►
From YouTube: IETF102-DOTS-20180719-1550
Description
DOTS meeting session at IETF102
2018/07/19 1550
https://datatracker.ietf.org/meeting/102/proceedings/
A
All
right,
good
afternoon,
good
afternoon,
everyone
we're
gonna,
get
started,
I
hope,
you're
here
for
dots.
You
may
want
to
step
out
just
for
last-minute
get
your
coffee
or
your
cookie.
We
have
somewhat
full
agenda
to
talk
through
some
things.
My
name
is
roaming
to
Nadeau
and
you
know
Frank
shall,
but
he
is
now
up
on
the
stage
here
with
us,
as
as
a
co-chair.
Tobias
will
be
stepping
down
after
this
meeting,
so
we're
thrilled
to
have
Franklin
on
the
team
here
pushing
our
working
group
through
some
progress.
A
It's
late
in
the
week
will
you've
seen
this
note.
Well,
it
references
a
number
of
policies
related
to
code
of
conduct,
copyright,
patents
and
privacy
policy.
Like
things.
If
you
do
have
any
questions,
please
don't
hesitate
to
ask
from
one
group
chair
or
the
a
did:
administrative
Lea
we
have
the
blue
sheets
getting
passed
around
cristinaw
Co
is
going
to
be
our
jabber
jabber
scribe
and
taking
notes
is
Jessica
and
Daniel.
Thank
you
so
much
for
doing
that.
For
us.
A
The
agenda
we
have
here
for
you
today
is
slightly
tuned
from
what
what
was
sent
on
the
mailing
list.
We
we
had
some
late-breaking
ads
to
talk
about
implementation
experience
and
then
some
commentary
about
some
possible
mods
to
the
signal.
Channel
we're
gonna
have
both
in-person
and
remote
participants,
which
has
historically
worked
really
well
for
us.
So
before
we
get
into
some
of
the
details,
we
have
a
lot
of
documents
and
different
different
kind
of
status,
and
we've
been
talking
about
what
next
steps
were.
A
Frank
and
I
wanted
to
summarize
that
for
the
working
group
and
have
a
conversation
about
whether
this
seems
right
and
whether
or
whether
this
is
the
next,
the
best
way
to
proceed
so
we've
gone
through
a
working
group
last
call
and
closed
issues
related
to
the
requirements
document,
and
at
this
point
we
have
a
Shepherd
write-up
prepared
and
we're
going
to
be
advancing.
That
document.
Thank
you,
Frank
for
for
doing
kind
of
that
write-up.
A
Then,
as
we
talked
about
use
case
signal
and
data
channel,
we
have
time
for
each
one
of
those
drafts
on
the
on
the
agenda,
but
to
kind
of
lay
it
out.
We
think
from
the
chairs
perspective
from
at
least
early
conversations
with
the
editor
team
that
the
use
case
is
almost
ready
to
for
its
Shepherd
kind
of
write
up.
It's
going
to
likely
take
one
more
version
to
process
last
call,
then,
with
the
signal
draft,
it's
been
many
months
of
processing
feedback,
there's
still
a
little
bit
more
on
the
mailing
list.
We
feel
that's
gonna.
A
B
C
A
You
prefer
to
have
that
as
the
basis
of
the
working
group.
Last
call.
Yes,
okay,
we
can
wait
again
that
actually
works
for
a
benefit.
There's
a
lot
of
documents
and
I.
Don't
think
we
have
the
bandwidth
to
to
go
through
last
call,
so
we
can
talk
as
we
as
we
cover
the
use
case,
the
signal
draft
and
the
data
channel
we
can
cover.
You
know
we
can
cover
the
specifics
of
what
makes
most
sense.
We
didn't
have
an
explicit
slot
for
requirements
and
architecture.
So
thank
you
for
bringing
that
up
to
date.
A
A
Okay,
I'm,
taking
that,
as
you
know,
okay,
so
we'll
proceed
so
first
up,
as
is
our
tradition.
Let's
talk
about
the
running
code.
We
have
for
all
the
drafts
we're
going
to
be
talking
about
so
first
stuff.
We're
gonna
be
talking
about
our
hackathons,
so
Konami
thanks
so
much
turning
you
over
to
you
can
I
give
you
the
quicker
please.
D
D
So
the
first
hackathon
we
did
only
the
implementation
of
implementation,
implementation
of
an
oasis
which
is
fraud
entity
then,
are
eating
100.
We
did
first
interoperability
testing
with
IDT
and
in
which
she
group
Patrick
Farrell
far
away,
but
it
is
only
limited
to
this.
You
know
each
other
about
this
time
in
ie8
mano
to
hackathon.
We
did
the
first
data
channel
intro,
so
I
can
take
both
signal
channel
today.
D
Then,
on
the
other
end,
in
the
sushi
group's
implementation,
which
is
in
London
running
on
proprietary
production
mitigation
box,
then
we
communicated
each
other,
both
signal
channel
on
the
data
channel,
then
I'll
start
cryin,
Godspeed
education,
request
and
sister
configuration
of
a
Sunnah
channel
and
also
used
data
each
other
for
the
registration
of
client
areas
is
issues
and
also
data
capability,
discovering
then
those
mushishi
groups,
implementation
work
as
the
thought
solder
them
eat,
eat,
toady,
dose
mitigation
actions.
Also,
vice
versa.
We
did
tests
within
she.
D
So
hey
the
summary
of
the
internal
testing,
then
ok
I
will
dig
into
the
details
in
the
latest
life,
but
you
may
see
that
the
green
cells
represent
tested
elements
in
the
eye.
Thick
bundle
and
blue
cells
represent
tested
element
in
this
ETA
102.
So
you
may
see
that
the
test
coverage
was
enhanced
significantly,
so
first
I'll
move
on
to
the
data
channel
result
so
on
the
data
channel
here
the
evaluated
features
so
for
the
iteration
of
triads
ideas
and
filtering
rules.
D
We
need
a
test
of
these
missiles
like
our
post
to
get
theories
of
these
elements
and
also
we
did
victories
of
the
capabilities.
We'd
get
method.
Then
here
the
result,
then
all
of
the
test
is
checked
as
green.
So
I
checked
with
this
check
mat.
So
actually
our
the
result
was
good.
Then
several
issues
found
so
those
are
already
reported
to
the
body
group.
