►
From YouTube: IETF103-V6OPS-20181105-0900
Description
V6OPS meeting session at IETF103
2018/11/05 0900
https://datatracker.ietf.org/meeting/103/proceedings/
A
B
A
B
F
F
G
B
But
is
there
any
bashing
that
people
want
to
do
to
the
agenda?
Do
I
need
to
change
the
agenda
in
any
way,
seeing
none,
okay,
so
two
questions
one
between
I,
ATF's,
101
and
102,
and
then
I,
atf,
102
and
103.
We
put
out
a
question
every
week
or
roughly
every
every
week
saying.
Let's
take
a
look
at
a
draft
and
comment
on
it.
Our
perception
is
that
that
work
has
worked
reasonably
well,
that
people
have
looked
at
the
drafts.
B
They've
found
the
load
acceptable
and
we've
gotten
comments
on
a
variety
of
drafts
and
in
at
least
one
case,
we
discovered
that
their
working
group
wanted
to
adopt
a
draft
and
we
hadn't
figured
that
out,
and
so
that
became
clear
and
we
adopted
a
draft
but
I'd
like
your
opinion,
because
I
I've
just
gotten
kind
of
a
few
comments
here
and
there
as
a
working
group.
What
do
you
think
about
that
process?
Is
that
working
for?
You
is
that
helpful.
Is
that
something
you
want
to
do.
B
C
C
H
C
H
C
I
I
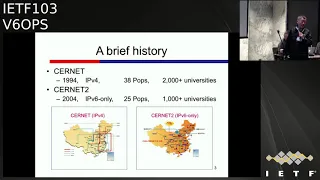
Currently
we
have
38
hops
and
about
more
than
2,000
the
universities
and
another
project
has
started
in
the
year
204,
which
is
called
Serna
to
actually
the
interests
is
seeing
is
here.
It
is
ipv6
only
studying
from
to
all
four
and
the
currently.
There
are
25
hops
and
about
1,000
the
university's
connected.
So
you
can
see
they're
separate
backbones
and
the
highway
starts
ernet
to
design.
Then,
actually
there
several
questions
we
asked
ourselves.
I
The
first
should
we
start
using
do
stack
our
ipv6
only
and
the
decision
is
ipv6
only
in
204
I
will
give
you
reasons
later
and
also
we
have
some
kind
of
promotion
strategy.
Basically,
it's
high
performance
in
there
free
another.
Another
thing
is
the
security
because
ipv4
their
nets
and
we
sought
the
ipv6,
because
there
is
no
net
six
six
then
properly.
We
can
restart
the
end-to-end
security
and
that's
the
thing
we
caught
salsa
address,
validation,
architecture
and
we
work
in
IETF.
I
I
Actually,
even
we
are
academic
network,
but
we
do
not
have
operation
fees
from
the
government
at
the
university
professors
in
the
students
pay
the
connection
fee.
So
that's
some
kind
of
sharing
model,
so
ipv4
is
not
free,
Anderson
I
to
ipv6
Tinley,
it
is
free.
So
actually
was
the
promotion
slogan
we
told
to
our
members
is:
if
you
want
use
free
and
high
performance
network,
then
please
use
ipv6.
So
that's
the
way
we
promote
from
the
beginning
and
tell
you
the
truth.
I
However,
in
reality
we
sought
can
we
turn
off
sir
net
ipv4
for
a
single
day
and
the
see
if
the
users
still
satisfied
with
our
network
and
service?
No,
so
the
users
need
to
communicate
with
the
ipv4
internet.
Even
the
network
is
somehow
congested
and
the
not
free.
So
that's
why
we
move
in
this
direction
and
the
solar
sings.
That's
a
summary
for
security
as
Sabah
and
the
Saudis
asada
are
cease
related
in
in
the
savvy
working
group,
mostly
savvy
working
group
and
ok
for
sir
net
some
tempers
networks.
I
Actually
we
actually
deploy
savvy
technology
so
make
the
sauce
trace
possible
and
the
most
secure,
so
that's
C
and
the
for
transition.
Actually,
that's
a
brief
history,
starting
from
1994,
that's
ipv4,
sir
net
and
the
in
the
year
1998.
Actually
we
start
to
connect
to
six
pool
and
that's
ipv6
over
ipv4.
The
reason
we
realize
we
need
to
work
on
IP
v6
is
in
China
email
in
China.
They
are
320
million
students.
I
Definitely
we
cannot
get
enough
ipv4
just
from
a
beanie
and
they
in
the
year
2000
we
tried
you
stack,
which
is
called
Natural,
Science,
Foundation,
Network
and
the
later,
as
I
mentioned
earlier
in
200
we
start
ipv6-only
signature.
Then
we
thought
we
can
do
innovation
so
as
ipv4
over
ipv6,
because
as
ipv6
only
backbone.
That's
turning
to
the
ITF
software
working
group
and
the
later
we
work
in
the
behaved
working
group.
I
That's
translation,
Staley's
translation
and
we
call
avi
because
in
Roman
replantation
IV
means
4
v
I
mean
six,
so
I
by
actually
means
four
and
the
six
can
talk
and
the
later
we
realize
there
is
some
application,
embed,
ipv4
literals
and
some
applications
ipv4
only
so
we
saw
two
probably
can
do
double
translations.
So
that's
the
boy
that
we
call
that
and
because
it's
something
for
64
issues
and
by
that
time,
actually
behaved
working
group
clothes
that
he
cleared
of
victory.
I
So
we
move
back
to
the
software
and
then
later
we
realize
actually
double
translation
and
they
in
cabaret.
She
is
something
quite
similar,
so
that's
into
the
outcome,
after
RFC
SMAP,
t
and
map.
So
that's
the
story
for
our
experience,
so
those
other
related
RFC's
and
the
for
single
translation
in
the
ipv4
as
a
service
actually
color
mark
the
blue
are
the
RFC's.
Actually
we
deployed
in
the
siRNA
to
backbone.
So
that's
basically
the
same.
So
currently
that's
the
situation.
We
have
two
backbones
cern
at
ipv4
and
the
siRNA
to
ipv6.
I
I
Trafficking,
one
direction
can
go
back
to
the
other
address
family
in
another
year:
translator
because
it's
tailless
just
like
in
a
BGP,
lo,
the
balancing
states
and
then
actually,
we
have
ipv6
only
servers
distributed
in
different
universities
who
connected
to
Sena
to
also
their
ipv6.
Only
clients
are
ipv4
as
a
service
clients
distributed
in
different
universities,
wire
second
translators.
I
So
the
the
first
translator
or
the
core
translator
are
the
same
Staley's
one-to-one
mapping
between
before
and
the
v6
and
the
depending
on
the
the
hosts
are
and
the
systems
either
as
a
single
translation
or
double
translation,
or
even
some
kind
of
encapsulation
or
not
in
this
case,
no
interpretation,
just
the
translation.
So
there
that's
the
same
and
okay
again
talk
a
little
bit
of
backbone
because
so
near
to
is
a
ipv6
only
backbone.
So
certain
Aitu
has
its
own
address
blocks,
lat,
/
32
and
the
some
converts
networks
have
their
own
provider.
I
Independent
ipv6
address
block
so
BGP
connected
to
those
universities
and
if
inside
the
/,
32
sir
netted,
then
that's
static
route
and
the
link
speed
is
2.5
g
Kenji
and
100
G
IDPs,
OSPF,
purchaser
and
the
BGP.
That's
IBT
PAE,
BGP
whatever
and
then
another
thing
I'd
like
to
mention
is
multicast.
We
run
SSM
in
the
sauna
backbone
and
actually
the
restriction
is
the
user
cannot
use
their
own
/
48
as
the
SSL
sauce,
but
instead
we
assign
a
special
as
the
sausages
of
SSM.
That's
a
better
security
control.
Another
thing
is
the
unicast.
I
Actually,
the
routing
accepted
link
change
of
those
kinds
of
his
static.
However
multicast
it's
depending
on
the
join
the
situation
as
install
that
route
are
not
install
and
that
make
security
and
the
scalability
or
whatever
performance
is
some
kind
of
disaster,
so
actually
because
as
SSM,
so
it's
predefined,
so
we
have
static,
join
for
the
groups,
so
the
whole
sir
net
to
back
boom
ipv6
SS
is
static,
not
a
dynamic
for
multicast.
So
that's
the
same
and
further.
