►
From YouTube: IETF103-HRPC-20181105-0900
Description
HRPC meeting session at IETF103
2018/11/05 0900
https://datatracker.ietf.org/meeting/103/proceedings/
A
I'm
sure
more
people
will
be
coming
in,
but
but
we
hit
the
time
and
we
have
a
fairly
full
agenda.
So
this
is
the
human
rights
protocol
considerations,
research
group
chartered
by
the
IRT
F
to
research,
how
protocols,
strengthen
and
or
threaten
human
rights,
as
defined
in
the
Universal
Declaration
of
Human
Rights
and
the
International
Covenant
or
Civil
and
Political
Rights,
okay.
So
the
agenda-
and
this
is
the
agenda-
Bash's,
welcome
and
introduction,
then,
as
talked
by
art,
Thai,
citizen
Network,
then
there's
a
talk
by
Ashwin.
B
A
You
to
talk,
then
there's
an
update
from
the
hackathon,
an
update
from
the
Human
Rights
review
team
research
group
drafts,
there's
three
of
them
that
will
go
going
through
then,
there's
update
and
discussions
on
drafts
yet
to
be
adopted
by
the
the
research
group
and
that's
got
five
minutes.
Is
one
draft
in
that
one
moment.
I
believe
then,
there's
an
open
discussion
which
is
focused
on
sort
of
what
is
our
next
task?
A
Where
are
we
going
and
and
some
of
the
questions
that
have
come
up
over
over
the
months
about
what
is
this
group
doing
and
and
where
is
it
going
and
then
any
other
business?
If
we
still
have
time
for
it?
Are
there
any
issues
with
this
agenda?
Any
additions
changes
things
that
are
wrong.
No
good,
then
I
guess
we'll
go
with
that.
One!
Okay,
the
note
well
is
here.
This
is
probably
the
first
meeting
of
the
week
with
the
note.
A
Well,
you'll
see
it
often
this
is
the
ietf
note
will,
but
it
applies
to
the
IRT
F
as
well,
and
what's
really
important
are
all
the
definitive
information
in
the
documents
that
are
listed
in
that
list.
I
will
not
read
them,
okay,
so
the
objectives
to
expose
the
relation
between
protocols
and
human
rights,
with
a
focus
on
the
rights
to
freedom
of
expression
and
freedom
of
assembly,
but
you'll
notice
that
we
do
go
broader,
and
that
was
partly
because
people
said.
A
Our
outputs
internet
drafts
policy
and
academic
papers,
of
which
we
have
done
very
few,
and
one
of
the
things
that
I
want
to
talk
about
at
the
end,
is
how
do
we
get
more
involved
in
that
film
and
textual
interviews?
There
was
the
film
that
was
produced
at
the
beginning
of
this,
which
is
still
available
on
the
website,
data
analysis
and
visualization
and
protocol
analysis
of
existing
protocol.
A
So
we've
have
a
fairly
wide
scope
of
work
that
that
we
can
do
some
of
which
we're
paying
more
attention
to
than
the
others
at
the
moment.
The
work
to
date,
yeah
October
14
through
15
research
and
research
group
proposal
in
15
there
was
the
screening
of
the
film
net
of
Rights
at
ITF
94
December
2015.
A
We
were
chartered
2017
80
to
80
research
and
human
rights.
Protocol
considerations
was
came
out.
Current
work.
We
have
internet
drafts
that
our
research
group
drafts
there
is
freedom
of
association
on
the
internet,
there's
guidelines
for
Human,
Rights
protocol
considerations,
there's
notes
on
networking
standards
and
politics
and
there's
an
expired
anonymity,
Human,
Rights
and
internet
protocols
and
there's
the
work
of
the
Human
Rights
review
team,
and
that's
it
for
this
one.
So
that
brings
us
to
our
first
speaker
correct
and
our
first
speakers,
art
and
freedom
of
assembly
and
Association
online
art.
A
You've
got
a
microphone
up.
There.
You've
got
a
clicker
place
to
put
your
stuff
down.
Make
yourself
at
home,
and
I
will
start
passing
out
the
sheets.
Now
that
I've
done
the
original
talking
and
the
room
is
full.
Will
fuller
you'll
go
ahead
yeah
this
microphone?
Is
yours?
Oh
wait.
A
second
before
you
start
I
forgot,
I
forgot,
I
need
a
ascribe
and
I
need
a
jabber
scribe
and
I
forgot
to
do
those.
A
C
Hi
everybody-
this
is
my
IETF
meeting
so
anyway
welcome
to
Bangkok.
Well,
this
is
my
hometown,
so
that's
the
whole
thing
I
very
confidence
about
to
moment.
Anyway,
let's
see
how
it
goes
right,
our
trying
to
basically
I'm,
not
a
network,
engineer
I'm,
although
I'm
graduated
in
like
designs,
I
worry
wherever
but
network
engineering.
It's
not
my
turf
right.
I'm
completely,
have
no
corporate
so
like.
C
Let's
have
some
discussion
after
this
way,
but
this
is
the
thing
that
I'm
doing
at
the
moment
and
work
for
an
NGO
or
base
in
Bangkok
or
working
on
digital
rights
right
specifically
or
more
on
the
data,
protection,
privacy
or
lie,
and
also
freedom
of
expression
right
so
and
actually
like
a
lot
of
materials
here.
Actually,
like
borrow
from
my
different
people,
article
19
included
a
PC
whatever
right,
but
let's
see
right
how
how
we
can
link
this
like
to
cater
so
maybe
first
things,
first
right
or
maybe
I.
C
Well,
our
so
we're
going
to
talking
about
like
to
kind
of
rise
right
to
have
freedom
here
right.
The
first
one
is
about
that
smv
right,
the
rights
to
be
able
to
just
like
an
educator
I
demonstrations
like
walking
on
the
street
public
spaces
inside
that
right.
So
that's
one
thing
to
smb1
right.
Another
one
is
association
right,
for
example,
like
a
forming
a
political
party
forming
a
trade
union,
labor
union
or
inside
your
workplace
right,
or
this
different
kind
of,
like
probably
a
national
or
local
regional
context
as
well
right.
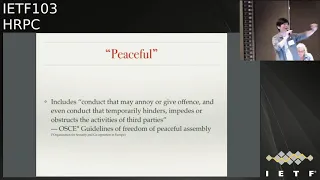
C
So
so
what
it's
actually
a
peaceful
like.
Oh
there's
many
interpretation,
rather
you
later
basically
right,
but
we're
talking
about
like
the
freedom
of
assembly
and
Association
right,
we're
talking
about
it
happens
in
a
space
right
where,
where
the
space
is
so
the
same
thinking
like
I
mean
shootable,
also
like
extended
to
the
online
spaces
as
well.
If
you
ask
me
I
answer
like
yes
right.
If
you
are
other
people,
I'm,
not
sure
well,
but
that's
that's.
C
The
kind
of
base
like
you're
right
that,
at
least
for
our
follower
of
groups
I,
would
think
that,
like
okay,
any
or
human
rights
that
or
we
enjoy
offline
should
also
like
the
same
extended
to
all
I
espero
right.
So
when
we
tal
a
peaceful
right,
what's
actually
keys
for
or
there's
one
interpretation,
let's
say
la
or
suggestion
like
are
in
the
guidelines
from
the
organization.
There's
a
lot
of
acronyms
here
right
but
but
but
I
mean
like
this
is
IETF
anyway
right
so
acronyms.
C
Because
of
the
fact
that,
like
someone
is
actually
I,
mean
there's
a
lot
of
people
in
front
of
like
some
buildings
or
on
the
street,
or
they
cannot
go
for
somewhere
or
in
the
city
easily
or
on
that
day,
but
but
that
still
like
peaceful
anyway
right
how
we
can
go
into
actually
like
interpreted
into
or
like
on
Texas
spill
right
should
lie.
I,
don't
know
like
if
I
actually
are,
if
I'm,
an
organizer
of
saving
all
I
campaign.
C
If
I
ask
like
people
who,
maybe
like
not
really
happy
with
some
bills
or
if
example,
right
or
two,
we
see
a
government
website
right,
a
lot
of
people
right
or
at
the
same
time
to
deploy
that
or
probably
the
regular
visitor
or
that
services
proper
cannot
Lily
use
the
service
or
the
service
they
are
going
to
be
very
slow.
We
would
that
be
stable,
like
a
peaceful
assembly
or
line
or
not
right.
I
know,
anyway
right.
C
So
you
talk
about
peace,
pool
right,
we're
talking
about
the
spaces,
we're
talking
about
activities
right,
but
as
or
in
any
kind
of
like
international
treaties
by
of
convention,
they're
always
limitations.
So
this
one
is
from
ICCPR
right,
international
or
continent
on
Civil
and
Political
Rights
right
so
in
article
twenty
first
and
two
in
the
second,
they
say
that,
okay,
that
should
there
can
be
right.
C
There
can
be
some
limitations
right,
but
those
limitations
should
be
provided
by
the
law
right
and
those
I
mean
there
should
be
some
Jose
like
really
really
really
legitimate
reasons
right
like,
for
example
like
this
is
like
very
common
right:
national
security,
public
order,
and
the
last
thing
is
like
the
protection
of
auto
rights,
which
is
like
it's
actually
open
to
a
lot
of
interpretation
in
some
countries.
This
authorize
will
also
include
like
well
copyright
infringement
or
like
pornography,
all
right
which,
like
to
order
people
interpretation.
C
This
color
debatable
right,
whether
like
pornography
or
copyright,
infringement
should
be
also
included
here
or
not
right
to
between
someone
to
enjoy
the
freedom
of
assembly
or
Association
to
dimension
right
off
SMB
right,
we're
talking
about
people
like
gathering
on
the
street
right
demonstration
or
lie
or
fly
right,
but
before
they
can
actually
do
that
like
there
should
be
some
plan
or
canine
organization
of
that
first
way.
So
when
you
talk
about
freedom
assembly,
we
at
least
very
talk
about
these
two
dimensions
right.
C
The
first
one
is
like
actually
before
there's
a
big
could
actually
take
place
right.
There
should
be
some
communication
planning
right,
organizing
something.
Okay.
Are
we
going
to
meet
here
and
there
are
at
these
players
how
many
people
or
how,
how
many
like
toilets.
We
actually
need
two
people
or
actually
have
some
like
a
special
needs
or
not
right,
so
they.
Actually
there
are
some
organizations
right
before
us.
We
can
actually
take
places
right.
C
So
that's
the
first
thing
like
people
should
or
have
to
rise,
so
actually
organize
the
plan
simply
right,
and
the
second
dimension
is
that
assembly
itself
right
and
these
two
apply
with
it's
like
online/offline.
Some
of
the
assembly
right
can
actually
organize
online
and
the
decibel
it
selves
actually
happens.
Offline
or
I
can
go
vice
versa
as
well.
I
can
actually
meet
someone
here
right,
offline
and
talking
about
well,
probably
at
next
week.
C
We
should
like
gather
together
or
maybe
on
the
Twitter
and
your
try
to
use
the
same
hash
hash
tag
for
the
whole
week
right,
so
we
actually
planned
it
offline
for
the
action
that
going
to
happen
online
right.
So
it's
actually
like.
Oh
there's,
there's
no
clear
border
here
right
or
the
same
freedom.
Rice.
Here's
actually
like
you,
can
ink
and
let's
keep
jumping
from
one
space
to
all
the
space.
C
C
There
are
these
two
things
that
we
can
thinking
about
like
here
right.
