►
From YouTube: IETF103-EMU-20181105-1610
Description
EMU meeting session at IETF103
2018/11/05 1610
https://datatracker.ietf.org/meeting/103/proceedings/
A
A
A
A
A
But
are
the
drafts
were
working
around
are
different.
We
have
the
epls
one,
two
one,
two
three
and
the
EMU
the
EBA
ka
this.
So
those
are
the
current
working
group
items.
I
think
we'll
have
a
couple
more
that
we'll
be
bringing
into
the
working
group
soon
and
hopefully
we
can
start
getting
these
towards
completion
as
well.
So
I
think
this
will
be
a
good
meeting.
I
think
there's
a
significant
work
done
on
both
of
these
areas,
so.
A
B
Something
there
yeah
I
see
great,
so
this
is
version
2
of
the
ETL
s103
draft.
The
version
that
was
presented
at
the
last
meeting
was
Cirrus
0,
so
we
have
seen
to
update
so
his
drops
and
basically
the
the
discussions
and
conclusions
last
time
was
most
of
the
things
we
discussed
at
the
last
meeting.
We
decided
not
to
change,
but
what
two
things
that
we
decided
to
change
and
that
has
been
done.
So
one
of
the
changes
are
quite
straightforward.
There's
session,
hiding
out
story,
serie
de
as
suggested
by
bernard,
a
boba.
B
B
Instead
of
deriving
the
session
ID
directory
from
the
TLS
exporter,
value
called
method.
Id
is
the
right,
and
this
is
according
to
some
other
ear,
PT
RFC
I,
don't
remember
which,
and
then
the
session
ID
is
created
by
concatenating
0d
with
the
method
ID,
and
this
makes
the
session
ID
65
bytes
long
as
in
RFC
52:16,.
B
No
other
change
that
may
resume
or
the
passion
is
the
empty
TLS
record,
and
this
was
brought.
The
discussion
was
brought
up
by
Julie
at
when
he
implemented
this
year,
maybe
not
the
syriza
version,
but
diversion
even
before,
and
he
said
that
with
a
new
session
ticket,
it's
hard
for
the
client
to
know
what
will
come
next
and
it
messes
up
the
EAP
state
machine
a
little
bit
and
was
comment
from
ban
on
that.
It
should
be
made
cryptographically
secure
and
him
short
suggested
added
an
empty
TLS
record.
B
Let's
see
empty
TLS
record,
this
is
just
an
empty
application.
Data
application
data
record
later
with
links
where
the
plane
takes
length
is
0,
and
after
doing
this,
the
server
does
not
send
any
more
handshake
messages
it.
But
it's
still
three
possible
options
what
it
might
sends,
and
after
this
it's
each
success,
failure
or
a
TLS
alert
message
and,
as
I
I
will
show
you
pictures
of
all
of
this
but
yeah.
B
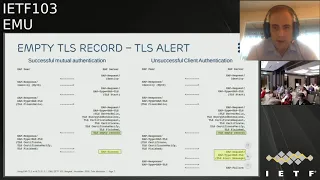
So
first
here's
the
case
when
we
have
success
to
the
left.
We
have
a
the
ordinary,
successful
mutual
authentication
and,
as
you
can
see
here,
marked
with
a
green
rectangle,
we
have
a
new
field
here,
the
TLS
MD
record,
and
by
sending
this
the
server
commits
to
not
sending
any
more
handshake
messages.
And
here,
in
the
case
of
a
successful
client
authentication,
the
server
responds
with
each
success.
B
On
the
right
side,
we
see
a
mutual
attempt,
gage
successful
mutual
authentication,
where
the
service
sends
a
new
session
ticket
to
enable
resumption
in
the
future-
and
in
this
case
the
server
does
not
send
a
empty
record
after
it's
finished
because
it
it
will
send
a
post
handshake.
So
it
sounds
a
empty
record
after
the
new
session
ticket
and
I'm.
In
this
case,
everything
is
successful.
B
In
the
left
page
here
there
is,
there
is
no
empty
record
because
we'd
never
reach
that
state.
The
client,
the
server,
reacts,
the
kind
hello
in
the
right
side.
We
have
this
case
where
the
server
authentication
fails,
or
the
country
exits
for
some
reason,
and
then
this
is
the
case.
Without
a
new
session
ticket,
then
the
client,
the
server
sends
TLS
empty
record
and
afterwards
it
will
be
a
EAP
failure.
B
The
next
slide
we
will
have
the
most
complicated
case.
So
here
is
the
left
side.
Here
is
the
successful
mutual
authentication,
as
described
earlier,
the
server
commits
to
not
sending
any
more
handshake
messages,
and
if
everything
is
ok,
it
was
a
leap
success
here,
but
on
the
other
hand,
if
everything
is
not
okay
here,
so
the
server
reacts.
The
client
authentication
that
the
server
responds
with
a
request
with
a
TLS
alert
message.
B
So
the
commit
here
with
empty
record
is
to
not
send
handshake
messages,
and
this
is
serving
the
best
we
can
do
at
least
it.
This
is
as
far
as
I
can
understand,
aligning
with
RFC
Phi
2
1
6,
in
which
this
case
is
what
happened.
If
the
client
authentication
fails
during
a
resumption,
then
you
have
the
same
scenario.
This
service
ends
either
success
or
it
sends
a
key,
less
alert
message.
B
One
thing
was
that,
when
writing
this
presentation,
I
noticed
that
we
have
error
cases,
for
we
have
figures
illustrating
the
message
flows
for
basically
every
error
cases,
and
this
was
requested
on
the
mailing
list
to
add
more
error
cases,
and
so
now
that
we
don't
have
an
error
cases
for
the
eap-tls
client
reacting
the
new
session
ticket
I
assume
the
client
was
under
TLS
alert
message.
In
that
case,
do
we
want
such
a
figure
and
that
could
have
be
edited
next
word.
B
Them
further
update
a
couple
of
Mia
had
discussion
about
privacy,
and
the
peer
may
reveal
its
identity
in
two
different
ways:
it's,
firstly,
it
can
send
its
identity
in
clear
text
in
the
first
EAP
response
called
ident.
My
idea
I
think
Oh
my
identity
in
droves,
and
this
is
for
all
TLS
version
and
the
second
way
the
peer
may
reveal
its
identity
is
to
send
its
certificate
in
clear
text,
and
this
only
happens
in
previous
versions
of
TLS.
B
What
we
can
do
in
the
privacy
for
privacy
is
a
little
bit
restricted
with
what
kind
of
legacy
interrupt
a
deployment
modes,
but
one
thought
I
had
was
that?
Can
we
do
something
more
specific
about
the
identity
sent
in
the
first
message?
Can
we
can
be
always
can
be
recommend
or
mandate
that
appear
sends
confidential
identity,
for
example
anonymous
nigh
or
is
there
in
your
key
service
that
will
not
like
this
RFC
five,
two
one
six
is
doesn't
say
very
much
about
this.
It
says
that
service
may
that
doesn't
support
privacy.
B
C
D
E
Yeah,
yeah
and
I
agree
with
your
advice.
What
I
came
up
to
say
here,
though,
is
that
I
struggled
a
little
bit
with
the
similar
issue
and
the
aka
draft,
like
how
monster
of
the
aka
attacks
should
I
describe
and
one
of
the
crucial
things
I
I
think
determines.
