►
From YouTube: IETF102-OPSAWG-20180717-1550
Description
OPSAWG meeting session at IETF102
2018/07/17 1550
https://datatracker.ietf.org/meeting/102/proceedings/
A
A
B
A
C
E
F
E
B
B
The
note
well,
please
make
sure
you
understand
those
important
legal
issues,
basically
for
your
contributions
need
to
for
a
variety
of
groups
and
the
blue
sheet
is
circulating.
Please
write
down
your
name
and
before
we
can
really
start,
we
need
a
JavaScript
and
the
meanest
acre.
Is
there
any
volunteer.
H
D
B
H
Indeed,
okay,
so
first,
what
mod
manufacturing
usage
description
that
is
moved
around
quite
well
in
the
in
the
iesg.
So
what's
currently
sitting
in
the
RFC
you
in
a
mr.
F
state
and
the
reference
that's
missing
is
the
AC
automatic
from
from
net
mod
I
talked
to
one
of
the
authors
of
the
ACL
model
that
is
currently.
There
are
two
iesg
comments
that
are
getting
taken:
care
of
he's
not
expecting
any
of
those
changes
to
be
held
up
too
well.
H
Nor
is
he
expecting
any
of
the
changes
to
cause
any
disruption
or
change
to
the
mud
or
the
current
mud
work.
So
we
expect
that
I'm
hoping
very
soon
like
next
month.
We
should
see
those
go
through,
but
that
is
the
current.
That's
there's
nothing
other
than
the
ACL
model,
gating
gating
mud.
As
for
the
IP
fix
bgp
community,
we
are
waiting
for
a
shepherd
right
up
on
that.
One.
H
With
four
with
regard
to
the
nat
yang
module-
and
that
is
currently
been
simply
iesg-
and
I
just
heard
from
one
of
our
Ignace
that
it
will
be
proposed
to
the
next
Elledge
at
whether
or
not
it
makes
the
pact
agenda
we'll
see.
But
it
is.
It
is
currently
slated
to
be
discussed
as
soon
as
possible
by
the
ASG.
H
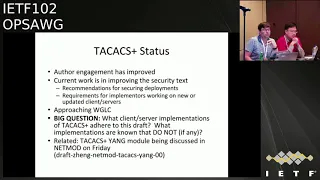
Saving
the
best
for
last
we'll
go
on
to
the
next
slide,
and
this
is
the
status
of
the
tax
plus
breath.
Fortunately,
we've
gotten
a
lot
more
after
engagement
releasable
on
the
list.
The
current
work
right
now
is
focusing
around
these
security
consideration
stocks
in
particular.
What
we're
trying
to
do
is
shore
that
up
too,
so
we
can
recommend
how
best
to
secure
what
we
generally
consider
to
be
insecure.
So,
just
as
a
summary,
the
draft
scope
is
to
document
the
tax
profile
as
we
believe
it
to
be
implemented
today.
H
This
is
an
informational
draft
of
tax
plus,
as
we
believe
it
to
be
implemented
today,
with
no
additional
extensions.
Anything
like
that.
We
would
like
to
give
recommendations
to
people
deploying
tax,
how
best
to
do
it
and
we
want
to
give
recommendations
to
vendors
or
implementers
of
tax
plus
clients
and
servers
what
they
should
do
if
they
are
going
to
create
a
new
implementation
or
update
existing
implementations.
H
H
Comment
on
the
list
specifically
to
what's
written
there,
if
you
know
of-
or
you
aren't
responsible
for,
implementations
of
tactics,
plus
clients
or
servers,
are
they
compliant
or
do
they
adhere
to
this
draft?
If
they
do
great
just
say
yes,
I
know
of
this
implementation
it
adheres
and,
as
importantly,
if
you
know
any
that
do
not
adhere
to
the
strap.
What
are
those
implementations?
Where
do
they
deviate
from
what
is
being
documented?
H
There's
also,
some
related
work
to
this
that
will
be
presented
Friday
and
net
mind
around
a
yang
module
for
doing
x+
configuration,
given
that
there
is
a
correlation
between
lap
and
and
this
drafting
worked
on
here.
If
you
have
comments,
it
would
be
good.
The
authors
I
know
would
appreciate
it
to
be
able
to
go
to
let
mod
on
Friday.
Listen
to
that
and
certainly
comment
on
the
net
lobbyists
yeah.
B
Microphone
Foley
I
speak
at
Turkish
young
modules
closer.
Yes,
we
have
employed
ataxia
motor
in
nine,
most,
not
known
working
group,
and
are
we
also
representatives
document
on
Fridays
versus
session,
and
we
I
know
the
how
come
the
quarry
have
incremented
took
the
crust
and
way
provided
yonder
DiMaggio
to
introduce
the
word
way
how
to
make
configurations
caucus
on
the
crack
sister
front.
So
if
you
have
interest
in
this,
topic
plays
to
general
discussion
and
our
Commons
and
stressin
yeah
very
welcome
yeah.
Thank
you.
I
B
G
B
B
So,
of
course,
what
what's
new
about
this?
A
new
revision?
Firstly,
we
have
a
quite
a
few
contributors.
We
have
closers
from
TI
from
china,
mobile
and
ICT
Nokia
and
China
Telecom
thankful.
This
causes
solid
contribution
to
make
this
chapter
better,
and
in
this
revision
we
make
a
clearer
definition
and
characteristic
a
summary
of
the
network
telemetry.
B
We
intentionally
make
a
clear
distinction
between
the
conventional,
om
and
telemetry,
and
also
proposed
from
now
on
to
user
telemetry,
as
a
standard
word
for
the
for
the
technology
to
achieve
our
network
visibility
on
so
they
can
support,
meets
the
today's
network
challenge
and
also
address
future
networks
requirements
and
also
to
completes
our
framework.
We
add
a
new
module
to
the
framework,
which
is
an
extensive
external
data
and
the
UN
telemetry.
Also
in
the
old
version,
we
have
only
control
plane,
our
telemetry
natively
in
temperature
at
the
managing
plane
telemetry.
B
We
identifies
some
requirements
and
the
challenges
for
the
control
plane
and
we
add
the
BFF
pnp
protocol
extensions
who
named
it
has
an
IP,
an
MP
I
believe
the
Robin
for
next
talk
will
talk
about
this
and
we
also
add
new
content
for
the
data
plane
telemetry.
First,
we
try
to
classify
or
the
existing
different
type
of
technologies,
so
the
classification
can
be
done
from
multiple
dimensions.
For
example,
we
can
do
the
active
and
passive
Graham
3
embed.
An
autopen
embedded
also
means
here.
We
use
the
term
in
situ
means
a
captured.
B
B
An
host
will
not
be
aware
of
it,
and
also
there
could
be
multiple
source
of
the
collected
telemetry
data.
It
may
be
belong
to
flows
or
belong
to
pass
or
go
to
the
node.
So
we
use
a
dis
different,
are
dimensions
for
the
classification
to
classify
different
technologies
and
for
the
specific
technologies.
In
this
new
revision.
We
give
some
brief
introduction
to
some
new
technologies,
including
the
IP
fpn
is
used.
B
B
Actually,
we
see
today's
network
become
more
and
more
complex
because
there
are
so
many
different
type
of
work
and
networks,
and
so
many
different
particles
introduced
in
network
and
nowadays
the
customers
are
more
and
more
concerned
about
application
level
of
performance
because,
for
example,
they
want
to
learn
exactly
how
there
are
application
or
service
traffic
experience
in
the
network
in
term
of
the
database.
Late
insane,
jitter
packet
drop
are
the
reason
for
the
drop
and
the
drop
rate
and
also
what's
happening
in
the
network,
and
we
see
the
network
network.
B
B
For
example,
nowadays
we
still
don't
have
very
good
choose
to
to
achieve
the
good
application
level
visibility
and
also
all
the
tools
involve
water
for
human
labour.
We
don't
have
enough
automation,
tools
to
automate
the
process
and
even
we
look
for
future
network
architecture.
We
seen
today
the
artificial
intelligence
has
been
introduced
into
the
network
and
we
can
foresee
that,
in
the
future,
network
management
will
be
mostly
handle
/
the
machine
instead
of
human
human
being.
We
call
that
we
intend
driven
autonomous,
Network
image.
K
B
Network
identity
and
the
performance
on
also
we
can
achieve
the
bio
test,
optimize
the
resource
utilization.
So
this,
if
you
look
at
the
network
architecture,
we
form
a
close
the
control
room.
On
the
one
hand,
we
just
attracts
all
the
enough
enough
data
to
gain
the
enough
visibility
from
the
infrastructure
and
basis
of
its
ability.
We
can
apply
the
policies
through
the
programming
way
to
do
that.
B
So
in
this
architecture,
network
visibility
is
a
it's
just
a
pillar
of
that
architecture,
so
the
telemetry
should
be
promoted
as
a
first
class
citizen
in
network
technology
and
the
particles
also.
There
is
a
need,
since
that
we
have
will
have
a
single
brain
in
this
that
were
architecture
and
we
believe
all
the
network.
B
Telemetry
work
should
be
unified
and
consolidated
and
also
integrated
to
support
the
future
network.
But
the
current
an
OEM
based
solution
is
insufficient
and
efficient
to
sustain
the
future
autonomous
network.
For
example,
the
today
we
are
still
using
the
SNMP
is
based
on
the
worldö
frequent
upholding
of
the
data
from
data
plane,
and
this
is
a
dance
through
the
command
line
interface.
The
data
is
lack
of
coverage,
timeliness
and
accuracy.
K
B
So,
for
example,
the
for
the
conventional
OEM
is
mostly
for
the
distributed
network.
Architecture,
but
same
tree
is
meaningful.
The
Sdn
based
architecture
we
assumed
there's
a
central
entity.
They
will
oversee
the
entire
network
and
also
apply
the
control
to
the
network
and
the
data
for
the
telemetry.
B
So
this
is
another
important
feature
for
the
network.
Telemetry
and
also
the
data
quantity
is
a
huge
and
there's
many
target
for
the
machine
to
consume
rather
than
for
the
human
consumer,
and
this
whole
process
for
net
with
them
tree
is
automated
and
through
some
programming
means
to
configure
what
data
will
be
collected
and
our
holiday
therapy
exported
and
based
on
the
data
analytics.
