►
From YouTube: IETF103-ICNRG-20181108-0900
Description
ICNRG meeting session at IETF103
2018/11/08 0900
https://datatracker.ietf.org/meeting/103/proceedings/
A
Okay
good
morning,
thanks
for
coming
to
icy
energy,
we
are
therefore
ran
by
a
woman
and
I'm
the
co-chair.
This
is
icy
energy
in
Bangkok
as
usual.
Let's
consider
the
ietf
IPR
policy,
so
just
very
briefly,
it's
quite
similar
to
the
ITF
IPI
policy.
If
you
see
anything
or
present
anything
that
is
related
to
IPR,
you
expect
it
to
let
the
group
know
in
a
short
timeframe:
yeah
we
have
a
mailing
list.
We
have
a
wiki.
A
The
wiki
is
the
place
where
we
typically
store
all
the
say,
current
meeting
information,
this
meeting,
so
we
are
super
grateful
that
we
already
have
a
note-taker
thanks
again
now.
In
truth,
we
not
sure
you
want
to
use
the
ether
pet,
but
if
you
do
there,
you
find
the
link
on
the
slides
or
on
the
ITF.
B
A
C
A
Case
this
is
followed
by
a
block
on
ICN
management
tools,
CC
an
info
and
so
compared
to
their
ping
and
traceroute.
We
have
a
brief
update
on
net
me.
Ravi
is
going
to
do
an
update
on
the
ICN
I
wrote
a
draft
and
Thomas
will
present
an
update
from
the
ICN
lope
and
work
any
need
to
fish
this
vendor
any
comments.
A
A
Those
of
you
who
haven't
been
following
every
meeting
recently
so
we
had
since
Montreal.
So
last
idea
we
had
two
interns,
one
after
the
AC
and
conference
in
Boston
in
September
and
one
just
last
Sunday
in
Bangkok.
So
I'm
not
going
to
give
you
the
total
detailed
summary
of
all
the
presentations
they
are.
So
the
everything
is
online
I'm
going
to
talk
about
in
the
next
slides
a
little
bit
about
you
know,
work
items
that
popped
up
and
so
relevant
things
that
that
happened
there.
A
Okay.
So
if
you
would
have
to
describe
what
I
see
energy
is
actually
doing
in
terms
of
technology,
so
we
thought
a
picture
like
this
could
be
helpful,
so
I
mean
I,
see.
Energy
is
a
same
IT
project
group
that
tries
to
do
continuous
work
on,
say,
ICN,
technology,
development
and
experimentation,
and
so
you
could
say
we
have
something.
You
know
like
a
core
specification,
some
things
like
C,
T
and
X
semantics
and
messages.
A
We
have.
You
know
work
that
looks
a
bit
into
getting
this
implemented
on
specific
link
layers,
for
example.
So,
like
Thomas
s,
lopen
work,
for
example,
h
ICN
could
perhaps
be
seen
in
this
category
and
then
we
have
saw
in
the
in
this
so
after
core
spec
layer.
If
you
want
a
couple
of
extensions,
so
mobility
support
things
like
let
me,
for
example,
or
other
work
outside
of
ice
energy
like
height,
we
have
work
on
named
evolutions
of
it
like
infrastructure
services.
There
are
some
proposed
extensions,
so
rice.
A
C
C
C
A
A
Which
it's
quite
possible
quick
update
on
our
work
items,
so
you
know
we
had
these
two
specifications
so
see
any
messages
and
semantics.
So
basically
they
passed
all
the
ports
here
in
the
group
and
also
in
the
ISSG
and
fathered
me.
We
are
currently
waiting
for
the
IETF
chair
to
move
this
to
the
next
level.
That
would
be
reviewing
the
ihe
and
I'm
finally
ship
this
to
the
IRC
editor,
so
we're
trying
to
progress
this.
It's
a
it's
a
bit
slow
right
now
that
progress
there.
A
D
A
So
how
you
could
describe
I
see
an
object
that
form
a
larger
file,
for
example.
So
this
draft
unfortunally
is
currently
expired.
So
we're
talking
to
the
teal
office
but
I
mean
everybody's
quite
time.
Conference
with
Chris
has
another
focus
now.
On
the
other
hand,
we
think
this
is
really
really
important,
work
and
really
useful
and
really
like
to
get
this
out
at
some
point.
So
if
anybody
you
know
wants
to,
you
know
have
a
long,
lasting
contribution
impact
on
ICN
and
is
interested
in
flicking.
A
A
Like
CTN
eggs,
for
example,
so
that
doesn't
mean
like,
for
example,
in
an
ITF
working
group
context.
This
is
the
one
solution
that
the
group
endorses.
So
what
we
are
really
doing
here
is
research
and
experimentation,
so
we
can
easily
have
thought
several
incompatible
competing
proposals
and
still
publish
each
of
those
incremental
our
sees,
for
example,
so
it
doesn't
mean
that
it's
he
connects.
Is
the
ICN
actually
specification?
It's
it's
one
and
half
the
things
that
people
brought
to
the
group.
A
A
There
were
some
comments
in
the
IR
3
review,
and
so
we
really
would
like
the
authors
to
consider
these
comments
and
come
up
with
an
update,
so
that
also
hopefully
should
happen
in
the
next
week's
we
have
the
deployment
conservation
draft.
That
is
basically
half
finished.
Last
call
here
in
the
group.
We
also
can
be
waiting
for
the
ITF
chair
to
initiate
the
review
at
the
iOS
G.
A
C
A
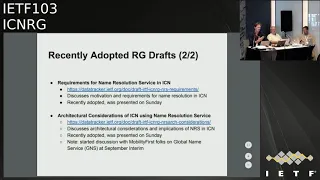
Also
adopted
the
IC,
an
application
to
to
lopen
that
works
with
what
Thomas
is
gonna
talk
about
later.
So,
let's
get
to
this
later,
we
also
adopted
two
drafts
on
home
resolution,
so
one
is
called
the
name.
Rutan's
requirements
were
frenemies
Ellucian,
there's
coming
more
the
motivation
and
requirements
it
was
once
name
and
the
other
one
is
called
architectural
Conservation's
of
ICM
using
n
is
so
bit
more
than
say,
broader
picture
and
architectural
impact
right.
Please
fill
out
the
blue
sheets,
interestingly,
at
the
last,
so
not
this
Sunday,
but
the
Boston
interim.
A
We
had
invited
people
from
obviously
first
to
give
us
a
first
say
overview
about
the
global
name
service,
GN
s
that
they
developed
in
mobility
first,
and
so
we
think
that
could
actually
be
a
fruitful
discussion.
So
there
there's
a
solid
body
of
work
in
that
in
that
project,
and
so
the
people
we
talk
to
I
actually
interested
to
to
see
how
that
could
perhaps
help
ICM
nor
at
least
have
our
discussion.
Again.
A
We
have
the
terminology
draft
so
but
I'm
kindly
updated.
This
recently
was
like
yeah
actually
updates,
mostly
we
just
discussed
in
a
little
bit.
So
Batson
is
kind
of
come
back
to
you
on
the
mailing
list
to
you
know,
ask
for
additional
comments.
We
think
it's
it's
relatively
complete
and
it
could
be
one
of
the
candidates
that
be
for
the
next
draft.
We
want
to
finish
up
here
and
publish
eventually
we
had
the
negative
lead
moment
of
IC
in
ite
and
that
works
draft,
so
there
was
also
planted
on
Sunday
and
there.
A
Is
discussing
next
steps
so
I
just
want
you
to
that
right
now
and
yeah
rather
later
is
going
to
talk
about
the
IC
and
I
go
t
draft.
So
how
I
would
he
can
leverage
ICN
features
that
me
so
the
mobility
they
could
support
was
updated.
What
happened
is
that
Cisco
declared
their
their
IP
arts
or
recently.
D
C
A
A
A
A
There
is
new
work,
so
I
mentioned
the
flow
classification
early
amped,
so
there's
an
additional
draft
on
POS,
so
that
is
petrov
currently
is
describing
how
to
basically
use
it.