It's
like
we're,
talking
bloody
the
associations,
like
all
category
of
associations,
that
already
existing
right
or
off
fly
right
because
there's
a
whole
like
communication,
electric
communication
right.
It
can
help
further
write
this
association
to
reach
out
like
more
members
or
have
like
more
activities
like
Oh
make.
It
lay
more
effectively
basically
right,
but
they
also
set
a
second
kind
of
thing
here.
So
it's
late.
C
So
this
is
why
a
lot
of
people
think
that's
where
actually
this
is
they
actually
are
very
crucial,
really
important
or
why
we
should
also
have
the
free
association
in
the
online
spaces
as
well.
We're
talking
about
to
write
or
feed
freedom
so
far,
right
or
freedom,
assembly
and
also
freedom
of
association.
C
How
this
actually
links
right
to
authorize
right
before
these
right
are
in
the
opening
we'd
be
talking
with
the
IFC
they're
talking
about
the
privacy
considerations
right
in
the
high
of
the
Internet
Protocol
right,
so
how
that's
actually
going
to
help
right
the
freedom
of
association
or
assembly
right?
So,
let's
see.
C
I'm
actually,
like
I,
mean
tiny.
The
Senate
work
right,
the
group
that
I'm
working
for
actually,
we
started
first
to
fight
basically
against
censorship.
Like
all
eyes,
it's
a
ship
right.
So
that's
the
freedom
expression
right.
That's
the
first
thing
that
we
working
for
for
like
I,
don't
know
nine
years
me
that,
but
so,
if
maybe
this
is
like
one
of
the
first
thing
that
people
can
think
about
it.
Like
yeah
well,
I
mean
to
be
able
I
mean
when
we
talking
about
freedom
of
assembly
and
Association.
It
is
because
something
are.
C
We
have
something
to
say
basically
like
where
it
is
all
going
to
be
on
the
street,
like
we
have
in
our
demonstration
right,
enjoy
the
freedom
ISM
absently,
because
we
want
to
express
something
like
oh
and
let
the
public
knows
about
that
right
or
we
can
express
that
in
the
form
of
Association
right.
We
form
a
group
right
and
then
we
submit
our
letters
or
recommendations
whatever
I
true,
some
like
a
little
bit
more
formal
or
mechanism
right,
but
this
is
basically
to
enjoy
also
like
our
freedom
of
expression.
C
So
that's
calico,
the
the
first
linkage
they've
been
thinking
about
like
how
freedom
expression
and
freedom
of
assembly
and
Association
links
together,
but
before
we
can
actually
have
some
messages
to
actually
to
express
to
say
something
out
loud
out
there
right.
Maybe
you
have
to
actually
a
little
bit
like
or
take
speck
back
and
think
through
right,
discuss
with
our
friends.
Colleagues
right.
Why
are
we
going
to
say
something
like
that
or
what
is
the
the
goal
of
saying
so
like?
What's
our
aim
of
the
demonstration,
for
example
right
so
before
the
expression?
C
Sometimes
right
actually
need
a
require
as
well
right
to
freedom
of
association,
so
we
can
actually
formally
like
the
expression
inside
that
maybe
the
last
one
is
like
about
the
rights
of
privacy
right.
It's
calico
because,
like
I
was
talking
about
this
layer
also
as
well
or
in
the
next
slide
things
like.
So
basically,
it's
like
to
realize,
where
I
or
these
two
freedom
right
is
in
the
association
right.
Some.
C
Right
or
privacy
right,
oh,
it's
a
key
as
well.
Why
why
right
I
mean
like
basically
like
we're
talking
like
online
spaces
right
or
we
are
the
freedom
to
actually
the
rights
to
actually
organize
and
plan,
something
right
and
actually
actually
taking
place
in
some
spaces
right
or
when
you
plan
something
right.
C
It
means
secure
communication
channels
right
and
when
you're
going
to
or
make
the
assembly
today,
most
recently
or
to
taking
place,
you
need
some
spaces
right,
I
mean
I,
cannot
actually
do
a
demonstration
right
without
space
to
stand
on
right,
I
mean
I,
have
a
speech.
Physical
self
example
right.
So
there's
some,
if
that's
the
demonstration
in
the
physical
space
right
that
there
should
be
well
physical
space
to
do
chemistry
anyway,
and
this
is
also
applied
in
the
online
spaces
as
well
right.
C
So
basically,
we
need,
like
I,
mean
to
enjoy
freedom,
assembly
revenue
and
secret
communication.
We
need
safe
and
publicly
accessible
space
right,
and
this
doesn't
need
necessary
to
be
publicly
owned.
Space
right,
for
example,
in
the
case
of
the
physical
orally,
occurs
right
demonstration
that
back
then
we
or
if
you
still
remember
that
Occupy
Wall
Street,
is
thankfully
taking
players
in
the
pirate
Lea
own
public
spaces
right.
So
when
we
talking
about
publicly
accessible
space,
it
doesn't
necessary
to
be
a
publicly
owned
or
SPSS.
C
It
can
be
like
or
privately
owned
right,
but
basically
are
the,
but
they
should
be
able
to
get
access
to
it
right
freely
and
also
to
enjoy,
through
my
association,
right,
I,
think
well-well
to
form
something
right.
You
need
someone
who
actually
like
mine,
you
can
actually
like
Kylie
lien
or
you
sell
flyer
on
them
like
sometimes
as
well
like
you
need
trust
way,
and
sometimes
right
or
in
the
situations.
They
say
it's
actually
maybe
less
sensitive
right
as
mentioned
earlier
in
some
countries,
some
political
ideologies
or
religious
belief
can
be
very
dangerous
right.
C
So
maybe
you
need
a
little
anonymity
as
well
right
to
be
able
to
form
some
clubs
or
associations
right
for
that
sensitive
matters
or
believe
right.
So
here
come
the
telecom
insurance
that
can
actually
go
against
all
these
right.
So
we're
talking
about
like
a
freedom,
assembly
right
or
governments
actually
or
sometimes
also
like
corporate
as
well,
that
has
enough
power
or
do
this
stuff
right
filtering
blocking.
This
is
kinda
common
practices
right,
but
also
like
the
distributed
denial
of
service
attack
as
well
right
to
bring
some
website
down.
C
So
in
terms,
let
me
freedom,
assembly
or
same
things
like
go
as
well
right,
I
mean
or
actually
Lily
attack
like
technical
measures
like
surveillance
and
profiling,
also
effects
or
confidentiality
right,
which
are
limits,
privacy
or
create
some
fear
among
people.
Widow
I
not
really
sure
whether
I
can
actually
trust
you
or
not,
actually,
the
one
that
actually
claim
that
you
are
or
whether,
like
the
informations
like
out,
there's
actually
can
be
trust
or
not
and
said
that
so
these
can
are
effects
right.
C
C
Apart
from
the
documentation
on
of
the
on
the
offline
assembly,
an
association
right
or
in
the
recent
years,
actually
more
submission
on
the
violations
of
his
club
things
online
as
well
right-
and
she
has
come
like
how
I
know
like
this-
this
company
right
and
orders
right,
I'm
trying
to
think
like
before
this.
We
already
mentioned
this
right,
but
they
are
also
order
like
atoms
as
well
right
from
from
this
community
right.
So
apart
from
the
privacy
consideration
right,
this
is
also
the
development
further
on
that
light,
so
I
mean
monitoring
rights.
C
Actually,
the
thing
that,
as
an
engineer
to
my
understanding
life,
people
actually
have
to
do
like
you
know
more
basis
anyway,
right
to
do
evaluation
to
taste
to
actually
improve
the
status
and
our
ability
and
and
the
quality
of
service
right
of
the
network
right,
but
pervasive
monitoring,
it's
different
right.
So
these
are
RFC
I
like
seven,
two
or
five
of
58
right.
What
they're
trying
to
do
is
like
this
is
from
from
the
abstract
right.
C
C
He's
one
related
to
like
getting
back
to
that.
The
freedom
of
association
right
when
we're
talking
about
is
a
like
previously
that
the
civil
ends
right
or
profiling
right.
We
will
create
atmosphere
of
fear
right
and
it
can
limits
our
freedom
like
the
people.
How
do
people
enjoy
the
freedom
association,
these
prophesied
money
drinks?
Basically,
the
surveillance
right,
including
of
in
a
spell
right
and
here
here
goes-
lay
order,
IFC,
so
I
think
I
just
like.
C
Right,
over-the-top
content
providers
idioms
inside
that
right,
which
lie
or
actively
labor
was
a
different
player,
is
probably
or
they
have
different
data
that
they
actually
handle
or
like
or
different
power
right.
They
can
actually
do
or
so
that's
all
for
me
at
the
moment
and
getting
back
to
this
thanks
a
lot.
Thank.
F
Please
remember
to
give
your
name
thanks:
Jonathan
Highland
brought
all
the
way
so
I've
been
reading.
Quite
a
lot
of
research
about
this
at
the
moment
and
apparently,
a
more
common
technique
than
fear
would
be
what
stem
to
flooding
and
so
providing
lots
of
alternative
content
to
prevent
people
being
able
to
find
the
appropriate
content
and
I
feel
like
you
need
some
extra
right
in
your
list,
because
you
could
respect
all
of
the
rights
you
late
yo're.
F
C
That
that
one
will
go
to
the
maybe
platform
provider,
level,
right
and
I
think
in
the
I'm,
not
sure
where,
where
because
in
the
end,
I
think
that
the
package
is
shockingly
is
smaller,
but
the
the
content
flapping
right.
So
probably
it's
like
Oh
both
or
this
layer
of
network,
so
I'm,
not
sure,
but
I
mean
like
oh
okay.
This
is
like
another
discussion
right.
Oh
I
used
to
have
a
communication
with
people
from
YouTube
inside
that
right
they
say
like
this.
C
It
is
actually
like
a
problem
not
or
not,
not
necessarily
because
of
they
actually
like
on
human
rights.
Whatever
right
I
mean
they,
they
actually
do
like
they're
they're
more.
They
have
actually
more
interests
of
their
life
because
of
that
it
will
decrease
the
quality
of
service
of
their
own
platform,
where
people
will
things
all
is
like
the
same
repetitive
content
again,
so
it's
boring
inside
that
right,
so
they're,
trying
to
like
find
somewhere
to
actually
solve
the
issue
as
well,
but
probably
it's
like
or
at
the
different
level,
but.
C
Maybe
I'm
sure
that's
the
stinks
thanks
a
lot
well.
In
addition
to
did
I
think
like
it's
very
interesting
that,
like
a
year
ago,
we
fight
we're
not
sure
that
they
actually
intentionally
do
this
or
not
like
we
found
inside,
at
least
in
Thailand
in
few
other
countries,
when
there
is
a
demonstration,
the
policemen's.
Actually
not.
Let
me
show
it
intentionally
or
not.
Okay,
let's
say,
but
they
do
this
like
that
it
is.
They
actually
open
the
music
worried
out
loud
right
and
this
music
is
actually
copyright
him.
C
So
once
so,
people
try
to
actually
do
life
on
their
Facebook
or
YouTube
or
whatever
right,
so
the
police
actually
like
open
this
copyrighted
music
allowed
right
and
the
algorithm
inside
Facebook
and
YouTube
detect
it
and
bring
the
clip
their
life
down.
We
don't
have
an
evidence
whether
they
actually
intentionally
do
this
or
not
that's
more
than
ho,
like
befoul
right
lately,
interesting.
G
Yeah,
so
just
to
sort
of
follow
up
on
what
the
gentleman
just
said.