We
can,
as
a
tram
tree,
can
do
the
prediction
rather
than
simple
troubleshooting
of
the
network.
B
And
finally,
this
telemetry
architecture
should
be
unified
and
many
data
source
can
be
correlating
automatically
and
for
the
conventional
OEM.
So
far
we
still
have
to
set
independent.
In
truth,
there's
no
very
hard
to
do
that
either
coronation.
So,
on
the
right
right
hand,
side,
we
missed
several
existing
protocols
and
our
work
open
source
works.
B
B
Could
be,
there
could
be
some
other,
our
interface
for
the
information
and
the
data
exchange,
an
outside
of
the
network,
will
have
a
external
data
and
invent
telemetry
modules
to
provide
the
data
to
the
network
operation
applications.
So
in
a
in
the
draft,
we
provide
a
use
case
to
show
why
this
is
necessary
and
for
each
of
this
plane
we
can
further
petition
the
telemetry
into
five
components.
The
first
is
data
source
which
covers
where
the
data
is
comes
from
and
the
data
subscription
are
cowards
how
the
application
will
subscribes.
B
The
data
and
the
third
components
is
data
generating
and
processing,
so
it's
ours
how
the
data
required
details
generated
and
the
pre-processed.
And
finally,
the
data
are
those
first
components:
data
export,
so
the
generated
data
will
use
some
interface
to
export
the
data
to
the
target
application
or
the
collector.
So
the
last
component
is
how
the
data
will
be
analyzed
and
the
store
for
future
use.
So
we
in
this
figure
we
need
some
representing
technologies.
B
B
So,
based
on
this
very
verification,
the
intent
engine
or
the
intelligent
hanjung
can
can
be
sure
their
policy
is
correct,
and
so
this
is
an
interactive
process.
You
will
need
to
continue
continuously
collecting
data
from
in
a
plane
and
do
the
analyst
analysis
and
then
push
the
updated
policy
back.
So
this
forms
a
closed
controller.
B
There
are
many
challenges
for
network
telemetry.
The
first
is
a
dynamics,
because
the
data
need
to
be
continuously
correctly
and
we
need
a
paper
to
be
real
time
and
the
process
in
turn
is
interactive.
So
it's
a
changing
to
provide
such
a
interface
and
also
from
both
sides
with
data
playing
capability.
Also,
the
harbor
control
plane
interactive
is
in
fact,
who
is
a
application.
They
suppose
a
very
challenging
and
the
data
could
have
come
from
anywhere.
B
B
Finally,
there's
a
performance
impact
because
most
of
the
data
can
be
directly
extracted
or
pre-process.
The
indeed
opening
in
the
create
some
a
performance
challenging
challenges.
To
that
word,
a
degree
to
achieve
the
ideal
families
and
the
vacancy.
Also,
the
huge
amount
of
data
need
to
be
stored
is
also
chatting,
and
then
we
don't
want.
D
B
Dilemma
tree
technology
to
interfere
with
forwarding
performance,
which
is
called
observing
effect
because
the
visibility
is
important,
but
the
first
priority
still
the
high
performance
forwarding,
so
we
don't
need
it's
a
fear
of.
Is
that
so
to
recap,
we
we
like
to
promote
the
significance
of
telemetry
work
in
IDF.
B
B
So
there
are
many
different
other
names
such
as
Network
merriman,
troubleshooting
monitoring.
So
we
believe
all
this
are
oriented
and
the
so
for
the
network
is
affinity,
so
this
should
be
all
covered
by
telemetry
and
we
all
want
to
consolidate
all
the
existing
work
and
mix
this
framework
to
guide
the
future
development.
So,
of
course,
we
continue
to
call
for
more
collaboration
from
the
operators
and
the
vendors.
Thank
you
very
much.
D
H
Thing
there
is
Clara
collaboration
from
operators
and
lenders.
What
is
the
goal
you
have
with
this
draft?
What
is
your
intent
will
take
me
forward
here?
What
work
do
you
believe?
I
mean
you're,
not
asking
for
adoption
at
this
point.
I
think
there
is
some
work
to
do
on
it,
but
what?
What
is
your
going
concerning
this
graph.
B
L
B
B
A
B
That
is
not
explained
in
a
way
to
fully
understand
all
okay,
that's
a
claim
that
is
a
little
bit
premature.
I
haven't
mentioned.
We
are
targeting
this
kind
of
future
network.
Okay,
anybody
say
this
already
soft
or
a
sporty
I
I.
Don't
believe
anybody
can
claim
that
we
are
still
very
far
from
that.
So
what's
missing
here,
we
are
moving
all
green.
That
telemetry
is
a
very
important
the
component
here,
but
with
I.
Don't
think
today's
technology
is
ready
to
support
this
kind
of
network.
So
that's
why
we
try
to
identify
almost
missing.
B
Work
I'm
wondering
a
key
reaping
how
broadly
or
narrowly
what
people
to
frame
confusing
telemetry
chemical
imagery
telemetry
clearly
is
a
part
of
providing
network
visibility,
not
the
only
part
of
ability,
because
you
have
events,
for
instance,
categorize
and
then
later
you
talk
a
lot
about
even
tend
and
all
those
things
and
intend
to
me
this
video
this
goes
into
a
beyond
just
assure.
The
visibility
goes
into
our
way:
fulfilled
services,
yeah.
L
K
L
B
K
B
I
K
B
K
K
In
fact,
this
work
has
a
mature
relationship
with
the
ego,
this
team
yeah
I'm.
He
walk,
but
in
fact
it
was
not
ready
for
me
way
to
working
shouldn't
be
long
so
that
we
purple
present
here.
This
walk
I
impose
the
obviously
WT
and
most
at
Mauro
Zucca
role,
working
group
for
more
comments
to
solicit
more
comments.
K
So
they
say
if
they
just
over
we'll
all
the
days
of
the
you
Christian
work,
we
do
for
the
network
at
elementary
from
work.
That's
so
here
for
the
past
years,
we
have
a
lot
of
water
related
with
very
intimately
in
elementary,
and
also
we
do
a
lot
of
work
related
with
that
infinite.
Elementary
related.
L
K
L
K
This
purpose
for
this
little
walk,
so
they
say
the
motivation
and
the
review
introduction
so
now
that
you
control
the
monetary,
especially
this
is
the
money
for
Iranian
state.
Hers
of
a
control
protocol
enable
the
solution
towards
automated
Network
om.
So
the
second
way
there's
the
I'm.
He
you
know
proposed
here
to
collect
the
protocol
granion
Staters
and
including
the
article
packets
and
the
protocol
statistics
and
export
the
collected
data
to
a
monkey
monitoring
station
for
analytics,
which
we
were
presented,
the
network
troubleshooting
so
in
the
current
version
of
the
draft
here.
K
K
This
work
may
be
extended
for
other
control
protocols,
so
here
this
is
the
you
do
cases
in
fact,
in
the
based
on
our
experience
for
the
routine
for
the
network,
there
are
many
other
cases
relating
the
way
of
the
control
protocol,
so
KRV,
cable,
some,
this,
the
user
case,
is
related
with
assess,
in
fact,
that
the
ITP
is
the
very,
very
important
here
very,
very
important
to
control
protocol
in
the
network
and
also
because
all
who
is
the
flooding
characteristics
once
some
failure
happens.
Even
we
affect
the
whole
network.
K
L
L
K
D
K
L
K
L
K
Is
a
does
not
work
because
of
the
world,
because
the
inconsistent
here
I'm
here
so
this
lead
also
can
gain
exported
some
information
to
locate
in
this
video
I,
the
next
one
and
the
route
of
liking.
The
in
factor
would
have
like
you
had
a
lot
of
reasons:
the
neighbor
down
near
the
one
possible
reasons,
but
in
fact,
based
on
the
experience
of
Linda
from
the
network,
there
are
so
many
other
reasons.
So
there's
a
was
our
incentive
pass,
the
protocol
packet
to
some
incentive,
and
so
this
you
know
usual
quickly.
K
Okay,
so
now
there's
the
you
can
see
still
troubleshooting
of
the
Messrs.
So
sometimes
we,
you
will
just
say
alright,
to
say
alright,
who
log
in
the
Reuters
and
to
check
the
nutrient
with
her
one
by
one.
So
this
is
a
time
consuming
and
also
sometimes
an
even
we
check
you
muster
to
comparing
a
lot
of
information
manually,
because
there
is
a
because
the
number
of
the
root
or
the
with
a
package
in
the
field
is
a
difficult.
K
So
that's
what
is
also
the
labor
consuming
and
also
a
days
of
the
data
appreciation,
difficult,
yeah
and
and
also
destiny
of
the
some
luckiest,
the
route
infiniium.
So
that's
the
you,
the
some
usual
the
failures
change
at
the
time
very
quickly,
even
the
time
consuming
and
labor
consuming.
When
we
found
that
some
days
we
lose,
but
the
usually
will
change
the
immediately
you'll
have
to
locate
again
so
they
say
also
there's
a
calendar
for
the
use,
a
steam
troubleshooting.
K
K
K
To
problem
some
new
bianchi
messenger
for
other
control
protocols,
so
this
has
some
other
one
here,
but
the
one
here.
So
that's
me
of
the
maybe
this
is
the
last
implementation,
and
so
there's
neither
father
and
also
the
actual
deployment
of
the
Bianchi,
so
based
on
the
extension
of
the
PM
here
for
I
am
King,
so
it
can
be
incremental
in
deployed.
So
this
is
the
other
one
here,
but
the
is
the
challenging
p.m.
he
uses.
The
other
begin.
You
need
to
have
super
safe,
equal
support,
but
now
you
extend
either
for
other
control.
K
L
K
L
K
L
L
L
K
Your
way
for
the
termination
of
message-
okay,
in
fact,
we
think
of
a
chance.
In
fact,
once
this
will
work
had
been
posted
in
will
idea.
