►
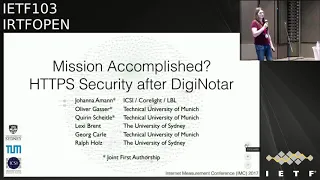
From YouTube: IETF103-IRTFOPEN-20181105-1610
Description
IRTFOPEN meeting session at IETF103
2018/11/05 1610
https://datatracker.ietf.org/meeting/103/proceedings/
A
A
A
A
A
She
is
yes,
yeah
she's
I
had
to
stay
home
to
deal
with
the
family
situation,
so
we're
sitting
in
for
her.
So
your
your
indulgence
consider
it
begged
for
okay,
if
you,
if
you've
been
here
before
you
recognize
this,
if
you
haven't
you
might
not,
this
is
essentially
the
IP.
Our
policy
we're
under
substantially
the
same
IPR
regime
as
IATA
IETF,
but
there
are
some
minor
differences,
so
note,
well
a
more
policy
on
there's
going
to
be
a
lot
of
photography
here
today,
because
we've
got
our
ARP
winner,
no
map,
no,
no
photographs.
A
Right
and
for
research
group
chairs
I,
who
are
meeting
later
this
week,
please
don't
forget
to
include
the
note
well
in
New
York,
and
your
slide
sets
for
those
who
aren't
familiar
with
the
IRT
F
on
the
mission
is
to
focus
on
longer
term
research
issues
related
to
the
internet.
In
parallel
with
the
IETF,
they
focus
on
engineering
and
standards,
making
we
focus
on
research
or
organized
into
topical
research
groups,
which
are
parallel
to
in
some
cases,
but
different
from
work.
A
Working
groups,
IETF
working
groups,
the
instead
of
having
an
ie
SV,
were,
and
we
have
an
Internet
research
steering
group.
It's
mostly
the
research
shares
in
a
small
number
of
at-large
members,
including
Spencer
right.
So
we
do
not
produce
standards
at
all
period.
We
do
produce
documents,
some
of
which
may
be
published
as
RFC
s
and
those
will
be
experimental
or
informational.
A
Okay,
these
are
our
research
groups.
These
are
all
probably
familiar.
There
are
a
couple
of
changes
from
the
last
time
we
met.
One
is
that
den
RG
is
now
a
full
research
group.
We've
been
promoted
and
there
are
two
new
groups
meeting
for
the
first
time
as
proposed
research
groups,
one
is
privacy,
privacy,
enhancement
and
assessment,
and
the
other
is
the
quantum
internet
research
group,
everybody's
meaning
except
ICC
IG
this
week.
A
Today's
excuse
me
today's
agenda,
as
I
mentioned
earlier.
Unfortunately,
Allison
is
not
with
us.
A
couple
of
things
are
coming
up
and
our
p
for
2019
nominations
are
due
November
11th,
so
I
get
those
in
we're
only
going
to
have
one
a
and
our
presentation
today
due
to
last-minute
visa
issue,
but
there'll
be
news
on
that.
The
talk
that
we're
going
to
have
today,
you've
probably
heard
about
it
and
fill
us
in
other
working
groups.
Today,
Johanna
Aman
is
going
to
be
talking
about.
A
A
Allison
Scott,
yes,
okay,
okay,
sometimes
people
confuse
nrw
and
a
and
RP
so
see.
Allison
provided
slide,
disambiguate
just
ambigú.
Writing
that
and
our
things
the
applied
networking
with
search
prize
on
it's
an
annual
call
for
nominees
based
on
papers
that
were
have
already
been
published
elsewhere.
The
applied
networking
was
workshop,
of
course,
is
a
workshop.
A
It
was
an
annual
call
for
papers
both
already
published
and
not,
and
then
presentations
are
given
in
a
day-long
workshop
co-located
with
the
summer
IETF
this
year
it's
going
to
be
in
July
in
Montreal,
I
should
say
in
2019,
okay,
so
we're
done,
and
if
there
are
no
questions
on,
let's
see
if
we
can
get
out
of
this,
we
escaped
doesn't
get
us
out
of
this,
but
yeah
Johanna
yeah.
As
soon
as
we
can
figure
out
how
to
switch
the
slides.
