►
From YouTube: IETF103-BESS-20181105-1350
Description
BESS meeting session at IETF103
2018/11/05 1350
https://datatracker.ietf.org/meeting/103/proceedings/
B
A
A
A
So
one
point
that
has
been
raised
by
a
Martina:
our
ad
is
that
some
of
the
drafts
are
still
not
choosing
via
new
requirement
language
templates.
So
please
ensure
that
all
of
your
draft
now
are
using
this
new
flavor
of
requirement
from
which
template,
which
is
into
the
RFC's
8174,
which
cry-face
via
ambiguity
between
usage
of
lowercase
and
uppercase
requirement.
Keyword
request
must
not,
and
so
on.
So
please
use
this
new
template.
A
So
this
is
our
hangender,
it's
not
completely
full,
but
it's
quite
it's
quite
still
quite
busy.
So
we
will
take
a
lot
of
time
to
review
as
working
up
statutes
and
documents
and
we
will
have
some
documents
about
evpn
OAM,
some
more
redundant
multi
test
source
for
EPN,
a
new
service
type
interface
for
a
VPN,
secure.
D
A
So
stage
some
date
we
don't
have
any
new
RC
since
last
IDF,
however,
we
have
several
documents
that
are
in
the
RFC
editor.
Q2
documents
are
still
pending
because
of
a
mr.
F,
so
we
can
overlay
still
waiting
for
the
tunnel
encapsulation
draft,
which
I
think
is
under
shepard
review.
Now
in
idea,
is
it
one
of
you
are
here?
Okay,
so
please
make
it
progressing
fast
and
we
have
another
one,
which
is
a
prefix
advertisement,
which
is
a
really
important
work
force
which
is
still
missing
the
intercept
net
forwarding
draft
so
ali.
A
A
So
increment-
and
we
have
also
the
last
me
be'
draft
about
m
VPN
and
layer,
2
layer,
3
VPN,
which
suggests
that
are
also
in
the
AFC
editor
cube.
We
have
also
some
documents
and
AG
review.
So
will
it
really
seamless
integration,
so
Martin
I
think
you
have
sent
some
current
on
it,
but
you
have
not
send
it
to
the
list
and
I.
Don't
think
that
you
have
received
any
reply.
E
E
A
E
A
A
So
we
don't
have
any
documents
that
are
ready
now
to
go
to
a
ESG.
However,
we
still
have
some
documents
that
asked
you
was
at
our
post
watching
hopeless
core.
So
again
we
intercept
net
forwarding
so
I
think
this
isn't
working
hopeless
:
this
one
and
we
still
have
some
comments.
So
now
it's
really
urgent
word
who
updated.
So
please
do
it.
By
the
end
of
the
month,
we
did
also
working
hopeless,
:,
his
best
service
training
draft.
A
F
And
for
me
to
progress,
because
there
is
this,
work
is
I,
think
very
useful
in
a
very
simple
service.
Training
I
think
does
a
number
of
good
things,
but
I
think
there
is
a
lot
of
coaches
when
you
implement
this,
which
should,
in
my
view,
be
reflected
in
that
draft
which
are
not
there.
I
think
the
comments
were
mainly
around
those
things.
A
A
A
So
I
don't
know
Mac
you
are
in
the
room,
unfortunately
not
so
he
has
to
provide
the
writer,
but
at
least
the
review
has
been
as
been
done
and
we
have
free
documents
that
are
ready
for
working
up
last
call
for
so
fast
failover
I'm,
just
wondering
if
it's
requires
a
new
revision
before
we
do
be
working
on
PLAs,
Cole
I.
Think
there
was
a
comment
raised
by
I
think
it
was
by
Alice
at
last
idea
that
need
to
be
taken
into
account
for
the
working
on
pleskot
is
done.
A
So
we
have
three
new
working
documents,
so
the
flow
direction
of
advancing
for
evpn
and
the
vehicle
segments
for
Vienna.
We
have
possibly
three
documents
that
are
all
ready
for
working
up:
adoption,
the
MVP
and
yang,
because
we
need
to
adapt
it.
There
was
already
a
poor
that
failed,
but
a
new
poll
in
it
needs
to
be
done.
We
are
wondering
if
the
LSP
ping
draft
and
the
ping
proxy
draft
are
ready
for
working,
hope
adoption.
So
if
the
authors
are
there,
could
you
just
say
us?
A
A
G
A
A
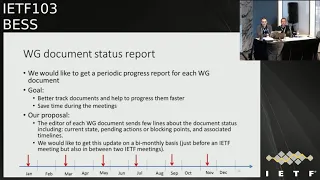
So
working
group
document
status,
we
have
some
issue
to
get
some
progress,
update
only
working
group
documents,
especially
when
we
have
some
sessions
like
this
one,
where
there
is
only
one
working
document
they
presented.
