►
From YouTube: IETF102-RTCWEB-20180717-1430
Description
RTCWEB meeting session at IETF102
2018/07/17 1430
https://datatracker.ietf.org/meeting/102/proceedings/
A
We
basically
have
two
three
drafts
that
are
not
yet
completed.
One
is
STP
examples
which
we
think
we're
pretty
much
ready
to
go
s
after
this,
but
we
don't
really
need
to
talk
about.
We
have
IP
handling
where
we
have
this
one
issue
about
hem
DNS
names
for
most
candidates
and
security,
our
architecture
document.
A
We
have
a
couple
of
pyaara
pyaara
later
than
that,
and
so
sorry,
so
most
of
the
PRS
got
merged,
which
was
good
so
there's
that
there
are
two
that
are
outstanding,
which
is
delicious,
because
that
means
we
could
almost
be
done,
but
I
guess
so
we'd
like
to
start
off
with
the
IP
handling
stuff,
but
before
we
get
there.
The
whole
plan
here
right
is
to
get
it
done
at
this
point.
We
need
to
pick
this
thing
up
and
get
it
across
the
finish
line
and
we
need
your
help.
A
B
One
thing
more
about
getting
finished:
I
I
want
to
note
that
one
outstanding
document
before
get
started
is
topic
in
the
working
group,
which
is
the
document,
and
that's
hyacinth
reviewed
comments.
Is
that
right?
It
would
really
be
good
if
people
comments
or
cetera
or
reads
and
comments
and
gets
this
help
getting
this
done,
because
that's
otherwise
it's
gonna
be
the
last
document
out
so.
C
All
right,
so
I'd
be
handling,
let's
start
by
sort
of
recapping
like
what
a
point
of
this
draft
is,
and
the
goal
here
was
to
you
know,
take
four
obscure
web
pages.
Previously
we
gave
out
all
ice
candidates,
and
this
created
some
problems.
The
two
most
specific
problems
were
that
by
giving
out
every
single
sort
I
address
that
the
I
station
and
find
this
and
a
lot
of
people
who
are
blind
behind
VPNs
to
have
their
public
eyes
be
address
identified.
This
was
not
good.
C
In
addition,
not
giving
out
all
the
set
of
addresses
allowed
more
fingerprinting.
You
know
and
we'll
get
to
more
about
this
later,
but
these
are
the
two
main
things
we're
trying
to
address
with
this
draft
and
in
addition
to
solving
these
problems,
we
also
learn
to
maintain
the
ability
to
actually
establish
direct
peer-to-peer
connections,
and
why
do
we
care
about
our
trailer
pages
being
able
to
able
to
establish
peer
connections?
Well,
it
turns
out
that
this
is
actually
a
very
frequently
use
functionality.
There
there's
actually
five
times
as
many
page
loads
in
Chrome.
C
You
did
a
channels
as
use
actually
RTC
web
for
audio
and
video,
and
this
traffic
has
been
growing
exponentially
over
400%
you
every
year
is
actually
starting
to
make
a
blip
on
me
compared
to
over
HTTP
traffic
data
channels,
I
started.
Actually
the
traffic
theory
is
that
starting
to
become
actually
comparable
all
on
its
way
to
becoming
humble
so
like
this
actually
big
deal,
we
don't
want
to.
Unlike
cut
this
thing
off,
it's
a
very
promising,
emergent
technology.
We
want
to
find
some
way
of
having
your
cake
and
eating
you
all
right.
C
You
know
the
same
way
that
we
used
to
touch
from
the
website
over
HTTP
using
that
for
actual
web
RTC
traffic,
and
so
what
we
ended
up
doing
was
we
gave
out
just
that
one
public
IP,
but
we
all
gave
out
its
associated
private
IP,
and
so
we
considered
this
an
acceptable
trade-off.
You
know,
because
we
wanted
to
make
sure
we
could
allow
these
direct
connections.
We
thought
that
the
actual
IP
before
information
given
out
was
fairly
minimal.
I
wasn't
really
identifying
and
overall
the
you
know
the
cutting
off
the
ability
to
have
direct
connections.
C
You
know
seemed
like
a
pretty
big
downside,
however,
like
that
we
knew
there
are
some
cases
that
you
know
the
IP
for
adjusters
might
actually
contain
valuable
information.