I
So
we
try
to
define
some
kind
of
controller
to
control
the
prefix
so
make
some
kind
of
Sdn
drive
and
for
the
first
hub
or
for
the
end
users
as
DLC,
p,
ra
and
sorry.
So
that's
basically
the
structure
in
the
backbone
and
the
ipv6
only
servers.
So
actually
we
deploy
ipv6.
Only
servers
with
the
ipv6
address
is
based
on
RFC
60
50,
so
the
ipv4
address
directly
embedded
into
ipv6
address.
I
So
if
the
the
user
connected
to
this
server
using
ipv6
that's
connected
directly,
if
that
so
ipv4,
actually
that
the
user
sees
the
ipv4
address
but
actually
is
translate
to
that
ipv6
and
because
it's
stainless
so
actually
we
is
more
people.
Translators
can
be
used
to
do
load.
Balancing
of
those
can
see-
and
so
currently
we
have
four
10g
translators
as
all
can
cast
it,
but
the
performance
still
relatively:
ok,
ok
and
the
ipv6
only
clients,
that's
the
interesting,
say:
ok
for
the
partial
function.
I
Ok,
that
means
if
your
application
is
ipv6
and
no
ipv4
letters
embedded
into
that,
then
actually
support
a
lot
of
operating
systems
and
the
last
th
CPV.
Ok,
ok,
I,
repeat
again:
for
the
clients,
there
are
two
kinds
of
clients:
wine
clients
can
support.
The
dhcpv6
stateful,
except
Android.
Most
of
the
operating
system
can
do
that.
Another
is
the
cannot
support
IP
dhcpv6,
that's
mainly
Android
in
Windows
XP,
for
example.
So
so
those
two
things
and
we
have
two
SSIDs
or
Wireless.
I
Why
is
for
is
the
pv6
state
for
another-
is
in
C
just
are
a
switch
the
rbass,
so
that's
the
ipv6
on
it.
That's
the
one
dear
he
mentioned
to
look
at
the
problem.
Another
direction
is
ok
if,
for
example,
the
iOS
and
Android
with
464xlat
they're,
actually
even
their
ipv4
later
O's
embedded
our
IP,
then
still
you
can
use
that.
So
this
we
call
the
full
function.
B
J
My
my
point
is:
that
is
not
that
simple
as
that,
when,
when
you
say
a
network
is
ipv6
only
if
there
is
some
ipv4
function,
even
if
he's
at
the
end
of
the
upstreams,
let's
say
you
are
translating
so
that
network
is
not
ipv6
only.
My
my
my
my
belief
is
that
we
need
to
start
speaking
about
when
we
say
ipv6
only
with
specific
part
of
the
network.
We
are
talking
about
it's
the
lands.
It's
the
access
is
the
core.
I
I
agree:
okay,
actually
here
I
mention
I,
think
v6
at
least
ipv6
only
subnet.
It
says
answer
your
question
right,
so
ipv6
only
subnet,
okay,
actually
a
little
bit
more
complicated,
that's
to
the
subnet
side
and
the
truth
application
said.
Actually
there
are
two
cases,
for
example,
iOS
as
single
translation,
so
to
the
application.
Socket
is
still
ipv6
only,
however,
for
enjoyed
that
the
probably
four
six
four
X
later
actually
to
the
socket
function.
That's
use
that,
however,
the
sub
thank
you
and
analysis
for
legacy.
Yes,
one.
K
K
I
Thank
you:
okay,
like
okay,
four,
six,
four
X
ladies
deployed
in
the
operating
systems.
If
for
the
legacy,
applications
are
owed,
OS,
which
is
ipv4
only
then
actually
we
deploy
a
translator
in
the
same
second
translator,
so
that
subnet
is
use
that,
however,
the
upper
stream,
so
that's
another
se
and
friendly
speaking
actually
at
our
campus
networks,
we
have
two
SSIDs.
Why
is
IP
V
still
only
subnet
another?
Is
you
stack
subnet,
however?
The
upper
stream
Arkham's
ipv6
only.
I
Okay,
another
thing
actually
type
II,
so
actually
this
is
also
ipv4
as
a
service,
so
the
upper
stream
is
ipv6
only
but
the
subnet
is
you
stack
and
then
the
same.
Actually,
this
friday
is
for
high
performance
computing
ipv4
as
a
service,
and
actually
you
may
know
there
are
some
top
super
computers
located
being
russia
city,
like
jump
supremacy
in
china,
middle
of
China
China.
However,
some
university,
for
example,
my
University,
the
bio
research
center
use
that
computational
facility
and
that
the
data
is
about
like
one
tea
per
day
or
those
kind
of
see.
I
So
actually
we
use
double
translation
to
provide
this
kind
of
service.
The
reason
for
that
is
actually
in
this
case
the
ipv4
address,
is
private,
address,
not
the
public.
Yes,
so
that
means
404
to
build
a
VPN.
So
that's
situation
and
the
the
consideration
for
this
is,
and
the
network
can
be
fine-tuned
using
ipv6
prefix
so
that
those
ipv4
the
physics
prophets
can
be
put
into
a
higher
priority
through
traffic
engineering,
so
more
flexible
in
the
controllable
than
ipv4
PDP
and
the
more
cost
effective
than
MPLS
and
then-
and
there
were
network
operation.
I
Amendments
very
simple
and
to
end
address
transparency,
no
in
calculation
decapitation
is
required
a
for
example.
If
the
network
operator
try
to
take
the
traffic
and
reducing
if
it's
in
calculation,
eternally,
then
the
first
IP
address
you'll
see
is
the
eternal
address
not
end-user.
Yes,
however,
for
double
translation,
the
ipv6
address
in
bad
before
so
you'll
see
different
end
user
has
different
addresses
and
the
no
need
to
activate
application
at
this
stage,
so
the
user
still
use
ipv4
as
the
application,
and
one
thing
quite
interesting
for
us
is
the
different
charging
model
can
be
applied.
I
Why
are
you
friend
I
pv
6
previous?
So
because
I
mentioned
earlier,
they
you
professors,
sharing
I,
mean
paid
the
fees
for
using
the
internet.
However,
for
this,
what
actually
they
can
have
unlimited
usage
and
that
also
make
the
tempers
network
administrator
life
is
much
easier.
So
there
are
some
interesting
discussion
since
that's
our
observe
the
filly
for
ipv4
as
a
service,
either
use
inhabitable,
Asia,
double
translation
and
the
way
play.
We
prefer
the
bow
translation,
because
the
turbo
translation
can
reduce
to
single
translation
and
eventually
as
ipv6.
I
Only,
however,
in
Kappa
later
you
need
to
keep
two
points
and
also
the
traffic
engineering,
as
I
mentioned,
I
have
a
thicker
meter
to
show
that
and
a
second,
the
staleys
are
stateful,
because
stainless
can
restart
entry
and
address
transparency
and
there's
much
more
easier
for
scalability
as
skill.
So,
if
possible,
try
stainless
and
the
RFC
1650
to
address
all
other
mapping
abuse
and
the
way
belief
there,
the
IDC
map,
you
know
those
kind
see
we
believe
we
should
make
the
the
why
the
people
take
a
look
at
the
wire
know.
I
What's
the
IP
before
literacy
bed
is
so
make
it
as
transparent
as
possible
and
the
same
crate,
ipv6
prefix
for
the
sauce
in
the
destination
or
befriend
ipv6
address
in
RFC
1652?
Actually,
it
says
you
should
use.
You
should
use
the
same
prefix
and,
however,
that
can
retail
okay
actually
same
prefix
can
result
in
the
optimal
route
him.
However,
if
you
have
two
administrative
domains,
then
probably
the
only
choice
use
different
of
prefix
and
finally
for
the
clients
here,
CP
v6r
snack.
I
Actually,
we
like
dhcpv6,
unfortunately
enjoy
the
cannot
support
us.
So
we
have
not
no
choice.
We
need
to
support
slack,
so
there
are
some
reasons
right,
because
this
is
quite
interesting
from
I.
Can
the
ipv6
address
protector
and
the
GPD
and
me
you
can
see
the
high
GDP
our
demand
countries.
Ipv6
is
quite
good,
however,
for
the
last
about
put
our
developing
countries,
there
is
no
ipv6.
I
So
probably
the
ipv4
exists
for
details
on
many
details
and
if
we
want
eventually
get
an
ipv6
only
then
we
need
to
deploy
translator
in
some
place
of
the
Internet
to
keep
a
single
engine
and
well.
This
is
actually
I
said
in
the
wire.