So
what
we
would
like
is
to
better
track
these
documents
and
make
them
progressing
faster.
A
So
what
we
are
proposing
is
that
each
editor
of
a
working
group
document
send
us
just
a
couple
of
lines
periodically
about
document
status,
what
we
need
to
ensure
what
we
need
to
to
get
islam.
What
is
the
status
of
the
document
is
where
what
is
also
pending
actions,
and
especially,
is
very
blocking
point
where
you
need
some
help
to
make
the
document
progressing,
and
we
want
also
to
get
your
timelines.
A
A
So
we
would
love
to
get
this
every
two
months
if
possible.
So
this
means
before
each
ATF
meeting,
but
also
in-betweener,
so
possibly
in
January
March
for
ATF
May
July
for
ATF
September
or
November.
Okay,
it's
not
a
lot
of
work,
just
two
or
three
lines:
tellings,
what's
your
plan
and
so
on.
So
it
will
help
us
12
the
statutes
on
what
is
going
on
and
we
are
also
able
to
help
you
if
there
is
something
that
is
blocking
or
possibly
you
don't
have
time
to
do
something
yeah.
A
E
I
Lower
Anderson,
we
are
doing
something
similar
in
MPLS,
though
we
request
reports
for
each
meeting,
not
like
this
by
monthly
stuff,
our
the
conclusion
or
our
understanding
of
it.
The
process
here
is
that
if
you
have
a
document
that
we
don't
have
any
problem,
this
is
very
easy.
We
get
reports
like
four
or
five
days
before
the
meeting,
and
we
can
put
them
on
in
the
slides
the
documents
that
we
have
problem
with
nothing
happens,
no
reports,
no
nothing
so
I
think
you
will
get
into
the
same
problem
here.
I
So
if
you
have
very
small
number
of
problematic
documents,
then
you
can
interact
with
one
or
two
of
the
authors
to
get
reports
kind
of
implicit
in
remain
male
responses,
and
you
can
kind
of
create
the
two
liner
at
yourself,
which
should
we
are
doing
in
MPLS,
sometimes
so,
I,
don't
think
this
is
too
much
work
for
the
author,
but
it
you
actually
creating
a
lot
of
work
for
yourself.
That's.
A
E
Agree
with
ro
I
think
that
it
will
add
a
lot
of
additional
work
on
your
side,
but
that
might
be
part
of
being
a
chair
and
I.
Think
the
the
the
first
bullet
point
of
the
goals
is
the
more
important
one
so
that
you,
you
have
a
better
vision
on
the
target
to
date
and
the
readiness
of
a
document.
So
you
can
better
track
that
I.
I
I
A
J
J
J
In
that
case,
the
chosen
PE
will
actually
decide
on
which
of
the
attachment
Circus.
It
will
accept
traffic
and
fork.
So
that's
the
one
step
solution,
the
hot
pans,
hot
standby
solution
is
that
some,
both
keys
coming
through
the
sources
will
send
traffic
into
Internet
network,
but
each
downstream
key
were
independent,
independently,
decide
from
which
ingress
feeds
traffic
will
be
accepted
and
forward
it
on
to
the
end
receiver.
J
So
there
here
are
some
very
high-level
details
on
how
warm
standby
works.
If
you
look
at
the
picture,
we
have
upstream
P's
p1
p2
there.
They
are
configured
to
know
that
group
1
is
a
single
for
flow
group
notice
that
the
sources
could
be
connected
or
different
PDS
or
not
connected
as
a
different
piece.
J
So
for
the
action
piece
to
let
each
other
ins
know
that
they
are
connected
to
the
redundant
sources,
we're
using
this
SPSA
rod,
selector
pins,
e8e
routes
and
indicating
deaths.
This
is
for
a
single
flow
group
and
they
are
important
by
all
the
peas
and
and
the
upstream
he
is.
They
will
receive
each
the
SPD
route
from
each
other
and
they
were
to
a
DF
erection
notice
that
the
traditionary,
the
DF
reduction,
is
using
the
ethernet
signals
and
the
purpose
of
the
even
a
segment
routes
is.
D
J
J
So
again
the
p1
p2
do
it
was
choose
one
person
except
traffic
and
send
into
the
net
network.
In
there
14
states
they
will
add
some
RPF
checking.
So
that's
on
the
children's
folder.
If
you
have
multiple
as
attachment
circuits
Calculon
through
those
sources,
then
only
Wilder
basis
will
be
used
to
accept
traffic
and
for
HUD
stand
by.
If
you
look
at
the
picture,
we
have
the
red
and
blue
flows.
J
J
Here.
The
ingress
P
doctoring
piece
will
again
will
seek
a
signal
to
the
downstream
piece
that
certain
groups
are
single
flow
groups
and
they
also
in
they
will
use
the
S
Pen
sea
routes
for
their
purpose.
