►
From YouTube: IETF102-SECDISPATCH-20180716-1550
Description
SECDISPATCH meeting session at IETF102
2018/07/16 1550
https://datatracker.ietf.org/meeting/102/proceedings/
A
B
It's
Monday,
so
it's
a
little
early.
So
here's
the
note
well
so
please
make
it
make
note
of
the
note.
Well,
there's
quite
a
few
BCP
he's
kind
of
in
place
there
as
you
look
at
that
very
quickly.
If
you
have
any
questions,
don't
hesitate
to
ask
us
or
the
AG
in
the
room
admitted
administrative
Lee,
we're
gonna
pass
out
blue
sheets
thanks,
Richard
salts
or
being
our
jabber
scribe
with
anyone
volunteer
to
be
a
note-taker
for
us.
A
B
Just
just
to
remind
everyone
about
our
our
ground
rules
here
in
the
dispatch
process,
we
recommend
what
the
next
steps
are
for
drafts.
We
do
not
adopt
draft
it's
as
we
have
the
conversations
individual
presenters
are
going
to
come
up
to
talk
about
their
work.
Remember
kind
of
outcomes,
we're
looking
to
decide
at
the
back
end
or
is
this
work
you
just
heard?
Is
this
best
fit
into
some
existing
working
group?
Maybe
a
couple
working
groups:
let's
have
that
conversation?
Should
this
be
new
work,
so
that
means
Bob.
B
Do
we
recommend
ad
sponsorship
if
they're
willing
to
take
it
or
in
the
negative?
Should
the
the
ietf
not
take
this
work
so
at
the
end
of
each
of
the
presentations
were
exploring
that
it's
the
solution?
Space
and
repeat,
we
do
not
adapt
adopt
drafts
here,
so
we
had
a
really
full
agenda
here.
Each
of
the
dispatch
items
is
going
to
be
about
10
to
15
minutes.
We
would
strongly
advise
the
presenters
to
talk
less
than
kind
of
10
minutes
to
leave
enough
time
for
the
discussion.
B
If
you
saw
the
agenda
earlier
on
the
mailing
list
we've
had
to,
we
have
to
juggle
it
around
a
little
bit
to
accommodate
other
constraints
for
some
of
the
presenters
and
other
working
groups
that
they
are
attending
that
are
happening
at
the
same
time.
So
there
is
the
order
for
us
and
at
the
end,
we'll
just
do
a
quick
wrap-up.
B
B
C
D
I'm,
a
booming-
you
are
yours:
okay,
okay,
excellent,
Oh,
monetize
and
yeah.
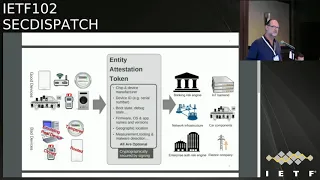
This
little
presentation
is
brought
on
the
different
kinds
of
Rodin's
here
in
the
ideas
which
have
to
be
addressed.
Our
audience
is,
of
course,
a
pond
that
is
referring
to
remote
attestation
procedures.
There's
a
lot
of
work
going
on
and
of
presenting
today,
a
specific
one
that
will
be
discussed
also
on
Thursday
after
the
last
session
in
square
dorchester
and
a
Baba,
and
it
is
the
remotest
ization
terminology.
D
So
attestation
is
being
used
basically
by
every
SDO
in
some
kind.
W3C
uses
it
for
web
authentic
application.
I
think
the
specification
divert
Internet
has
the
term
attestation
like
500
times
in
the
document,
and
still
it's
totally
something
different
than
the
trusted
computing
group
for,
for
example,
things
or
specifies
what
edit
station
is,
or
in
this
case
I
would
like
always
to
highlight
remote
attestation,
attestation
to
other
parties
so
and
I'm,
providing
here
a
preliminary
definition.
D
So,
in
most
of
the
contributors
to
the
ITF
in
the
last
one
and
a
half
years,
remote
attestation
is
the
procedure
of
providing
cryptographic
evidence
which
is
basically
a
proof
that
a
system
entity
is
a
trusted
system
or
a
trustworthy
system
which
both
terms
are
defined
for
ages.
Now
in
RFC,
49
49
and
it's
go
a
little
bit
on
there.
It
means
that
the
system
is
exactly
doing
what
it
is
intended
to
do,
and
nothing
else,
and
this
proved,
that
is
a
trusted
system.
D
It
conveys
in
a
secure
manner
via
an
interconnect
which
could
be
I,
don't
know
a
open
nor
the
Internet
to
another
entity
or
other
entities
so
effectively
these
three
activities.
We
call
them
here
that
are
typically
tightly
coupled
due
to
the
use
of
Ananse
and
the
challenges.
One
scheme,
that
is,
the
attestation
itself,
the
creation
of
evidence,
the
conveyance
of
evidence
from
the
attested
to
the
verifier.
D
We
are
the
supported
interconnect
which
could
be
again
very
close
or
very
far
away
and
then
a
verification
process
that
somehow
assesses
this
evidence
and
to
establish
the
actual
trust
in
the
entity,
creating
the
evidence
so
remote
attestation.
Basically,
as
a
component
composite
of
all
these
three
activities,
which
are
typically
tightly
coupled
and
now,
there's
work
in
the
IT
of
the
decouples
The
Times
points
of
where
the
evidence
is
created
and
may
be
conveyed
years
later
and
still
able
to
be
verified
appropriately.
D
So
there
were
some
time
terms
back
in
the
days.
It's
like
a
statement
of
health,
let's
call
it
system
health
to
be
more
agnostic
and
trustworthiness
and
freshness.
So
this
is
a
very.
This
is
reference
model,
basically
I
stole
that
from
another
da.
This
is
not
from
the
attestation
terminology,
but
it
shows
you
basically
how
this
works,
so
there's
an
ons
in
an
handshake
and
this
nuns
somehow
processed
by
the
ax
tester.
That
is
creating
the
evidence
and
therefore
the
very
final.
D
D
There
is
a
document
which
is
the
attestation
terminology
and
we
try
to
consolidate
terms
here,
roles
and
entities
and
processes
and
so-called
activities
across
work
in
the
ITF,
and
there
are
now
about
I
think
ten
drafts
already,
including
use
cases
coming
from
an
Etsy,
a
liaison,
a
relationship
regarding
envy,
and
so
current
work
in
progress
on
that
graph
is
maybe
there's
more
than
one
kind
of
hardware
root
of
trust.
There
might
be
a
root
of
trust
or
measurement
that
might
be
a
root
of
trust
for
storage.
D
There
might
be
a
root
of
trust
for
reporting,
and
although
science
found
some
what's
the
same
of
different
and
so
there's
confusion
about
this,
there
are
also
multiple
ways
to
prove
freshness,
and
maybe
the
entity
that
creates
the
evidence
is
not
the
claimant.
That
creates
the
content
of
the
evidence,
for
example,
so
multiple
roles
are
not
in
yet,
and
maybe
all
this
terminology
should
also
be
somehow
interoperable
the
other
work
that
is
not
about
attestation,
for
example,
new
forms
to
create
identities,
yeah
more
details,
and
then
we
already
have
a
list.
D
It's
easy
to
know,
remember
the
rats
at
the
ITF
and
we
also
have
a
place
to
look
at,
which
is
a
github
repository
called
ITF
rats
and
if
any
of
you
somehow
is
interested
in
providing
some
proof
of
integrity
that
you
are
actually
healthy
and
the
party
you're
talking
to
should
believe
that
maybe
join
us
on
Thursday
for
our
buff
and
talk
about
what
your
requirements
are.
This
domain.
B
F
F
Perhaps
it
would
it's
a
matter
of
deciding
between
a
50
dollar
and
a
500
dollar
transaction
amount,
or
perhaps
it's
like
that
that
that
we
trust
that
the
reading
of
the
electric
meter
so
we're
out
to
try
and
avoid
or
understand
you
know
if
device
has
been
tampered
with
or
cloned
or
it's
emulating
a
real
device
or
something
like
that.
The
notion
is
that
all
claims
are
optional,
because
otherwise
we're
going
to
have
an
awful
discussion
about
which
claims
are
mandatory,
because
I
don't
think
we
could
converge
on
that.