D
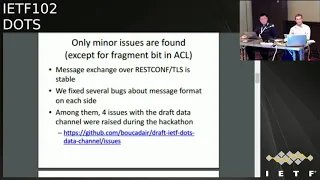
So
with
the
summary.
So
actually,
our
message
exchange
over
risk
of
over
TLS
is
very
stable,
so
I
can
say
that
there
are
no
problem
with
such
transport,
but
we
fixed
several
thoughts
about
message:
format
itself
on
each
side,
so
among
them
for
issues
with
the
data
draft
child.
A
data
channel
draft
were
a
race
to
the
party
group
during
the
hackathon
and
all
of
issues
on
the
repository
of
get
heart
of
met.
Dana,
okay,
I
was
also
occupied
and
only
minor
issues
are
found,
except
for
fragment
bits
in
Asia.
D
Okay,
family,
a
very
tiny
issue,
just
a
clarification
of
ambiguity
about
a
text
in
the
6.1
create
aliases.
So
in
that
take
is
the
ban
of
these
attributes
like
target
prefix
target
fqdn
I'll
get
you
a
light,
must
be
present,
input
request,
but
it
post
progressed,
but
it
must
be
exist,
existing
in
post
and
also
put
so
just
updated,
Atticus
and
second
one.
Second
one
is
about
painting
lifetime
in
the
response.
If
you
are
credit,
you
are,
a
query,
is
aliases
content
config,
so
pending
lifetime
is
defined
as
a
config
false.
D
E
D
Okay,
then,
the
issue
number
two
fragment
bits
representation.
He
the
most
important
one
then
for
ipv4
fragmentation,
the
current
roster.
It
should
be
represented
as
a
beach
type.
So
it
includes
the
name
of
Pete
like
a
la
morra,
in
the
flux
leaf,
then
a
pizza
names
should
be
in
the
one
string
with
space
superlative
form
1040
v6.
The
type
is
a
peaceful,
it's
2d
representation
of
this,
but
this
is
not
active
if
six
case
is
not
difficult,
but
for
ipv4.
There
is
a
problem
like
this,
so
the
current
draw
stage
of
K.
E
D
If
there
is
a
defined
beat,
it
should
be
repeated
as
zero
if
in
our
C,
seven
nine
seven
nine
five
round,
so
that
is
difficult
to
represent
the
fragment
in
this
form.
So
question
is
how
best
to
represent
irrelevant
futile
rules
with
net
misako
or
each
enhancement,
so
for
me,
bgp
prospect,
like
representation
for
her
fragment,
fit
for
my
feelings,
but
we
should
discuss
about
this,
but
discussion
will
be,
should
be
in
the
little
the
made
presentation
or
not
here.
D
D
So
first
you
know
each
other.
We
evaluated
these
features
so
the
category
the
category
of
features
is
myself.
So
if
you
have
some
objection
to
the
categorization,
please
let
me
know,
but
in
this
category
categorization
we
can
say
that
I
can
say
that
these
specifications
like
session
configuration
which
mission
request
code,
pink,
observe
of
mutation,
session,
config,
Akashi
update
and
the
request.
Confliction,
hungry
and
confliction.
Not
fault
is
a
constitution,
because
without
them
we
can't
do
not.
We
can
not
execute
DDoS
mitigation
of
god.
Clients
do
not
stop,
but
further.
D
These
features
like
that
month
trigger
it
wave
function
with
erection
and
happy
eyeballs.
We
can
do
the
minimum
mitigation
request
without
those
features
so
I.
They
all
say
that
those
additional
specifications
so
among
be
call
800
specifications.
We
tested
the
six
specifications
in
this
in
testing,
so
this
is
the
summary
of
the
testing
of
she
knows:
charlie
drop,
so
there
are
several
bugs.
So
several
dogs
are
found
on
both
site,
but
those
bugs
are
already
fixed
during
the
hackathon,
even
after
the
hackathon.
D
Then
the
second
one
is
about
Sri
know
each
other
four
point:
five
point:
three
configuration
freshness
and
notification,
so
I
explained
I
explained
this
shortly.
The
adult
server
needs
to
be
able
to
update
you,
know,
channel
configuration
parameters
so
to
toad
server
and
postcard
need
to
agree
on
the
funeral
channel
configuration
so
it
needs
to
be.
D
It
need
to
be
able
to
update
it
and
then
dot
triad
can
do
the
food
to
refresh
the
configuration,
so
it
overwrite
the
server's
configuration,
as
you
know,
channel
configuration
so
then
that
client
needed
to
get
to
reach
the
agreed
configuration
within
the
max
age
type,
so
dot
signal.
China
draft
did
mention
about
these
features,
so
the
trust
is
not
updated.
So
again,
this
issues
issue
is
already
fixed.
D
So
this
is
a
wrap
up
of
the
presentation.
So,
as
takeaway
I
can
say,
successful,
interrupted.
Continuing
then
Co
efficient
of
dot
is
now
major
enough,
not
only
for
our
channel
but
also
the
each
other.
Then
several
issues
are
fund
during
the
hackathon,
but
they
are
not
so
significant,
so
they've
been
sorted
out
on
the
fixed,
then
we
have
two
implementations.
One
is
OSS.
The
reports
tree
is
here
at
github
from
ninety
T
entity
named
co,
dot
and
one
proper
proprietary
from
initiative
groups
which
will
be
the
production
level.
D
A
So,
on
behalf
of
the
chairs,
we
want
to
thank
the
hackathon
team
for
for
doing
for
do
it
for
doing
everything
they
did
this
past
kind
of
weekend.
I
know,
there's
been
a
lot
of
focus
in
previous
events
on
the
signal
channel
giraffe,
we
know,
has
improved
the
quality
of
a
document.
Now
that
you,
the
fact
that
you
focused
on
the
Daito
channel,
helped
tremendously.
We
hadn't
previously
done
that
and
you've
clearly
found
issues
so
to
the
editor
team
of
the
signal
and
data
channel
document,
thanks
again
for
revving
again
in
preparation
for
this
meeting.
A
F
G
Exactly
who's
affected
to
the
latest
document
that
Konami
raised,
we
discussed
them
and
we
we
fixed
the
document.
We
update
them
so
that
there
is
no
confusion
about
the
some,
because
most
of
the
of
the
issues
are
not
that
that
majors
only
about
clarification
and-
and
some
of
them
could
be
just
to
leave
the
technologies
but
as
an
editor
I
preferred
to
to
modify
it
so
that
there
is
no
someone
else,
can
not
misinterpret
the
text
and
so
on.
