►
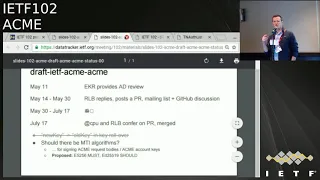
From YouTube: IETF102-ACME-20180717-1720
Description
ACME meeting session at IETF102
2018/07/17 1720
https://datatracker.ietf.org/meeting/102/proceedings/
A
A
A
The
agenda
and
the
document-
statuses
that
includes
the
main
document
CAA
and
I,
forget
what
other,
what
the
other
one
was.
The
at
the
second
dispatch
star
came
up
and
the
dispatch
dispatched
it
back
to
Acme.
So
we'll
have
a
brief
overview
of
that.
There
are
some
concerns
and
issues
about
Interop
for
the
CEA
challenge,
we'll
discuss
that
a
little
bit
and
then
there's
acne
authority
tokens
to
presentations
one
from
Chris
and
job
any
other
changes.
A
B
A
C
B
D
B
E
B
The
real
full
color
version
there,
but
today
CPU
and
I
got
together.
We
worked
through
the
the
minor
disagreements
we
had
and
got
it
merged
the
the
one
thing
that
had
any
significance
there
is
we
that
was
all
say
the
one
like
breaking
change
there
was
there
was
a
typo
where
the
key
role
of
her
object
had
new
key
is
the
inner
thing.
So
you
had
the
old
key
signing
over
the
new
key
in
the
account
URL
and
the
new
key
signing
over
the
new
key
in
the
count
URL.
B
So
you
didn't
have
the
symmetry
that
you
want
in
the
role
of
her
hand
ever
so
we
had
to
fix
that
and
change
it
back
to
the
old
key
and
the
other
thing
you
can
see
that
in
the
diff
and
the
PR
should
it
should
be
an
easy
thing
and
it
is
breaking
on
any
existing
implementations.
But
it's
an
easy
thing
to
fix.
B
A
B
B
Those
of
you
playing
along
at
home
there's
a
PR
which
I
also
sent
a
link
to
the
list
to
the
PR
there.
That
says,
basically
this,
that
a
server
of
the
new
acne
server
implementation
must
implement
yes,
2.6
and
should
implement
EDD
sa
with
82
five
five,
one,
nine,
it's
one
sentence:
it
goes
in
the
paragraph
where
we
put
constraints
on
jws
that
we
use
in
here.
B
So
it's
a
very
simple
change,
but
it
doesn't
entail
a
concrete
requirement
on
server
implementers,
so
I
think
I'm.
Okay,
with
this
CPU
is
nodding.
So
I
think
the
author
team
is
okay
with
this,
but
wanted
to
put
this
out
here
for
anyone
in
the
room
to
object.
Anyone
really
hate
those
NIST
algorithms
think
we
shouldn't
be
requiring
them
everywhere.
So
before
we
okay,
these
are
by
the
way,
also
required
signing
algorithms
for
TLS.
So
there
they're
gonna,
be
in
your
crypto
stack.
F
B
That's
always
the
risk
with
these
is
the
trade-off
is
getting
interoperability,
ensuring
those
common
algorithms
between
implementations
versus
the
risk
that
you've
got
to
go
fix
it
later
and
I.
Think
the
assumption
is
these:
algorithms
are
long
enough
lives
there.
We
expect
them
to
last
for
a
while
longer
and
so
when,
when
things
fail,
we'll
come
back
and
revise
and
and
change
out
to
the
recommended
algorithms
I.
F
F
Obviously
this
is
the
kind
of
like
health
warning
you
should
give
to
all
implementers,
don't
hard-code
this,
like.
Obviously
you
want
to
have
updatable
code
right.
That's
gonna!
Allow
you
to
put
new
things
in
later,
because
we're
gonna
need
it,
because
these
algorithms
will
go
to
hell
in
a
handbasket
at
some
point.
So.
A
Okay,
so
just
I
think:
first,
we
should
decide.
We've
gone
from
the
beginning
without
having
any
MTI
signature
stuff.
So
I
first
want
to
know
what
the
working
group
feeling
is
about
that
so
have
a
home.
Are
you
in
favor
of
MTI?
Are
you
not
you
know?
Are
you
opposed
to
having
an
ti6
signing,
or
do
you
not
have
enough
information
to
decide?
So
all
those
in
favor
of
specifying
an
MTI
signing
algorithm.
A
A
So
we'll
confirm
that
on
the
list
and
we'll
just
confirm
we'll
ask
similar
consensus
for
the
signing
algorithms
and
then
you
can
just
make
the
pull
request,
since
that
was
the
only
open
issue
in
the
last
call
in
the
ad
reviews
are
correct:
yeah.
That
was
the
only
remaining
open
issue
and
where
there
was
just
a
hub
in
favor,
yeah.