This
surf
like
model,
however,
there's
a
thread
on
the
mailing
list
discussing
that
the
other
options
and
we
had
a
really
interesting
discussion
on
Sunday
and
maybe
please
check
the
the
presentation.
A
A
D
E
The
interesting
observation
here
is
that
we've
been
doing
that
for
a
couple
of
years
within
go
to
sick
with
the
system
known
as
Bluetooth
mash.
That
involves
both
the
low-power
short-range
radio
transport
technology,
including,
like
multi
hope,
network
and
the
application
layer
for
building
automation
as
well.
And
what
was
surprising
to
me
kind
of
maybe
a
year
ago,
is
that
many
concepts
that
we
developed
there,
we're
kind
of
counter
wouldn't
say
maybe
counterintuitive,
but
they
were
definitely
against
the
conventional
wisdom,
because
everybody
else
was
doing
like
a
node-based.
E
Address
routing
and
point-to-point
unicast
communication
and
we
came
with
the
concept
of
hey:
let's
use,
let's
optimize
the
network
for
massive
multicast
and
let's
use
pub/sub
paradigm,
and
then
we
realized
that
the
friends
at
IC
energy
are
like
using
the
same
concept
for
the
big
internet,
so
that
was
very
encouraging
and
and
refreshing.
So
so
that's
what
initially
brought
me
here
to
this
group
and
Bluetooth
mash
is
today
it's
not
a
an
IP
based
system,
so
we
are
moving
into
that
direction.
E
So
my
interest
here
is
as
well
to
like
figure
out
how
to
merge
the
IP
based
approach
and
whether
and
how
the
ICN
concept
should
be
brought
into
that
in
that
system.
So
did.
The
highlights
here
are
that,
from
the
practical
perspective
we
were
looking
for,
simplified
configuration
and
named
addressable
data
really
helps
there.
We
were
looking
at
scalability
and
no
points
of
failure
in
a
network,
and
we
realized
that
we
need
to
use
like
at
the
transport
level.
E
Building
like
this
one,
it's
probably
in
the
range
of
twenty
thirty
thousand
lights,
for
example-
and
it
will
like
buildings
like
this,
one
will
soon
have
equal
amount
of
sensors.
They
don't
have
there
yet,
but
but
but
definitely
like
the
trend
is
that
each
light
points
in
a
building
is
equipped
with
sensors
and
is
a
sensor
itself,
because
it
can
provide
maintenance
data
and
such
so
speaking
about
the
lighting
applications.
So
the
the
concept
here
you
are
on
the
left
side,
you
have
the
traditional
approach.
E
C
E
They
can
have
multiple
sensing
elements
in
in
a
package
and
the
blue
box
is
the
controller.
So
the
traditional
approach
has
been
that
sensors
ABC
are
reporting
some
data
and
that
data
is
collected
by
the
controller.
The
controller
runs
the
control,
algorithms
and
then
issues
control
messages
that
control
the
light
fixtures,
so
the
lights.
First
of
all,
like
the
basic
scenario,
is
occupancy.
So
you
enter
a
room,
the
lights
come
up,
you
leave
the
room
and
after
a
while,
they
go
into
didn't,
go
off
and
that's
how
everybody
has
been
doing
that
today.
E
So
the
first
observation
that
we
had
was
that
there
is
some
necessary
traffic
coming
from
the
controller
to
the
light
fixtures,
because
if
you
realize
that
the
controller
is
a
piece
of
software,
then
today
you
can
distribute
that
across
the
network.
So
you
don't
need
to
have
a
single
controller
that
controls
the
whole
thing.
E
You
can
have
a
copy
of
a
controller
embedded
into
each
each
node,
so
that
alone
saves
a
huge
amount
of
traffic
on
the
network
and
also
makes
the
network
much
more
redundant,
because
you
suddenly
have
a
completely
distributed
system
and
the
second
observation
was
how
to
easily
match
the
sources
of
information
with
the
consumers
of
information.
And,
of
course,
what
is
represented
here
by
the
hashtag
like
Twitter,
like
paradigm
of
pub/sub,
is
really
applicable
here,
because
that
really
decouples
the
controllers
or
controller
equipped
light
fixtures.
E
They
subscribe
to
given
information
like
the
lights
in
this
room
are
interested
in
occupancy
in
this
room.
So
that's
the
information
that
they
are
interested
in,
so
they
want
to
subscribe
to
that,
and-
and
if
that
the
information
is
addressable,
then
of
course
the
whole
system
is
naturally
easy
to
configure
and
the
sensors
they
publish
and
they
publish
again,
it's
really
not
important
how
many
sensors
you
have
in
the
room,
it's
important
that
they
all
contribute
to
the
whole
block
of
information
referred
to
as
occupancy
in
in
room.
E
We
are
meeting
to
write
so
meaning
to
occupancy.
Is
our
addressable
info
block
and
many
sensors
in
the
room
contribute
to
that
publish
to
that
address
technically
and
the
light
fixtures
subscribe
to
it
and,
of
course
you
can
have
more
advanced
configuration,
as
illustrated
here
so
luminaire
may
also
be
interested
in
subscribing
to
ambient.
C
E
E
In
that
case,
you
need
at
least
two
pieces
of
addressable
information.
What
one
is
the
ambient
light
level
and
the
other
is
you
can
see,
of
course,
in
my
multiple
zones,
so
that
depends
on
how
many,
how
many
light
sensing
elements
you
have.
So
you
might
have
a
zone,
that's
closer
to
the
projection
screen
and
the
sensors
that
are
further
out,
and
then
you
may
want
to
set
the
thing
that
that
close,
the
projection
screen.
It
is
dimmer
because
that
makes
the
projection
better
visible
and
also,
as
illustrated
on
the
right
side.
E
The
luminaires
themselves
can
produce
information
because
they
produce
information
about
their
status,
their
health,
their
operating
parameters
and
that's
very
important,
and
that
information
goes
to
another
address.
That
is
like
a
system
health
address
and
that
may
be
subscribed
to
by
variety
of
system
monitoring
devices
like
little
boxes
that
display
ok.
This
is
running
ok
or
the
the
network
operating
center
that
that
can
display
the
overall
health
of
the
entire
system
and
of
course,
you
can
mix
and
match.
So
it's
really
a
peer-to-peer
system.
E
You
don't
have
a
clear
distinction
between
who
really
is
a
consumer,
because
the
consumer
is
also
a
producers.
So
it's
a
it's
a
flat
peer-to-peer
architecture
that
anyone
can
contribute
the
information
and
anybody
can
can
subscribe
to
that
information-
and
what's
interesting
here,
is
that
this
decoupling,
by
addressing
the
information,
gives
us
the
opportunity
to
really
simplify
the
configuration
because,
like
yeah
I'll
get
there
I
have
one
more
slide.
One
configuration
example
that
is
also
illustrated
here
and
it's
color-coded,
so
the
luminaries
in
the
upper
row.
E
They
are
denoted
by
the
orange
antennas
and
they
subscribe
to
the
orange
light
sensor
and
once
at
the
bottom,
the
green
ones
they
subscribe
to.
The
green
light
sensor
and
in
roman
era,
has
a
occupancy
sensor
and
they
are
all
in
the
same
room.
So
you
can
imagine
that
all
the
lights,
although
all
the
occupancy
sensors
they
publish
to
the
same
address
the
orange
light
sensor,
publishers
to
Zone
one
address,
the
green
light
sensor
publishes
to
Zone
two
and
then
they
subscribe
accordingly
and
again.
E
E
There
are
today
about
close
to
100
different
qualified
products
and
they
are
interoperable
with
each
other,
so
the
installers
can
mix
and
match
sensors
and
drivers
and
and
switches
dimmers
from
different
manufacturers,
and
it
all
works
based
on
on
that
part
on
that
on
that
paradigm.
