►
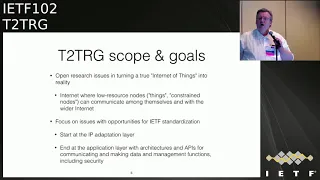
From YouTube: IETF102-T2TRG-20180719-1550
Description
T2TRG meeting session at IETF102
2018/07/19 1550
https://datatracker.ietf.org/meeting/102/proceedings/
A
A
A
Okay
and,
of
course,
now
it's
a
waiting
list
and,
most
importantly,
there
is
a
github
repository
for
every
meeting
of
research
month
in
any
form,
we
have
a
github
repository
so
in
that
you
to
TIG
organization
that
Nestor
2018
I
actually
have
one
or
two,
and
then
you
find
point
us
through
slides
and
to
the
note-taker
in
a
paired
and
things
like
that.
So
who's
doing
the
double
thing:
I'm,
not
sure
that
we
will
need
that.
What
we
got
to
have
it.
B
A
One
segment
next
steps
in
security
and
read
up
at
hopefully
end
by
5:15.
So
what
is
this
next
step?
In
security
thing,
we
asked
a
number
of
people
to
give
a
quick
personal
point
of
view
of
what
we
should
be
doing
next,
where
we
might
be
for
the
research
community
that
is
interested
in
energy
security
in
general.
B
A
C
C
A
D
A
A
When
we
get
our
activities
this
week,
some
of
these
are
pretty
pedestrian,
which
doesn't
change
the
fact
that
it's
not
something
where
you
just
sit
down
and
interview.
You
have
to
think
about
the
problem
and
maybe
try
something
and
measure
something
before
you
have
fun
with
the
right
answer,
and
one
of
these
references
is
given
that
we
now
have.
A
The
next
question
is:
how
do
we
get
all
this
legacy?
Information
that
is
in
some
binary
blobs
from
us
and
get
these
data
over
intuitive?
It
will
not
deliver
that
we
enjoy,
or
with
formats
like
Jason
and
Zeebo,
and
how
can
we
do
this
in
a
way
that
it's
maintainable
and
people
can
vacation
it's
kind
of
like
what
we
do
like
CBB.
A
A
So
maybe
this
is
something
that
most
of
all
most
of
us
think
we
understand,
but
we
can
generate
a
good
example
for
misbehaving
like
chains
around
or
something
that
is
seems
to
be
trivial,
but
in
realism.
So
that
would
be
something
that
is
some
effort
working
things
and
competing
it.
Maybe
not
not
classical
research
paper
or
something
like.
A
The
third
thing
we
noticed
is
we
have
this
large
set
of
description
techniques
out
there,
but
it's
not
always
clear
how
these
disruption
techniques
handle
protocol
evolution.
So
how
do
you
describe
something?
That's
changing
so
yesterday
when
we
talked
about
the
if
some
data
model
or
we
started
discussing,
there
might
be
different
versions
of
the
episode
81
and
and
how
does
that
work
right
now?
A
The
description
technique
does
not
enable
describing
that
evolution
and
that's
not
a
problem
that
is
unique
to
leave
some
words,
but
we
need
to
understand
particle
evolution
and
we
need
to
enable
it
as
much
as
possible,
because
the
way
Garage
us
does
change
okay.
So
these
are
three
examples
for
activities
we
might
be
picking
up,
but
of
course
brings
in,
for
that
is
that
we
have
people
who
are
interested.
Yes,
it's.
A
Like
Austin,
thank
you
no
Robin
Wilton,
looking
at
your
second
one,
their
semantics
of
state
over
an
operations
on
a
light
and
I
think
you're.
Absolutely
right.
These
things
may
seem
simple,
but
when
you
walk
them
through,
they
really
aren't,
and
that
example,
in
particular
resonates
with
me,
because
I
often
use
that
as
an
example
when
talking
about
the
privacy
implications
of
IOT
and
the
reason
I
use
it
as
an
example
is
a
mental
model
for
what
the
light
does
is
that
the
user
interface
is
binary,
it's
either
on
or
off.
A
So
what
you've
described
is
the
stuff
that
is
not
accept,
not
accessible
or
visible
to
the
user
is
actually
much
more
complicated
than
that
users
model
of
what
is
happening
and
I
think
there's
a
privacy
gap
there,
which
can
give
rise
to
the
opportunity
for
things
to
happen.
That
the
user
did
not
legitimately
expect,
and
so
I
don't
know
if
it
would
work
as
a
security
considerations.
Part
of
that
research,
but
I,
think
that
would
be
a
really
good
adjunct
to
it.
A
A
Monthly,
we
will
continue
our
virtual
meetings
with
ocf
and
possibly
another
face-to-face,
or
we
will
start
having
virtual
meetings
with
only
spec
works
from
the
people
known
for
a
live
reading
to
image
and
the
next
ITF.