B
It's
all
set
okay,
so
I
mean
I've
got
the
four
requests
queued
up,
but
I
mean
I
would
be
tempted
to
say,
let's
just
go
ahead
and
merge
the
pull
request,
given
the
strong
agreement
in
the
room,
and
we
can
back
it
out
if
there's
a
dissension
of
dissent
on
the
list,
just
in
the
interest
of
kind
of
keeping
up
the
tempo
that
we've
got.
You
know
radio,
silence,
I,
think.
A
H
H
B
H
B
A
A
Next
item
is
the
CAA
challenge.
If
you've
looked
at
the
mailing
list
and
a
cap
a
couple
days
or
yesterday,
and
today,
the
the
issues
are
that
the
CA
browser
for
mandates
RFC
whatever
at
six.
Eighty
eight
for
that
specifies
how
to
put
CA
records
in
DNS
and
one
of
the
things
you
put
in
there
is
you
know
which
CAS
are
allowed
to
sign
for
your
items.
A
The
examples
and
the
document
text
don't
match.
There's
a
BIST
document
going
on.
It
also
doesn't
match.
You
know.
Is
there
parameters
of
the
zero
space
parameters,
space
versus
tab,
I,
don't
know
of
any
good
solution
here
it
would.
We
could
try
to
file
in
errata
against
684,
but
there's
already
at
this
document
under
works
Sean.
You
look
like
you
can
say
something.
D
So
the
Tim
Holoubek,
the
purpose
of
the
errata,
is
because
the
business
is
probably
going
to
take
a
while
to
come
out.
Narada
is
would
be
basically
for
the
purpose
of
having
something
to
point.
To
that
says.
Nist
excuse
me,
IETF
has
acknowledged.
This
is
an
issue.
This
is
their
preferred
solution.
This
is
what
we're
going
to
do
in
the
short
term.
This
is
a
good
time
to
figure
out
what
we
want
to
do
here,
because
parameters
essentially
are
unused
in
the
wild
at
the
moment.
D
So
there's
relative
freedom
to
pick
what
we
want
now,
if
we
wait,
I
mean
acne
wants
to
use
this
now.
If
we
wait
we're
going
to
have
problems
with
as
well,
people
are
always
do
already
doing
it.
This
other
way,
so
I
don't
have
a
strong
preference
for
what
the
decision
is.
Just
that
we
make
a
decision
and
then
I'm
actually
very
active
in
this
here.
Browser
form,
and
you
can
point
Britt
and
say
right.
F
I
shot
Turner
again,
so
we
just
kind
of
have
this
process
where
we
point
to
a
document,
it's
got
an
errata
and
when
he
gets
updated,
the
old
one
goes
away
and
the
new
one
just
kind
of
gets
specified
like
we
kind
of
have
this
so
I
think
you
guys
have
the
ability
to
point
to
the
errata.
If
that's
the
way
you
want
to
go
well,
it
sounds
like
you
don't
want
to
do
is
like
be
pinned
waiting
for
this
other
document
to
get
right
the
process.
F
J
F
D
D
I
haven't
gone
back
and
looked
at
the
history,
but
if
here's
to
me
what
happened
was
that
the
a
B
and
F
and
the
examples
there
was
a
change
between
a
separator
being
spaces
and
I
think
something
else
and
one
of
them
got
updated
and
the
other
one
didn't
and
the
document
went
out
the
door
so
right,
it's
the
only
real
question
is
what
do
you
want
this
into?
What
does
the
you
know?
What's
the
consensus
for
what
this
index
should
be
the
examples
or
the
a
B
and
F
so.
A
D
A
Anyone
want
to
get
their
name
in
lights,
write
it
submit
an
errata.
Oh
okay.
I
will
take
the
action
to
talk
to
a
lawyer
offline
and
if
he
doesn't
do
it
I'll
do
it
okay.
So
that
means
that
then
the
CAA,
which
is
already
in
last
call,
will
move
forward
a
LPN
and
IP
validation.
I,
don't
think
he's
on
the
call
to
make
screens.
K
A
I
I
A
A
A
A
I'll
talk
to
the
email
documents,
this
meeting
conflicted
with
CFR
genie
so
Alexie's
over
there,
the
first
one
he
searched
for
s,
mine,
there's
a
challenge.
He's
got
some
discussion,
a
co-author
they're
working
on
it,
they'll
come
back,
I,
don't
know
they
will
meet
in
Bangkok
well,
actually,
because
the
stir,
we
probably
will
so
that'll,
be
coming
up
on
the
Acme
email,
TLS,
one,
the
other
acne,
the
other
acne
email.
Sorry,
sorry
doc.
He
says
it's
ready
for
last
call,
but
there
are
two
issues,
and
this
is
for
other.
This
is
for
servers.