So
it
kind
of
proves
itself
because
already
there
are
case
studies
that
that
showcase
buildings
that
are
equipped
with
with
exactly
the
cities
this
system
and
the
benefits
from
the
configuration,
simplicity
and
and
reliability
are
really
huge.
E
So
it's
it's
very
from
a
maintenance
perspective,
very
very
simple:
scalability
comes
naturally
and
and
it's
even
more
natural,
taking
into
account
the
fact
that
this
is
a
wireless
network.
So
so
you
don't
have
isolated
between
parts
that
the
information
is
going.
It's
always
broadcast
media,
so
notes
are
overhearing
each
other.
So
it's
inherently
multicast
by
nature.
That's
how
radio
systems
are
built
and
and
and
by
distributing
the
controller
application
to
the
notes.
Then
we
are
like
having
the
the
amount
of
traffic
immediately
and
then,
of
course,
because
sensing
is
not
only
for
one
application.
E
Occupancy
sensor
can
contribute
to
lights.
It
can
contribute
to
Hedgehog
system.
It
can
contribute
to
space
utilization
application.
It
can
contribute
to
whoever
who-
who
knows
what
and
that's
the
beauty
of
that-
that
the
sensor
just
published
its
height,
there's
occupancy
in
the
room
or
there's
no
equipment
in
the
room
and
whoever
wants
may
subscribe
to
it
and
the
sensor
doesn't
need
to
be
reconfigured
so
that
ends
up
in
a
very
robust,
flexible
and
simple
to
configure
system,
so
that
reliability
aspect
is
also
very
important
because
we
really
have
achieved
here.
E
The
no
single
point
of
failure
setup
because
it's
hot
it's
all
distributed,
so
it
marries
the
concept
of
ICN
with
the
concept
of
distributing,
which
is
the
the
trend
that
is,
that
is
really
taking
up
today,
and
it
really
makes
sense
to
push
the
computing
to
the
very
edge.
So
each
node
has
as
its
own
controller
logic
and
it's
capable
of
subscribing
to
whatever
information
it
needs,
and
then
it
makes
its
own
decisions
and
if
it
fails,
only
one
node
fails
and
the
rest
of
the
system
keeps
operating.
E
So
it's
more
like
a
swarm
type
of
an
organism.
So
it's
a
collectively
intelligent
system
where
each
cell
is
just
a
contributor
to
the
behavior
of
the
overall
systems.
We
are
like
getting
all
the
all
the
benefits
of
that
approach.
So
that's
it
I'm
sure.
If
we
have
time
for
questions
or
not,
and
please.
F
C
E
F
E
F
E
Icn
style,
yes,
and
now
what
we
are
looking
for
is
to
how
to
bring
the
two
really
together,
because
we
find
that
architecture
very
applicable
to
the
area
that
we
are
proposing.
Bluetooth
match
for
like
smart
buildings
and
now
we're
looking
to
how
to
inject
the
ICN
through
ICN
layer
in
between
the
application
and
the
transport
network.
H
Differend
one
comment:
one
question
to
the
question:
first:
so
it:
how
do
you
think
about
how
to
design
the
namespace
for
these
things?
Because
that's
sort
of
protocol
independent,
but
how
the
how
the
names
get
assigned
and
what
semantics
get
put
onto
the
structure
of
the
names
seems
to
be
something
the
whole
everybody
could
learn
about
you're
independent
of
whether
you
know
you
choose
one
ICN
protocol
architecture
or
another
or
actually
bypass
it
directly
to
the
application
so
I'm.
Curiously,
we.
E
Also
can
provide
our
names
there's
the
addressing
space
for
the
network
is
short
that
resists
16-bit
addresses,
and
there
is
also
a
concept
for
the
of
128
bits
addresses
that
can
be
used
for
the
pub
sub
relationships
and
currently
whom
they
are
just
randomly
generated.
The
addresses
themselves,
the
long
addresses-
and
we
really
at
the
network
layer,
we
don't
have
a
name
space-
is
managed.
C
H
So,
on
the
other,
next
one
is
a
comment
and
may
have
more
to
do
with
the
actual
product
design.
Here
then,
with
the
architecture,
I
was
involved
in
the
design
of
a
system.
A
few
years
ago
that
was
deployed
at
the
MIT
Media
Lab,
which
had
this
nice
property
that
you
could
tell
the
difference
with
whether
the
bulb
was
burned
out
or
the
device
was
offline
and
there
were
sensors
on
each
of
the
the
fixtures
they
were
actually
monitoring
the
other
fixtures.
H
E
E
First,
this
product
here
in
the
lower
left
corner,
it's
a
sensor
that
you
can
buy
today,
it's
in
in
distribution
and
it's
actually
a
combined
sensor
and
fixture
controller.
So
the
output
of
that
device
is
the
light
level,
so
you
can
hook
it
directly
to
the
power
supply
of
the
light
and
it
monitors
of
it
has
an
ambient
light.
Sensing
element
has
the
occupancy
sensing
element.
It
has
temperature
sensing
element
and
yeah
it
exactly
is
capable
of
doing
so.
We
have
to.
I
You
mentioned
it's
like
twenty
thirty
thousand
bulbs
and
you
have
a
lot
of
publish
and
subscribers,
but
I
don't
see.
I
know
you
didn't
talk
about
how
these
multi
casting
routing
itself
is
managed.
It's
broadcast.
I
can
understand
broadcast
happening
in
this
single
room.
So
does
it
mean
that
you
scale
you
basically
manage
the
system
by
just
localizing
the
network,
and
this
network
doesn't
deal
with
anything
to
do
with
the
other
network
in.
E
Another
room:
yes,
so
it
supports
the
concept
of
subnets
and
subnets
very
nicely
confined
the
traffic,
because
traffic
does
not
propagate
across
subnets.
You
can
configure
a
subnet
bridges,
so
it
hops
from
one
subnet
to
another
and
the
the
flooding
is
controlled
with
TTL
and
message
caches
on
on
each
device.
So
it's
it's
confined
and
so,
for
example,
ambient
light
sensor
in
this
room.
It's
unlikely
than
somebody
in
the
other
tower
in
this
interest
in
informations,
there
may
be
a
gateway,
but
the
scaling
factor
for
gateways.
E
E
Of
times
per
second,
so
if
you
have
a
number
of
them
in
the
room,
then
then
your
air
space
feels
up
quite
quickly.
So
that's
definitely
coming
into
a
hybrid
physical
structure
that
you
have
gateways
that
offloads
to
a
faster
backbone
and
and
the
last
two
hops,
maybe
are
wireless.
So
you
only
have
routing
between
the
bridges.
J
The
way
we
need
to
address
names
in
the
communication
world
is
often
very
different
than
how
we
address
names
contextually
as
humans,
and
it's
a
really
hard
problem
and-
and
things
like
you
know,
when
we
have
50,000
lights
in
a
building
that
gets
much
harder
because
humans,
like
to
think
about
things,
have
please
turn
the
lights
off.
That
works
in
my
house.
I
can
tell
my
local
listening
device
turn
the
lights
off
and
it
does,
and
if
I
tell
my
phone
here,
turn
the
lights
off.
It
might
turn
the
lights
off
in
my
house.
J
B
E
I
think
because
now
we
are
working
on
the
design
of
this
IP
layer
because,
as
I
said,
we
have
the
networking
layer
and
the
application
layer
bound
together.
We
want
to
inject
IP
in
between,
so
the
application
like
the
lighting
control
can
run
over
IP
as
well
as
IP
can
run
on
top
of
the
mesh
under
Bluetooth.
Now,
of
course,
there's
pretty
straightforward
to
do
using
the
classic
IP
six
approach.
E
Now
what
we
are
looking
into
are:
how
do
we
take
advantage
of
the
ICN
concept
because
we
consider
it
very
relevant
and
that's
still
a
design
work,
so
we
are
kind
of
more
listening,
so
what
this
group
is
doing
and-
and
and
that's
yeah
looking
for
input
at
this
moment
when
we
are
ready
with
the
IP
design,
I,
think
that
I
will
be
able
to
share
that
with
with
the
group
and
then
maybe
collectively
we
can
come
up
with
the
unified
architecture,
because
that's
definitely
what
we
are
after.