There
are
some
efforts
going
on
to
try
to
reduce
the
number
of
fingerprinting
surfaces.
You
know
on
the
web
and
in
doing
some
enumeration
of
what
people
are
actually
doing
with
WebRTC
and
analysis
of
Chrome
stats
show
that
there
is
a
non-trivial
number
of
pages
that
basically
create
a
peer
connection,
get
addresses
and
then
do
nothing
else,
and
even
after
we
implanted
this
solution
for
problem
1.
D
Ok,
so
in
Safari
we
went
to
our
team
and
basically
they
said,
there's
one
rule
you
can
send
anything,
but
it's
already
public,
but
if
it's
private,
please
do
not
send
it.
So
we
decided
to
use
what
free
by
default.
What
do
you
when
get
you
the
media
is
on
and
this
it's
better
to
ship
something
than
nothing
so,
and
some
people
were
happy,
so
it
was
already
good
still
we
we
broke
some
existing
applications
that
are
running.
You
know
the
browsers.
D
We
got
something
back.
We
had
some
pretty
good
feedback
actually
from
things
like
web
torrent,
where
they
do
not
really
care,
maybe
no
kind
of
okay,
but
still
there
are
some
applications
like
games
where
latency
is
important,
so
turn
is
not
very
good
and
there
are
also
some
apps
where
that
are
like
sending
a
massive
amount
of
data
between
devices
and
we're
turn
might
be
too
expensive
or
very
small
apps,
where
turn
is
also
is
already
too
expensive.
D
D
Okay,
so
we
looked
at
muted
it
and
said:
hey:
why
not
choose
mdns?
So
when
you
gather
Eiskant
days,
you
have
host
candidates
with
ipv4
addresses,
so
why
not
generate
a
new
ID
register
it
for
n
DNS
and
then
replace
in
the
field.
V
IP
address
with
this
new
ID.
That's
what
we
did.
We
implemented
it
into
Safari
behind
the
flag.
So
it's
available,
you
can
activate
it
and
play
with
it.
It's
not
100%
well
implemented,
so
it
could
be
optimized,
but
still
it's
available.
D
You
can
play
with
it
and
then
the
good
thing
is
that
we're
able
to
get
some
early
experiments.
The
good
thing
is
that
it's
working
very
well
as
expected
on
unmannered
networks,
meaning
like
small
offices,
networks
home
like
if
you
play
a
game,
maybe
it's
at
home
and
not
at
work.
So
maybe
maybe
there
it
will
almost
get
everything
working.
D
It's
really
it's
adding
some
potential
latency
you
to
immunise
resolution
to
connection
setup.
It's
not
I,
don't
think
it's
a
big
deal,
but
still
it's
something
that
you
should
be
noted.
It
does
not
always
work
on
enterprise
networks.
That's
for
sure.
So
it's
not
like
full
solution.
Some
networks
will
disable
multicast.
If
you're
not
on
the
same
network
segment,
then
mdns
will
probably
not
work
as
as
well.
D
I
should
note
that
only
add
that
expects
direct
host
to
host
connection
working
in
an
enterprise
network
might
face
some
issues
anyway,
because
you
have
no
guarantee
so
you
need
to
have
anyway,
some
of
a
solution.
Like
turn,
servers
like
something
like
that
that
will
allow
you
to
actually
ensure
that
you
will
connect
the
people
you
actually
want,
but
still.
D
D
C
Okay,
so
to
try
to
you
know,
come
up
with
the
best
possible
solution
that
gets
the
mineral
sort,
privacy
impact
and
the
maximal
my
code
of
connectivity.
You
know
the
thing
we
sort
of
came
up
with
was
to
use
mdns
to
hide
private
addresses
I,
any
a
v4
v6
addresses
that
are
public
and
how
I
determine
that's
public
is
like
something
we
can
talk
about
on
a
later
slide.
