►
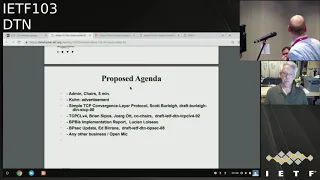
From YouTube: IETF103-DTN-20181108-0900
Description
DTN meeting session at IETF103
2018/11/08 0900
https://datatracker.ietf.org/meeting/103/proceedings/
A
A
Short
announcement
discuss
sculpt
early
TCP,
simple
to
CP
C
L,
then
before
Brian
is
not
available.
Joerg
will
will
actually
take
the
lead
on
this
presentation
and
we
have
an
implementation
report
of
VP
abyss,
which
is
great
you
seen.
Are
you
in
okay?
Thank
you
and
update.
Opp
said
any
suggest.
Some
suggestions
for
changes
or
bashing
of
the
agenda.
A
B
C
C
How
to
make
all
the
research
in
network
cooling
applied
to
satellites
systems,
so
we
have
identified
lots
of
shoes
cases,
one
of
them
being
DTN.
So
for
that
respect
we
may
have
all
the
pointers
to
network
code
again,
DTN
so,
and
the
draft
is
maybe
come
in
working
or
press
costume.
So
if
you
want
any
more
volunteers
to
review
it,
I
sent
it
to
the
list
and
make
an
announcement
here.
C
B
D
B
A
E
E
The
motivation
for
this
was
if
we,
if
we
needed
to
have
a
conversion,
Slayer
draft,
in
addition
to
the
security
and
global
Protocol
draft,
so
that
they
could
all
go
ahead
at
once.
I
thought
a
way
to
accelerate
that
might
be
to
offer
another
conversion
Slayer
draft,
which
is
what
this
is.
It
is
much
less
it's
less
capable
than
the
TCP
convergence
layer
draft
from
them
working
on
for
a
long
time.
It's
very,
very
simple:
it's
I
mean
it's
it's
seven
pages
of
specification
and
a
lot
of
that
is
boilerplate.
E
E
This
may
be
just
too
simple-minded
even
to
bother
with
it,
but
on
the
other
hand,
if
it
it
can
move
things
along
rapidly,
so
that
we
can
get
into
the
editors
queue
with
the
other
books.
I
think
that
would
be
a
good
thing.
I
will
say
that
this
very
simple
PCP
based
convergence.
There
protocol
has
implemented
for
many
years
it's
in
heavy
use
on
the
international
space
station.
Now
it
works
fine,
it's
it's
a
viable
agent
to
move
fumbles
and
with
that
I
would
stop
and
ask
if
there
any
questions.
F
F
E
G
Spencer
Dawkins
says
the
outgoing
Area
Transit
Transport
director
for
this
working
group,
so
I
think
that
telling
the
truth
is
always
appropriate.
Let
me
tell
you
what
I've
heard
so
far
that
you
want
to
put
this
out.
It
is
already
in
heavy
use
in
some
like
real
world
environments
that
are
really
inconvenient
to
repair
the
other
end
of.
G
You
know
it
doesn't
support
TLS
and
you're,
not
confused
that
this
is
somehow
okay,
except
in
these
most
restricted
and
monitored,
and
you
know
people
whose
lives
depend
on
it
at
the
other
end
environments,
so
that
you
know
there's
somebody
watching
at
all
times
at
both
ends.
I
think
if
you
say
that,
whether
it's
in
the
whether
it's
in
the
Sheppard,
write-up
or
preferably
in
the
draft
itself,
is
you
know
it's
like
here's,
the
warning
thing.
G
But
and
I
mean
maybe
even
this.
Maybe
this
is
even
a
down
roof
for
the
for
the
for
the
other
documents.
But
you
know
if
the
concern
is
that
you
you
want
to
do
this,
because
it's
in
use
today
in
environments
the
better
and
it
would
help
you
do,
testing
and
things
like
that,
while
we
well,
we
get
the
TLS
support
right
and
things
like
that.
I
think
that's
got
a
decent
shot.
G
G
Is
I
mean
that
the
other
part
of
this
that
we
haven't
mentioned
in
this
conversation,
yet
is
the
idea
you
know
how
do
you
know
that
you've
got
the
right,
convergence,
layer,
semantics
and
the
easiest
way
to
do
that
is
to
have
two
of
them.
You
know,
so
it's
like
we're
we're
testing
with
this
one.
Here
you
can
test
with
this
one.
You
could
test
with
that
one.
So
you
know
that
you're
not
looking
at
artifacts
of
what
the
only
convergence
layer
you
got.
Does
that
make
sense.
G
Yeah
I
mean
like
I,
don't
write
this
code,
but
I
mean
if
I
you
know,
if
I,
if
I'm
lying
to
you,
you
would
tell
me
because
the
truth
is
always
appropriate
in
any
direction,
but
that
that's
the
way
that's
the
way.
It
looks
to
me,
you
know
if
you
said,
would
be
cool
for
us
to
slide
one
through
without
TLS
support
and
there's
no
plan
to
do
what
with
the
LS
support
or
we
hope
nobody
notices,
okay,
the
answer
I
would
be
less
excited
about
doing
that.