This
is
actually
a
theme
that
I've
been
noticing
as
I've
been
reading
the
current
documents.
They
seem
to
really
be
talking
about
the
world
as
if
it
were
I,
don't
know,
1970
and
they're,
not
really
talking
about
all
the
various
ways
that
you
can
attack
and
suppress
human
rights
using
the
internet
that
are
not
possible
elsewhere,
and
so
it's
more
so.
G
That
can
be
done,
and
this
is
very
concerning
to
me,
because
you
know,
if
you
look
at
what's
actually
going
on
on
the
Internet
as
opposed
to
you
know,
what's
being
written
in
the
drafts
most
of
the
issues
that
we're
having
are
more
along
the
lines
of
what
we
were
just
talking
about,
like
the
attack
that
you
just
described,
which
I
think
we
can
very
clearly
say
is
an
attack,
whether
it's
intentional
or
not.
It's
brilliant
right.
You
you're
using
the
content.
G
Where
the
problem
lies,
the
problem
doesn't
lie
in
I
mean
yes,
of
course,
you
know
we
can
it's,
we
can
put
up
firewalls,
you
know,
they're,
like
the
Great
Firewall
of
China
is
an
example
of
censorship
right,
but
but
these
are
relatively
trivial
in
comparison
to
some
of
the
other
attacks
that
we've
seen
and
I.
Think
that,
if
we're
not
seriously
talking
about
those
other
attacks
than
then
we're
really
not
going
to
accomplish
a
whole
lot,
thanks.
A
Just
a
quick
comment
on
that
one
that
seems
to
also,
though,
be
one
of
the
the
problems
that
we're
getting
into
on
the
list,
sometimes
is
where
we
talking
about
how
some
application
is
used
versus.
Where
are
we
talking
about
what
a
protocol
enables
or
disallows
and
and
sort
of
cutting
that
line
there?
It
has
been
sort
of
a
difficulty,
but
thanks,
please.
H
Nalini
elegans
I
really
want
to
agree
a
lot
with
what
Ted
is
saying.
One
of
the
real
problems
I
think
we
have
is,
you
know,
there's
so
many
new
things
that
are
possible
and
so
many
new
things
that
are
going
to
happen
with
the
capabilities
that
we
have.
That
I
think
we
really
need
to
be
thinking
and
talking
about
what's
going
to
hit
us
in
the
future,
not
just
what
has
happened
in
the
past.
G
Thanks
Ted
lemon
again
so
I
think
we're
possibly
using
this
as
an
excuse
to
have
a
discussion.
That's
not
quite
on
the
topic
of
the
talk
that
we
just
heard
so
I
apologize
for
that,
but
to
just
speak
to
to
Aubree's
point
the
the
problem
that
we
have
is
yeah,
that
the
difference
between
an
application
of
protocol
is
relevant
here,
but
I
think
that
we
can
learn
a
lot
by
looking
at
the
applications.
Even
if
we're
not
you
know,
of
course,
if
we're
writing
protocol
considerations,
then
we
can't.
G
We
can't
tell
you
how
to
write
your
application,
but
we
can
think
about
how
the
protocol
implicated
or
how
the
how
the
the
functioning
of
the
application
was
affected
by
the
protocol
that
was
running.
We
can
learn
a
lot
from
these
protocols.
So,
for
example,
if
you
look
at
SMTP,
if
you
look
at
the
things
that
are
implemented
on
top
of
SMTP,
there
are
some
pretty
clear
abuses
that
we've
seen
that
actually
are
part
of
the
protocol.
G
Like
they're
there
they're
there
second-order
effects
of
the
way
that
the
protocol
is
structured
if
the
protocol
had
been
structured
quite
differently.
Many
of
the
negative
behaviors
that
we
see
occurring
as
a
result
of
applications
of
SMTP
wouldn't
even
be
possible.
So
it's
something
to
think
about
is
that
the
theme
that
I've
been
seeing
as
I've
been
reading
these
documents
is
that
they
really
don't
seem
to
be
rooted
in
problems.
G
How
those
were
made
possible
by
the
way
we
designed
the
network
and
by
the
way
we
designed
our
protocols,
then
then
we
can.
We
can
come
up
with
a
taxonomy,
that's
rooted
in
actual
experience,
rather
than
one
that's
rooted
in
you
know,
papers
of
people
you
know,
like
I
mean
somebody
was
referencing
Heidegger
in
one
of
the
one
of
the
documents
it
actually
was.
A
very
topical
I
mean
it
was
actually
a
really
good
reference,
but
but
we
need
stuff
that's
about
what
we're
doing
now,
not
about
dams,
on
rivers,
Thanks.
A
I
Right,
Jordan,
just
a
quick
comment
on
the
attack
surface,
the
things
to
think
about
I
think
we
and
the
IETF
have
done
a
great
job
recently
or
over
the
past
five
10
years
of
starting
to
make
it
so
passive
surveillance
is
not
possible
and
to
protect
people,
sessions
and
and
integrity
of
their
sessions.
But
one
of
the
concerns
I
have
is:
are
we
basically
guaranteeing
that
people
will
be
able
to
be
identified?
You
know
because
they're
session
is
completely.
You
know
non-modified
between
two
points.
So
are
you
basically
guaranteeing
that
people
can
be
traced?
A
C
So
far,
right,
Ali's
life
from
the
outside
your
perspective
would
say,
but
I
think
one
of
the
problem
here,
a
lot
of
people
he
already
realizes
like
there's
a
lot
of
technical
assumption,
also
like
societal
assumption
right
that
we
use
right
to
decide
is
protocols
right
and
it's
probably
those
assumption
is
like
from
twenty
forty
years
ago,
and
it's
no
longer
hold
true
right,
so
I
think
that's
that's
the
way
forward
that
light.
Yeah
thanks.
Thank.
A
A
A
J
B
J
Although
I
will
try
and
make
those
connections,
I
used
to
be
a
technologist
when
I
went
to
school
and
became
a
social
scientist
so
now,
I
pretend
that
being
both
I'm
currently
with
the
Center
for
long-term
cyber
security
at
UC
Berkeley,
where
my
current
work
is
looking
at
the
role
of
trust
and
cooperation,
learning
an
information
security
I'm
also
attached
a
packet
Clearinghouse,
which
some
of
you
may
know.
But
what
I'll
be
talking
about
today
is
some
of
my
earlier
work.
J
Looking
at
one
Internet
Protocol
in
particular
the
border
gateway
protocol
and
looking
at
the
role
of
trust
in
the
border
gateway
protocol
and
what
I'll
do
in
my
talk
today
is
walk
you
through
some
of
that
research
and
try
and
generalize
it
in
a
way
that
I
hope
will
be
more
broadly
applicable.
Thinking
about
the
role
of
trust
in
protocol
design
next
slide,
please.
J
The
subject
of
all
of
you
are
dealing
with
is
how
we
connect
the
infrastructures
of
the
world
Internet,
in
particular,
to
questions
of
the
social
to
questions
of
Rights,
and
it's
going
from
as
obvious,
because
at
the
micro
talking
work,
the
concrete
threats
in
the
world,
how
do
you
actually
connect
them
to
particular
articulations
of
protocol
standards?
No,
it's
a
relationship!
That's
long
been
discussed
in
some
the
social
science
literature
on
on
infrastructure
and
our
reference,
some
that
as
I
go
along
next
slide.
Please.
J
So
my
stories
are
where
the
border
gateway
protocol
and
one
of
the
more
visible
route
hijacks
in
the
protocol,
which
of
which
there
are
many.
But
this
was
one
that
got
a
lot
of
attention
at
the
time,
which
was
when
Pakistan,
briefly,
hijacked
YouTube,
and
this
was
because
now
connecting
to
a
rights
issue
where
the
Government
of
Pakistan
issued
an
order
to
the
Box
on
internet
exchange
and
to
networks
within
Pakistan
to
block
a
particular
video
on
YouTube,
claiming
it
was
blasphemous.
J
The
way
that
the
Box
on
internet
exchange
chose
to
implement
that
block,
as
some
of
you
may
know,
was
to
announce
Dan
you're,
better
off
to
youtube
than
Google
intended
to
do
it
only
within
Pakistan.
But
it's
room
is
configuration
that
announcement
spread
to
their
upstream
networks
into
the
rest
of
the
Internet
and
so
for
about
two
and
a
half
hours
back
in
2008.
The
internet
thought
that
YouTube
wasn't
Pakistan,
and
this
very
much
set
me
on
on
my
thoughts,
my
research,
which
was
to
ask
the
question.
J
Well,
if
Pakistan
can
hijack
YouTube
so
trivially,
why
is
it
that
the
internet
is
stable
at
all?
Why
is
it
that
the
border
gateway
protocol
BGP
is
stable
and
it's
an
interesting
moment
to
look
at
this
because
in
many
ways
again
as
some,
because
the
my
colleague
were
pointing
out,
we
understand
infrastructures.
J
We
understand
rights
at
moments
of
breakdown
and,
at
this
moment
of
breakdown
connected
to
a
moment
of
a
breakdown
of
Rights
as
much
as
a
breakdown
of
the
infrastructure,
we
can
start
to
connect
some
of
the
technical
affordances
in
bgp,
with
some
of
the
expressions
of
control
being
it's
over
it
in
the
way
that
the
Box
on
internet
exchange
chose
to
do
this.
Our
next
slide,
please.
J
Just
a
very
quick
overview
and
the
reminder
of
how
BGE
works
if
I
was
sitting
at
home
at
my
provider,
sonic,
dotnet
and
I
wanted
to
get
the
wet
uc-berkeley
website.
I
would
go
through
the
networks
and
layout
and
trance
trailed
and
scenic
and
get
UC
Berkeley,
but
the
way
that
my
provider
gets
to
know
about
this
route
to
UC
Berkeley
is
at
UC.
J
Berkeley
is
announcing
its
IP
addresses
using
BGP
to
seen
it
which
relays
them
to
transit,
rel,
realism
and
Lehr
and
so
on
to
Sonic,
and
so
the
the
routing
table
the
internet
gets
about.
True
in
this
distributed
fashion.
Now,
what's
interesting
about
BGP
as
it
stands
today
is
that
there
are
all
these
kinds
of
claims
are
routing
claims
above
where
you
can
get
their
identity
claims
about
who
you
are
and
who
you
can
get
to.
There
are
resource
claims
about
what
IP
address
is
you
carrying,
but
what's
really
interesting
about
it
as
a
protocol?
J
J
Now,
what
does
this
mean
for
us
when
we
think
about
rights,
and
let
me
broaden
out
the
conversation
for
a
minute
before
I
narrow
back
down
on
BGP
again
now.
One
way
that
we
think
about
rights
is
in
a
balance
between
autonomy
and
accountability.
We
have
you
have
the
guarantee
of
a
freedom
of
speech,
but
equally
you
have
your
held
accountable.
You
can't
engage
and
hate
speech.
J
For
instance,
you
can't
engage
in
defamation
and
that
balance
is
in
many
ways
the
ways
in
which
one
way
in
which
rights
are
articulated
and
again
the
balance
is
found
differently
in
different
places
under
different
political
conditions.
Now,
how
might
we
start
to
think
about
that
balance
in
terms
of
protocols,
but
this
is
very
much
a
balance.
J
It
goes
back
to
the
early
days
of
the
internet
when
John
Perry
Barlow
was
telling
us
with
declaring
the
independence
of
cyberspace
right,
but
this
is
a
space
beyond
control,
but
instead
I
suggest
what
we
might
start
to
ask
of
our
protocols
instead
of
looking
at
particular
rights.