In
that
pians
SP
in
the
route
they
will
identify
the
internal
segments
on
which
the
sources
are.
So
that's
how
the
downstream
PE
can
use
can
can
can
use
the
SPI
routes
to
make
each
one
to
make
an
independent
selection
on
which.
J
J
K
L
L
J
J
N
O
L
When
you
do
that,
you
can
do
the
same
thing:
that
okay,
for
these
a
specific
group
run,
the
DF
election
I
think
the
difference.
The
reason
I'm
saying
that
it
needs
to
be
extended.
The
current
EF
election
is
because
the
current
EF
election
is
limited
to
a
given
Ethernet
segment,
whereas
this
can
it
spans
across
multiple
Ethernet
sickness,
because
it
can
sit
on
different
BSS
right.
J
L
L
And
there
was
a
certain
point:
there
was
a
notion
of
the
hierarchical
es
that
spans
across
multiple
years,
so
that
maybe
should
be
considered
and
on
this
front
a
still
currently
up
to
this
point,
as
PMC
were
used
for
the
on
the
receiver
side.
When
the
receiver
indicated
they
have
an
interest,
they
were
using
the
s-pen
cities
and
the.
A
J
I
P
Yeah
I
would
say
this
looks
sort
of
reasonable
to
me.
My
only
concern
is
maybe
that
it
requires,
of
course,
certain
deployment
that
it
chooses.
Your
group
addresses
I
mean
not
every
dementia
close
use.
The
same
group
address
so
I
was
wondering
if
you
have
forth
about
some
way,
instead
of
signaling
that
you
know
you
have
maybe
two
different
desk
emojis,
that
form
like
a
redundancy
group
or
something
like
that.
We.
J
Thought
about
that
in
in
fact,
initially
with
s1,
she
would
ever
has
s
once
you
and
an
s2
gg1
a
spin
0.
We
figured
that
you
have
those
two
roles
with
different
route
keys.
It
makes
it
harder
for
for
the
software
to
to
group
them
together.
So
we
said
using
the
starship
and
then
man
Akana
actually
has
a
good
point
that
you
can
just
use
source
prefixes,
for
example,
s1
s2.
J
H
P
D
A
Q
So
in
this
presentation
we
are
defining
new
service
interface
type.
So
before
going
to
what
exactly
it
does,
maybe
it's
good
to
talk
about
what
exactly
we
need
or
what
are
we
expecting
so
some
of
the
deployments
they
need
to
have
multiple
subnets
within
single
domain
when
we
say
multiple
subnets,
so
they
will
be
differentiated
by
VLANs.
And
now,
if
you
see
seven,
four
three
two
defines
three
type
of
service
interface
and
these
three
types
are
we
land-based
service
interface,
and
here
we
have
one-to-one
mapping
with
respect
to
bridge
domain
and
VLAN.
Q
But
if
you
see
traffic
is
expected
to
be
coming
tagged
and
that's
how
we
are
able
to
get
the
right
port
and
in
case
of
wheel
and
aware
bundle
services,
we
we
have
multiple
bridge
tables,
but
the
actual
requirement
was
to
have
single
bridge
table
and
having
still
having
multiple
subnet.
But
one
more
question
comes
here
that
why?
What
is
the
motivation
for
anyone
to
do
that?
Q
So
one
of
the
motivation
will
be
will
be
simplicity
because
if
you
want
to
have
hundreds
of
subnets
and
if
you
end
up
having
100
I
arm
interface,
basically
you
have
to
have
those
many
configurations
and
you
have
to
manage
IP
addresses
so
many
other
things
and
just
to
understand
the
problem
statement.
So
if
you
see
here,
P,
1
and
P
2,
they
are
multihomed
and
they
are
multi
whom
are
active
and
if
you
see
I,
am
showing
different
color
of
subnets
here
and
in
the
same
yes.
Q
So
if
P
one
learns
about
Mac
of
h1,
and
today
we
just
do
when
we
send
my
crowd,
so
p2
will
receive
the
macro
format.
1
and
P
3
will
also
receive
the
same
macro
now,
if,
let's
think
about
the
case,
if
traffic
is
coming
from
the
IRB
interface,
so
if
you,
if
you
are
getting
traffic
from
the
IRB
interface,
you
don't
have
any
VLAN
tag
there.
Q
How
are
you
going
to
associate
that
which
subnet
basically
Mac
1
belongs
to
because
P
2
doesn't
know
about
it
today,
when
we
we
send
the
macro,
we
don't
send
Ethernet
tag
and
a
similar
way.
It's
for
Mac
2,
also
now
one
of
the
question
which
comes:
why
can't
we
just
send
the
ether
tag
in
the
macro?
So
if
we
do
so
what
is
going
to
happen?