B
C
Okay,
it's
the
Sun,
yes,
hello!
Everyone
I'm
happy
to
be
here
as
thank
you
for
the
introduction,
so
my
name
is
Johanna.
I
am
a
researcher
at
the
international
computer
science
institute,
which
is
a
research
institute
that
affiliated
with
UC
Berkeley
and,
as
you
can
already
see
by
the
slashes
I
wear
several
hats.
I
am
simultaneously
also
an
engineer
at
a
startup
called
colloid
and
I
am
affiliated
with
the
cyber
security
department
at
the
Lawrence
Berkeley
National
Laboratory,
and
today,
I
am
going
to
give
a
talk.
That
is
basically
that
is
called
mission
accomplished.
C
C
That
kind
of
ties
into
this
research
too,
and
it's
also
about
TLS
one
thing:
this
work
was
done
together
with
a
few
other
people
at
the
Technical
University
of
Munich
and
the
University
of
Sydney,
and
one
thing
before
I
start,
so
this
set
up
is
a
little
bit
different
than
what
they
typically
have
because
typically
I
can
see.
The
next
slide
to
this
presentation
is
a
little
bit
long,
and
if
I
am
confused
a
little
bit
look
I've
confused
a
little
bit.
C
Sometimes
it
might
be
because
I
actually
am
because
I
have
no
idea
what's
coming
up
next,
because
I
have
a
lot
of
slides.
Okay,
let's
start
a
little
bit.
So
what
does
this
paper
about?
So
basically,
what
we
did
in
our
paper
is.
We
said
after
that,
did
you
note
our
incident?
What
did
change
and
more
specifically,
we
took
a
look
at
the
TLS
and
https
security,
extensions
that
mostly
came
up
after
digital
and
I.
C
Have
you
were
interested
and
how
deployment
actually
looks
like
in
practice,
and
we
picked
a
few
extensions
that
we
thought
the
most
important
ones?
What
specifically,
we
looked
at
certificate
transparency,
HTTP,
strict
Transport,
Security,
HTV
public
key,
pinning
the
TLS
4x,
signalling,
cipher,
suite
value
certificate,
authority
authorization
and
they
in
TLS
a,
and
how
did
we
look
at
this
B?
It
did
active
measurement
and
passive
scans,
so
active
measurements
means
that
it
basically
did
domain
based
measurements
of
the
internet
Concord
for
for
three
from
two
continents.
C
C
So
we
had
three
sites
which
we
got:
access
to
the
Internet
uplink
of
universities
and
very
looked
at
the
outgoing
TLS
connections
and
looked
how
certificate
transparency
was
used,
and
the
one
thing
that
was
quite
a
few
scientifically
interesting
about
this
work
is
that
we
had
an
active,
a
shared
pipeline
between
the
active
and
passive
scans,
because
until
s
in
academia,
a
lot
of
scans
have
been
done
before
both
active
and
passive,
but
they
typically
even
when
they
were
done.
Athenaeus
e
for
the
same
paper
did
not.
It
was
completely
different
software.
C
That
is
the
active
further
than
the
passive
card,
and
in
our
case,
what
we
did
is
basically
for
the
active
scans.
We
took
a
network
ties
of
the
entire
traffic
that
was
exchanged
by
the
machine
that
was
doing
the
scanning
and
shaft
that
ties
for
a
passive
measurement
pipeline
later,
where
it
was
possible
and
then
used
the
data
from
the
path
of
measurement
pipeline.
So
we
had
the
exact
same
source
code
running
for
both
the
active
scans
and
the
passive
measurements
later.
C
Think
in
April
this
year,
back
on
the
paper
was
open.
This
was
not
yet
being
enforced.
So
and
basically,
we
have
three
big
entities
interested
here,
which
are
the
certificate
authorities,
the
certificate
lock
and
the
browser,
and,
as
you
might
also
know,
there
are
several
ways
in
which
certificate
transparency
can
be
used
and
which
those
inclusion
dogs
can
be
transferred
to
the
client.
C
The
first
potentially
easiest
to
explain
method
is
that
you,
as
a
user,
request
a
certificate
and
get
the
certificate
from
the
CA,
and
if
you
want
to
give
out
a
certificate,
a
lot,
an
including
proof
of
certificate
transparency.