The
operator
can
take.
Look
at
the
ipv6
address
without
a
declaration
to
do
a
CR
or
traffic
control
rate
limiting.
However,
if
that's
turning
in
technology,
you
can
not
do
that
directly
using
the
existing.
So
you
have
to
do
the
calculation
and
they
make
sure
the
traffic.
I
You
give
me
all
the
traffic
in
that
provided
by
that
Turner
point
also,
the
end
window
just
transpose
I
mentioned
so
on
the
wire
we
know
across
the
ipv4
address,
embedded
that
we
can
do
a
better
and
that's
the
optimal
routing.
So
if
it's
the
same
prefix,
then
no
matter
the
ipv4
is
used
in
ipv6
or
I.
Translate
it
in
ipv6
are
in
original
no
problem.
The
longer
is
the
prefix
match
to
automatically
redirect
your
traffic
into
the
right
place.
I
However,
if
different
projects,
then
you
need
to
do
whatever
here
being
all
those
kind
of
seeds
and
though
I
could
certainly
support,
as
I
mentioned,
the
full
function
so
for
for
iOS,
9.2
and
above
in
the
Mac
OS
10
point
13
above
in
the
464xlat
Android.
Actually,
that's
quite
quite
good,
like
originally
for
six
for
explained,
supported
the
LTE
interface,
but
currently
about
6.0.
The
W
dentists,
support
soils
very
good
and
now
I
heard
the
Windows
10
can
support.
However,
the
Home
Edition
we
try
to
have
not,
but
eventually
that.
L
I
Supported
that's
a
very
good
news.
However,
one
thing
is:
if
you
want
sled,
you
have
to
be
very
careful
because
Windows
7
cannot
support
our
DSS.
That's
the
problem.
I
don't
know,
Microsoft
can
have
upgrades
attack
attached.
That
will
be
great.
So
finally,
because
our
theory
is
IP
pics
only
with
single
translation,
if
you
can
ipv4
as
a
service
with
double
translation
information,
if
you
should
and
the
do
step
and
if
you
must
and
the
way
to
ipv6
only
as
for
as
a
service
ipv6
only
with
single
translation
and
they
eventually
ipv6
only
so.
M
I
I
Actually,
that's
that's
a
very
good
question.
We
actually
prefer
some
kind
of
Spanish
translation.
So
if
we
want
to
use
just
representation
defined
in
like
map
t,
then
actually
we
can
not
use
the
slash
36
in
that
case.
Actually
the
compromise
is
the
salsa.
Yes,
that's
the
map,
t
format.
However,
it's
the
nature
of
gasses
laughs
so.
I
N
N
I
N
There's
a
draft
in
six-man
later
a
little
later
this
week,
we're
presenting
the
reason
for
not
supporting
it
is
that
it
would
make
the
option
50%
bigger
in
the
RA
there's
no
space
for
prefix
length
if
you
want
it
to
fit
in
16
bytes,
and
so
maybe
you
want
to
might
want
to
comment
on
that,
because
we're
not
aware
of
any
implementation
that
supports
it
actually
I
think
the
iOS
implementation
does
support
it.
Did
you
did
you?
Did
you
verify
that
I
OS
supports
non
/,
96
yeah?
It
does
no.
I
B
Well,
not
shingling.
Let
me
comment
on
that
when
you
started
building
ivi,
which
was
2008.
Something
like
that.
Your
argument
for
the
way
you
structured
the
address
was
that
you
wanted
to
straddle
the
ipv4
address
across
bit,
64,
so
that
you
could
use
ipv6
routing
to
take
traffic
to
different
places
and
have
multiple
hosts
in
a
given
place.
But
but
basically
it
became
a
routing
game.
Are
you
still
doing
that
in
ivi
yeah?
Yes,.
I
O
B
J
So
that's
that's
what
we
have
at
the
document
today
across
the
different
versions
of
the
document.
I
got
sometimes
questions
like
if
the
document
is
just
talking
about
NASA
64
as
a
preferred
transition
mechanism
that
that's
not
the
thing.
What
I
am
NOT
suggesting
in
the
document
is.
This
is
the
way
to
go.
What
I
am
saying
is:
if
you
already
decided
to
go
to
not
64,
then
this
is
the
way
you
can
deploy
it,
not
not
just
to
discussion.
J
That's
another
question
I
got
frequently
is
not
just
a
discussion
about
God
are
the
things
that
dns64
breaks
with
the
intersect,
it's
one
of
the
important
things,
but
it's
not
the
only
one
okay.
So
the
starting
point
for
the
document
is.
There
are
three
main
issues
which
deploying
necessity
for
one
of
one
of
those
is,
if
you
are
using
the
unassisted
for
it,
may
break
the
intersect.
J
J
There
are
applications
that
use
literals
or
api's
that,
of
course,
they
are
not
going
to
work
on
that
situation
and,
of
course,
if
you
happen
at
work
with
just
not
64
and
you
have
still
all
devices
or
applications
that
use
IP
before
only
they
will
not
work.
So
that's
that's
meaning
that
in
some
scenarios
you
cannot
just
survive
with
nat64
alone
right.
J
When
the
DNS
system
for
document
was
published,
there
were
a
few
scenarios,
work
it
out
in
that
document
and
from
the
perspective
of
an
operator
today,
I
believe
there
are
much
more
scenarios
and
I
have
done
a
classification
of
those
scenarios
in
a
scenarios
that
are
known
to
work
and
those
that
will
work
only
in
a
special
circumstances
which
are
still
valid,
but
not
the
generic
case.
So
for
the
scenarios
not
to
work,
there
are
for
possible
scenarios
or
super
scenarios
where
you
have
an
internal
or
outsourced
nat64.
J
Dns64
combination.
Okay,
so
that's
that's
the
first
set
of
a
scenarios.
Then
there
are
three
additional
scenarios
where
you
are
using
for
six
Forex
lat
and
either
you
have
an
internal
or
obtuseness
sista
for
dns64
combination
and
then
two
more
possible
super
scenarios
where
you
have
four
six
Forex
lat,
but
in
this
case,
without
using
DNS
64
and
again,
you
have
the
necessity
for
functionality
inside
the
network
or
outside
the
network
known
to
work
in
a
special
circumstances.
J
There
is
when
a
scenario
which
is
not
64
without
dns64,
another
scenario
which
is
dns64
in
the
ipv6
host,
which
is
something
that
more
and
more
operating
systems
are
already
including.
So
it's
it's
something
that
maybe
today
is
not
the
optimal
situation,
but
it
may
change
in
the
future,
and
then
service
provider
with
the
NAT
64
and
the
dns64
is
in
the
remote
only
network.
J
It
seems
that
this
this
scenario
don't
makes
too
much
sense,
because
if
you
have
at
the
NS
64
in
the
remote
network,
they
logic
thing
is
to
have
actually
those
remote
that
remote
network
is
already
a
pv6
right,
but
it
may
happen.
I
am
trying
to
do
a
very
quick
comparison
about
these
twelve
scenarios.
At
the
end
we
come
to
12,000
areas,
and
this
compression
is
based
in
four
specific
questions.
The
first
one
is:
are
the
hosts
in
that
network
validating
the
intersect?
The
second
one
is:
are
the
hosts
using
literal
or
api's?
J
The
third
one
is:
there
are
any
ipv4
on
the
hosts
and
the
last
one
is
any
chance.
The
user
can
change.
The
DNS
I
call
this
foreign
dns,
because
that
may
break
some
things
that
the
operator
is
considering.
So,
for
example,
if
the
operator
is
providing
a
dns64,
but
the
user
is
changing
the
DNS,
then
of
course
the
DNS
system
for
function
is
not
working.
J
J
Discussing
one
of
the
possibilities
is
not
using
a
dns64.
The
other
one
is
the
dns
evaluator
aware
of
dns64
estoppel
editors
silat
with
DNS
proxy
and
validator
ACL
of
clients,
mapping
out
ipv4
addresses
and
then
considerations
regarding
dns,
reverse
mapping,
then
the
usage
of
forces
for
X,
let
which
or
without
the
end
of
64
explaining
what
are
the
differences
of
one
case
and
the
other
a
manual
configuration
of
pouring
the
DNS
again,
is
when
the
user
is
able
to
change
the
DNS
configuration.
J
So
that
means
that
the
DNS
functionality
is
not
under
the
control
of
the
operator
anymore,
DNS
privacy,
because
that's
another
thing
that
get
broken
when
you
are
using
DNS
64
together
with
privacy,
you
are
not
controlling
using
the
DNS
system
for
probably
a
split
DNS.