G
D
G
So
yeah
I
have
only
one
confession:
question
one
question
about
the
behavior
of
the
implementation,
given
that
I
have
seen
one
question
from
Andrew
about
the
mitigation
or
loss
yeah,
so
just
to
make
sure
there
is
no
confusion
about
about
about
that,
one,
how
the
implementation
is
behaving
right
now,
when
you
activate
the
year,
you
have
the
parameter
which
is
trigger
on
loss,
which
is
enabled.
How
do
you
accept
the
mitigation
coming
from
the
DES
client
or
you
you
discard
them?
Sorry,
I.
C
C
D
A
H
Okay,
so
you
know
I
have
the
dead.
My
interpretation
was
that
the
dead
man
trigger
was
there.
If
there
was
a
loss
of
signal
heartbeats
between
the
server
and
the
client,
and
then
the
server
could
then
initiate
whatever
he
needed
to
initiate
to
start
mitigation
as
a
consequence
of
the
dead
man's
trigger.
But
following
Andrews
email
that
came
out
about
an
hour
ago,
I
realized
that
we
don't
actually
have
anything
in
place
for
what
should
happen
to
start
the
mitigation
dude
you
just
take
overall.
Does
it
have
some
predefined
kind
of
environmental
words?
H
It's
nothing
as
clear
as
to
what
actually
should
happen
when
the
dead
man's
trigger
kicks
in.
So
we're
missing
a
part
on
that,
but
certainly
it's
not
that
if
that
is
not
set
in
the
signal
channel
mitigations
are
held
until
it
is
set.
True
in
the
signal
channel,
it's
that
was
not
my
interpretation
of
the
original
text.
H
G
Because
what
we
have
done
in
this
signal
change
that
we
in
avoid
to
in
order
to
avoid
having
redundant
specification
of
what
we
do
at
authoritative
text
for
us,
is,
as
we
just
pointed
to
this
section
in
the
architecture.
So
I
don't
know.
I
didn't
read
the
latest
version
of
the
architecture
that
we
have
to
make
sure
that,
whether
to
import
all
the
text
and
put
it
on
the
signal
channel
or
to
leave
the
text
as
right
now,
so
we
can.
You
can
see
at
the
point.
A
G
Have
what
we
have
say:
we
have
the
parameter
there
and
what
we
said.
The
full
description
of
the
behavior
see
section
theta,
then
on
the
detector.
For
me,
that's
that
is
fine.
That
sounds
fine.
Sorry.
My
question
is
that
if
we
think
that
we
will
avoid
confusion,
perhaps
this
is
an
open
question.
We
just
need
to
copy
the
most
point
from
the
architecture
and
put
it
into
the
the
signal
channel.
Even
if
this
is
my
favorite,
but
it's
I
transfer
to
your
to
your
to
your
issued.
It's
after
you
to,
let
us
know
sure
yeah.
G
That's
that's
really
it
so.
For
me,
it's
okay,
the
current
the
current.
The
current
Texas
is
okay,
because
I
am
pointing
to
to
to
the
architecture,
but
if
you
think
that
this
is
not
the
way
to
where
to
go,
and
if
you
prefer
that
we
do
add
few
sentences
there
that
this
is
something
that
can
be
done.
Sorry.
G
C
The
issue
for
me
really
is
that
we
don't
have
it
defined.
What
mitigation
is
the
scope
of
the
mitigation
actually
is
on
the
dead
man's
trigger?
We
can
say
that
it
takes
place
on
loss
of
signal
in
the
architecture
graph,
but
them
there's
no
way
to
tell
the
server
currently
based
on
the
specification
in
the
signal
Channel.
What
that
scope
should
be.
A
Good
Thank,
You,
Canali,
okay,
so
next
up
we
were
gonna
transition
from
the
implementation
work
at
the
hackathon
to
other
implementation.
Work,
that's
happening
so
first
up,
youhave,
Romain
Kiki
was
gonna
talk
about
the
particular
intradomain
orchestration
use
case
with
with
go
dots.
So
you
hey
we're
pulling
up
your
sides.
A
D
Hayashi
wrong
entity.
Thank
you
for
choose
to
give
me
presentation
throat
today,
I
want
to
make
a
presentation
about
the
POC
report
of
inter-domain,
so
castration
use
case
and
I
want
to
discuss
what
those
should
be
for
a
journey
took
providers.
First
of
all,
I
will
explain
brief
summary
of
this
presentation.
Annex
please.
D
D
We
also
want
to
use
a
standardized
interface
between
the
orchestrator
and
the
security
products
in
IETF
100,
so
I
went
to
Singapore
and
investigated
a
security,
automation,
working
group
and
I
got
to
know
about
adults
working
group,
so
we
want
to
try
adults
as
a
standardized
interface
between
the
orchestrator
and
throw
cricketers
or
adidas
mutation
systems
from
next
rice.
I
want
to
explain
about
the
POC
next
piece.
This
figure
shows
a
POC
overview.
Our
left
one
is
our
pockets
case
and
light.
One
is
adidas.
Orchestration
use-case
are
written
in
the
draft.
D
D
This
figure
issues
our
environment
at
the
Polk
inter-domain
network
consists
of
two
types
of
networks.
A
core
network
on
scrubbing
center
core
network
consists
of
two
peer
artists.
The
scrubbing
center
consists
overflow,
corrector
Orchestrator,
a
DDoS
mitigation
system
on
GRE
and
point
water.
In
this
environment
we
assumed
that
the
flow
corrector
and
the
DDoS
mitigation
systems
was
a
dots
client
about
dot
server.
A
we
deployed
to
the
Saba
VM
with
goats
Abba
on
the
orchestrator.
D
On
the
other
hand,
about
touch
grant,
there
were
no
commercial
products
which
implemented
to
describe
function,
so
we
deployed
dots,
grant
BM
for
the
flow
corrector
and
tedious
mutation
systems
on
the
orchestrator,
each
dose
cry
and
vm
has
some
functions.
A
friendiy
is
a
pasta.
Fiji
transforms
sister,
all
of
the
protractor
or
DDoS
musician
system
into
imp,
top
go
Dawgs
grant
controller,
the
goats,
current
controller
controls,
goats,
client
and
the
goats
crayons
st.
dot
Sigrid
suffer
from
next
rise,
a
week's
pray
about
how
it
works.
