it
needs.
H
In
fact,
we
were
talking
in
the
secured
neighbor
cars
and
so
on.
It
needs
to
know
when
it
can
actually
remove
that
state
when
it
needs
to
stop
allowing
that
node
to
be
sending
it
unencrypted,
payloads
and
and
at
that,
because
that
congressional
spare
node
he
doesn't
need
to
know
if
the
whole
network
is,
you
know
all
that
proquest
might
still
be.
Are
you
know
access
allowing
you
know
joins,
but
he
doesn't
want
to.
You
know
that
one
node
to
do
that
anymore,
because
it's
already
done
because
he
just
doesn't
want
to
keep
keep
opening.
H
You
know
Tipton.
You
know
whole
open
for
somebody
to
attack
him
by
sending
you
know
faking
to
be.
They
know
that
joints
couple
of
minutes
earlier
and
send
in
clear
text
packets.
So
that's
what
I
was
thinking,
but
you
know,
of
course,
now
it's
very
easy.
You
know
said
one
frame
and
one
frame
comes
back,
but
in
the
future
it
might
be
something
that
we
actually
have
a
multiple
round.
Trips
going
bad
and
I
I
think
it's
actually
bad
idea
to
have
a
JP.
You
know
not
knowing
whether
it's
usually
is
easier.
H
If
they,
if
a
JP
knows
when,
when
the
process
is
finished
and
also
he
needs
to
know
if
it
was
successfully
done,
it
failed
because
if
it
failed,
he
probably
went
to
blacklist
aha
node
with
what
happens
there.
If
you
have
a
wrong
key
or
something
like
that
in
the
chaining
node
he
joins,
tries
to
joins
Costa
jrc
Jersey
says
wrong.
Key
which
goes
back.
He
gets
from
key
okay,
I
will
break
for
ten
seconds
and
try
again
and
then
the
Senate
tries
again
consuming
resources
and
editing
is
done.
H
He
said
oh
I
write
there
for
30
seconds,
come
back
again
and
then
he's
doing
that
for
a
couple
of
months
until
somebody
actually
no,
they
said.
Oh,
we
have
this
node
there
that
is
actually
been
trying
to
join
because
we
didn't
actually
configure
it
in
the
TRC
ever.
So
that's
why
I
was
thinking
about
okay,
the
Tony
JP
might
actually
want
to
blacklist
that
node
and
set
up
a
que.
Yes,
even
if
you
try
to
join
to
me,
I'm
not
answering
to
you
because
go
away,
do
something
else.
H
B
H
If
he
ever
extra,
for
example,
make
it
so
that
okay
be
back,
have
a
the
joining
process
might
be
actually
do
step
process
you
first
identic
out
indicates
something
and
then
you
TRC
says
okay
here
so
first
off,
then
you
do
the
second
step
on
subtract
that,
like
next
pin
card
type
of
thing
out
and
the
guy
said,
if
JC
puts
in
the
first
after
the
first,
you
know.
Okay,
this
is
the
first
exchanged
on
okay
he's
trying
again
I
will
blacklist
him.
H
We
can't
actually
do
this
kind
of
extensive
since,
but
but
do
you
need
anything
in
the
spec
to
do
that
or
usually
use,
but
what
I
was
thinking,
but
it
would
be
useful
to
have
in
the
response
coming
back
from
the
GRC
to
have
something
for
the
Jaypee
to
say
that?
Okay,
yes,
this
process
is
now
done.
When
you
have
reverted
this
process,
this
packet
to
the
you
know,
do
the
turning
node
and
it
was
done
successfully
or
no.
It
was
veiled
or
Canaries.
A
A
Typically,
if
you
have
a
50
node
Network
50
nodes
can
play
the
role
of
the
JP,
and
now
you
are
saying
that
each
of
these
50
nodes
will
be
doing
an
authorization
decisions
who
should
we
do
should
be
joining
and
who
should
be
blacklisted
to
me,
this
is
a
centralized
decision
for
the
GRC
and
if
it's
a
centralized
decision,
it
should
be
the
GRC
who
decide
okay,
I'm
getting
too
many
packets
from
this
pledge.
This
means
something
is
wrong.
A
H
The
I
agree
that
it
could
be
done
without,
but
I
have
noticed
it
in
some
places.