This
is
if
there
is
a
reasonable
reference
for,
for
those
other
things
and
I
said
I
assume
lean
in
the
case
of
TLS
there
there
is
TLS
working
group
documents
past
the
ls1.
F
B
F
If
this
is
Elliot
again,
if
you
think
the
attacks
are
applicable,
then
you
certainly
should
refer
to
them.
You
don't
have
to
read,
ascribe
it,
but
adding
maybe
a
at
least
my
advice
would
be
to
just
add
a
reference,
but
not
to
spend
a
lot
of
effort.
Recapitulating
everything
is
something
that
went
through
a
whole.
The
whole
process
of
an
RFC
did
no.
A
F
So
just
this
Elliot
again,
one
thing
you
can
do
is
you
can
put
it
actually
something
in
the
front
matter
of
this
document
which
says
this
I.
If
the
attacks
are
actually
motivation
for
this
work
right,
at
least
in
part,
some
of
the
some
of
the
holes
and
the
earlier
versions
of
TLS
or
motivations
and
I
think
you've
done
some
of
that
right.
But
just
maybe
you
could
even
add
a
reference
up
front
against
that.
You
know
you
don't
have
to
go
into
any
detail.
F
F
You
know
a
line
or
two
in
the
non
browser
risks,
maybe
might
might
be
useful
and
the
reason
that
I
say
that
is
that
we've
seen-
and
maybe
this
is
a
good
thing,
but
we've
seen
basically
a
blanket.
You
know
attempt
to
just
get
to
the
latest
version
of
TLS
without
actual
analysis
of
what
the
attacks
are
and
that
that
that
poses
a
long-term
threat
in
terms
of
people
having
spent
money
on
upgrades
that
they
didn't
need,
and
they
say:
oh
you're,
just
a
boy
who
cried
Rolf
again
see
they're.
B
A
B
B
Not
spending
too
much
time
that
ya
think
mm-hmm.
Let's
do
any
more
questions
next
slide,
so
this
was
quite
short
I.
Take
that
as
people
like
the
changes,
if
they
have
rather
I,
think
this.
What
is
trough
needs
now
is
more
more
reduce
and
more
feedback,
also
more
implementations
and
possibly
interrupt
I.
B
A
A
A
B
So
this
presentation
will
hopefully
be
very
short,
so
we
made
an
update
based
on
the
discussion
at
the
last
tight.
If
you
go
to
the
next
slide,
so
it
has
been
updated
from
0
0
to
0
1,
and
it's
not
that
much
add
added
information.
It's
the
drug
has
been
reorganized
to
distinguish
between
recommendation
requiring
change
of
certificates
and
recommendation
only
requiring
changing
the
code.
For
example,
update
me
to
TLS
1.3.
B
So
there
and
there's
some
new
text
describing
the
cached
information
extension
that
was
discussed
that
last
time
stating
that
it
in
some
cases
is
not
helpful
if
the
handshake
phase
anyway,
but
it
can
be
helpful
if
you
have
done
a
notification
in
your
home
network
and
on
your
roaming
and
an
or
full
handshake
without
this
would
fail.
This
can
make
it
possible
to
do
a
handshake
there
authentication.
G
No,
so
Shawn
Turner
had
some
ideas
on
how
you
can
give
guidelines
to
people
issuing
certificates
like
don't
put
tons
of
oh
I'd
ease
into
the
certificate.
Don't
have
like
thousands
of
subject
all
names
in
the
certificate,
so
those
kind
of
guidelines
specially
so
using
TLS
on
the
web
is
a
little
bit
different
from
using
TLS
on
Ani,
where
you
have
access
points
that
dropped
sessions,
if
they
don't
complete
in
in
time.
B
All
right
yeah
next
slide,
so
that's
it
except
that
planned,
update
from
Shawn
I,
don't
think
we
have
many
many
many
else
planned
updates.
We
will
need
suggestions
and
review
some
feedback
from
the
working
group
and
both
this
and
the
eat.
Eap-Tls
1.3
draft
is
on
github.
So
if
you
want
to
know
what
we
are
planning
for
the
next
version
and
any
open
issues,
you
should
look
there
and
feel
free
to
commit
issues
there
or
make
a
pull
request
or
comment.
A
G
E
E
But
it's
now
finding
also
use
in
in
the
upcoming
5g
standards
and
as
part
of
that,
we're
trying
to
make
sure
that
everything's,
correct
and
things
that
we've
learned
in
the
past
or
things
that
we
missed
on
the
first
specifications
are
actually
corrected,
and
the
initial
thought
was
that
there's
three
things
that
we
need
to
do
identifiers
are
a
little
special
in
5c,
so
I
figured.
We
need
to
do
something
for
that.
The
EAP
aka
prime,
does
sort
of,
like
a
network
name
binding
that
you.
E
Both
parties
agree
to
what
what
they're,
what
they're
authenticating
for,
or
what
network
they're
connecting
to
and
that
changed
a
little
bit
also
for
5g,
so
fix
that,
and
then
we
knew
that
exported
prime-minister
forgotten
in
the
old
RFC's
that
we
didn't
do
that.
Even
those
mother
RFC
required
that
so
fix
those
three
things,
but
it
turned
out
that
we
actually
needed
to
do
a
bunch
of
other
stuff
too
in
the
meantime
that
IETF
demands
for
what
should
you
talk
about
in
the
security
constraints?
E
E
E
There's
been
two
updates
since
last
IDF,
l2
and
l3.
The
general
state
is
just
that.
We
now
believe
that
this
well
I
know
I
said
this
before,
but
now
we
really
believe
that
this
is
in
sync,
with
3gpp
specs
we've
done
some
5g
related
updates.
We've
done
some
general
updates
and
we've
done
a
lot
of
work
with
the
security
consideration.
Section
I'm
gonna
go
through
some
of
the
main
points
here,
so,
first
of
all
identifiers.
E
E
One
is
the
permanent
identifier
called
the
soupy
and
and
then
as
concealed
or
privacy,
friendly
I
didn't
if
I
call
tsuki
or
Susi
and-
and
the
idea
is
that
these
are
used
for
different
purposes-
that
the
permanent
one
we
can
use
for
keys
in
a
race
or
no,
that's
that's
what
they
wanted
at
3gpp.
So
that's
what
we'll
do
and
then,
obviously
the
privacy
friendly
one
is
the
one
that
we
used
use
for
any
any
other
passing
of
identifiers
around
and
there's
couple
of
things
in
the
draft.
E
First
of
all,
you
or
this
additional
text
to
fix
this
case,
where,
like
the
previous
RFC
said
that
always
ask
or
should
ask
I
think,
was
the
was
the
phrasing
for
identifiers
inside
the
EAP
aka
method
rather
than
the
EAP
framework,
but
in
in
a
case
where
you
are
connecting
to
a
5g
network
and
using
the
5g
protocols
to
do
the
signalling
and
and
man-carrying
EAP
there.
Then
you
do
something
slightly
different.
It's
of
course.
It's
also
requirement
of
implementations
to
be
able
to
do
this
or
detect
this
kind
of
situation.
E
phone
or
or
some
kind
of
other
client
will
actually
get
a
request
for
identity.
What
do
you
do
then?
Well
3gpp
had
developed
a
table.
What
to
do
in
this
different
case
is
there
and
we
basically
follow
that
same
here
just
to
make
sure
that
specs
are
aligned.