We
get
a
lot
performance
in
the
Middle
East
when
this
at
that
time,
I
need
to
be
live,
made
the
many
affairs
so
there
the
cannot
have
replies
or
the
comments,
the
entire,
so
I
think
the
chance
to
say,
thanks
to
you,
see,
Randy
Jeff
I
in
a
robot
Wilton
robot,
her
team
and
correct
for
the
running
performance.
K
L
K
Lies
to
explain
more
the
sort
of
our
history
for
reference.
We
also
been
able
that
you
forget
that
history
to
repeat
it,
but
we
in
fact
we
are
also
half
of
the
history.
You
know
past
the
years
we
are
involved
in
in
March,
walk
in
the
Europeans
name,
net
conquer
yeah,
even
the
deepening
state,
but
then
experience
favor
the
earth
for
complementary
solution
combined
with
the
existing
work.
K
We
even
with
this,
we
solve
the
network,
ovm
issues
better
and
a
blast
away
so
that
he
would
pro
post
read
to
refine
this
draft.
So
we
will.
This
will
done
in
the
introversion
okay.
So
here
we
explain
this.
Why
not
that
your
PC
and
young
so
does
the
in
fact
in
the
parliamentary
net,
was
at
elementary
for
a
walk.
We
missed
the
identifier.
Was
the
control
point
in
elementary
and
was
the
management
in
elementary
from
this,
the
our
detonation?
We
seek
control.
K
K
The
second
one,
you've,
the
theta
interaction.
So
there's
a
for
the
manage.
My
name
is
the
Slater's
today,
/
sedate,
her
retrimmed
and
configuration
manipulation,
but
for
the
monetary
is
not
an
incorrect.
Him
is
a
unidirectional
data,
retrieved
chemical
sensitivity
that
either
for
the
man
in
the
play.
So
now
that
we
tried
to
improve
the
performance,
but
from
our
point
of
view
is
the
note
here,
so
they
were
not
a
very
tiny
sensor
to
button
for
the
troubleshooting
for
the
control
plane.
L
K
More
hyoe
sensor
team
and
they
a
seminar
for
the
tinker,
update,
the
sequencing
and
the
days
of
the
Expos
I,
think
they
say
with
the
other,
is
out
no
to
derail
my
sensor
and
the
further
data
modeling.
We
synced
as
though
this
one
we
use
the
young
model,
but
for
the
Islam,
when
you,
the
header,
plus
that
your
way.
L
L
K
Of
the
trial-
and
this
is
the
PPU-
yes
in
fact,
we
try
that
will
simulate
to
simulate
the
work
of
the
army
using
your
PC
and
a
yacht.
We
same
thing
is
a
little
difficult
because
of
many
troubleshooting
work
may
be
done
based
on
the
protocol
packets,
but
then,
if
we
will
use
a
young
model
monitoring,
there's
a
package
so
that
we
must
let
defend
a
young
model.
K
K
They
say
so
we
think,
and
also
the
past
days
of
the
packet,
also
the
time
consuming.
So
we
seen
her
with
directory
to
export
the
PPU.
He
is
not
necessary
to
pass
it
directly
in
standard
with
the
analytics
with
sedation.
So
the
ask
to
the
station
to
pass
the
original
prototype
heads
so
that
may
be
and
analyse
good
cause
for
some
failures
of
the
control
protocol.
K
They
usually
seen
two
minute.
Okay,
so
there's
the
last
one,
they
say
when
not
a
period
in
the
state.
Firstly
missing
the
beginning:
the
state
is
a
lot
of
other
purpose
of
the
monetary,
though
the
though
the
Fate
a-w-two
cases
may
be
it
done
by
the
beginning.
The
state,
by
the
way
of
doing
the
same,
could
be
pinning
state
the
purpose
of
monitoring.
We
think
the
principle
to
Aqaba
the
operation
protocol
and
the
monitoring
protocol
is
the
basic
of
principle.
K
K
Say,
oh,
we
synced
as
they
they
are
given
instant
difference
between
the
control
and
elementary
are
the
management
elementary.
But
our
we
also
drill
that
much.
We
overlap
and
also
the
other
cases
appear
the
to
justify
the
necessity
of
the
unarmed
king
but
the
day
so
does
not
a
new
school
with
the
possibility
of
other
measures
missing.
That
may
be
a
combined
a
solute
solution.
So
together
we
before
better
solution.
I
know
for
the
past
years
we
learned
the
form
the
SQL
we
seen
at
the
beginning.
K
The
only
would
be
base
what's
the
management,
what
control,
what
the
wind
and
follows
the
lessons.
So
that's
what
sometimes
combined
this
management
controlling
even
more
Messrs
analytics.
So
there's
the
usual
for
better
solution
is
aligned.
So
there's
neither
maybe
had
a
different
a
choice
because
of
the
different
is
under
different
requirement.
K
L
H
K
This
is
about
continuity.
The
spent
address
is
measurement
chasm
architecture
chasm.
It
is
a
general
reference
architecture
designed
to
as
a
basis
for
developing
human
eyes
address
moment
and
for
Martinez
kisses.
Actually,
this
fact
has
originated
from
several
other
documents,
so
this
is
output
of
March
aside
and
when
his
models,
it
is
very.
We
hope
that
the
just
posed
in
other
work
can
be
automatically
ceremonies,
so
the
time
can
be
networked.
Environment
can
be
reduced
and
hopefully
that
this
can
improve
address
usage.
K
Idea
one
so
we
service
elements,
the
contract
has
a
beam
device
based
on
the
comments.
Some
technology
had
been
changed,
such
as
API
manner
and
as
well
jobs.
Reference
were
replaced
with
the
latest
ones.
At
least
we
need
to
handle
this
hazmat
unit
to
handle
containers
being
as
elements
refer
to
another
in
progress
has
needed
of
this
tab
solutions.
K
We
also
need
some
other
refinements,
for
example,
crack
some
repair
errors
and
instruct
the
component
structure
is
moved
close
to
the
reference.
Octet
renew
section
three
so
measure
here
is
that
also
we
want
to
mention
is
that
actually
we
have
implemented
the
prototype
of
a
chasm
one
two
years
ago
and
following
that
I've
drawn
this
one
and
we
have
cutouts
before
the
trail
network,
so
this
gets
trapped.
We
have
a
unit
case
which
is
visited
by
Italia
telecom
service.
At
amendments.
K
K
L
K
And
pride
operators
so
you've
stopped.
We
summarized
some
requirements
from
a
prize
operators.
The
first
one
is
that
it's
just
part
of
magic,
correlation
of
address
block
and
the
single
dress
simultaneously
and
using
a
friendly
interface
when
we
need
to
acknowledge
and
address
usage
in
the
soul
having
to
detail
of
the
lower
layer,
configuration
and
the
action.
Canopy
cannot
get
exposed
and
manually
parameter,
restarts
Konishi,
also
supported
in
chasm.
K
We
recent,
as
mentioned
another
wave,
see
the
comments
in
the
last
meeting
and
we
also
reserved
not
comments
in
the
mail
list.
So
I
here
only
shows
some
of
them.
The
first
of
all
the
first
one
is
that
comments
from
training
dome.
There
was
lots
of
comments
and
since
it
has
been
discussed
with
many
as
ever
now
to
illustrate
them
one
by
one.
K
The
next
step
necessary
of
will
continue
to
refine
document,
based
on
your
comments
and
annek
revolutions,
no
confusion
a
welcome,
and
specifically
our
emphasis
efforts
will
be
given
to
enterprises,
operators
and
finally
scenario.
So
we
also
concern
that
to
know
whether
this
document
can
be
authoritative,
resonating
as
a
working
prototype
comments.
H
D
L
It
sounds
like
you're
proposing
making
a
database
with
an
API
I,
don't
understand
why
that
is
a
generic
or
mediate
standard
thing
or
see.
You're
gonna
work
for
me
and
you
at
the
same
time
like
there's
part
of
like
deploying
stuff
when
you
build
the
database,
that
has
a
bunch
of
identifiers
and
the
IP
address
of
your
VLANs
are
back
yes.
Well,.
L
K
L
Totally
different
than
IBM,
whatever
the
heck
it
is,
but
typically
different
than
Oracle's
product
or
whatever
like
they
all
do
something
different
everything
I
built.
This
does
stuff
that
uses
my
internal
up
to
structure.
I.
Imagine
that's
what
happened
everywhere.
That's
what
happens!
That's
what
happens
everywhere,
I've
seen
as
dtu's
some.
B
This
topic
has
been
discussed
for
quite
a
while
and
I.
Remember.
There
was
something
like
a
semi
before
an
official
meeting,
probably
couple
of
IVF
cycles
ago,
and
at
the
time
there
was
one
interesting
topic
raised
by
the
registrar's
to
try
to
define
an
interface
where
potential
user
of
a
blog
can
request
a
lot
from
a
registrar
and
I'm,
not
talking
about
the
level
as
as
a
address
block,
wheezing
or
acquiring
mechanism,
and
that
seems
to
be
of
that
possible
value.
B
At
least
looking
at
the
developments
in
the
industry,
trying
to
standardize
the
internal
implementation
of
how
do
I
allocate
an
assignment,
distribute
addresses,
identify
us
what
not
it's
an
implementation.
The
make
ITF
doesn't
seem
to
be
the
right
place
to
standardize
some
by
the
vendors
for
some
internal
implementation.
For
that,
even
besides
being
caught
the
right
place,
that's
just
not
possible
because
each
and
every
user
that
the
identifiers
address
a
locator
mechanisms
are
so
different
and
so
specific.
B
The
environment
in
which
you
use
that
that
it's
hard
to
talk
about
standardizing
something
otherwise
well
and
therefore
I,
would
suggest,
probably
that
you
should
explore
the
space
of
interacting
for
the
address
registrar's
more.
That
was
one
of
the
topics
discussed
in
in
in
that
your
interim,
and
it
doesn't
forget
to
be
on
on
in
this
presentation
here.
That
is,
that
seems
to
be
the
real
problem.
What
you
are
describing
here.
B
B
My
my
questions,
I
wanna,
know
the
plan
to
deliver.
The
customer
like
you
to
draft.
Is
this
their
only
job?
Do
you
wanna
standardize?