B
Rick
Taylor
speaking,
not
as
a
chair,
I,
don't
and
I've
got
a
review
of
this
pending
over
science.
You
just
need
to
send
to
the
list.
I,
don't
think
it
needs
TLS,
because
the
bundles
being
shipped
have
their
own
security
profiles
that
are
applicable.
So
what
might
be
being
shipped
along
in
the
clear
is
an
opaque
blob
of
encrypted
authenticated
material
and
the
only
thing
only
extra
thing
that
could
leak
privacy,
etc,
etc.
B
Is
the
length
of
that
blob
now
we're
so
stepping
the
entire
end-to-end
authorization
do
I
do
I
know
who
I'm
talking
to
and
do
I
trust,
there's,
not
a
man
in
the
middle,
but
if
you
are
happy
with
not
having
that
level
that
guarantee
you
know,
I'm
Stephens
gonna
tell
me
I'm
completely
wrong
and
I.
Probably
am
we.
G
Could
oh,
how
convenient
that
a
former
security
area
director
should
pop
up
you
remember
being
on
the
IHG
right?
Okay!
Well,
sorry,
that
I
tried,
but
the
good
news
is
he
didn't
tackle
me
at
the
microphone
before
so
we
could
talk,
but
but
let
let
you
guys
have
that
conversation,
but
what
so?
What's
your
what
you're
saying
I
think
brick
is
a
nuance
that
needs
to
be
part
of
the
conversation
which
is
you
know
the
people
today
it's
like.
F
G
But
but
but
I
think
my
point
was
you're
talking
about
applicability
statements
where
is
this
applicable?
But
yes,
and
no
people
people
put
applicability
statements
in
their
in
their
protocol
specifications
the
standard,
the
standards
process
kind
of
assumed
they
would
be
two
different
documents
and
everybody
kind
of
freaked
out
about
what
that
actually
meant.
So
we
don't
do
it
very
often,
but
people
people
do
put
clickability
statements
in
protocol
specifications
and
I
think
that
Stephen
is
giving
you
excellent
advice,
which
is,
if
you,
if
Stephen,
doesn't.
G
Maybe
that's:
okay,
I
can't
promise
and
I
can
really
not
promise
when
I'm
not
on
the
IHG.
A
tree
large
but
I
can
I
can
tell
you.
I
can
tell
you
that
I
would
support
something
like
this.
If
you
were
telling
the
truth
about
it
and
I
would
be
able
to
explain
that
why
that
is.
That's
you
know
why.
That
is
a
good
thing
and
I
think.
Based
on
this
conversation,
I
could
start
that
convert
I
can
start
the
conversation
during
I.
See
evaluation
even
during
last
call.
Is
that
make
sense.
Yeah.
I
B
B
B
E
Convergence
there
are
tuned
to
be
provided
by
management,
and-
and
so
we
don't
and
that
that
includes
the
parameters
for
establishing
the
TLS
protection
on
connection.
So
that's
the
the
spec
doesn't
ignore
TLS
it's
outside
the
establishment
of
the
TLS
is
right.
The
rest
of
the
Southshore
know
the
connection,
including
things
like
you
know.
What's
the
IP
address
is
outside
the
scope
of
specification.
Now
we
don't
have
to
say
that
I'm
happy
to
put
in
some
language
that
says:
here's
how
you
do
the
connection,
here's,
how
you
do
TLS.
E
I
E
I
F
E
It's
currently
a
personal
draft
I'm
asking
for
working
group
adoption.
If
the
working
group
feels
that
it's
worth
taking
forward,
I
I
proposed
it
because
because
I'm
hoping
it
might
help
us,
you
know
move
forward
and,
and
if
so
then,
yes
I,
would
like
the
working
group
to
adopt
it
I'd
like
to
to
move
ahead
with
it.
If
it's,
if
it's
not
worth
pursuing,
that's
fine,
but
it's
it's
really
up
to
the
working
group.
Okay,.
B
So
so,
looking
at
the
working
group
now,
the
the
question
really
is:
if
we
were
to
adopt
simple
or
whatever
we
want
to
call
it
TCP.
Does
this
give
us
an
opportunity
to
take
the
pressure
of
TCP
CL,
which
we
have
worked
on
it
and
including
the
authors
and
the
working
group
over
the
last
number
of
years?
We
have
discovered,
you
know
there
are
lots
of
options.
There
are
lots
of
different
ways.
We
can
you
know
pipeline
and
you're.
Getting
bidirectional
and
I
won't
dig
over
all
the
all
the
work
and
churn
that's
happened.
B
D
So
it
brain
a
quick
question
when
we
were
looking,
for
example,
at
BP
sac,
and
we
were
talking
about
cipher
Suites
and
what
different
people
thought
were.
Good
cipher
suites
are
bad
cipher
suites.
This
seemed
similar
to
the
discussion
of
what
is
a
good
convergence
layer
and
what
is
a,
not
good
convergence
layer.