This
applies
only
to
5g
case
here
and
I.
Don't
represent
the
whole
table
here
that
point.
Let's
just
give
you
an
example,
so
in
5t,
because
the
basically
old
identifiers
that
you
pass
around
publicly
are
privacy
friendly
identifiers.
E
E
Key
generation
I
mentioned
that
that
we
use
one
of
these
two
special
identifiers
in
key
key
derivation.
So
there's
some
language
about
that
like
under
what
condition
you
do
that
and
then
this
is
what
you
do,
and
these
are
the
bits
and,
regarding
the
bits,
there's
a
format
question:
it's
not
just
a
conceptual
thing,
but
also
a
question
of
exactly
how
to
represent
things.
E
So
one
one
is
this
permanent
one
that
is
in
the
clear
here's
the
example
in
the
upper
or
the
upper
example
is
like
that
it's
kind
of
easily
readable
and
then
there's
a
encrypted
identifier,
where
the
network
part
is
like
you
specify
what
operator
you
go
into,
but
then
you
hide
the
subscriber
identity
part
with
public
key
encryption.
That's
been
specified
in
in
3gpp,
but
it
still
maps
to
a
in
AI,
and
so
we
don't
specify
any
of
that.
We
just
point
to
that
then
and
provide
some
examples.
E
So
that's
identifier,
and
then
we
have
another
thing
that
we
want
to
make
sure
that
the
3gpp
specifications
for
IG
and
and
the
RFC's
agree,
because
the
previous
RFC
declared
that
in
in
in
these-
and
this
is
these
situations
you
use
like
these
strings
to
determine
like
this
is
for
wireless
LANs.
This
is
the
string
that
you
should
use
and
and
so
on
now
here
in
bit,
5g
we're
introducing
a
new
string.
E
E
If
people
have
comments
on
that,
that'd
be
useful.
My
understanding
also
is
that,
while,
while
there
is
an
RFC
that
requires
us
to
export
these
parameters
from
EAP
methods,
there
isn't
a
lot
of
implementations
or
even
any
implementations
that
would
actually
use
this
infamous
all
right.
People
who
have
EAP
experience
care
to
comment
if
they
seen
this
this
information,
but
depending
on
the
answers
this
either
matters
a
lot
or
doesn't
matter
a
lot
moving
on.
A
E
And
then
the
previous
RFC's-
and
this
has
nothing
to
do
with
5c.
This
is
like
a
totally
general
change.
The
previous
RFC's
defined
this
pseudonym
approach
and
fast
via
indication,
identity
approach,
and
they
they
sort
of
provided
special
usernames
that
can
be
used
in
these
processes
and
and
the
assumption
was
that
these
be
like
totally
random,
and
you
know
you
cannot
figure
out
what
the
user
is
from
those,
but
we
didn't
actually
say
that
in
the
specs.
E
E
E
So
if
in
fight
see,
you
are
sort
of
protected
against
privacy
violation,
so
looking
at
identifiers
and
then
then
you
suddenly
use
pseudonyms
and
use
the
same
children
in
multiple
times.
Then
then
you've
disclosed
that
that
you're
the
same
entity
in
these
two
instances
and
that's
bad,
so
the
purpose
of
the
5g
enhancements
would
be
lost.
If,
if
you
did
that,
so
we
are
prohibiting
that
we
discussed
the
implications
of
different
protection
profiles
of
3gpp
when
they
did
this
encryption
of
identifiers.
They
have
multiple
different
profiles,
including
the
new
profile.
E
E
We
also
added
a
section
on
pervasive
surveillance
considerations
discusses
in
particular
the
attacks
that
were
claimed
to
have
happened
a
couple
of
years
ago.
2015,
the
sim
heist
look
up
the
reference
from
that
draft
and
obviously
all
protocols
are
vulnerable
to
compromise
of
the
primary
key
material.
We
discuss
some
specific
means
to
make
sure
that
that
doesn't
happen
when
you
manufacture
these
cards.
I
mean
also
suggest
that
some
form
of
perfect
forward
secrecy
protection
may
be
useful.
E
E
We
did
add
a
fairly
extensive
section
on
discovered
vulnerabilities,
and
this
is
what
I
was
referring
to
when
we
were
talking
about
John's
draft,
how
much
to
talk
about
general
aka,
how
much
talk
about
aka,
prime
issues
and
I
didn't
have
a
really
good
trip.
We
were
unable
to
find
a
really
good
reference
for
you
know
here
are
all
the
attacks.
You
know
sort
of
fair
and
balanced
manner
reported
on
on
aka,
so
we
try
to
write
our
own.
E
That
is
not
really
relevant
for
this,
but
I
did
point
to
like
this.
We
did.
Some
of
us
are
c-33
10
that
is
aka
inside
HTTP
and
he
turned
out
to
go
really
badly
and
we
didn't
use
the
crypto
keys
in
the
end
result,
which
meant
that
this
is
vulnerable
to
man-in-the-middle
attacks
and
fixed
that
in
later
RFC,
41
69.
E
So
that's
that's,
basically
the
the
bigger
issues
in
in
in
this
draft
or
issues
or
things
that
we
had
done
in
the
in
the
previous
round
and
and
where
we
are,
would
love
to
get
feedback
and
discussion.
There's
someone
going
discussion
also
with
some
3gpp
people
are
being
able
to
at
least
interact
with
some
some
other
implementers
we're
implementing
some
of
this,
but
there's
also
others
that
do
this
and
like
going
back
and
forth
like
what
do
you
put
in
the
identifier
fields
has
been
useful.
E
We're
also
trying
to
add
a
reference
to
this
draft
to
3gpp
specs,
we'll
see
if
that
happens,
hopefully
they're
having
a
meeting
next
week.
I
think,
and
we
think
we
understand
now
the
interactions
between
the
3gpp
specs
and
and
this,
and
maybe
this
it's
worthwhile
to
note
that
like.
Why
do
we
have
to
do
anything
to
begin
with,
like
you
know,
if
they
just
use
your
your
RFC
like?
E
What's
the
problem
and-
and
that
would
not
have
been
a
problem
if
they
just
use
the
RFC,
but
they
actually
wanted
to
use
the
RFC,
but
do
these
and
these
changes
and
behave
in
this
slightly
different
manner.
So
that's
why
we
have
to
Tran
sync
up
because
the
the,
if
we
don't
sync
up
and
then
the
result,
is
that
the
RFC
will
say
something
and
possibly
some
implementations
will
fall
the
RFC
and
not
do
the
five
G
thang.
A
Now
the
draft
is
up
to
date,
kind
of
discussions
and
things
that
you've
had
in
3gpp
and
elsewhere.
Yeah
is
is
any
how
many
people
have
read
this
5448
Biss
or
any
any
version
or
later
the
better?
But
okay,
would
some
of
you
be
able
to?
If
we
do
a
working
group
last
call,
can
you
give
a
review
of
the
latest
changes?
H
E
E
We've
discussed
about
this
extensively
last
time
also
I
have
taken
into
account
reviews
or
discussions
that
we
had
last
time
and,
for
instance,
mo
its
review
and
and
and
this
person
is
more
detailed.
We
also
renamed
the
attributes
and
made
the
protocol
use
the
e
cd8,
the
8e
terminology
and
RFC
80
31
terminology,
and
we
clarified
the
use
of
the
negotiation
process.