Also
because
usually
the
framework
you
have
two
is
a
kind
of
support
document.
It's
not
necessarily
been
standardized
and
if
your
goal
is
to
standardize
the
interface,
so
you
may
want
to
deliver
a
young
model.
B
K
K
K
L
K
K
N
K
Than
before,
as
do
you
want
service
opportunities,
the
best
you
want
means
that
service
academic,
for
example.
We
need
to
add
new,
or
sometimes
new
branches,
just
anyways
sometime
in
may
change
over
time
in
holidays,
and
we
also
need
to
decrease
or
increase
the
cloud
service
functions
and,
of
course
it
is.
We
need
a
sec
amendments,
so
other
kind
of
pictures
requires
automation
of
an
automation,
so
the
service
academy
requirements
should
have
been
obstructed
obstructed.
K
K
So
feels
about
the
sd1
service
model
same
to
actually
be
as
we
SM
at
USM
estimated
model
adopted
or
emote
architectures,
and
it
has
two
major
components
at
the
first
line:
segment
network
that
for
Kevin
enterprise
as
t1
and
make
has
model
virtual
network
which
cannot
which
may
be
separately
and
then
the
second
way
is
policy.
Policy
could
be
applied
to
the
segment
or
percent
yep
allocation
of
low
granulate
is
so
give
his
models
the
first
one,
the
first
permanent
sites
such
means
that
custom
office
looking
at
specific
locations.
K
That
may
has
a
following
attributes:
for
example
the
increment
types,
the
transport
links,
such
as
access
types,
IP
addressing
and
the
protocols
the
second
one
sacramental
network.
We
has
been
missionary
which
will
be
discussed
later
later
and
the
third
one,
the
policy
policy,
many
people
over
the
past
election
policy
or
quality
of
service
products
and
a
security
policy.
K
K
So
the
parameters
of
segments
network
included
apology,
so
the
proposed
the
model
here
supporter
happens
book.
A
new
training,
topology
and
here
also
set
lists
saturdays
and
under
settings,
is
an
analog
leased,
which
means
that
a
set
of
network
that
attached
to
this
segment
from
different
locations
but
belong
to
the
same
segment
and
work.
K
The
page
at
the
permanence
of
a
network
needs,
including
you
know,
to
expose
IP
address
and
the
protocols
so
policy
earliest
era
policy,
whose
openly
called
about
the
past
energy
policy.
There.
Any
parameters
in
this
policy-
first
wise
application
of
classification
and
the
second
wise
application
of
low
air
Zoe,
the
third
one
is
primary
past
or
second
pass
so
for
given
traffic
will
classify
the
traffic
based
on
this.
K
The
first
parameters
will
classify
the
different
service,
such
as
voice
when
you
came
and
some
critical
critical
data-
and
we
also
need
to
measure
the
a
sorry-ass
area
of
this
of
this
past.
Where
more
is
a
delay,
jitter
or
packet
of
the
application
of
loss,
then
the
password
is
matching
the
face
of
this
feathers,
smoother
traffic
to
appropriates
the
transport
network
link.
K
D
Thank
you
for
this
interesting
I'm,
obviously
familiar
without
you
SM
and
l3s,
and
levels.
What
I'm
trying
to
understand
what
this
one
is.
Who
are
the
users,
so
somebody
builds
novel
and
sends
it
to
somebody
else
who
consumes
it
in
May,
LTS
m
and
L
3
sm
cases,
it's
the
customer
talking
to
the
provider.
M
D
K
J
K
K
J
B
B
Most
probably
in
routing
as
that
is
much
closer
to
the
routing
domain.
However,
from
the
usability
point
of
view,
those
models,
they
are
far
closer
to
the
service
models
in,
in
the
knowledge,
the
knowledge
of
idea,
so
I
cannot
give
you
a
definite
advance
of
age,
belong.
I,
think
it
should
be
iterative.
Do
some
experimentation.
It's
been
a
few
revisions,
see
how
that
fits
in
the
world
with
honor,
and
maybe
that
can
be
published
as
and
as
as
an
irresponsible
man
without
any
formal.
H
I
I
That
so
this
is
our
administrivia
slides.
Once
again,
the
note
well-
hopefully,
you
have
already
noted
this
well
when
it
started
off
with
pops
aw
gee.
Please
make
sure
that
you
look
at
this
and
understand
it.
It
says
all
sorts
of
important
things
which
I
am
NOT
going
to
try
and
interpret
for
you.
You
should
discuss
this
with
your
lawyer.
Slash
Ravel,
slash
whatever
welcome
to
UPS
area.
I
We've
already
done
this,
but
I'm
one.
This
is
Agnes.
We've
done
the
note
world
blue
sheets.
Please
make
sure
you
have
already
signed
the
blue
sheets.
Otherwise,
next
time
we
get
a
small
little
room,
we
have
a
jabber
screen,
I
believe
we're
scribing,
better
Thank,
You,
Scudder
and
Joe
Clark
is
doing
minutes.
I
Thank
you
Joe
and
here
earth,
where
the
meeting
slides
are
so
we
are
currently
during
the
administration,
but
and
where
could
I
swap
the
order
of
the
next
fit
around
so
that
Russ
come
on
we'll
go
next
and
then
after
that,
that
will
be
Ignace
I.
Don't
think
anybody
will
care,
but
does
anybody
object
or
have
any
objective?
Ashing
didn't
think
so.
So
let
me
just
get
the
slides
queued
up.
L
I
M
I'm
retired
I
can
write
this
all
up
because
it
seemed
to
me
it
should
get
written
up
because
we
don't
want
to
do
it
again
and
I'd
like
being
retired
too
much,
and
so
I
never
got
it
done.
And
then
you
guys
decided
to
have
an
idea
pretty
close
to
you
know
where
I
originally
came
from
and
then
even
where
I
was
currently
living,
so
I
am
currently
living,
so
I
thought
well,
maybe
I
always
come
by
in
and
present
it
to
you
guys.
So
they
know
I've
written
down
that
so
I
I
suggested
the.
L
M
Area
directors
and
the
ops
and
management
area
directors
then
I
get
to
talk,
and
they
immediately
said
yes,
which
meant
oh
dear
I,
was
gonna,
actually
have
to
do
the
slides,
so
so
I
did
this
lion
sent
a
man
and
Here
I
am
so
there'd
been
some
interesting
events
in
the
1970s,
80s,
90s
and
I.
Think,
though,
one
of
the
vents
I'm
going
to
talk
about
even
occurred
after
2000,
we
didn't
always
know
what
we
were
going
way
back
when
when
we
started
doing
this
building
this
thing
called
the
Internet.
M
Some
of
the
knowledge
of
things
we
did
wrong
is
in
the
minds
of
old
people,
and
some
of
us
old
people
retire
two
years
ago,
and
some
of
us
haven't
quite
retired
yet,
but
we'll
you
know
at
some
point
into
your
future.
We're
not
going
to
be
here
forever,
so
I
thought
it'd
be
a
good
idea
to
write
it
down.
So
I
got
a
bunch
of
examples
written
down
here.
One
thing,
I
want
to
say,
is
I
made
an
effort
in
these
slides
to
try
to
be
a
vendor-neutral
for
several
reasons.
M
There's
no
point
in
pointing
fingers.
In
many
cases,
the
stuff
that
got
deployed
got
deployed
specifically
because
it
was
the
best
stuff
what
was
available
so
basically
they
the
equipment
that
did
not
collapse
like
this
was
was
was
even
worse.
So
you
know
that's
a
reason
to
not
point
fingers
and
there's
nothing
to
be
gained
by
it.
M
In
the
1970s,
the
ARPANET
was
routing
on
a
distance
vector
routing
protocol.
That
Hill
ran
into
some
of
the
troubles
that
dis
inspector
protocols
used
to
run
into
so
they
came
up
in
the
late
1970s
with
something
called
the
new
ARPANET
routing
protocol
back
then,
the
ARPANET
was
running
at
much
lower
bandwidth
than
we
have
today.
M
I
think
that
the
main
wide
area
links
were
56
kilobits
per
second,
given
that
much
bandwidth
available
in
me,
like
the
core
main
backbone
links,
you
want
to
be
a
little
careful
about
your
use
of
bandwidth
for
control
protocols,
so
the
sequence
number
space
on
the
new
ARPANET
routing
protocol
against
link
state
routing
protocol.
So
you
know
these,
you
know
maps
of
1
nodes
view
of
its
local
apology.
We
could
flood
it
around
that
was
flooded
around
using
a
sequence
number
that
was
3
bits
given
a
3-bit
sequence
number.
M
That
means
you
only
have
any
possible
values,
which
means
you
know,
you're
going
to
run
off
the
end
and
have
to
go
back
again.
So
it
was
a
circular
space,
and
so
you
know
whether
Able's
before
the
Ouray
was
after
me,
it
could
be
figured
out
by
seeing
which
way
it
was
closer
or
round
your
circular
space
way
back
then
a
switch
happened
to
crash
when
it
came
back
up
again.
M
If
somehow,
whoever
implemented
that
switch
thought,
it
would
be
great
fun
to
forward
all
the
packets
that
were
in
the
queue,
because
maybe
some
of
them
would
still
be
useful.
So
we
did
well,
it
turns
out
one
of
the
packets
in
the
queue
and
when
one
particular
switch
came
back
up
again
was
an
old
routing
update
that
happened
to
be
exactly
halfway
around
the
circular
sequence,
space
from
an
update
that
was
in
processed
at
the
time.
M
So
there
were,
therefore
you
know
that
one
old
update,
the
one
that
was
only
slightly
old
and
the
brand-new
update.
All
three
of
those
were
all
going
around
at
the
same
time,
and
they
just
so
happened
to
be
so.
Their
sequence
numbers
a
B
and
C
came
out
as
a
squared
and
B
and
B
is
greater
than
C
and
C
is
greater
than
a
so
updated.
A
replaced,
update
thing
and
I
think
replacing
and
c.replace
day,
and
the
three
updates
chased
each
other
around
the
arpanet
as
fastest.
Witches
could
forward
them.
M
So
three
of
things
chased
each
other
around
the
ARPANET
for
a
few
hours.