D
Next,
please,
first
of
all,
a
pirata
seems
net
flow
to
the
flock
Richter.
Next,
please,
when
the
protractor
detects,
the
polymer
dark-eyed
sends
his
dog
to
the
dog
client
vm.
Other
dogs
mitigation
request,
after
that,
in
dose
grinder
BM,
our
friend
de
extracts,
target
IP.
Others
from
the
Cicero
makes
a
JSON
file.
Are
the
input
of
the
gods
grant
control,
then
the
god
of
grant
contour
is
invoked
so
that
the
chords
gray
and
sends
the
signal
to
the
world
server.
Next,
please,
the
goddess
Sabra
invokes
a
go.
D
D
Finally,
the
goal
of
server
inbox
go
BGP
on
a
peer
outer
abroad,
attack
traffic
by
abraca
whole
routine.
That's
all
of
action,
our
POC,
a
home
next
race.
We
will
explain
our
requirement
so
far
in
our
pork
we
use
bracha
horrid
thing,
gossipy,
ruta,
fiber
I.
In
the
future,
we
want
to
use
BGP
prospect,
2
Broke
attack
traffic
@p
Lotus
more
correctly,
so
we
want
to
just
grants
to
send
attacker
information
like
top
talker
for
IDF
103,
I
I.
Think
I
want
to
write
draft
about
expansion
of
toad
signal,
a.
D
C
G
Yeah
I
think
this
is
a
valid
question.
This
is
a
question
wishes
we
received
several
times
to
add
more
information
into
the
signal
channel
and
what
we
have
decided
so
far
is
to
maintain
the
signature.
I
would
say
the
monetary
information
to
be
included
there.
So
once
the
signal
shown
is,
is
frozen
and
sent,
then
we
can
open
the
discussion
about
the
new
information
to
be
included
new
section,
but
this
will
be
really
extension
that
optional
to
have
and
not
as
what
we
have
in
in
the
current
signal
channel.
I
Imma
take
know,
the
use
case
is
interesting
and
this
alludes
to
what
I
was
kind
of
like
thinking
earlier
when
I
was
reading
through
the
signal
channel
in
the
fact
that
we
kind
of
mentioned
vendor
extensions
twice,
and
then
we
just
gloss
over
where
we
see
anything
else
so
I
think
from
rather
than
how
it
is
vendor
extensions.
We
might
want
to
change
it
to
extensions
of
some
description
or
optional
extensions
or
non.
F
Frank's,
how
I
sense
that
you're
here
you
bring
this
your
your
poke
and
the
yard
comment
here.
Yes,
I
think,
that's
real
that
this
you
come
and
make
sense,
and
maybe
in
future
we
can
do
some
extension
to
counter
protocol
to
so
it
so
my
individual,
and
yet
from
my
my
individual
comments-
is
that
if
you
want
to
bring
this
new
work
to
this
working
group,
please
write
a
draft
to
describe
your
use
case
and
the
requirements
so
that
we
can
check.
We
can
have
more
discussion
more.
F
I
Nick
Teague
again
now
I
just
wanted
to
say
that
I,
don't
think
you
should
it's
there's
nothing,
stopping
you
from
putting
this
into
a
draft.
Now,
though,
as
far
as
everything
goes,
if
you
want
to
do
it,
it's
it,
we
might
consider
it
to
be
the
next
consideration
or
something,
but
while
we're
getting
everything
else
sorted
out,
but
at
the
same
time
would
be
nice
to
have
stuff
sitting
there
waiting
to
work
on.
A
So
I
wanted
to
hold
a
working
group
on
this
thread,
as
Frank
could
of
alluded
to.
This
conversation
has
come
up
before
about
wanting
to
do
extensions,
and
you
know
at
the
my
god,
I
heard
something
that
I
guess
is
a
little
too
vague
for
me.
You
know,
we've
talked
about,
let's
get
the
core
thing
done
and
then
we
can
kind
of
have
extensions,
but
what
does
that
practically
mean
to
folks
to
folks
kind
of
here
in
the
room
I
mean?
Is
there
are
we
talking
about?
A
I
Hey
Nick,
Teague,
well,
I
think
when
we,
when
we
first
started
this
we
always
kind
of
had
extensibility
is
part
of
the
one
of
the
reasons
we
were
doing
it
or
one
of
the
one
I'm
sorry,
one
of
the
attributes
and
I
think
from
every
kind
of
like
very
variation
that
we've
put
together
of
protocol
standard.
You
know
critical
candidates
always
had
some
kind
of
extensibility
in
there
now.
The
one
with
you
have
has
a
bunch
of
stuff
already
there
we're
just
hand
waving
over
it
as
being
there,
but
we've
made
room
for
it.
I
J
I
said
danyoung
me,
Gary,
Erickson,
so
I
think
we
well.
The
protocol
needs
to
have
some
extensions,
but
we
should
really
think
about
which
extension
we're
going
to
go
through.
You
can,
if
you
see
what
makes
a
product
all
successful,
is
that
it's
been
extendable,
but
when
you
see
why
a
protocol
is
dying,
is
that
when
you
have
a
bunch
of
uncontrolled
extensions,
so
I
think
that's
where
the
discussion
has
to
take
place,
which
extension
where
you're
going
through
and
find
the
right
one
that
is
hitting
all
the
use
cases
we
want
to
address.
A
D
A
Okay,
we'll
close
the
the
conversation
here,
but
I
mean
we
are
having
a
recurring
conversation
about
extensions
and
I'll,
put
something
again
on
the
mailings
to
discuss,
but
I
think
you've
us
to
have
some
text
somewhere
or
some
guidance
that
we
can
point
you
that
would
govern
how
we
want
to
handle
this
in
the
future,
but
I
think
we
need
to
flush
this
out
a
little
more.
So
what
we'll
take
it
to
to
the
male
voice?
Okay,
yoohoo.
Thank
you
for
your
presentation.
A
We
have
a
little
bit
of
time
left
just
for
open
mic
if
folks,
with
implementations
that
already
exist
want
to
talk
about
progress,
they've
made
or
if
someone
here
in
the
room
or
in
media
Co,
would
like
to
surface
the
existence
of
another
implementation
that
we
haven't
previously
learned
about.
So
hoping
my
time.
If
you
want
to
talk
about
running
code,
you
have.