It's
another
possible
case
where
the
dns64
may
be
not
working
comparison
between
using
a
well-known
prefix
or
a
specific
network.
J
If
you
are
an
enterprise
headquarter,
you
are
trying
to
use
nat64
in
that
network,
so
basically
it
makes
no
difference
and
then
it
was
I
think
it
was
suggested
by
my
fret
to
include
an
example
of
broadband
deployment
which
forces
Forex,
lat
and
also
seal
at
implementation
and
I'm,
not
really
sure
that
that
will
be
possible.
But
there
was
also
suggesting
a
suggestion
to
include
some
benchmarking
and
I.
J
Think
that
was
that
was
it
so
questions,
because
one
of
the
problems
I
I
am
having
is
that,
since
probably
two
months
or
so,
I
am
NOT
getting
inputs
for
the
document?
So
even
if
this
document
was
adopted,
as
a
working
group
item
is
still
useful,
is
somebody
interested
in
contributing
or
saying
something?
I
don't
know?
Jenn.
P
In
one
scenario,
for
example,
saying
you
have
not
six
four,
you
have
dinner
six
four
and
it
really
doesn't
matter
where
dns64
is
located
because
I
think
currently
it's
a
few
different
scenarios,
which
makes
the
document
probably
way
too
long,
because
I
actually
was
struggling
finish
and
originate
because
I
found
too
many
similar
scenarios
and
you
need
to
sit
down
what's
the
difference
between
them.
Actually,
so
it
would
be
my
suggestion
to
scientific
to
see
if
you
can
slightly
simplified.
P
Also
margin
from
NICTA
said
just
recently
did
more
measurements
on
dns64
and
ipv6,
similar
to
what
I
did
a
couple
of
years
ago
and
percent
they
look
quite
similar.
I
can
send
you
link,
but
it's
not
in
unfortunately,
the
same
I
need
to
use.
Google,
Translate,
sorry,
I,
said
consumer
format.
Again,
as
I
said,
my
suggestion
would
be
to
review
how
you
make
it
more
readable
at.
J
The
beginning
I
was
used,
I
was
having
lesser
scenarios
and
actually
I
got
the
input
that
I
should
describe
more
more
of
them
there.
The
reality
is
that
I
agree.
There
are
some
scenarios
which
are
very
similar,
but
this
is
not
actually
making
the
document
longer,
because
if
you
look
at
the
length
of
that
part
is
because
the
pictures-
so
it's
not
like
you-
need
to
read
a
lot
of
more
things
is
because
each
picture
they
have
four
page.
J
Okay,
so
I,
don't
think
that's
increasing
the
complexity
of
the
document,
but
I
thing
is
providing
clarity.
If
you
see
a
picture,
it's
very
easy.
You
don't
need
to
read
the
text,
because
the
text
is
basically
not
saying
anything
different,
but
you
have
been
one
case,
for
example,
four
scenarios
and
looking
at
the
picture,
you
get
the
idea
about
all
of
them
and
then
the
text
says
all
these
four
are
the
same.
Okay,.
P
J
Can't
take
a
look
again
and
try
to
squeeze
a
little
bit
the
text,
but
for
clarity,
I
think
it
was
that
way,
and
that
goes
the
suggestion.
I
got
before
so
so.
I
agree,
we'll
have
different
views
and
some
people
will
say
it's
too
long
and
some
others
will
say
is
too
short.
Please
terrify
it
and
some
people
were
suggesting
even
additional
scenarios,
which
I
don't
think
we
need.
We
need
them
right.
B
H
J
B
So
it
sounds
like
we're
really
not
ready
to
close
up
on
this
documents
until
you
get
Jen
to
review-
and
you
know
whatever
comes
out
of
that,
so
what
I'll
do
is
in
in
our
list
of
documents
going
forward,
then
I'll
ask
for
people
to
comment
on
the
document.
So
it's
again,
your
review
will
be
very
helpful.
J
J
So
what
what
happened
here
is
this
document
is
started
as
two
different
documents.
The
older
one
is
is
the
sunset
ipv6
document.
Unfortunately,
there
were
very
very
few
comments
on
that
document
and
then
sunset
is
sleeping.
So
so
there
is
nothing
to
do
that
and
and
Cameron
from
D
Mobile
was
sending
another
document
and
I
think
it
was
somehow
fretful
that
fred
was
suggesting
to
merge.
Cameron
document
with
the
previous
document
I
have
presented,
and
my
comment
was:
no,
it
don't
make
sense.
J
I
mean
those
two
documents
don't
work
together,
but
then
I
realized
that
the
ideal
thing
will
be
to
match
these
two
documents
and
I
talked
it
to
Cameron
and
he
agreed.
So
we
drafted
a
document
which,
basically
saying
hey
dns64
is
while
you
deploy
it
for
six,
for
ex-lap
is
quite
the
deploy.
Yet
we
have
also
support
for
dns64
in
happy
eyeballs.
We
have
also
not
sixty-four
widely
deploy
it,
especially
in
cellular
networks.
J
There
are
million
of
costs
using
those
mekinese
and
what
happens
is
that
horse
validating
dns
act
may
fail
the
same
command.
I
I
did
before
it's
true
that
most
of
the
server
networks,
the
the
smartphones,
are
not
validating,
I
think
they
have
functions
that
can
be
call
it
by
applications
to
validate,
or
that
can
happen
in
the
future,
but
today
is
not
used,
but
what
happens
when
you
are
doing
tethering
and
there
are
horse
behinds
that
may
be
validating,
so
it's
still
a
problem.
J
So
why
not
try
to
find
a
way
for
content
or
application
providers
to
carry
at
least
part
of
the
cost?
Okay,
the
thing
is:
if
they
have
the
technical
of
to
do
the
intersect,
they
should
have
as
well
the
technical
ability
to
do
ipv6,
so
that
will
solve
the
problem.
Clearly,
if
we
have
ipv6
in
every
DNS
SEC
horse,
we
don't
have
dns64
breaking
anymore
that
functionality
right.
J
So
the
thing
we
are
trying
is
to
find
a
way
to
push
the
application
or
service
or
content
providers
to
to
deploy
ipv6
if
they
are
deploying
the
intersect.
That's
the
first
thing
and
then
indirectly,
to
assume
part
of
the
transition
cost
as
well
and
find
a
way
to
get
them
clear
signals
that
this
should
be
provided.
They
should
really
make
an
effort
on
this.
That's
that's
the
thing.
J
So
what
we
want
to
men,
which
ipv6
ready,
is
that
ipv6
is
accessible,
that
there
are
quite
a
rare
resource
records
that
pm-2
is
not
broken
and
so
on,
so
that
that's
that's
easy,
so
we
are
trying
to
define
a
time
line
to
make
this
happen
and
the
time
line
is
root
until
this,
and
we
know
that
most
of
them
are
already
done.
Roots
are
done
already,
TLDs
I
think
99
per
second
of
the
CCT.
J
J
It's
this
an
auto
P
I,
don't
know,
but
clearly
there
is
a
contract
which
I
can.
That
is
not
big,
follow
it
and
yes,
we
are
ITF.
We
are
responsible
of
the
numbers,
so
somehow
we
are
indirectly
responsible
that
this
is
happening
or
not
right
and
there
is
clearly
some
kind
of
infrastructure
or
liaison
or
whatever,
which
icon
that
we
should
work
together.
J
Q
Jordi,
its
yep
dan,
you
work
I
spent
some
time
before
when
I
was
in
more
of
an
ipv6
advocacy
role
and
I
was
very
excited
when
that
contract
that
you're,
referring
to
it's
the
registry
agreement.
But
the
detail
is
that
only
applied
to
the
new
gTLDs.
It
did
not
apply
to
any
of
the
country,
code,
TLDs,
etc.
So
I
think,
and
most
of
all
of
the
new
gTLDs
are
ipv6
because
they
had
to
be
in
in
order
to
be
launched.
The
I
can
process.
So
that
was
so.
Q
J
Q
J
Q
I
would
encourage
you
to
do
that.
I
will
admit.
I
haven't
been
following
as
much
here,
but
I
have
been
over
there
and
I
think
that
would
be
useful
to
provide
that
input
to.
But
the
other
part,
when
you
ask
about
DNS
SEC
and
saying
that
you
know
so,
I
agree
with
the
goal
right,
yeah
but
I
think
from
an
implementation
point
of
view,
I'm
not
going
to
necessarily
sign
any
quad-a
records
if
I
don't
have
them.