Fortunately,
back
in
those
days,
the
telephone
network
did
not
run
over
the
Internet,
so
it
was
possible
to
pick
up
a
telephone
and
call
somebody
and
say
I.
Don't
like
your
switchback,
a
switch
please.
So
somebody
was
able
to
physically
go
to
each
packet
switch
and
unplug
it,
and
so
they
were
able
to
turn
off
all
of
the
packets
which
is
accept
to
well
once
they
got
it
down
to
only
two
packet
switches
we're
still
up.
M
You
know
up
roaming
update
and
with
only
two,
you
can't
chase
each
other
anymore,
because
one
comes
out
ahead
of
the
other,
and
so
then
there
was
only
one
and
then
you
could
plug
all
of
your
switches
back
in
again,
as
you
might
imagine,
if
this
would
happened
today
with
you
know,
100
or
maybe
even
a
thousand
routers
in
your
network,
it
might
be
quite
unpleasant.
It
would
be
even
more
unpleasant
if
your
phone
system
went
over
the
same
network,
because
how
would
you
call
people
and
say
go
unplug
near
switch
thanks?
M
Oh
he's
faster
than
me
in
the
early
I
thought
it
was
the
early
1990s.
It
was
like
very
early
1990s.
There
is
a
network
out
there
with
a
you
know,
stable
network.
What
was
working
well
with
a
small
number
of
the
biggest
routers
that
could
be
bought
at
the
time
and
I
a
large
number
of
little
railroads
that
were
all
single
home
to
the
court
and
the
service
provider
thought
I,
really
care
about
reliability.
M
What
happened?
A
router,
in
this
case
the
router
at
the
top
in
the
middle,
had
a
leak
state
advertisement
was
sent
out
and
it's
all
that's
new
purrs,
honest
neighbors
saw
all
my
other
neighbors
will
want
to
hear
that
too,
and
forwarded
on
a
whole
bunch
of
LS
aids,
identical
ones
all
showed
up
in
the
same
place
at
the
same
time,
and
there
was
too
many
identical
updates
arriving
in
one
place
at
one
time
and
the
router
couldn't
handle
it,
so
it
just
sort
of
keeled
over
instead.
M
So
one
of
the
lessons
is
that
buffering
and
discarding
duplicate
link-state
advertisements
is
actually
a
hard
part
of
almost
an
ayah
science.
We
did
not
break
that
I.
Remember
at
the
time
people
complaining,
oh,
the
dykes
were
so
slow
and
then
somebody
looked
at
in
detail
know
that
Dijkstra
wasn't
slow,
no
I
I
couldn't
even
imagine
the
time
how
banks
were
could
be
that
slow,
but
it
turned
out.
It
was
dealing
with
redundant
link
state
advertisements
noticing
there
the
redundant
and
throwing
them
away
would
slope.
A
similar
issue
happens
with
IP
over
ATM.
M
Some
of
the
there
was
a
time
in
the
past
where
ATM
switches
and
frame
relay
switches
were
faster
than
routers,
and
so
people
would
build
networks
with
ATM
switches
and
then
attach
the
routers
in
Britain
with
a
full
mash,
and
that
meant
that
every
router
had
every
other
router
and
then
network
as
its
immediate
neighbor.
That
was
a
little
inefficient.
M
Also
with
all
Athan
is,
is,
and
we
added
mesh
groups
to
handle
that
now
this
one
I
know
was
1992
because
I
remember
where
I
was
and
what
was
happening
at
the
time
which
I
will
talk
about.
But
somebody
decided
a
network
operator
decided
to
grab
me
and
pull
me
into
the
lab
and
say
look
what's
happening
so
after
some
analysis
would
turned
out
what
was
happening
is
that
a
neighbor
were
a
network.
M
And
so,
if
you
fell
behind
in
the
processing
of
the
whole
packets,
a
timer
would
go
off.
Saying
you
haven't,
got
a
little
packet
from
this
neighbor
for
a
while.
He
must
be
now
well,
in
fact,
you
had
the
updates.
You
know
the
hello
back,
because
they
were
sitting
in
a
queue
and
I'm
looking
at
them
yet
well,
once
the
timer
goes
off
inside
okay
he's
gone,
I'll
send
out
another
link,
saying
advertisement
saying
that
neighbor
is
gone,
so
a
few
routers
got
slowed,
decided
to
send
out
these
updates
that
their
links
were
down.
M
That
meant
that
there
was
more
work
for
more
of
the
only
other
motors
to
do.
They
all
started
doing
too
much
work
on
processing
the
links,
data
updates
and
all
notice
that
they
didn't
gotten
hellos,
and
so
they
all
disconnected
all
of
their
links.
Every
link
in
the
network
disconnected
now
the
routers
had
nothing
to
do
so
they
caught
up
and
since
they
caught
up,
they
brought
up
all
their
links.
With
their
neighbors
sent
out
the
link
state
advertisements,
everything
came
up
and
worked
fine,
except
for
another
problem.
M
All
the
links
had
come
up
at
the
same
time
and
they
had
fixed
timers
in
terms
of
when
they
would
react.
Ver
ties
their
advert
the
next
day,
packets,
so
20
minutes
later.
Everybody
sends
out
an
update
at
the
same
time,
because
it's
20
minutes
past
when
it
came
up
well,
that
means
everybody
gets
congested.
M
Nobody
processes,
all
those
all
the
links
go
down.
They
all
come
back
up
again
because
nobody
has
anything
new
and
20.
Minutes
later
all
happens
again,
so
you
know
at
some
point
in
1992.
Somebody
actually
grabbed
me
and
pulled
me
down
to
the
lab
and
forced
me
to
sit
and
watch
for
an
hour
as
everything
went
down
every
20
minutes
and
it
all
came
back
up
again.
It
was
happening,
then.
M
Fun,
so
that's
what
I
did
1992.
It
only
took
me
an
hour.
So
the
solution,
you
optimize,
your
protocol
processing,
you
prioritize
the
hellos.
You
do
the
looms
first
before
you
do
anything
else
and
you
randomize
the
timer.
So
if
a
bunch
of
stuff
happens
at
once
you
it
doesn't
happen
all
that
once
again,
sometime
later
this
was.
M
So
at
some
point
one
of
those
links
that
caused
the
partition
came
back
up.
Probably
a
human
without
you
know,
replug
something
in
this
somebody
knocked
out
or
whatever
caused
the
problem.
As
soon
as
that
link
came
back
up,
the
ATM
switch
on
each
side
of
that
partition.
They
try
to
do
database
thing
right,
so
each
switch
sends
everything
it
knows
to
the
other
switch
that
call
and
then,
of
course,
the
switch
that
receives
all
that
sends
it
to
all
their
neighbors
and
they
flood
it
through
there.
Their
side
of
the
partition
that
apparently.
M
Side
of
the
partition
had
enough
link-state
advertisements,
but
having
them
all
arrived
at
once
caused
all
the
routers
on
the
other
side
to
become
too
busy,
and
so
they
so
sometime
in
the
mid-1990s,
an
entire
large
service
provider
somewhere
in
the
US
all
went
down
and
came
back
up
again
now
to
the
credit
of
the
software
engineer
who
written
this
software,
they
did
randomize
their
timers.
So
when
it
came
back
up
again,
you
know
20
minutes
later,
when
it
was
time
to
send
on
all
your
links,
their
advertisements
again.
M
M
I'm
pretty
sure
it
was
January
2003,
where
the
slammer
worm
pit
so
I
assume
that
anybody
who
was
managing
the
network
in
January
2003
can
confirm
whether
it's
right
or
not,
although
I
think
I,
do
know
that
verifying
it
was
right,
very,
very
rapidly
propagating
worm
that
doubles
every
eight
seconds.
So
you
know
from
the
time
you
notice
it
until
it's
a
disaster
is
not
very
long.
M
Slammer
worm
propagated
by
picking
an
IP
address
at
random
and
trying
to
attack
it,
and
if
it
could
get
in
it
good
and
if
not,
it
would
pick
another
one
at
random
and
try
to
attack
it.
So
some
of
those
randomly
chosen
IP
addresses
just
happened
to
be
the
IP
address
of
a
router,
so
there
was
lots
of
traffic
aimed
at
the
router,
as
well
as
a
lot
of
traffic
aimed
at
everything
else.
So
the
routers
processors
were
busy.
The
links
were
busy.
M
It's
from
I
heard.
It
is
not
clear
whether
or
not
that's
a
CPU
congestion
or
link
congestion,
but
I
think
both
we're
going
on
at
the
time
again
paradise
the
hellos
get
priority
to
the
loads
and
then
next
to
the
routing,
packets
and
the
network
management
packets,
and
on
the
after
that,
do
you
bother
without
Google
traffic?
M
This
is
a
fun
problem
that
happened.
Also
sometime
in
the
1980s
is,
is,
and
OSPF
were
designed
defined
in
the
mid-1980s.
So
it
was
a
time
when
processors
were
somewhat
slower
than
now
and
they
were
forwarding
packets.
So
the
original
specs
were
trying
to
minimize
the
strain
on
the
CPU
and
trying
to
optimize
the
flooding.
So
the
ayah.
M
L
M
M
I
Esaias
had
been
salted
for
several
years,
and
most
of
the
biggest
service
providers
in
the
world
and
had
is
is
running
for
at
least
a
couple
of
years
and
working
well
when
a
problem
with
her
as
networks
got
faster,
write
more
packets
somewhere
on
some
router
somewhere
in
a
network
which
won't
be
named.
There
was
an
interface
that
was
just
thrashing
packets.
It
was
just
changing
bits.
If
you
change
one
bit,
the
checksum
will
always
catch
it.
M
If
you
change
a
bunch
of
bits,
some
packets
will
get
through,
and
it's
about
1
in
65,000
that
will
get
through.
So
you
change
one
bit.
You
know
you
change
several
bit
randomly
in
several
updates
and
after
you've,
randomly
trash,
65,000
or
so
updates.
Something's
gonna
get
through
well.
Some
of
those
may.