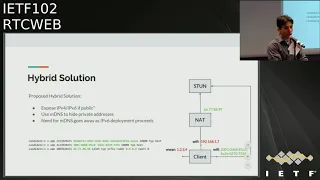
C
Give
this
out,
because
that's
on
the
website
to
see
anyway,
and
then
the
nice
sort
of
thing
about
this
solution
would
be
that,
as
I
p
v6
deployment
proceeds,
the
need
to
rely
on
MDM
DNS
goes
away,
and
so
you
can
see
from
the
diagram
here
kind
of
what
would
happen
that
you
have
this
client
and
it's
multihomed.
It's
got.
You
know
cell
interface,
WN.
It's
got
Wi-Fi
interface,
which
has
both
v4
and
v6.
The
v4
address
is
your
typical
mattad
before
that
gets
hidden
and
is
covered
by
the
this
thing
work.
C
Yes,
the
M
DNS
name.
The
v6
address
is
public,
that's
here
and
then
the
actual
public
you
know
server
reflexive
address
doesn't
launch
from
the
stun
server
is
also
given
out.
You
can
see
that
the
local
address
here
is
emitted
from
the
are
ever
so.
This
is
what
we
propose,
you
know,
is
the
sort
of
sweet
spot
in
terms
of
what
we
can
make
work
today.
Yep.
F
C
G
G
G
F
F
Yes,
Thompson
I
think
the
I
think
this
is
a
good
observation.
It's
very
simple
to
say
that
I'm
gonna
buy
into
this
address
and
then
do
whatever
is
necessary
for
this
I
think
this
is
just
an
optimization
on
their
front.
I,
don't
I,
don't
think
it
actually
changes
the
the
the
nature
of
this
at
all.
To
use
the
the
same
label
all
same
mdns
address
to
refer
to
multiple
host
candidates.
I
mean
that's
it's
it's
just
an
optimization.
If.
C
G
C
E
I'd
also
like
to
point
out
that
there
are
will
be
cases
where
the
ipv6
address
has
a
different
scope,
especially
on
wired
interfaces.
So
you
may
be
able
to
use
em
DNS
and
have
a
different
scope.
Then
you
would
have
the
public
ipv6
address,
so
you
may
be
getting
a
different
ipv6
address
than
this
ipv6
address,
because
it
reflects
a
different
ipv6
scope,
so
I
think
having
a
separate
UUID.
If
you
want
to
use
a
UID
to
front
that
separate
scope
is
a
good
idea.
So.
H
H
F
D
D
F
Yes,
I'm
not
in
Thompson
I,
think
that's
my
preferred
approach
for
this.
If
we
can
find
a
way
to
just
adjust
the
IP
handling
document
so
that
it
doesn't
add
this,
this
new
stuff
then
and
describe
some
modes
and
maybe
recommends
the
safer
option
of
the
set,
and
then
we
can
later
on
update
it
with
the
new
things
with
I.
F
C
E
C
G
J
A
E
E
K
C
A
problem
with
the
current
specification
I
mean
I
think
we
would
say
that
this
is
not
yet
solving
the
specification
and
who
knows
maybe
define
I
mean
guess,
is
practically
speaking
like
each
browser
now
has
made
its
decision
of
what
it's
going
to
do
so
I.
Don't
think
this
will
actually
change.
You
know
any
actual
implementations.
C
G
E
L
G
You
know
we're
interested
in
this
mode
like
understand
how
that
works.
I
think
you
put
you
right
to
accurately,
which
is
some
serious.
It
works
in
some
cells,
many
more
interestin
scene
measurements
about
like
how
eleven
there's
two
things
occur,
which
I
suspect
you
are
as
well
and
that
you
know,
but
that
like
having
these
documents,
tough
negotiator
queue
for
a
year
and
a
half
while
you
buy
eight
those
questions
or
whatever
it
is,
is
not
gonna
like
that's
not
gonna
make
it's
not
gonna.
Make
us
like
more
aggressive
babbling
about.
M
You
know,
I
think,
there's
a
lot
it's
hard
to
make.
This
call
because
there's
a
lot
of
unknowns.
We
don't
know
about
this
like
we
have
questions
about
like
does
just
enabling
this
allow
you
to
do
DDoS
attacks
on
the
multicast
traffic
inside
the
enterprise,
just
by
creating
a
lot
of
these
and
what
are
sort
of
the
rates
and
stuff
of
that.
How
well
does
it
actually
work
in
enterprise?