Okay,
very.
C
C
K
What
am
I,
what
am
I
working
on
so
this
is,
you
know
a
I'm
working
on
air
quality
monitoring
in
Thailand
the
problem
of
air,
for
it
is
very
serious,
particularly
in
in
term
not
of
Thailand,
because
a
lot
of
crop
burning
and
as
you
can
see
that
the
previous
Oh
has
put
very
serious
warning
to
ask
that
three
point:
three
million
deaths
linked
to
outdoor
air
pollution,
and
you
know
the
the
reason
why
am
I
get
problem
with
my?
My
vertical
respiratory
system
is
because
of
this.
K
So
this
is
the
the
picture
of
the
northern
Thailand
during
the
breeding
season,
which
is
around
March
April.
You
can
see
that
with
the
debris
the
near
the
safety
PM
level
was
only
twenty
five,
my,
but
what
we
observe
in
Thailand
was
over
100
in
the
north,
so
it
really
serious
and
problems
mainly
caused
by
hot
spot.
K
K
So
we
propose
to
use
sensors
to
do
ground
level,
monitoring
the
PM
2.5,
which
is
the
other
thing
that
costs
your
lung
to.
You
know,
keep
creating
a
lot
of
health
problem.
So
with
this
one,
we
try
to
try
to
make
sure
that
we
can
provide
timely
warning
to
the
local
communities
that
get
affected
by
PM
2.5,
so
that
people
can
stay
indoor
not
not
going
out
today
to
to
inhale
the
PM
2.5.
K
So
in
my
mind,
I
I
was
thinking
about
in
the
end,
since
I
met
Li
Jie
in
2011,
when
she
I
listened
to
her
talk
at
a
conference
and
I
think
this
is
something
I've
been
waiting
for.
I
wanted
to
use
the
network
more
than
just
sending
information.
I
wanted
to
be
able
to
compute
and
using
the
network.
Just
like
you
know,
very
big,
distributed
computers
so
that
that
I
mean
the
idea
of
using
Indian
started
since
2011,
but
I
didn't
know
what
kind
of
application
I
can
try
this
and
the
end
on.
K
So
with
this
particular
problem,
I
found
that
it
fits
very
well
with
Indian,
because
we
are
dealing
with
a
very
remote
area.
Where,
then,
the
network
is
very
often
disconnected,
so
you
cannot
rely
on
a
centralized
system
to
do
any
data
analytic.
First,
you
know
feedback
crew
to
provide
the
feedback
to
the
community.
You
will
really
have
to
have
your
own
decent
decentralized
system,
and
you
can
you
should,
since
you
have
this
centralized
system
in
a
village,
nobody
is
willing
to
pay,
for
you
know
some
for
electricity
to
run,
centralized
system
even
innovation
himself.
K
So
if
we
can
distribute
computation
to
every
node,
then
the
Lord
is
you
know,
distributed
to
everyone
and
I.
Think
the
Indian
concept
fits
very
well
with
that.
So
another
thing
is
that
we
have
you
know
multiple
data
sources
where
each
node
produce
stream
of
readings
and
all
the
time.
So
if
we
can
leave
that
in
order
to
do
that
job,
we
can
also
always
take
the
stream
and
do
some
computation
locally.
K
K
This
is
the
PM
sensor
that
we
used
plant
plant
tower
p.m.
PMS,
seven,
zero,
zero,
three
I
think
it's
the
one
that's
commonly
used
by
the
you
know
p.m.
sensors
okay.
So
this
is
our
anode.
We
worked
with
our
colleagues
in
University
of
Saban
and
I,
think
Macau
and
met
several
others
universities.
So
this
is
our
node.
K
You
may
notice
that
we
used
hulu
neo
with
one
key,
because
we
plan
to
run
computation
in
each
node
and
we
used.
We
have
SD
card
to
store
readings,
even
when
the
network,
when
you
don't
have
the
network,
you
can
keep
the
data
and
then
upload
it.
When
you
get
connection,
our
node
has
a
Wi-Fi
connection,
but
we
are
putting
Lauro
and
on
this
node
at
the
moment
there
are
sensors
that
we
have
is
4
p.m.
1,
2.5
and
PM
10.
You
just
tell
me
when.
K
K
K
So
now
this
is
what
we
found.
You
could
predict
the
PM
2.5
quite
accurately
from
our
data,
and
we
found
that
the
burning
I'm,
sorry
p.m.
level
relates
to
the
burning
period,
relate
to
the
number
of
hotspot.
So
you
we
are
now
convinced
and
we
are
going
to
move
forward.
So
we
moved
to
step
2.
Now
that
where
I
want
to
insert
my
idea
of
in
the
end
to
system
so
and
what
we
want
to
do,
as
you
know,
as
I
said
I,
when
I
listen
to
this
yeah
I
thought.
K
Oh,
we
can
do
computation
on
the
network
so
and
then
I
found
you
are
talking
about
in
network
computation,
so
we
match
the
air
quality.
You
know
is
meaningful
for
people
in
the
affected
affected
area.
So
we
need,
you
know
to
do
computation,
even
though
the
network
get
disconnected,
and
you
can
warn
the
people
in
the
affected
area
immediately.
K
So
what
we
need
is
the
programmable
Network,
the
what
we
need.
You
know
the
kind
of
question
that
we
need
to
query.
The
network
is
something
like
to
search
for
a
possible
source
of
fire.
Ok,
so
if
you
have
this
kind
of
interest
you,
instead
of
asking
for
a
particular
stream
of
data,
you
should
be
able
to
stand
your
query
to
the
network
and
the
network
can
find
you
know
you
can
write
a
program
that
say
this
kind
of
question
can
be
handled
by
searching
for
sites
with
higher
and
higher
p.m.
K
at
that
particular
time,
and
then
you
can
find
traced
back
to
the
source
of
the
fire.
Of
course,
you
can
take,
you
know,
learn.
You
can
also
use
the
wind
direction
to
guide
your
search,
so
this
kind
of
computation
should
be
done
locally,
and
the
next
question
that
we
can
do
on
this
kind
of
network
is
that
the
each
community
affected
of
community
would
be
interested
to
know
what,
were
you
know,
the
PM
level
for
tomorrow,
the
very
near
future?
Not
you
know
weeks
ahead,
so
they
they
would
send
interest
to
find.
K
In
order
to
do
that,
that
note
has
to
do
some.
You
know
some
modeling
and
prediction,
and
in
order
to
do
that,
you
need
to
get
of
data
from
the
neighboring
nodes
and
you
have
to
get
the
reading
from
the
wind
sensor
and
then
feed
that
to
the
prediction
model,
and
then
you
can
provide
a
prediction.
So
this
is
the
kind
of
thing
we
think
that
fits
into
the
ICN
framework.
K
So
what
we
are
doing
now
is
that
that
we
continue
with
the
project
we
try
to
expand
sites.
We
are
trying
to
scale
and
put
our
nodes
in
other
countries,
because
there
are
many
colleagues
are
interested
in
using
our
node.
We
are
trying
to
expand
to
allow
Philippines,
Indonesia
and
Malaysia
as
well.
Thank
you
thank.
F
F
So,
thank
you
very
much
for
this
inspiring
talk
to
my
suite
from
happy
Hamburg.
Actually,
first
question
is
a
simple
one:
wouldn't
it
be
useful
for
you
to
have
a
small
energy
autonomous
nodes
that
use
harvesting
when
you,
of
course,
would
be
too
small
use
smaller
nodes,
then
you
use
in
the
moment
yeah.
K
F
But
the
maybe
the
more
interesting
question
do
I
get
you
right,
I
mean,
if
you
say,
you're
searching
for
the
highest
pollution
value
or
something
that
you're
actually
asking
for
a
routing
scheme
that
that
I
mean
routes
along
there's,
something
like
the
steepest
descent
or
something
like
this.