It
actually
is
easier
if
you
actually
know
what,
even
if
the
it
just
proxying
things,
for
example
in
in
my
question
two
we
have
it
we
approximately
exchange
and
one
of
the
things
we
actually
need
to
do.
We
need
to
know
when
the
process
is
either
successful
or
failed,
so
we
can
actually
know
okay
for
successful.
H
Now
we
need
to
do
some
other
automatic
tricks
there
behind
the
scenes
to
be
able
to
do
some
other
things
and
that
kind
of
thing
see,
even
if
you're
just
proctoring,
you
no
doubt
integration
information.
True,
we
still
might
need
to
have
a
you
know,
but
it's
useful
useful
to
have
a
clue
of
what's
going
on
there,
how
many
but
I,
don't
see
how
it's
really
and
I
think
it
might
be
different
here,
but
so
where
I
was
just
thinking
about
this?
A
The
moment
I
don't
see
because
I
mean
when
the
pledge
drawings
I
mean
it
may
never
ever
communicate
with
this
JP
again
I
mean
this
is
the
key
point.
I
mean
this
was
one
node
that
was
selected
based
on
the
information
in
has
beacons
from
the
moment
the
pledge
joins.
It
can
decrypt
di
it
selects
a
triple
parent.
According
to
the
ripple
specs,
it
may
never
again
communicate
to
the
Jaypee
and
2jp.
That
is
just
I
mean
I,
don't
see
what
should
the?
Why
should
this
all
be
relevant,
but
I
mean
we
got?
A
F
So
I
think
I
think
it's
a
twist
on
what
they're
always
talking
about
this.
It's
essentially
the
same
thing
right.
It
is
switching
on
and
off
the
capability
to
two
to
four
notes
to
join
at
the
Jaypee
level,
whether
it's
a
decision
made
by
the
chair,
C
or
not.
My
question
is:
is
this
mechanism
or
this
policy
I
mean
if
I
wanted
to
implement
this
kind
of
behavior
I
have
all
the
tools
at
my
disposal
to
do
this
in
an
implementation
you
do
not
yet.
A
Know
at
the
moment,
no
at
the
moment
no
I
mean,
if
so,
I
mean
you
have
the
drawing
metric.
You
would
have
to
abuse
what
one
value
of
the
drawing
method
for
this,
and
what
this
is.
One
resolution
that
I
was
proposing
earlier
is
basically
to
say:
zero
hex
FF
in
the
B
in
hands,
because
what
the
draw
metric
means
I,
don't
accept
any
plunges.
B
Is
very
thin,
I
mean
something
we
could
progress
quite
rapidly,
because
most
of
the
work
which
relates
to
Michael's
draft
is
actually
the
work
at
all.
But
here
we
just
need
to
present
the
interface
in
the
beacon
to
say
basically
signal
we
want
to
join
or
not
join
preference.
That's
it
I
mean
we
can
and
then
we
can.
We
can
publish
that
document
very
quickly,
so
we
don't
delay
minimal.
The
point
many
shine
is
that
option
one
and
option
three
are
not
equivalent.
I
know.
A
B
Can
hunt,
for
instance
and
steal
in
the
future
create
a
improvement
on
addition
to
minimal
and
that
that's
three,
because
it's
it's
really
a
something
that
you
can
always
define
later.
We
can
move
minimal
the
way
it
is
today
without
that
and
always
define
it
later.
It's
kind
of
a
global
toggle.
My
network
is
stable,
I
don't
want
to
enjoy,
and
that's
that's
a
global
decision
by
by
lesser
entity.
An
Almond
beacon
is
more
like
this
network
is
more
loaded
than
this
one.
B
So
in
terms
of
balancing
you'd
better
join
here,
and
actually
this
proxy
is
doing
a
number
of
rows
already.
It
can
hardly
take
more.
This
one
is
as
more
resources
just
use
the
other
modest
join,
but
it's
what
it's
worth
you're
alone
and
not
in
an
speak
and
dance,
so
it
has
to
do
with
with
particular
notion
of
critical
node,
not
policy
or
new
strategic
decision
of
taking
or
not
taking
new
joint.
Yes,.