The
way
that
we
might
get
to
thinking
about
how
a
balance
we
are
gonna
mean
accountability
is
manifested
within
infrastructure
might
be
ask
these
questions,
who
can
exert
control?
J
Who
is
able
to
exert
control
to
ensure
autonomy
or
to
ensure
accountability
and
equally?
How
can
we
trust?
How
can
we
trust
these
systems?
How
does
trust
function
within
the
context
of
these
systems
and
analytically
I'll
break
these
down
in
the
cosmetic
over
three
areas
right
the
standards?
What
is
the
actual
form
of
the
standard?
J
What
was
the
standard
alone
but
gentlemen
earlier
was
talking
about
SMTP,
that
there
are
particular
features
of
SMTP
B
that
allowed
particular
kinds
of
abuses
equally
from
BGP
that
are
particular
features
of
BGP
that
allow
route
hijacks,
for
instance,
and
equally,
who
makes
the
standards
all
of
you
at
the
IETF
how
the
standards
organizations
function.
The
next
piece
is
resources.
What
resources
does
a
protocol
need
in
order
to
operate
and
who
controls
those
resources?
How
are
they
to
be
trusted?
The
regional
internet
registries
in
this
instance?
J
J
And
so,
let's
talk
about
how
Authority
shifts
like
over
the
history
of
the
protocols
that
came
to
be
BGP
and
back
in
the
days
of
the
ARPANET,
we
go
back
to
our
FC
eight
to
three.
You
have
the
gateway
to
gateway
protocol,
the
original
protocol
for
interconnecting
networks
for
interconnecting
the
different
gateways
of
the
time.
In
that
protocol
it
actually
defines
Authority.
It
says
you
know
all
the
gateways
are
under
a
single
authority
in
control,
as
is
the
practice
and
other
network
implementations.
There
was
no
notion
that
the
internet
was
to
be
decentralized.
J
There
was
a
very
clear
definition
of
where
Authority
and
control
was
meant
to
reside.
You
move
forward
to
the
next
generation
of
the
protocol,
the
exterior
gateway
protocol,
which
was
deployed
in
the
NSFNET,
and
you
see
again
not
a
different
definition
of
authority
or
a
definition
of
topology.
It's
intended
for
set
of
autonomous
systems
connected
in
the
tree
with
no
cycles
and
therefore
the
NSFNET
backbone
becomes
the
authority,
the
default
Authority
they
around
the
policy
routing
database,
where
all
the
routes
were
maintained
and
were
just
from
the
backbone
that
routing
was
controlled.
J
But
then
you
get
to
the
internet
with
BGP
BGP
originally
born
the
NSFNET,
but
then
was
used
to
make
the
public
Internet
and
you
get
to
a
point
where,
all
of
a
sudden
there
is
no
hierarchical
Network.
You
have
a
complex
graph
that
we
have
changed
and
in
making
the
transition
from
the
NSFNET
to
the
internet,
the
NSF
issued
a
solicitation
for
a
resource
arbiter,
which
has
become
the
RA
VB
today
and
the
system
of
internet
route
registries.
That,
in
theory,
would
act
to
establish
and
maintain
databases.
J
Routing
services
which
may
be
used
by
attach
networks
talked
a
lot
of
information,
but
need
not
be
used
and,
as
many
of
you
may
know,
these
are
in
fact
not
used
by
our
networks.
Some
use
them
some,
don't
they
use
different
degrees.
So
the
question
then
becomes
as
enough
along
the
YouTube
example.
How
is
Authority
maintained
within
the
context
of
this
decentralized
system
and
just
to
remind
us
about
how
complex
the
system
really
is
next
slide?
Please.
J
We're
currently
looking
at
over
60,000
individual
networks,
60,000
autonomous
systems
announcing
over
seven
hundred
and
forty
thousand
IP
address
prefixes
and
as
I
found
in
my
research,
the
key
mechanism
stabilizing
these
interconnections
is
really
trust
and
interpersonal.
Now,
what
do
I
mean
by
Trust
and
I
will
tell
you
when
we
get
to
the
next
slide
next
slide.
Please.
J
Now
there
are
many
definitions
of
trust,
but
for
the
purposes
of
this
presentation,
I'm
going
to
talk
about
a
relational
definition,
then
in
general,
when
you
have
a
problem
of
engaging
with
for
miles
and
an
interaction
that
it
involves
some
risk
and
uncertainty.
How
do
you
solve
that
problem?
Now?
One
solution
is
to
have
an
assurance
capture,
as
might
be
called,
which
is
well
I'm,
exchanging
people
money
with
someone
do
they
need
to
trust
you,
except
if
the
money
has
value,
trust
your
central
bank?
Yes,
something
else,
you
have
an
Australian
structure,
the
bank
money.
J
J
Seen
you
like
shopping
that
for
a
while
and
wonder
you
forget
your
wallet
and
perhaps
the
shop
owner
says
well,
I
trust
you
I've
known
you
for
a
while
payment
when
you
come
the
next
time,
and
so
it's
not
to
say
that
these
are
the
only
two
solutions
to
the
problem
of
risk
and
uncertainty
and
not
that
are
mutually
exclusive
but
analytically
to
you.
So
to
pull
them
apart.
To
think
about
assurances
versus
interpersonal
trust,
has
solutions
to
the
problems
of
risk
and
uncertainty
next
slide.
Please.
J
And,
of
course,
these
aren't
merely
interpersonal
problems.
These
are
societal
problems,
and
so
we
can
talk
about
system,
trust
but
large
systems
that
we
trust
in,
like
the
Internet
and
the
assurance
structures
that
provide
anchors
for
those
systems
we
can
eat.
We
talk
about
interpersonal
trust
networks
or
relationships.
The
reputation
we
form
within
those
networks
that
allow
those
systems
to
function
and
equally
talk
about
generalized
trust.
J
J
So
I
studied
a
two
major,
mostly
studied
two
major
network
operator
communities,
the
North
American
network
operators,
group
Nano,
which
many
of
you
may
know
the
picture
above
and
the
South
Asian
network
operators
group
some
are
down
below
and
I
will
talk
about
both
of
them
briefly
in
a
moment.
But
what
I
very
much
focused
upon
was
the
role
of
trust
relationships
being
formed
within
these
communities
of
practice
and
the
importance
of
these
trust
relationships
to
the
operation
of
the
global
Internet
and
of
BGP,
particularly
next
slide.
Please.
J
So
I'll
give
you
a
couple
of
quotes.
Just
two
brief
quotes
from
interviews
that
I
did,
which
should
give
you
a
flavor
of
what
people
were
saying
to
me,
but
equally
things
that
are
probably
many
of
you
are
very
familiar
with
when
I
was
asking
someone
about
how
they
are
about
BGP,
he
said
well
and
the
idealized
role
of
humans,
not
being
social
animals
you'd,
have
really
really
high
quality,
low-friction
functioning
contacts.
J
J
And
then
someone
else
said
well,
how
do
you
start
to
solve
this
issue?
This
problem?
Well,
there's
lots
of
communication
through
backchannels
lots
of
unofficial
communication,
lots
of
things
nobody
can
officially
talk
about,
but
if
we
can
also
have
information
about
it,
we
can
make
the
internet
a
better
place.
There's
lots
of
communities
and
the
only
way
that
you
gain
admission
into
a
community
is
to
be
a
trusted
individual,
so
very
much
trust
within
the
operation
of
the
infrastructure
as
much
as
past
the
infrastructure
next
slide.
Please.
J
So,
when
I
go
to
an
automatic
and
network
operators
group
meeting-
yes,
they
have
the
formal
sessions,
but
much
more
important
than
the
formal
sessions
are.
The
hallway
tracts
the
informal
meetings,
the
building
of
trust
relationships
within
these
spaces
and
that's
sufficiently
important,
as
some
of
you
may
know,
that
it's
not
just
North
Americans,
who
show
up
to
nominal
meetings.
It's
people
from
around
the
world,
because
North
America
is
so
relatively
central
to
the
global
Internet
and
people's
affiliations
to
this
community,
as
in
many
ways
as
important
as
their
affiliations.
To
that
employers.
J
In
fact,
many
people
wouldn't
deny
our
community
are,
will
be
hired
by
companies
for
the
relationships
that
they
hold
and
their
ability
to
get
things
done
within
this
community.
So,
on
the
one
hand,
yes,
the
technical,
commercial
political
relationships
that
make
the
internet
go,
but,
on
the
other
hand,
the
commitments
and
the
trust
relationship.
So
within
this
community
that
make
the
internet
go
and
the
doors
to
aren't
mutually
exclusive,
but
really
very
much
rely
upon
one
another
next
slide.
Please.
J
But,
of
course,
this
is
not
a
purely
North
American
problem
that
the
Internet
is
a
global
system
and
part
of
what
I
was
interested
in
was
well.
If
I'm
making
the
claim
that
Trust
is
so
important
to
the
functioning
of
a
global
Internet,
how
does
it
travel?
How
does
it
get
established
in
other,
geographies
and
so
I
went
to
meetings
of
the
South
Asia
network
operators
group
and,
while
South
Asia
as
a
whole,
is
relatively
peripheral
to
the
Internet
compared
to
North.
American
trust
was
equally
important
in
this
context.
J
I
frequently
found
people
that
I'd
met
at
Nanog,
showing
up
to
Sun
of
meetings,
often
as
instructors
I
frequent
I
found
people
within
sanog
building
relationships
not
necessarily
to
that
peers.
Yes,
but
much
more
so
to
others
who
could
then
facilitate
those
connections
that
were
international
and
so
there's
this
way
in
which
sure
we
now
have
this
protocol,
the
border
gateway
protocol
right
that
is
defined
as
a
technology,
but
that
very
much
relies
upon
these
communities.
J
J
J
The
overlapping
network
operator
groups
around
the
world,
I've
got
a
handful
of
them
listed
there
and
in
between
the
social
network
of
trust
relationships,
but
this
lighter
lives
in
one
or
the
other,
but
was
really
facilitated
by
both
people
connecting
networks
together
and
come
to
trust
each
other
in
the
practice
of
interconnecting
networks,
people
negotiating
best
practices,
building
relationships
within
the
communities
of
non
emergency,
AMARG,
and
so
on
next
slide.
Please.
J
But,
of
course,
I
hope,
I've
only
talked
about
the
problem
of
interpersonal
trust
over,
but
it's
equally
important
as
talking
about
assurance,
trust
structures
earlier
to
talk
about.
How
do
we
trust
institutions?
How
do
we
trust
an
IETF
and
I?
Can
a
regional
internet
registry
now
the
way
that
we
often
think
about
assurance
structures
like
a
central
bank
or
an
IETF
or
regional
internet
registry
is
in
terms
of
autonomy
and
independence.
These
are
organizations
that
we
would
like
to
function
autonomously
from
society.
We
want
them
to
be
independent.
J
We
want
them
to
be
impartial,
but
yet
for
these
institutions
to
function
efficiently
to
make
sense
the
world
they
equally
have
to
function
in
terms
of
what
we
might
call
embeddedness,
building
relationships
to
the
communities
that
they
serve
and
so,
for
instance,
and
many
of
the
people
that
I
met
at
nanog
I.
Equally
matter,
IETF
and
I'm.