Q
Q
So
this
information
is
supposed
to
be
used
by
only
multi-home
peer
and
to
do
so
we
are
using
a
new
extended
community
and
this
extended
community
is
called
so
it
will
carry
the
attachment
circuit
ID,
and
this
attachment
circuit
ID
extended
community
has
to
go
for
unicast,
sorry,
Mac,
IP
route
and
route
X
7
at
eight,
which
is
multicast
so
just
to
go
back.
Why
exactly?
We
need
it
for
multicast,
so
if
you,
if
you
see
let
us
say,
host
h1
sends
IGMP
join
and
I
jump.
We
join
reach
to
p1.
Q
Mac
route
is
not
only
for
the
multi
home
Pia,
where,
as
it
goes
to
remote
piece
as
well
so
remote,
we
must
ignore
attachment
circuit
extended
community,
whereas
only
multi,
whom
we
are
should
be
using
it
so
with
respect
to
control,
plane
operation.
So,
let's
think
about
what
is
going
to
happen
for
the
loop
route.
So
when
he
learns
local
local
route,
it
must
attach
new,
extended
community
with
Mac
route
and
same
thing
with
multicast
routes,
which
is
route
pipe
seven
and
eight
at
the
remote
side.
So
the
more
for
the
remote
route
you
could.
Q
You
could
be
one
of
the
two
role
either.
You
are
remotely
are
you
or
multihomed
peer?
If
your
remote
Pia,
you
must
ignore
it
in
the
Mac
route,
you
you
must
not
ignore
the
Mac
route,
whereas
you
must
ignore
the
extended
community
information
and
remote
remote
P
is
not
going
to
get
multicast
route
so
for
multicast
route.
There
is
nothing
to
do
with
respect
to
remote
ease
for
multi,
home
P
for
multicast
routes.
You
must
set
your
s,
comma,
G,
R,
star,
comma
G
association
with
appropriate
subnet
and
even
the
same
thing
for
my
crowd.
Q
For
data
plane
operation
for
non
multi-home
peer,
so
with
respect
to
non
multi-home
PF,
there
is
no
change.
Whatever
procedure
has
been
defined
in,
say
one
four,
three:
two
it
it
will
be
still.
It
remains
same
data
plane,
operation
at
multi-home
PF.
So
now,
so
there
are
two
ways
if
traffic
is
coming
from
the
see
nothing
changes.
Whatever
is
a
procedure
has
been
defined
in
seven
four,
three
two,
it
remains
same
and
unknown.
Unicast
packet
must
follow
the
same
procedure.
Q
What
has
been
defined
in
seven
four,
three,
two
and
with
new
defined
service
interface,
type
or
known,
known,
unicast
packet.
Now,
when
we
do
Matt
lookup,
we
are
going
to
get
old,
plus
V,
9
and
4,
and
with
respect
to
multicast
traffic,
known
multicast
traffic,
we
are
going
to
get
the
appropriate
a
see
where
this
traffic
has
to
go
out.
A
L
Basically,
the
gist
of
this
is
this
solution
is
intended
for
the
hardware
or
low
cost
hardware
that
have
a
limitation
that
they
cannot
have
one
bridge
domain
per
subnet,
because
up
to
this
point,
we're
talking
about
villain,
aware
bundled
service
that
we
can
ask.
We
can
allocate
one
bridge
domain,
one
bridge
table
per
subnet.
There
are
hardware
with
that
limitation
and
for
those
hardware
we
are
saying:
okay,
you
can
use
one
bridge
domain,
use
it
for
a
lot
of
subnet.
However,
there
is
a
caveat
and
that
didn't
come
across.
L
Clearly
the
catch
is,
if
you
do
that,
then
the
MAC
addresses
needs
to
be
a
unique
across
all
the
subnets
which
poses
the
requirement.
Basically,
that
is
very
good
for
the
managed
series
that
the
operators
can
manage
their
MAC
addresses
so
for
those
pieces,
and
this
is
the
requirement
that
have
come
that
have
come
to
me
that
the
operators
saying
that
we
can
manage
or
see
is
we
can
make
sure
that
the
MAC
addresses
are
unique.
Can
you
solve
our
SQL
problem
and
this
solution
is
water?
Thank.
G
G
G
D
G
L
G
G
L
G
L
O
L
Starting
with
the
problem
statement
that,
as
we
know,
e
between
has
become
very
prevalent
solution
in
the
DC
Espeon
enterprise
network
and
for
DC
and
enterprise
application,
especially
when
we
talk
about
the
DC
interconnect
and
enter
PI.
Enterprise
connectivity
over
van
consumer
want
secure
connectivity
with
a
VPN.
When
you
have
that
connectivity
over
Internet.
L
What
are
the
requirements?
The
requirements
is
to
be
able
to
do
protection
of
the
tenants
layer,
2
and
layer,
3
data
and
control
traffic
by
IP
say
so.