B
A
F
This
is
this
is,
it
seems
to
me
like
this
is
another
feature
and
other
capability
it
does
not.
It's
not
like.
The
draft
is
broken.
It's
that
this
could
enhance
the
draft
in
some
way,
so
I
would
I
would
I
would
say
this
could
be
a
different
document
that
I
wouldn't
want
to
to
stop
the
progress
of
minim
or
stop
the
we're
in
workgroup
last
call
right.
F
So
so,
if
we
decide
to
work
on
this,
we
have
to
go
back
to
the
working
group
and
go
and
not
a
workgroup,
a
school,
whereas
I
think
we're
there.
Yet
we
can.
We
can
push
this
and
then
have.
If
this
seems
interesting,
we
can
have
an
extension
and
and
everything
that
you're
describing
are
all
extensions.
It
doesn't.
D
B
Beacon
can
describe
that
piece
by
itself
for
what
it
does
and
as
part
of
the
the
option
three
option.
Three
is
part
of
your
management
manageability.
So
if
you
want
to
do
anything
in
this
draft
about
option,
three
anything
you
can
do
is
have
a
manageability
section.
Well,
you
say
which
kind
of
objects
in
minimum
can
be
managed
from
the
outside
and
just
say:
okay,
there
is
this
this
bit,
which
means
enough
that
can
be
managed
from
the
outside
and
and
the
protocol
to
manage.
B
I
A
There's
no
way
I
can
I
can
get
it
yeah,
so
yeah
this
is
the.
So
let
me
just
think
I
think
this
is
yeah.
This
is
the
the
point
raised
by
Tara
about
layer
to
state.
So
let
me
just
sum
it
up
briefly
sum
it
up.
Basically,
Tara
raises
a
point
that,
with
a
compliant
802
15
for
security,
implementation,
JP
needs
to
keep
some
state
I
responded
to
this
email.
Just
today,
I
don't
know.
A
If
Tara
we
had
time
to
see
it
I
think
there
is
a
mechanism
that
this
could
be
implemented
fully
compliant
with
15.4,
the
one
that
I
sent
in
the
email
today,
but
I
also
like
to
note
that
there
are
many
existing
implementations
where
this
performance
hit.
The
truth
describe
where
simply
can
be
can
be
bypassed,
because
it
is
possible
to
add
something
in
the
Mac
layer
where
you
could
signal
where
you
could
pass
this
frame
upwards,
even
though
it's
not
super
compliant
with
15
for
APS.
A
A
Yes,
so
another
issue,
but
error
I
think
we
agree
on
this.
He
just
proposes
to
add
a
simple
delay
or
configurable
delay
when
a
node
in
the
network
receives
the
new
key
before
removing
the
old
key
in
order
to
account
for
possible
losses
and
that
some
nodes
might
receive
the
key
before
others,
so
yeah
I
think
we
agree
on
this.
I
mean
we
can
implement
this
in
the
next
version.
5,
yes,
Travie
raised
the
point
about
the
error
handling
it
to
the
code
level.
A
Basically,
this
is
the
semantical
handling
of
the
errors
of
the
parameters
passed
as
part
of
project
I
mostly
agree,
I
agree.
Definitely
with
this
we
focus
so
far
on
the
errors
on
the
Oscar
level,
when
we
try
to
protect
from
from
denial
of
service
and
there
we
had
a
couple
of
exchanges
and
the
main
conclusion
of
that
part
was
basically,
we
don't
send
any
errors
that
are
related
to
us
core
processing
because
they
can
be.
They
can
just
open
the
denial
service
vectors
the
yes
handling.
A
Yes,
so
the
Travie
raised
the
point
about
how
should
the
jrc
handle
if
the
node
in
the
network
cannot
be
reached,
for
example,
if
he
tries
to
rekey
it,
we
agreed
on
the
mailing
list
that
this
is
an
implementation,
this
decision,
but
that
we
should
explicit
it.
So
the
implementers
are
aware
of
it
next
next,
please,
yes,
so
this
issue
was
raised
by
Jim
shot.
This
is
an
important
one
about
non
3
use,
basically
the
right
now
in
the
draft.
A
We
have
we
mandate
that
all
your
score
security
parameters
are
written
to
persistent
memory,
both
at
JRC
and
at
the
pledge,
and
this
is
an
important
security
required
now.