We
probably
will
have
some
activities
and
to
one
of
them
like
a
next
round
of
the
wishing
Epiphone
but
another
one
might
be
to
go
a
little
or
let
such
networks
and
talk
about
all
things
that
are
sometimes
called
in
computing
or
in
network
or
computing.
A
A
A
A
B
A
B
A
B
A
A
A
A
E
A
So
wishy
a
salesperson,
so
the
work
on
society,
semantics
and
hypermedia
and
our
ability
we
have
teleconferences
between
IETF
meetings
and
we
have
significant
ability,
hands-on
testing
and
more
recently,
some
breakout
sessions,
I
think
any
T
of
hackathons.
The
last
some
of
the
topics
that
we've
been
covering
in
the
meetings
are
related
to
planning
for
the
hackathons,
as
well
as
exploring
the
general
space
around
requirement
zones
and
various
solutions
and.
A
A
B
A
We
recently
looked
at
how
we
apply
IRT
schema.org
to
episode,
and
we
don't
involve-
and
we
recently
were
there's
a
lot
of
us
is
repeating
on
Carson
ders
said
we're
working
with
ocf
when
we
lightweight
him
to
him,
but
the
previous
bloodfest.
We
had
some
work
with
Jimmy
being
VSS,
which
is
a
automotive
specification
that
talks
about.
A
Different
vehicle
information
systems
there,
of
course,
one
of
things
in
IRT
schema.org
and
for
the
rest
of
this,
is
a
little
bit
of
a
description
of
what
those
last
year.
Things
are
thing
description,
link
description
is
a
file
format
and
an
area
of
media
type
that
describes
the
abstract
interactions
with
things
such
as
how
do
I
read
temperature
lock
the
door
or
change.
A
Those
interactions
so
defines
the
payload
structure
that
you
are
either
for
the
addresses
where
you
go.
How
are
you
operate
the
transformer
and
they
want
the
data
characteristics,
look
like
coming
back
and
so
using
the
description.
Applications
can
use
the
abstract
interactions
to
sort
of
start,
decoupling
from
the
underlying
implementations
and
start
providing
an
abstract
interaction,
application
layer
and,
ultimately,
you
want
to
be
able
to
automatically
adapt
to
all
the
specifics
of
the
device
protocols
and
data
formats.
We
only.
B
A
Welty
schema.org
is
an
external
vocabulary
that
we
use
to
annotate
instances
of
the
descriptions
or
other
general
hyper
media
controls,
metadata
comedians,
really
in
any
any
metadata
framework.
We
have
some
high-level
semantic
categories
to
annotate
systems
at
different
layers.
We
can
imitate
our
local
capabilities,
we
can
annotate
interactions
and
we
can
annotate.
B
A
B
A
Etc,
things
that
we
might
be
seeing
in
the
future,
so
this
weekend
we
had
a
hackathon
and
we
we
wanted
to
mean
basically
what
we
do
is
we
test
the
open
operability
mechanisms
in
a
real
system
humans
and
make
simulators
when
we
try
to
innovate,
operate
across
the
teams
and
across
the
contributors
and
I'll
try
to
operate
some
device
that
someone
else
brought
and
someone
else.
We
have
an
application,
then
tries
to
interoperate
with
the
device
that
I
brought.
A
D
A
C
A
Internet
and
local
network
cube
and
then
w3c
provides
a
number
of
components.
Analysts
know
there's
some
color,
you
can
see
a
color,
so
there
are
a
couple
of
components:
node
wallet
and
cane
directory
that
can
be
used
to
fill
those
roles.
But
you
know
other
other
components
can
be
used
as
well
as
as
well
and
gives
us
an
idea
of
what
we've
been
working
with
in
terms
of
the
different
formats.
B
A
So
we
had
on
your
ipython
are
basically
looking
at.
How
do
we
map
Epsilon,
lightweight
m2m,
to
abstract
models,
use
anything
description
on
your
test
email?
How
do
we
in
that
blue
CF
the
same
way?
How
can
we
build
an
Arg,
a
resource,
a
core
resource
directory
implementation
that
can
be
used
for
semantically,
pepin
and
higher
layers
than
just
the
current
our
game?
B
A
More
decoupled
and
where
again,
the
demo
system
integration,
but
some
of
the
results
we
did
have
a
good
breakout
discussion
leave
some
some
topics
collected
from
that
we
did
demonstrate
in
an
operation
between
clients
and
different
devices.
We
disclose
24
issues
with
no
bottom
and
move
that
over
to
eclipse
foundation.
So.
A
A
Say-
and
we
got
the
Rd
person
what
they
are,
the
implementation
up
to
speed
and
we're
ready
to
start
moving
out
a
thing
directory
based
on
order,
B
again
like
this
again,
because
it's
so
cool
they
just
automatically
interoperate
with
collab,
DTLS,
new
handshake
and
everything
and
we're
working
on
a
report
for
that.
So
the
breakout
topics
were
sort
of
again.