C
Hi
we've
made
some
progress
internally
with
the
coop
based
version,
and
we're
also
now
experimenting
with
additional
languages,
with
the
intention
of
bringing
some
a
variety
to
the
foundations
and
frameworks
that
are
being
used
currently
I
believe
it's
all
the
coop
based
yes,
Kaname
is
nodding,
so
we
we're
hoping
to
at
least
bring
some
of
that
forward
as
open
source
and
are
also
potentially
looking
for
some
Interop
opportunities
in
other
venues
in
the
future.
So
I
would
be
eager
to
hear
of
additional
implementers
aside
from
John.
A
A
G
Okay,
so
this
would
be
a
quick
update
of
the
signal
specification,
so,
as
you
know
last
so
it
was
in
and
of
naturalism
I
woke
you
up
last
fall.
That
was
issues
for
this,
for
is
the
document
yeah.
It
was
very
happy
for
about
the
outcome
that
that's
working
on
glass
Scott
was.
This
only
shown
that
we
have
only
manner
memory
issues
and
all
the
qualifications
to
be
to
be
added
to
a
document
this
so
I.
G
This
is
a
signal
for
us
that
that
we
are
close
to
to
travel
version
of
the
of
the
document,
so
this
is
only
the
listen
there,
the
some
of
the
main
point
at
Brazil
at
that
time,
so
it
is
only
clarifications
there
to
about
the
do
arise
to
to
be
used.
This
is
something
which
is,
and
we
had
explicit
sentences
to
document
to
make
it
sure
that
people
we
understand
that
we
are
using
this
your
items
because
we
are
just
in
the
beginning.
We
are
just
pointing
to
the
RFC's
in
which
is
defined.
G
We
enhance
the
develop
behavior
in
the
document
so
again
when
there
is
a
loop
which
has
it
taken
somewhere
by
the
Gateway.
What
now
the
behavior
is
that
we
are
asking
each
gateway
to
insert
its
own
information
and
then
it
will
prepend
it
to
add
weather
gateway,
so
that
this
will
simplify
and
is
a
diagnostic
if
there
is
any
any
troubleshooting
to
to
to
be
done.
G
Another
modification
was
about
the
direct
signal
in
there,
so
we
the
beginning.
We
assume
that
the
the
server
is
know
that
what
it
is
it
is
doing.
That
means
that
if
there
is
an
a
request
to
a
client
or
direct
to
another
server,
we
are
assuming
that
there
is
an
some
configurations
which
is
done
at
the
server,
but
we
figured
out
that
in
case
there
are
some
misconfigure
there.
We
introduce
this
a
guard
in
order
to
avoid
us
relation
between
multiple
servers.
G
For
instance,
if
you
ever
see
a
signal
from
a
given
server
to
you
that
you
have
to
go
direct
to
another
server
and
then
right
after
you
receive
another
signal
for
that
server
as
you
go
back
to
the
other
one.
So
this
will
be
something
which
is
bubi.
So
that's
why
we
we
introduced
this
guard
about
the
five
minutes
that
we
forbid,
that
you
can
go
back
to
to
the
previous
server.
Unless
this
lifetimes
expired.
G
We
also
clarify
the
way
we
are
using
detail
there.
We
have
four
direction
so
where
direction
can
be,
can
can
last
forever
or
can
be
limited
in
time.
So
this
is
something
that
we
are
conveniently
parameter
and
also
we
have
introduced
that
there
are
some
sentences
to
say
yeah.
We
are
dis
recommending
against
returning
short
TTL
for
our
direction,
because
it
will
impact
the
stability
of
the
service.
G
This
is
happening.
The
outcome
for
discussion
we
had
with
about
the
phone
that
economists
about
the
D
behavior
when
there's
a
conflict
before
in
the
in
the
previous
version
that
we
only
returned
a
conflict
there,
but
the
Konami
R
is
a
valid
point
is
that
you
cannot
send
back
an
update
of
this
situation
if
you
don't
create
the
resource.
So
that's
why
we
we
updated
the
behavior
again,
it
is
stable
policy
based,
but
it's
up
to
the
server
to
decide
whether
it
has
to
return
the
decrypted
code
or
the
deconflict
code.
G
A
G
It's
fine
they're
too
closely,
actually
to
make
sure
that
we
make
some
progress
on
that
one.
So
what
next?
So
this
slice
when
I
prepare
the
slides?
This
is
before
Andrew
raise
the
point
about
the
mitigation
or
loss
so
yeah.
So
it's
on
draw
it
sucks,
you
yeah
really!
So
that's
whether
we
yeah
we
proceed
with
with
the
plan
that
we
we
agree
so
together.
That
means
that
next
week
there
will
be
another
last
fall
of
the
of
the
document.
It
will
one.
A
Week,
we're
gonna
do
cachi
weeks,
one
of
the
things
that
the
core
working
group
has
asked
is
hey
you're
using
coop.
That's
that's
great.
Actually,
after
this
meeting,
I'm
gonna
go
remind
everyone
and
I'm
gonna
make
the
work
route
in
a
state.
You
know
put
eyes
on
it
and
I'm
hopeful
that
I'm
not
necessarily
expecting
to
find
anything,
but
if
nothing
else,
I'm
hoping
this
will
grease
the
grease
the
process
through
through
iesg,
given
that
we've
had
more
eyes
to
look
on
it.
So
my
hope,
if
that's
okay
setting
the
date,
we
could
start
the.
A
We
can
start.
The
working
group
last
call
starting
on
Monday
and
kind
of
run
into
kind
of
a
customary
to
get
or
two
weeks,
and
that
way
we
can,
you
know,
start
from.
We
think
we
fixed
absolutely
everything.
We
have
a
clean
document.
Does
anyone
have
any
comment
last
kind
of
comments
on
this,
and
then
we
can
move
forward.
A
G
Don't
know
if
you,
you
have
a
discussion
with
the
core
cheers:
yeah,
okay,
so
yeah,
because
we
have
you
have
written
and
in
errata
because
we
contacted
them
multiple
times
the
authors
or
the
the
the
coop
RFC
and
also
for
the
civil.
We
clarify
some
of
the
point
with
the
Carson,
but
there's
one
a
errata
which
we
opened
there
and
they
didn't
heard
any
feedback
from
then
it's
about
the
token
for
the
observe
case
and
so
on,
but
but
anyway,
it's
to
them
to
manage
the
errata.