We
only
send
one
key
if
there's
like
negotiate
groups
of
algorithms
and
and
so
on,
so
we
never
send
like
multiple
keys.
B
E
This
protocol,
then
it
will
just
ignore
this
and
continue
us
as
it
does
normally,
if
that's
allowed
by
the
the
parties.
But
if
it
doesn't
and
and
want
to
do
this
protocol,
then
it
also
picks
its
private
information,
generates
a
public
key
and
there's
some
calculations
and
since
the
public
key
to
the
other
side,
it's
also
does
some
calculations
based
on
the
private
information
and
and
the
other
side's
public
information.
E
E
There
are
some
tricky
parts,
though,
so
one
is
backwards,
compatibility
that
I
already
talked
about
a
little
bit
how
to
avoid
change
this
or
how
to
run
in
in
different
kinds
of
environments.
Very,
not
everybody
may
be
supporting
this
yet
and
how
to
minimise
changes
all
over
there's
some
negotiation
issues
with
both
like
how
do
you
negotiate
if
you
have
support
multiple
algorithms
or
groups,
and
and
since
there's
already
negotiation
processes
in
in
the
EAP,
a
K
Prime?
E
So
we
tried
to
do
this
on
the
phone
and
then
on
the
network
side.
We
try
to
put
it
on
the
EAP
server
code,
not
not
there,
not
the
server.
That
holds
the
permanent
secrets,
so
this
keeps
the
interface
sim
card
in
the
authentication
database
unchanged
and
no
changes
to
the
minimum,
minimal
changes
to
infrastructure
and
no
changes
to
credentials.
But,
of
course
you
have
to
change
the
port.
You
have
to
update
the
phones,
have
to
update
the
EAP
server.
A
E
A
A
You
don't
have
because
yeah
all
right
I
mean
that
might
be
something
to
have
a
little
bit
of
a
discussion
about
and
CFE
I
I.
Don't
know
what
benefit
you
would
necessarily
get
from
me
for
encryption
either.
But
I
mean
you
would
get
the
benefit
of
the
encryption,
but
how
important
that
is
in
this
scheme,
but.
A
E
Encryption
that
you
would
get
like
it's
actually
I
think
it's
not
not
that
like
there's
other
ways
of
doing
this,
but
I
think
the
benefits
always
but
then
like.
If
you
just
do
like
a
EAP
level,
negotiation
I,
don't
think
you
actually
get
any
benefit
from
that.
It's
just
do
the
same
thing,
but
then,
but
if
you
reorganize
the
messages
in
some
other
fashion,
that
you
did
like
a
little
bit
like
Ike,
v2
or
actually
one,
that's
the
first.
E
E
E
That
indicates
the
the
preferred
algorithm
is
the
first
one
and
then
the
possible
other
algorithms
and
server
sends
this.
And
if
the
preferred
algorithm
acceptable,
then
the
peer
just
executes
this
protocol
and
and
proceeds
and
there's
no
RTT
here.
But
if,
if
you
do
want
to
do
some
of
the
other
ones,
not
the
preferred
algorithm
by
the
server,
then
then,
then
the
peer
indicates
that
I
want
this.
This
other
thing
instead
and
then
the
server
responds
and
then
there's
some
special
rules
that
you
like
you.
You
carry
the
the
old
irrelevant
information.
E
E
They
exact
exactly
the
same
process
just
that
they're
negotiating
a
different
thing
and
they're
currently
defined
as
separate
like.
If,
if
you
have
to
do
the
negotiation,
then
you
do
one
and
then
you
do
the
other
one
after
that,
in
theory,
we
could
probably
define
this
to
happen
also
in
parallel,
but
maybe
that's
not
worth
our
time
seems
simpler.
This
way
people
have
opinions.
Otherwise,
then
talk
about
that.
E
Denial
service
and
and
Hannes
had
this
question
last
time
and
Russ
I
think
you
were
also
commenting
on
that
that
about
the
order
of
computations
and
that
was
actually
partially
in
the
draft
already
last
ICF
I
wasn't
entirely
there
and
now
we
have
all
of
that
there
and
and
also
talked
about
it
in
the
security
considerations
and
here's
the
deal.
So.
E
The
first
message
in
this
whole
protocol
comes
from
the
server
and-
and
it
doesn't
come
unless
you
like
we're
already
identified
that
this
is
this,
is
the
given
subscriber
or
that
like
we
haven't,
authenticated
the
subscriber,
but
but
we've
seen
a
valid
user
name
and
you
can
spoof
this,
but
it
requires
that
attackers
at
least
use
specific,
real
identities.
They
can't
just
randomly
generate
numbers
and
and
try
and
use
them.
E
So
that's
first
level
of
defense
and
the
second
level
of
defense
is
that
once
you
get
the
messages,
then
all
the
parties
at
both
on
the
pier
and
the
server
side.
They
will
first
do
the
the
old
process.
They
will
authenticate
using
the
long
term
shared
secrets
and
make
sure
that
that
that
succeeds,
and
if
it
doesn't
succeed,
then
the
person
or
the
other
party
doesn't
have
the
right
key
and
therefore
this
is
an
attack
and
you
you,
you
bail
out.
They
never
do
the
expensive
computation.
It's
only
after
that.
E
I
E
E
So
the
Mac
I
I
think
the
Mac
is
it's
done
like
it's,
it's
done.
Ask
the
the
the
the
previews
or
the
original
RFC.
Does
that.
So
you
calculate
that
the
Mac
process
is
done,
that
that
is
step.
One
and
step
two
is
generate
the
keys
and
then
the
resulting
higher
quality
key
is
then
that
is
the
output
from
the
EAP
process.
So
now
your
traffic
protection
can
be
protected
with
this
higher
quality
keys,
but
your
Mac
will
still
run
on
the
original
process.
So
what.
I
E
E
Updated
the
security
properties
also
trying
to
be
accurate
here.
So
basically,
what
does
this
give
you?
It
gives
you
that
and
like
if
we
have
used
two
SIM
card
and
now
somebody
at
some
point
learns
the
key
then
and
and
and
that
somebody
has
recorded
all
your
previous
conversations
now.
You
can't
go
back
and
look
at
those
previous
conversations
and
decrypt
them,
because
PFS
was
was
in
effect
in
in
those
things
and
also
if
the
attack
you're
still
I
mean,
has
the
key
but
doesn't
do
active
attacks.
E
Then
future
communications
are
also
secure
and
then,
if
the
attacker,
who
has
the
long
term
key,
is
also
an
active
attack,
then
nothing
can
be
done
like
they
can.
They
can
do
anything.
They
can
be
pretend
to
be
any
of
the
parties
they
can.
They
can
be
also
be
a
mitten
if
they
need
to
and
they
can
determine
the
session
keys
change.
The
negotiations
yeah.
E
Think
this,
at
least
from
our
aside,
would
be
interesting
to
see
this
working
group
document
again.
There's
this
window
of
thing
for
some
some
amount
of
time
into
the
future.
It's
not
not
the
next
week
thing,
but
for
the
next
half
a
year
or
something
like
that.
If
we
have
a
solution
in
this
space,
we
might
actually
be
able
to
stick
this
in
into
the
next
release
and
actually
have
an
effect
on
on
people's
security.
E
In
this
sense,
protection
from
the
organizations
that
try
and
spy
on
things
and
and
there's
some
some
interests
from
our
side.