F
There's
other
ways
of
doing
this
and
I
think
we're
going
to
have
to
accommodate
many
other
flows
just
because
of
the
there's
some
complexities
in
the
way
it's
works,
but
the
the
first
step
is
for
the
manufacturer
of
the
entity
to
put
key
material
into
the
entity
itself.
This
is
done
once
during
manufacturing.
Perhaps
this
is
EPA.
Perhaps
this
is
an
RSA
private,
key
or
keypair.
F
The
ruling
party
would
then
undergo
a
verification
process
where
probably
they
get
keys
from
the
entity
manufacturer,
but
possibly
they
send
the
token
to
the
manufacturer
for
verification
or
a
service
in
between
outcomes,
the
verified
claims,
and
then
they
look
at
those
they
put
them
into
the
risk
engine
along
with
maybe
other
things
they've
got
in
their
risk
engine
and
make
a
decision
about
what
they're
going
to
do.
So.
The
proposal
is
to
use,
chose
a
and
C
bore
for
the
for
this
KO's,
a
a
nice
small
works
for
IOT
devices.
F
Modern
crypto
allows
for
all
the
variations
you
need
in
signing
on
rhythms
and
whatnot
gives
you
the
rules
for
how
you
know
what's
signed
and
what's
not
signed,
and
all
that
see
more
because
it's
nice
and
compact
it
allows
you
to
label
it
label
the
claims.
Clearly,
as
representations
for
all
kinds
of
different
data
you
might
want
to
put
in
claims
in
my
vision
of
claims
is
someone
devices.
Maybe
you
have
two
claims
that
are
integers
other
devices.
F
How
do
you
put
a
key
into
a
chip
where
you
have
to
put
that
key
into
fuses
and
anything
more
than
maybe
256
bits
is
too
expensive,
so
it
tends
to
drive
complicated
manufacturing
processes,
there's
also
the
issue
of
privacy
in
the
signing,
because
if
you
have
a
unique
key,
perdy
and
you're
signing
that
can
reveal
the
identity
of
the
device
so
yeah
that
drives
you
to
things
like
ec
DAA.
So.
F
F
F
And
what
I
mean
particularly
in
what
are
those
claims,
and
what
do
they
mean,
because
if
we
can
all
agree
or
partially
agree
or
somewhat
agree
on
some
sets
of
claims
and
what
they
mean,
then
you
get
the
interoperability
of
these
tokens
in
a
broader
way.
So
to
me,
that's
probably
where
the
large
amount
of
work
would
go
in
this
particular
effort
and
then
one
last
I
guess
one
last
last
thing
is:
the
idea
is
also
that
this
is
not
a
protocol.
F
C
F
So
I
think
that
in
common
that
you
know
the
idea
of
the
flow,
the
basic
flow
and
and
you
you
have
some
some
claims
and
you're
gonna
sign
them,
send
them
to
relying
party
and
they're
gonna
get
evaluated,
there's
some
key
material.
That's
that's
pre
provision.
That
seems
in
common
to
me
when
I
looked
at
your
slides
and
that
that
seems
very
much
in
common
to
me,
I'm,
not
particular
about
a
hard
definition
of
attestation.
I
want
to
solve
the
problem
alright
or
provide
something
useful
whatever
we
call
it.
D
F
D
G
So
I'm
sorry
I
was
I.
Think
I'm
done
for
a
second,
but
is
this?
Does
this
intended
to
support
massive
insures?
The
way
Fido
does
so
Fido
and
Fido
things
are
on
devices
are
assigned
in
groups
so
that
so
it's
not
so
that,
basically
you
don't
create
a
super
cookie
station.
It
would
this
support
that
yeah.
F
D
G
D
G
B
H
H
And
so
that
part
you
can
probably
leverage
or
even
work
with
yep.
The
rest
of
the
attestation
thing
sounds
a
little
bit
more
different
right.
I
know
that
when
working
with
JWT
one
of
my
biggest
frustrations
has
been
the
lack
of
designation
of
what
the
claims
mean
and
and
a
need
for
more
language
around
that,
so
I
think.
D
F
So
we
actually
proposed
using
the
same
Ayana
registry
for
the
claims
as
CWT,
but
the
reason
I
wanted
to
separate
it
is
because
we're
actually
trying
to
prove
something
about
something
different
than
CWT
is
trying
to
prove
and
we're
gonna
run
into
issues
of
like
how
the
keys
are
provisioned
and
handled
and
what
they
mean.
The
claim
sets
are
going
to
be
different
and
there's
gonna,
be
a
lot
of
I
think
a
lot
of
things
that
are
going
to
be
different
and
I.
Don't
think
it
makes
sense
to
combine
the
work.
I
Yes,
Steven
bang,
Hart
I
said
a
couple
quick
clarifying
questions,
so
the
chairs
put
you
guys
together,
you're
standing
both
up.
There
are
these
efforts
that
work
together
to
get
to
this
point.
Did
you
talk
to
each
other?
It
does
the
terminology
for
this.
There
were
these
like
competing.
We're
gonna
toss,
one
of
you
in
the
lion's
den
after
this
I'm
trying
to
understand
the
relationship
here
and
clear
to
me.
F
I
I
D
D
So
yeah,
but
the
scope
is
different
because
you're
deliberately
trying
to
be
an
extension
and
being
used
by
multiple
things
and
we
are
trying
to
scope
the
multiple
things
that
belong
into
the
ITF
and
we
have
a
set
of
protocols
like
time-based
piercings
and
challenge-response
pairs,
yang
modules,
reference
interaction
models
all
there,
but
we
have
to
find
out.
How
does
this
curious
thing?
This
is
the
inbox
API
mix
with
the
extra
protocols
weeks
right
here.
Okay,.
I
C
There's
Richard
Barnes
from
the
floor
so
one
way-
and
this
seems
pretty
significantly
different
from
something
like
JWT
or
CABG-
is
that
with
these
add
sensation
things
you
have
significant
replay
problem.
You
know.
Usually
we
just
tolerate
that
we're
passing
around
identity
tokens,
but
with
these
things,
when
you're,
when
you're,
really,
if
you're
feeding
it
into
a
risk-
and
you
want
some
real
assurance
that
you're
talking
to
the
thing
to
which
that
a
sensation
belongs.
So
do
these
schemes
have
some
mechanisms
to
accommodate
that
risk
and
it
ends
a
deal
with
it.
C
F
C
So,
for
instance,
in
webathon
I'll
call
it
the
proper
name.
There's
the
attestation
certificate
that
you
know
has
a
bunch
of
this
stuff
that
talks
about
what
the
device
says
and
then
there's
a
certain
there's,
a
signature
using
a
public
key
in
that
certificate
over
a
bunch
of
data
that
binds
it
to
a
specific
instance
of
the
anta
station
yeah
right
so
would
the
focus
of
this
work
be
both
of
those
parts
or
just
the
kind
of
equipment,
moral
equivalent
of
the
attestation
certificate.
K
C
D
M
A
my
name
Qualcomm
I'm,
one
of
the
authors
of
the
draft,
so
I'm
Richard
in
response
to
your
comment
on
the
entire
replay,
because
we
leverage
this
the
Seaboard
web
token.
To
my
you
know:
Mike's
draft
the
claims
are
extensible
and
one
of
the
into
the
claims
that
we
can
add
are
the
client
data
hash
and
the
Authenticator
data
which
are
critical
for
keeping
the
attestation
fresh
and
web
authen.
So,
in
fact
not
just
that's
one
of
the
beauties
of
using
a
jot
or
a
caught.
M
H
N
The
the
problem
being
solved
by
remote
attestation
is,
but
is,
is
specifically
the
one
where
you
don't
already
have
a
secure
channel
or
trust
your
channel
with
the
client
or
trust
in
the
client
that
you,
as
you
have
not
yet
established
that
the
client
is
who
it
says
it
is
right.
So
in
that
sense,
it's
not
the
same
as
the
problem.
N
You
know
essentially
like
a
beachhead
on
that
device
to
decide
whether
you're
gonna
trust
it
or
not,
and
then
tying
a
credential
that
that
device
is
created
to
a
specific,
secure
channel,
whether
it's
a
key
or
a
TLS
session,
or
something
like
that
so
I
feel
like
I'm,
like
the
focus
on
rat,
seems
to
be
more
towards
solving
the
problem.
I'm,
not
sure
that,
like
the
precise
token
format
is
all
that
important.