How
do
we
attach
models
to
existing
instances
of
descriptive
data,
so
this
is
sort
of
like
the
thing
description
problem
about
a
little
more
generic
than
that?
A
What's
what's
the
general
of
the
general
issues
in
these
cases
for
doing
that,
on
the
topic
of
shared
models
across
devices
or
systems
like
we
built
some
shared
models
that
work
well
for
different
targets,
high
level
semantics
opinion
I
mentioned
that
this
is
the
idea
of
not
noon,
to
use
the
addresses
but
being
able
to
operate
devices
based
on
their
semantics.
Only
we
work
on
mapping
in
description
to
form
each
we're.
Not
we
have
some
some
oh
I've
been
discovering.
A
A
A
A
We
might
start
thinking
about
modeling
internal
behavior
of
things,
and
you
know
so
we
send
a
command
to
something
and
we
get
a
response,
but
you
know
what
is
what
does
that
really
mean
if
I
find
an
IOT
application?
I
might
want
to
know
a
little
bit
more
about
what
I'm
actually
doing
and
then
logistically
we
found
that
there's
still
a
big
issue
in
the
setup
time.
We
need
to
figure
out
how
to
streamline
things
and
get
everything.
B
A
A
I
hope
they
schema.org.
This
is
this
is
basically
we
we've
got
about
one
year
of
experience
with
this,
since
the
Vichy
workshop,
we're
validating
the
basic
categories
and
the
annotation
style
by
using
thing
description,
we've
been
using
it
in
several
plugfest
when,
where
she
hackathons
there
are
twenty
or
thirty
experimental
definitions
in.
A
A
A
To
achieve
this
being
complimentary,
you
do
not
prescribe
the
full
stack
solution.
This
is
how
you
have
to
build
everything
from
now
on,
but
we
provide
a
set
of
building
blocks
that
people
can
pick
to
solve
existing
problems
that
we
have-
and
you
already
heard
the
key
word
in
description
a
few
times
in
the
previous
work.
So
this
is
something
that
can
be
picked
up
by
any
other
ecosystem
if
they
want
to
be
accessible
from
from
other
ecosystems
across
application
domains
and
so
on.
What
building
blocks
to
do?
We
standardized
at
the
moment.
A
So
if
you
look
at
the
generic
IOT
system-
and
it
usually
has
a
stack
something
like
this-
the
central
building
block
is
this
fing
description.
So,
overall
it's
a
JSON
based
representation
format
that
can
describe
instances
of
things
and
through
a
formal
interaction
model,
so
it
kind
of
improves
over
beta
models
or
information
models
that
might
be
kind
of
implicit
in
the
ecosystems
and
again
give
some
semantic
meaning
to
it.
So
it's
not
only
what
data
is
provided,
but
also
how
do
I
get
it?
How
do
I
modify
it
and
so
on?
A
Overall,
you
can
think
about
the
famous
captions
a
bit
like
it's
the
index
index.html
for
things,
and
this
interaction
model
is
built
around
the
FIFO
of
properties,
actions
and
events
which
comes
a
bit
from
the
programming
model.
So
it
should
be
easier
for
the
way
you
build
applications
or
it's
and
from
the
programming
abstractions,
because
it's
about
building
applications,
the
second
building
block
binding
template.
So
here
the
idea
is
that
you
look
at
the
specific
ecosystem,
so,
for
instance,
ocf
you
capture.
A
What
are
the
specifics
that
you
have
to
go
to
to
know
about
so
what?
For
instance,
it
uses
co-op
okay,
but
it's
not
interoperable
with
lightweight
and
plan,
because
you
have
to
know
which
methods
are
used
for
specific
interactions.
You
have
to
know
what
special
headers
or
what
special
options
have
to
go
in
there
and
this
we
capture
in
these
templates
and
then,
if
you
want
to
write
the
things
between
for
a
certain
device
from
an
ecosystem,
you
look
at
the
template
R.
This
is
what
they
do.
A
This
is
how
I
describe
it
in
a
Finglas
kitchen
and
ya
can
easily
then
provide
information
for
such
an
ecosystem
and
the
last
one
is
the
scripting
API.
Think
of
this,
like
the
browser,
so
it's
a
runtime
for
applications
or
the
here.
The
focus
is
not
on
a
user
interface,
but
on
a
faceless
runtime,
where
you
can
deploy
our
key
applications
that
do
the
automation
for
you
and
we
define
kind
of
a
small
basic
API
that
can
be
extended
later,
for
instance,
the
semantic
API
that,
like
the
cost
I
mentioned
earlier,
I
think
of
it.
A
This
is
like
the
browser
API,
and
on
top
you
can
build
something
like
jQuery
that
has
done
all
the
fancy
functionality
over
all.
We
also
include
security,
so
in
the
working
group
we
do
not
define
any
new
security
mechanisms
or
whatsoever,
but
we
define
some
vocabulary
so
that
we
can
specify
what
security
mechanism
is
used
and
how
is
it
configured
about
parameters?