Both
data
and
control
traffic
at
both
l2
and
l3
protection
of
unique
and
tenants,
unicast
and
multicast
data
traffic
using
BGP
to
do
point
to
multi-point
signaling
to
set
up
point-to-point
IPSec
si,
and
that
is
for
the
a
scaling
purposes,
because
if
we're
going
to
use
ID
for
a
call,
Ike
is
a
point-to-point,
then
basically
you're
gonna
need
in
terms
of
the
message.
L
Exchanges
is
ons
square,
whereas
when
you
use
BGP,
point-to-multipoint
signaling,
you
reduce
data
skill
too,
or
be
able
to
support
a
different
level
of
granola
teas,
which
I
get
to
the
next
slide
and
also
be
able
to
support
either
a
single
IPSec
policy
with
that
defi
Hellman
group
or
multiple
policies
with
multiple
development
groups.
Now
what
the
level
of
guarantees
do
we
want
to
support?
L
We
want
to
be
able
to
support
setting
of
an
IPSec
session,
say
among
the
key
Pease
to
for
aggregating
all
tenants
traffic,
so
basically
think
of
it
as
a
single
IPSec
si
between
a
pair
of
PE
and
that
tunnel
aggregates
all
the
traffic
from
all
the
tenants,
dance
mode
and
the
highest
level
of
guarantee,
then
you
go
to
the
next
level-
is
be
able
to
do
it
on
a
pair
tenant
basis
to
set
up
a
IPSec
tunnel
pertinent
and
if
the
PE
suffers
100
tenants.
That
means
you
need
to
set
up
hundred
such
tunnels.
L
Then
you
go
down
to
the
next
level
of
generality,
for
the
a
VPN
we
have,
this
notion
of
the
subnet
and
a
tenant
can
have
multiple
subnet,
multiple
VLANs,
so
be
able
to
do
IP
SEC
tunnel
on
a
per
subnet
basis,
and
you
can
go
down
the
list
that
okay
in
case
for
it
a
tenant,
has
some
workload
and
I
just
want
to
secure
connectivity
for
them
for
a
pair
of
workload.
I
need
to
be
able
to
do
that,
and
that
is
done
for
be
able
to
do
it
on
a
pair,
I.
L
L
L
And
when
a
PE
first
comes
up
and
wants
to
set
up
an
IPSec
si
between
itself
and
each
of
the
interested
remotely,
it
basically
generates
deafie
Hellman
pair
for
each
of
his
intended
IPSec
security
Association,
and
then
it
distributes
these
information
that
the
Hellman
public
value,
along
with
new
neurons
to
the
other
remotely
is
via
there
are.
Each
receiving
PE
then
uses
this
data
Hellman
public
number
and
corresponding
ones
in
creation
of
the
IPSec.
As
a
pair.
L
Just
quick
note
in
here
before
getting
into
a
bit
of
details
that
this
is,
there
is
a
framework
draft
that
goes
with
this
draft
and
that
framework
giraffe
is
called
controller
Ike
got
presented
in
the
last
ITF
and
at
the
security
working
group,
and
that
is
basically
sense
of
the
framework
that
of
how
to
when
you
have
a
controller,
how
you
can
leverage
that
controller
to
do
point
to
multi-point
signaling
and
one
of
the
main
area
that
is
covered
in
that
framework
draft
is
the
reaching.
If
you
need
to
do
the
routine.
L
It
covers
two
type
of
encapsulation
one
IPSec
end
cap
in
transport
mode
without
the
other
UDP
header
and
then
another
one,
each
other
UDP
header.
The
reason
for
these
for
the
these
two
type
of
encapsulation
is
when
you
do
IP
second
cap,
and
you
do
it
without
the
other
UDP
header,
then
the
question
is:
how
do
you
do
if
you
want
to
do
load
balancing?
Are
you
gonna?
Do
the
load
balancing
on
a
peripheral
basis,
because
your
entropy
was
used
to
mean
the
source
port,
which
is
no
longer
visible?
L
Okay,
so
this
is
the
end
cap
with
the
without
the
author,
UDP
header,
and
the
next
one
is
incomplete
UDP.
Both
of
these
end
caps
are
standards.
Okay
and
we
are
using
the
standard.
The
second
one
with
the
UDP
has
two
UDP
header,
and
that
can
be
up.
The
optimization
of
this
is
for
further
study,
and
this
is
the
molasses
line.
L
This
table
basically
covers
what
are
the
different
level
of
generality
for
what
VPN
solutions,
which
of
them
both
Roth.
We
need
to
send
for
each
level
of
granola,
tea
and
bit
of
which
level
of
guarantee
is
applicable
for
what
VPN
solution.
Some
of
them
are
not
applicable
like
a
pair
Mac,
their
IP
is
not
applicable
for
VPLS,
okay,.