J
S
The
problem
is
the
the
assumption
you're
making
assumption
here
that
if
you
can
do
dns
sick,
you
can
also
do
ipv6
and
once
you
down
a
little
beneath
the
tail
days
to
the
actual
enterprise
that
isn't
true,
it
is
not
true,
to
a
large
extent,
to
do
DNA
sick.
All
you
have
to
do
is
to
deploy
a
name
server
which
supports
it
and
register
your
keys
in
the
pair
exam.
S
S
So
anything
which
actually
get
which
actually
slows
down
DNS
SEC
deployment
by
getting
it
on
ipv6
being
deployed,
is
actually
a
bad
idea,
the
DNS
SEC,
which
is
why
this
craft
this
as
a
recommendation.
You
should
do
this
yeah,
it's
it's
all
good
motherhood
stuff,
but
in
practice
it
guess
what
happened
so.
S
O
Paul
Wilson
here
for
maybe
Nick
very
recent
discussions
with
ICANN
senior
folks
showed
that
though
they
are
very
interested
in
this.
They
are
aware
that
there's
a
lack
of
compliance
in
the
support
that
they're
expecting
for
ipv6
functionality
to
be
provided,
but
one
of
the
things,
for
instance
that
they're
after
is
that
their
registrar's
should
simply
provide
the
interface
that
allows
domain
holders
who
have
ipv6
to
to
register
that
it
into
the
inter
DNS.
So
I
think.
O
J
C
P
So
if
we
think
that
the
dimension
of
the
maiden
Claes
that
the
problem
is
a
Dennis
operators,
do
not
really
understand
the
impact
of
having
dinner
check,
enabled
without
the
ability,
v6
then
I
agree,
we
need
to
educate
them.
So
probably
so,
I
really
like
the
first
draft,
which
was
just
saying
if
you
deploy
it
in
a
silk,
you
should
think
about
the
impact.
You
should
be
aware,
as
that
some
people
might
have
issues
accessing
your
record.
So
please
consider
an
event
ipv6,
that's
the
right
thing
to
do.
P
However,
what
your
draft
is
currently
said
is
that
your
suggestion
to
invent
a
magic
wand
which
will
get
ipv6
deployed
global
in
18
months
and
I
just
do
not
believe
it's
feasible.
So
basically
what
your
suggestion
I
could
not
see
how
it
could
be
implemented.
It's
I
just
do
not
see
implementation,
details
and
I
think
you
basically
suggested
something
which
is
not
feasible,
so
I
do
not
think
we
should
be
enforcing
this,
because
there
are
countries
which
do
not
have
v6
at
all.
People
who
have
sides
there.
P
Q
Second
Dan,
you
work
it
just
one
comment
the
mark
led
onto
it.
I
think
you
are
off
on
the
idea
that
somebody
who
has
DNS
expertise
is
also.
If
they
have
that
technical
expertise,
then
they
could
do
ipv6
because
to
Mark's
point
you
know,
activating
DNS
SEC
on
a
zone
is
really
just
a
matter
of
maybe
uncommenting
a
line
in
one
of
the
config
files
or
doing
something
like
that
and
so
boom.
You
do
that
and
it's
on
and
now
you're
signing
all
of
your
zones,
depending
upon
which
of
the
various
different,
authoritative
service
you're.
Q
Using
so
that's
I
mean
a
very
basic
thing
that
you're
done
versus
trying
to
get
ipv6,
transit
and
ipv6
routing
and
everything
else
and
firewalls
and
all
that
configured.
So
it's
a
different
technical
set,
so
I
would
not
make
that
assumption
in
there
too,
to
Paul's
plan
I
think
there
are
people
within
ICANN
and
in
NSR,
C
and
other
folks
who
are
out
there
working
on
ipv6
issues,
who
you
would
talk
to
I.
Don't
know
that
Ayana
has
any
role
in
that
type
of
thing
with
that,
but
I
can
would
be
the
folks
item.
B
B
J
B
So
are
there
any
other
things
that
I
should
be
pulling
out
at
this
site?
Those
are
the
two
points
that
I'm
pulling
out
at
them.
Okay,
so
I
have
one
other
question.
During
the
discussion
a
few
months
ago
on
Cameron's
document,
there
were
several
people
who
said
that
they
shot
thought
his
document
should
go
to
BC
P.
So
let
me
ask
the
working
group.
If
those
changes
are
made
in
this
document,
do
you
want
to
take
it
to
bc
p
question
for
the
group?
If
that's
a
direction,
you
think
it
should
go.
T
J
Okay,
so
what
we
are
trying
to
do
to
address
here
is
the
perception
of
many
ISPs
read
the
677
as
something
which
is
not
very,
very
clear,
so
I
decided
to
speak
with
the
outers
of
that
document
and
try
to
see
they
going
to
get
involved
in
this
version
and
I
think
we
didn't
get
a
response
from
Thomas,
Martin
and
Jeff
said:
I
am
NOT
interested
at
this
stage
and
then
leader
over
said.
Yes,
let's
work
on
that,
because
she
has
the
same
perception.
J
J
J
So
let's
make
make
sure
that
we
fix
this
document,
especially
to
say
a
site
needs
to
help
many
subnets,
not
just
one
and
a
single
as
last
64
is
never
recommended.
This
is
somehow
already
in
the
document,
but
we
want
to
make
it
more
clear.
Okay,
I
was
working
for
two
years
and
is
still
ongoing
in
a
survey
the
last
time,
I'd
look
at
the
figures.
Probably
about
six
months
ago,
I
had
almost
1600
responses
from
ISPs
from
all
the
wall.
J
35%
are
using
as
last
56,
and-
and
this
is
the
big
problem
there
is
33
percent
that
are
using
a
single,
is
last
64
for
rental
customers.
Okay,
and
when
we
speak
with
those
they
are
somehow
pointing
to
energy
6
177.
So
that's
that's
the
reason
we
believe
it's
is
broken.
You
want
to
say
something
now:
Barbara,
okay,
so
what
we
are
trying
to
do
in
this
document
is
to
update
the
recommendations.
J
J
One-Size-Fit-All
is
not
necessary
or
appropriate,
but
we
still
need
to
ensure
that
insights
get
a
sufficiently
big
number
of
subnets.
A
single
is
last
64
is
not
a
normal
choice.
There
may
be
cases,
of
course,
but
is
not
a
normal
choice.
Neither
should
be
a
small
number
of
subnets
and
we
don't
go
to
define
what
is
a
small.
J
Ok,
we
don't
want
to
enter
into
that
discussion
because
that
will
be
endless
inside
should
always
be
able
to
take
a
reasonable
number
of
his
last
60
force
for
the
rectal
and
planet
usage
and
over
time
range
is
specific
in
many
years,
probably
decades.
Ok,
so
we
are
not
talking,
get
the
use
of
something
for
the
next
four
years,
get
them
something
for
the
next
20
years.
Ok,.
J
J
If
you
want
to
match
that
which
the
preface
that
you
get
from
the
upstreams
is
not
going
to
work.
If
multiple
links
are
present,
DNS
is
simple:
with
same
traffic
size
from
each
link.
Instead
of
having
different
is
business.
Different
traffic
sizes
business
may
need
more
than
a
single
as
last
48
and
the
actual
addressing
policies
from
the
resistors
already
allow
it.
J
If
we
have
as
last
three
that
contains
that
number
of
slash
48,
if
we
are
really
really
really
bad,
deploying
ipv6
and
we
have
a
fifty
percent
utilization,
we
have
only
the
half,
of
course,
and
then,
if
we
suppose
we
are
going
to
have
32
billion
population
and
that
they
average
expectation
for
every
human
is
hundred
years,
and,
let's
suppose
that
when
everyone
dies,
we
don't
recover
this
last
four
days
that
get
to
them.
We
can
give
as
last
40
is
for
the
next
forty
one
thousand
a
hundred
thousand
years.
J
G
Julie,
that's
a
curiously
naive
modeling
of
human
behavior
and
addresses
are
actually
not
used
by
humans,
they're
used
by
machines
so
well
I,
don't
I
it's
hard
to
even
criticize
the
model
on
which
the
assumptions
in
this
slide
are
built
on,
because
it's
not
well
described
but
I
think
it's
I
think
it
I
think
we
can
be
reasonably
certain
that
that
assumptions
that
you
have
there
are
completely
meaningless.