Do
I
need
to
know
about
so
basically
to
make
it
easy
to
give
all
the
information
to
a
client,
so
it
becomes
able
to
interact
with
with
an
existing
device
good.
A
Let's
have
a
look
at
the
timeline,
so
this
picture
already
shows
that
we
are
quite
progressed
so
overall,
the
activity
is
that
around
2014
interest
group
work
started
in
2015.
The
first
two
years
were
mainly
spend
on
bringing
the
different
people
from
the
different
backgrounds
on
the
same
page,
to
get
a
common
understanding
without.
A
The
implications
of
that
are
now
that
we
could
make
the
semantic
annotations
for
the
optional.
So,
basically,
you
can
now
use
finger
scriptures
without
any
knowledge
about
a
json-ld.
It
just
looks
normal
to
you.
Of
course
you
don't
have
done
these
semantic
annotations
in
there,
but
you
can
still
programmatically
build
something
that
can
consume
these
description
into
the
right
thing.
This
implicit
knowledge
main
is
made
explicit
by
using
a
specific
media
type
for
that,
so
we
want
to
allocate
application
td+
Jason
for
that,
and
if
you
receive
something
with
that,
the
jason
of
the
context.
A
So
that
is
the
the
external
side
it
gives
meaning
to
all
the
keywords
that
you
use
in
in
adjacent
document
yet
is
derived
from
that
media
type.
And
so
you
don't
need
the
special
gaze
near
the
keywords
anymore,
and
we
are
also
losing
a
bit
the
convention,
so
that
feeds
more
what
web
developers
expected
some
other
changes
and
we
could
also
make
a
compatibility
with
json
schema
before
we
use
the
terminology
from
from
that
draft,
but
had
the
different
syntax.
A
Now
those
can
actually
be
aligned
so
that
you
pick
out
the
data
schema
definitions,
feed
introduces,
email,
validator
and
it
will
work
out
of
the
box.
It's
a
nice
combination
of
these
these
different
through
chains
and
some
other
things
are
kind
of
housekeeping.
So
we
looked
into
what
are
the
terms
that
he
actually
needed
to
make
this
productive.
A
E
E
A
That's
how
I
started
out
with
this
light,
so
it's
not
as
bad
as
this
anyhow.
So
this
is
for
the
fingers
kitchen
and
they
were
also
following
up
changes
to
the
scripting
API
and
it
turned
out
quite
nicely
because
now,
basically,
the
software
object
of
the
thing
that
you
would
instantiate
in
your
scripting
environment
is
basically
adjacent
parts
of
the
fing
description
and
augmented
with
some
functions.
That
will
do
that.
The
network
operations
for
you.
A
So
it's
really
easy
for
them
from
your
script,
to
do
introspection
and
figure
out
the
metadata
of
the
yeah
thing
itself,
the
interactions
that
are
provided
and
so
on
again.
This
is
for
you
to
study
at
home,
okay.
So
what
is
left
to
do
until
we
release
for
the
fingers
kitchen-
and
there
is
one
issue
that
came
up
pretty
late-
is
that
people
wanted
to
have
good
support
for
these
read
or
write,
multiple
interactions
that
are
quite
common
in
industrial
systems
and
but
also
quite
often
used
in
web
UIs.
A
For
instance,
when
you
want
to
display
something,
and
of
course,
although
the
field
should
be
populated,
it's
also
bit
related
to
the
trend
of
graph
QL,
for
instance,
where
you
want
to
reduce
round
trips
and
get
all
the
information
you
want
to
display
at
a
time.
We
want
to
revisit
the
event
model,
because
some
of
the
existing
ecosystems
have
also
input
data
on
subscription,
so
that
you,
for
instance,
can
install
theatres
that
you
are
notified
only
under
certain
conditions,
and
that
was
not
possible.
A
Good
and
then
you
finish
up
with
some
Yanna
considerations
of
an
instance,
I
mentioned
the
media
tab
you
want
to
allocate
for
the
finger
scription,
then
for
the
scripting
API.
We
want,
of
course,
then,
to
handle
food.
How
to
model
this.
We
tried
multiple,
we
have
two
finalists
or
the
discovery
codes
and
what
is
so
far
open
is
to
define
how
arrows
should
be
flown
or
whatever
the
error
modeling
within
the
API
works
and
for
the
binding
templates
they
are
pretty
far.
A
So
that
means
at
the
moment
we
just
described
kind
of
these
classic
systems
where
you
send
a
request,
and
you
will
get
an
answer
and
but
we
see
the
need
that
if
you
want
to
continue
here
and
really
apply,
for
instance,
these
restful
design
guidelines
that
we
also
discuss
in
the
research
group
here
and
there
should
be
something
yeah-
that
we,
for
instance,
invoke
connection
and
receive
something
that
it
guides
us
for
more
complex
process,
so
that
the
response
again
has
some
hypermedia
controls
that
tell
us
yeah.