M
Bits
that
cause
the
sequence
number
to
be
wrong
and
it
gets
thrown
out
and
whatever,
but
one
not
true,
which
checked
the
sequence
number
and
got
passed
the
checksum
and
got
passed
everything
the
outer
wrapper
was
fine.
The
fact
he
got
forwarded
flooded
out
and
then
the
router
looked
at
the
inside
found
a
length
field
out
of
range
and
crashed
and
the
fun
thing
about
this:
a
couple
of
fun
things.
Why
did
you
first
forward
the
packet?
Then
you
look
at
it
and
crash.
So
all
your
neighbors
get
to
crash
too
and
another
fun
thing.
M
This
is
a
different
problem.
Now
the
distance
vector
count-to-infinity
I.
Think
probably
you
guys
know
this
well
enough.
I
could
have
done.
You
know,
15,
slides
on
it
and
you're
probably
glad
that
I
only
had
to
I
think
the
problem
is
pretty
well
understood.
You
have
a
destination,
a
the
router.
Next
one
says
I
can
get
to
a
it's.
Only
one
hop
away.
The
next
router
here
is
that
says,
apply
some
get
to
a
it's
two
hops
away
the
routers.
M
Next,
to
that
say,
I
can
get
three
hops
away,
however,
just
when
they
say
this
and
when
they
notice
it
is
going
to
be
a
little
bit
random
as
to
the
timing
of
events.
So
if
any
were
to
go
away
at
some
point
that
guy
in
the
middle
might
say,
I
can't
get
to
a
you
know:
it's
not
two
hops
anymore:
it's
I,
just
I
can't
get
there
and
those
two
routers
over
on
the
right
might
notice
that
at
different
times,
so
one
of
them
might
immediately
notice.
M
Oh,
he
said
he
can't
get
there,
but
this
other
neighbor
said
he
can
get.
There's
three
hops
away.
So
I'll
tell
him.
I
can
get
there,
it
is
four
hops
away
right
and
depending
on
the
order
in
one
direction
or
the
other,
you
can
start
counting
to
infinity
around
that
loop,
and
so
you
know
I
just
assumed
one
particular
order
in
which
things
were
noticed.
So
the
router
on
the
upper-right
says
I
can
get
there.
M
It's
three
hops,
the
guy
at
the
bottom
hears
that
says
it's
four
hops,
the
guy
in
the
middle
says:
okay,
I
can
get
there.
It's
five
hops
right
says:
I
can
get
there
at
six
offs
and
you
count
to
infinity
or
rope
handles
this
by
setting
infinity
to
a
small
number.
15
is
infinity,
so
you
don't
have
to
count
to
15
it's
a
little
bit
ugly.
A
bunch
of
fixes
have
been
proposed
and
some
have
been
deployed.
There
were
Leeson
interesting
augmentation
of
this
problem
and
Jace's
problem
wasn't
bad
enough.
L
M
Friendly
university,
professor
and
some
students
appeals,
but
together
these
things
called
fine
swell
routers,
which
used
a
delay
based
routing
in
the
core
of
the
NSFNET
between
these
funds
walls.
So
they
looked
at
the
real-time
queuing
delays
and
then
on.
The
outside
of
the
NSFNET
routing
was
done
with
rip
and
they
mapped
one
to
the
other.
So
if
from
one
edge.
M
That
was,
let's
say
three
hops
away-
that
three
hops
would
be
mapped
to
a
particular
delay
and
advertised
into
the
core
that
delay
would
get
added
to
the
delay
of
whatever
the
queues
were
in
the
NSFNET
somewhere
on
another
side
of
the
NSFNET.
They
would
have
gotten
to
a
slightly
higher
delay.
They
would
map
that
back
into
a
rip,
hop
count
and
advertise
it
out
on
the
other
side.
Now.
M
One
fun
thing
here
is
with
the
lady
based
routing,
where
you
have
malt
ways
to
get
across
the
rest.
Let's
say,
and
you
have
one
path:
that's
got
very
little
traffic.
The
lanes
are
very
small.
It
gets
advertised
from
the
very
low
metrics.
Another
path
is
more
congested,
so
let's
go
higher
metrics
all
the
traffic
goes
on
the
path.
That's
advertising
low
metrics,
so
they
gets
congested.
The
metrics
go
way
up.
It's
reanalyzed.
M
Later,
a
much
higher
value,
the
other
path
has
gotten
empty
in
the
meanwhile.
So
everything
goes
back
the
other
way.
So,
with
the
delay
based
routing,
you
tend
to
get
this
flapping
back
and
forth.
You
put
that
at
the
core
of
your
NSFNET
and
you
put
work
on
the
outside,
with
the
counting
to
infinity
and
you're,
feeding,
rapidly
changing
up
and
down
metrics
into
rip
on
the
edge.
As
you
might
imagine,
this
did
not
actually
work
very
well,
I,
remember,
being
logged
in
at
the
National
Center
for
Atmospheric
Research,
which
was
just
hosting
a
meeting.
M
It
had
nothing
to
do
with
any
of
these
problems
and
I
was
logged
into
my
computer
in
Cambridge
Massachusetts,
my
home
computer,
and
it
just
froze,
and
it
just
sat
there
for
45
minutes.
I
couldn't
do
anything,
I
couldn't
log
out
and
then
45
minutes
later
it
came
back
and
I
was
logged
in
if
I
walked
away.
Any
student
could
walk
down
brach
by
sat
down
and
started
typing
away
on
my
computer
in
Cambridge
Massachusetts
and
of
course
you
know
the
first
thing
I
might
I'd
log
out
because
I
had
to
do.
M
M
Having
noticed
some
of
this
problem
with
delay
based
routing,
moved
to
a
metric,
which
was
a
linear
combination
of
hop
count
and
delay,
with
the
contribution
of
delay
being
small
enough
that
you
were
really
just
changing
within
one
right,
so
you
you
do
minimum
heart,
but
with
time
you
take
the
rest
delayed
route.
The
is
that
with
56
kilobytes,
which
might
have
gone
a
little
bit
faster
by
then,
but
traffic
demands
going
up
after
a
while.
The
delay
got
large
enough
with
a
linear
combination
of
the
two.
M
What
used
to
be
an
overdamped
system
became
an
under
damped
system,
and
so
they
went
from
nice,
stable
routing
to
again
wild
oscillations
because
of
this
problem
with
the
damping
not
staying
sufficient.
Now
it's
time
for
John
Schneider
to
get
out
there
now,
the
last
time
we
went
through
these
slides,
they
were
a
little
wedged
and
so
John
had
to
talk
to
slightly
convoluted
slides.
But
that's
the
fault
of
translation
between
different
slide
formats.
I.
K
Okay,
so
I
I
guess
this
is
a
good
thing,
didn't
manage
to
come
up
with
as
many
halt
and
catch
fire
problems
as
lost
it.
So
that's
that's
probably
good
that
PGP
doesn't
have
that
many
documented
examples
of
the
whole
thing
falling
over,
especially
because
we've
learnt
it
across
the
whole
world,
but
there
are
a
bunch
of
things
that
I
didn't
have
to
come
up
with
they're,
all
kind
of
in
the
category
of
or
at
least
most
of
them
weren't.
K
K
D
B
K
K
K
K
So
when
the
technology
comes
up,
everything
is
good
traffic
forwards,
Oh
in
the
way
they
accomplished
this
as
they
base
in
the
community,
this
provider,
the
community,
has
the
local
semantics
of
things,
use
this
route
that
I'm
advertising
you
along
this
link
as
a
route
of
last
resort.
If
you
have
any
other
option
to
reach
this
prefix,
please
use
that
instead,
so
they
advertise
that
community,
the
provider
also
gets
the
route
this
way
and
selects
that
route,
and
so
everything
is
good.
The
forwarding
topology
goes
this
way
up
and
around
as
desired
great.
K
M
K
Link
goes
away
that
route
gets
withdrawn
withdrawn
and
therefore
this
rug
gets
advertised
off
that
way,
and
you
know
in
a
short
period
of
time,
you're
back
in
business
boarding
traffic.
You
know
you're
back
up
like
just
the
way
you
wanted
great
now
is
the
fun
part
where
things
get
wedged.
This
link
gets
put
back
in
service,
so
we
just
go
back
to
this
boarding
topology
right.
No,
we
don't
what
actually
happens
in
this
because
remember
like
now,
God,
perhaps
they
got
advertised
this
way
and
because
you
genie
has
the
property.
K
Only
advertise
your
best
path
along
if
this
guy
here
this
provider,
why
happens
to
prefer
the
route
that
goes
to
provider
X?
But
you
know
where
imagine
he
knows
in
this
case,
you
know
happily
continues
to
use
that
route,
and
so
now
the
forwarding
topology
looks
like
this
traffic
goes.
That
way.
This
traffic
goes
that
way,
because
provider
X
never
receives
a
backup
path
for
writer.
X,
never
stops
using
this
path,
and
topology
has
now
stabilized
into
a
new,
stable
topology.
That
does
something
completely
different
from
what
the
customer
wanted.
K
But
sorry
I
mean
you
can't
even
always
multi
stable,
sometimes
it's
just
not
stable
at
all,
so
the
bgp
immunity
oscillation
has
been
around
a
really
long
time.
You
know
there
are.
That
is
any
useful
reference
for
it.
If
you
somehow
haven't
heard
of
this
thing
and
because
it's
been
around
so
long,
we
have
a
solution
for
it
right
wrong,
and
so
so
how
did
this
come
to
happen
if
it
wasn't
because
the
protocol
designers
well,
we
backtrack
and
the
fact
that
it.
K
Think
is
a
hint
that
there
are
two
important
things
that
are
they're
both
important
to
users
of
the
protocol
that
are
not
commensurate
or
you
can't
satisfy
both
the
the
requirement
to
have
a
multi
exit
discriminator,
which
in
case
somebody
doesn't
know,
is
that
an
attribute
that
lets?
You
say
you
know
for
for
traffic
towards
us,
whom
prefer
this
link
over
that
leg.
You
can't
have
that
and
you
and
have
data
hiding,
which
you
get
from
route
reflection
and
have
done
both
work
and
that's
because
the
route
selection
process
assumes
total
ordering.