R
R
Questions
but
this
one,
the
clarifying
question
so
here
you're
talking
about
between
keys
right
because
we
have
a
track
about
sd1-
is
really
about
the
CPE
and
also
the
zero
touch
provisioning
that
required
a
CPU
have
private
addresses
private
port.
So
do
you
see
this
similar?
Because
we
also
use
that
BGP
to
advertise
the
IP,
sag,
okay
properties,
plus
the
net
properties
as
well.
L
In
here,
but
this
is,
you
can
refer
it
as
a
customer,
PE,
okay,
si
PE,
I
think
Eric
in
his
draft.
He
refers
to
it
as
C
PE
I
didn't
wanted
to.
If
such
clarification
is
needed,
we
can
do
it,
but,
as
you
can
see,
these
are
the
basically
behaves
in
a
as
a
PE,
even
though
it
is
in
a
customer
admin
domain,
and
so
you
want
to
call
it
C
period.
That's
why
okay.
A
L
No,
no
actually,
the
Eric's
solution
is
completely
apple
and
orange
is
he's
talking
about.
The
only
similarity
is
the
term
C
V.
Everything
else
is
different
because,
because
he
is
this
and
they're
trying
to
solve
different
problem.
Okay,
this
is
trying
to
say
that
I
am
gonna,
be
using
the
BGP
and
how
I
am?
Are
you
gonna
be
using
the
BGP,
which
is
point-to-multipoint
signaling,
to
set
up
a
point-to-point
Association?
That's
the
gist
of
this
draft
that
is
not
address
in
our
external
okay.
A
L
T
Arcus
hub
we
there
is
a
separate
work
going
on
on
an
old
VPN,
at
least
for
l3
VPN
ipsec
RFC,
which
is
already
out
there,
which
needed
to
be
refreshed
as
part
of
as
part
of
tunneling
kept
strafes,
so
we're
working
on
it.
We
should
chat
offline
and
see
if
we
can
make
it
generic
you're,
making
this
on
a
tunnel
and
cap.
So
one
thing
to
actually
clarify
which
your
traffic
person
and
we
can
take
it
offline,
is
how
do
you
prevent
the
security
profile,
getting
leaked
out
of
interest
truly
option?
B
L
U
L
We
updated
it
last
year
with
the
bomb
procedure
jeffrey
help
with
that
section,
and
it
is
in
pretty
good
shape
right
now,
and
the
draft
is
basically,
in
a
nutshell,
is
optimizes
the
learning
in
leaf
nodes
of
a
data
center
AKA,
a
sports
so
currently
for
a
data
center.
A
given
leaf
nodes
needs
to
learn
all
the
MAC
and
IP
addresses
of
the
of
the
tenant
and/or
end
station
in
that
data
center.
What
this
solution
does
it
limits
it
to
that
node
only
so
this
solution
is
intended
to
ask
al
the
forwarding
tables.
L
L
In
we,
basically
in
order
to
identify
the
sources
port
in
local
bias,
local
bias
applies
to
IP.
So
if
you
bring
it
to
MPLS,
the
question
is:
how
do
you
identify
the
you
know?
What
mechanism
do
you
use
to
identify
the
source
PE
and
we
use
PE
distinguisher
label
and
in
this
roof?
In
addition
to
that,
we
added
one
more
mechanism
to
do
that,
and
that
is
basically
using
a.
L
V
So,
whatever
the
requirements
to
support
l2
access
protocols
in
European
networks,
for
example,
letting
legacy
data
centers,
which
are
running
this
long
list
of
STP
directed
derivatives
like
STP,
g80,
32,
mb,
l,
ftp,
MST,
AG,
and
so
on
into
an
EVP
n
core
network,
the
evpn
core
peas
are
generally
agnostic
of
what
the
what's
happening
in
the
access.
But
one
thing
is
certain
in
this.
V
In
these
use,
cases
is
that
these
european
peas
do
know
that
the
access
is
running,
an
l2
protocol
to
break
loops,
which
leads
us
to
the
the
actual
requirement
list
to
support
these
l2
access
networks.
The
solution
must
support,
must
do
optimal,
forwarding
at
l2
and
l3
and
support
any
caste
IRB,
while
providing
fast
convergence
and
scalability.
V
If
we
go
through
an
overview
of
the
existing
two
modes
of
load,
balancing
first
off
all
active
all
active
per
7432
creates
a
nice
EMP
at.
If
you
look
at
the
picture
on,
the
right
creates
a
nice
EMP
at
p3,
which,
in
in
this
topology
of
the
switches
a
to
a
to
2d
below,
would
create
a
nice
EMP
towards
the
wrong
p4,
some
of
the
traffic.