You
have
to
wait
that
long.
A
Now
you
have
to
go
there
and
now
you
have
to
submit
this
form
to
go
to
the
next
step
of
the
process
and
yeah.
For
this
we
want
to
define
just
the
extension
point
because
it
actually
goes
beyond
our
original
mission
of
just
be
describing
the.
This
is
something
that
doesn't
really
exist
in
existing
ecosystems
out
there.
So
this
has
been
probably
something
for
the
new
retarted
working
group
that
will
start
on
yeah
second
quarter
of
next
year,
hopefully,
and
security
and
privacy.
A
We
also
have
to
finalize
the
test
cases
and
provide
a
test
suite
for
our
definitions
here,
so
that
we
can
then
actually
go
into
the
face
of
the
w3c
process
or
for
one
sole
candidate
recommendation.
Is
there
you
have
to
go
through
the
test
Suites
and
have
to
prove
that
there
are
two
independent
implementations
that
basically
have
the
full
coverage
and
they
are
interoperable
good.
A
A
Anyone
awake
questions,
good
good,
thank
you
ideas
and
as
a
reminder
for
everyone.
If
you're
interested
in
the
hypermedia
and
semantics
work,
please
join
the
we.
She
calls
and
hackathons
and
there's
always
information
when
we're
thinking,
research,
mailing
lists
and
also
in
in
our
github
and
other
logistics
of
them.
G
D
B
So
this
is
how
to
my
did
the
IOT
security
and
that's
internet
draft
at
very
early
version,
that
is
to
with
tor
stand
up
from
Google,
and
so,
if
you
go
to
the
next
slide
yeah,
so
we
have
this
internet
draft
with
overview
of
the
IOT
security,
and
there
is.
There
are
many
issues
over
there.
But
the
issue
that
we
are
trying
to
address
here
is
mismatch
between
basically
the
security
capabilities
of
the
devices
when
they
are
designed
manufactured
the
deploy
yeah.
B
So
it
happens
that
when
you
manufacture
a
device,
maybe
it
ends
having
some
security
protocols
or
settings
and
when
it's
actually
deploy.
Maybe
the
environment
is
completely
different
and
then
different
security
protocols
are
required
or
settings
and
may
also
be
that
there
are
Pune
ratings,
and
then
you
don't
have
a
way
to
reduce
ones
also
what
they
both
a
second
bullet
says
is
that
well
the
requirements
evolve
over
time
and
we
don't
have
means
basically
to
adjust
the
security
settings.
B
Yeah,
so
we
put
here
three
problems
and
the
first
one
is
well:
if
you
have
the
device
yeah,
a
device
that
you
might
use
in
a
home
or
an
office
or
in
the
permanent
fence.
Obviously
the
security
requirements
are
quite
different,
and
even
if
you
have
a
document
that
gives
a
guidelines
of
security,
this
happens
and
sometimes
those
guidelines
are
not
follow.
And
then
what
do
you
do?
B
The
second
one
is
that
you
have
a
ball
with
threads,
somehow
hands
become
insecure
and
then
what
happens?
If
you
have
a
network
with
yeah
in
some
of
those
devices,
you
have
a
line
that
is
not
completely
secure.
How
can
you
make
sure
that
that
device
it
was
not
compromised,
not
are
stealing
keys
or
that
in
some
devices,
then
there
are
bugs
and
then
are
used
by
an
attacker
to
compromise
the
device,
or
maybe
also
that
if
you
have
a
home
environment
that
the
users
change
their
preferences,
it
may
be
a
privacy
wise.
B
So
that
was
a
compromise
or
one
is
that?
Well,
sometimes,
if
you
yes
manufacture
devices,
and
then
you
put
them
in
the
field
with
some
conflation,
maybe
that
also
adapted
I'm
there
also
arrows
could
also
happen.
Maybe
is
not
known
that
the
protocol
is
to
be
disabled,
or
maybe
a
developer
does
not
remove
all
the
code
that
that
should
be
remove,
or
maybe
the
documentation
does
not
state
that
a
specific
protocol
acini,
and
so
these
are
problems
that
the
well
are
talking
just
about
a
fix.
B
The
setting
and
the
question
is
how
to
automate
security
to
deal
with
this
week.
Setting
can
you
go
to
the
next
slide,
so
in
the
draft
again,
as
I
said
this
very
first
idea,
we
have
three
parts.
The
first
one
is.
We
just
give
examples
of
security,
threats
and
mitigation
strategies
just
thinking.
Well,
if
you
have
this
threat,
then
I
do
a
type
of
mitigation
strategy.
B
Then
the
second
part
is,
we
call
it
a
speculative
framework
to
include
a
race
community
attendant
processes
in
the
lifecycle
of
a
of
a
device.
So
you
just
think
that
you've
settled
to
the
resources
meant
at
the
beginning,
when
you
are
designing
the
product
that
you
can
do
the
results
meant
in
the
specific
environment
where
the
device
is
deployed.