I
mean
the
case
where
this
tends
the
the
way
you
described
where
it
works
and
doesn't
work.
G
M
Lots
right,
it's
those
are,
of
course
exactly
some
of
the
places.
This
is
most
valuable
in
the
home
residential.
In
that
situation,
it
didn't
matter
that
you
hair,
pin
through
the
GNAT
anyway,
it
wasn't
like
you
went
across
the
land,
because
the
address
filtering
was
such
that
you
could
hair
pin
on
the
map
versus
having
to
go
to
a
tremor.
So
I
think
we
start
looking
at
some
of
those
statistics
now.
The
thing
I'm
interested
in
about
at
this
is
this
is
not
just
strictly
a
security
improvement.
M
It
makes
a
bunch
of
security
much
worse
and
what
it
makes
much
worse.
Is
it
now
forces
a
whole
bunch
of
traffic
that
didn't
use
to
have
to
go
through
middle
boxes,
to
go
up
through
middle
boxes
that
are
typically
run
by
somebody
who's
not
really
fully
trusted
by
the
end
users,
in
these
cases
and
anytime,
that
we
start
taking
traffic
that
could
have
remained
on
a
local
network
and
not
have
to
push
it
through
a
place.
That's
an
awesome
place
for
law
enforcement
to
intercept
it
yeah.
It
makes
me
a
little
queasy.
M
M
E
E
E
If
you
cannot
live
with
this
being
in
a
separate
document,
because
I
think
that
if
it's
in
a
separate
document,
we
can
progress
it
after
we've
gotten
some
of
this
experimentation
in
front
of
the
working
group.
If
it
has
to
be
in
this
document,
we'll
move
forward
a
different
way.
But
what
we
really
want
to
know
is
whether
or
not
you
can
live
with
this
being
in
a
separate
document
or
not.
So
anybody
have
questions
on
the
hums
before
we
take
the
hummus.
E
M
M
I
thought
that
I
think
that
putting
it
into
another
document
is
no
guarantee
that
we're
actually
what
happens
right.
The
working
group
will
come
to
whatever
consensus
it
comes
on
on
whether
it
goes
in
the
same
document
or
a
different
document.
There's
a
lot
of
work.
That
needs
to
be
done
before
we're
done
with
this,
and
it
will
need
working
group
consensus.
M
E
E
M
E
Any
more
hum
questions
before
we
take
the
Hummels
hum
now,
if
you
think
you
understand
the
problem
I'm
relieved
if
it
was
dead.
Quite
at
that
point,
though
I
would
be
like
you're
gonna
have
to
bring
me
a
live
crow
at
this
point.
That
picture
is
not
cutting
it.
Okay,
hum
now,
if
you
can
live
with
us
separating
this
document
out
from
IP
handling.
E
E
E
A
C
E
C
C
I
am
not
aware,
oh
they're,
very
few
of
these
today,
so
we
would
basically
be
asking
digital
applications
to
be
deploying
v6
down
servers
and
then,
even
once
we
have
this,
then,
if
you
are
behind
that
six
four,
you
won't
be
able
to
use
that
v6
to
actually
give
a
direct
connection.
So
we'll
do
some
experiments
here
will
understand.
If
this
is
a
big
issue,
you
know
one
of
the
options
could
be.
We
just
always
give
our
v6,
a--'s
and
well.
C
N
B
F
C
F
G
N
D
We're
testing
we
there's
no
1
second
delay
for
a
connection
setup,
that's
interesting!
The
second
thing
is
that
you
know
so.
For
the
first
connection,
you
might
have
a
small
delay
in
solutions.
We
we
had
like
200,
millisecond
delay.
It's
highly
depends
if
you
want
Wi-Fi
or
not.
If
you
are
like
packet
loss,
so
we
might
be
about
to
measure
to
make
measurements
here
to
precise.
You
know,
yeah.
F
F
M
F
G
G
O
D
D
Some
might
say
that
if
you
have
two
pages
with
two
iframes
that
our
trackers
and
you
are
trying
to
isolate
these
two
trackers
that
so
that
they
do
not
state
which
is
actually
what
is
implement
in
severy,
then
allowing
these
two
Tigra
tracker
iframes
to
know
that
they're
running
in
the
same
device
and
start
to
use
WebSocket
to
share
stage
cookies
and
everything
might
be
an
issue.