What
you
can
do
is
you
can
send
that
certificate
to
a
certificate
as
parent
see
certificate,
transparency
will
send
you
back
a
signed
certificate
timestamp,
so
the
inclusion
proof
and
when
a
vet,
but
also
connects
to
you
that
support
certificate
transparency,
you
can
send
that
poof
in
a
TLS
extension.
C
The
second
way
that
you
can
do
things
is
that
the
CA
basically
sends
the
information
to
a
certificate
transparency.
In
this
case,
the
CA
sends
a
pre
certificate
to
a
certificate,
transparency,
lock
server
and
a
pre
certificate.
Basically,
it's
just
a
certificate
with
an
additional
extension
that
says
that
it's
not
valid,
so
it
has
a
poisson
extension.
C
The
certificate
transparency,
log
I'm
science,
this
and
since
the
signature
back
to
the
CA,
the
CA
Daleks,
the
science
certificate
time
stamps
includes
it
into
an
extension,
puts
it
into
the
certificate
and
since
the
certificate
with
the
pre
certificate,
a
city
to
the
web
server
and
the
web
server
doesn't
have
to
do
anything
besides.
Sending
that
certificate
to
the
browser
and
the
powers
about
that
support.
Certificate.
Transparency
basically
does
the
reverse
process.
C
The
city
is
send
in
the
stapled
or
CSP
response
that
the
web
browser
can
then
use
to
validate
the
status
again.
So
we
basically
measured
how
much
we
see
certificate
transparency
being
used
in
practice,
and
so
these
numbers
from
2017.
So
these
are
a
year
old
panel
and
back
then
you
could
see
that
approximately.
C
C
What
you
can
see
here
is
that
most
of
these
contained
a
city
in
the
certificate,
though
there
is
also
a
significant
amount
of
cases.
A
sativa
sent
by
a
TLS
extension
or
CSP
is
a
little
bit.
He
said
the
what's
interesting
is
who
chooses
to
send
the
city
in
a
tie,
let's
examine
at
least
last
year.
This
was
mostly
Google
and
I
think
there
might
have
been
another
big
site.
That
does
that.
C
We
assume
that
whoever
chooses
to
do
this,
because,
if
you
send
the
scientific
a
time
stamp
as
a
tail,
as
extension,
you
can
basically
choose
if
you
send
it
or
if
you
don't
send
it.
So
if
you
have
a
mobile
client
connecting
to
your
site
and
the
mobile
client
does
not
send
the
I
support
sends
a
CT
extension
and
the
connection
you
can
just
skip
sending
the
few
hundred
bytes
of
data
and
they
are
not
contained
in
the
certificate
either,
which
might
make
your
hand
shake
a
little
bit
faster.
C
We
redid
this
measurement
tool
a
few
months
ago
and
what's
kind
of
interesting,
is
that
this
actually
hasn't
changed
all
that
much
it's
about
32%
of
connections.
Now,
all
that
contain
an
SCT,
but
it's
still
not
massively
more.
We
expect
this
to
change
rather
quickly
because
our
measurement
was
done.
Basically,
when
the
comb
changes
started
to
go
into
effect,
but
they
don't
go
into
effect
for
all
certificates
only
for
new
ones.
So
the
certificates
have
to
first
time
our
for
us
to
see
big
changes.
In
any
case.
C
How
does
this
look
like
in
practice?
So,
if
you
using
go
back
home
and
go
into
a
development
mode,
you
can
see
the
certificate
transparency.
It
pulls
that
transferred
here
on
the
right.
So
in
this
case
we
have
a
certificate
that
has
a
bunch
of
valid
polls
both
in
the
certificate
and
sent
via
the
TLS
extension.
C
This
is
another
case
that
we
found
for
a
paper
in
which
two
cities
were
sent
in
the
TLS
extension
and
both
of
them
were
invalid
and
why
we
did
our
measurement
again.
In
2017,
we
found
one
five
certificates,
for
which
this
exact
case
happened,
that
because
an
invalid
Wolf's,
and
where
the
tls
extension
and
ninety
one
of
them
from
issued
by
let's
encrypt,
and
why
we
don't
exactly
know
why
this
happens.