G
A
Indicates
surprise
they
actually
indicated
that
they
wanted
to
help
and
they
invited
us
just
to
come
to
the
working
group
meeting
and
just
remind
everyone.
Then
there
is
a
couette
another
couette
protocol,
that's
in
another
working
group
and
offer
to
put
some
eyes
on
it.
So
what
I'm
just
gonna
do
a
little
advertising
at
the
next
session.
So
thank
you
for.
D
Okay,
one
question:
welcome
Adam:
could
you
return
the
one-page
the
fun
as
well?
You
was
a
three
I
mean
she's
got
from
NTT
communications,
so
about
a
faster
rate.
Okay,
I
know
why
these
changes
and
also
I,
know
that
was
read
discussed
about
this
issue,
but
I
just
feel
that
this
updated
text
is
not
friendly
to
the
new
readers
of
this
draft.
So
I
hear
some
of
explanation
of
the
context
which
was
disgusted
up.
Eating
with
us
should
be
included
in
why
the
food
is
replaced
with
Kate,
why
it
is.
G
In
document
we
don't
remember
where,
in
which
part
that
might
be
explain
what
we
mean
by
refresh
surfaces,
you
updates
and
something,
and
then
so
you
receive
the
configuration.
You
have
the
the
max-age
option
which
indicate
the
lifetime
for
this
configuration
and
the
you
have
to
take
contact
the
server
before
the
expiry
of
that
max
option.
To
add
to
refresh
it
refresh.
It
does
mean
that
you
are
sending
the
you
see
in
a
sign
of
life,
that's
in
it
that
you
are
there
and
you
will
receive
your
new
configuration
from
the
server.
G
G
Because,
actually
for
this,
for
this
change,
I
am
personally
fine
with
the
previous
text
that
we
have,
but
I
decided
to
change
it
because
a
for
the
implementation
I
received
from
John
that
he
has
some
confusion.
When
I
read
the
text,
I
don't
see
the
the
origin
of
the
confusion,
but
even
for
that,
with
that,
I
decided
to
modify
the
text
to
avoid
this
capital.
So
if
you
think
that
this
is
still
not
better,
if
there
are
a
room
for
enhancement,
please
feel
free
to
propose
texts
and
proposals
for
that.
D
A
L
L
L
L
Is
much
better?
Thank
you.
Okay,
okay
I
must
go
very
near
to
the
mic
in
my
my
book,
okay,
so
this
is
a
very,
very
short
discussion
about
the
intention.
Oh
oh,
this,
this
presentation
is
not
not
just
introduces
some
trouble
to
the
group,
but
because
we
know
that
we
we
are
almost
in
the
time
over
the
last
call
over
there
or
the
signal,
but
because
this
is
a
the.
L
This
is
a
requirement
from
us.
We
want
to
have
a.
We
are
going
to
have
a
Kuip
for
that
for
the
toast.
So
that
way
we
can
make
some
changes
to
that.
We
can
make
some
better
performance
to
the
meaty
mediations
over
and
there's
a
arrangement
of
the
resource.
So
this
is
a
what
what
we
intentioned
actually
can
you
please
Fred?
Can
you
please
display
the
slides.
M
A
L
For
the
background,
is
that
him
that
way
in
our
in
our
in
our
work?
We
do
find
that
if
we
have
some,
we
have
some
type
t.
Finally,
it
will
be
very
paid
her
for
you
know
for
that
for
the
resource
arrangement,
but
actually
it's
not
very
easy
to
give
them
to
a
very
worried,
because
that
there
are
many
those
types,
it's
not
very
easy
to
give
all
the
types
defined
and
now
because
we
were
how's
a
new
type
of
doubts.
Oh
oh
das,
excuse
me:
I,
do
not
have
a
slight
copy.
F
F
G
Of
the
channel,
so
the
there
will
be
a
bit
about
the
the
progress
status
and
the
dependent
issues
and
then
the
the
next
steps.
So
this
is
just
as
a
reminder
of
the
delusive
issue
that
we
have
discussed
last
time
in
London
and
also
in
the
mailing
list.
I
want
to
go
and
to
all
of
them.
So
it's
only
two
to
report
that
the
outcome
of
the
discussion
about
the
resolution
that
we
have
for
each
of
these
issues
have
been
implemented
in
the
in
the
14
version
of
the
of
the
document.
Yes,.
A
No,
no
I
was
just
gonna
jump
in
so,
if
you're
seeing
mad,
you
could
have
come
up
with
numbers
to
things.
That's
because
we
have
explicitly
asked
in
the
case
of
the
various
documents
just
to
help
us
track
all
the
issues
and
kind
of
number
them.
So
we
know
when
we
got
closure.
So
we
thank
you
very
much
for
doing
that.
G
So
then
the
where
is
the
the
versions
there?
So
the
memory
finish
need
that
in
the
in
the
diversity
that
we
in
the
discussion
I
had
with
Jeremy,
figured
out
that
in
the
Danette
mode
working
group
access
list
specification.
Do
you
have
the
some
slides
there
for
the
AP
before
I
before
hand
with
the
fragments,
but
for
ipv6?
This
is
not
something
which
is
really
really
clear.
So
we
released
with
the
a
lot
but
working
up,
and
also
the
outward
of
the
net
word
specification
to
make
sure
about
our
interpretation
of
the
order
specification.
G
So
yeah
and
the
outcome
of
that
discussion
is
that
they
don't
handle
a
physics
fragment
in
D
in
the
current
net
mode
eco
egg
model.
So
the
the
as
an
outcome
of
that
we
there
is
no
modification
that
we,
we
include
it
into
a
channel
specification,
but
we
we
added
an
example
in
an
appendix
to
show
to
the
Raiders
how
you
can
use
the
D,
our
data
channel
for
the
the
first
reign
of
the
ipv6
fragments
for
the
ipv4.
G
Also
the
de
packet
are
not
not
fragmented.
This
is
also
the
same
issue
as
you
have,
if
you
have,
for
instance,
a
packet
in
which
which
is
the
dot
fragment
is
set,
and
you
in
your
rule,
you
are
just
checking
that
the
more
bit
is
set
or
unset
the
the
packet
with
the
don't
fragment
will
go
through.
While
this
is
this,
this
is,
should
not
be
the
the
operate
behavior.
So
this
is
this
is
why
we
are
proposing
to
to
update
the
data
channel
specification.