F
K
Is
this
is
honest?
You
think
we
we
support
the
eat
effort
simply
because,
as
Lawrence
you
just
stated,
there's
a
format
or
container
problem
that
we
we
need
to
resolve
in
in
order
to
pass
that
information
from
the
device
to
the
different
parties,
how
the
keys
are
distributed
in
most
of
those
cases
will
be
really
doing
manufacturing
so
I.
D
And
to
close
that
up,
I'm,
a
big
fan
of
cementec,
well
understood
and
interoperable
claim
sets
so
to
be
clear
about
that.
I
actually
support
both
the
representation
and
also
the
cosy
signing
mechanism.
That
is
a
great
idea
to
do
it
and
I
would
do
it
at
every
place,
possibly
if
it
would
be
possible,
but
unfortunately,
some
of
the
work
that
is
all
there
is
still
TLB
and
the
signatures
won't
really
match
that
new
at
all.
D
So,
but
we
found
all
deals
with
that,
even
with
Seaborg
created
structures
that
are
not
necessarily
cots
but
close
to
that.
But
this
is
only
migration.
I
think
I,
think
where
we
want
to
be
is
actually
be
using,
claim
sign,
sets
and
sign.
Claims
said
sorry
using
cozy
import
scale
to
ESRI
support
that
interoperability
and
so
on
with
you
there
absolutely
so.
B
What
we
heard
coming
up
to
the
mic
were
a
couple
of
things.
First,
we
didn't
hear
anyone
running
up
saying
this
is
not
an
area
we
should
be
exploring
at
all.
What
we
also
heard
was
not
what
we
didn't
hear.
I'm,
sorry
is
anyone
saying
that's
clearly
in
this
working
group
or
that
working
group
or
another
working
group,
and
what
this
leads
us
to
suggest
yours?
This
is
probably
a
Boff
there's,
clearly
some
heat
here.
We
need
over
more
discussion
to
kind
of
flush
that
out,
it's
not
naturally
fitting
in.
A
C
P
This
is
okay,
so
there
wasn't
concerns
that
way.
We
had
too
many
slides
I
will
try
to
be
a
fast.
Basically,
it's
about
intruder,
introducing
a
draft
that
is
complementary
to
another,
one
that
is
being
discussed
in
acme
and
that
we
expect
to
go
for
working
group.
Let's
call
this
during
these
days
well
just
to
set
in
the
the
ground.
We
are
using
three
elements
here.
P
One
is
what
we
call
the
I:
do
the
identity
owner
the
other
one
is
the
NDC,
which
is
intentionally
reverse
the
CDM,
because
this
has
been
originally
shot
for
the
case
of
Syrians
and
basically
the
CA
that
you
all
should
know
what
means
the
VI.
Basically
here
is
about
the
possibility
of
that
the
I
do
delegating
the
identity
identity.
P
To
sorry,
the
I
do
delegating
the
possibility
that
the
NDC
can
use
a
certain
private
key
to
a
to
prove
the
association
of
this
private
key
to
the
delegated
identity
by
means
of
a
certificate
in
the
case-
and
this
is
in
which
all
these
statuses,
in
the
case
of
relationship
between
CBM
provider
and
content
provider
case
this
cop,
is
when,
for
whatever
the
reason
you
are
not
using
your
rewriting
or
resurrection.
So
you
are
accessing
directly
the
domain
name
and
the
certificate
I
mean,
and
yet
the
domain
name
is
hosted
elsewhere.
P
P
Well,
we
have
been
working
on
one
of
the
size
of
the
protocol
inside
acne
and
the
idea
that
when
we
started
defining
the
how
the
requests
should
go
well,
historically,
we
studied
with
this
inside
acne,
and
we
were
asked
to
come
here
just
to
see
whether
there
was
a
general
agreement
that
this
belongs
to
add
me
or
not.
Well,
apparently,
apart
from
that,
the
reason
for
standardizing,
it
is
clearly
what
we
are
talking
about:
different
organizations,
different
relationships,
several
ideas
working
with
the
same
and
de-seed
several,
and
this
is
serving
the
same
idea
with
cetera.
P
So
as
I
said
before
the
idea,
all
these
was
in
a
single
document
that
was
submitted
to
Acme.
When
the
ACMA
document
Atma
Starr
was
adopted,
there
was
a
suggestion
of
splitting
both
both
parts
of
the
protocol,
and
it
was
not
clear.
There
was
an
doubts,
whether
their
requests
themselves
really
belong
to
Acme
or
not.
The
other
side
I
mean
on
the
side
of
the
Atma
is
there
is
an
agnostic
extension
in
the
side
of
requests
is
not
such
an
extension.
P
P
The
draft
is
about
precisely
how
the
the
NBC
requests
and
Nachman
certificate
through
the
ideal,
because,
as
the
one
that
has
the
the
trans
relationship
with
the
CA
is
a
VOD,
the
CA
never
sees
beyond.
This
is
about
delegates
me
a
certificate
for
a
particular
power.
It's
keyed
and
they
issue
a
CSR
template
and
the
I
do
is
able
to
analyze
it
and
match
it
with
the
whatever
the
policy
and
agreements
be.
A
behavior
has
with
you,
and
they
say
this
is
this.
Is
this?
P
Is
that
man
with
a
fuse
extension,
which
is
against
our
thing?
That
is
this
draft
I,
was
mentioning
before
the
CA
issues
following
the
ACMA
prophet,
the
ACMA
protocol
sense.
He
sends
back
the
the
request
and
something
that
is
important
in
the
request.
There
is
a
period
and
a
frequency,
because
we
are
talking
about
I
forgot
about
this
I'm.
Sorry
we're
talking
about
temporary
certificate.
P
Very
surely,
if
that
are
automatically
renewed,
because
one
of
the
essential
mechanisms
is
that
periodically
the
NDC
using
Acme,
don't
lost
the
certificates
and
updates
it
and
then
any
moment-
and
this
is
the
other
part
on
this
important,
which
is
essentially
its
equivalent
to
a
revocation.
The
idea
at
any
moment
can
using
the
administer
protocol
request
to
invalidate
this
and
then
the
end.
This
is
not
able
to
the
low
enemy
anymore,
dear
refreshed
certificate
and
review,
and
the
certificate
becomes
invalid.
Let
me
say
this
is
equivalent
to
revocation
well
just
to
finish.
P
P
Q
A
very
clarifying
question
on
your
previous
slide,
so
in
this
particular
case
the
fact
that
I
do
and
and
the
certificate
certifying
Authority
are
cooperating,
does
not
actually
require
the
certifying
authority
to
be
using
acne
to
deploy
certificates
right.
Do
you
mean?
Do
you
mean
yeah,
so
that
CA
here,
if
it's,
if
it's
doing
its
certificate
management
without
using
Acme,
can
it
still
use
idea
in.
P
Q
R
P
It
goes
because
we
were
considering
this
case
as
I
said
before:
it's
not
that
you're
asking
I
mean
you're
the
owner
of
the
of
the
domain.
If
you
want
AG
me
to
sign
something,
for
you
is
that
you
want
to
say
AG
me
to
sign
something
for
a
third
party
that
is
going
to
use
a
private
key
with
a
certificate
I.
R
Don't
think
that's
fundamentally
any
different,
so
you
mentioned
that
the
this
third
party
gets
you
a
CSR
from
private
key
that
it
owns
and
it
talks
to
this
middle
box
and
says
I
create
I'd
like
to
create
a
new
order
and
there's
no
authorization
required
other
than
the
fact
that
it's
got
client
authentication
at
the
TLS
layer,
for
instance.
No.
P
R
P
R
S
G
Music
I
can
clarify.
Does
that
terminology
here
for
saying
I'm
a
middle
box?
The
point
is
that
the
I
do
is
telling
CA
to
give
a
certificate
to
the
NDC.
Yes,
so
Martin's
point
as
I
understand
it
is
why
don't
you
speak
acne
on
both
sides?
Why
does
an
I
do
act
like
an
acting
with
both
sighs?
You
mean
the
set
request.
Yes,.
T
R
R
P
R
Do
all
of
that
business?
Yes,
but
and
and
will
gain
those
authorizations
and
can
then
make
a
certificate
request.
It
just
happens
to
use
the
CSR
that
was
provided
to
it
by
the
NBC.