Certainly
and
then
another
manufacturer
working
on
the
chipsets
may
be
also
interested
on
this.
So
we
might
actually
get
this
actually
deployed.
If
we
do
do
it,
so
I
would
love
to
move
forward
on
this.
So
that's
the
end.
G
J
J
Okay,
so
I
wanted
to
tell
about
this
EAP
method
called
EAP,
noob
and
nimble,
out-of-band
authentication
for
EAP
and
what
it
does
is
it's
a
bootstrapping
method
for
smart
appliances.
Now
there
are
many
of
those,
but
this
is
an
EAP
method
and
we
have
worked
on
this
for
quite
a
couple
of
years
and
we
had
a
version
4
of
the
draft.
The
specification
starts
to
be
pretty
complete,
but
there's
still
some
things
to
do
and
then
to
review
and
document
about
the
design
process.
J
J
What
method
of
authentication
do
we
use?
Well:
user,
assisted
out-of-band
authentication
and,
for
example,
in
the
our
implementations,
this
has
been
a
dynamic
QR
code
or
dynamic
NFC
tag
and
in
addition
to
to
just
authenticating
the
device
once
this
method
also
registers
new
devices
to
the
authentication
server.
So
you
don't
want
to
let
the
user
every
time
you
want
to
connect
to
them.
J
Let's
say
Wi-Fi
network
to
redo
this
process,
but
but
once
and
then
we
create
a
permanent
association
for
that
device,
and
that
association
then
authorizes
the
device
in
the
future
for
network
connectivity
and
it
gives
that
device
an
owner
and
an
assigns
a
network
to
it.
So
it's
a
two-way
authentication
process
and
then
trust
relation
that
is
created.
J
J
So
here
is
the
protocol
architecture
and
we
have,
as
usual,
in
this
case
a
Wi-Fi
network
and
with
an
access
point,
and
then
we
have
these
IOT
appliance.
That
would
like
to
join
the
network
and
we
have
some
triple
a
server
like
radio
server
locally
on
the
network.
In
in
our
use
cases,
we
have
kind
of
thought
that
the
actual
server
that
does
the
authentication
is
a
remote
Triple,
A
server,
maybe
in
the
cloud
maybe
on
site,
but
is
it's
a
separate?
You
know
Triple
A
server
that
implements
this
EAP
noob.
J
You
out-of-band
miss
it's
processing
and
the
user
interface
for
that
and
okay.
So
so
what
what's
the
point
of
this?
Well,
we
use
the
EAP
tunnel
for
in
band
or
the
communication
with
the
authentication
server.
So
that
way
we
are
actually
actually
the
appliance
is
able
to
talk
with
the
authentication
server
before
it
is
registered
on
the
network
or
register
at
authentication
server
and
before
it
has
a
full
net
internet
connectivity.
So
that's
the
main
trick
that
we
are
playing
here
and
how
do
we
achieve
this?
J
Well,
the
device
initially
uses
this
network
access
identifier
loop
at
EAP,
new
dotnet,
because
it
doesn't
yet
know
what
identifier
it
will
have
and
then
we're
out
the
those
I,
though,
that
really
to
this
special
triple-a
server
that
supports
our
protocol
and
then
the
out-of-band
communication
happens
there.
That's
why
we
need
this
kind
of
special
server,
because
it
needs
to
have
a
UI
or
API
for
delivery
of.
B
J
Out
of
nine
messages,
so
here
in
the
picture,
there's
a
single
out-of-band
message
from
the
from
this
appliance
through
the
user
to
this
UI.
If
it's,
if
it's
manual
configuration
or
api,
if
the
user
is
using,
it's
a
smartphone
with
add
to
a
system,
and
so
there's
just
single
message
in
one
single
direction
that
has
been
our
design
goal
and
that
message
couldn't
be
could
be
in
also
in
the
server
to
peer
direction.
So
we
wanted
to
make
the
protocol
as
generic
as
possible
and
to
allow
both
directions
for
this
out-of-band
methods.
J
J
Okay,
so
wait
has
to
see
what
kind
of
security
do
we
get
here?
Where
does
the
security
come
from?
Well,
we
had
this
one.
We
wanted
to
have
a
like
minimal
assumptions
in
the
protocol
on
the
out-of-band
methods,
and
so
it's
just
one
message
in
either
direction
from
server
to
pierre-pierre
server,
and
we
assume
that
the
autopen
channel
will
provide
either
integrity
or
secrecy,
but
we
don't
require
both.
J
But
of
course
we
it's
I
would
say
it's
better
to
have
both,
but
if
you
think
of
let's
say
you're
scanning
a
QR
code,
someone
could
be
spying
on
that
QR
code,
so
it
might
not
be
so
securely
secret
and
then
it's
the
only
the
integrity
that
remains
the
protector
security.
So
it's
kind
of
for
failure
fail
safety.
J
Well,
another
concern
that
we
have
had
in
the
last
year.
We've
spent
a
lot
of
time
on
modeling
this
protocol
and
and
verifying
its
properties
and
then
the
main
concern
we
had
was
this
denial
of
service
attacks
by
someone
a
man-in-the-middle
attack,
err
on
the
network
on
the
inbound
channel
like
on
the
wireless
network,
who
could
call
maybe
they
could
cause
persistent
failure
of
the
protocol
and
and
I
hope.
It's
not
I,
feel
so
powerless.
J
Okay,
so
that
man
in
the
middle
attacker,
especially
it
could
temper
messages
or
it
could
drop
messages,
or
maybe
it
could
prove
error,
messages
and
use
that
for
causing
din
our
service
and
and
we
we
can't
avoid
that.
But
but
we
want
to
avoid
persistent
in
our
service.
If
the
attacker
then
goes
away.
J
So
here
is
a
use
case
to
get
an
idea.
What
is
this
useful
for
so
secure
boot?
Stepping
of
cloud
manage
displays-
and
this
was
our
initial
use
case-
that
motivated
the
work.
So
here
is
a
comic-strip
there.
There
is
alice
with
attaching
displays
to
the
wall.
Powers
are
one
of
those
new
displays.
The
display
doesn't
know
where
it
is
it
scans.
The
wireless
networks
looks
for
support
for
EAP
noob
when
he
finds
that
kind
of
network
it
connects
to
that
network.
J
There
happens
to
be
just
one
in
this
case
and
and
the
initial
exchange
for
the
protocol
happens
in
the
background
it
gets
a
QR
code.
They
said
this
is
the
out
of
hand
message
now:
the
QR
code
shown
to
the
to
Alice
and
Alice
scans,
the
QR
code,
with
a
smartphone
which
may
or
may
not
have
an
app,
so
it
just
needs
to
be
capable
of
scanning
QR
codes
and
a
web
browser
will
be
then
open,
but
but
it's
kind
of
there's
all
kinds
of
tricks
against
the
user
facing
type
attacks.
J
So
it
would
be
a
little
bit
better
if
there
is
an
app,
but
it's
not
required,
and
then
the
user
has
to
either
be
already
logged
in
on
the
cloud
server
or
or
will
enter
the
login
credentials,
and
that
magically
attacks
is
the
device
to
the
cloud
service
and
and
then
enables
network
access,
because
the
cloud
service,
now
the
remote
a
triple
a
server
and
and
now
the
display
starts
in
our
implementation.