So
you
know
Maxima
and
we.
C
K
F
K
K
A
A
G
So
we
published
the
paper
with
the
name
of
the
countries
and
submitted
the
same
countries
as
an
individual
draft,
and
now
it's
revised
with
a
new
name,
which
is
a
CC
anymore,
because
the
con
tres
is
a
little
bit
too
complex
a
lo
difficult
to
understand
the
real
meaning.
So
we
change
a
name
and
now
last
month
it's
a
accepted
as
a
research,
acute
draft.
So
this
is
a
initial
version
of
CC
n
info.
As
such
good
draft.
A
G
Takes
them?
Okay,
so
what
seasoning
one
can
provide?
Actually
I
already
mentioned
and
I
already
talked
about
a
benefit
and
advantage
what
kind
of
information
or
what
kind
of
status
we
can
obtain
using
CC
any
four.
So
it's
a
really
powerful
networking
too,
and
also
precisely
because
it's
really
powerful
networking
tool.
We
need
to
have
some
function
to
enable
some
access
control,
ports,
the
cooperation
or
information
disclosure,
so
this
is
also
included
into
this
draft.
G
G
The
the
message
newly
defined
the
similar
type
values,
so
the
CCNE
for
message
itself
is
compatible
with
CC
NX,
1.0
TLB
format,
but
request
message
consists
of
a
fixed
header.
This
is
Allegra
and
message
for
mothers.
One
and
also
liquid,
spoke
TLV,
lipid,
pretty
arabic
and
named
clearly.
So
these
two
requests
bhaktir
by
report
bacterias
on
you
and
the
reprime
message,
also
consists
of
fixed
data
as
well
as
a
fixed.
The
request
block
TLB
report
rectory
named
Jared.
G
D
G
So,
okay,
so
that
this
is
not
so
meaningful
anyway.
So
initially
the
consumer
sender
initiated
request
message
and
the
liquid
message
type
is
specified
into
this
field.
Pt
request
actually,
but
now
it's
already
animation
is
already
done.
So
it's
now
it
says
reply
but
injury.
It's
a
request
and
the
intermediate
routers
insert
zero
block,
Lippo
Tobruk
inside
hop-hop-hop,
headers,
step-by-step
and
finally,
the
last
hop
lot
over
publisher
itself,
changed
message,
type
field
to
reply
and
appended
the
reply
block
and
repressive
rock
infamies.
L
M
Hear
you
can
you
hear
me
well
great
I
was
curious,
even
though
the
animation
didn't
work.
Presumably,
are
you
sending
just
a
single
interest
and
then
it
is
generating
multiple
responses,
as
it
winds
its
way
through
the
network,
or
were
you
sending
multiple,
that's
a
multiple
interests,
each
of
which
goes
somewhere
different.
So.
G
G
D
L
G
G
So,
okay,
so
the
request
and
reply
communication
is
not
really
same
of
the
ordinary
interest
and
the
data
communication.
So
the
question
are
the
the
lady
asked
me.
So
one
interest
may
initiate
multiple
reply
message.
It
happens
but
regularly
regularly
means
as
a
default
as
a
it's.
Okay,
as
a
default.
G
G
For
reprise
must
not
be
catchment
allowed
us,
because
it's
something
like
a
measurement
to
and
the
for
march
past
support
allowed
us
should
not
leave
me
the
pit
entry
created
by
city.
I
have
requests
on
the
timeout
bar
expired.
This
is
a
unique
point.
This
means
that,
even
though
you
receive
the
one
request,
if
you
request
amount
fully,
you
want
to
fully
discover
the
potential
pass
for
getting
the
some
specific
content.
Then
your
pit
entry
cannot
be
removable.
So,
of
course,
there
is
timeout
body.
G
F
F
H
Maybe
so
similar
vein,
but
maybe
a
more
positive
cast,
making
this
a
separate
message,
type
means
you
don't
necessarily
have
to
do
resource
allocation.
The
way
you
would
for
interest
data
exchanges,
which
means
the
fact
that
you're
breaking
flow
balance,
allows
us
to
rethink
how
we
do
the
resource
allocation
for
doing
these
operations.
One
thing
you
really
like
to
know
when
the
request
message
arrives:
it's
what's
the
worst
case
number
of
reply,
messages
that
might
come
back.
H
G
So
I
think
there
are
several
not
definitive
but
several
solution.
One.
The
simple
solution
is
something
like
a
later
limiting,
so
you
can
just
vary
some
apollomon
you
can
stop.
Even
though
there
is
someone
something
like
a
bogus
to
be
pry
happened,
then
the
love
digest
can
discard
everything
and
he
doesn't
need
to
reply
back
to
consumer.
H
Yeah,
the
problem:
we
should
talk
offline
about
the
problem
with
the
scheme
like
that,
because
if
you
want
to
do
that,
these
these
messages
now
have
to
be
way
lower
precedence
for
bandwidth
than
normal
interest
data
exchanges,
which
means
they
won't
work
when
you
need
them
the
best.
But
most
let's
go
talk
about
the
other.
G
Fly
again,
okay,
but
in
general
my
feeling
that
laid
control
can
help
something,
and
also
some
if
we
have
some
doubts,
something
like
a
bailout,
a
verification
mechanism
inside
this
protocol,
then
maybe
bogus
traffic
can
be
also
discarded
so
but
anyway.
So
this
is
a
very
detailed,
so
I
want
to
go
the
next
right.
So
this
is
a
really
important
discussion
point
and
one
of
the
important
open
issues,
so
maybe
I
will
back
to
that
kind
of
discussion.
C
G
Expect
that
this
kind
of
discussion
happens
here
so
I
already
mentioned
that
so
how
we
can
enabling
multiple
support
the
legally
as
a
default.
So
the
CCNA
in
for
message
exchange
is
behave
as
behave
as
something
like
ordinary
interest
and
data
communicate
data
communication,
because
CCNA
will
request
as
a
default
comprise
with
the
strategy
and
season
user.
You
use
a
could
trace
the
actual
boarding
pass.
So
usually
if
the
strategy
allows
a
single
pass,
even
though
some
router
has
a
multiple
fever
entries
toward
some
specific
content.
G
Finally,
the
the
consumer.
They
see
with
a
single
data,
because
pit
entry
was
already
removed
so
regularly.
If
we
follow
that
kind
of
regular
behavior,
then
we
don't
eliminate
some
program,
but
as
option
we
should
have
some
potential
to
capture
the
whole
potential
voiding
pass
information
or
the
potential
cashing
places.
Someone
may
want
to
retrieve
such
kind
of
information,
so
as
an
option.
We
should
have
some
capability
to
allow
that
getting
the
multiple
little
apply
toward
the
to
consumer
and
port
information.
So
this
is
also
okay,
just
keep
it
today
and
discussions.
G
So
there
are
several.
So
this
is
a
initial
button
of
such
craft
and
I
know.
There
are
several
open
issues
and
the
discussion
do
we
need
to
discuss
so,
especially
for
March
discovery,
and
this
one
is
also
a
little
bit
of
details,
so
we
can
just
skip
and
no
no
go
back,
go
back
yes
and
the
neighbor
modification.
So
actually,
as
an
academic
paper,
we
already
published
how
the
neighbor
can
verify
each
other
without
having
something
like
a
CA,
so
something
like
I,
say
central
management
system.
C
G
Is
really
useful?
We
also
have
a
plan
to
submit
as
a
different
or
another
document
internet
draft
and
we
can
discuss
more
and,
as
maybe
you
have
a
lot
of
a
discussion.
So
please
keep
in
touch
and
let's
start
the
discussion,
and
if
we
have
some
interesting,
the
comment
and
I'm
really
happy
to
hear
and
okay.
So
today
I'm
happy
to
announce
our
new
implementation.
G
G
So
there
are
several
interesting
function
that
interesting
implementation
functions
to
be
implemented,
and
it's
a
there
is
a
to
demo.