Yes,
that's
a
alphabet
soup
right
there,
but
anyway
and
then
returns
back
a
pointer
to
the
CA
in
in
its
final
response,
saying
your
certificates
over
here
to
the
MDC,
and
so
the
NDC
can
then
talk
to
the
CIA
directly
to
get
the.
S
R
P
T
M
L
T
R
P
R
S
S
P
P
C
C
P
N
N
But
there
are
tons
of
uses
for
multicast,
obviously,
but
what
is
the
problem
that
multicast
has
well?
The
big
problem
it
has
is
that
inter
domain,
multicast
has
security
issues
which
is
a
polite
way
of
putting
the
problem.
It's
susceptible
to
injection
attacks,
even
if
you,
even
if
you
do
have
filtering
or
BC
p-38,
you're,
still
subject
to
man
on
the
side
in
the
middle
attacks.
N
So
what
we
would
like
is
an
integrity
scheme
that
satisfies
the
following
requirements:
line
rate,
verification,
the
use
of
asymmetric
crypto,
which,
as
I'll,
discuss
a
little
bit
later
and
precludes
the
use
of
something
like
Tesla.
We
also
need
it
to
be
efficient
right.
We
can't
the
the
the
sort
of
oblivious
solution
or
naive
solution
of
just
signing.
N
Every
packet
is
not
going
to
work
because
you
have
low
power
devices
downloading
large
videos
and
it
needs
to
authenticate
every
packet
before
it
displays
it
that
just
wouldn't
work,
and
we
also
want
it
to
be
lost
tolerance.
So
we
need
for
multicast
you're
going
to
assume
that
some
of
the
packets
are
going
to
be
lost.
Although
we'll
have
to
do
some
analysis
on
what
the?
What
the
profiles
of
that
loss
are
because
we're.
We
suspect
that
it's
not
uniform,
so
the
scheme
that
we
came
up
with
in
the
draft
that
we
posted
here.
N
This
is
the
simple
version
of
that
scheme,
so
you
essentially
have
an
anchor
that
has
a
public
key
in
it.
Just
assume
for
the
moment
that
this
anchor
you
that
you've
received
this
anchor
in
a
secure
way
from
some
from
some
entity
that
you
trust
the
manifest
is
a
single
packet
that
contains
that
contains
a
signature
of
itself
and
the
and
hashes
packet,
IDs
and
hashes
of
the
data
packets
that
are
sent
that
are
sent
asynchronously.
So
the
idea
here
is
that
the
manifest
provide
the
manifest
providing
uses.
N
One
signature,
one
asymmetric
signature
to
provide
integrity
protection
for
all
of
those
data
packets.
Now
you
can
see
immediately
the
problem
with
this.
Is
this
limits
your
data
rate,
if
you're
using
32-bit,
hashes,
32-bit,
full
hashes,
and
even
if
your
packet
numbers
are
implicit
where
you
don't
have
to
include
them
in
the
in
the
manifest
you're
still
going
to
run
into
a
limit
of
about
40
packets
of
integrity,
information
per
manifest?
N
Information
for
child
manifests
that
themselves
have
have
integrity,
information
for
the
data
packets,
and
by
extending
this
you
can
have
you,
you
can
increase
the
bit
rate
almost
arbitrarily,
but
there
are
a
ton
of
problems
with
the
scheme
like
this,
because
if
you
lose
any
single
packet,
you
lose
the
ability
to
verify
the
integrity
of
all
the
data.
So
you
can
imagine
doing
something
like
this,
where
you
have
a
rolling
route,
manifest
where
the
where,
if
you
lose
one
route,
manifest
you're
fine,
because
you've
got
others
that
will
cover
the
same
data.
N
In
this
case,
you
have
the
the
first
route
manifests
on
the
left.
There
provides
integrity
information
for
the
for
the
first
three
child
manifest
the
second
route,
manifest,
provides
integrity,
information
for
two
three
and
four
and
it's
set
and
so
forth
and
so
on,
and
so,
if
you,
you
can
imagine
extending
this
further
I
didn't
produce
a
diagram
for
this
where
you
would
have.
The
child
manifests
also
roll
over
a
window
of
the
data
packet,
so
you
would
have
enough
enough
redundancy
under
expected
loss
conditions
to
be
able
to
cover
all
the
data
packets
occur.
N
N
G
I
guess
he's
just
in
several
use
cases,
so
you
said
audio/video
and
software
download.
Those
are
quite
different
in
the
sense
that
software
download
like
actually
get
all
the
bits
eventually
and
so
typically,
and
so
typically
your
supplies
to
ensure
that
covers
the
entire,
the
entire,
the
entire
body.
And
then
you
don't
need
to
worry
about,
but
about
sorry.
N
I
guess
I
didn't
describe
the
I,
didn't
fully
describe
the
the
motivation
for
doing
inter
domain
multicast
right.
So
if
you
have
a
popular
software
download
sure,
let's
say
there's
a
you
know
like
a
new
OS
update
or
something
like
that,
and
you
want
to
distribute
that
to
millions
of
people
at
the
same
time
yeah.
It
would
be
nice
if
you
could
use
multicast
to
do
that.
Sir
right
I
mean-
and
in
that
case,
if
you
lose
some
packets,
if
you
lose
some
data,
it's
not
a
big
deal.
G
N
Right,
so
that
was
actually
what
I
was
going
to
get
to
at
the
end
here
so
there's,
so
the
idea
would
be
to
use
a
miracle
tree
like
structure,
to
have
the
integrity
information
inside
each
data
packet.
That
complicates
things.
One
of
the
reasons
why
we
didn't
where
we
didn't
decide
on
that
initially
is
that
that
requires
a
change
in
the
data
format.
One
of
the
nice
properties
of
this
is
that
you
can
provide
the
integrity
information
in
a
separate
channel
and
not
have
to
modify
the
data.
G
N
We
are
thinking
I,
think
from
a
I.
Don't
want
to
tie
this
necessarily
just
to
live
video,
but
for
the
live
video
use
case,
there's
the
hand-wave
latency.
So
basically,
when
somebody
waves
their
hand,
how
long
is
it
until
people
see
it
on
their
screen,
and
so
obviously
you
need
to
you
need
to
authenticate
everything
you
need
to
on
it
authenticate
a
segment
of
video
that
is,
that
is
at
least
sorry
at
most,
the
length
of
the
hand-wave
latency
right.
N
G
Bays,
however,
how
long
is
your?
How
long
is
your
her
I
mean
how
many,
how
many
packets
yeah
that's
a
hundred
packets
I
mean?
Basically
it's
like
I
mean,
like
I,
mean
you're.
You
just
consumed
all
my
latency
with
your
scheme
right
on
so
I
guess.
My
point
is
like
that
that
that
you
say
you
say
you
can
only
get
40,
packets
or
so
within
a
you
know,
within
your
just.
G
R
N
Tesla
right
yeah,
so
that
so
I
can
explain
one
of
the
use
cases
that
we
were
trying
to
that.
We
were
trying
to
address
that
Tesla.
Doesn't
so
Tesla
achieves
a
symmetry,
essentially
temporarily
right,
so
it
doesn't
release
the
key
until
after
all
the
recipients
and
had
the
data
delivered.
So
that's
how
it
prevents
one
recipient
from
impersonating
the
publisher
right
that
doesn't
work.
M
Your
amonium
Qualcomm,
so
this
may
be
well
they're
related
to
that
grid's
point,
but
when
I
look
at,
if
you
look
at
briefly
standardized
and
deployed
IP,
multicast
over-the-air
systems
like
a
TCP
data
which
you
implement,
live
streaming
using
file
cast
a
using
file
cast
transport.
In
this
case,
ATSC
specifically
does
a
fluid
derivative
called
route
and
I'll
be
actually
talking
about
that.
The
GGI
ii
task
force
meeting
later
on
this
week.
M
This
wouldn't
be
implemental
because
you're
doing
all
the
all
the
integrity
checking
at
a
packet
level
I'm
still
not
quite
clear
about
the
argument.
Why
you
couldn't
do
it
at
an
object
or
file
level,
given
that
you
can
still
meet
your
requirements
as
far
as
live
TV
services
are
concerned,
unless
you're
not
looking
at
live
services
for
streaming
well,.
N
What
were
you
considering?
What
were
you
using
this
transport
for
live
video
right?