C
We
have
a
suspicion
and
our
suspicion
is
that
back
then,
let's
encrypt
wasn't
quite
that,
while
used
as
today-
and
we
assume
that
this
is
earlier-
that
at
the
post
that
are
actually
interested
in
security
and
back
then,
let's
encrypt
did
not
automatically
submit
the
certificates
to
certificate
transparency,
those
people
who
wanted
to
tie
certificate
transparency.
So
what
you
do
is
that
you
said
it
up
yourself.
You
send
your
certificate
to
a
certificate.
C
Transparency
lock,
so
I
get
back
the
signature
and
put
that
into
you
about
server
configuration
so
that
it
sends
the
SCT
back
to
the
browser.
And
then,
after
three
months
you
have
to
change
out
your
certificate,
and
at
that
point
it's
easy
to
forget
to
update
the
configuration
of
your
web
server
and
you
send
outdated
post.
C
C
What
they
did
in
that
case
is
that
they
issued
a
certificate
for
if
age
I
know
and
for
some
reason,
something
went
wrong
during
the
issuance
process
and
they
didn't
actually
give
the
certificate
to
the
web
to
the
people,
and
then
they
issued
a
second
certificate
and
included
the
pool
for
the
first
certificate
that
they
generated
so
the
time
stamps,
or
something
like
that,
but
different
between
the
pre
certificate
and
the
final
certificate
via
redid.
This
measurement
for
our
for
the
paper
that's
going
to
be
talked
about
tomorrow,
and
this
year
found
sixteen
more
certificates.
C
Their
invalid
signatures
were
embedded
into
the
certificates
by
four
different
CAS
I.
Think
it's
kind
of
interesting
writers
happen
in
each
cases,
because
in
each
case
it
was
a
different
reason,
but
they
all
kind
of
a
similar.
So
one
of
the
CAS
was
two
years
in
error.
They
in
this
their
case.
It
was
a
inter
it
was
a
test
certificate
on
one
of
their
test
servers
and
that
they
had
set
up
and
was
happened.
C
Global
sign
had
a
few
certificates.
In
their
case,
it
was,
if
you
included
IPS
and
as
an
eye.the
ordering
between
pre
certificate
and
final
certificate
was
different
and
it
wouldn't
be
validated.
Details
had
till
as
extended
ordering
differences
between
betwee
certificate
and
Trenor
certificate
and
net
lock.
Hungarian
CA
actually
had
a
few
random
fears
being
different.
But
that
being
said
at
this
point,
there
were
basically
millions
and
millions
and
setteth
of
certificates
that
were
issued.
C
That
did
all
of
this
correctly
and
all
of
these
were
kind
of
extraordinary
cases
that
they
did
not
see
very
often.
So,
from
our
point
of
view,
the
deployment
actually
worked
very
good
and
they
were
just
a
few
handful
of
special
cases.
We
contacted
the
CAS
and
they
replaced
all
of
the
affected
certificates
so
and.
D
C
People
you
also
took
a
look
at
log
operators,
both
active
and
passive.
This
again
is
the
data
set
of
a
year
ago,
especially
both
the
active
and
the
passive
side.
Look
a
little
bit
different.
Now,
like
the
Simon
tech,
log
and
passive
traffic,
it's
I
think
it's
like
50%
and
the
Google
Docs
are
also
a
little
bit
low
and
it's
more
distributed
because
there
are
more
different
walks.
Now.
C
One
thing
that
the
AUSA
found
last
year
that
was
kind
of
interesting
was
this
kind
of
certificate
that
was
back
then
issued
to
transponders
on
amazon.com
I.
Don't
think
that
exists
anymore.
What
they
did
is
that
Simon
tech,
I
think
had
an
interesting
idea.
So
one
of
the
problems
of
certificate
transparency
in
some
people's
eyes
is
that
it
makes
the
certificate
public.
C
Transparency
required
our
message
because
home
already
enforced
certificate,
transparency
for
Simon
tech
back
then
he
also
found
another
really
interesting
thing
so,
and
this
is
one
certificate
that
being
counted
during
our
passive
measurement
on
the
right
and
but
you
can
see
it
down
here
is
when
you
pass
this
certificate
of
OpenSSL.