J
Sure
many
of
you
in
the
room
go
to
many
of
the
network
of
Pitta
groups,
meetings
that
I
described
or
have
been
to
something
at
least,
and
the
balance
really
here
is
between
embeddedness
and
autonomy
and,
as
some
scholars
called
embedded
autonomy
that
you
want
institutions
that
are
well
connected
to
the
society
that
they
represent.
But
at
the
same
time
you
want
them
to
be
functioning
autonomously
independently.
J
That
actually
is
security
is
a
technically
required
to
make
DNS
SEC
more
secure,
probably
not,
but
it
does
play
a
significant
role
in
ensuring
the
trustworthiness
of
the
bnsf
process
and
that
there
are
other
DNS
operators
who
have
talked
to
who
will
say
well,
I,
don't
know
about.
I
can
but
I
trust
the
individuals
who
these
trusted
community
representatives,
because
they
would
witness
this
process
and
I
trust
the
individual
and
therefore
I,
have
more
trust
and
this
process
next
slide.
Please.
J
In
the
context
of
BGP,
we
see
this
playing
out
at
places
like
aaron,
the
american
Registry
for
internal
numbers
and
other
regional
internet
registries,
because
these
the
organizations
that
manage
the
resources
required
for
BGP
each
operate,
IP
address
space,
autonomous
system
numbers
and
there
are
formal
mechanisms
through
which
this
occurs.
As
many
of
you
know,
the
Arin
Advisory
Council
that
Sheppard's
their
policy
process
is
populated
by
people
elected
from
the
community
by
the
community.
J
The
Arin
board
is
populated
by
people
from
the
community
elected
by
the
community,
while
at
the
same
time
ahran
maintains
a
professional
staff,
professional
bureaucracy
so
in
a
way,
a
way
to
balance
that
embeddedness
and
autonomy
through
these
mechanisms
of
representation,
but
at
the
same
time,
through
established
principles
that
I
agreed
upon
with
the
community
that
aaron
and
others
may
be
held
to
account
for
so,
for
instance,
notions
of
conservation
and
stewardship
in
the
way
that
address
space
is
managed
next
slide.
Please.
J
Now,
of
course,
to
go
back
to
where
I
began.
Thinking
about
the
history
bgp
equally
does
another
change
of
4th
in
BGP
right
now,
which
is
instructive
and
thinking
about
the
story
that
I've
told
so
far.
We
have
rpki,
which
is
cryptographic
mechanism
for
securing
bgp
announcements
and
I'm,
not
getting
into
a
discussion
of
whether
this
is
good
or
bad.
But
the
point
that
I
want
to
make
from
a
perspective
of
how
is
how
does
Klaus
control
establish
how
distressed
function
as
if
we
move
we're
moving
from
a
system
in
which
it
was
not
trust?
J
Community
and
practice
is
a
greater
salience
to
maintaining
the
interconnection
networks
to
a
system
in
which
governance
and
institutional
accountability
and
assurance
are
more
salient
as
the
regional
internet
registries
and
other
organizations
start
to
function
as
trust
anchors
for
rpki,
and
it's
not
a
complete
transition,
of
course,
but
small
shift
and
emphasis
in
the
way
that
BGP
is
managed,
and
it's
something
for
us
to
think
about
critically-
gives
us
some
fuels
about.
Well,
if
we're
going
to
think
about
the
expression
of
Rights
within
the
system,
how
do
we
not
hold
it
accountable?
J
We
might
earlier
have
gone
to
have
said
well.
We
need
to
express
these
principles
and
rights
within
the
practices
that
are
being
transmitted
across
the
network
operator
groups
within
the
principles
held
by
organizations
like
the
IETF,
the
regional
internet
registries,
and
now
we
might
have
to
focus
much
more
upon.
Well,
what
are
the
formal
mechanisms
of
accountability
for
the
trust
anchors
to
ensure
that
they
don't
violate
rights,
that
they
don't
they're,
not
politically
captured
by
another
agency?
That
forces
them
to
withdraw
ROVs
to
remove
certification
for
us
next
slide.
Please.
J
And
so
we
go
from
a
perspective
where
I
started
by
talking
about
BGP
as
a
technical
problem
and
like
this
I
describe
the
technology.
Briefly,
let
me
now
give
you
the
brief
overview
of
BGP
as
a
social
problem,
which
is
what
I
walked
through
today,
very
much
as
circulations
of
trust
in
practice,
across
geographies
across
geographically
distributed
network
operator
groups
held
together
by
different
organizations,
managing
standards
and
resources
that
are
held
accountable
to
these
groups
or
not,
people
will
debate
that
through
mechanisms
of
embeddedness
and
autonomy
as
they
balance
next
slide.
Please.
J
Which
brings
us
full
circle
back
to
where,
where
I
began,
in
thinking
about
the
balance
between
autonomy
and
accountability
in
rights,
to
talk
about
well
cus,
the
questions
of
protocols,
how
can
we
exert
control?
How
can
we
trust
and
apply
those
questions
to
standards,
resources,
anthropology
as
independent
problems
and
yet
next
slide?
Please.
J
What
I'd
like
to
suggest
is
that
somebody's
awesome
topology
aren't
quite
so
independent
as
we
might
like
to
treat
them.
They
in
fact
intimately
connected,
and
it
was
something
again
that
came
up
in
the
conversation
before
I
began
my
talk
of
well.
How
does
something
in
one
space
and
then
how
do
violations
of
rights
we
see
in
topology
affect
a
discussion
about
standards
and
equally
I
would
suggest?
How
does
it
affect
the
way
that
resources
should
be
managed
and
that
all
these
three
are
really
intimately
connected?
J
And
while
analytically,
we
can
pull
them
apart
and
we
should
pull
them
apart
in
reality,
we
know
equally
need
to
think
about
how
they're
connected
together
and
how
they
influence
each
other
and
one
way
to
approach
that
across
each
of
these
rounds
across
standards.
Topology
and
resources
is
to
think
about
how
the
design
of
Technology
interacts
with
the
design
of
institutions
required
to
manage
that
technology,
so
BGP
needs
autonomous
systems,
needs
IP,
address
space
to
be
unique,
and
so
you
have
regional
internet
registries
that
ensure
the
uniqueness
of
those
allocations.
J
We
had
EGP
that
assumed
that
again,
a
central
point
of
control
and
the
topology
and
now
BGP,
which
assumes
a
completely
decentralized
system,
but
then
what
relationships
are
required
to
manage
that
as
I've
argued
as
I
found
on
my
research
relationships
of
trust
carry
across
these
network
operator
groups,
I'll
close
there
I
offer
this
as
hopefully
a
useful
analytic
for
thinking
about
the
way
that
we
might
think
what
control
and
Trust
and
protocol
design
and
hopefully
inform
the
way
we
think
about
rights
and
the
balance
of
Rights
is
articulated
across
those.
Thank
you.
Thank.
A
G
Great
presentation,
thank
you.
So
it's
head
11
by
the
way,
so
so
the
question
that
I'm
running
into
when
I,
when
I
think
about
what
you
just
said,
is
that
we
seem
like
we're.
We
have
a
we
seem
like.
We
have
a
bit
of
a
Hobson's
choice
here
between
you
know,
a
system
that
we
currently
have
that
doesn't
actually
work
all
that.
Well,
though,
it
works
damn
well
and
another
system
that
has
been
proposed
to
replace
it.
G
J
It's
a
hard
one:
I,
don't
pretend
to
have
a
pad
to
answer
to
it,
because
on
the
one
hand,
the
I
I
think
that
there
has
been
the
Internet
and
part
has
been
successful
because
it
has
been
permissionless
and
people
have
been
able
to
connect
at
will
without
having
to
get
permission
from
anywhere
and
can
continue
to
do
so.
On
the
other
hand,
that
has
come
with
a
responsibility.
Thinking
about
that
balance
between
autonomy
and
accountability.
We
have
autonomous
systems,
they
can
configure.
J
You
can
connect
to
you
will,
but
accountability
has
largely
been
social,
it's
what
so
far,
but
as
we're
seeing
increasingly,
there
are
effects
which
go
from
the
Pakistan
case
that
you
could
say:
oh
well,
that
was
a
local
attack.
It
wasn't
meant
to
spread
outside,
yet
it
did
to
other
more
recent
attacks
that
have
been
in
the
news
again.
That
do
seem
to
be
much
more
intentional
and
I
think
the
balance
there
as
well.
J
L
Go
ahead
covered
iceberg.
Thank
you
for
the
presentation.
I
actually
have
multiple
issues
with
it
with
the
points
there,
but
I
will
focus
on
the
main
one
which,
which
is
basically
the
way
I
saw
it.
You
mixed
up
different
protocol
stacks
and
different
layers
of
stuff,
which
was
supposed
to
be
separate
and
then
draw
conclusions
which
are,
in
my
opinion,
wrong
because,
for
example,
BGP
is
decentralized.
It
is
supposed
to
be
like
that
and
and
most
of
the
peering
actually
is
not
discussed
in
Aaron
or
Sanok,
or
things
like
that.
L
They
are
discussing
global
peering
from
a
New,
Yorker
and
peering
from
venues
like
that,
then.
But
then
you
make
conclusions
which
are
relevant
to
DNS,
for
example,
and
then
you
bring
I.
Can
you
had
you
said
things
like
you?
People
observe,
because
they
trust
individuals
for
key
signing.
That's
not
the
case,
so
the
whole
notion
of
trust.
We
cannot
put
all
of
these
things
in
a
soup
and
say
decentralized,
nature
of
DNS
versus
decentralized,
nature
of
bgp
versus
all
other
phones
on
top
of
them,
and
then
make
conclusions
about
trust
about
this
big
soup.
L
We
have
to
look
at
them
separately
and
they
have
they
have
separate
functions,
and
this
institution
is
the
one
you
mentioned.
For
example,
if
there
is
tomorrow,
there
is
no
I.
Can
nothing
will
change
your
router?
Even
if
there
is
no
dns,
nothing
will
change
in
Rajan.
So
we
really
have
to
look
at
these
things
separately
and
and
understand
them
separately,
because
yeah,
it's
really
impossible
to
take
it
to
to
draw
conclusions
from
from
top
layer
and
then
apply
them
to
the
two
layer
below
so.
J
I
actually
agree
with
you,
they
should
be
considered
separately
and
I
was
trying
to
do
that.
I'm.
Sorry,
if
that
wasn't
very
clear
to
you,
my
focus
was
on
BGP
I
was
using
DNS
straight.
Some
of
my
points,
I
do
think
that
the
relationships
of
trust
that
I
was
describing
are
articulated
differently
in
different
protocols.
J
I
didn't
dwell
on
DNS
at
any
length
now.
The
point
that
I
was
trying
to
make
was
that
the
relationships
of
trust
while
they
are
articulated
in
different
protocols
differently,
the
communities
are
the
same
right.
So
you
have
people
who
are
doing.
Dns
operations
will
often
be
involved
with
the
network
operation
operator
community
will
shelter
the
same
spaces.
Those
relationships
of
trust
form
they're,
actually
form
that
actually
cut
across
now.
J
Do
people
trust
I
can
I'm
offering
you
one
way
for
thinking
about
how
people
do
trust
I
can
and
it's
not
that
they
trust
I
can
the
institution,
but
they
trust
the
people
witnessing
the
process
now.
Other
other
ways
that
you
could
trust
I
can
absolutely
I.
Don't
disagree
with
you,
but
I'm
offering
you
one
way
through
which
you
think
about
trust.
J
As
being
a
problem
of
embeddedness,
one
way
in
which
you
think
about
how
to
hold
institutions
to
account
right
so,
on
the
one
hand,
something
like
an
errand
advisory
council
that
is
elected
and
actually
is
involved
in
the
process
actively.