Then
start.
It's
also
gets
this
application
layer
configuration
and
starts
displaying
some
content.
J
Just
just
a
display
obviously
has
output
and
the
user
has
the
smart
smartphone
and
then
what
we
need
to
have
in
the
background
is
that
the
remote
Triple
A
server
is
configured
with
that.
Well,
the
local
police
trust
it
for
authentication.
This
EAP
noob
not
met
any
eyes
and
and
also
in
this
case,
the
the
multiplayer
server
is
integrated
with
the
application
level
display
man,
it's
been
serviced,
and
here
this
still
shows
the
same
comic.
With
the
protocol
steps
like
the
initial
exchange
with
EC
the
AIDS
happens.
J
In
the
background,
then
the
outer
band
message
is
shown,
the
user
scans
it
it's
delivered
as
through
the
URL
to
the
cloud
server
the.
If
it's
a
web
browser.
The
user
here
needs
to
check
that
it's
the
correct
cloud
server
that
that
she
has
an
account
to
and
then
log
in,
and
then
there
is
the
final
key
confirmation
that
happens
and
again
in
the
inbound
channel
without
the
user
noticing
anything.
J
J
That's
a
server
allocated
identifier
that
just
helps
the
server
to
to
know
with
which
messages
it
belongs
to
which
peer,
and
then
there
is
the
two
two
fields
noob
and
hub,
and
the
noob
is
the
secret
knowns
and
Huub
is
the
has
of
the
ECD
age
parameters
they
can
all.
This
can
be
encoded,
for
example,
and
any
respect
week,
so
an
example
how
to
encode
it
as
a
URL
and
that's
a
important
thing
to
know
that
is
a
dynamic
URL,
so
it
will
change
for
every
after
every
initial
exchange.
It
will
change.
J
So
let's
say:
if
it's
a
display,
you
configure
it
might
change
every
minute
or
so,
and
so
it
can't
be
a
printed
QR
code.
It's
a
dynamic,
QR
code
or
dynamic
NFC
tag
and
in
this
noob
is
the
part
that
requires
confidentiality
and
hope.
The
part
that
needs
integrity-
and
one
of
those
is
enough
to
get
say,
I
get
security
here.
J
Well,
when
we
create,
we
create
this
persistent
user
association.
So
we
don't
want
to
repeat
this
authentication,
and
this
is
kind
of
one
place
where
the
the
method
differs
from
typical
EAP
methods
that
you
have
some
method
of
authentication
and
you
keep
repeating
that.
But
we
can't
do
that.
We
can't
trouble
the
user
every
time
the
the
device
gets
disconnected
from
the
wireless
network.
So
we
must
create
a
persistent
Association
and
then,
basically,
at
all
cost
avoid
returning
that
out-of-band
step
and
authenticate
with
this
association
that
was
created.
J
J
The
device
can
additionally
send
in
this
protocol
as
there's
a
peering
fulfill.
It
can
send
some
other
information
about
its
capabilities.
Like
its
brand
and
type
and
so
on,
but
that
information
is
something
that
is
authenticated
in
the
sense
that
it
is
sent
by
that
specific
device.
But
it's
not
authenticated
in
the
sense
that
user
has
to
verify
that
that
the
device
itself
is
not
lying
English.
If
you
don't
trust
or
all
your
IOT
device,
it's
not
to
lie.
So
if
the
device
stays
I,
don't
have
a
camera,
it
might
still
have
a
camera.
J
Well,
the
Association
we
obviously
in
the
use
case.
We
used
it
for
bootstrapping
application
security,
so
that
method
can
export
keys
to
the
application
layer,
and
we
also
have
used
it
to
convey
initial
application
layer
configuration
to
the
peer.
Although
I
now
realized
this
during
this
meeting
that
that
we
actually
need
to
clarify
how
to
do
that
and
then
maybe
make
it
clear
in
the
spec.
J
And
if
you
compare
this
with
I
mean
to
me
it's
essential
that
we
bootstrap
the
application
security
with
the
same
step,
because
that
was
our
in
this
celebrate
that
when
we
configure
these
devices
like
this
place,
you
often
have
to
first
enter
wireless
credentials,
tediously
to
to
a
IOT
device
and
then
configure
some
cloud
credentials
for
connecting
it
to
the
cloud
picture.
They
have
network
access
and
then
the
cloud
connection,
and
if
we
skip
one
step
here,
then
we
are
kind
of
only
halfway
through
roaming.
J
We
have
added
this
option
for
the
server
to
send
a
list
of
SSID
so
that
in
a
distant
or
instead
of
the
SSID,
where
you
currently
configure
the
device,
you
know
that
you're
persistent
association
will
be
valid
also
on
this
other
edge
society.
It's
so,
for
example,
if
I
configure
the
device
on
my
University
Network,
then
it
would
store
the
the
association
would
also
be
valid
for
Eddie,
and
the
server's
can
allocate
a
real
them
for
this
purpose
for
the
device.
J
J
That
says
it's
a
things
like
those
papers
just
lie
around
and
there's
lots
of
them
around,
and
one
of
them
eventually
gets
delivered
to
the
to
the
server
and
another
case
where
you
have
multiple
messages
in
flight.
Is
that
the
the
we
support
both
directions
peer
to
server
and
server,
appear
for
the
out-of-band
methods
and
and
never
thought
that
that
anyone
would
want
to
support
both
directions?
But
then,
out
with
when
you
think
about
it,
someone
might
be
crazy
enough
to
implement
the
device
that
allows
both
directions,
that
the
protocol
allows
both
directions.
J
J
And
then,
as
I
mentioned
in
the
previous
slide,
there
could
be
multiple
users
delivering
other
men
messages
to
different
servers
and
and
with
with
behind
different
wireless
networks
and
and
they
compete
for
the
device.
And
we've
worked
out
these
different
cases
of
multiple
messages
in
flight
and
verify
this
to
check
that
that
there
is
no
no
deadlocks
caused
by
by
these.
J
But
since
we
we
decided
that
we
don't
want
to
bother
the
user
to
redo
them
out
of
pen
step
again,
in
any
case
where
we
can
avoid
it.
We
wouldn't
want
to
bother
the
user
even
when
the
crypto
suit
needs
to
be
updated
and
the
so
the
normal
solution.
When
you
update,
let's
say
signature,
the
crypto
algorithm
for
signature,
keys
for
someone's
credit
and
so
see
also
is
your
new
certificate
and
that's
a
kind
of
administrative
process
and
a
human.
J
You
is
involved
in
that
or
some
some
another
layer
level
of
credentials
for
deploying
it,
but
we
don't
want
to
do
that.
So
we
want
that's
why,
in
the
reconnect
exchange,
may
negotiate
a
new
crypto
suit
and
update
the
persistent
Association
keys,
but
this
leads
us
to
the
really
interesting
stuff
where
the
crypto,
so
that
update
might
fail,
but
it
might
fail
so
that
it
fails
for
one
end
and
succeeds
for
the
other
end.
J
So
the
issue
here
is
still,
if
the,
if
you
are
doing
a
crypto
suit,
upgrade
in
the
reconnect
exchange
and
then
the
last
message,
which
will
be
the
final
EAP
response
that
is,
dropped.
The
pier
will
move
to
the
new
crypto
suit
because
it
thinks
all
is
ok.