We
can
use
all
this
address
space
in
two
three
four
decades,
maybe
without
too
much
trouble.
J
U
Chief
Houston,
not
chuckling
part
of
the
reason
why
we
had
a
problem
with
the
3177
or
whatever
it
was,
was
that
in
looking
at
the
ratios,
we
were
using
in
deployment
and
50%
utilization
is
a
laughable
joke.
The
whole
idea
of
v6
was
not
to
place
pressure
on
operators
to
achieve
address
utilization
densities,
which
were
expensive.
U
The
whole
idea
was
to
be
enough
space
that
it
really
didn't
matter
and
the
combination
of
using
enough
dress
space
that
it
really
doesn't
matter
and
projections
of
device
density
meant
that
assigning
a
/
48
to
everything
would
give
us
less
than
a
decade.
If
you
happen
to
read
the
stuff,
what
I
object
to
about
this
kind
of
slide
is
joke
mathematics,
it
just
doesn't
cut
it
and
the
case
that
they're
trying
to
make
that
slash,
48,
SAR,
fine
implicitly
behind
this,
is
completely
and
utterly
false.
In
my
mind,
I
reject
that
as
being
irresponsible.
U
If
what
we're
trying
to
do
is
to
utilize
the
larger
address
space
in
v6,
not
to
repeat
the
phenomenal
pressures
we
placed
on
this
industry
to
strangle
v4
beyond
its
reasonable
lifetime,
then
what
you're
doing
here
is,
oddly
enough
repeating
that
same
mistake-
and
the
least
we
can
do-
is
learn
from
this.
So
no
it's
not
funny.
It's
actually
misleading
and
wrong.
I'm!
Sorry,
it
just
doesn't
cut
it.
For
me,.
L
Go
ahead,
Christian,
Itamar,
Jody,
I
kind
of
agree
with
what
Jeff
said
and
one
thing
you're
missing
there
is
that
the
pressure
is
not
linked
to
the
ratio
that
you
are
using.
It's
actually
look
a
bit
meek
and
we
explained
that
in
RFC
4180
for
and
if
you
do,
that,
you
should
actually
go
from
there
and
if
you
go
into
the
logarithmic
effect,
then
it's
very
much
closer
to
just
position
than
yours.
J
J
We
are
providing
just
as
last
64
and
we
don't
use
the
HCP
and
so
on,
and-
and
the
thing
here
is
that
the
the
reason
for
that
is
because
it's
an
alternative
to
broadband
networks,
right
cellular
networks
and
more
and
more
alternative
to
to
broadband,
and
in
some
cases
there
may
be
users
that
only
have
cellular
connectivity
for
their
broadband
connectivity,
and
today
they
got
only
a
single
is
less
64.
So
we
we
want
to
make
sure
that
that's
also
fixed
and
that's
it
basically
so
Barbara
yeah.
I
V
Disagree
Geordi,
first
of
all,
I
guess
on
various
levels.
You
mentioned
the
mobile
networks,
which
are
handing
out
the
SAS
64
effectively
because
there
is
no
DHCP
I,
a
PD
in
those
networks
and
right
now,
64
is
the
best
they
can
do
with
the
mechanisms
they're
using.
Yes,
it
would
be
lovely
if
they
handed
out
more
but
I
think
that
putting
out
some
strongly
worded
RFC
that
says
you
know
we
really
discourage
slash,
64
and
sending
it
to
them,
and
it's
like
tilting,
it
will
windmills.
V
You
know
if
you
start
putting
more
and
more
barriers
like
this
in
front
of
ipv6
deployment,
then
you're
actually
going
to,
in
my
opinion,
decrease
ipv6
deployments
that
still
need
to
happen
in
so
much
of
the
world
and
I.
Don't
think
you
have
made
a
case
for
why
this
extent
of
address
space
is
really
needed.
N
Lorenzo
clitty,
I
think
I
think
this
is
a
tussle
and
and
and
the
reason
is
that
and
the
reason
I
say
that
is
that
I
disagree
with
everything
you
said:
Barbara
well,
pretty
much.
Everything
I
agree
that
saying
it's
like
I
agree
that
saying
something
super
wordid
is
not
gonna
help
that
much.
But
I
think
I
think
we
have
to
say
something
here.
I
think
we
have
to
say
here's
what
you
can't
do
when
there's
when
you
just
use
a
64
and
it's
I
think
we
have.
N
We
have
guidance
on
this
in
in
terms
of
our
ir
policies,
but
we
also
have
to
have
guidance
to
isp,
saying
look.
Our
protocols
are
designed
for
this,
and
that
is
a
statement
that
the
ITF
is
qualified
to
make.
It
has
to
make
right.
I
think
we
wrote
a
bunch
of
stuff
I,
don't
know.
Was
it
10
15
years
ago
these
days
and
we
wrote
a
bunch
of
stuff
about
address
sizing,
and
you
know
that
was
before
ipv6
was
deployed,
and
now
we
have
operational
experience
and
I
think.
N
Yes,
there
are
operational
reasons
to
assign
a
60
to
assign
a
64,
but
there
are
not
good
things
to
follow
in
the
future
right
when
those
operational
reasons
disappear,
like
the
fact
that
you
can
only
do
a
60,
because
if
you're
6
Rd
pools
are
given
size,
we
should
move
towards
56.
If
you
have
a
native
network,
there
is
no
reason
why
you
can't
do
56,
and
if
you
don't
know
that
as
an
isp,
you
should
now.
If
their
operational
reasons,
sure
I
mean
reality
takes
precedence
over
wish
lists.
N
W
J
A
S
Yeah
two
points:
a
sticks,
ID
there's
nothing
stopping
any
6id
operator
from
deploying
slash
48
to
every
one
of
their
users.
It's
only
when
you
start
shoving
the
whole
/
32
from
ipv4
into
the
address
that
you
actually
become
become
size,
limited
in
the
number
of
prefixes,
and
what
we
really
need
to
do
is
start
trying
to.
S
Describe
how
to
not
waste
addresses
be
that
the
instructions
to
enterprises
on
how
to
actually
allocate
addresses.
So
if
your
enterprise
and
you
actually
just
assign
a
slash
64
on
demand,
yep,
you
have
65,000
slash,
60
forced
to
hand
out
you
don't
need
to
have
internal
structure.
When
you
heard
her
an
enterprise,
it
might
be
nice
that
handing
out
the
dresses
doesn't
require
doesn't
require
internal
structure.
U
Jeff
Houston
again
look
either
we're
all
commonly
amnesiac
and
we
just
simply
forget
everything,
or
we
endlessly
repeat
these
conversations,
so
we
can
get
more
and
more
expert
at
reciting
our
positions.
Neither
of
these
correspond
to
progress.
There
is
nothing
in
61
77
that
said
user,
slash
60
for
nothing.
It
actually
says
the
opposite.
U
As
you
might
recall,
what
it
did
say,
which
is
what
you
seem
to
be
contradicting
here,
was
that
one
size
fits
all
is
wrong
and
the
whole
idea
of
classful,
addressing
as
we
learned
in
v4,
was
actually
a
hideous
mistake
and
deployments,
and
operators
have
enough
nouse
to
figure
out
what
they
need
to
do
and
trying
to
do.
One
size
fits
all
create
such
gross.
An
extraordinary
wastefulness
of
address
space
that
even
the
128
s--
of
these
some
bits
of
v6
get
wasted
almost
immediately.
U
We
can
hear
through
this
space
in
a
year
if
we
really
want
to,
because
we're
endlessly
inventive
I
do
not
see
anything
in
this
draft.
That
justifies
why
we
should
be
doing
abyss
on
61
77.
To
me,
this
seems
like
a
complete
waste
of
time.
What
we
said,
then,
is
true.
Now
there
is
no
one-size-fits-all
go
pick.
What
you
need
to
do
by
the
way
a
slash
64
to
insights
is
kind
of
difficult
for
those
insights.
U
You
really
shouldn't
go
there
or,
if
you
do
understand
very
clearly
what
you're
doing,
because
it's
not
the
best
idea
beyond
that.
Go
figure
out
what
your
customers
need
and
do
the
right
thing
by
them,
not
as
you're
saying
strongly
suggest
going
back
to
the
exact
same
problem
that
prompted
61
77
to
come
up.
So
you
know
I'll
keep
on
saying
this
and
you'll
keep
on
doing
that
throughout
the
next
five
years
and
we'll
all
feel
good
about
it.