So
we
are
actually
investigating
that
the
the
point,
where
is,
should
we
document
this
issue
somewhere?
Is
it
an
issue
and
if
so,
what's
the
path
forward?
I.
G
Mean
this
is
an
issue:
there's
a
lot
I
mean
I,
guess
I
mean
I'm,
you
know,
I
got
I
feel
like
or
worst
nightmares
about,
like
co-located
code
have
now
come
true.
So,
like
the
the
it's
a
quaint
tour
in
the
face
of
Specter,
it's
can
equate
to
worry
about
like
determining
you're
missing
the
host
team
at
this
point
in
the
game.
G
Perhaps
if
you're
chrome,
you
feel
differently,
but
here
people
don't
so
you
come
so
I
I'm
we're
also
working
on
it
I'm
more
seriously,
they're
just
a
lot
of
ways
to
determine
I.
Think
if
you're
like
on
the
same
post,
you
service
Lee,
if
not
not
poker,
solution
or
v6,
but
as
far
as
I
can
tell
there's
no
clear
solution
at
all.
Unless
I
mean
maybe-
or
perhaps
you
can
disable.
G
No,
but
no
I
I
miss
I'm,
assuming
user
different,
you
IDs,
but
then
basically,
what
I
do
is
I
take
the
you
know:
I
take
the
I,
I
did
I,
you
know
I
had
to
dive
to
two
domains
that
I
want
to
see.
They're
co-located
in
the
double
keyed
and
I
have
both
of
exfiltrate
the
addresses
and
then
yeah
I'm
trying
to
grab
pretty
call
and
like
it
works
then
like
I'm
on
basically
the
same
machine
or
I'm
that
same
or
in
the
same
local
network.
So
so
I
I,
don't
know.
G
M
M
M
D
M
D
D
It's
not
a
priority
because
it's
true
that
there
are
other
issues
but
I
think
it
should
be
in
the
one
map
and
maybe
we'll
find
some
solutions.
Maybe
on
our
side,
when
we
just
disabled
like
when
we
are
spaced
in
Safari,
where
we
are
very
restrictive
and
what
we're
hoping
to
do
is
to
open
the
door
a
little
bit.
So
we
can
open
video
like
just
a
little
bit
or
a
little
bit
more,
not
on
iframes,
maybe
a
my
friends.
We
have
some
granularity
there
that
we
can
play
with
since.
E
We
I
think
that
the
current
proposal
is
that
we
will
document
this
issue
in
the
IP
handling
draft
and
then
consider
solutions
in
the
follow-on
draft.
Please
indicate
when
you're
standing
up
at
the
mic
line,
whether
you
have
any
problem
with
us,
documenting
the
issue,
because
I
think
we
can
postpone
discussion
of
the
solutions
till
the
discussion
of
the
follow-on
draft.
If
we
have
agreement
that
we're
documenting
the
issue.
O
K
E
C
Twenty
one
final
note,
one
more
in
common
choice:
I'd
mentioned
that
Mike.
If
you
can't
stablish
a
track
connection
will
typically
fall
back
hair,
pinning
through
that
and
in
doing
some
tests
here.
I
was
surprised
by
how
infrequently
hair
printing
actually
occurred
even
in
today's
internet
on
some
from
popular
nap
products,
and
you
need,
did
you
see
the
same
thing.
C
I
I
Not
the
author
is
the
reason
our
period
is
is
because
well
I
have
indicated
I'm
willing
to
help
with
STP
issues
and
so
on,
but
but
before
really
starting
to
write
text,
there
were
some
some
issues
that
I
think
we
need
to
turn
me
on
or
to
make
sure
we
have
a
common
understanding,
not
how
to
really
write
lower
things,
as
also
to
make
clear
least,
this
is
not
generated
general
overview
of
the
whole
document.
Only
the
STP
I
attribute
part
of
it.
I
So
if
you
have
other
issues,
you
know
with
the
IDP
and
an
identity
assertion
in
general,
they.
This
is
not
a
time
and
place
place
for
that.
So
this
and
also
I'm
not
going
the
review
that
I
did.
For
example,
Martinez
already
created
a
request
in
that
I
think
the
link
is
on.