What
the
Jim
raises
is
that
if
jrc,
for
some
reason
dies
and
all
of
this
information
is
lost,
what
happens
jrc
dies,
six
cell
addresses
in
the
cloud
it
dies?
6O
BR
continues
to
operate,
so
the
network
is
operational.
Now
the
same
company
brings
a
new
DRC.
A
How
do
how
does
it
continue?
It
doesn't
know
the
state,
the
security
state
with
the
nodes
and
if
it
tries
to
use
the
keys
that
it
has
from
some
database,
it
will
reuse
the
partial
IV
and
therefore
non
non
three
use
will
occur
and
the
confidentiality
on
20
city,
basically,
all
security-
will
be
lost
for
those
dreams.
So
now
the
the
question
for
the
grouping
for
the
group
is:
how
do
we
handle
this?
We
can.
There
are
a
couple
of
cases
here
and
I.
A
A
I
A
This
was
this
issue
was
raised
by
thank
Faye,
basically
with
the
updates,
where
the
quadruped
supports
the
joining
of
the
6lb.
Are
we
enabled
the
6lb
are
to
be
bootstrap
and
we
were
missing
a
couple
of
parameters
that
are
needed
by
the
network
and
that
the
GRC
can
configure
into
the
network,
such
as
the
time
flow,
template
channel
hopping,
template,
etc,
etc,
and
with
this
we
I
think
we
have
all
the
parameters
needed
to
have
a
fully
autonomous.
They
are
seen
the
cloud
and
managing
multiple
multiple
networks
and
updating
the
keys,
etcetera,
etcetera.
F
This
is
the
beginning
of
an
infinite
list
of
feature
requests
for
adding
this
and
that
parameter.
My
personal
opinion
is
that
you
know
let's,
let's,
let's
have
something
minimal
working.
If
this
is,
you
know
really
a
an
issue,
then
somebody
can
write
a
different
draft.
What
what
this
is,
what
this
is
talking
about
is
I
have
a
six.
It's
a
very,
very
specific
use
case.
F
Right,
I
have
a
6
lb
are
that
joins
somehow
a
GRC
and
the
Gerasenes
to
configure
the
6
lb
are
and
configuration
can
be
all
the
way
to
like
what
was
the
color
on
the
box.
You
know
there's
so
many
things
that
are
can
be
configured
if
we
start
creating
a
list
and
maintaining
I
Ana
register
it.
You
know
it
will
never
stop.
F
B
Have
a
long
history
of
overloading
triple
a
mechanism
with
with
configuration
and
using
them
or
misusing
them
as
configuration
tools,
let's
build
a
young
model
about
six
AVR
and
let's
use
Akamai
or
something
to
to
configure
the
6
ampere.
What
we
learn
from
the
join
process
is
the
6
lvl
to
be
identified
as
a
6
lb
our
and
to
be
able
securely
connect
once
we
do
that,
then
we
can
use
a
yarn
that
we
can
always
extend
to
go
and
configure
these
things
and
all
the
rest.
A
Alright,
oh
I,
guess
then
there
was
an
extensive
review
by
William
on
the
bitbucket
page
I
responded,
I
mean
we
have
a
couple
of
Tamizh
ations
that
we
can
do.
I
mean
this
is
not
major
I
mean
I
will
discuss
this
with
Oscar
otters.
If
some
of
these
can
can
happen,
second,
optimization,
ok
can
I
just
go
back,
I
mean
one
second
yeah
was
regarding
the
short
addressed
least
I'm.
Currently
this
list
time
is
encoded
in
seconds
from
the
instant
the
quadric
message
was
received
at
basically
at
the
pledge.
F
A
A
A
A
Yeah,
the
final
one,
but
this
goes
along
the
adding
features
this
is
William
who
requested?
If,
if
there
is
interest
in
the
group
to
support
fragmentation
by
by
quarter
block
wise
and
we
for
now,
we
implicitly
assume
the
fragmentation
being
done
at
the
612,
a
layer
when
it
occurs
in
the
default
cases.
We
ensure
that
the
presentation
does
not
happen,
but
when
it
occurs
with
fully
blown
object,
we
we
assumed
the
six
open
layer.