A
L
Corey
Bowen
Howell
Trustwave,
so
I
took
a
read
of
via
the
draft
earlier
today.
One
thing
that
jumped
out
at
me
is
the
the
port
service,
header
parameters
or
actually
in
a
protected
jws
payload
or
not
in
the
payload
there
during
the
the
protected
header
they're,
not
in
the
payload,
which
I
think
is
basically
goes
against
the
way
how
the
base
acne
spec
encodes
the
request.
A
Just
a
quick
show
of
hands
how
many
other
people
have
read
this
document
either
one
okay
Tim,
not
many
okay,
I'd,
like
volunteers,
cuz
I,
don't
think
it
did
not
the
second
one
isn't
ready
for
last
call.
It
seems
to
me
how
many
people
promise
soon
to
read
the
next.
The
the
sir
email
server
document
document,
it's
pretty
short
if
the
scribes,
how
to
get
certs,
servus,
Tim,
yeah,.
D
D
I
forget
who
is
sitting
there,
but
the
general
view
is
that
LM
TP
support
was
not
really
necessary,
but
that
perhaps
the
issue
for
multiple
services
on
the
same
host
needs
a
closer
look
just
to
make
sure
that
it
doesn't
have
any
of
the
issues
that
we
ran
into
with
t
LSS
and
I,
for
example.
Okay,
all.
A
A
E
About
the
s
p--,
I'm
sure
to
you,
there
yeah,
I
think
I
just
looked
at
it.
It's
like
four
pages
right
and
there's
still
a
lot
of
like
TBD
in
it,
including
the
entire
security
considerations,
including
there's
just
a
lot
of
stuff
event.
Still
I
mean
if
you
haven't
probably
review
something
that
is
short
but
I
feel
like
that's,
maybe
not
ready.
Okay,
thanks
thanks.
A
J
J
So,
basically,
the
story:
again,
we
came
with
this
proposal
about
having
a
mechanisms
for
using
acne
to
generate
short-term
certificates
as
certificates
for
delegates
identities
of
the
desert.
I
guess
that
this
isn't
something
that
is
quite
familiar
the
now
there
is
a
draft
that
is
at
my
star
that
by
the
way
and
it's
our
fault,
we
didn't
send
you
an
update.
J
We
believe
it's
material
for
last
call
just
as
a
note-
and
this
is
something
that
well
I
know
that
should
be
in
the
other
part
of
the
agenda,
but
this
something
that
we
were
all
obvious
at
this
patch
our
stuff,
and
we
were
much
more
focused
on
that
so
and
forgot
I-
must
confess
I
forgot
to
send
you
the
yeah,
the
update,
so
we
believe
it
is
foremost
called
yes
for
if
anyone
is
taking
notes
for
the
minutes,
that's
that's
the
other
part.
Let's
say
how
do
you
admit
to
generate
these
temporary
delegate?
J
The
certificates,
then,
is
how
the
the
entity,
that's
asking
for
these
certificates,
requests
the
the
to
start,
the
the
Acme
process
to
the
owner
of
the
identity.
So,
basically,
let
me
say
this
is
a
CDN
that
is
asking
a
content
provider
to
give
to
provide
a
certificate,
a
temporary
certificate
that
can
be
used
by
the
CB
n
nodes
to
prove
that
they
are
using
a
correct,
correct,
delegated
identity
that
has
been
delegated
precisely
by
the
identity
on.
So
originally
we
in
a
certain
moment,
we
split
the
process.
J
On
the
one
hand,
the
the
pure
Ahmed
a
process,
and
the
other
case
is
how
do
requests
to
start
these
delegation.
We
were
told
to
go
to
check
this
patch.
Yesterday,
we
were
presenting
the
other
sexist
patch
believes
that
this
belongs
here
and
that
it
was
interesting
that
some
suggestions
were
made
there.
We,
we
went
with
a
with
the
draft
that
details
basic
rest
in
set
of
rest
interactions
who
to
send
a
request
and
receive
back
the
URL
with
the
certificate
generated
by
admin
and
during
the
discussion.
J
Some
of
some
people
who
are
reflecting-
and
this
is
something
I-
must
say
that
they
found
interesting
and
I
basically
agreed
with
they'd-
hear
that
for
these
requests
we
could
use
Acme
as
well.
Maybe
would
be
a
profile
that
maybe
because,
for
example,
validation,
it's
not
to
be
made
there,
because
you
don't
need
any
validation.
The
validation
is
made
in
the
other
leg
of
the
protocol,
but
at
least
that
we
could
use
a
basically
an
acme
request
as
well.
So
since
we
have
been
bounced
back
by
Sec
dispatch,
the
questions
are
and
is
a
fir.
J
This
is
whether
the
group
believes
that
the
problem,
not
the
solution.