We're
considering
a
situation
in
which
you
would
use
in
which
you
would
use
multicast,
maybe
within
the
publisher
network,
then
am
a
tunnel
into
an
AAS
that
has
multicast
supported
natively
within
their
network
yeah.
M
So
we
would
be
looking
at,
in
that
case,
we're
looking
at
IP
multicast
from
the
broadcast
or
tower
down
to
the
television
set
where
there's
a
where
the
transport
is
essentially
is
something
very
similar
to
flute.
I
forget
there
are
I've
seen
on
the
flute,
but
I
mean
flute,
is
essentially
a
podcasting
system
and
which
marries
well
with
technologies.
M
Like
a
raid
or
something
in
the
recipient
in
the
recipients
network,
if
you're
talking
about
a
TV
set,
they
would
fire
it
requires
a
bit
requires
a
protocol
stack
at
the
transmitter
side
in
the
broadcaster
carry
they
may
be
ingesting
over
the
internet
and
that
may
be
done
over
a
non
IP
multicast.
So
that
might
be
done
over
your
test
Network,
but
then
it'll
multicast
over
two
different
TV
receivers.
Is
that
not
the
use
case
you're
looking
at
or
is
that
completely
different
I'm.
S
The
way
that,
basically,
there
are
many
different
solutions,
I'm
a
different,
but
the
problem
is
that
it's
difficult
to
come
to
a
generic
problem,
because
the
solution
that
you
come
to
is
really
sensitive
to
the
attack
model.
They
assume
other
constraints
that
you
assume
and
changing
the
attack
model
or
the
consequence
very,
very
small
changes,
the
optimal
solution
dramatically.
So,
for
example,
for
anything
that
static,
you
don't
want
to
do
any
of
this.
S
S
Known
data,
that's
a
separate
problem
entirely,
so
you
talking
about
live
and
then
the
question
comes
up.
Well,
what
consequence
are
you
willing
to
accept?
I
mean,
like
denial
of
service,
isn't
going
to
be
soluble
because
if
you've
got
denial
of
service
going
on
or
you
can
do-
is
to
shut
down
this
the
pipe.
N
N
N
I
mean
I'm,
not
yeah,
I,
think
I'm,
more
looking,
so
where
we
want
to
go
with
this
is
we're
wondering
what
the
next
step
should
be,
whether
this
is
something
that
we
should
something
that
the
security
area
should
look
at
in
a
little
more
depth
even
to
decide
whether
it's
worth
doing
or
not,
and
one
of
the
ideas
that
Jake
and
I
had
was.
Should
we
reopen
m/sec
to
look
at
this.
I
Chris,
oh
yeah,
Chris
would
I
just
want
to
point
out
some
related
work
in
the
ice
interview
working
research
group
there
again
this
thing
called
flick.
This
file,
like
I,
say
in
structure,
which
is
basically
exactly
what
you
described.
The
Disraeli
manifest
thing
so
might
be
worthwhile,
taking
a
look
at
that
not
advocating
for
ICN
in
any
way
shape
or
form
just
pointing
it
out.
Okay,
thanks.
G
Well,
I,
the
cetacean
I
was
referring
to
earlier
ISM
go
away,
and
what
did
you
do
from
NDS
2001
authentication
data
and
presence
of
random
packet
loss?
I
sent
mr.
sagen
yeah,
it's
Cola
amudha
dugu
from
n
DSS,
2001,
authenticating
stream
data
and
the
presence
of
random
packet
loss
because
they
walk
out
the
with
a
claim
of
the
optimality
bounds
for
various
kinds
of
constructions.
Using
caches,
that's
grown.
G
C
G
N
Conception
is
that
the
protocol
would
be
would
allow
for
a
broad
range
of
use
models
models,
but
without
the
draft
would
specify
a
recommended
K
recommended
use
case
right,
recommended
parameters
for
for
overlap,
or
if
we
decide
to
go
with
the
Merkle
tree
for
how
that
would
be
constructed.
You
know,
based
on
math
that
actually
tells
us
what
the
optimal
the
optimal
parameters
are.
So
I'm
thinking
both
a
specification
of
a
protocol
for
for
creating
and
distributing
the
integrity
data
as
well
as
recommendations
and
how
it's
used
so.
G
I
think
my
advice
would
be
to
try
to
find
some
particular
use
case
where
people
actually
want
to
do
this
and
specify
for
that
use
case,
but
with
generality,
if
you
can,
and
if
you
can't
get
that,
then
I.
Think
probably
you
know
that's
a
different
question,
but
I
think
like
I,
saw
some
people
I
think
for
the
same
community
of
interest
if
I
looking
at
the
namespaces
correctly.
So
so,
maybe
those
guys
can
form
a
community
interest
with
you
wants
to
do
a
protocol
that
people
care
about
okay,
cuz
I,
do
I.
G
C
G
So
I'm
not
Bank,
addict
I've,
literally
never
seen
these
slides
before
in
my
life
quite
interesting,
yeah
thanks
exactly
I
guess
the
first
thing
I'd
say
is
I
think
it
has
to
be
clear
from
this
like
this
is
not
my
draft
I'm,
not
a
proponent
of
this
draft
on
the
ad.
You
potentially
have
to
manage
this
draft
so
thanks
to
Adrian
for
giving
us
the
giving
us
the
timeline
here.
G
So
this
is
basically
this
is
draft
on
which
I
don't
I,
don't
even
know
if
there
was
description
of
what
this
is
about,
but
it's
next
slide
awesome.
So
so,
basically,
this
is
a
draft
for
an
enhancement,
pkcs
8,
which
I
guess
I'll
talk
about
in
a
minute
which
the
the
author
proposed
on
Sun
sag
before
we
had
like
I
guess
before
we
had
sex
dispatch
and
there
was
like
man
not
really
much
interest.
Dafwa
submitted
is
see.
You
can
see
this
incredibly
long
thing
here.
G
We
said
back
at
do
not
publish
coffee
response,
which
basically
said
we'd
like
to
see
you
bring
this
a
sec
dispatch,
and
so,
as
you
can
see,
this
has
been
appealed,
but
not
by
the
opponent
rather
by
john
clinton
and
now
we're
here.
So
that
think
of
the
appeal
and
and
this
in
the
sexist
best
thing
is
separate
things.
God
leave
John's
appeal
actually
says
that
so
any
case
appeal
regardless
you'd
be
good
to
see.
If
this
actually
has
a
dresser
the
sex
dispatch
for
Ike.
If
stick
it
on
right.
C
G
G
That
you
might
wish
to
have
have
proofs
that
the
primes
are
generated.
Primes
in
a
public.
Private
key
were
generated
a
certain
way
and
it's
possible
to
package
those
proofs
up
along
with
your
public,
along
with
your
key,
that's
private
key,
and
so
this
document
basically
specifies
how
to
do
that
in
pkcs.
8
the
write
less
law,
okay,
so
this
is
Ana
slide,
so
I'm,
just
I'm
vamping
now,
but
on
the
relevant
facts
are
on
that,
because
these
are
rights
in
the
slot.
G
This
is
going
in
as
an
extension
slot
and
piggy
ssa.
So
it's
a
noite
and
the
there's
there
further.
No
any
considerations,
the
document
and
the
oeid
that
this
is
a
publication
in
this
particular
attention
is
using
red
hats
or
dark,
not
my
TFO
york.
So
there's
no
there's
no
technical
requirement.
This.
We
have
any
interaction
with
ETF
at
all.
G
S
G
It's
not
coming
out
on
IETF
registry.
So,
however,
the
app
is
chief
Feld
and
as
I
say,
we
have
an
appeal.
So
we
have
an
opportunity,
consider
that
position
but
felt
that
while
it
was
perfectly
fine
for
that,
why
he
published
and
for
some
other
document
outside
the
RFC
series
to
document
that
you
said
that
if
there
were
to
be
things
were
effectively
sanchez
de
piqi
SSA,
which
went
through
the
ITF
process,
and
they
were
as
publishers
RFC's,
they
should
go
through
the
ITF
process,
run
a
published.
G
Nya
say
that
with
the
contest
in
which
the
which
the
DMP
was
presented
so
I
guess
the
but
I
think
the
court.
The
question
at
hand
this
last
slide.