But
the
server
will
never
receive
that
final
message
and
it
will
keep
the
old
cryptic
and.
J
J
And
when
does
it
get
that
confirmation?
Well,
the
next
time
it
does
rekeying.
So
if
it,
if
the,
if
they,
if
the
synchronization
failure
happens.
Obviously
the
peer
cannot
connect
to
the
to
this
network,
and
then
it
tries
immediately
to
reconnect
and
that's
when
either
they
will.
The
peer
will
discover
the
servers
in
the
previous
crypto,
so
it
or
it
is
in
the
new
one,
and
then
it
only
keeps
that
one
and
there,
although
all
the
attacker
can
do,
is
it
can
again
drop
the
final
message
and
then
it's
the.
J
One
note
about
the
isolating
the
peer
devices,
so
the
so,
if
you
think
of
devices
that
connect
to
connect
to
this
wireless
network
and
and
you
you,
let
users
configure
new
devices
and
connect
them
to
the
network.
Well,
they
might
connect
all
kinds
of
devices
to
it
and
especially
like
any
out-of-the-box
device
that
supports
EAP
new
band
and
buy
it
from
the
shop
and
and
just
that,
that's
it
to
your
local
network.
J
Also,
we
in
some
in
our
use
cases
we
delegate
the
control
over
this
network
access
to
some
cloud
server
which
may
be
provided
by
a
third
party.
So
if
it's
not
your
own
own
remote
authentication
server,
but
but
some
external
service,
then
yeah
kind
of
trusting
access
to
your
wireless
network
to
them
and
obviously
corrupt
devices.
Iot
devices
might
leak
the
network
credentials
I'll.
J
Let
anyone
on
your
wireless
network,
so
we
think
that
it's
quite
quite
very
important
to
isolate
these
devices
to
a
virtual
LAN
and
that
so
that
they
don't
get
in
touch
with
your
regular
hosts
on
the
network,
preferably
isolate
them
from
each
other
as
well.
But
the
current
access
points
and
and
radio
servers
don't
really
support
that
speed
source
as
far
as
I
know,
but
we've
managed
to
implement
it
on
on
open,
open
source
radios
and
open
wrt
access
points.
J
J
Well,
the
trick
here
is
that
the
EAP
allows
us
to
do
the
inbound
communication
with
the
north
indication
server
in
the
back
in
the
network
internet
or
on
your
back
in
network
before
you
have
network
connectivity,
and
thanks
to
that,
the
autopen
communication
can
be
one
short
message
and
in
any,
if
you
don't
use,
have
this
kind
of.
If
you
don't
use
the
EAP
tunnel,
you
usually
have
to
communicate
much
more
information
and
then
the
out-of-band
messages
in
our
protocol
is
designed
so
that
it
should
should
get
either.
J
The
outer
band
channel
should
provide
either
secrecy
or
integrity,
but
but
if
one
fails
we
are
still
ok
and
then
kind
of
you
can
ask
like
we
get
this
magic
attachment
to
the
network
with
with
just
scanning
one
QR
code.
But
what's
the
cost
here
and
of
course
one
thing
is
that
we
need
EAP
and
and
Triple
A,
and
that
means
WPA
enterprise,
so
not
passphrase
networks
and
then
the
main
thing
is
that
the
network
had
been
has
to
choose
ones.
J
F
F
Meetings,
wiki
and
I
want
to
look
to
address
like
there's
a
series
of
IOT
onboarding
work,
that's
going
on
across
the
organization
and
and
so
I
want
us
to
get
our
hands
around
all
of
it,
but
I
would
definitely
support
if
it's
possible
to
use
the
EMU
working
group
wiki
to
track
issues
here
with
us
and
I
look
forward
to
working
with
you
to
try
and
find
the
common
architectural
components
on
these.
Okay.
K
Eric
nor
mine
yeah-
this
is
very
interesting
and
I.
Ain't
think
I
have
other
use
cases
from
the
output
devices,
just
an
LED
that
can
blink,
but
you
can
have
your
phone
receive
that
stuff.
Somehow
one
question
I
had
was
so,
can
you
do
mutual
authentication?
Can
you
authenticate
to
place
or
wear
this
as
well
as
long
as
the
device
has
some
credentials?
It
knows.
K
J
So
it
is
mutual
authentication.
The
device
is
authenticated
as
a
physical
device.
It's
the
autumn.
Identity
of
the
of
the
device
is
defined
by
which
device
where
the
user
reads
or
writes
the
out-of-band
mess.
It's
it's
a
physical
device
that
the
user
accesses
turn
that
part,
but
the
tree
server
as
well
people
a
server.
So
here
the
user
is
assumed
to
have
some
way
or
secure
channels
that
he
plays,
or
it
could
be,
of
course,
physically
if
it's
a
home
network
and
some
device
hub
at
home.
J
B
J
L
To
follow
up
on
that
because
I'm
with
him,
you
mentioned
on
one
of
your
slides
that
if
you
don't
know
which
a
server
to
talk
to
you
just
talk
to
them
all
yeah
now
that
is
conserved
now
what
QR
code
do
you
present
at
that
point?
Because
you
have
you,
have
three
you've
got
two
evil
triple
a's
that
you're
talking
to
and
the
real
triple
a
and
just
h1.
J
It'll
play
well,
the
display
shows
them
so
these
three
codes
and
if
the
user
somehow
is
trick
to
choosing
the
wrong
one,
then
it
doesn't
really
do
anything.
Well,
there's
no
baby,
because
he
because
it's
the
correct
server
that
you're
delivering
it
that's
the
important
thing,
but
but
I
mean
this
will
have
the
the
cure
code
has.
But
in
our
case
we
write
the
text
there.
The
base
URL
under
the
QR
code
right.
J
M
J
N
F
But
you
haven't
been
abducted,
hi
Elliot,
your
last
meeting
Owen
presented
on
something
that
we've
been
tossing
around,
which
is
to
take
the
brewski
work.
That's
been
done,
the
bootstrapping
key
infrastructure
work
and
apply
it
into
eat
so
problem
statement.
It
was
pointed
out
that
maybe
we
didn't
do
as
good
a
job
on
a
problem
statement
as
we
should
have
in
the
previous
presentation.
So
these
are
basically
a
couple
of
reasons
why
we
went
there
and
I'll
set
this
through
in
just
a
handful
of
slides.
This
is
a
very
short
presentation.
F
The
the
key
issue
is
that
we
need
a
trusted
introduction
between
a
device
and
local
deployment,
absent
that
trust.
An
introduction
device
is
going
to
join
the
wrong
network
or
they
make
it
they
may
do
so
either
out
of
incompetence
or
malice
depending
and
I.
Think
everybody
in
this
room
understands
that
problem.
F
Brueski
provides
for
a
truss
city
introduction
and
it's
a
certificate
based
method
at
this
point,
and
it
also
relies
on
a
third
party,
which
is
to
say
the
manufacturer
you
go
out
to
the
internet.
Manufacturer
says
I,
you
know,
device
has
got
a
I'll,
explain
the
flow
in
a
minute.
Actually
so
I'll
go
through
it
once
you
have
a
trust
anchor
in
brewski,
you
go
and
you
do
an
EST
transaction.
You
got
yourself
a
local
deployment
cert
and
both
of
these
mechanisms
assumes
some
amount
of
network
on
ik
TV.
Really
it's
internet
kind
of
really.