Now
he
was
asking
about
using
block
wise,
and
this
would
indeed
enable
the
protocol
to
be
with
the
non
IP
networks.
B
B
So
Michael
cannot
be
with
us.
I
built
a
number
of
slides
on
his
behalf,
and
since
we
gave
the
time
too
many
sure
I
will
skim
them
through
them
very
very
already.
So
the
biggest
news
for
the
zero
touch
is
that
anumana
is,
is
well
advanced,
Russkies
gone
through
welcome
Ascot
and
the
constrain
culture
on
which
we
depend
for
this
work
as
in
adopt
yet
and
Michael's
hope
is
that
it
will
work
up
my
score
this
year.
B
B
Here
is
how
you're
going
to
do
the
same
thing
with
us.
There
is
how
you
will
format
this
here's
the
protocol
that
will
match
the
sort
of
protocol,
etc.
Everything
everything
is
much
one-to-one.
That's
pretty
much
what
this
document
does.
It
does
not
really
range
on
the
world
3
maps,
the
methods
to
our
world,
and
basically
you
will
find
this
explanation
of
the
different
pieces
of
protocol
which
are
done
by
which
work,
which
document
the
Messiah
is
where
the
vendor,
with
its.
B
What
were
the
original
authentication
lines
and
small
argent
for
us
is
the
work
on
a
nun
speakin.
So
we
just
said:
we've
got
this
dependency
on
minimum
security
so
that
we
can
actually
expose
join
preference
and
extended
notion
of
joint
preference
on
the
beacons,
so
that,
when
you
get
this
note
coming
in
and
trying
to
find
a
trend
proxy,
it
will
hopefully
find
the
right
network
in
the
middle
of
physical
networks
and
then
inside
that
right
network.
B
It
would
find
a
proxy
which
is
not
too
busy
which
hopefully
is
not
too
far
from
the
route
etc.
So
it
will
figure
out
which
is
the
best
possible
gentry
occifer
it.
It's
not
meant
as
a
administrative
method
for
preventing
joints,
but
it
could
be
used
that
way
by
just
having
a
virgin
proxy,
not
announce
themselves
or
announce
that
they
are
free
visit.
B
B
Can
go
through
slides
will
not
have
time
now
so
you're
interested,
please
go
through
site,
Debbie
else,
so
for
six
dish.
What
the
only
thing
we
have
to
do
is
really
expose
this
little
agree
on
the
field,
but
there
is
no
rocket
science
in
there
agree
on
the
field
put
that
in
the
beaker
and
set.
So
it's
really
something
that
we
can.
We
can
do
there
rapidly,
the
point
being
that
we
will
have
a
normative
reference
on
it
in
minimal,
so
that
tree
means
that
minimum
will
not
get
the
RFC
number
and
yeah.
B
This
thing
gets
its
RFC
number,
so
the
four
except
to
depend
on
it
based
on
militias
proposal
earlier,
then
we
need
to
progress
them
thing
and
go
through
with
it.
It
was
called
for
adoption
mid-june,
so
the
call
is
passed
I've
not
seen
anybody
objecting,
so
the
indeed
try
stuff
progressing.
The
document
is
adopted,
and
that
comes
from
that
on
the
list
and
so
we'll
ask
Michael
to
publish
a
zero-zero
blah
blah
blah.
As
usual
question
discussion,.
E
G
E
E
It's
dependent,
I
guess
because
we're
discussing
the
previous
meeting
that
we,
if
we
want
to
use
these
through
the
the
constraint
joint
protocol,
we
need
that
that
the
GRC
is
also
the
global
time
manager
or
the
global
time.
No
note
in
the
network
that
is
able
to
do
this
mapping
between
ASN
and
global
time,
and
if
we
want
this
to
work
from
the
beginning
when
the
node
joins,
then
it
has
this
dependency
that
you
have
to
transport
these
options
as
part
of
the
constraint
joint
protocol.
E
So
so
I
I
did
I,
followed
the
comments
on
the
mailing
list
and
I
remove
some
of
the
options
we
had
mainly
because
they
had
security
issues.