Simple
consists
of
two
main
demo
is:
definitely
this
is
affording
them
its
basic
demo
and
there's
ICS
monitor.
This
is
a
separated
daemon,
which
support
enables
the
content
store
and
since
F
initely
itself
is
the
right
weight
and
it
can
just
connect
to
CS,
monitor
D
via
UNIX,
socket
or
T,
are
TCP
socket
and
also
usually
I.
Hope.
G
The
many
researchers
or
engineer
want
to
develop
their
original
implementation,
but
they
are
usually
I,
don't
know
usually,
but
some
many
times
don't
need
to
care
the
pit
management
or
fit
management
itself.
So,
for
example,
if
we,
some
of
the
researcher
engineer,
want
to
develop
the
caching
algorithm
replacement,
algorithm
or
some
other
algorithm
or
transport
mechanism
allow
demon,
they
can
all
implement
as
a
separate
plugin
liabilities.
G
So
plugging
lava
is
just
built
in
the
sample,
780
or
CS
manager
D,
and
they
can
extended
easily
there
and
create
their
own
CCN
communication
between
blocks,
and
there
are
several
operational
tools.
Your
keys
are
also
supported
and
also,
of
course,
the
second
safe
point
is.
This
is
a
CC
and
info
already
implemented
so
next
page.
So
this
is
a
very,
very
simple
demo,
so
we
just
capture
the
screen
and
CCN
of
people.
Ccn
:
rush,
newness
science-
and
this
is
topology
consumers
here
and
published
here,
and
that
this
is
route
route
in
cash.
G
So
and
we
set
up
a
10
millisecond
delay
for
each
and
then
the
consumer
center
request
and
toward
along
the
feeb,
and
then
the
seasoning
for
request
is
alive
that
are
5,
then
out
of
5
reply
back
toward
the
consumer,
so
this
is
a
one-way
da.
He
can
see
you
can
see,
and
this
is
round-trip
time
and
there
is
a
cashier
information
here
and
this
content
is
so
the
sizes
and
cob
and
how
many
interests
he
received
and
what
kind
of
a
chunk
here
is
stored
and
the
expiration
time
and
so
on.
G
And
this
is
a
so
someone
just
want
to
trace
the
network
condition
and
he
doesn't
care,
for
example,
caching,
condition,
and
he
would
know
the
march
past
condition
instead.
So
in
that
case,
consumer
here
and
the
cache
is
there
r2
and
r4,
and
this
request
message
is
transmitted
and
toward
art
were
the
publisher.
But
actually
the
album
is
split.
G
The
request
message
and
the
once
request
message
is
sent
to
toward
r2
and
once
the
request
message
sent
twelve
feet,
maybe
or
alpha
or
some
somewhere
here
and
finally,
are
the
2
and
alpha
reply
back
to
see.
So
he
received
the
two
messages
after
he
received
two
messages.
So
why
is
from
Delta
2
and
the
other
is
route
from
route
of
all
and
each
has
a
RT
key.
G
So
this
is
a
final
site,
so
season
4
is
compatible
with
CC
and
extra
format
and
it's
a
powerful
network
to
providing
various
information,
and
it's
already
provided
in
c4
support
surface.
Of
course
it's
really
ongoing
until
there
are
maybe
lots
of
back
I
know,
but
we
have
been
working
for
to
mature
the
quality
and
we
are
really
sure
that
we
need
to
others
many
open
issues,
but
maybe
step
by
step,
and
we
revise
the
ID
and
the
comments
is
always
welcome.
Thank
you,
fantastic.
That
was.
G
Yes,
yes,
actually,
the
our
specification
already
mentioned
about
something
like
a
expanding
link,
search,
something
like
expanding
advancing
exists,
so
you'd
image
the
hop
count
and
then
the
new,
your
request
must
be
stopped
at
that
hop
count
and
or
operatory.
If
you
already
know
the
caching
information
within,
let's
say
the
NEX,
the
small
network
with
which
is,
for
example,
our
hop
count
is
3,
but
you
don't
know
that
from
3
to
pop
count,
5
for
example,
then
you
can
specify
a
boundary
between
3
and
5.
Then
you
can
search
the
three
and
five.
G
A
G
G
H
H
Hibernating
state,
but
now
that
the
the
research
group
has
gotten
interested
in
really
moving
forward
on
management,
instrumentation
tools,
we
kind
of
brought
it
back.
What
happened
this
screen?
Okay?
So
on
our
view-
and
you
toshi-san
and-
and
some
of
us
have
talked
about
this-
a
lot
is
that
there
isn't
a
one-size-fits-all
instrumentation
and
management
tool
for
things.
H
Ccn
info
is
kind
of
your
big
toolbox
that
can
do
a
whole
lot
of
things
and
get
really
rich
information
back
from
from
the
elements
and
in
a
nice
en
network,
the
ping
and
traceroute
are
much
more
like
at
least
conceptually
the
equivalent
IP
world
tools,
which
is
their
intended
to
be
extremely
lightweight
and
usable
by
end-users,
to
at
least
get
some
sense
of
how
things
are
working.
So
my
the
contention
is
where's.
The
free
button.
A
H
Is
that
we
need
some
lightweight
tools
for
troubleshooting
before
employing
more
heavyweight
heavy-duty
tools
like
CCN
info
you'll,
see
that
these
have
a
very
different
kind
of
target
and
a
very
different
kind
of
approach
to
how
they're
done
so.
The
first
of
these
is
ping,
and
you
can
think
I,
pee
style
ping
in
your
brain
is
your
mental
model
for
this?
H
What
we
want
to
be
able
to
do
with
ICN,
since
it's
a
richer
architecture
in
many
ways
than
IP
is
to
get
information
back
about
the
the
targets
of
requests
in
an
an
ICN
world.
So
the
questions
we'd
like
to
ask
with
this
is,
is
a
particular
ICN
forward
or
reachable
is
a
producer
application
reachable
and
is
a
cached
object
on
the
path
to
a
particular
can
produce
err,
reachable
and
in
the
process
of
doing
multiple
of
these
just
like
we
can
do
in
the
IP
world.
H
You
can
run
several
of
these
and
to
get
some
statistics
like
average
and
and
dispersion
on
round-trip
times.
So
one
of
the
things
we
note
here
is
that
if
you
want
to
talk
about
the
forwarder
since
we're
in
a
and
routing
by
name
environment
for
ICN,
you
need
to
give
names
to
the
things
you
want
to
route
to.
So
in
this
case
we're
not
necessarily
interested
just
in
getting
to
application
objects.
But
we
need
to
talk
about
the
forward
errs,
which
means
forwarders
need
names
now,
I
would
claim
independent
of
any
of
these
particular
tools.
H
The
other
thing
we'd
like
to
be
able
to
do-
and
this
comes
up
in
the
CCN
info
context
as
well-
is
to
be
able
to
do
our
TT
measurements
in
the
presence
of
multipath.
This
is
this
is
a
generally
difficult
problem.
Some
of
us
have
tackled
it
in
the
context
of
trying
to
do
multipath
congestion
control,
so
we
basically
adopt
the
same
since
the
same
group
of
people
who
designed
both
we
adopt
sort
of
the
same
overall
approach
to
doing
this.
H
So
we
use
a
path
ID
identifier
in
the
data
message
package
and
then
presume
that
this
path
steering
work.
That's
been
going
around
in
the
research
community
for
the
last
couple
of
years.
We
can
import
into
here
and
use
path.
Steering
to
steer
ping
messages
over
particular
paths.
The
way
you
obtain
these
path,
IDs
is,
you
can
do
path,
discovery.
H
The
actual
packet
encoding
is
an
echo
request
and
an
echo
reply.
Now.
The
interesting
thing
in
the
CCN
architecture
is
remember.
We
have
both
message
types
and
packet
types.