V
So
the
new
mode,
which
we've
coined
a
single
flow
active
what
this
mode
does
is
we
reuse
the
same,
so
we
create
a
peering
between
p1
and
p2
using
the
same
ESI.
So
all
the
Ethernet
segment
procedures
still
applies,
such
as
sync
and
mass
withdraw
procedures
to
implement
this.
We
have
an
extension
to
the
ESI
label,
BGP
extended
community
to
single
this
new
load
balancing
mode.
We
we
carved
up
the
flags
of
ESI
label
into
borrowing
three
bits
currently
bid:
zero
is
all
active
and
bit
one
is
single
active.
V
With
this
mode,
the
peering
PE
must
now
not
perform
the
split
horizon
filtering
to
allow
the
dl
to
access
protocols
to
communicate
VPD
use
in
some
of
in
some
of
the
access
protocol
cases,
and
so
more
importantly,
here
actually
is
the
parent
bees
have
to
enable
Mac
mobility
procedures
within
the
same
ESI
from
a
remote
PE
perspective
for
a
remote
PE
such
as
p3
here
and
facing
p1
p
in
the
same
ESI
in
single
flow.
Active
mode.
V
V
So
do
a
local
Mac
Mac
flush
based
on
this
TCN,
but
also
propagated
to
the
peering
PE
via
dedicated
pseudo
wire,
for
which
we've
actually
looked
at
EVP
and
PPOs,
which
is
quite
well
suited
for
this
on
the
untagged
interfaces
or
untagged,
AC,
sorry
and
then
basically
relay
this
TC
and
I
was
forwarded
on
the
EVP
MVP
WS
back
into
the
access
for
for
consumption
by
the
other,
the
other,
the
other
access
network
segment,
we've
also
considered
PE
3.
What
PE
3
should
do
with
the
the
TC
n?
V
G
G
Yeah
the
draft
was
originally
presented
in
ITF
99
last
year,
so
in
this
draft
we
are
adding
a
new
tunneling
cap.
A
VPN
already
support
multiple
kneecap,
so
we
are
adding
Geneva
as
one
of
the
tunneling
capita
VPN
and
Geneva
has
a
tunnel
in
cap.
It's
similar
to
be
excellent,
but
was,
as
a
capability
of
adding
options,
option
T
alien
carrying
as
well.
Definitely
our
two
protocols
other
than
Ethernet.
G
So
so
what
we
are
specifying
in
the
draft
is
a
way
to
communicate
in
control
plane
what
kind
of
options
are
going
to
be
included
with
the
genève
dominant
cap,
so
those
different
option
can
be
carried
with
in
data
plane.
Now
was
the
genève
tunnel
has
pair
the
control
plane
so
as
a
control
plane
as
well,
could
allow
the
pease
to
negotiate
what
kind
of
option
should
be
present
based
on
the
capability
of
HP,
accepting
the
reception
of
certain
option,
but
not
accepting
others,
for
example?
G
So
this
is
like
was
a
quick
background
or
history
on
the
draft.
You
know
new
tunnel
type.
A
VPN
tunnel
v
has
some
capability
related
to
options,
so
this
is
how
we
can
communicate
those
option
in
the
evpn
BGP
control
plane.
Since
the
drafters
original
draft
that
was
presented
last
year,
we
added
few
extension
here
or
couple
of
extension.
We
updated
more.
The
section
on
the
negotiation
of
those
options
that
can
be
carried
in
data
paths
was
a
genève
tunnel
and
as
well,
we
define
a
new
option
at
V.
G
We
called
it
Ethernet
option
T
le,
so
that
is
an
option.
T
and
V
allows
the
data
packet
to
carry
in
the
Geneva
tunnel
header
as
an
indication
that
the
traffic
is
Bond
traffic
and
as
well
Alif
indication
as
well
and,
furthermore,
an
option
source,
ID,
24-bit
source
IDs
that
canny
code,
an
ESI
label
for
split
horizon
procedure,
as
defined
by
RFC
7432,
so
I
think
yeah.
This
was
the
changes
mainly
to
the
draft
and
I
think.
We
believe
that
the
draft
is
ready
for
our
group
adoption,
so
so
we're
asking
shares
was
not.
T
Go
ahead:
Thank
You,
Caleb,
Patel,
arcus,
I
I've
got
through
the
draft
one
meta
comment:
I
have
was
the
same
one
for
ollie,
also
that
at
an
e
BGP
boundaries
when
the
next
hop
changes.
You
need
a
text
in
here
that
says
that
the
tunnel
encapsulation
cannot
be
carried
beyond
that
unless
and
until
it's
configurable,
because
if
you
signal
a
wrong
tunnel
and
kept
beyond
your
domain,
boundary
forwarding
may
not
be
able.
G
To
actually
work
agreed,
agreed,
I,
say
I
think
yeah.