On
the
other
hand,
a
trusted
community
representative
for
DNS
SEC
who
witnesses
the
process
and
reports
back
on
it.
These
are
both
mechanisms
of
trust,
admittedly
very
different,
but
the
different
ways
through
which
institutions
can
be
held
to
account.
J
L
You
right
I
think
we
need
to
discuss
this
a
bit
of
flight
as
well,
because
just
just
my
closing
point,
the
the
point
of
creation
of
an
inn
situation
like
I
can
is
was
basically
the
community
didn't
want
to
trust
in
one
person.
So
the
whole
thing
is
it's
not
trusting
individuals
or
you
create
a
system
which,
based
on
transparency
and
accountability,
you
can
trust
it
or
you
don't,
but
it's
a
system
you're
dealing
with
it's,
not
individuals
and
it's
and
the
motivation
and
drive,
should
never
be
trust
in
individual.
Thank
you.
J
Well,
thank
you
and,
as
a
closing
response,
I'm
happy
to
keep
talking
about
it.
It's
also
important
to
remember
that
I
can
was
created
by
the
US
Department
of
Commerce
at
a
particular
moment
in
history,
and
that
there
was
central
debate
around
who
should
be
trusted
and
who
should
not
be
trusted
and
I
think
it
continues
to
hold
true
today
that
individuals
are
still
trusted
within
these
systems.
M
M
Be
the
reality
of
of
this
of
the
scenario,
so,
even
if
you
can
ensure
something,
but
you
cannot
always
future
proof,
so
so
that's
an
aspect
that
gets
whether
you
take
medical
devices,
there
are
million
dollars,
so
they
must
be
still
running
some
windows
XP
or
to
95
or
98.
It's
hard
to
replace
them.
So
so
I
feel
that
this
discussion
is
missing.
That
key
element
of
the
disparity
of
devices
that
exist
out
there
right.
J
And
I
agree
I
mean,
for
instance,
thinking
about
BGP,
just
what
I
talked
about
when
you
go
from
the
way
that
it's
designed
now
to
the
deployment
of
RPI,
some
networks
are
deploying
RPI,
others
aren't
and
it'll
probably
be
a
long
time
before
it
has
deployed
widely
in
any
meaningful
way.
For
multiple
reasons,
there
are
capital
costs
and
buying
new
equipment
that
there
are
costs
in
training
personnel.
The
new
equipment
has
to
handle
cryptography,
it's
gonna
be
more
processor
intensive.
J
There
are
all
these
considerations
who
come
in,
which
means
we're
going
to
continue
just
as
we
have
a
dual
stack,
v4
v6
internet
will
have
a
dual
stack
BGP
that
some,
which
has
a
PKI
some
but
doesn't
now.
How
do
we
start
to
handle
that?
And
that's
where
I
think
that
communities
that
I
described
become
really
critical?
J
On
the
one
hand,
you've
got
the
institutions
that
you
might
start
to
rely
upon
like
the
errors
like
the
IETF
like
I
can
and
so
on,
but
in
those
networks,
those
broad
networks
of
social
relationships
formed
within
the
communities
of
practice.
The
network
operator
groups
I
think
those
play
a
critical
role
and
allowing
for
some
leeway
in
those
Tran
the
longfin,
more
negotiation
in
those
transitions
at
the
operational
level
in
ways
that
are
really
critical
and
I
think
overlooked
in
a
lot
of
policy
discussions.
O
J
Question
so
I
I
think
that
in
this
particular
instance,
I
would
say
it's
not
so
much
about
trusting
the
cryptography
and
the
algorithm,
although
that's
certainly
an
aspect
of
it
as
it
was
about
studying
the
institutions
that
act
as
the
trust
anchors.
So
if
you
were
talking
about
blockchain,
for
instance,
I
would
say
yes.
N
J
Have
you
need
to
like
trust,
the
algorithm
much
more
in
the
community
of
practice
that
develops
that
algorithm
in
this
particular
case,
because
it's
publicly
cryptography,
it's
were
recognized.
The
regional
internet
registries
are
holding
the
root
keys,
not
for
all
of
it,
but
at
least
for
some
parts
of
the
system.
It
becomes
much
more
important
to
trust
and
hold
to
account
the
internet
registries
than
it
does
the
broader
community
of
practice.
A
A
P
First,
we
started
with
a
discussion
on
the
recent
developments
with
the
bo
h,
VN
s
over
HTTP
DNS
over
TLS
and
encrypted
s,
ni,
which
is
still
a
draft,
and
we
wanted
to
explore
them
from
a
measurement
angle
and
see
how
tools
and
tests
which
are
in
let's
say,
measurement
as
in
censorship.
Measurement
tests
will
change
and.
P
P
We
didn't
find
a
web
based
DNS
over
HTTP
test,
so
we
made
one,
and
this
is
life,
so
you
can
go
to
net
blocks,
dot,
o-r-g,
/tmp,
slash,
do
H,
I,
think
I
can
share
it
later,
and
you
can
basically
enter
one
domain
name
and
just
test.
Your
responses
from
different
publicly
available
do
ad
servers,
and
one
thing
that
we
might
bring
up
with
the
DOE
community
is
that
you
will
find
that
some
of
these
are
failing.
P
This
is
because
they
haven't
enabled
the
cross-origin
resource
sharing
course
header
on
their
servers,
so
if
they
allow
that
without
any
tweaks
at
the
client
end,
what
you
can
have
is
like
a
completely
distributed
system
for
testing
do
X
responses,
and
this
can
also
be
extended
to
detect
in
DNS.
Suppressing
censorship,
as
though
becomes
popular
I
think
there
will
be
pressure
from
dosa
was
likely
out
fair
and
Google,
not
in
a
particular
location,
suppress
DNS
responses,
so
this
might
be
a
useful
tool
to
test.
That
is
what
yeah.
Q
We
were
all
we
were
also
laying
the
basis
with
other
people's,
therefore,
a
human
rights
review
for
Dome,
but
then
we
also
understood
that
this
is
a
huge,
interconnected
thing,
with
different
configurations
between
dots,
doe
es
ni,
opportunistic
DNS,
DNS
X.
So
we
thought
before
we
start
going
into
anything.
Let's
first
understand
what
the
whole
thing
is,
and
this
was
the
first
try
at
that.
R
R
R
Okay,
as
I
say,
the
issue
is
not
the
precise
cryptographic
technology
user
made
the
connection
the
resolver.
It
is
the
means
by
which
you
determine
which
resolver
to
use
it
is
relevant.
So
you
will
find
this
much
simpler.
If
you
collapse,
doe
dot
do
Q
and
Deena
script
into
one
giant,
secure,
Channel
bucket.
A
N
S
So
I
came
up
to
ask
to
go
back
one
slide,
so
thank
you
for
doing
that.
It's
impossible
to
see
this
in
the
back
of
it.
No,
that
was
the
slide.
The
one
that's
impossible
to
see
yeah.
Could
you
describe
what
we're
seeing
here,
because
it's
an
eye
chart
we
I
could
not
read
anything
on
that
slide
from
the
back
of
it.
This.
Q
At
so
we're
looking
on
in
the
column
left
we're
looking
at
different
configurations
of
DNS
the
combination
Tina's
over
TLS
DNS
over
HTTP
DNS
with
es
ni
and
then
different
configurations
of
that
combined
and
in
the
upper
row.
There
is
different,
there's
different
scenarios
and
then
the
column
is
filled
in.
What
is
the
case
where
and.
T
E
Don't
think
it
quite
matters
here
is
that
people
often
conflate
the
notion
of
DNS
over
HTTP
and
the
way
that
it's
been
implemented
in
the
only
implementation
that
I'm
that
that's
widely
deployed
where
it's
been
coupled
with
the
the
choice
of
resolver
and
the
question
of
who
chooses
the
resolver
and
how
is
fundamental
to
all
of
this
and
be
interesting
to
say
if
you
could
do
some
more
exploration
of
that
problem,
as
opposed
to
looking
at
channel
security
and
the
various
other
things,
because
I
think
what
a
fairly
fairly
long
way
down.
That
path,
though,.
Q
So
we're
totally
so
we
actually
completely
wanted
to
do
that,
but
what
we,
what
we
got
on
our
plate
was
a
lot
of
questions
and
a
lot
of
uncertainty
and
a
lot
of
different
things
out
there.
So
we
wanted
to
create
some
clarity
and
we're
not
there.
This
was
just
step
one
in
just
trying
to
understand
what
different
configurations
possibilities
are
and
to
understand
what
is
actually
in
a
network
protocols.
What
is
in
the
play
implementation,
and
what
can
we
recommend
and
understand
what
happens
on
different
levels.
U
Hey
Nelson
salia
is
actually
I,
think
there's
a
pretty
good
slide
as
a
way
to
start
right
and
to
answer
Martin's
point
I,
think
Mark,
Martin,
you're,
I
know
this
is
an
eye
chart.
You
got
a
look
at
that.
What
does
a
column
number
two
there?
Where
it
says,
network
provider
sets
DNS
provider
I?
Think
that
aims
towards
where
you
were
going
and
to
Eric
your
point
I?
U
What
what
you
start
with
is
something
like
this
and
then
you
figure
out
how
to
buck
it
and
I
see
some
buckets
forming
there
and
I
think
we
all
have
a
good
feel
for
where
those
buckets
are
gonna
land.
But
it's
nice
to
have
this
sort
of
comparison.
So,
apart
from
the
colors
I
think
it's
a
good
start
and
then
your
next
step
is
to
bucket.
A
Thanks,
did
you
have
okay,
so
you
wanted
done?
Okay,
any
other
comments
or
are
they
all
in?
If
not,
then
we'll
move
to
the
next
section
we
we
probably
will
run
out
of
time
before
we
get
to
everything
on
the
agenda,
but
that's
okay.
We
we
had
ranges
of
time
for
the
previous
discussions
and
we
went
to
the
maximum.
So
the
update
on
the
human
rights
review
team
and
that
Spheeris
or
Niels
who's
talking
meals.
Q
So
unfortunately,
Beatrice
is
not
here,
but
this
is
just
an
overview
of
a
recent
Human
Rights
refused,
as
we've
done,
we've
done
a
couple
again,
so
it
is
starting
to
become
a
bit
more
of
a
standing
practice.
This
one
was
based
on
quick,
so
we
analyzed
three
different
drafts.
Even
though
we
read
a
lot
of
other
drafts,
we
used
a
bit
of
different
methodology
than
with
the
other
Human
Rights
reviews,
so
that
we
also
get
better
in
our
methodology
and
try
to
understand
better
how
to
approach
this.
Q
We
got
a
lot
of
feedback
from
the
community
that
it's
better
to
do.
Reviews
earlier
instead
of
last
call,
because
at
last
call
there's
already
been
a
lot
of
discussion
and
people
don't
really
like
to
change.
We
thought:
let's
try
to
do
it
earlier
with
quick.
We
might
have
not
been
so
early
which
we
heard
when
gursha,
but
it
is
great
great
review
of
a
suit
in
IP
wave.
The
the
the
feedback
was
well
you've
done
this
review
really
early.
Q
Q
We
read
all
the
drafts
in
and
then
came
up
and
then
used
that
did
that
next
too,
while
keeping
the
considerations
from
RFC
eighty
two.
Eighty
next
to
it,
came
up
with
questions.