The
message
type
for
this
is
still
an
interest
message,
but
the
packet
type
is
echo
request,
an
echo
reply,
and
this
allows
us
to
emulate
the
actual
forwarding,
behavior
of
interests
and
data
messages.
Almost
exactly
a
couple.
H
Now,
what
we
did
with
trace
route
is
remember
in
the
IP
world,
trace
route
is
done
with
exactly
the
same
packet
type
as
ping.
It's
a
echo
Qwest
echo
reply
packet,
it's
just
the
processing
is
different.
We
follow
a
similar
architecture
here,
but
there's
some
differences,
so
we'd
like
to
know
what
the
path
of
the
forwarder
is:
what's
the
path
to
a
producer
application
and
what
are
the
pads
to
cached
objects,
so
we
want
instead
of
just
getting
reply.
Is
it
there?
H
We
want
to
look
at
what
the
paths
are
and
do
hop-by-hop
RTT
measurements
on
paths,
so
the
differences
here
from
an
encoding
standpoint
is
we
have
two
new
packet
types,
although
again
it's
an
interesting
response
and
the
core
message:
core
mechanism
is
what
came
up
just
a
few
minutes
ago
that
it's
an
expanding
ring
broadcast.
So
we
use
hop
limit
expiry
in
order
to
explore
the
the
diverging
paths,
as
would
have
been
done
with
with
IP
trace
route.
The
same
way
and
that's
it
I'm
done
comments
on
the
drafts
they've
been
adopted
by
the
RG.
H
Okay
and
now
for
something
completely
different,
so
there's
some
work,
that's
been
going
on
primarily
at
Cisco
I,
don't
work
for
Cisco
anymore.
In
case
people
haven't
noticed,
but
I
still
collaborate
with
the
team
there
on
a
number
of
things,
this
being
one
of
them,
so
since
none
of
them
can
make
it
here
today,
I've
been
sort
of
called
into
service
to
present
their
drafts.
So
this
is
not
my
work.
This
is
their
work.
H
So
what?
What
is
what
is
map
they
do
very
quickly
before
I
go
into?
The
updates
is
ICN
needs
mechanisms
to
support
producer
mobility.
Consumer
mobility
is
kind
of
naturally
built
in
to
the
CCN
and
Indian
architectures.
We
don't
need
to
talk
about
it
much
when
you
do
producer
mobility
on
a
mobile
network.
There
are
only
a
few
feasible
ways
to
do
this.
You
can
do
anchored
mobility
with
a
with
reflection
point
back
in
the
network.
H
You
can
try
to
make
your
routing
protocols
converge
so
fast
that
you
can
track
directly
via
routing
the
movement
of
a
producer
or
you
can
design
some
kind
of
custom
mechanism
and
map.
Me
is
kind
of
a
compromise
custom
mechanism.
It
assumes
that
your
routing
can
converge
reasonably
fast,
meaning
in
some
small
number
of
seconds,
so
this
creates
volatile
state
that
allows
you
to
track
producers
and
deal
with
their
mobility
during
the
time
that
the
routing
is
rican
verging.
So
this
draft
has
been
around
for
a
little
while
there
is
Cisco
IPR
on
it.
H
I
think
that's
mentioned
somewhere,
but
I'll
mention
it
right
off
on
the
top,
so
I
won't
present
the
whole
draft.
Obviously,
in
the
interest
of
time
and
people
can
read
it,
but
there
have
been
a
few
changes
since
the
last
time
we
went
through
this.
The
first
is
that
the
the
original
spec
had
sort
of
like
a
full-blown
retransmission
management
scheme,
so
it
had
its
own
kind
of
transport
protocol
properties
for
the
control
messages
that
were
going
back
and
forth
between
the
the
diversion
elements
that
did
the
the
bypass
routing.
These
have
been
simplified
considerably.
H
It
turns
out,
didn't
need
all
those
mechanisms
after
building
it
and
trying
it
out
a
bit.
Secondly,
there
was
some
assumptions
in
the
in
the
previous
version
of
the
draft.
Was
that
what
you
were
talking
to
as
an
output
face
was
simply
a
layer,
2
mobile
network
interface
to
the
to
them
to
a
mobile
network?
This
this
scheme
obviously
has
much
more
broad
applicability
to
that.
So
the
descriptions
have
been
broadened
to
deal
with
any
type
of
face,
including
tunnels
IP.
You
know
IP
tunnels,
UDP
tunnels,
any
kind
of
tunnel
so
that
that's
been
expanded.
H
Last
time
there
was
a
whether
it
was
in
Cambridge
or
previous
meeting.
We
had
a
presentation
on
the
socket
interface
that
has
been
designed
for
H,
ICN
and
potentially
other
ICN
flavors,
and
it's
now
this
scheme
is
now
implemented
for
that
that
socket
interface,
so
it
the
code
that
you
get
is
workable
with
the
with
the
socket
interface
that
that's
been
provided
by
Cisco
for
H
ICN.
So
where
we
are
here,
is
that,
despite
the
name
of
the
document,
it's
been
missin
aimed
originally
and
the
chairs
had.
H
You
know
too
busy
to
worry
about
that
too
much.
This
is
not
yet
an
RG
adopted
draft,
even
though
it's
named
as
if
it
were,
although
it's
marked
in
the
data
tracker
correctly
we'd
like
more
feedback
where
the
authors
would
like
more
feedback
from
the
from
the
IC
energy
community
find
out
whether
other
people
are
interested
in
taking
the
implementation
and
using
it
for
various
things
and
see
about
we'll
talk
more
about
adoption
of
this
and
whether
it's
a
good
idea
at
in
Prague.
Thank
you
thanks
a
lot
Dave.
A
I
So
this
draft
has
been
in
this
group
for
some
time,
so
the
basic
goal
of
this
draft
is
I
mean
it
is
a
modern
information.
In
fact,
so
the
idea
is
to
basically
present
how
ICN
it
would
be
a
good
kind
of
network
stack
for
those
to
have
to
serve
several
IOT
applications
and
so
I.
What
I'm
I
mean
since
it's
been
there.
I
So
this
is
the
primarily
the
table
of
content
of
the
draft.
I
could
spend
some
time,
so
the
basic
idea
is
to,
as
I
said,
tries
to
motivate
ICN
for
IOT
and
I
think
it
kind
of
resonates
with
the
kind
of
points
that
Simon
brought
out
saying
that
you
know
I
see
IOT
networks,
family
information
sentiment.
They
just
producing
information,
so
all
you
need
from
an
IOT
network
is
to
get
that
piece
of
information
or
if
you
can
talk
in
terms
of
a
consumer
publisher
model,
it
is
fundamentally
the
same
so
so
in
this.
I
What
we
try
to
do
is
to
primarily
in
section
3,
is
to
identify
some
of
the
general
requirements
of
from
an
IOT
perspective,
so
in
terms
of
naming
security,
privacy
and
so
and
so
forth.
Then
then
we
in
section
4.
We
basically
talk
about
how
the
current
architectures
failed
to
scale
primarily
because
I
mean
you
know.
I
Iot
is
it's
a
plethora
of
stacks
there,
and
so
primarily,
this
huge
set
of
interoperability
issues
all
the
age
issues
a
final
fundamentally
handled
later,
the
application
get
to
a
level,
and
that's
a
basic
point
that
this
section
four
brings
out
and
then
section
five
is
where
we
talk
about
how
the
different
constructs
of
ICN
can
be
used
to
meet
the
requirements
of
the
things
that
we
mentioned
in
section
3
and
the
different
design
choices
you
could
make
within
ICN
to
meet
those
requirements
so
yeah.
So
that's
about
the
the
main
meat
of
the
trap.
I
So
going
into
the
into
the
changes
that
we
did
I
mean
mostly
it
is
about.
Most
of
it
is
very
editorial.
I
mean
there
was
some
redundant
discussion
that
we
eliminated
and
some
and
we
kind
of
moved
some
of
the
discussion
into
different
to
make
it
more
relevant
where
we
felt
was.
It
was
lying
further
out
in
the
draft,
so
in
section
2
we
have
the
this.