The
mailing
list
is
also
I'm
going
to
show
it
in
other
presentations.
I
So
there
are
basically
a
couple
of
main
issues
which
I'm
going
to
bring
up
here,
which
I
think
is
is
is
what
we
need
to
agree
on
and
to
make
sure:
okay,
okay,
so
basically
yeah
but
background
I
also
said
about,
but
the
the
Assumption
here
is
because
this
draft
is
foreign
foreign
as
it's
written
in
this
in
this
working
group
is
very
web.
Rtc
specific,
but
assumption
here
is
the
best
EP
identity
attribute
is
a
generic
attribute
which
can
be
used
to
carry
identity
Association.
I
Also
in
other
environments,
not
really
the
bar
can
see
specific,
and
even
if
one
pair
is
of
a
party
CN
point,
the
other
pair
may
not
not
be
a,
but
it
could
still
use
the
same
identity
assertion
mechanism
to
do
so.
That's
the
assumption
to
have
a
generic
attribute
which
can
be
used
by
anyone
supporting
in
an
iid
p
assertion
mechanism.
I
One
of
the
question
I
raised
is
that
do
you
have
to
use
the
fingerprint
always
or
could
you
use
also
something
else
and
the
answer
I
got
and
now
when
I
say
answer
here,
is
this
discussion
I
had
and
I?
Both
people
have
indicated
on
the
list?
Is
it's
not
something
we
have
agreed
on,
but
but
what
those
who
have
provided
input
instead
from
a
protocol
expect
that
you
could
use
something
else
than
a
fingerprint.
I
E
Already
just
a
clarifying
question:
you
have
here
in
the
answer
from
a
protocol
perspective,
but
here
what
you
mean
in
particular
is
this
usage
of
SDP
is
allowed
to
use
other
information,
not
J
cept.
The
protocol
will
use
other
information,
but
this
SDP
identity
may
use
other
information.
That's
what
you
mean
by
protocol.
Yes,.
I
F
Is
about
making
sure
that
the
definition
of
the
STP
attribute
is
consistent
with
other
attributes
and
all
those
things
largely
editorial?
What
Krista
has
actually
done
is
highlight
a
few
places
where
there's
a
little
hole
or
two
and
that's
been
quite
helpful,
but
other
than
that
yeah
don't
change
anything.
We
did
change
something
by
the
way,
but.
I
That
issue
was,
which
is
interesting,
is
if
you
have
a
subsequent
offer
a
server.
Actually,
the
pair
or
even
yourself,
updates
the
identity
and
and
I
have
one
example
where
this
cause
case.
We
often
talk
about
this
third
party
call,
can
cross
and
call
transfers
done
just
by
updating
the
STP.
So
you
have
your
browser,
for
example,
is
communicating
with
another
pair,
and
then
you
have
a
call
controller
which
is
going
to
to
make
a
call
transfer.
I
I
The
the
feedback
here
is
that
you
gain
from
our
pure
purko
spur
sexy.
We
we
shouldn't.
We
shouldn't
disallow
this.
It's
allowed.
However,
it
may
not
be
supported
by
the
receiver
and,
for
example,
web
RTC.
That's
not
allowed
to
update
the
identity
of
appear,
so
they
suggested
way
forward.
Here
is
that
you
say
yeah.
You
can
do
this,
for
example,
when
you
send
us,
you
can
do
it,
but
also
to
indicate
that
this
is
not
something
that
that
anyone
must
report.
If
the
receiver
doesn't
support
it,
it
doesn't
accept
it.
I
H
I
F
So
the
web
RTC
Martin
Thompson,
sorry,
the
WebRTC
specs-
are
very
clear
on
this
point.
Once
you
have
an
identity
for
a
Pierre,
you
can't
go
backwards
from
that
point.
It
has
to
remain
the
same
thereafter.
So
any
any
session
description
you
receive
from
that
point
onwards
has
to
have
the
same
identity,
because
we
don't
know
how
to
do
anything
else.
Nothing
else
really
makes
any
sense
if
you
want
to
have
a
different
identity,
make
a
new
peer
connection
and
then
first
and.
I
Actually,
what
I'm
going
to
put
in
it
you
know
it
takes
about.