Ok,
is:
is
there
interest
in
the
ITF
in
actually
doing
doing
this
work
or
reviewing
it
or
something?
Or
is
there
no
interest
me
ietf
in
which
gift
that
can
be
taken
back
to
the
ISC,
and
then
there
can
be
discussion
about
what
so
I
think?
G
G
Sean
Leonard
so,
as
I
said
on
the
list
recently
I'm
in
favor
of
this
trap
preceding
the
publication
and
I,
don't
see
a
reason
why
it
has
to
go
through
further
IETF
process
beyond
just
what
it
is
now
which
is
I
see
it
is
in
a
private.
Oh,
I,
dr
canned.
I
think
that
that
pkcs
ate
as
a
container
format
is
designed
so
that
these
types
of
extensions
can
can
be
made
and
I
think
that
Kathleen
Mori
already
made
it
similar.
G
V
So
roughly
my
view
is
that
we
should
let
this
go
forward.
I
think
we've
aggravated
this
author
by
him.
First
coming
a
sag,
we
saying
go
over
there
who
comes
over
there.
He
brings
it
back
through
the
ISE
and
then
we
say
oh
conflict,
for
you
know
you
shouldn't
go
forward
this,
the
basically
it's
the
oil
has
already
been
assigned.
The
context
is
clear:
the
only
difference
is
whether
we
tell
the
world
whether
that
ID
means
and
in
RFC
or
something
else
so
I
think
he's
engaged
with
our
process
and
we
go
just
look.
W
X
I,
just
I'm
sorry
I'm,
just
coming
out
of
this
slightly
cold
I,
just
want
to
comment
that
you
have
the
shot.
Taylor
Rufo
primality
is
fine,
but
you
can
deduce
by
looking
at
it
what
Pro,
how
what
Prime
you're
talking
about
and
so
is
able
to
factor.
If
you,
if
you're,
trying
to
show
that
an
RSA
key
is
actually
prime
actually
dinner
properly,
what
we
better
would
be
a
journal
that
is
a
that
is
an
RSA
key,
was
a
have
exactly
two
prime
factor.
E
Stephen,
so
I,
don't
I
think
this
should
be
just
should
go
forward
in
the
IC
I.
Don't
I
don't
understand
the
is
G
reason
for
saying:
do
not
publish
I'm
a
number
yeah,
I
guess
you're
gonna
deal
with
that.
The
appeal
but
I
have
to
say
it's
really
unclear
to
me
what
the
justification
for
that
was
and
I
didn't
understand
how
you
described
it.
Okay,
wait
help
I
said
it
again,
not.
G
If
you
use
the
same
words,
I
mean
I,
think
yeah
I
think
the
I
use
decision
I
wrote
that
tack
so
I'm
not
trying
to
like
I'm
not
trying
to
like
MIT,
but
the
IOC's
I
know
that
was
that
having
this
be
an
RFC
implies
something
to
many
people
about
what
on
the
IITs
position
on
on
it
was,
and
that,
given
that
and
the
given
that
the
originally
it's
came
through
IETF,
but
extensions
that
have
already
seen
also
compromise.
Yet.
G
E
S
Y
Adrian
Farrell,
currently
the
IOC
the
point
of
coming
to
set
dispatch
with
this
document
was
to
hear
the
iesg
when
they
said.
We
think
that
there
might
be
community
interest
in
publishing
this
as
an
IETF,
RFC
I
put
that
on
the
list
and
set
dispatch
list
a
month
ago
and
I
don't
want
to
interpret
consensus
in
your
working
group.
But
I
didn't
hear
anybody
saying.
Oh,
oh,
we're
really
interested
in
doing
this.
In
this
meeting,
I
actually
heard
even
the
opposite.
I
heard
a
number
of
people
say
I'm,
just
just
get
it
out
as
ISE.
Y
Now,
if
you
want
to
push
it
through
the
IETF
as
a
an
IETF
document,
I
have
no
objection
to
that.
I
like
stuff
coming
through
the
ITF,
virtually
quite
like
the
IDF,
but
I
I
would
really
encourage
that
it
happens
with
at
least
some
kind
of
process,
support
from
the
chairs
or
a
DS
or
the
working
group.
Otherwise,
it's
questionable
whether
there's
ATF
consensus
on
an
IETF
consensus
document.
G
R
Proposed
standard
is
better
than
whatever
other
labels
that
might
be
available,
so
the
only
problem
is
finding
a
home
for
it.
I
don't
like
eighty
sponsorship,
but
I
mean
it
seems.
Okay,
in
this
case,
I
mean
I'd
rather
never
use
ad
sponsorship.
But
if
this
one
group
thinks
that
the
ad
should
sponsor
it,
then
that's
actually
not,
and
that's
actually
probably
the
best
way
to
use
ad
sponsors.
G
And
the
purpose
of
success
bash
is
precisely
the
wanderer
ad
sponsorship
through
community
input.
Right
so
I
mean
I
mean
no
seriously,
it's
just
to
make
it
so
that
we're
not
just
making
over
your
decisions.
So
I
guess
Ben's
not
here
and
been
sort
of
with
the
person
doing
this,
but
I
guess
we
I
mean
if,
if
one
of
us
were
once
of
this,
which
is
this
something
that
the
people
would
want
to
have
doing
and
we're
going
to
reveal
so.
E
Steam,
so
I
guess
I
would
probably
be
against
making
this
noise
yep.
This
is
going
to
be
something
somebody
has
done
and
then
publishing
the
ICC's
fine.
If
we
want
to
do
something
in
the
IETF
nathers
interest,
then
I
think
we'd
have
to
we'd
have
to
wonder
about
the
cryptographic
spent
behind
this
and
possible
other
ways
of
doing
it,
and
that
doesn't
sound
to
me
like
something
that
we
should
do.
E
V
B
B
O
Is
Mary
may
I
suggest
the
first
question
be
who
objects
to
telling
the
ISEE
that
it's
okay
with
us
to
publish
it
and
then,
depending
on
the
outcome
of
that,
you
can
consider
another
question
about
a
key
sponsor.
Can
you
say
that
again,
I
suggest
the
first
question
asked
for
objections
to
telling
the
ISC
we
think
we
should.
He
should
go
ahead
and
publish
it.
B
G
I
guess
that
makes
me
a
little
sad
to
be
honest,
you
know
I
think,
as
I
said,
I
think
we
felt
like
that.
We
Isis
went
through
the
ITF
and,
notwithstanding
I
I
still
think
that
I
still
prefer
things
that
are
any
publishers,
RFC's
they
go
to
the
ITF.
So
so
you
know
the
I
notice,
I
think
I,
think
I
guess
I
would
like
to
hear
like
our
people
were
willing
to,
like,
like
our
people,
comfortable
use,
a
dispositive
going
to
you
sponsor.
U
G
Z
This
is
Pete
Resnick
I
doubt
Adrian
will
say
this
is
the
mic,
but
but
I
want
to
be
clear
that
whatever
this
group
says,
Adrian
can
say
screw
you
I'm,
publishing
it
anyway
and
and
can
just
go
ahead
and
pull
the
trigger.
It's
a
courtesy
for
him
to
ask,
but
we
are
not
making
a
decision
for
him.
Let's
be
clear
on
that.
That's
miners
in
the
process
as
well.
C
J
B
I
want
less
Hans
right
I
want,
is
you
publication?
I
want
ad
publication
I
want
something
else
in
IETF.
I
object
to
this
work
at
all.
That's
all
right!
So
let
me
again
the
options
again:
I'll
speak
more
slowly,
we're
not
typing
it
on
the
screen.
The
first
home
is
going
to
be
I,
want
to
publish
this
draft.
It's
is
C.
The
next
hum
is
I
want
to
publish
this
as
a
key
sponsor.
The
third
hum
is
I
want
to
publish
this
since
this
some
other
way
in
the
IETF
fourth
option.
B
B
S
So
this
is
what
I
talked
about
at
RFC
date:
data
at
rest,
encryption-
dare
we
came
up
with
the
acronym,
and
so
you
had
to
have
a
draft
okay,
so
PGP
and
s/mime
are
really
good
for
the
things
that
they're
designed
to
do
they're,
not
really
designed
to
encrypt
data.
That
comes
to
you,
one
chunk
at
a
time.