It
says
CTP
certificate,
ICT
and
then
it
says
a
random
string
goes
here.
So
the
first
thing
that
I
thought
when
I
add
this
is
okay.
It's
among
didn't
implement
this
in
open
SSL.
C
So
let's
look
at
the
actual
data
and
actual
data
is
all
the
extensions
I
think
how
ordered
as
mock
testing?
And
if
you
decode
that
Octus
thing
manually,
you
see
that
actually
that
the
certificate
really
contains
an
utf-8
string-
that's
just
States
states.
Random
string
goes
here
so
for
comparison.
This
is
how
it
is
supposed
to
look
like.
C
So
the
interesting
question
is
why
so
this
took
a
little
bit
of
digging
and
we
actually
never
found
out
the
entire
reason.
But
basically
the
certificate
claims
to
be
a
certificate
is
valid
for
cloud
hunt
but
net.
We
found
a
similar
ones
for
Twitter
dotnet,
twitter.com
I
think
we
found
like
three
hundred
something
for
platform
and
like
sixty
four
Twitter
and
those
were
not
valid
certificate.
So
this
certificate
was
not
actually
signed
by
Symantec.
C
It
was
just
a
exact
clone
of
a
real
certificate
that
was
issued
to
cloud
phone,
so
someone
copied
the
serial
number
issue
a
subject
and
all
the
exemptions.
Besides
the
pre
certificate,
the
certificate,
transparency,
extensions
which
they
apparently
couldn't
handle,
and
just
what
release
to
do
anything
about
and
I
assume.
C
C
There
were
a
few
misspellings
HP
KP
was
used
by
not
that
many
people
just
over
six
thousand
five,
forty
one
misconfigurations
as
CSV,
so
the
for
awake
as
psycho
suite,
which
is
automatically
deployed
when
your
software
supports
it,
was
used
by
more
than
96
and
more
than
96
percent
of
connections,
and
there
isn't
that
it
was
only
96
percent.
Is
that
IAS
doesn't
support
it?
What
didn't
back
then?
C
C
So
this
basically
supports
our
thesis
that
we
aired
in
the
paper
that,
if
you
want
to
design
a
hotel,
call
us
something
that
someone
should
actually
use
and
the
end
it's
kind
of
neat.
If
you
make
it
a
low
effort
and
if
possible
also
lowers.
But
if
you
can't
have
a
low
effort
at
least
tie
to
keep
the
risk
of
using
it
a
relatively
low.
If
you
want
it
to
see
being
deployed,
we
also
had
a
bunch
of
community
contributions
in
our
paper.
C
So
one
of
the
fun
things
that
we
did
is
as
I
mentioned
at
the
moment.
At
the
beginning,
we
had
a
shared
pipeline
between
active
scans
and
passive
scans
and
we
actually
put
the
peak
apps
online.
So
if
you're
interested
in
a
PK
of
span
of
193
million
domains,
you
can
go
to
the
UL
that
is
on
the
slide
and
download
it.
It's
a
little
bit
big.
C
We
also
published
active
scan
Lisa
as
we
publish
the
database
terms
of
certificate
transparency
that
we
use
and
we
publish
the
analysis
scripts
that
we
used
for
the
paper
and
also
the
software
that
was
used
to
do
this.
Okay
and
now
I'm,
going
to
talk
a
little
bit
about
our
follow
up
work
that
was
done
later.
So
this
is
a
new
paper
that
was
published
at
the
internet
measurement
conference
2018
so
just
a
few
days
ago,
and
that
will
be
talked
about
again
tomorrow.
I
am
actually
not
going
to
talk
very
much
about
it.
C
I'm
just
going
to
talk
about
things
that
have
a
tiny
bit
to
do
with
what
I
talked
about
already
one
of
the
fun
things
that
we
did
in
that
paper.
Is
we
created
a
honeypot
for
certificate
transparency?
What
that
means
is
we
were
interested
if
you
put
a
certificate
into
the
certificate
transparency
with
again
a
host
name
that
could
no
one
could
ever
guess.
How
long
do
you
think
it
takes
till
someone
connects
to
the
domain.
C
Another
thing
that
I
wanted
to
talk
about
a
little
bit
is
the
xes
notary.