We
did
interviews
with
seven
of
the
working
group
chairs
document,
authors
and
working
group
contributors
of
about
sixty
to
ninety
minutes.
We
fully
transcribed
these
interviews
and
then
try
to
puzzle
together
relevant
answers
to
relevant
categories
from
RFC
eighty
to
eighty
and
then
trying
to
clean
it
up
and
make
it
more
readable
and
paraphrase.
Q
Then
we
shared
the
first
draft
with
all
interviewees
incorporated
the
feedback
and
try
to
do
that
twice.
Well,
we
published
it
as
a
draft.
Previously
we
only
have
shared
it
as
a
on
a
mailing
list,
but
we
heard
from
people
that
that
was
a
bit
hard
to
track.
So
then
we
put
it
in
in
the
we
published
it
as
an
internet
draft.
We
shared
it
on
the
quick
mailing
list
on
October
22nd
and
thus
far
we
have
not
received
any
responses
on
lists.
Q
So
I
don't
know
whether
this
was
because
it
is
relatively
late
in
the
process
or
drafts.
A
model
was
not
that
good
later
I
also
posted
a
markdown
version.
So
that's
that's,
maybe
something
we
need
to
configure.
Maybe
we
should
just
wait
a
bit,
but
the
interesting
thing
is
that
we
it
when
the
kind
of
ballistic
on
Twitter,
which
is
a
bit
weird
for
an
internet
draft,
to
do
that
at
least
when
I
post
them.
So
so
it's
maybe
different
audience
different
ways,
but
I
see.
V
Lars
has
a
lot
of
Tiger,
so
personally,
I
think
you
probably
didn't
get
any
comments,
because
there
didn't
really
seem
to
be
anything
that
that
needed
commenting
it.
So
there
wasn't
anything.
There
was
nothing
that
was
urgently
needed.
Fixing
right,
plus
the
working
group
is
kind
of
busy
with
getting
the
protocol
on
at
the
moment.
So
that's
sort
of
my
personal
take
why
you
didn't
get
any
feedback
or
any
any
responses.
Did
you
expect
anything
they
in
there
to
raise
concerns
for
us.
Q
Well,
there
were
a
few
considerations,
but
then
I
also
got
some
hints
of
lens.
That
I
should
that
I
should
open
tickets
in
I
should
use
them
to
open
tickets
in
github.
We
could
do
that
sure,
for
instance,
the
internationalization
stuff
isn't
fixed
yet
and
I
think
that
will
be
good
to
do
it
before
we
ship
it
right.
So.
V
That
thought
so
again
personally,
I
think
this
is
so
far
down
the
priority
list
of
people
at
the
moment
right
where
a
lot
of
the
basic
protocol
stuff
doesn't
quite
work
it
or
isn't,
interrupts
tested
that
I'm
not
surprised.
You
didn't
get
any
feedback
on
that,
no
sure,
but
that's
where
internationalization
always
is,
though,.
W
Me
accouterment,
so
I
gave
you
some
private
feedback
and
I
think.
The
reason
why
I
didn't
get
a
lot
of
feedback
is
because
I
think
some
of
the
issues
you
mentioned
are
not
well
discussed.
Like
some
of
the
issues
you
you
discuss
in
the
draft
have
been
like
heavily
discussed
and
the
working
group,
so
many
people
contributed
their
different
opinion,
including
people
who
also
contribute
to
this
group
and
I.
W
So
for
me,
the
document
didn't
reflect
well
what
was
done
in
the
working
group
and
what
the
issues
are,
and
it
didn't
add
anything
to
the
discussion.
Unfortunately,
so
I
mean
like
I'm
a
little
bit
disappointed
because
I
think
it's
a
good
effort-
and
you
put
so
much
so
much
work
into
this
but
I
think
the
outcome
didn't
really
value
that
work.
To
be
honest,
sorry
well.
Q
That's
fine,
that's
great,
so
we
can
do
it
better,
but
can
I
ask
one
question
so
do
you
think
that
in
general
the
relationship
between
human
rights
and
protocols
is
not
made
clear
or
you
think
specifically
here,
because
we
use
concretely
the
framework
from
RC
80
to
80?
And
if
you
say
that
that
is
not
clear,
then
then
that's
a
bigger
discussion
so.
W
I
think
the
framework
is
is
fine,
just
the
text
specifically
doesn't
really
give
the
connection.
At
the
end,
I
mean,
like
the
framework,
gives
you
a
structure
which
points
you
should
discuss
right
and
you
do
discuss
this
point,
but
you
don't
really
reflect
you
know.
What
is
what
is
the
impact
at
the
end,
you
just
like
kind
of
rephrasing.
The
discussion
we
already
have
in
the
working
group
without,
as
I
said,
adding
anything
from
my
point
of
view.
Okay,
so
I
think
actually
I.
W
So
for
me,
the
better
model
which
which
you're
doing
right
now
is
that
people
who
had
contributed
this
book
also
come
to
the
quick
group
and
actually
participate
in
the
discussions
and
bring
the
point
into
the
discussion
when
the
discussion
happens
right
and
it's
not
that
everybody
in
this
group
has
to
come
to
every
meeting
and
participate
in
every
discussion,
but
some
people
do
and
I
think
that
work
very
well.
So
I
think
this
is
a
very
good
interconnection
I'm,
not
sure
what
this
additional
review
actually
brings
at
the
end.
Well,.
Q
And
it's
also
a
risk
of
actually
using
the
method
of
interviews
right,
because
that
is
a
way
in
which
you
repeat
what
has
already
been
said
and
which
would
actually
explain
why
it's
relevant
for
people
outside
of
the
working
group
and
not
so
much
for
the
people
inside
of
the
working
group,
because
they've
already
been
talking
to
each
other.
So
that
might
be
a
direct
property
of
this
method
of
doing
the
review.
So
I
I
find
this
extremely
useful
you're.
So.
W
Q
True
and
but
then
the
problem
there
was,
we
had
over
100
pages
of
transcript
and
then
we
put
it
together
and
then
with
our
notes.
We
still
had
75
pages
and
then
we
knew
no
one
is
going
to
read
this
right.
So
then
we
also
started
weeding
out
and
then
a
lot
of
stuff
got
lost.
But
then
we
all
you
know.
So
it's
also.
So
it's
it's
still
trial
and
error
and
trying.
Q
R
Erica
Corolla
yeah
I
mean
I,
read
this
in
preparation
for
this
meeting.
Gonna
send
comments,
and
frankly,
it
was
just
seems
so
disconnected
from
the
actual
work
or
the
quick
working
group
that
it
just
didn't
seem
useful
to
send
comments.
Like
I
mean
the
vast
bulk
of
this
is
sort
of
like
Pressey
of
like
what
quick
does
and
a
lot
of
us
wrong.
R
Just
doesn't
seem
connected
to
like
anything
like
the
working
group
cares
about
as
like
as
comments
I
mean
you
could
say,
any
tie
a
Tetris.
If
occasionally
you
translate
it
so
like
what's
special
about
this
one.
So,
like
you
look
at
me
puzzled,
but
I
was
puzzled
by
this,
so
maybe
you
can
explain
why
your
can
be
puzzled.
No.
Q
There
are
working
groups
with
this
very
small
amount
of
people
who
maybe
do
not
have
the
resources
that
it
could
do
it
making
the
tooling
available.
The
tooling
is
available
by
people
in
the
working
group,
so
they
could
also
make
it
available.
I
think
these
are
definitely
things
that
will
be
possible
to
be
done
by
the
people
in
the
working.
Well,
it
totally
already.
R
N
R
As
a
nil,
so
I
mean
I,
guess
I'm,
just
saying
the
like.
This
is
not
a
form
of
engagement
that
is
likely
to
have
useful
impact
on
what
working
groups
do
I
want
to
echo
what
Miriah
said
the
right
way
to
do.
This
is
not
to
put
a
long
document
but
to
show
up
at
the
working
group
and,
like
specifically,
engage
with
a
working
group
on
specific
issues
and,
frankly,
do
more
generally
and
working
group.
People
will
show
up
and
have
exactly
one
hobbyhorse
and
have
real
impact.
R
E
So
Martin
Tolson
I
was
one
of
the
interviewees
for
this
one
and
someone
who
commented
about
that
process.
I
thought
for
a
group
like
this,
where
we
value
the
input
that
and
the
perspective
right.
So
this
is
the
this
is
the
perspective
that
we
don't
necessarily
get
a
lot
of
in
the
discussions
that
we're
having.
E
So
we
value
that
and
we
we
appreciate
the
fact
that
people
coming
into
this
from
this
perspective,
often
don't
have
the
depth
of
knowledge
that
that
the
participants
in
the
working
group
have
and
that's
it's
kind
of
challenging
to
come
up
to
speed.
So
the
interviews
were
a
ton
of
a
good
way
to
get
that
that
process
started
and
sort
of
bootstrap
your
understanding
of.
What's
going
on
here,
you
read
the
documents
you
talk
to
people,
maybe
read
the
documents
again,
but
as
a
process
of
finding
problems,
I
think
that's
great
I.
E
Think
the
the
end
of
this
process
is
where
we
need
a
via
tension,
and
you
got
some
feedback
on
on
the
specific
document
that
was
produced.
If
you're
looking
to
make
the
contributions,
you
I
think
it
would
be
more
valuable
to
to
simply
say
we
have
identified
the
following
things
and
now
we're
going
to
go
and
participate
in
the
working
group
on
those
almost
topics
raised.
E
This
is
intense
work
by
a
single
working
group
that
you
have
no
hope
of
participating
in
across
the
breadth
of
the
the
issues
that
we're
talking
about,
but
you
want
to
come
in
and
you
want
to
want
to
address
a
particular
problem.
So
say
the
internationalization
thing
for
the
error
messages
was
was
something
that
you
you
cared
about.
You
take
that
to
the
working
group.
You
you
start
a
thread
on
that
discussion.
You
participate
in
that
aspect
of
the
discussion.
E
That
was
their
right
yeah,
so
you
have
those
things
in
the
draft
which
is
fine,
but
you
can,
you
can
say
those
things
in
in
any
number
of
ways,
and
what
what
I
think
part
of
the
problem
here
is
that
there's
there's
a
lot
of
information
in
this
document.
This
sort
of
tries
to
cover
a
whole
bunch
of
different
things.
E
That's
it's
a
little
diffuse
where,
if
you
just
picked
the
one
thing,
we
think
that
the
documents-
fine
from
a
censorship
perspective
or
pick
a
couple
of
topics
it
would
you
can
sort
of
simplify
the
process
a
little
bit
more
rather
than
having
that
you
know
long
sections
broken
down
in
the
ADC
aidid
format
and
what
I
think
maybe
there's
there's
a
different
way
to
provide
that
feedback.
That's
all
yeah.
X
Elisa
cooper,
picking
up
on
some
of
what
the
last
three
people
said,
but
something
that
Mary
is
said
in
particular
brought
this
to
mind
so
in
the
process
of
writing.
Rfc
69
73,
the
security
area
directors
also
tried
to
set
up
a
privacy
directorate.
Basically
to
do
privacy
focused
reviews,
and
it
didn't
go
anywhere.
X
So
that's
just
kind
of
a
data
point
specifically
with
respect
to
privacy
that
we
kind
of
went
down
the
same
path
and
tried
to
do
the
same
thing,
and
it
turned
out
that
doing
the
kind
of
engagement
that
Marion
occur
and
Martin
just
talked
about.
Like
specifically
on
particular
issues.