F
That's
not
only
network
connectivity
via
never
conductivity
of
the
device,
but
it's
also
internet
connectivity
as
it
turns
out
in
terms
of
brewski,
and
you
just
don't
have
the
network
connectivity
in
802
11.
Obviously
it's
a
you
have
a
chicken-and-egg
problem
there,
and
so
of
course,
we
looked
at
eat
for
the
exact
same
reasons
that
the
new
folks
looked
at
eat.
F
We
thought
was
pretty
cool
and
for
the
exact
same
reasons-
and
in
fact
we
thought
t
p--
was
even
cooler
because
it
covers
a
fair
amount
of
this
ground
already
and
it
just
needs
a
little
bit
of
tweaking
keep
tweaking.
So
here's
an
eye
here,
here's
an
eye
chart
for
you.
This
is
actually
on
the
materials
page
units.
Look
at
this.
F
This
is
the
basic
anima
flow,
where
you
establish
what
we
called
provisional
trust,
it's
directly
analogous
to
what
noob
does
in
many
respects
and
what
you
do
is
you
go
through
in
a
transaction
in
which
you
go
where
essentially,
the
local
deployment,
which
is
the
switch
and
the
registrar?
Really
the
registrar,
goes
and
asks
the
manufacturer?
Is
this
one
of
your
devices,
the
manufacturer
would
say
yeah
it
is
or
no
it's
not,
and
it's
essentially
sign
a
voucher
request,
which
you
know
then
gets
returned
as
a
voucher
which
the
pledge
can
then
use
to
say.
F
Yes,
okay,
I
should
join
this
network
and
here
are
the
credentials
for
that
network,
and
then
you
go
through
and
EST
transaction
again
yeah.
This
problem,
which
all
that
was
IP
based
s--,
worked
on
an
anima
group,
and
so
we
have
a
little
problem
there.
If
you
don't
have
IP
connectivity
yet
so,
what's
the
idea
shove
the
whole
thing
into
each
flow?
F
I
am
NOT
going
to
go
through
the
Holi
flow.
Today
you
can
read
the
draft,
but
the
basic
idea
is
that
we're
you
know
we're
leveraging
eat.
Teep
we've
created
just
a
handful
of
new
TLDs
that
one
would
use
to
do
this
and
the
differences
between
this
version
and
last
version
is
that
we've
created
it
even
a
handful
less
than
we
thought
we
needed
in
this
version
and
so
we're
trimming
down,
and
so
we,
the
the
other.
F
The
other
difference
is
that
we
actually
documented
out
all
the
tlvs
that
we
think
we
need
and
I
added
a
Ayanna
considerations
to
match
the
the
flows
themselves
have
been
updated
because
in
the
process
of
defining
anity,
all
these
that's
how
we
found
out
you
can
piggyback
messages
and
Eve.
Isn't
that
so
lovely?
So,
let's
condense
here
and
here
here
we
have,
and
so
obviously,
if
you
look
at
the
security
sick,
you
know
consideration
section,
it
says
TBD.
G
F
Means
we're
nowhere
near
ready
for
adoption,
we're
working
group
adoption
we're
just
we're
just
not
there
yet,
and
we
think
there
are
some
in
the
process
of
doing
this
draft
and
there
possibly
and
also
the
process
of
looking
at
new
and
in
the
process
of
looking
at
DPP
as
well.
Actually,
we
think
we've
come
across
what
we
see
as
some
architectural
questions,
and
so
one
of
those
is
that
there
there
seems
to
be.
F
We're
not
asking
for
working
group
adoption
for
one
thing:
I
would
like
to
look
across
the
five
or
six
different
working
groups
at
this
organization
and
then
five
or
six
organizations
that
are
looking
at
this
entire
problem.
We're
seeing
fragmentation
because
of
this
and
to
just
take
a
step
back
for
a
moment,
pause,
take
a
breath
and
say
what
are
the
common
architectural
components?
F
F
I've
got
about
a
half
hour
to
talk
about
all
of
this
I'll
try
and
speed
talk
a
little
bit
even
in
that,
so
that
we
have
more
time
for
discussion
and
less
time
for
Elliott
blabbing
on
and
then
please
come
to
the
side
meeting
tomorrow
evening.
It's
an
apartment.
Three.
On
the
ninth
floor,
we
only
have
a
12
person
room,
but
that's
okay,
I
figure.
If
100
people
show
up
we'll
just
switch
rooms
with
someone
or
have
the
meeting
in
the
hallway,
like
we
usually
do,
that's
it
questions
comments.
A
F
O
Yusef,
just
provisional
TLS
connection
and
that's
going
to
be
completely
unauthentic
ated,
so
it
doesn't
provide
any
security
over
just
sending
the
the
brewski
voucher
request
and
getting
a
voucher
response
in
the
clear
right.
So
it
why?
Don't
you
just
make
instead
of
hacking?
Teep
just
make
a
brewski
and
send
a
voucher
request
to
get
a
budget
response
or
in
Arabic
Oh.
So.
F
Essentially,
brueski
does
the
exact
same
thing
and
what
the
way
that
the
provisional
thing
works
is
that
you,
the
the
what
you
have
to
do,
is
by
the
end
of
the
transaction.
You
have
to
have
been
able
to
authenticate
the
beginning
that
you
have
to
have
been
able
to
authenticate
the
credentials
that
were
used
in
the
in
the
beginning.
If
you,
if
at
the
end
of
the
brewski
transaction
you
could
not
have
you
have
not
received
the
appropriate
trust
anchor,
then
then
you
throw
away.
F
B
F
Pointer
on
the
sky,
so
there
is
okay,
so
essentially
so
here's
where
you
into
your
provisional
trust
state
right!
Yes,
okay-
and
at
this
point
we
you
at
this
point.
You
have
no
reason
to
trust,
which
is
why
you're
in
that
provisional
trust
phase.
In
fact,
that's
a
really
good
signal
that
that
says,
I
need
more
trust.
Let
me
go.
Do
some
brewski
or
something
like
that,
and
so
you
end
up
doing
a
request.
Voucher
I
think
we
might
even
be
able
to
nuke
that
guy,
but
I'm
not
sure.
F
You
you
end
up
doing
this
request
voucher.
Then
you
get
a
then
you
get
a
response
at
this
point
in
time.
You
should
be
able
to
have
validated
the
the
server
hello
if
you're
the
client
right,
at
which
point
you're
no
longer
in
provisional
trust
mode.
So
I
won't
claim
to
be
the
perfect
expert
on
this
trust
model.
That's
the
work
of
Max,
Pritikin
and
and
Kent
and
Michael
Richardson,
but
I'm,
essentially,
borrowing
that
model
wholesale.
So.
F
O
F
H
N
N
O
F
P
F
F
G
A
F
I
plan
to
take
this
up
in
you
know
separate
context,
so
I
think
there's
an
it's
important,
that
the
new
draft
have
a
place
to
do
that,
and
also
this
one
as
well.
If
it's
not
with
you
guys,
then
we'll
sort
that,
with
the
you
know,
I'll
talk
to
some
of
the
iesg
members
to
see
if
we
can
find
the
right
place
and
I'm
willing
to
discuss
that
too.
It's
yes,
you
know
this
is
a
solvable
problem.
I
wouldn't
worry,
I'm,
quite
certain.
We
can
solve
this
one,
all
right,
that's
it
for
now!