Basically,
we
were
enabling
to
have
this
global
time
service
as
an
external
thing
out
of
the
GRC
and
indicating
what
is
the
address
and
the
service
that
is
exposed,
but
this
had
other
security
problems
like
red
erection,
or
you
know
the
the
the
note
is
not
authenticated
by
the
by
by
this
new
service,
so
that
would
require
some
new
keys
and
I
remove
that
part.
E
E
So
the
main
issue
is
that
now
the
interaction
has
changed
before
when
I,
when
a
node
had
this
global
time
option
installed.
It
was
subtle
this
time
and
it
was
asking
to
the
GRC
to
get
an
update
when
the
least
time
expires,
but
now
the
interaction
model
through
the
parameter
updates
that
malicious
expose
are
in
the
other
way.
So
my
my
guess
is
that
I
need
to
switch
that
now
and
make
that
GRC
updates
the
the
global
time
to
the
to
the
node
when
the
lease
expires.
E
So
that's
one
of
the
things
I
need
to
do
in
the
next
version,
but
another
more
critical
thing
that
I
want
to
discuss
not
today,
but
in
the
following.
Sixty
meetings
is
how
we
ensure
that
the
GRC
can
know
the
mapping
between
the
ASN
and
the
global
time
and
I
can
understand
that
the
GRC
can
have
this
global
time
through
ntp
or
through
any
external
protocol.
B
B
H
Can
you
hear
me
well
perfect,
okay?
Well,
this
says
this
is
a
draft
about
all
the
considerations.
Federal
implementers
will
have
to
take
into
account
when
considering
implementing
Cistus
were
more
than
one
physical
layer
so
well.
This
is
the
content
of
a
draft.
So
this
is
the
considerations
they
cover
pretty
much.
All
the
all
the
Cystic
protocol
stack
next,
please
so
what
cysts?
C
H
With
different
characteristics
and
different
of
abilities
such
as
well
and
with
whatever
that
arise,
from
6.95
skills
per
second
up
to
800
liters
per
second
and
a
frame
length
of
2
3,
7
bytes,
also
there
are
new
relatives
such
as
well
autumn,
would
be
from
open
mode
that
they
can
be
went
both
15
452,
4G
and
forcibly
person
to
predict
Hertz.
So
this
makes
possible
to
have
assisted
network
where
nodes
will
have
can
have
multiple
physical
layers
at
the
same
time,
and
so
links
can
happen
in
dual
bands
and
can
happen
over
different
physical
layers.
H
So
one
of
the
first
considerations
to
take
into
account
will
be
the
definition
of
neighbors.
So
here,
for
example,
we
see
that
no
stabian
see
when
using
physical
layer
a
node
a
is
enabled
to
be
be
neighbors,
a
and
c
and
c
only
neighbor,
speed.
Next,
please
and
then
consider
another
physical
layer.
They
might
implement
everybody
neighbors
everybody.
So
then
next,
please,
then
now
what
happened
when
and
when
this
knows
can
implement
in
the
same
network
more
than
one
physical
layer.
H
So
the
the
definition
of
neighbors
changes
to
any
node
which
is
within
the
same
interference
domain,
but
for
a
given
person
for
the
precise
physical
layer.
So
this
changes
how
neighbors
store
their
or
manage
the
nodes,
March
their
neighbors
information
so
going
to
the
max
Bleyer.
The
considerations
is
at
the
moment
of
the
network
formation,
for
example,
knows
that
in
the
coding
6
applications
they
have
to
listen
for
V's
so
well.
H
We
know
that
nose
will
listen
in
a
round
robin
fashion
for
wannabe
over
one
of
the
16
frequencies,
but
now
this
this
list,
or
this
amount
of
frequencies
no
scan
and
listen
to
we'll
multiply,
will
expand
if
we
include
multiple
physical
layers
and
with
multiple
frequencies.
No,
so
this
may
be
very
heavily
in
terms
of
energy,
so
here
future
implementers
they'll
have
to
come
up
with
a
mechanism
to
ink
well
to
to
improve
the
joining
process
and
and
yeah
and
to
shorten
this
time.
B
H
No,
so
we
would
decrease
the
amount
of
well-
let's
say
the
efficiency
of
the
network,
so
also
since
we
have
what
which,
since
we
have
different
physical
layers,
having
different
characteristics,
also
for
the
channel
hopping
sequences
they
can,
they
cannot
have
it.