S
In
that
the
only
way
you
can
do
it
really
is
to
do
a
sequence
of
open
PGP
messages
and
then
have
some
sort
of
way
of
turning
them
into
a
sequence,
and
it
it's
big
and
it's
bloated
and
you
don't
get
any
cryptographic
return
on
that
overhead,
so
dare
container
is
a
way
to
do
incremental
encryption,
oh
yeah,
so
it's
doing
incremental
encryption
and
authentication.
So
you
have
an
impending
Lee
log.
S
You
only
write
things
to
the
end
of
the
log
and
you
have
an
authentication
mechanism
built
in
or
rather
than
the
option
to
do,
authentication.
You
can
hash
each
item.
As
you
add
it,
you
can
do
chains
of
digests
across
the
sequence
or
you
can
do
a
Merkel
tree
across
the
sequence,
and
these
allow
you
to
do
rapid
authentication
of
the
entire
log
from
a
single
signature
or
to
sign
individual
records
in
the
sequence,
and
it
gives
you
the
same
capabilities
of
something
out
there
called
clock
chain
or
something.
S
You
also
have
the
incremental
encryption,
so
you
can
do
a
key
exchange
and
then
you
can
apply
that
key
exchange
to
one
record,
a
sequence
of
records
that
are
contiguous
or
even
non
contiguous
records.
So
one
way
that
you
can
use
this
is
say:
a
server
is
using
this
to
encrypt
its
log
files.
It
starts
up,
it
doesn't
have
any
ability
to
read
its
own
logs
because
it
doesn't
have
the
private
key.
S
It's
a
write,
only
log
for
the
server
it
does
a
a
key
exchange
when
it
starts
up,
writes
to
the
log
when
it
reboots
new
key
exchange
starts
writing.
You
could
even
have
two
processes
writing
to
the
same
log.
At
the
same
time,
and
provided
you
stay
within
the
4096
bytes
that
the
operating
systems
provide
you
otama
city
with
the
two
won't
interfere,
you
can't
do
Merkel
tree
or
the
hash
chaining
with
that,
though,
but
so
this
allows
you
to
have
encrypted
attributes
or
payloads.
S
So
it's
a
little
bit
more
than
you
get
from
SM
from
CMS
or
PGP,
okay,
so
efficiency
all
operate.
This
has
been
designed
so
that
all
operations
are
going
to
be
log
N
or
better.
So
when
you
open
up
a
container,
even
if
it's
got
the
Merkel
tree
is
never
going
to
be
worse
than
a
log
n
operation
to
open
that
container,
appending
a
record
is
always
going
to
take
you
unit
time.
S
Read.
Efficiency
is
going
to
depend
upon
the
container
type
in
that.
If
you
formed
a
tree
index
over
the
container,
then
you
can
seek
to
can
do
random-access
in
log
n
time.
If
you
haven't
well,
you're
gonna
have
to
read
the
whole
it's
sequential
container
and
whether
or
not
that
matters
to
you
really
depends
upon
your
application.
It's
and
you
can
also
choose
the
encoding.
You
can
actually
do
this
in
stripe.
S
So
this
is
the
way
that
we
traditionally
do
our
key
exchange
in
SMS
or
PGP.
You
have
your
public
key
information.
You
have
your
encryption
key,
you
have
your
plaintext
and
you
have
your
initialization
vector
and
that's
all
the
data
that
you
provide
in
the
encrypted
message.
Then
you
go
through
the
key
exchange
and
you
spit
out
a
public
key
identifier,
recipient
information,
your
ciphertext
and
you
give
the
use
of
the
initialization
vector
okay.
S
S
We
take
the
plaintext
and
the
master
key.
We
apply
those
and
that
gives
us
a
cipher
text.
So
the
only
thing
that
we
actually
need
to
tell
the
user
is
who's.
Decrypting
is
the
salt
and
the
ciphertext.
Sorry
I
just
realized
that
the
salt
should
have
carried
across
onto
the
sequence:
outputs
as
well.
We
use
HK
DF.
The
key
derivation
function
that
we
use
in
other
protocols
to
generate
both
the
encryption
key
and
the
initialization
vector.
S
So
we
don't
allow
users
to
generate
their
own
initialization
vectors,
which
is
something
that
I've
not
seen
done
before,
but
is
kind
of
logical
to
me,
I
mean
a
lot,
the
less
things
you
allow
the
user
to
generate
the
better
because
the
less
randomness
you
moving
around.
So
this
allows
us
to
reuse
the
same
master,
key
Skee
multiple
times,
because
every
time
we
apply
it
to
a
new
data
set
say
a
new
data
sequence.
We
will
automatically
get
a
new
session
key.
S
So
what's
it
for
well,
one
application
is
to
archive
a
website
offline
in
an
encrypted
format.
So
you
can
web
web
a
website.
You
can
put
it
into
one
of
these
containers.
You
can
sync
it
on
to
say
USB
key
and
if
you're
in
parts
of
the
world
where
the
web
is
censored,
that
gives
you
a
very
easy
way
to
surf
the
web
in
minimal
time.
S
S
S
And
of
course,
yes,
the
three
key
cryptography
things
I've
presented
at
previous
IETF
I'm,
still
working
on
that
and
using
the
multiple
decryption
key
sorry,
the
split
decryption
key
tricked
ography
is
one
of
the
reasons
that
we
invented
this
format
for,
but
that's
not
what
I'm
presenting
it
here
and
I'm
quite
happy
for
people
to
say
that
they'd
like
to
wait
until
I've
got
that
as
well.
This
particular
container
format
is
not
tied
to
my
particular
key
management.
You
could
use
PKK's
for
it.
S
C
C
S
S
AA
S
I
mean,
like
you
know,
my
main
business
is
as
an
expert
witness
in
patent
defenses,
so
the
work
that
is
similar
to
this
that
I'm
aware
of
will
be
the
crips
elope
stuff
from
IBM
and
I.
Believe
all
those
patents
have
expired
because
that's
over
20
years
old
now,
I
think
that
the
reason
that
we've
not
done
something
like
this
before
was
because
the
harvester
Netta
patents
stopped
you
doing
the
digest,
authentication
training,
but
the
encryption
piece
I
mean
basically
that's
the
TLS
key
exchange
but
applied
to
static
data.
B
J
S
C
L
L
In
particular,
the
drafting
question
has
for
Ayane
registrations
to
curve
identifiers
and
to
algorithm
identifiers
one
each
for
Jose
and
COEs
a
that
is
all
it
does.
It
registers
identifiers
for
the
curve
and
signatures
using
that
curve
for
the
sec,
P
256
K,
one
algorithm
that,
among
other
things,
was
described
by
Dan,
Brown
and
sort
of
calm
in
the
sec
to
publication
that
a
number
of
you
are
familiar
with.
This
algorithm
is
used
by
by
no
uif
the
w3c
verifiable
claims
interest
group
several
blockchain
projects,
and
my
goal
is
pretty
simple
right
now.
L
Those
of
you
who
are
familiar
with
cozy
and
The
Associated
Ayane
registration
procedures
will
recognize
that
for
the
very
small
integers
in
the
24
23
range,
those
are
what's
called
standards
action
required,
meaning
that
only
an
RFC
can
do
that,
because
this
is
an
algorithm
that
will
be
commonly
used
for
a
lot
of
particular
kinds
of
projects.
I
was
seeking
a
path
to
make
this
an
RFC
so
that
the
cosy
integers
can
be
small
ones.
Now
Ecco
did
point
out
an
alternative
which
is
rather
than
using
an
RFC
to
register
this.
L
We
could
change
the
registration
procedures
for
cosy
and
let
it
be
document
required
and
leave
it
up
to
the
designated
experts,
whether
the
particular
assignment
and
their
arts
use
of
the
small
integers
or
not.
It
turns
out
that
there's
a
current
precedent
for
this
there's
draft
ITF
TLS
Ayana
registry
updates,
which
lets
people
register
TLS
algorithms
I
think
without
becoming
without
using
an
RFC
in
some
cases.
L
So
the
backstory
quickly
is
I'd
asked
Ben
about
ad
sponsorship.
He
suggested
I
bring
it
to
our
new
sec
dispatch
working
group,
which
we've
done.
There's
been
discussion
on
the
list.
Michael
Richardson:
are
you
here,
Mike
volunteered
to
Shepherd
the
document?