G
Actually,
this
applies
not
only
for
the
fragment,
but
also
for
the
TCP
flags,
but
I
am
NOT
putting
it
here,
because
we
have
to
decide
whether
we
have
to
generalize
this
for
the
TCP
flags
and
also
for
the
different,
the
ipv4
flags
there
and
the
there
is
a
point
that
was
raised
to
the
widow
wish
that
we
need
to
go
back
to
the
net
mode
working
group
so
that
they
can
fix
their
module
there.
But
the
issue
is
that
the
they
are
already
sent
and
their
document
to
a
to
the
SG
and
the
discussion
I.
G
Have
we
with
manage
that
did
not
want
to
have
this
kind
of
features
in
their
module,
so
I
prefer
that
we
fix
that
in
our
document,
rather
than
just
going
back
to
them
to
have
this
dependency.
So
that's
that's
the
plan
for
the
the
proposal
for
the
fragmentation
and
if
he,
where
yeah,
we
would
like
to
hear
from
the
working
group
with.
Oh,
you
are
you
agree
with
that
or
not
so
just.
A
C
A
C
D
No
I'm
not
sure
the
team
will
accept,
but
I
like
the
representation
in
the
flow
of
HP
from
1855
extreme
high,
because
I
as
a
dot
server
I
will
convert
the
dot
message
into
the
acrostic
message.
We
know
that
to
stop
that
eatos
attack,
so
the
digital
spec
itself
has
a
representation
of
the
fragment
of
flags
with
masks,
so
maybe
about
a
hospital.
G
Okay,
so
that's
yeah,
that's
that's!
The
plan
that
we
are
proposing
for
this
graph
is
that
we
took
to
prepare
an
abyss
version
in
which
we
will
fix
this
fragmentation
and
for
the
TCP
flanks.
I,
don't
know
if
you
want
us
to
cover
it
in
the
next
version,
so
that
we
have
the
same
behavior
for
build
TCP
flags
and
also
the
IP
flags,
or
if
you
want
us
only
to
to
focus
on
the
ipv4
flags
only
because
this
will
require
two
modifications
for
TCP.
One
is
not.
G
F
F
L
Sir,
oh
you're
up,
yes,
is
killing
me
for
that,
because
I
do
not
take
my
hello.
Can
you
hear
me?
Okay,
yeah,
we
can
hear
you
now
you
were
breaking
up
there.
Okay,
excuse
me
for
that,
because
I
did
not
take
my
my
laptop
to
my
my
home,
so
I'd,
not
how
all
the
things
is.
It's
really
a
mistake
for
me.
So
so
let
me
have
a
quick
introduction
about
them
with
insulation.
Actually,
the
those
attacks
can
be
generated
in
different
ways.
Different
mechanisms.
L
L
H
So,
just
picking
up
the
TCP
flag
situation,
we
can
specify
something
like
the
sin
and
the
fin
flag
in
their
mosques
and
we
want
to
drop
that
type
of
attack.
But
again
the
issue
is
if
the
attacker
then
adds
in
any
other
bit
using
the
current
bits.
Implementation
of
memo
ACL
that
will
bypass
that
particular
ACL
and
go
on
to
the
next
ACL,
so
I
think
I
would
also
like
to
see
the
ability
to
have
the
bits
and
the
mask
capability
of
the
TCP
flags.
A
Thank
you
for
the
feedback,
okay,
so
kind
of
rolling
things
up.
Thank
you
for
for
the
briefing
and
I
kind
of
med,
we
have
a
little
bit
of
an
issue
still
to
resolve
we're
gonna
clear
that
in
18,
when
we
have
18
we're
going
to
go
order
last
call
on
this
document.
That's
the
plan.
Okay,
very
good!
Thank
you!
Okay!
So,
let's
loop
back,
though
we're
gonna
bring
your
talk
back
up
here.
A
L
L
We
things
that
those
attacks
can
be
formed
in
different
ways.
Different
mechanisms
is
required
to
use
a
different
mutation,
measured
actually
from
our
our
information.
We
we
do
have
three
types,
and
the
definition
is
that
the
network
layer
we
have
ICMP
I
for
transport
alive
with
having
TCP,
UDP
and
soul
application
like
we
have
so
many
candles.
L
L
L
L
L
L
It
aware
how
very
very
very
detailed
information
about
what
kinda
with
detect
protector
its
suffered,
and
it
helps
make
the
decision
right,
which
store
to
send
the
medications
requirement,
because
we
have
the
one
client
to
earn
store
connections
and
for
the
dots
gateway
it
will
help
to
aggregation
over
the
same
time
attacked
so
more
efficiency
communication
and
it
will
help
the
thought.
Did
we
to
have
the
information
come
to
the
native
speakers
and
help
to
analyze
this
things
and
a
photo
store.
L
It
will
help
of
two
intruders
their
medication
Santa,
although
it's
for
the
communication
between
the
dose
so
under
the
mitigator,
is
the
outer
scope.
But
actually
it
will
help
for
doing
that.
So,
with
the
toast
type
included
in
single
movie,
share
the
information
between
client
and
the
getaway
and
the
store
each
node
should
have
more
information
about
the
attacks.
The
opposite.
This
model
can
even
be
set
up
easily.
L
L
A
Okay,
so
let
me
just
while
we're
waiting
for
Roland's
conduct
come
up.
I
mean
again
to
summarize,
with
this
draft
there's
an
introduction
of
an
optional,
an
optional
field
that
does
classification
of
a
particular
das,
the
denial
service
type
and
there's
a
desire
to
drop
that
into
the
signal
draft.
Now.
O
D
Tsunami
yeah
convenient
easy
communication,
maybe
are
the
same
common
law
Alice's
but
yep,
so
how
to
keep
young
model
and
simple
mapping
latest
with
imagine.
These
are
taxis,
difficult
question
in
my
feeling
it
is
nature
to
be
included
in
the
you
know,
each
other
and
also
to
each
other.
Is
that
kind
of
get
those
types
yeah.
D
L
O
C
That
he's
correct,
but
that
is
the
the
most
standardized
version
of
the
document
that
we
that
we
have
inside
to
work
on.
So
the
other
thing
is
that
we
we
have
discussed
something
like
this
in
the
past.
One
of
the
reasons
we
didn't
do
it
if
I'm,
recalling
correctly,
is
that
the
signal
or
the
dots
client
may
not
actually
have
the
full
scope
of
the
attack.