Definitely
that
draft
is
limited
to
one
boundary
and
and
handling
you
know
different,
but
because
we
can
have
different.
He
kept
as
long
as
the
different
boundary,
MPLS
and
so
on.
So
so
that
will
be
addressed
not
advancing
could
address.
It
was
in
the
scope
of
the
draft,
but
we
are
seeking.
Maybe
another
draft
can
address
at
school
right
but
which.
G
T
A
T
D
T
U
N
A
A
W
I'm
Patrice
reset
Cisco
I'm
here
to
present
you
the
EBP
and
it's
a
home,
a
productive
load-balancing,
so
we
already
talked
about
few
of
them
today.
I
think
it's
just
one
more
so
we
have
all
active.
We
have
single
active.
We
are
a
single
flow
active
and
now
it's
protected,
so
we
keep
adding
alright.
So
this
is
very
simple.
W
Basically,
what
we
want
to
do
is
with
a
VPN.
We
call
it
also
many
people
card
EB
tag.
We
support
multihoming.
We
want
to
make
sure
that
we
can
almost
I
cover
all
the
legacy
technologies,
so
in
that
pass
we're
doing
an
MC
lag
with
ICCP
veins
and
by
I
was
willingly
all
hours
on
this
and
we
actually
we
made
it.
W
W
So
therefore,
we
came
out
with
the
ICO
standby
concept
for
the
what
we
call
also
for
port
load
balancing.
So
it's
very
simple.
So
we
are
doing
the
same
thing
pretty
much
as
before,
but
we
make
it
a
bit
more
simpler
with
ICCP.
There
was
a
lot
of
negotiation
to
make
sure
we
can
bring
the
bundle
alive
on
one
side
and
stand
by
on
the
other
side.
So
now
what
we
are
saying
is:
let's
configure
it
kind
of
manually
on
both
sides
make
sure
that
all
the
the
SI
system-
ID
port
priority
and
so
on.
W
W
W
All
right,
that's
the
my
longest
presentation
at
IDF.
Look
at
that!
So
if
you
can
yang
one
side,
so
we
updated
v-0,
six
I
know
this
comments
from
you
to
be
answer
as
we
discuss
at
the
beginning
and
from
Sasha
as
well.
So
we'll
do
this
and
we'll
update
it
as
fast
as
we
can.
So
we
can
go
to
that
call
comments.
Question.
X
Good
of
everyone,
my
name
is
Cheng
I
represent
this
topic.
It's
about
yamete,
the
motor
for
VPN
service
performance
monitoring.
So
this
actually
is
a
new
chapter.
We
was
any
way
we
are
posted
in
s.
Working
group
motivation.
We
write.
This
chapter
is
right.
Now
we
have
found
children,
no
performance,
Mercer
protocol
that
had
been
proposed
for
Eastern
and
traffic,
RP
traffic
and
NGOs
traffic,
such
as
Peter
figure.
We
have
21
protocol
and
we
also
have
a
ponchos.
A
performance
metric
has
to
be
proposed
for
delay
and
packet
loss
and
achiever
and
MPL
traffic.
D
X
The
right
now
all
of
these
programs
may
mean
actually,
we
used
actually
an
online
network,
but
how
we
can
expose
these
performance
measurement
results
to
the
own
to
the
overlay
to
the
operate
or
customer.
Allow
the
operator
to
Rio
Oh
real
optimism
met
worker,
that's
something
we
really
want
to
go
for.
We
think
we
haven't
seen
any
worker
to
discuss
these
so
typical
use
cases.
The
way
it
is
clear.
X
Actually,
for
example,
we
want
to
set
up
a
when
we
can
service
with
three
site,
so
from
customer
perspective
or
from
operator
perspective,
they
don't
have
our.
What
is
underlying
technology
you
are
using,
but
what
was
he
care
about?
Is
the
freedom
for
when
we
delay
between
the
site
or
packet
loss
within
the
site,
so
we
can
actually
settle
the
sauce
in
the
online
network.
We
can
actually
export
these
kind
of
performance
may
resolve
the
to
the
overlay,
and
when
this
is
possible,
actually
service
provider
can
use
these.
X
D
X
D
X
So
in
this
way,
actually
we
can
establish
the
link
or
relationship
between
over
a
and
Andre.
So
here
we
can
example
about
the
ratio
between
ovary
and
Andre.
Actually,
you
can
map
the
site
information
in
over
the
into
the
underlying
the
network,
like
the
node
in
the
network
device
in
underlying
network,
so.
X
You
are
interesting
and
and
allow
the
network
device
or
management
system
to
to
publish
it
is
work,
allows
it
to
to
the
to
the
to
to
the
overly
allows
operator
to
to
basis
based
kind
of
results
to
reorganize
the
network.
In
addition,
we
can
allow
the
custom
actually
can
do
some
query
using
some
RPC
model
to
do
that.