The
problem
is
something
that
is
as
sec
dispatch
thinks
something
that
has
to
be
sorted
out
here
and
that
we
had
to
embrace
inside
that
minion
and
and
look
for
a
solution
for
this.
This
is
the
first
thing
were
asking.
The
second
thing
is
precisely
related
with
this
idea
that
appeared
during
the
success
patch
job
is
whether
this
request
should
be
implemented
and
as
they
are
right
now
in
the
documents
that
is
draft
Scheffer
is
not
on
me
any
longer
right.
J
Okay,
so
is
the
draft
Scheffer
Acme
stripe
request
whether
we
should
proceed
with
what
we
have
right
now?
Does
this
this
rest
protocol?
All
we
should
explore
the
idea
of
profiling
at
me,
I'm
thinking
you
know,
simplify
or
simplified
different
in
interaction
as
another
kind
of
Acme
request,
and
does
it
as
a
here
is
where
we
we
stand
right
here
right
now,
so
Eric.
B
A
H
The
following
observation,
which
was
that
you
could
just
make
this
an
Activia,
be
you
a
in
which
cases
to
be
something
which
we
prefer
you
met
here.
If
nobody
hears
reason
documenting
it,
then
I
think
you
kind
of
felt
like
a
no
or
you
could
ask
for
a
broth
but
I,
don't
think
you're
gonna
get
very
far,
but
so
I
think
they're
binding
in
the
sense
that,
like
you,
can't
really
come
back
to
success
patch
again
without
binding,
says
there
I
guess,
I
take
it.
B
Yeah
so
I
think
there's
a
potentially
interesting
problem
here,
but
it's
a
little
bit
hard
to
there's
a
pretty
significant
refactoring.
We
talked
about
it,
SEC
Dispatch,
so
I'd
kind
of
like
to
see
the
thing
in
a
new
form
before
I
make
it
go
no-go
decision
here
in
terms
of
what
that
problem
is
I
think
you
might
benefit
from
conceptualizing
it
a
little
bit
more
broadly
I
thinking
back
so
early
and
some
of
these
Acme
discussions.
People
were
asking
about
kind
of.
How
would
something
like
an
RA
like
a
remember,
Aria
stands
for
bridge
authority.
B
Yeah
really
right
people
looking
for
something
like
how
a
kind
of
intermediate
trusted
entity
like
that
could
fit
into
an
ACME
situation,
which
is,
if
you
look
at
the
architecture,
the
the
domain
owners
kind
of
acting
in
that
way.
So
you
might
reach
out
to
some
folks
that
have
kind
of
that
use
case
and
fold
that
in
and
I
think
that
would
become
a
little
bit
more
compelling
than
as
opposed
to
just
focusing
this
on
the
short
term
law
or
new
case
well.
F
H
F
E
Chat
Pearson,
so
looking
at
this
slide,
I
was
just
thinking
how
similar
it
is
to
a
slide
that
I'm
going
to
have
talking
about
authority
tokens
which
have
a
very
similar
problem
in
the
sense
of
you
need
to
kind
of
like
go
off
to
someone
to
make
a
request
from
the
authority,
and
we
were
just
actually
talking
about.
We
need
to
hack
in
some
protocol.
E
That's
going
to
explain
what
the
request
is
that
we're
making
in
this
Authority
we're
going
to
turn
around
and
give
to
the
acting
server
afterwards,
and
it
made
me
wonder
if,
like
this
is
an
I
may
be
coextensive
problem
even
in
terms
of
what
exactly
it
is
that
we're
trying
to
get
from
this,
so
I
mean
I'm
going
to
present
this
in
in
a
minute.
So
we
talked
about
it.
J
But
basically,
basically
the
concern
is
about
someone
the
Downs
and
identity
and
want
to
bind
it
to
a
private
key
that
they
don't
have
it's,
basically
that
which
is
the
archetypal
use
case.
You
say
again,
it's
a
CDN
note
that
without
you
don't
want
to
deliver
your
private
key
and
what
you
get
is
a
temporary
saying
that
can
be
a
so.
The
idea
I
remember.
I
J
Basically
that
whether
I
mean
boof,
maybe
thinking
what
Richard
was
saying,
maybe
that
we
are
talking
about
something
that
is
a
much
more
general
environment.
We
could
think
about
making
them
commercial
I,
don't
know
what
I
would,
like
my
golfers
to
say
have
their
say,
because
maybe
I
was
a
to
me,
looks
looks
cool.
E
Discussion
about
this
and
figures,
I'm
saying
a
lot
of
what
we
came
to
as
we
started
cook
here
and
the
stuff
that
we're
doing
Worcester
as
the
need
for
this
kind
of
more
generic
mechanism,
for
it
right
and
I
could
see
there
being
set
of
kind
of
adjacent
tools
to
Acme
that
provide
properties
just
like
this,
that
are
probably
as
generic
as
what
we're
doing
on
the
authority.