B
I
will
explain
this
later
and
the
third
part
and
you
go
to
the
next
slide,
it's
about
security
profiles
and
that's
something
that
was
the
very
first
versions
of
the
truffle
security
considerations
for
IT
and
the
basic
idea
that
you
can
configure
devices
with
different
security
profiles.
The
basic
idea
is,
depending
on
the
environment,
where
the
device
is
deployed
and
depending
on
ressentiment,
that
you
come
to
for
that
specific
Garmin,
you
can
deploy
a
security
profile
or,
depending
on
a
so
the
overview
of
the
draft.
B
Can
you
go
to
areas
like
yeah,
so
there
are
two
main
protocols:
the
idea
to
develop
those
protocols,
and
we
would
like
to
get
feedback
on
this.
The
first
one
is
called
automatic
security
confirmation
and
the
VAS
idea
is
well.
If
you
look
at
the
picture,
the
current
practice
to
perform
a
reason,
segment
or
privacy
impact
analysis
when
you
are
designing
the
product
and
then
later
the
thing
is
deployed,
and
maybe
the
security
that
you
cover
does
not
fit
the
specific
environment.
B
So
the
basic
idea
to
a
Hafidh
protocol
that
once
the
device
has
been
deployed,
you
can
actually
perform
resources
meant
in
the
field
and
then
based
on
those
the
risk
assessment.
Then
you
can
deploy
configure
a
security
profile
for
the
smart
objects
in
that
environment
and
next
slide.
Please
so
a
very
high
level
study
of
this
protocol
that
will
be
taking
place
exactly
where
the
figure
indicates.
B
Basically,
information
also
of
the
specific
preferences
of
users
in
that
environment
can
perform
a
risk
assessment,
basically
determining
potential
threats
for
that
device
or
on
the
device
and
basically
determines
the
security
profile
for
the
device,
but
also
for
other
devices
in
the
moment,
and
this
is
modeling,
what
makes
it
perform
will
deploy
to
security
profiles
on
the
devices
in
the
market.
So
this
was
a
great
idea.
B
Instead
of
just
opening
it
to
first
on
your
home,
a
specific
device
with
a
specific
configuration
and
not
being
able
to
do
anything,
yeah
put
in
possibly
the
apparatus
to
add
your
security
added
after
the
implement
phase.
So
that
was
again
the
idea
in
here
and
then
a
second
protocol
that
we
have
in
mind.
Can
you
go
to
the
next
slide?
Please
it's
called
a
Papa,
so
it's
a
protocol
for
automatic
vulnerability
assessment
and
the
current
practice
is
what
you
have
smart
home,
and
maybe
there
is
a
goon
or
a
teen
specific
device.
B
B
B
If
you
want
to
annex
like
so
the
big
high-level
idea
of
this
protocol,
that
is
the
less
described
on
the
previous
one
in
turn
a
trap.
So
for
sure,
if
they
are
these
interesting
drifts,
there
lots
of
work
to
do
and
the
thing
will
send
standard
reports
of
potential
to
neurotic
to
the
gateway.
First,
us
be
a
syslog,
the
Gateway
can
analyze
those
reports,
and
these
are
regarding
assistance
of
a
polarity.
B
So
is
basically
the
idea
of
the
protocol
and
if
you
go
to
the
next
latinus
this
my
last
one.
So
we
believe
that
these
make
sense
because
of
three
things
the
first
one
is
for
manufactures.
They
don't
need
to
decide
with
security
mitigation
or
require
this
I'll
point
or
visually.
This
has
also
constraints
right
limitations
and
you
have
to
describe
the
usage
how
the
fields
will
be
used
for
system
operators,
minimizes
operational
cost,
while
ensuring
the
system
remains
secure
at
any
moment,
and
it
enables
automation
of
a
security
and
for
the
users
publicly.
B
B
A
B
B
D
From
where
it
should
get
commands,
but
it's
it's
a
problem
that
needs
to
be
solved.
So
there's
there's
two
parts:
you
need
identifiers
and
credentials
for
first
connecting
to
the
network,
which
would
give
you
access
to
the
Internet,
and
then
you
need
to
connect
to
the
cloud
from
from
where
you
get
your
updates
on
some
commands.
D
D
Bringing
this
to
the
device
is
challenging
for
very
many
reasons,
but
one
reason
is,
of
course
they
have
limited
user
interface
and
then
you
know
if
at
home,
I
have
like
two
or
three
laptops
and
phones
right
now,
connected
or
even
in
office.
I
mean
this.
We
are
just
going
to
see
many
more
of
these
devices,
so
scalability
is
also
a
challenge
and
of
course,
you
and
I
probably
have
some
clue
about
SSID
secrets.
Passphrase
boring,
but
maybe
not
not.
Everyone
has
the
same
same
level
of
scale,
so
it
should.
D
D
This
is
just
peering
phone
with
the
printer
or
some
some
simple
pressing
buttons.