So
one
of
the
reasons
I
have
been
doing
a
lot
of
SSL
research
over
the
last
few
years.
That,
and
one
of
the
reasons
that
this
paper
was
possible,
is
that
back
in
2011,
we
started
a
project.
We
were
interested
in
how
SSL
is
actually
being
used
on
the
Internet,
and
what
we
did
back,
then,
is
that
we
started
a
measurement
effort
with
several
universities,
mostly
in
North
America,
that
give
us
information
about
their
outgoing
SSL
session.
C
So,
basically,
all
of
these
people
are
using
a
network
monitoring
software
that
is
actually
just
changed.
Name
and
there's
now
called
seek
like.
Then
it
was
called
bro
and
we
give
them
a
little
script
that
generates
information
about
every
single
assertion,
that's
outgoing
from
the
network,
and
they
send
that
to
us
for
stored
data
evaluations
and
to
talk
a
little
bit
about
network
monitoring
soft.
If
you
have
not
heard
about
it,
Sikh
is
an
open
source
network
monitoring
software
that
basically
looks
at
network
traffic.
C
That
we
see
and
hoe
nowadays
hand
is
a
whole
bunch
of
the
different
TLS
exemptions
that
we
actually
see
being
used
in
practice.
So
back
to
the
notary.
This
has
been
running
since
the
end
of
2011
and
at
the
beginning
of
2012.
When
he
started
look
at
the
measurement
data,
he
noticed
that
there
were
some
packs
in
the
software
and
that
we
were
doing
things
wrong.
C
On
the
other
hand,
we
try
to
make
this
retire
to
respect
people's
privacy,
so
we
are
not
really
interested
where
a
specific
person
is
surfing
to
and
because
of
that,
we
don't
keep
playing
IP
addresses.
We
keep
hashes
that
assorted
that
allow
us
to
tell
them
the
same
client
is
connecting
to
the
same
server
that
so
that
we
can
see
how
effective
sessional
assumption
is,
but
we
cannot
see
when
the
same
client
connects
to
the
transfer
of
us
over
time.
C
So
this
is
a
graph
that
shows
the
amount
of
connections
that
we
get.
So
basically
we
get
a
few
million
connections
per
hour
by
our
different
sites.
At
the
moment,
we
are
at
a
little
bit
of
300
billion
total
connections
that
we
have
observed.
We
have
more
than
45
million
certificates.
Now
those
jumps
that
you
see
in
the
graph,
mostly
people
at
one
of
our
contributing
institutions
that
do
an
active
scan
of
the
Internet,
which
then
also
shows
up
in
our
data
and
also
in
the
last
few
months.
C
C
It
was
never
really
an
used
much
all
that
much
on
was
unused
for
a
short
period
of
time.
One
reason
for
that
is
that
I
think
a
lot
of
software,
especially
open
SSL
jump
from
supporting
1
0
to
supporting
everything
up
to
1
2
without
the
intermediate
step.
So
there
was
I
think
no
version
that
supported
upon
one
and
not
don't.
C
Servers
are
also
kind
of
interesting,
though,
in
our
case,
for
the
networks
that
we
are
monitoring,
their
actual
kind
of
use
for
uses
for
not
ciphers,
and
one
of
the
reasons
why
we
see
this
isn't
used
a
little
bit
is
that
they
additionally
I
used
for
the
WP
connections,
because
the
FTP
connections
are
big
data
transfers
of
scientific
data,
where
the
scientific
data
is
not
really
private.
But
you
want
to
authenticate
yourself
to
the
Eleonora.
You
are
sending
data
to
it.
C
So
you
use
authenticated
TLS
with
a
null
cipher
another
one
that
I
really
really
liked.
Is
this
one?
So
this
is
negotiated
static
as
a
versus
forward
secret
connection
types
diffie-hellman,
and
if
a
melody
fisherman
and
FMLA
he
seed
the
fireman
and
what
you
kind
of
can
see.
Is
that
there's
this
one
line
in
2013
from
which
it
seems
like
people
stopped
using
static
key
as
a
bad
match?
C
How
like,
for
example,
rc4
or
how
authenticated
encryption
is
use,
how
much
authenticated
ecolution
is
used
and
if
you
interest
it
read
the
paper
and
I
was
about
to
give
a
little
bit
of
information
about
teal,
as
once
we
use
so
I,
don't
actually
have
or
too
much
about
that.