U
J
N
Learn
zouk
lady
I
do
think
we
need
something
that
discourages
a
single
/
64,
because
we
have
things
like
HomeNet.
That
say
that
you
shouldn't
do
that
and
I
think
we
I
think
I
think
it's
worth
writing
a
document
that
says
look
here's
what
we
learned
and
here's
what
we
think
this
should
look
like
in
the
future.
I,
don't
you
know,
maybe
61
77
says
exactly
what
we
need
to
say
for
what
it's
worth.
I
mean
Jeff.
Is
this
just
because
you
don't
you
don't
like
48?
J
U
You
Mike
I'll,
try
and
paraphrase
my
understanding
of
our
IR
policy
and
I.
Don't
want
to
be
authoritative
about
it,
but
the
our
IRS
heard
very
strongly
in
their
policy
fora
that
one
size
didn't
fit
all
and
what
they
allowed
as
far
as
I
can
see,
is
v6
allocations
based
on
what
the
operator
said
they
were
doing
and
it's
not
a
/
56
or
a
/
48
or
anything
else.
There
is
a
charging
structure
in
a
lot
of
the
our
IRS
we're
forced
some
of
them.
U
U
This
is
not
an
RI
armaiti.
The
second
thing
is
sixty
one.
Seventy
seven
says
very
clearly:
don't
go
down
the
/
64
path
and
I
really
don't
understand.
Why
we're
having
a
debate
about
that
because,
as
I
said,
you
couldn't
make
it
much
clearer
if
you
actually
read
the
taste,
so
I
don't
see
where
the
problem
is
on
that
side.
So
you
see
this
is.
X
So
just
pushing
back
on
the
last
one
and
so
going
back
to
33
14
from
2000
like
we
had
this
discussion
and
we
really
recommended
3gpp
to
go
its
last
64
and
it
was
like
a
big
big
battle
to
get
it
pushed
down
there.
People
say:
oh,
that's
like
really
wasteful
and
everything
I.
Just
don't
want
this
to
be
the
open
again,
at
least
for
the
cellular.
X
I
know
like
Lorenzo's
gonna
come
back
here,
probably,
but
everything
that
needs
to
be
said
has
been
said
in
79,
34,
okay,
it
says
like
what
can
you
do
it
this
last
64?
What
you
cannot
do
so
I
think
that
work,
at
least
for
the
cellular
side
is
done
like
I.
Don't
want,
like
anything,
specific
saying,
put
in
a
bigger
prefix
for
a
cellular
network,
because
this
is
like
really
entrenched
and
we're
really
happy
that
this
happened,
that
everybody
got
us
last
64.
K
Hi
Bob
Hinton
two
points
from
the
discussion,
so
certainly,
if
we
are
not
prudent,
we
will
use
up
this
address
space
very
quickly.
It's
we
know
how
to
do
that.
So
we
do
need
to
be.
You
know
careful
how
what
allocation
policies
are,
and
the
other
thing
that
I'd
like
to
add
is
that
the
intent
behind
this
was
not
to
make
the
ISPs
better.
It
was
to
give
the
N
sites
enough
address
space,
so
they
could
do
whatever
they
needed
to
do
so.
K
There
wouldn't
be
address
scarcity
like
we
have
with
before
and
that's
you
know,
thinking,
or
at
least
my
thinking
was
that
the
ISPs
have
resources
and
can
manage
it
their
space
and
they
conduce.
They
can
deal
with
complexity
at
that
level,
but
the
insides
can't
and
if
we
make
it
hard
for
the
insights
to
get
enough
presses
or
having
to
renumber
frequently,
then
we'll
end
up
with
that
again
exactly.
N
Lorenza
Khalil
I,
you
know,
I
think
what
if
we
said,
simply
assigning
a
single
size,
64
per
site
is
not
recommended,
I
mean
I,
think
pretty
much.
Everyone
agrees
with
that
right
and
that's
clearly
not
being
done
everywhere
and
the
reasons
are
varied,
but
I
think
if
we
I
think
even
ice.
Bees
would
agree
with
that
aspirationally.
They
would
like
to
assign
that
and
I
think
it's
important
to
state
that
in
a
very
simple
way.
As
for
cellular
networks,
I
mean
Suresh.
N
The
that's
actually
a
great
example
of
how
what
we
said
made
a
difference,
and
it's
it's
a
shining
example
I.
Remember
a
major
one
of
the
earliest
adopters
of
ipv6
and
the
person
at
that
operator
who
was
pushing
my
pv6
was
I'm,
not
gonna
name.
Any
names
here
was
convinced
that
64
per
to
the
device
was
super,
wasteful
and
was
really
stupid,
and
that
operator
discovered
after
deployment
that
actually
this
thing
that
they
had
assigned
a
64,
because
the
stupid
ITF
had
forced
me
to
do
that.
I
was
like
oh
cool.
N
N
And-
and
we
shouldn't
say
like:
oh
don't
assign
is
64
right,
but
and-
and
you
know
it's
to
the
earlier
point-
that
date-
that
mobile
networks
don't
support
HPV
6.
Well,
it's
written
in
the
standards
right.
It's
not
like
it's
not
there.
In
theory,
you
know,
maybe
the
gear
doesn't
support
it,
but
it's
there
since
release
10,
so
I
mean
I.
Think
that
that
that's
a
good
statement
to
make
you
know
if
you
want
to
provide
an
alternative
to
to
home
routing
to
to
home.
N
C
C
An
area
where
we
give
operators
free
rein,
anything
between
the
upper
and
lower
limit
is
just
fine.
Now
the
question
is:
what's
that
upper
limit?
The
best
thing
we
have
to
judge
the
upper
limit.
Your
analysis,
which
was
clearly
humorous,
but
not
serious
and
I've,
also
heard
that
if
we
use
slash
48,
we
can
run
out
in
ten
years.
X
X
Just
like
going
back
to
what
Lorenzo
said,
so
there
is
some
limitations
in
in
cellular
networks.
Okay,
so
we've
done
quite
a
bit
of
study
on
this
on
a
fixed
network.
If
somebody
gets
this
last
64
and
they
decide
they
need
more
at
this
pace,
they
asked
for
more
address
space
and
they
can
get
a
48
or
as
50
like
56
or
60,
whatever
they
want
right.
But
the
way
the
cellular
networks
are
architected,
they
get
only
one
prefix.
It
can
be
a
what
Evelyn.
So
if
ITF
decides
like
hey,
everybody
should
get
a
slash.
X
30
do
like
fine
right,
but
but
once
the
session
is
established
like
putting
in
a
second
prefix,
it's
very,
very
difficult.
So
bunch
of
us
worked
on
this
thing
together.
I
think,
like
Ola
worked
on
it
with
me
and
youngy
like
few
P,
we
worked
on
it,
so
we
figured
out,
like
you
know
how
to
delegate
a
prefix
with
the
hole
in
it
so
that
6603
that
came
out
from
like
you
know,
how
do
you
take
a
prefix,
take
a
whole
lot
of
it.
X
X
So,
whatever
number
we
come
up
with
right
now,
it's
gonna
be
equally
painful
to
have
that
discussion,
so
I'm
really
happy
that
we
have
the
64
there
and
we
can
try
to
push
like
further
if
needed,
but
I
think
64
works
well
for
mobile
networks
like
for
mobiles
and
as
like
Lorenzo
said.
If
it
becomes
like
more
like
a
site,
that's
behind
a
mobile
network,
then
maybe
we
can
come
up
with
a
slightly
more
targeted
recommendation
for
other
things
in
there.
But
I
don't
want
this
to
be
like
a
chain.
U
Geoff
Huston
I'm
just
going
to
remind
the
IATA
from
this
working
group
where
we
are
because
61
77
is
a
BCP
now
underlying
this
is
where
does
address
allocation
policy
happen
in
the
internet
and
a
long
time
ago,
after
a
lot
of
fights-
and
some
of
you
might
remember-
PR,
we
kind
of
said
to
the
our
IRS-
will
give
you
architectural
guidance
but
URI
hours
of
the
address
policy.
Fighting
room
go
there
and
hash
it
out.
The
ITF
can
recommend
that
it
can't
enforce
so
61
77
says
very
clearly.
U
The
IETF
recommends
that
any
policy
on
v6
address
assignment
policy
to
end
sites
takes
into
consideration
the
following
points,
which
is
an
appropriate
language
for
this
working
group.