K
K
K
And
there
are
actually
some
some
parallels
between
this
and
the
case.
Roz
was
talking
about
for
flood
and
then
I
check
the
validity
of
the
data
you've
already
flooded.
So
we
do
GP.
We
have
these
things
called
optional,
transitive
attributes
they're
great,
they
make
the
protocol
extensible,
but
they
also
mean
that
what
can
happen
is
you
can
inject
a
route
into
the
computer
policy
somewhere.
It
gets
transitive
by
the
whole
bunch
of
routes
or
routers
that
have
no
idea
of
what
the
data
is
inside
of
there.
K
K
They
all
look
at
it,
and
we
say
this
attribute
is
terrible.
It's
completely
malformed.
My
peer
must
be
insane
and
resetting
the
session
right
now
I'm.
What
I
was
you
know?
Good
intentions
are
terrible
things,
because
the
protocol
designers
have
a
good
intention
that,
if
your
peers
insane,
because
PGP
is
a
purely
in
Furman
Alberto
call
it's
really
hard
to
it's
impossible.
In
fact,
to
recover
properly
from
from
do
synchronization.
K
The
only
safe
thing
you
can
do
is
reset
the
session
and
start
from
scratch,
but
of
course
that
doesn't
make
sense
if
the
the
person
who
injected
with
the
idea
that
it
was
some
way
off
across
the
internet,
so
they
pretty
much
think
the
only
good
thing
about
this
is
that
we
eventually
realized.
That
was
a
terrible
idea.
Yeah.
L
K
H
K
You
can
take
simple
building
blocks
and
it's
really
surprisingly
complex
emergent
bidding
of
yours,
extensible
protocols,
you
know
PGP,
is
famously
extensible
and
it's
also,
you
know,
really
really
simple,
but
the
fact
that
it's
so
extensible
means
that
we
get
lots
of
little
extensions
coming
from
different
places.
People
don't
consider
how
they
will
interact
and
when
they
interact,
sometimes
they
do
serve.
K
K
This
is
the
case
or
the
that
that,
where
we
have
their
parallel
is
is
having
data
that
is
sometimes
opaque
and
sometimes
not
is
sometimes
really
terrible.
So
the
words
sometimes
in
protocol
design
should
maybe
sometimes
be
considered
a
red
flag
and
reconsidered
whenever
you
find
yourself
using
it
and
finally
I
just
really
like
that,
you
know
short
paper
on
horses,
better,
that
you
can
find
by
googling.
It
and
I
think
that
you
know.
M
I
just
have
two
slides
left
if
we
can
succeed
in
getting
along
okay.
There
are
other
examples
that
I
have
not
bother
to
write
up
as
I'm
sure
some
people
in
this
room
know
there
have
been
cases
of
operator
errors,
distribution
of
full
I
made
you
free
routes
into
the
IGP
is
not
come
across
very
well.
Sometimes
in
the
past
we
serve
already
mentioned.
That
is,
is
and
OSPF
are
real-time
systems.
You
know
the
right
thing
way
too
slowly.
M
You
have
a
problem
and
if
you
put
three
hundred
thousand
or
more
GP
routes
into
yeah,
you
might
end
up
the
right
thing
to
normally
I've
been
some
hard
coded
scaling
limits,
as
well
as
other
forms
of
scaling
limits
there
and
some
some
data
on
the
internet
about
a
signaling
system,
7
failure.
That
was
quite
catastrophic.
M
That
happened
a
while
back
I'm
curious
as
to
what
sort
of
similarities
there
are
between
that
failure,
and
some
of
the
failures
we've
seen
I've
heard
many
rumors
that
most
of
us
have
noticed
that
it's
possible
for
entire
network
to
fail
at
once,
and
sometimes
we
don't
necessarily
want
to
talk
about
it
publicly.
So
whether
there's
other
ways
that
things
have
failed,
that
I
didn't
talk
about,
I,
think
it's
likely
and
I
did
not
mention
the
word
multicast
yeah.
M
M
You
know
they're
talking
about
multicast
in
general
from
the
outside
of
the
scope
of
this
talk.
So
then
my
last
slide,
which
is
what
do
we
do
with
this
information
when
I
retired
two
years
ago,
I
went
to
the
ITF
in
Berlin
two
years
ago
and
figured
I
was
gonna
retire
two
weeks
later
and
did
retire
two
weeks
later
and
thought
it
would
be
great
fun
since
I
was
retired
and
would
have
lots
of
time
to
write
it
all
up,
but
I've
gotten
absolutely
nothing
done
whatsoever
in
two
years.
M
Really,
thanks
for
writing
this
up,
and
so,
when
I
discovered
that
you
guys
were
going
to
meet
in
pretty
close
to
my
neck
of
the
woods,
I
figured
I'd
show
up
and
at
least
get
this
talk,
which
would
at
least
force
me
to
put
these
slides
together,
and
you
know
and
bug
John
to
do
the
BGP,
slides
and
at
least
I
got
that
much
done
I've.
You
know,
there's
a
soul
saying
that
those
who
cannot
remember
the
past
are
condemned
to
repeat
it.
M
The
internet
claims
that
that's
caused
by
George
Santayana,
whoever
that
was
I've,
no
idea,
if
that's
true
or
not,
but
obviously
you
can
always
trust
everything
you
see
on
the
internet,
so
it
must
be
true
back
in
the
70s
and
80s
where
some
of
these
disasters
occurred.
It
was
sort
of
okay
to
take
down
an
entire
major
service
provider.
M
Some
of
these
failures
occurred
in
places
that
were
a
little
bit
embarrassing.
Even
back,
then,
if
we
were
to
take
out
a
large
chunk
of
the
Internet
today,
it
would
be
very
bad
and
it
would
get
the
lead
names
on
all
of
the
news
media
if
you
could
even
get
the
copy
of
the
news
media
and
they
and
if
those
weren't
down
to
so
we
do
not
want
to
do
this
again.
M
I
So,
thank
you,
I
think
we
probably
all,
but
you
know,
were
stories
that
you
can
can
do
I,
don't
think
we
have
time
for
them,
but
seeing
as
I've
got
the
mic,
I'll
do
my
run
so
back
in
2002
issue,
so
I
was
working
it
over
and
for
various
stupid
reasons.
We
have
one
OSPF
era
with
a
couple
of
hundred,
rather
for
it
seemed
like
a
reasonable
idea
at
the
time.
I
guess
anyway.
I
These
were
all
by
one
member
reasons:
an
implementation
bug
words
every
now,
and
then
they
would
have
point
arithmetic
errors
and
the
pointer
to
the
OSB
of
edibles
will
be
offset
by
ramp
and
suddenly
you
would
end
up
with
link
state
IDs
of
255
mm
mm
flora
and
a
mass
for
191
six,
eight
zero,
zero,
at
which
time
this
looks
new
and
it
decides
to
flood
this
entire
new,
more
firm
earth-death
database
to
everyone
else
who
gets
it
distributes.
It
and
company
falls
over
because
they
don't
know
a
bit
of
the
old
Marinaro
wrath
vo.
I
K
J
J
M
With
some
of
these
examples,
of
course,
I
could
have
done
you
know,
I
could
have
talked
twice
as
long,
but
also
some
of
these
examples
there's
other
people,
many
of
whom
also
have
old,
great
beards
or
at
least
gray
hair.
That
would
have
more
detailed
knowledge
of
I
I.
Think
the
most
of
the
people
who
would
be
aware
of
these
examples
are
either
active
in
the
routing
area
or
they're
active
in
the
ops
and
management,
which
is
why
I
thought
these
were
the
right
two
places
to
get
the
talk.
M
But,
of
course,
there's
also
some
people
who
are
familiar
with
some
of
the
instrument
retired
and
in
some
cases,
I
know
how
to
find
them.
In
some
cases,
maybe
I
don't
know
if
John
knows
how
to
find
you,
a
cop
or
not
yakov
seems
I
did
actually
succeed
in
calling
him
at
home
a
couple
years
ago,
because
I
had
a
reason,
but
it's
you
know,
there's
some
people
that
are
retired
but
can
still
be
found,
and
so
yeah
I
do
think.
It'd
be
interesting
for
somebody
to
make.
K
H
Hi
Jeff
any
motor,
no
I'm
leaving
as
spring
well
I'm,
leaving
aside
the
N
lamps
and
drop
the
diversity
of
Technology,
and
thanks
for
your
presentation
for
summarizing
such
a
later
period
of
time
in
a
search,
concise
and
yet
comprehensive
light.
So
I
think
it
was
very
interesting.
A
bunch
of
stuff,
like
you
talked
about
that
I
only
see
you
saw
when
it
was
caught
up.
So
that's
very
interesting
thanks
a
lot
for
that
and
I
just
wanted
to
say.
H
D
D
We
don't
really
limit
watching
them,
I'm
interested
in
how
we
extract
the
lessons
form
of
the
stories,
because
it
seems
to
me
that
the
people
who
committed
the
sin-
that's
the
people
who
designed
the
protocols,
did
not
actually
intend
to
create
protocols
and
situations
when
networks
crashed,
and
so
then
the
next
generation
of
protocol
designer
also
does
not
intend
to
do
that
and
they
look
at
all
the
stories
in
the
history
and
they
say
well
I'm
not
doing
that.
But
what
they're
missing
is
is
how
to
get
there.
D
B
It
rocky
were
were
worship
we
protect
against
things
and
voila
key.
Just
knowing
that
design
decisions
does
not
actually
help
exactly
tell
what
you
should
be
doing
against
them.
As
my
area
of
work
is
has
been
for
a
couple
of
years,
essentially
bgp.
I
am
essentially
talking
about
stuff
that
John
had
and
voila
key.
First
I
have
the
observation
that
some
of
the
problems
reported
actually
well.
Okay,
actually
were.
B
B
Whether
it
is
completely
unexpected
that
the
protocol
designers
don't
use
those
tools
seems
to
be
a
little
bit
more
interesting
now.
The
veggie
stuff
is
very,
very,
very
kind
of
easily
done
in
the
algebraic
domain
figuring
out
in
the
algebraic
domain,
how
to
control
and
easy
stuff,
and
something
like
that
is
feasible,
and
someone
done
with
eh
gear
on
that
and
kind
of
that
PhD
work,
kind
of
done
as
an
exploration
when
the
reflector
stuff
was
put
in
sweet,
actually
done
that.