You
know,
narrowing
in
the
focus
in
individual
working
groups
is
much
much
more
effective
than
trying
to
like
write
these
broad-based
reviews,
and
you
know,
come
in
from
the
outside
and
try
to
influence
the
work
that
way.
Thank
you.
Thank.
A
You
it's
actually
an
interesting
data
point,
because
the
last
meeting
we
got
sort
of
the
opposite.
These
things
are
useful,
so
trying
to
find
the
balance
between
those
I
think
has
become
sort
of
an
issue
from
one
time.
Thank
you.
It
helped
to
another
time.
Thank
you.
It
doesn't
help.
So
thanks
is
this.
We're
almost
I
mean
we're
really
going.
Q
So
I
think
this
is
going
to
be
extremely
useful
for
this
document,
which
describes
how
to
do
protocol
considerations
and
how
to
do
those
kind
of
reviews
once
our
idea
was
to
create
a
document
for
Human
Rights
guidelines
based
on
RFC.
Eighty
to
eighty,
as
many
of
you
know,
RFC
eighty
to
eighty
is
a
bit
of
a
bulky
document
also
because
it
was
establishing
an
idea
and
a
practice.
Q
They
made
the
idea
that
there
is
a
relationship
between
human
rights
and
protocols
and
a
practice
of
doing
providing
guidelines
for
these
reviews,
but
by
that
time
we
hadn't
done
many
reviews
yet,
and
currently
we
have
done
many
more
and
we're
there
for
what
the
document
will
be
practice
based
and
practice
oriented,
so
that
people
ideally
can
do
these
themselves
and
they
don't
even
need
us
to
participate
in
their
working
or
to
the
reviews.
So
if
we
are
useless,
that
would
be
the
perfect
outcome
of
this
document.
Q
So
what
we
have
changed
in
the
latest
version
is
that
we
tried
different
approaches
using
the
lens
of
the
guidelines.
The
lens
of
the
perceived
impact
of
the
of
the
protocol,
so
ecker
said
before
this
is
not
something
to
working
group
cares
about.
Well,
maybe
there
are
things
that
the
working
group
should
care
about,
that
it
doesn't
care
about
now.
So
that's
also
a
role
of
the
rear
of
the
review
by
looking
at
it,
not
from
the
side
of
the
developer,
but
a
side
of
the
people
impacted,
so
that
might
be
a
useful
contribution.
Q
We've
also
documented
how
we've
done
gone
ahead
with
the
expert
reviews
and
interviews
with
impacted
persons
and
our
communities,
so
that
is
stuff
that
we
have
added
so
possible.
Next
steps
will
be
definitely
be
integrating
comments
that
we've
just
received
in
a
way
that
could
help
people
make
different
decisions
about
how
to
do
a
review,
how
to
make
a
selection
and
where
to
engage
in
the
process.
Q
He
suggested
that
we
could
reformulate
the
questions
so
that
we
don't
have
such
a
mess
at
the
table,
as
we
had
before
to
ensure
that
either
all
good
answers
are
yes
and
all
bad
answers
are
no,
but
then
Corinne
mentioned.
If
you
do
that,
then
you
make
it
easier
to
skip
over
all
the
questions
to
some
ones:
I.
Just
yes!
Yes,
yes,
yes,
yes,
yes!
So
that
is
something
that
we're
still
trying
to
think
about.
Q
Q
We
could
discuss
whether
that
should
have
a
separate
heading
or
whether
that
should
actually
go
under
outcome,
transparency
or
whether
we're
actually
muddying
the
waters
of
outcome,
transparency
there
and
then
it
was
also
mentioned
that
we
should
perhaps
add
environmental
concerns,
also
because
at
a
and
RP
and
in
reason,
more
discussions
and
academic
and
popular
literature.
There
has
been
a
lot
of
discussion
about
the
impact
of
energy
consumption
on
climate
change
and
impact
of
climate
change
on
the
Internet
infrastructure
and
architecture.
Q
A
Y
A
Y
Q
Point
so
right
now
we
have
the
we
have.
This
thing
outcome,
transparency
right.
So
is
it
clear
what
your
protocol
will
change
when
it's
actually
implemented
right
right,
so
at
what
scale
is
that
meant
it's
a
little
early?
The
last
word:
I
have
no
idea
what
you
mean
so
is
like.
So
what
power
means
like,
as
in
current
or
as
in
as
in
political
power
or
as
an
economical
power
as
an
economic
concentration
or
in
relation
to
consolidation.
Y
B
Q
B
Q
Easy,
so
we've
done
that
we've
discussed
Association
and
political
both
a
lot.
What
we're
trying
to
do
is
in
reaction
to
Ted
I,
think
we're
trying
to
do
two
things.
One
thing
is:
do
work
on
very
concrete
problems
with
the
reviews,
and
one
thing
is
deepened
and
understanding
like
on
a
larger
axis.
What
is
the
relationship
but
I
think
this
relationship,
especially
in
relation
to
political
and
Association
draft?
We
discuss
a
lot.
Q
We
worked
on
this
a
lot
and
I
think
the
discussion
on
the
list
is
also
petered
out
a
bit,
so
I
think
we
should
either
go
into
publication
or
do
something
else
with
it.
So
that's
pretty
much
where
we
are
and
that's
the
same.
That's
the
same
with
Association
as
with
political
and
I
think
it
establishes
both
documents,
a
good
discussion
that
we've
had
and
it
further
expands
the
relationship
as
put
out
in
the
Charter.
Q
A
G
Lemon
I'd
really
like
to
see
some
discussion
of
the
tensions
between
rights,
because
right
now,
every
one
of
the
rights
that
you
talk
about
in
these
documents
is
stated
as
essentially
a
as
just
a
good,
in
other
words
maximizing
it
would
be
best
and
in
practice
that's
not
really
actually
the
case.
There
are
tensions
between
rights
and
so,
for
example,
freedom
of
association
has
some
serious
problems.
Q
A
G
There's
the
discussion
winds
up
being
a
denial
of
service
attack
and
it's
it's
a
bit
of
a
problem.
It's
it's
difficult
to
have
a
discussion
when
the
discussion
turns
into
a
thousand
messages
and
nobody's
really
trying
to
to
converge,
but
rather
just
trying
to
get
their
point
across
and
be
the
last
one
to
speak.
That
point:
I,
don't
know
that
that's
actually
what's
intended,
but
that's
how
it
feels
so
I.
Don't.
N
A
Discussion
about
the
discussion
and
that
and
that
could
be
entertaining
I-
have
sort
of
felt
as
a
chair
that
I've
sort
of
been
very
less
a
fair
about
it
and
let's
see
what
came
up
but
I've,
never
seen
any
of
it
sort
of
work
its
way
to
resolution
and
to
to
a
discussant
resolution,
and
it's
probably
something
we
should
try
to
do
now.
But
I
really
want
to
cut
this
discussion
on
that
one,
because
we
only
have.
U
B
That's
a
good
proposal
and
I
just
add
another
one,
which
is
that
I
think
Aubrey
and
I
as
chairs
should
just
work
with
meals
to
get
it
to
a
point
where
we
feel
like
it's
satisfied
by
looking
at
the
list
by
using
our
or
our
knowledge
and
so
to
work
with
you
more
on
unfine.
Aligning
these
meals
I
think
we
both
agree
I'm
doing
that.
Okay,.
A
The
other
one
we
had
was
we
had
a
discussion.
We
wanted
to
give
it
just
a
couple
minutes
and
we
won't
get
to
the
open
discussion
on
I
filter
on
that
discussion.
That
document
had
a
fair
amount
of
unresolved
discussion
and
I
just
wanted
to
say
in
the
beginning
that
you
know,
I
certainly
had
an
impression
that
it
was
more
of
an
engineering
suggestion
than
it
was
a
a
research
group
document,
but
I
wanted
to
give
you
a
chance
to
talk
about.
Thank
you
so
much.
A
H
Okay,
I'm
gonna,
keep
I'm
gonna,
try
and
summarize
really
briefly.
What's
going
on
the
idea
is
there
is
a
human
right
which
is
the
right
to
live,
which
many
people
are
concerned
with,
and
it
comes
about
with
the
right
of
there's
a
lot
of
tensions
between
freedom
of
speech
and,
as
I
say,
the
right
to
live.
This
is
one
of
the
biggest
problems
that
we
face,
which
is
the
dark
side
of
the
internet,
and
it
may
be
the
point.
H
Nine
nine
or
99.9999%
of
the
Internet
is
wonderful,
but
there
is
a
dark
side
and
if
we
can
briefly
turn
it
into
the
unintended
consequences
of
not
doing
anything
is
in
many
many
many
different
areas
and
we
can
have
a
further
discussion
on
it
and
a
more
contest
just
to
give
you
one.
It's
one
example
which
is
about
Isis.
Two
days
ago,
I
was
with
somebody
in
the
Indian
government,
and
he
was
saying
to
me:
I
wish
to
follow
the
rule
of
law,
but,
as
you
know,
India
we
have
a
great
problem
with
terrorism.
H
People
other
people
have
asked
me
also
is:
is
there
a
protocol
solution,
or
is
this
just
basically
a
lot
of
hot
air,
and
so
I
will
suggest
to
you
that
there
are
multiple
protocol
solutions
and
also
people
are
doing
many
things
today.
So
this
is
not
as
if
this
does
not
exist.
That
things
don't
exist
today,
but
there
are
non
transparent
efforts
to
do
this
and
and
efforts
by
multiple
governments
to
do
various
things,
private
companies
and
so
forth.
H
One
possible
solution
is
something
out
of
SFC,
which
is
basically
a
shim
that
sits
between
any
protocol
in
any
or
any
layer
in
any
other
player,
any
other
layer,
let's
say
possibly
between
the
the
IP
layer
and
TCP
layer,
and
you
put
a
metadata
type
in
there.
What
is
metadata
big
good
long
question?
How
do
you
decide
what
metadata
type
is
for
the
packet
large
question?
H
All
I'm
suggesting
is
that
there
are
potential
protocol
solutions
and
I
will
also
suggest
that
this
is
probably
the
biggest
problem
that
we
face
and
as
many
many
many
more
millions
in
India
come
online.
The
people
in
our
villages
are
not
sophisticated,
and
today,
when
there's
a
fake
video
from
someone
from
another
sect
saying
a
child
has
been
kidnapped
or
a
girl
has
been
abused,
people
are
killed
and
this
will
only
increase.
Thank
you.
Okay,.
A
Thank
you
and
one
of
the
comments
I've
got
and,
and
then
this
will
be.
The
end
of
the
meeting
is
that
the
the
document
talks
about
the
issue
in
a
general
sense,
and
but
it
also
is-
is
getting
into
the
engineering
and
and
proposing
a
solution
and
and
and
I
want
to
be
careful
about
keeping
the
the
research
on
protocol
considerations
and
is
there
something
to
be
considered
here
in
terms
of
protocol
and
consideration
without
suggesting
new
protocol
elements?
Absolutely
I
totally.
H
A
Thank
you.
We
ran
out
of
time
for
how
we're
going
to
move
forward.
I
will
try
to
take
that
to
the
list
still
have
the
blue
things
to
sign,
for
anybody
that
didn't
sign
them
and
I
want
to
thank
all
the
people
that
spoke
all
the
presentations
and
see
you
next
time
and
let's
see
if
we
can
have
the
ad-hoc
conversation
on
some
of
the
documents
that
we
talked
about
and
if
we
were
having
it
then
we'll
sort
of
let
people
know
so
that
people
can
join
in.
Thank
you.