But
you
basically
started
implemented.
Support
for
teal
as
monthly,
relatively
early
on
and
I
have
a
few
statistics
that
are
kind
of
current
on
how
it's
being
used
at
the
moment.
So
the
first
one
is
connections
where
we
basically
see
the
client
supporting
it.
C
In
this
case,
measured
by
the
client
sending
the
supported
versions.
Extension
I
have
not
actually
looked
into
the
extension
for
this
measurement.
We
have
that
data,
but
it's
a
little
bit
hard
to
access
at
the
moment
because
of
the
way
our
databases
are
organized.
But
basically,
what
you
can
see
is
that
the
moment
that
home
pushed
out
there
update
that
enable
TLS
one
free
for
everyone
which
was
in
March
I
think
is
monthly
for
everyone.
C
You
get
up
to
35
percent
of
outgoing
connections
that
we
see
that
signal
support
for
it
on
the
server
side.
Things
are
a
tiny
bit
different,
but
it
also
see
something
between
four
and
five
percent
of
connections
that
send
this
extension
on
the
server
side,
which
probably
means
that
they
negotiated
TLS
one
three
at
the
end,
okay,
and
with
that
I'm
actually
kind
of
at
the
end.
C
Meanwhile,
you
were
scanning,
and
so
in
our
case,
doing
distributed
measurements
from
several
sites,
made
the
effort
like
three
times
as
high
as
it
would
have
been
just
doing
it
from
one
side
and
did
not
really
get
us
any
more
results.
Besides
being
able
to
say
yes,
it
looks
the
same
from
every
and
with
that
I
think
I'm
open
for
questions.
E
Hey
my
name
is
Otto
Singh,
so
my
question
is:
did
you
also
have
two
questions?
Actually
one
is:
is
this
reflective
of
only
North
America
or
across
geographies?
Do
you
think
there
will
be
a
difference
and
the
second
question
is:
did
you
also
look
into
the
certificate
types
and
the
key
sizes,
whether
EC
certs
are
picking
up
and
if
RSA
is
still,
the
you
know
is
still
more
popular
than
what
are
the
key
sizes?
If
you
have
some
comparisons.
C
So
this
is
mostly
North
America
v
we
have
some
people
contributing
from
outside
North
America,
but
I
am
not
at
liberty
to
say
from
there,
because
the
size,
the
contribute
data
to
us,
want
to
stay
private,
but
nearly
all
of
our
data's
from
North
America.
So
I
cannot
say
how
if
it
would
be
significantly
different
if
you
get
it
like
in
Asia
and
to
the
certificate
sizes,
we
could
look
that
up.
I,
admittedly,
have
not
looked
in
recent
memory
like
when
I
looked
a
year
ago,
nearly
everything
was,
as
I
said,.
F
C
C
Actually,
yes,
we
have
the
problem.
Is
that
I,
don't
quite
remember
the
numbers
and
I
will
have
you
look
in
the
papers
so
from
what
I
remember
there
is
it's
kind
of
unusual
that
sides
to
both
simultaneously.
This
is
was
in
2017
and
if
they
do
it
simultaneously,
it's
typically
via
the
TLS
extension
and
via
the
certificate.
There
were
like
two
cases
in
which
OCSP
was
used
simultaneously.
If
something
is.
G
Wesford
occur,
it
is
a
fantastic
work.
You
know
this
is.
This
is
great
to
see.
My
immediate
reaction
is
okay.
Well,
how
can
we
translate
this
into?
You
know
helping
deployment
and
you've
answered
some
of
that
as
well.
Did
you
look
at
so
now?
Switching
to
the
question
side,
did
you
look
at
other
usages
of
TLS
besides
web,
you
know.
Did
you
look
for
certificates
in
other
places,.
C
So
the
answer
is
yes,
we
do
so
our
measurement,
so
basically
how
the
network
monitoring
system
works
is
that
we
attach
ourselves
a
few
ports
like
four
four
three
that
are
very
known
to
speak
to
us.