This
section
was
kind
of
hidden
somewhere
in
section
I,
think
section
4
or
something
so
pulled
it
up,
and
so
then
we
then
we
have
the
Services
scenario.
I
So
initially
that
was
kind
of
the
section
2.
So
the
main
idea
with
services
in
are
you
again.
You
know
IOT
is
a
very
siloed
kind
of
an
area
so
at
what
we
provide,
there
is
discussions
with
on
specific
scenarios
and
then
see
how
ICN
could
help
those
specific
scenarios.
So
then
there
was
some
discussion
on
naming
where
we
had
some
discussion
on
particular.
I
This
was
the
requirements
kind
of
the
part
of
the
draft,
so
we
had
some
specific
solutions
being
discussed,
so
we
eliminated
that
contextual
communication
in
terms
of
long
term
short
term
context,
and
so
this
was
there's
some
kind
of
we
tried
to
merge
kind
of
make
the
discussion
more
kind
of
seamless
to
read,
and
then
some
renaming
of
this
section.
So
primarily
this
is
the
the
main
changes
that
we
made
to
the
trap
and
since
we
do
not
do
it
in
the
last
IETF
we
plant,
we
were
happy.
I
We
wanted
to
bring
this
back
so
that
people
can
have
again
a
good
view,
review
of
it
and
provide
as
much
feedback.
So
we
had
some
feedback
from
Thomas
on
some
references
and
we
should
I
didn
t
trade,
because
I
I
thought
we
could
get
in
more
inputs
before
coming
up
with
a
new
version.
So
so
more
comments
and
requested
for
this
thing:
Thanks
yeah.
F
F
The
last
version
of
this
document
is
basically
the
CC
annex,
stateless
compression
schemes
that
haven't
be
hadn't
been
defined
yet,
and
then
we
only
had
to
find
Indian
and
others
a
renaming.
We
then
we
use
ICN
Lok
and
as
a
name
to
make
it
more
inclusive
for
the
different
ICN
dialects
and
security
considerations
were
added.
Just
a
brief
recap.
What
is
the
objective
of
this
draft?
First
of
all,
may
I
say
in
lopen
compliance
or
had
defined
a
convergent
layer
for
low
power,
lossy
networks,
in
particular
a
two
2.15
for
adapt.
F
For
instance,
a
boolean
bit
vector
vector
can
be
reduced
to
a
bit
and
we
also
try
to
remove
a
lot
of
fields
from
the
header
wherever
possible
if
if
they
are
not
needed,
for
instance,
length
if
you
have,
if
you
are
in
a
more
or
less
confined
scheme,
then
you
can
adjust
this
to
fixed-length
and
you
don't
need
the
need
to
carry
this
also
remove
redundant
header
fields
and
there's
an
overview
of
the
to
understand.
Missed
that
point,
are
you
yeah.
F
Anyway
of
the
two
flavors
Indian
NCCN
X,
so
what
you
see?
What
does
grey
here
is
the
stuff
that
is
basically
attacked
or
or
reduced
by
by
the
stateless
compression.
What
we
do
is
we
use
the
6lowpan
dispatch
fields
which
which
are
used,
which
I
need
it
anyway,
because
we
want
to
make
the
slope
infantry
they're
compliant
and
we
encode
bits
and
that's
the
lower
line
here.
We
encode
bits
about
about
the
presence
of
compressed
fields.
F
F
The
original
encoding
had
been
longer
saiful
compression.
To
recap.
There
two
approaches:
one
is
too
similar
to
the
the
6lowpan
approach
to
put
a
context,
specific
state
like
prefixes
or
other
stuff,
in
in
common
knowledge
that
is
identified
by
the
by
context
identifier.
So
you
don't
need
to
carry
it
in
the
packets
because
it
will
be
redundantly
communicated,
for
instance,
common
prefixes,
common
suffixes
common
options,
and
the
second
approach,
which
is
that's
unique
to
add
to
an
ICN
approach,
is
to
replace
the
the
names
in
the
in
the.
F
If
you
send
an
interest,
you
send
a
name,
and
if
you
reply
to
this,
actually
the
name
is
replied
again
at
you.
You
elide
this
name
by,
or
we
like
this
name
by
generating
short-short
local
ID,
so
making
it
sort
of
a
stateful
hop
compression.
This
has
a
following
as
a
message,
much
stronger
impact
here.
F
So
if
you
look
at
the
the
example
of
the
interest,
if
you
compress
this
only
using
the
common
prefix
out
and
you're
in
the
compression
in
this
example
by
about
40
percent
in
the
data
case,
where
you
omit
the
full
name,
then
we
are
really
down
to
to
something
that
is
very
small,
which
is
important.
Just
recap.
F
This
was
more
or
less
to
give
the
the
overview
and
what
we
we
are
now
at
is
we.
We
have
a
draft
that
has
a
sort
of
shape
and
we
have.
We
want
to
stimulate
a
couple
of
discussions.
First
of
all,
the
India
and
CCN
X
faults.
So
the
question
is:
is
this?
Actually
this
were
these
other
compressions,
as
you
like?
That
is
it?
Does
it
meet
me?
F
Just
to
recap,
we
can
always
send
uncompressed
interest
in
data,
so
it
doesn't
mean
that
we
are
where
we
are
doing
onto
the
network,
but
if
we,
if
we
compress
them,
we
have
some
restrictions
and
question
is:
are
they
feasible
and
do
they
actually
match
the
common
use
cases?
Are
they
actually
that
the
useful
things
to
do
and
in
our
call
to
the
community
is
on
the
implementers?
We
are
working
on
implementing
stuff
and
we
are
originally
started
at
the
collaboration
with
the
Indian
Ooty
team
and
you
see
a
UCLA.
F
Actually,
the
Indian
Ooty
team
was
recently
formed
and
the
question
is
yeah:
are
we
ready
to
implement
this
together
and
others
to
others?
Are
they
willing
to
adopt
this
encode
I
mean
making
this
code
yeah
and
to
all,
of
course,
are
we
in
line
with
hue,
with
key
use
cases,
and
or
did
we
miss
anything
that
is
really
relevant
here?
So
please,
please,
speak
speak
up
on
this,
and
our
next
steps
will
be
continue.
Implementations
get
get
more
code,
running,
get
more
experiments,
get
more
real
experiences.
F
A
F
A
A
Yes,
okay,
yeah
sounds
very
good
thanks.
So
just
to
put
this
into
perspective-
and
this
is
a
really
interesting
piece
of
work
because
it
enables
us
to
you
know,
run
the
semantics
of
ICN
without
translation
was
in
say,
convergence
layer
that
is
specifically
adapting
to
the
needs
of
constrained
networks
and
very
elegant
way
to
basically
have
end-to-end
as
in
communication
on
the
semantic
level,
and
maybe
that's
actually
something
that
you
guys
want
to
look
on
before
you
lose
work
great
thanks.
So
thanks
a
lot,
everyone
for
you
know
being
so
good
on
the
time.
A
C
A
A
So
routing
and
congestion
control,
so
it's
not
like
there's
no
work
on
congestion
control.
There
there's
been
really
good
work.
It's
just
hasn't
been
brought
to
eyes
the
energy,
so
so
in
case
you're.
Looking
for
a
way
to
make
a
you
know
dent
in
in
ICN
a
nice
energy,
it
could
consider
either
one
of
those
topics
all
right
think
that
that
was
just
a
quick
reminder.
I
wanted
to
communicate.
A
Okay,
great.
That
brings
me
to
the
end
so
yeah
we
are
planning
the
upcoming
meetings.
So
probably
you
will
have
the
same
set
up
in
in
Prague
depends
on,
of
course,
a
bit
on
what
people
bring
to
us
and
in
previous
year,
not
this
year,
but
we
are.
We
sometimes
did
it
interim
in
January,
so
we
haven't
prepared
anything
yet,
but
if
people
want
to
do
something
host,
something
please
talk
to
us.