We
cannot
identify
them
just
by
a
numbers
because
for
different
physical
layers
might
my
diff
might
mean
the
different
things.
H
Also
for
record
for
resource
allocation
in
the
six
tops
layer
is
that
resources
are
measured
in
the
amount
of
cells,
but
when
having
multiple
physical
layers,
cells
don't
mean
only
cells,
don't
mean
anything
because
for
a
specific
time
is
lock
duration
for
a
low
data
rate.
Can
you
can
pass
less
information
that
when
having
a
high
laterites?
Also
here,
we
think
in
the
six
tops
layer.
H
We
miss
a
kind
of
mechanism
hard
to
cope
with
a
regulatory
norms
or
legislation,
because
if
we
use
sub
digger
frequency
bands,
these
are
very
highly
regulated,
so
there
must
be
a
mechanism
that
takes
into
account
this
this
regulation.
Next,
please
well.
This
is
my
last
slide
and
also
for
6lowpan
considerations
now
that,
since
it
was
defined
with
a
15-4
to
be
skin,
mind
now
with
having
multiple
physical
layers
and
capable
of
sending
more
than
hundred
sm
bytes
per
frame,
so
6lowpan
should
adapt
to
send
more
bytes
per
per
frame.
H
Know
when
doing
the
fragmentation
and
also
pile
to
end
this
presentation
about
the
ripple
considerations
is
here:
we
foreseen
that
you,
audit
function
should
be,
should
be
written
or
taking
into
account
their
resource
occupancy
or
the
true
booth
and
energy
consumption
of
of
the
multiple
physical
layers.
There.
H
B
G
What
happened
is
that
I
were
struggling
to
understand
the
retransmission
algorithm,
defining
the
15.4
standards,
so
I
asked
for
help
on
the
merriest,
and
then
these
slides
captures
my
current
understandings.
So
if
you
are
interested
in
the
algorithm
itself
or
when
you
are
implementing
this
algorithm,
please
take
a
look
at
this
slide,
which
could
be
helpful
so
and
also
the
the
Terrell
told
me
that
now
the
ITP
15.4
MD.
G
H
H
F
Tara
I
have
a
question
for
you:
actually
the
what
is
the
right
way
for
so
so
yeah
ound,
some
things
that
are
not
very
clear
and
and
try
to
clarify
them
is
there?
Are
you
the
right
person
to
convey
those
messages?
Is
there
an
inbox
where
you
can
drop
these
things,
or
what
do
you
recommend
as
a
as
feedback
or
or
will
you
start,
as
liaison
so.
H
There
is,
there
should
have
been
a
formal
lioness
and
there
some
requests
coming
to
IETF
saying
that.
Okay,
this
is
the
current
version
of
the
craft
which
we
are
going
to
be
editing.
Do
you
have
any
comments?
It
probably
has
been
disappeared
somewhere
in
the
IETF.
You
know
no
administrative
or
such
like
that.
So
I
don't
actually
know
what
would
be
the
formal
process
of
doing,
but
I
will
be
in
Thai
Tripoli
meetings.
I
will
be
actually
being
low-income
and
I
can
put
in
the
comments.
H
If
you
have
any
comments
that
you
found
out
there,
if
they
send
it
to
me,
I
can
put
them
in
as
a
comments
for
myself
and
table
bit
and
acted
on,
and
then
there
is,
if
there
is,
you
know
there
is
a
the
Tripoli
has
a
mailing
list
that
you
I
think
you
can
actually
show
in
that,
but
it
doesn't.
But
most
of
their
meeting
most
of
the
stuff
happens
in
them
axle
meetings
and
because
the
meetings
don't
have
they
don't
allow
any
kind
of
remote
participation.
C
B
Well,
if
so
perfectly
in
time,
we
will
conclude
this
meeting
and
use
our
business
well.
Thank
you
all
and
we'll
announce
the
next
series
of
interim.
We
recently
we
didn't
do
so
many,
so
we
will
workout
probably
would
want
one
interim
and
minimal
and
we
had
several
drafts,
which
was
not
really
discussed
yet
we'll
probably
announce
an
interim.
We
have
to
announce
them
seven
weeks
in
advance,
so
you,
you
probably
won't
see
them
before
September
I,
like.