Joking,
but
please
other
people
weigh
in
on.
K
For
delegation,
we
need
two
pieces.
One
is
the
piece
that's
hopefully
going
into
working
group
last
call
here,
which
is
an
arc
extension
and
I
think
we
have
like
general
consensus
how
this
can
be
done.
There's
also
this
other
piece
of
the
request.
Were
the
client
delegate
requests
delegation
from
the
forwarder
for
lack
of
a
better
name.
K
Today
we
have
a
very
simple,
very
small
solution
for
the
request
piece
it
could
be
termed
as
a
subset
of
Acme
and
it
could
be
generalized
into
something
more
like
a
registration
registration,
whatever
it's
called
array.
So
it's
also
ready
right,
but
we
have
not
heard
an
actual
requirement
for
an
for
an
RA
in
acne,
so
we're
taking
a
very
small
solution,
that's
actually
needed
by
a.
H
Right
I
mean
procedurally
you
just
kind
of
outright
order
here.
I
mean
basically
the
the
way
in
which
you
have
a
number
of
options
for
bringing
work
work
here
and
those
options
are,
you
know
like
if
you
want
to
do
something
that
is
like
the
thing
your
repose
or
your
object,
your
avenue
for
that
is
dispatch,
sex
dispatch
or
asking
for
a
boss,
and
if
you
wanted
to
say,
and
so
like
I,
think
you
kind
of
didn't
get
like
relief.
Super
positive
response
there.
J
A
So
I
I
don't
hear
anyone
saying
this
is
a
bad
idea
to
make
this
thing
fit
in
the
Acme
framework.
The
best
the
most
negative
thing
is
well.
We
don't
have
a
document
yet
to
really
look
at
so
bring
it
up
on
the
lists.
We
have
at
least
some
people
on
them
in
the
group
who
were
interested
in
doing
this.
Obviously
they've
gone
and
come
back
and
garden
come
back,
so
you
know,
let's
give
them
another
spider.
Let's
do
it
any
objections.
Concerns
okay,
go
off
and
write
and
do
it
zero,
zero
and.
J
B
A
A
A
G
G
The
problem,
basically
is
if
an
attacker
can
reuse,
an
IP
address,
for
which
is
their
DNS
record
exists.
So
you
know,
as
we
got
pointing
to
an
IP
address,
the
attacker
can
actually
get
a
valid
certificate
by
a
domain,
public
domain
validation
and,
in
fact,
was
a
serious
problem.
So
we
did
a
measurement
study
and
we
found
seven
hundred
thousand
domains
which
were
actually
stale
pointing
to
Amazon
ec2
instances
demonstrated,
says
relatively
easy
to
actually
get
an
IP
address.
That
points
to
a
specific
domain
which
you
want
to
take
over.
G
Basically,
this
is
not
only
IP
use
after
free,
this
is
Oscars
after
free.
So,
for
example,
uber
was
hit
when
one
of
their
load
balancer
instances
that
they
had
used
was
Amazon
became
stale,
so
they
still
had
it
in
the
rotation,
but
well
they
forfeited
it,
and
then
an
attacker
was
able
to
actually
register
it
and
thereby
steal
cookies
for
us,
if
you
were
at
home,
which
meant
that
they
could
basically
steal
accounts
from
Hoopa
users,
and
this
can
also
happen.
G
This
should
have
only
been
one
slot.
So
what
are
we
doing
about
this?
So
we
do
have
on
the
standard
process
of
requesting
your
certificate,
getting
back
a
challenge
and
hosting
the
challenge
of
HTTP.
What
we
are
suggesting
is
an
additional
step,
so,
instead
of
directly
sending
back
the
challenge,
you
first
check
to
see
T
logs,
see
if
there
has
been
ever
certificate
issued
for
the
domain,
for
which
you
see
a
certificate
request
and
if
there
ever
has
been
a
certificate
issued
for
that
domain.
G
You
actually
ask
the
requester
to
host
the
challenge
for
HTTP
on
this.
A
little
bit
of
argument
proxy
here
occurs.
There's
some
considerations
we'll
go
into
like
later,
but
technically
this
should
prove
that
authority
over
the
domain
was
continuous,
so
that
the
person
now
requesting
a
certificate
is
the
same
person
or
a
person
authorized
by
the
party
request
as
a
previous
certificate
to
actually
request
a
new
certificate.
G
This,
of
course,
comes
with
several
civets,
so,
for
example,
what
do
we
do
if
things
fail?
What
we
do
do
we
do
if
the
certificate
has
expired?
There
was
some
discussion
about
proving
possession
of
original
keys.
That
was
in
version
zero,
zero
of
the
ACMA
drop
and
section
7.3,
there's
other
questions.