You
can't
say
Oh
URI
eyes
have
to
do
this
or
that
it's
beyond
your
scope,
your
arms
aren't
long
enough.
You
can't
reach
that
far
point
one.
It
should
be
easy
for
an
insight
to
attain
address
space,
to
number
multiple
subnets
ie,
a
block
large
single
/
64,
and
to
support
reasonable
growth
projections
over
long-term
periods,
either
a
decade
or
more.
U
If
that
doesn't
say,
don't
use,
64
I,
don't
know
what
does.
Secondly,
the
before
yeah
typically
I'm.
That's
why
I'm
helping
by
reading
it
out
the
default
assignment
size
should
take
into
consideration
the
likelihood
insights
we'll
have
need
for
multiple
subnets.
So
my
point
is:
all
of
this
is
stated
already
so
I
really
don't
understand
exactly
why
we're
circling
around
this
again
and
again,
and
the
real
issue
is
the
architectural
guidance
might
come
from
here,
but
the
feet
on
the
ground
is
actually
inside
a
different
room,
a.
Y
N
I
think
we
we
need
to
bear
in
mind
that
160
177
was
written
v6
deployment
at
the
Internet's
to
the
0.2%
okay.
Now
it's
two
orders
of
magnitude
above
that
and
I
think
we
can.
We
can
it's
kind
of
like
amazing
to
me
that
61
77
has
a
BCP
cuz,
there's,
basically
no
deployment
right,
so
it
wasn't
a
current
practice.
N
It
was
a
future
practice
to
CNBC
piece
you've
been
like
BFP
or
something
so
and
to
your
point,
Jeff
I
think
that
text
is
so
easily
that
people
can
read
whatever
they
want
into
it
and
I.
Think
while
I
would
agree
with
you
that
it
says,
don't
do
slash,
64
I
think
there's
benefit
to
saying:
don't
do
slash
64,
because
if
that's,
if
that's
what
everyone
agrees,
it
says,
then
let's
write
it
in
plain
English
right.
If
we
already
agree
on
it,
you
don't
do
64.
N
N
I
didn't
think
this
room
would
I,
don't
think
the
IRS
would
either
because
the
IRI
has
already
say:
don't
do
this,
so
let's
just
write
it
and
in
plain
English
and
say:
look
if
we
want
to
I
I
think,
from
my
perspective,
having
a
clear
document
as
a
win
and
I
think
if
we
want
to
say
look:
here's
after,
like
whatever
between
0.3
percent
and
25
percent
of
v6
deployment,
here's
what
we
learned
and
here's
what
we
want
to
recommend.
Let's
do
that
thanks.
P
John
linka
I've
been
listening
to
this.
That
looks
like
we
just
basically
discussions
that
the
few
section
in
the
original
RFC
is
not
clear
enough.
Should
it
just
be
a
very
short
document,
saying:
let's
update
this
text
with
zebb
text
and
that
section
and
we
are
done
making
it
more
clear
and
to
wrong
point
about
providing
upper
limit.
I
do
not
think
it's
a
problem.
P
We
have
now
right
because
I
think
practically
most
of
the
real
problem
is
that
ISP
is
assigned
just
slash,
64
or
even
slash,
128
I
do
not
think
we
have
problem
with
two
blocks
assigned
being
too
large,
so
we
probably
do
not.
I
am
Not
sure
we
need
to
concentrate
on
discussion.
Should
it
be
slash,
48
or
something
else.
We
need
to
make
sure
we're
not
assigning
too
little
because
it
hurts.
If
you
assign
too
much
well,
you
burn
out
your
address
space.
P
C
J
Please
I
will
suggest
the
people
that
that
happen
not
read.
The
document
make
a
deal
between
the
original
six
177
and
this
one,
because
the
difference
are
not
that
much
so
I
agree
with
Jen
that
it
may
be
a
shorter
document.
Yes,
this
document
is
shorter
than
the
original
one,
so
we
actually
remove
it.
Parts
of
the
original
document.
B
J
Okay,
so
this
this
document
I
think,
actually,
you
suggested
doing
a
comparison
of
the
transition
mechanism.
So
GABA,
which
is
the
main
author
of
the
document,
said
yes,
I,
take
it
and
ask
it
for
volunteers,
so
few
of
us
started
contributing
I
know
we
have
short
time
so
so
I
I
did
a
very,
very
small
presentation,
because
the
main
goal
of
this
presentation
is
to
to
get
input
from
the
working
group.
Okay.
J
So
we
need
a
lot
of
work
here
and
we
don't
expect
this
document
to
be
an
easy
one
or
something
that
we
are
going
to
do
in
a
in
a
short
time.
So
basically,
what
we're
trying
to
do
with
this
document
is.
There
are
five
basic
transition
mechanism
that
we
call
like
ipv4
as
a
service
which
are
four
six
four
X
Latvia's
light
like
way
for
over
six
months
and
mati.
J
There
are
a
few
others
like
Lee's
theory
on
ipv6,
and
so
on
that
we
decided
not
to
consider,
because
there
is
not
that
much
deployment
as
the
previous
ones,
so
we
prefer
to
concentrate
on
de
what
we
believe
are
the
five
mine
ones.
If
somebody
disagreed,
please
state
hey,
there
are
that
many
number
of
deployments
which
other
documents,
sorry
which
other
mechanism-
and
maybe
we
will
consider
that.
J
So
the
thing
is
if
we
try
to
make
a
comparison
between
all
of
them
to
make
easier
for
an
ISP
to
decide-
and
we
already
know
from
the
beginning
that
this
this
is
not
really
an
easy
task
and
at
the
end
it
will
depend
a
lot
on
every
specific
Network
case.
So
we
have
different
sections
of
the
document
again.
J
We
have
also
typical
deployment
and
traffic
volume.
There
are
some
figures
that
that
Cameron
from
t-mobile
provided
to
the
mailing
list.
Oh
we
compared
it.
Those
stickers
which
other
similar
makers-
and
it
looks
like
like
most
of
them,
are,
coincidentally
in
that
in
that
sharing,
so
we
are
basically
describing
the
deployment
possibilities,
including
the
server
which,
for
six
Forex
lat,
the
load
sharing
performance
comparison.
This
is
something
that
we
want
to
do
so
this
is
not
still
done,
but
the
idea
is
Gabbar
has
some
students
that
will
be
able
to
do
this
performance
comparison.
J
We
still
need
to
define
exactly
how
we
are
going
to
do
that,
because
it's
not
an
easy
task,
and
that
will
be
part
of
the
document
and,
of
course,
we'll
have
a
security
considerations,
and,
and
that's
it,
they
thing
here
is
asked
to
the
working
group
to
contribute
ask
to
the
working
group.
What
other
aspects
do
you
believe
are
interesting
to
to
be
considered
by
the
document?
V
So
something
I
think
would
be
useful.
Is
a
number
of
these
technologies
actually
have
various
options
as
to
how
they
can
be
set
up?
You
know,
maybe
you
have
blocks
of
ipv4
addresses
associated
with
it,
maybe
you're
using
that
you
know,
there's
all
these
various
things,
and
so
it
would
be
useful
to
understand
what
are
the
most
common
configurations
that
are
in
use.
Z
Expensive
task-
and
it
probably
should
have
been
done
some
time
ago-
I
gotta,
look
through
it
and
I've
got
a
raft
of
comments
and
the
current
version
of
there,
which
I'll
post
the
list
later
on,
but
the
main
things
I
had
some
there's
been
a
spreadsheet.
That's
been
doing
the
realms
over
the
last
few
months
and
I
think
Lee,
Howard
and
well,
based
on
your
work.
Z
That
does
some
kind
of
comparison
between
these
things
based
on
kind
of
yes/no
is,
and
you
know,
are
very
easy
to
look
up
and
something
is
the
plan
to
kind
of
incorporate
this
stuff,
and
you
know
find
some
ASCII
way
of
rendering
that
that
thing,
sorry
is.
The
plan.
Is
the
plan
to
incorporate
that
comparison
table?
Z
So
here's
an
easy
and
yeah
yeah,
okay,
good
the
performance,
testing,
I
I
mean
we've
talked
about
this
one
already,
but
I
I've
been
kind
of
wracking,
my
brains
about
this
as
to
whether
it
can
anything
meaningful
come
out
of
this.
That
isn't
just
going
to
say
this
implementation
is
faster
than
that
implementation.
You've
got
physical
versus
virtuals,
you've
got
God
knows
how
many
different
variables
on
here.
To
be
honest,.