Hopefully
Philipp
suggested
adding
a
table
of
cross
references
for
other
identifiers
for
this
algorithm,
including
oils
which
are
already
assigned
I,
said
that's
a
good
idea.
L
Eka
suggested
that
I
asked
the
CFR
G
for
feedback
on
the
curve
before
we
consider
taking
action.
Dan
brown
who
wrote
the
original
publication,
provided
a
pretty
useful
analysis
of
pros
and
cons
of
this
particular
curve.
My
layman's
interpretation
of
it
is
that
there's
no
known
practical
attacks
against
the
curves,
so
there's
not
a
security
reason
to
prohibit
its
use
as
a
process.
Point
I
will
point
out
that
this
will
not
be
the
last
such
draft
that
its
purpose
is
to
register
identifiers
for
algorithms.
L
Indeed,
the
reason
we
have
the
jose
algorithms
registry
in
the
cosy
algorithms
registry
is
exactly
so
that
you
can
keep
using
those
data
structures,
but
with
new
formats,
I'm
aware
of
some
work,
for
instance,
where
people
want
to
use
some
of
the
cha-cha
and
salsa
algorithms
and
assuming
they
pass
muster,
we
should
be
able
to
do
registrations
for
those.
My
draft
only
does
one
algorithm,
which
was
there
was
an
immediate
need
for
in
part,
because
some
projects
I
care
about,
are
currently
doing
ad
hoc
crypto
and
I'm
telling
them.
You
should
stop
doing
that.
L
It
seems
to
me,
like
some
of
the
choices
available
or
eighty
sponsorship,
which
would
be
expedient
and
ask
Mike
to
Shepherd
or
I
would
be
willing
to
write
the
draft
relaxing
the
rules,
in
which
case
the
w3c
could
just
publish
a
w3c
document
and
ask
IANA
to
do
the
registrations.
There
may
be
other
choices,
but
that's
all
I
had
to
say
in
background
rest.
L
V
If
the
area
directors
would
be
willing
to
take
on
the
third
bullet,
I
think
that's
the
best
way
forward,
so
that
we
have
roughly
the
same
bar
for
registering
TLS
algorithm.
We
ran
s/mime
algorithm
where
an
IPSec
network
on
a
cross
so
I
think
having
the
same,
you
know
you
must
be
this
tall
metric
across.
All
of
those
makes
the
best
sense.
Okay,.
W
W
R
So
Martin
Thomson
I
had
a
couple
of
questions,
I
thought
to
say
the
path
towards
something
like
the
ECB
AAA
stuff.
That's
used
in
flight
over
obviously
that's
completely
new
algorithm
that
has
some
utility
in
particular
context
and
we
don't
have
any
real
equivalent,
but
we
have
an
equivalent
here.
So
why
is
the
one
option?
Not
a
good
one,
just
for
my
gratification
that
it.
L
Has
in
my
mind
and
I'm,
not
an
expert
more
to
do
with
sociology
of
the
engineers
involved
and
their
belief
systems
than
particular
engineering
choices.
I
firmly
believe
I
will
not
be
able
to
dissuade
some
of
these
projects
to
move
off
of
these
algorithms
I
made
them
a
promise
that
I
would
attempt
to
let
them
use
standards
with
these
well
known.
Algorithms,
rather
than
have
them,
have
to
be
often
an
invented
land
that
has
no
real
peer
review.
So
I'm.
R
Trying
to
bring
them
near
the
fold
understood
that
is
a
fair
point
and
we
shouldn't
necessarily
now
forces
people
to
go
elsewhere
as
a
result,
but
we're
not
forcing
them
into
a
ghetto
we're
forcing
them
into
using
it
to
octet
encoding
for
their
identifiers,
rather
than
a
one
up
ten
encoding
for
their
identifiers.
How.
L
L
Particular
point
is,
you
know
debatable
whether
it
should
be
a
very
short
or
a
short
identify.
Er
and
I
could
personally
go
either
way.
I
wanted
to
be
able
to,
in
good
faith,
request
the
short
kind
to
the
designated
experts
and
leave
it
up
to
the
designated
experts.
What
to
actually
assign
if
I
don't
have
an
RFC,
then
their
hands
are
tied
about
whether
it
makes
sense
to
use
the
short
identifiers
or
not.
L
R
So
I
I
guess
my
point
here-
is
that
we
we've
done
a
lot
of
work
recently
to
sort
of
narrow
down
the
set
of
recommended
algorithms
that
we
use
in
protocols
and
support,
while
we're
not
in
the
in
the
business
of
telling
people
that
they
can't
use
algorithms
that
they
want
to
use.
And
obviously
we
are
not
going
to
go
off
and
persuade
people
in
the
blockchain
world.
I
like
well
like
using
that
word
it's
great
to
to
change
their
minds
about
with
what
it
is
that
they
use.
R
R
L
All
you
know
to
bring
these
people
into
the
fold
of
using
IETF
standards
for
cryptographic
representations.
It
is
sort
of
an
asterisk
on
the
side,
whether
we
do
the
work
to
let
it
be
a
short
identifier
or
a
medium-sized
identifier.
That
is
not
the
high
order
bit
the
higher
tab.
It
is
registering
identifiers
for
these
algorithms
so
that
people
will
start
using
Jose
and
arc
Jose
rather
than
ad-hoc
crypto
formats,
which
is
what's
actually
happening
so.
R
There's
a
number
of
points
that
I
was
trying
to
get
to
and
probably
should
try
to
pull
them
apart
a
little
bit.
I,
don't
think
this
needs
in
one
octet
identifier.
I
do
think
that
we
should
have
registration
policies
that
are
consistent
across
all
of
these
different
spaces,
because
we
they're
basically
the
same
things.
The
TLS
code
points
the
pickax
code
points.
What
Jose
Jose
code
points.
They
should
all
follow:
relatively
consistent
registration
policies.
Otherwise
we
create
some
weird
side
effects,
but.
G
G
In
the
three
anything
longer
is
expert
review
right
with
apparently
no
specification,
perhaps
right
so
I
guess
well,
I,
guess
well
I'm,
so
so
well,
I'm
gonna,
try
to
understand
is
it
seems
to
me
like
if
they
wanted
to,
but
identifier.
Why
can't
they
have
that
right
now
without
doing
nothing.
This
is
Beth.
This
is
the
specification
required
to
say
it
has
to
be
an
RFC,
so
so
so
and.
L
G
G
L
L
O
G
G
Why
was
I
Anna?
Why
were
you
able
to
do?
Why?
Wouldn't
you
do
a
right?
Why
we
were,
you
know,
update
the
registry
with
a
draft.
That's
the
part
I'm
confused
about
what
are
the
rules
now
say
say:
specification
required
right,
so
those
that
would
incorporate
that's
the
point
of
not
like
I'm,
not
I,
feel
I'm,
not
sure,
there's
I
think
I
can't.
B
Standards:
action.
Sorry,
if
I
want
a
to
by
its
specification
required
anyone
specification,
w3c
or
otherwise.
If
I
do
three
byte.
That
means
I
need
expert
review.
So
I
think
the
question
is
again:
I'm
correct
me:
if
I'm
not
getting
it
wrong
option
number
three
says:
we
need
to
change
how
we
do
registration
encoding.
That
means
governing
one
byte
things
as
well,
because
I
get
that
already
with
two
byte
and
effectively
three
but
correct
correct.
G
G
Suggested
number
thought
I
think
I
did
III,
guess
quite
possibly
I
guess.
I
meant
quite
appreciate
this
V
this
one
versus
two
byte
issue,
I
mean
I.
Guess,
like
my
personal
view,
I
guess
that's
what
I'm
wearing
right
now
but
I'll
try
to
talk
anyway
on
is
like
I.
Don't
know
how
scarce
these
one
weight.
Identifiers
really
are.
If
you're
like
super
scarce,
then
like
then,
probably
it
lines
up
with
the
recommended
column,
which
case
you
shouldn't
be
allowed
to
get
one
without
be
without
recommended.
G
R
So
Martin
Thompson
just
to
Mike's
point
there
there
are.
There
are
48
of
them
why
they
decided
that
negative
identifies
was
a
good
idea,
is
completely
escape
to
me,
but
there
are
48
of
them,
but
the
registration
policy
for
standards,
action
required
extended
to
minus
256
and
positive
to
255
from
Murray.