What
we
can
do
if
things
fail,
so
we
could,
for
example,
say:
okay,
let's
gracefully
do
a
dns
charge
the
curse,
then
you
cannot
only
take
over
a
single
IP
uterus.
G
You
actually
have
to
take
over
the
whole
domain
and
if
you're
then
bruiser
again
also
requiring
DNS
SEC
you're,
also
preventing,
for
example,
BGP
MRT,
an
attacks,
there's
a
lot
of
corner
cases.
We
would
have
to
investigate.
So
what
happens
if
you
lose
a
case?
If
there's
some
disaster
happening
to
your
server,
no
backups
or
if
your
opponent
process
is
actually
broken
and
you're
just
randomly
losing
Keys
hoping
to
be
able
to
reissue,
again
and
again
again.
G
And
there's
also
problems
with
using
HTTP,
so
HTTP
is
explicitly
not
allowed
and
the
ACMA
HTTP
challenge
I
think
it
was
already
mentioned
earlier.
This
is
because
of
the
SNR
problem,
which
means
that
you
might
be
displaying
a
default
be
host
that
then
can
be
used
to
actually
also
impersonate
the
client,
which
is
somewhat
similar
to
the
problem.
We're
trying
to
address
you
technically
for
the
case
we
are
dealing
with.
G
This
is
not
a
problem,
because
we're
assuming
that
there
are
already
is
a
certificate
so
under
default
the
old
case,
certificate
validation
would
not
be
successful
because
the
common
name
does
not
match.
Another
option
would
be
to
actually
building
a
dedicated
challenge
in
which
the
previous
SSL
keys
are
used
to
sign
a
challenge.
G
So
from
all
perspectives,
there
are
several
next
steps,
so
we
should
first
figure
out
on
the
different
corner
cases
and
should
figure
out
how
many
certificate
issuances
are
actually
affected.
By
this,
we
plan
to
write
a
draft
document
for
this
in
the
next
couple
of
weeks,
which
is
hopefully
available
for
discussion
in
bangkok,
and
we
want
to
brought
some
PRS
to
the
ahmed
client
server
implementations
to
actually
enable
this.
B
It's
Richard
Bunn,
so,
first
of
all,
thanks
for
this
I
think
this
is
is
really
it's
interesting
work
that
you've
found
that
there
is
this
issue
and
I
think
this
is
a
real
risk
to
the
PKI
ecosystem.
You
know
applause
even
more
broadly
than
a
commune.
It's
great
that
you
guys
have
have
looked
into
what
the
mitigations
could
be.
B
We
had
that,
for
instance,
using
the
DNS
challenge
to
fall
back
when
you
you
can't
when
you
run
into
these
brittleness
problems,
though
yeah,
where
you've
lost
the
prior
keys,
so
I'm
looking
forward
to
after
I
think
this
is
something
work,
but
there's
probably
some
useful
stuff
to
be
done.
I'd
be
interested
to
hear
from
some
of
the
CAS
in
the
room.
I'm
looking
at
like
Tim
and
CPU,
like
is,
is
this
something
you
guys
find
concerning
and
where
you
might
be
interested
in,
you
know
trying
to
do
better.
H
Okay,
Erica
school
I
guess
Richard
may
be
that
the
pieces,
the
peas
in
that
red
box
there
like
doesn't
actually
need
to
be
like
dinner
eyes
at
all
right
yeah.
You
know
that
basically
I
mean
I,
think
the,
but
there's
this
working
you
must
standardize.
If
anything
is.
This
is
how
you
establish
that
the
prior
available,
okay,
the
priority
that
will
certificate
actually
is
it
corresponds
the
new
request
and
something
right
box.
It's
just
like
there's
some
Oracle
hotels
use
appraised
it.
These
are
all.
D
D
M
D
Are
lots
of
things
that
aren't
so
that
one
actually
was
one
of
Ryan's
Levy's
favorite
things
to
worry
about
before
it
became
one
of
the
things
that
he
decided?
He
no
longer
was
worried
about
a
couple
years
ago
in
Switzerland.
He
wanted
CAS
to
check
every
month
whether
the
the
domain
validation
was
still
valid.
I
mean
that's
part
of
the
problem,
with
certificates
as
you're
certifying.
What's
true
at
the
time
of
issuance,
and
it
may
cease
to
be
true
in
the
future
and
I,
don't
know
other
than
revocation
how
you
deal
with
that.
A
B
What
I
would
expect
to
see
in
this
draft
is
some
protocol
mechanism
for
proving
possession
of
a
prior
key,
probably
I,
either
resurrecting
some
of
the
syntax
we
had
before
to
Jason
Lee
over
HTTP,
together
with
some
operational
considerations
about
when
you
would
use
that
mechanism
and
how
it
would
fit
in
with
some
other
stuff.
This
isn't
actually
just
so
that's
what
I
expect
seeing
droughts.