What
some
some
people
would
call
as
Wi-Fi
unprotected
setup,
and
then
we
have
the
more
managed
solutions,
such
as
radius,
diameter,
802,
1x
and
all
the
vendor
and
enterprise
certificates.
So
these
are
typically
something
that
you
will
see
in
a
small
small
office
and
and
enterprise
deployments,
but
I
think
as
as
the
number
of
devices
K,
and
this
is
something
you
might
even
move
to
home
networks,
because
just
having
the
same
key,
when
you
have
100
devices
at
home,
won't
won't
work.
D
D
So
the
next
few
slides
that
I
have
is
just
some
example
deployment
models
of
how
this
could
work.
So
we
can
never
agree
on
what
each
vendor
is
going
to
use
for
authenticating
their
devices,
but
I
am
hoping
if
they
use
some
form
of
EEP
method,
I,
don't
care
whether
it's
TLS
or
HP,
SK
or
whatever
method
they
want
to
use.
But
the
good
thing
about
it
is
that
it
can
make
sure
that
there
is
four
device
credentials.
D
So
for
those
of
you
who
are
familiar
with
a
band
network
access,
identifiers
and
radius
peering,
what
I
would
do
is
do
peering
between
between
the
access
point
and
and
the
device
vendor,
and
basically
the
idea
would
be
that
any
authentication
requests
that
come
from
vendor
a
will
go
to
that
vendor.
That
vendor
would
authenticate
using
some
request
response
messages
and
then
enable
internet
access
for
this
device.
D
So
you
know
this
is
for
one
one
IOT
device,
but
if
you
have
a
vendor
B,
so
if
I
have
a
Philips
light
bulb,
it
could
go
to
the
Philips
server
authenticate
and
then
enable
internet
access
for
that
device.
And
again,
the
important
point
is:
is
the
working
group
interested
in
some
deployment
scenarios
like
this
I?
Don't
think
we
have?
The
energy
have
one
uniform
eat
matter
for
all
of
them,
because
we.
D
So
here's
another
deployment
model
which
might
happen
in
a
more
enterprise
scenario
so,
instead
of
having
you
know
the
triple
ace
over
in
the
access
point,
most
enterprises
already
have
a
local
triple-a,
and
this
local
triple-a
can
also
be
in
being
the
flower.
This
is
just
a
example,
but
then
the
peering
would
would
be
more
simpler.
You
will
have
a
network
administrator
who
would
set
up
disappearing,
so
the
idea
would
be
then
forward
from.
F
A
You
that
the
basic
idea,
kind
of
works-
or
we
know
from
a
very
large
Federation,
called
you
that
doesn't
work
at
this
meeting
site
for
some
reason
or
no,
but
of
course
the
main
substance
of
any
one
is
that
you
have
this
contract
that
made
the
Federation.
So
maybe
that
that's
part
of
the
examination
thinking
worse,
what
is
actually
the
legal
framework
that
would
make
something
like
this
work.
A
F
D
So
I
think
what
I
was
suggesting
is
how
do
you
redirect
at
an
authentication
grettings
from
from
one
IOT
device
vendor
to
that
vendor
service?
If
you
want
to
run
a
competing
service-
and
we
direct
your
queries
to
to
these
competing
surveys,
that's
fine.
So
this
would
still
allow
that
I.
Don't
think
we
we
need
to
stop
that
I'm
I'm,
all
for
it.
I.
D
Shouldn't
have
lived
this
Mike.
This
actually
helps
you
in
that
case,
so,
instead
of
now
directing
queries
to
that
vendor,
if
you
want
to
direct
your
queries
to
somewhere
else
yeah,
this
is
this
is
a
big
question
who
would
be
interested
in
running
such
as
always,
but
if
there
is
some
open
source
community
that
wants
to
do
it
and
we
have
seen
it
in
two
cases,
so
nowhere.
D
Signage
in
mode
and
with
with
access
points,
we
have
open
wrt.
So
we
have
seen
two
examples
or
consortiums
come
in
and
you
can
flash
your
devices
on
hoping
if
your
manufacturer
runs
out-
and
you
don't
want-
or
for
some
reason
you
don't
want
to
use
their
authentication
service.
This
deployment
mode
will
still
allow
you
to
redirect
queries
to
some
other
service.
So
the
important
thing
to
note
is
the
peering
here,
so
you
can
cure
it
with
some
other
service
of
your
choice.
A
Elaborate
a
little
next
steps
in
security,
which
is
a
little
bit
a
very
hard
question
to
answer,
but
I
do
focus
really
on
crypto
aspects,
because
lots
of
people
are
right
off
about
authorization
issues.
So
so
this
is
how
I
see
a
device
and
there's
a
bunch
of
keys.
It
has
song
like
crypto
algorithms
on
it,
and
then
it
has
some
functionality
on
top
to
invoke
these
functions
and
to
manage
it
and
the
security
policies
and
I.