This-
is
there's
going
to
be
a
section
about
modifying
a
session
and
there
is
going
to
be
a
must.
You
must
include
identity
and,
of
course,
if
even
if
it's
the
same
as
previously,
not
not
including
it
means
that
you're
actually
removing
it.
So
so
so,
of
course,
if
that's
what
you
want
to
do,
that's
what
you
want
to
do,
but
if
you
want
to
keep
the
same
identity
as
previously,
then
then
you
must
include
it
in
this
subsequent
offer.
M
Right,
yeah,
I
think
a
general
policy
I'm
in
favor.
That's
the
general
policy
here
is
what
you
do
with
identity
is
effectively
a
policy
decision
about
what
the
security
and
it
means
in
whatever
you're
using
application.
In
WebRTC,
we
have
very
clear
things
of
what
that
policy
is
and
other
things
they
might
have
different
policies
and
different
rules,
and
you
know
even
the
the
call
that
way
of
doing
transfer
is
not
generally
how
it's
done
because
of
all
kinds
of
problems
like
this.
I
I
So
the
way
forward
is,
and
asaba
indicated
a
I'm
willing
to
help
with
this.
For
example,
one
of
the
things
I
didn't
bring
up
here.
What
would
I
had
in
my
review
was
that
we
should
also
use
this
template
for
for
defining
your
SDP
attributes
this,
if
you
read
I,
mean
sending
a
mission
offer
or
sending
the
answer
or
modifying
a
session
and
so
on,
and
so
on
and
I'm
now
willing
to
help
to
put
a
pull
request
regarding
that
together.
I
K
I
G
For
loads,
so
thank
you
for
doing
this
review
and
thank
you
for
if
you
just
reload
I,
think
those
are
all
great
all
gone
yeah
there.
You
go
it's
linking
interview
and
thank
you
for
catching
these
I
guess:
I'm
reluctant
to
screw
the
structure
at
this
point
in
the
game.
I
understand
your
willingness
to
do
it,
but
it
seems
like
it
seems,
like
that's
really
kind
of
like
gonna
make
our
lives
harder.
Maybe
there's
pacific
points.
Do
you
think?
G
I
Think
I
had
a
look
at
a
document.
Currently
there
did
attribute
is
defined
somewhere
in
a
subsection
level,
3
or
level
4.
So
my
yeah
something
like
that,
but
my
idea
would
be
just
to
move
that
into
a
separate
main
section
and
then,
of
course
we
have
to
add
this
sending
an
issue
of
her
answer
and
blah
blah
blah.
But
it's
going
to
be
very
it's
not
going
to
impact
other
parts
or
the
documents.
G
E
The
terms
do
not
believe
that
there's
a
natural
law,
so
we
would
recommend
that
you
generate
the
pull
request
and
have
it
reviewed,
but
it
will
be
up
to
the
editors
discretion
to
or
not
except
the
pull
request,
depending
on
the
the
amount
of
confusion
and
work
he
believed
it
will
take.
So
the
the
key
thing
is
that
the
material
be
right
and
the
structure
is
not
normative
and
certain
and.
E
G
I
I
think
that
means
we're
a
mission
now
is
they're.
Sending
this
initial
offer
and
modifies
a
session
I
mean
it
could
be
written
in
other
ways
to
and
of
course,
those
things
that
we
previously
discussed.
You're
clarifying
that
that,
for
example,
if
you
use
something
else
and
fingerprint
is
in
name
just-
could
prescribe
and
also
about
this
updating
identity,
there
there's
nothing
about
that,
but
I
mean
I'm.
G
A
A
A
E
And
we
have
fun
in
several
outside
reviews,
for
it.
I
really
want
to
thank
Paul
and
Fleming
and
the
other
reviewers
who
have
already
done
that.
But
it
is
a
big
piece
of
work
to
look
at.
Please
do
take
some
time
grab
a
few
of
the
examples
go
through
them.
I
think
anybody
who
does
the
whole
document
is
is
going
to
be
very
tired
indeed,
by
the
end
of
it,
because
the
productions
are
very,
very
complicated,
but
please
do
sample
a
few
of
giving
your
expertise
and
give
us
comments
as
fast
as
you
can
I.