This
is
it's
just
to
clarify
the
scope
here.
This
isn't
actually
about
continuity,
invalidation.
B
B
You,
then
let
that
a
record
there
cancelled
your
AWS
account
an
AWS
recycled,
the
IP
address
and
reassign
it
to
those
guys,
and
so
when,
when
those
those
guys
can
now
go
to
you
and
get
certificate
or
it
can
go
to
the
CA
and
get
certificates
for
your,
for
example,
comm,
even
though
they
don't
have
an
example
comm.
Yes,.
D
So
that's
another
one
that
no
well,
we
actually
solved
it,
so
it
was
easy,
but
then
people
decided
they
didn't
want
to
do
with
this.
This
is
related
to
the
question
of
whether
whether
you
can
do
validation
successfully
was
stale
information.
That's
sitting
around
from
previous
validations.
The
entire
point
of
the
improvements
to
the
validation
methods
that
we
made
involving
a
challenge
response,
was
supposed
to
prevent
that
threat.
It
does
not
work
with
certain
things
that
people
want
to
do
around
delegated
validation
or
they
just
want
to
point
over
to
some.
D
A
L
So
this
court
from
Trustwave
so
I'm,
looking
at
the
the
workflow
here
and
I'm
wondering
if
we
could
maybe
simplify
it
a
bit
since
most
web
P
cached
if
it
gets
now
having
better
that
cts
I'm
wondering
that
you
could
basically
remove
that
step
to
check
for
existing
certificates.
Do
the
do
the
host
challenge,
retrieve
the
certificate
and
then
look
up
and
there's
in
the
certificate
transparency
log
using
the
embedded
SE
one
of
yes,
one
of
the
embedded
SVT's
to
go
and
see.
L
A
N
As
a
small
note
and
earlier
when
you
were
mentioning
the
the
fallback
2d
NSO
one
challenge
type
from
a
practical
perspective,
the
deployments
that
we've
seen
of
acne
clients,
particularly
with
large-scale
integrations
at
hosting
providers,
they
almost
always
select
one
challenge
type
and
their
client
is
configured
only
to
address
that
challenge
type.
It's
the
idea
that
if
you
are
an
integrator,
even
an
individual
user,
that's
running,
surf
odd
or
another
acne
client
expecting
to
solve
an
HTTP
or
one
challenge,
and
the
server
gives
you
back.
N
Just
a
DNS,
so
one
challenge
I,
would
say
almost
universally.
That
client
is
not
going
to
be
set
up
to
provision
the
DMS
records
in
the
zone,
not
expecting
it
so
it
you
know
we
could
get
to
a
world
where
maybe
the
clients
would
support
multiple
authentication
methods
and
the
user
would
have
to
configure
all
of
the
authentication
methods
that
may
be
possible,
which
will
be
challenging,
especially
based
on
the
DNS
own
requirements
and
they
update
API.
N
E
H
E
I'm
doing
this,
ecker,
like
circa
2005
speeds
what
we're
aiming
for
excellently
so
for
those
not
reversed
in
this
work.
This
is
our
attempt
to
leverage
Acme
and
provide
certificates.
That
will
be
helpful
in
defeating
Robo
call
that
annoying
crafts
from
going
around
forever.
But,
as
we
looked
at
this
problem,
what
we
quickly
discovered
was
that
we
needed
a
more
generic
mechanism
really
to
be
able
to
go
out
and
to
ask
an
authority
who
knows
things
about
telephone
numbers,
about
similar
resources
that
exist
outside
of
the
internet.
E
Basically,
to
give
us
some
kind
of
token
that
a
client
could
then
present
in
response
to
a
challenge
to
an
ACME
server
in
order
to
get
a
say,
a
CI
issued
for
the
proper
resource,
and
you
know,
as
we're
kind
of
studying
that
looking
at
the
edges
of,
but
we
realized
this
was
applicable
actually
to
a
whole
lot
of
different
things,
and
so
we
have
this
document
here,
the
Acne
authority,
token,
which
kind
of
genera
sizes
this
mechanism
Chris
went
in.
A
second
is
going
to
talk
about
the
specific
application
of
this
to
the
problem.
E
We
have
for
issuing
certs
for
telephone
numbers
and
for
similar
resources
next
slide.
So
this
is
we're
talking
about.
Basically,
we
are
creating
a
challenge
cipher
40k
off
and
we
have
a
subtype
mechanism
for
right
now
called
a
TC.
This
is
based
on
the
notion.
We
might
actually
want
to
have
multiple
subtypes
for
this
and,
although
we've
gone
back
and
forth
about
this,
I
still
think
there's
some
utility
potentially
in
doing
that.
I
don't
know
if
we
really
have
time
to
delve
too
much
into
that
issue
today.