C
It's
hard
to
trust
the
dots
client
to
actually
be
reporting
accurate
information
in
certain
cases,
certainly
even
one
of
the
attack
types
he's
got
if
there's
a
care
gem,
an
amplification,
that's
pretty
easily
represented
in
a
source
port
in
an
Akal
UDP
19.
So
there
are
other
ways
to
get
some
of
this
information
across
okay.
L
Actually,
I
just
give
both
back
about
that.
Yes,
maybe
that
client
do
not
have
the
whole
information
or
even
ADA
to
the
information
is
not
fully
trusted,
but
it,
but,
as
we
suggested
it's
a
optional
field,
it
can
be
used
as
a
reference,
at
least
the
inside
the
inside
a
wine
domain,
as
it
were
important.
C
A
Okay,
so
thank
you
for
that
I
mean
what
we're
hearing
with
the
multiple
kind
of
presentations
we
had
is
we're
gonna
have
to
figure
out
what
to
do
with
extensions
and
how
to
talk
about
them
in
parallel
to
advancing
the
signal
draft,
so
that
that's
a
marker
for
something
we
need
to
resolve
as
a
working
group.
Okay,
so
next
up
on
the
agenda
is
the
use
case,
conversation
so
Daniel.
J
Hi
everyone
so
the
use
case
so
actually
I
in
the
front
page,
there
is
15
version
15,
but
I
think
at
the
time.
I
was
writing
the
presentation
testers
while
I
was
writing
the
presentation.
Another
version
came
up,
yeah
16,
so
in
in
the
ITF
101
in
London
we
had
a
commitment
from
the
co-author
to
put
a
version.
Then
it's
gonna
be
wrecking
your
black
hole
into
a
month
and
I
think
that's
what
we
which
hit
our
goal.
So
so
that's
fine.
J
We
had
very
few
comments
from
version
12
to
the
working
of
last
hole,
but
since
the
version
of
Lascaux
that
means
started
Trey's
a
lot
of
questions,
a
lot
of
comments
and
reviews,
so
the
latest
we
had
was
version
16,
just
published
today.
I
think
we
are
really
in
this
state
where
we
are
polishing.
Two
drafts
now
so
well,
I
believe
from
version
10
to
11.
We
had
a
major
refactoring,
nothing
controversial,
we
most
of
the
tech-savvy
net,
just
for
youth
and
this
place
of
different
places.
A
So
Daniel
thank
you
for
all
the
rapid
revisions
there
we
so
Frank
and
I
need
to
kind
of
take
a
look
at
given.
Yet
many
of
these
revisions
were
made
this
week.
We
have
not
had
a
chance
to
kind
of
review
the
things.
Certainly
in
the
last
two
days,
it
looks
like
many
of
the
issues
kind
of
are
closed.
It's
likely
our
feeling
that
we
will
not
need
another
worker
blast
call.
This
is
really
a
matter
of
kind
of
closing
those
issues
and
we
believe
it
will
likely
be
ready
to
submit
for
for
shepherding.
A
J
A
A
Anyone
descending
anyone
else
have
any
other
comments
to
add
into
the
use
case
document
there's
been
robust
discussions,
yeah,
okay,
very
good,
thank
you
for
all
data
duration
and
thank
you
for
the
mailing
list
for
responding
back
with
all
of
all
of
that.
Okay,
thank
you,
Daniel,
thanks
for
preparing
that
all
right.
So
let's
do
we
have
a
little.
We
had
actually
quite
a
lot
of
time
for
open
mic.
So
if
there
are
things
folks
would
like
to
raise
by
all
means
come
come
on
up
while
we
prepare
the
wrap-up.
N
A
So
we
did
a
bunch
of
discussion
about
where
to
take
the
giraffe,
so
I
have
updated
the
the
table
so
on
requirements
we
have
the
Shepherd
right
up.
That's
going
to
be
going
to
our
ad
with
the
architecture
draft,
there's
one
more
revision
to
do
ready
about
mid-august
and
we're
gonna
start
a
working
group
last
call
than
likely
kind
of
late.
August
I
see
head
nodding
from
the
architecture
team.
So
that's
good
with
use
cases.
That
text
is
actually
incorrect.
A
The
15
is
the
last
version.
It
believes.
We
believe
that
that
covers
everything
that
needs
to
get
done.
The
chairs
are
going
to
make
sure
that
it
looks
like
everything
is
closed
and
if
it
is
we're,
gonna
go
to
kind
of
you,
the
Shepherd
review.
If
not,
we
may
force
another
Rev.
We
talked
about
the
signal
draft,
there's
going
to
be
one
more
revision
to
22
and
then
we're
gonna
go
working.
A
second
group,
a
second
working
group
last
call
or
did
I
not
write
that
down
right.
Then.
Do
we
go
work?
A
The
second
working
group
last
call
with
21.
Yes,
okay,
so
we
go
second
working
group
last
call
with
21.
Thank
you
for
that
clarification
and
then,
with
the
data
channel,
we
we
at
least
know
about
the
fragmentation
issues.
So
that's
going
to
take
a
revision
to
18
and
that's
going
to
get
us
to
working
group
last
call
in
this
September
timeframe,
and
that
is
our
whole
stack
of
documents.
A
And
then
we
noted
that
we
need
to
further
a
conversation
relative
to
kind
of
extensions
and
make
sure
it's
clearly
known
how
to
how
to
proceed
there
and
we're
gonna
take
that
to
the
mailing
list.
Okay,
so
anything
wrong
with
that
voiceover
in
terms
of
kind
of
dates.
We
have
some
time
I
see
Konami
approaching.
Please.
D
E
D
K
D
E
G
Think
that's
it's
time
that
we
think
about
the
at
the
next
estate
in
Italy
charter
to
see
that
we
we
have
something
which
is
official
in
term
of
the
the
item
of
interest,
the
working
group
we
in
the
past
we
have
presented
the
the
dots
discovery,
discussions
with
a
home
in
and
so
on.
I
would
like
that
we
revive
all
this
discussion
so
that
he
can
be
considered.
G
A
C
Hi
enter
Mortensen
yeah,
one
of
the
things
that
is
to
mention
in
the
use
cases,
but
it's
not
necessarily
been
treated
here
is,
is
the
case
where
the
I
think
could
be.
Itp
is
actually
signaling
downstream
to
the
the
enterprise
to
say,
you're
the
source
of
an
attack.
You
need
to
block
closer
to
it,
and
we
haven't
seen
any
of
that
treated.