In
addition
to
that,
you
basically
have
a
regular
expression
that
we
match
to
the
beginning
of
every
connection
that
should
be
able
to
catch
or
TLS
connections
and
then
that
a
regular
expression
matches
the
beginning
of
a
connection
that
basically
tries
like.
Does
this
look
like
a
client,
hello
or
a?
C
There
was
something
else
that
you
can
send
at
the
beginning
of
a
connection
issue
really
want
to.
Then
it
just
shoves
it
to
the
TLS
analyzer
and
the
teal
as
unless
authorized,
depositing
either
says
yes,
the
CLS
of
Avery,
and
we
actually
have
written
papers
about
him.
As
on
other
parts,
there
was
one
paper
and
users
I
think
two
years
ago,
where
we
looked
at
TLS
for
communication
protocols
like
email,
XMPP
and
so
on.
Back
then
it
was
deployment
was
worse
there
and
for
HTTP.
Okay.
G
H
H
C
E
C
C
And
speaking
about
that,
I,
don't
think
that
I
forgot
they're
actually
already
looking
at
the
data
of
the
beginning,
like
until
s1
3
was
experimental,
is
kind
of
fun
because
you
have
that
supported
versions,
extension
and,
from
my
point
of
view,
it's
kind
of
interesting.
But
everyone
sticks
in
there,
because
why
there
are
the
obvious
graphed
values
like
I
support,
Hill
as
one
fleet
of
28,
or
something
like
that.
C
Google
had
their
own
values
that
they
used
I
think
they
started
with
Vaughn
II
and
they
used
it
for
stuff
that
was
kind
of
teal
as
monthly,
but
not
really
and
I
suspect
Facebook
also
had
some,
because
we
saw
a
bunch
of
them
started.
Fb
I
didn't
actually
look
if
the
collections
terminated
with
Facebook,
but
that's
always
a
good
guess.
So
you
see
interesting
things.
C
C
So
basically
web
browsers
might
refuse
to
connect
to
your
domain,
because
the
key
of
the
certificate
that
you
are
serving
doesn't
match
anymore,
and
you
don't
have
access
to
that
anymore
and
that
by
oles
us
in
theory,
you
can
set
something
like
cache
this
information
for
a
year
and
have
a
certificate
on
there
and
it
works
for
a
bit.
And
then
you
lose
the
key
and
don't
have
access
to
it
anymore
and
get
a
new
certificate
and
people
that
have
your
old
pin,
save
very
refuse
to
connect
to
your
site
until
that
years
up.
C
B
You
have
near
a
former
website
where
we
standardized
HP
KP,
and
the
thing
is
once
browsers
record
that
your
your
key
should
be
this
once
it's
different
they're
blocked
and
they're
blocked
for
months
yeah
and
there's
no
way
you
can
remedy
that's
other
than
push
not
be
to
Chrome
in
the
via
browser,
so
that
never
caught
on.
Because
of
this.
E
Yeah,
this
is
more
of
a
comment:
I
feel
spk,
p
and
CTL
the
certificate
transparency
list,
they're
sort
of
competing
programs,
so
Google
decided
to
pick
one
eventually
and
that's
why
CTL
picked
up
and
they
decided
to
decommission
as
pkp
that
says,
I
know
so.
I'm
saying
of
the
two
I
think
that
they
picked
up
CTS.
I
C
It
might
solve
what's
generally
kind
of
interesting
is
when
you
compare
passive
measurements
to
active
measurements,
because
then
you
see
a
huge
difference
because
active
measurement.
Basically,
you
see
everything
that
exists
on
the
internet
more
or
less
on
passive
measurements.
You
see
what
is
being
used,
and
one
thing
that
you
might
have
noticed
is
that
we
have
like
45
million
certificates
in
our
active
data
set,
and
our
passive
data
said
no,
but
you
might
be
aware
of.
C
When
you
start
digging
into
things,
you
find
things
that
you
find
like
one
connection
in
your
data
set
that
used
a
specific
random
type
that
you
have
never
seen
before,
but
I
think
you
get
a
little
it's
from
a
vantage
point:
we've
not
really
seen
a
big
difference,
but
if
you
compare
pest
measurements
with
active
measurements,
you
get
a
completely
different
point,
different
view
from
what
is
going
on
in
the
ecosystem.
At
the
moment,.