A
A
Is
that
that
may
actually
conflict
the
need
for
cryptography,
because
people
guilty
means
that
you
may
be
able
to
switch
one
algorithm
suite
for
none
of
them
and
it
could
feel
perfect.
The
single
function
for
each
task,
and
so
I
will
go
through
some
aspects
of
some
things
that
I
in
this
big
rectangular
box
over
here.
So
first
keys.
H
C
B
A
B
A
D
A
A
A
I
was
just
saying:
I
just
need
recently
a
webinar
on
on
the
orangey
topic
and
I
just
went
to
to
see
how
uncommon
or
common
orangey
hardware-based
running
the
my
generators
is
in
my
controller
I
MSU
finder
from
STMicroelectronics,
which
is
allows
the
easy
way
to
cure
all
the
devices,
including
searching
for
different
devices,
and
it
turns
out
even
SD
micro.
Electronic
alone
has
more
than
400
low
and
microcontrollers
that
half
an
orangy
in
support
India,
which
I
thought.
A
A
A
A
A
A
A
A
A
A
C
Hello,
catch
pain
and
CSE
slow
and
a
couple
of
comments
on
your
post
quantum
section
that
you're
just
talking
about
so
the
aes-256
pretty
standard,
so
subjective,
Grover's
algorithm.
That
still
would
give
you
one
to
eight
bits
of
security,
yes
being
quite
lightweight,
that's
just
something
that
I
think
would
be
fine
and
with
public
key
crypto.
You
saying
thinking
outside
the
box
and
there's
conversation
going
on
in
Icke.
At
the
moment.
C
It's
like
that
I
clean
one
is
actually
post
quantum
resistance
and
because
they're
appreciating
so
there's
a
proposal
going
through
at
second
moments
to
introduce
that
into
version
two
as
well
likely
to
and
add
pre-show
keys
to
give
that
quantum
resistance.
So
you
don't
need
to
be
using
large
parameters
or
something
even
something
as
simple
as
a
PPS
K
in
there.
A
C
I'm,
just
generally
I
think
crypto
agilities
important,
although
I
do
take
a
point
that
if
you
have
no
security,
classical
cryptography
is
better
than
going
home.
Holding
going
for
post
quantum
as
well,
but
crypto
agility
just
generally
is
quite
good.
If
something
is
later
found
to
be
weak
to
be
able
to
replace
that
and
drop.
That
in
is
quite
a
useful
property.
A
Hi
Robin,
Milton,
I
think
you're
right
to
at
least
re-examine
the
the
traditional
assumptions
about
how
PKI
ought
to
work
than
to
question
the
this.
You
know
the
rules
say:
what's
forbid
man,
what
what
it's
acceptable
to
do
when
I
say
that,
because
when
several
years
ago
I
was
doing,
research
into
this
I
spoke
to
him,
they
pick
al
bender
and
I
kind
of
started.
A
The
conversation
by
saying
and
people
keep
saying
that
this
is
gonna,
be
the
year
of
pique
all
right
and
he
said
I
want
to
stop
you
there
two
years
ago
was
the
year
of
PKI,
and
this
was
what
he
was
talking
about
about
2008
2009.
He
said
in
2008
we
shipped
a
million
public
key
pairs
and
we
expect
billion
in
this
year
and
he
was
shipping
with
the
mobile
devices
and
they
didn't
put
public
keys
and
certificates.
That's
why
you're
breaking
all
the
rules?
How
can
you
do
that?
A
Some
of
the
controls
was
because
if
there
was
a
problem
with
it,
an
assault
key,
you
didn't
bother
about
having
a
management
interface
to
replace
the
key
remotely
you
replace
the
device,
well,
the
smart
plug
in
the
device.
So
again
an
example
of
heart.
It
is
valid
to
question
the
assumptions,
even
if
at
the
end
of
that,
you
come
back
and
say
well,
actually,
no.
The
assumption
still
holds
in
this
case,
and
so
when
you're
talking
about
these
devices,
there's
like
duct
to
the
difficulty.
A
A
A
D
A
A
A
A
A
A
A
A
A
A
D
B
F
B
A
A
A
F
F
A
A
E
F
A
A
A
Idea,
so
if
you
do
this,
okay,
you
have
to
think
about.
So
what
is
my
innovation
spectrum
in
the
space
overhead?
So
what
is
the
good
balance
between
a
general
purpose
system
in
the
highly
efficient
system
and
so
from
a
for
the
ICN
folks?
The
question
is:
should
we
actually
control
the
data
plane
to
support?
You
know
finding
functioning
its
optimizing.
A
To
what
extent
should
we
leave
this
to
orchestration
test,
and
then
finally,
I
think
really
crucial
is
what
what
are
the
requirements
for
trust
management
been
available?
You
know
the
security
in
the
systems
of
how
can
I
trust
platforms,
the
generated
data
and
the
mobile
code
actually
run
on
these
systems.
So
if
you're
interested
in.