E
The
basic
idea,
though,
is
that
the
token
you're
gonna
get
from
an
authority
is
a
job
and
that
you're
then
going
to
present
this
job.
We
just
gonna
have
some
stuff
in
it.
That's
gonna
make
it
clear
kind
of
what
the
Acme
account
is
and
what
the
resources
you're
asking
for
that'll
go
back
to
the
Acme
server
response
to
the
challenge
and
presto.
You
get
your
circle
resource
next
slide,
please
and
so
yeah
this
this.
You
can
see
how
we,
with
just
kind
of
jam
in
the
Acme
response
there
down
the
payload.
E
E
So
I
will
try
to
at
least
say
things
about
a
couple
open
issues,
people
a
microphone
and
speak
to
this.
If
they
were
so
inclined
previously,
we
had
a
discussion
about
whether
or
not
we
should
use
the
fingerprint
or
the
nonce
to
kind
of
bind
the
token
that
was
being
generated
by
this
authority
to
the
the
Acme
challenge.
If
you
found
really
to
the
challenge
or
to
the
Acme
account-
and
that's
really,
the
distinction
here
between
the
fingerprint
vs.
E
nonce
and
what
we
decided
to
do
is
to
say
that
for
the
use
case,
we're
most
interested
in,
we
think
fingerprint
works
best,
the
reasons,
some
of
which
are
actually
really
like
star,
that
we
want
to
be
able
to
get
short-term
certs.
And
so
we
want
to
be
able
to
issue
one
of
these
tokens
potentially
reuse
it
to
get
multiple
certs
from
it,
without
having
to
kind
of
go
back
and
constantly
be
paying
the
authority,
and
things
like
that.
E
What
actually
makes
more
sense
to
say
for
this
kind
of
authority
yeah
you
want
to
actually
have
be
bound
to
that
particular
challenge
that
was
issued.
You
know
by
the
Acme
server
I
know
that
we
have
like
no
time
so.
I
don't
want
to
get
too
much
into
this.
We
also
as
I
just
mentioned
earlier.
We
have
this
notion.
E
There
should
be
a
way
to
go
to
a
token
authority
and
to
say:
hey,
I
need
one
of
these
jobs,
and
that
requires
protocol
and,
as
we
thought
about
that,
we're
like
well,
we
should
probably
mock
something
up
right
now.
We
just
have
like
DVDs,
and
the
document
about
it
are
thinking
up
until
now,
anyway,
had
been
we'll
just
use
the
rest,
a
REST
API.
E
Some
of
the
people
who
are
applying
this
to
the
telephone
problem
have
already
suspect
one
in
another
sto
and
add
us,
and
we
can
just
basically
like
scarf
all
that
material
and
put
it
in
here,
but
if
there
is
a
need
to
create
something
more
generic
that
might
help.
The
Starr
case
that
you
were
discussing
like
I'd,
certainly
be
open
to
that
and
I
guess.
E
O
O
I
changed
the
value
to
a
base.
60
and
64
encoded
value
next
slide
same
thing
with
challenge
in
a
response,
you
have
that's
the
value
there
that
was
changed
next
slide
and
then
the
ATC.
This
is
the
fingerprint
part
in
the
ATC
claim.
I
have
an
example
in
the
document
where
it
shows
the
fingerprint
and
I
defined
it
as
I.
Think
typically
has
done
the
algorithm
and
then
the
the
X
values
with
colons
and.
O
A
Yeah
I
have
to
show
hands
how
many
people
have
read
do
with
the
simple
I
either
or
both
of
the
documents:
okay,
so
yeah,
skimmed
it
okay!
So
right,
this
is
like
secure
identifiers
for
mobile
telephones.
This
could,
in
he
anyone's
got
a
mobile
phone,
wants
to
know
who
the
other
side
of
the
party
that's
right.
This
is
important
in
useful,
so
I
again
encourage
people
and
the
user
community
of
mobile
phones
is
going
to
obviously
swamp
to
user
communicative
websites
before.
J
J
Probably
with
a
different
goal-
and
this
is
important-
because
in
one
case
we
are
talking
about
accessing
general
information
in
this
case
is
something
that
it's
much
more
sensitive
from.
This
is
probably
there
should
be
mu,
or
we
should
be
much
more
careful
here
that
maybe
the
guys
involve
anyone
well.
E
Play
right
in
a
sense,
these
these
resources
are
not
like
human
resources
that
we
use
for
like
SSO,
or
something
like
that
right.
These
are
like
industrial
things
controlled
by
the
government
bodies
that
are
issued
for
corporations
for
a
purpose.
It's
very
different
from
like
I
need
the
login
or
whatever
to
multiple
places.
So
yeah
I
mean
I,
don't
I,
don't
think
I've
got
my
head.
I
see
a
great
deal
analogous,
but
maybe
there's
more
to
discuss
about
that.
Well,.