B
L
L
B
Thank
You
Ross.
Definitely
thanks
a
lot.
This
is
this
is
valuable
and
valuable
and
having
a
long,
historical
value,
information
and
discussion.
Just
one
comment:
Adrienne
I
wanted
to
respond
to
that
and
I'm
able
to
respond
a
little
bit
indirectly.
So
there
is
already
an
internet
and
it's
protocols.
Maybe
that
could
be
a
sequel
to
that.
The
history
of
the
internet
and
it's
protocol.
I
B
Quick
overview
of
the
state
of
the
Younger
in
the
industry,
that
kind
of
a
funny
title
for
this
is
how
is
young
doing,
and
it
appears
that
young
could
do
a
little
bit
better.
The
reason
for
this
discussion
we
as
an
idea
for
spent
over
a
decade
working
on
new
ways
of
manageability,
especially
the
model
based
lots
of
effort
spent
on
model
development,
and
if
we
look
really
realistic
looking
to
the
industry
and
do
a
check
of
whether
that
is
being
used
deployed,
it
is
actually
not
that
much
accepted
and
that's
definite.
B
B
However,
the
reality
is,
it
will
be
different.
It
is
not
getting
deployed
that
much
one
of
the
reasons
for
that
is
education.
This
is
a
rather
different
paradigm
shift
to
what
the
operations
in
the
field
operations
I
used
to
be
doing.
For
quite
a
long,
and
even
here
they
able
to
talk
about
models
and
the
young
and
other
things.
B
L
B
This
is
this
is
an
education
and
information
discrimination
question,
so
it's
not
enough
to
develop
a
model
that
also
needs
to
be
some
way
of
explaining
why
we
think
that
we
do
things
this
way,
the
right
way
or,
on
the
other
hand,
ITF
needs
to
model
developers,
need
to
understand
how
those
things
are
in
fact
used
and
what
needs
to
be
modeled
in
that
this
is.
This
is
a
saying
that
I
sometimes
use
of
a
2080.
B
D
B
At
working
at
fragments,
different
working
groups
work
at
fragments,
which
often
don't
even
interact,
one
of
each
other
and
the
manageability
deliverables
from
itea.
Yes,
there
are
different
young
models.
Do
those
models
combine
into
the
usable
here?
Do
those
models
end
up
in
being
something
like
a
system
which
can
be
taken
and
used?
B
It's
an
open
question
and
not
necessary.
If
we
look
at
alternative
paradigms
of
modeling,
there
is
perceived
the
conflict.
What
is
the
disagreement
between
the
IETF
modeling
way
and
open
config
open
model,
employee,
the
fundamental
difference
and
why
one
seems
to
be
getting
traction
while
another
isn't
is
that
it
works
on
a
system?
This
is
something
that
doesn't
have
or
may
be
very
beautiful
architecture,
as
idea
of
model
start
with,
you
doesn't
have
very
over
over
covering
overarching
coverage,
as
ITF
models
try
to
do
to
come
up
with
everything.
B
That
is
something
which
covers
the
majority
of
the
practical
we
needed
tasks
and
actually
can
be
used
practically
whether
that
is
an
ideal
solution,
hard
to
say,
maybe
not
on
another
hand.
It's
absolutely
not
evident
that
that
nice
architecture,
a
nice
overarching
architecture
coming
from
IETF
side,
is
also
no
any
riddle.
B
One
of
the
sources
of
this
seems
to
be
the
lack
of
communication
in
both
ways,
trying
to
understand
what
the
problem
is
and
trying
to
understand
how
the
things
are
being
used.
Instead,
we
quite
often
we
end
up
in
a
situation
where
the
vendor
community
is
telling
to
the
operator
community
how
they
should
run
things,
and
that
is
not
necessary.
The
right
approach
settle
the
vendors,
have
expertise
on
how
their
platforms
work,
but
the
platform
is
just
a
component.
It's
not
a
deciding
factor.
B
What
is
important
is
how
that
platform
integrates
into
the
end-to-end
solution
and
how
that
engine
solution
is
managed
as
a
solution
as
an
entity
and
not
as
a
bunch
of
separate
network
elements.
There
is
also
need
for
communication
in
the
other
direction.
The
field
is
an
Operations
communities.
They
are
not
aware
of
what
IETF
is
doing
and
why
they.
B
L
B
Was
a
question,
or
so
with
this:
it's
an
experiment
to
try
to
do
something
like
a
communication
channel
in
the
form
of
experimental
working
group
or
some
other
group
which
tries
to
work
on
on
developing
the
guiding
documents,
not
RFC's,
but
temporary,
guiding
documents
on
how
the
protocol
and
component
working
groups
needs
to
be
working.
What
are
the
priorities?
What
are
the
important
things,
and
the
most
important
part
is
how
this
should
be
matching
together.
B
It's
Europe
jumping
to
the
microphone
excellent,
this
time
for
discussion,
but
the
reason
for
doing
that
a
young
young
routing
design
team
seemed
to
have
resulted
in
good
outcome,
but
rounding
is
not
enough.
It's
just
a
component.
So
if
I
want
to
use
a
practical
system
is
much
more
than
just
routing
and
on
another
hand,
yes,
the
way
the
way
workshops
being
done
quite
a
while
to
check
what
is
the
state?
What
is
needed,
maybe
maybe
that
needs
to
be
a
rerun,
as
things
simply
have
changed
over
the
last
15
years.
B
Questions
please
and
also
much
a
question,
but
a
series
of
comments
on
gotcha
Karen
things
at
Google.
I
am
one
of
the
criminals
behind
open
company.
What
I
would
say:
I
stood
up
a
few
ITF
segoe
I
can't
remember
which
one
because
there's
beer
in
this
weekend.
Oh
that's
my
memory,
the
ender
said
nobody
cares
that
you
using
you
and
that's
like
the
exact
thing.
B
The
philosophy
we're
going
with
in
this
in
this
area
is
that
open
source
as
much
of
the
work
we're
doing
is
possible,
which
is
to
get
to
the
stage
where
somebody
can
log
on
to
gear
after
they've
read
how
to
get
flown
something
because
so
they
log
on
to
github,
and
they
can
pull
that
they
can
pull
this
down
documents
they
explain
in
like
oh,
you
might
implement
it
like
this
I.
Don't
think
they're
sufficient
in
this
world
I
think
that
we
have
to
get
to
the
stage
where
we
have
running
code.
B
That
folks
can
play
with
and
that
they
can
start
to
address
some
of
their
problems
with,
and
we
have
to
think
about
transition
mechanisms
so
in
in
the
work
that
we've
been
doing
on
the
interfaces
to
the
device.
In
my
one
of
the
key
things
that
we
did
over
the
last
year,
or
so
was
this
mix
schemer
implementation?
So
how
do
I
move
partial
part
of
my
config
to
levels?
How
do
I
like
address
the
pain
frames,
so
I
can
still
pull
in
all
these
static
conflicts
that
are
the
boilerplate.
B
B
I
think
are
you
know,
we've
spoken
and
a
lot
about
the
weather,
whether
it's
a
working
group
or
not,
but
I,
think
so,
focusing
that
whatever
that
ends
up
being
on
things
that
folks
can
actually
use
and
solve
practical
problems
and
have
hope
that
people
can
pull
that's
where
we
should
be
looking
dictum
progress,
this
area,
so
just
to
be
clear
yang,
is
not
the
goal.
Youngest
pool
is
just
a
component.
B
B
Maybe
started
years
ago
and
look
at
the
models
that
come
out,
you
know
bender
being
the
auto
generated
from
vendor
config
databases.
It
is
impossible
to
use
these
things,
I
think
there's,
there's
huge
amounts
of
duplication
is
very
unclear
as
to
how
to
actually
consume
it.
So
we
have,
as
an
industry,
focused
on
owner
the
thing
that
we
should
have
a
few
demos
and
we've
gone
and
found
shortcuts
to
ticker
an
RFP
box.
B
That's
actually
moved
us
backwards
because
folks
go
and
look
at
it
and
then
they
have
no
idea
how
to
consume
it
and
I
say
this
just
as
background
as
so
many
that's
now
written
to
complete
cogeneration,
two
shades
for
yang
and
reference
implementation
for
both
the
comp
against
state
side
of
climate
orient
and
configuration
so
I.
Think
I.
Don't
think
that
this
message
is
clear
to
people
that
yang
models,
Antonov
an-2
mastered
all
the
way,
they're,
not
something.
That's
usable
and
useful.
B
B
This
is
not
the
regular
working
group
testing.
This
is
an
experiment
and
that's
still
a
question
and
that
will
be
then
joined
with
other
organizations,
in
particular
I
panic
and
that's
just
an
experimentation,
so
something
more
tangible
probably
would
happen
by
the
103
timeframe.
Now
this
is
an
early
social
socialization
of
the
ideas,
so
any
any
other
comments
definitely
welcome.
B
D
B
B
That
I
can
like
take
this
and
get
some
code
to
work.
We
just
not
indeed,
for
instance,
so
I
can
look
if
I
can
send
it
to
a
device
owners
later
five
years
later,
I'm
still
working
on
the
I'm
still
maintaining
a
tool
chain
to
do
that,
because
there
were
very
few
open
source
options,
so
the
the
ease
of
consuming
this
is
significantly
simpler,
because
you're,
really
just
using
a
bunch
of
temporal,
do
stuff
that,
since
you
were
designed
for
web
development
and
young
doesn't
have
the
ecosystem
around.
B
Do
you
end
up
replicating
is
massive,
so
I
think
I
significantly
underestimated
how
much
it
was
so.
The
chef
and
an
small
thing
is
much
easier
because
of
the
fact
that
this
code,
that
you
can
run
and
just
go
and
do
it
as
a
standalone
java
in
even
commercial
solutions
and
try
and
find
somebody
that
will
sell
you,
something
that
is
complete
generation
involving
you
modules
that
doesn't
also
sell
you,
professional
services.