There
was
a
thought
that
you
could
have
interoperability,
ciphers,
which
which
would
never
be
operational,
cipher
suites,
but
they
serve
the
purpose
of
making
sure
that
you
could
have
done
a
correct
job
with
BP
sac.
Not
necessarily
the
cipher
suite
is.
D
Is
this
a
case
where
the
the
not
the
simple
but
not
to
be
named
simple
at
ECB
convergence
layer
has
a
value
because
it
will
help
from
an
interoperability.
Standpoint
show
that
BP
biz
can
run
over
something,
and
the
point
of
this
convergence
layer
is
to
show
that
BP
biz
is
correct,
as
opposed
to
trying
to
be
an
operational
convergence
layer,
and
is
that
a
useful
distinction
that
would
allow
us
to
say
here's
an
interoperability,
TCP
convergence
layer
and
later
we
will
have
an
operational
TCP
convergence
layer
in
TCP,
v4.
E
J
J
You
serve
as
white
as
the
standard
track
document
as
experimental
as
informational,
I,
I
think
one
of
the
things
that
would
help
if
this
was
published
as
informational,
for
instance,
then
all
of
the
additional
text
that
Scott
just
that
they're
talking
about
here
it
is
it's
working.
This
is
what
we
did
on
our
summer
vacation
in
one
instance
with
the
ISS
and
it's
working.
However,
you
know
in
terms
of
security,
it's
not
where
it
needs
to
be,
and
you
just
it
that
goes
back
to
what
Spencer
was
saying
as
well.
J
E
What-What-What-What
I
think
I've
heard
was
that
that
adding
adding
some
language
that
says
to
his
heart
of
here's,
how
a
TLS
is
is
invoke
when
you
run
this
thing
is
easy,
because
here
less
is
easy.
That
being
the
case,
just
can't
arrest
of
this
I'm
fine
with
that
as
well.
I,
certainly
wouldn't
insist
that
that
that
nothing
more
than
what's
in
this
document
would
go
forward.
G
Mr.
Dawkins
responsible
outgoing
area
director
again
so
don't
get
too
hung
up
on
the
status
for
the
document,
because
the
is
G
has
control
over
that
once
this
event
is
G
evaluation
anyway,
so
don't
spend
a
lot
of
time
trying
to
figure
out
what
you
wish.
It
would
be,
take
your
best
shot,
but
don't
spend
a
lot
of
time.
G
Thinking
about
it,
the
you
know,
if
the,
if
part
of
the
answer,
if
part
of
the
answer
is
that
you
could
write
something
that
says
this
is
how
to
do
TLS
and
it
and
that's
not
hard
and
a
more
complete
tcp-based
convergence
layer
is
on
its
way.
That's
also
really
interesting
conversation.
You
know,
because
I
mean
the
ones
where
you
say.
No
one
should
do
this
and
there
is
no.
There
is
no
plan
to
develop
anything
else.
The
those
are
the
ones
they're
gonna
drive
the
is
G
over
the
edge.
A
K
E
A
B
Convinced
that
sorry
Rick
at
mark
I'm
not
convinced
it's
going
to
work
at
all.
Tisa
PCL
has
its
own
effective
protocol
on
top
of
TCP
and
and
Scott's
pretty
much
says,
chef
bundle
them
all.
You
know
it's
it's
that
simple
right,
I'm
sort
of
cutting
this
conversation
here,
because
we
we've
got
the
TCP
CL
presentation
next
and
then
once
we're
both
up
to
speed
with
both
of
the
options,
we
can
probably
have
a
more
productive
discussion.
F
F
Three
I
have
been
commenting
a
lot
of
on
the
early
versions
of
TCP
CL
version
4
at
some
point,
I
got
distracted
and
stopped
paying
attention
and
lots
of
interesting
things
happened,
and
then
I
did
a
draft
review
and
found
lots
of
interesting
things
happen,
which
I
wasn't
at
all
convinced
of
the
part
which
may
have
led
I,
don't
know
how
much
of
this
has
motivated.
It's
got
to
do
a
simple
version
of
CPC
I
before
whether
he
was
just
tired
of
waiting
any
case
so
I
had
I
had
my
share
in
this
delay.
F
F
Ok,
so
there
were
a
bunch
of
obvious
of
issues
with
TCP
CL
version
3
part
of
this,
which
came
from
us
trying
to
be
backward
compatible
with
an
earlier
version
of
it
that
has
to
some
extent
Hine
dirt
flexibility
and
limited
what
we
could
design
with,
and
there
were
some
really
ugly
things
that
we
came
up
with
in
the
end,
which
have
been
fixed
in
version
4,
which
didn't
need
to
be
backward
compatible.
So
this
is
actually
very
good.
F
So
we
try
to
be
roughly
culturally
compatible
with
version
with
the
original
version.
Things
got
a
number
of
enhancements
and
there
was
lots.
There's
lots
more
explanation,
there's
now
a
bunch
of
state
diagrams
in
and
so
forth
next
slide.
But
you
probably
have
all
read
all
of
this,
so
we
had
Brian
did
in
a
round
of
edits
based
upon
some
common
issue.
Descent
on
the
list
clarified
context,
header
exchanges
extended
the
section
on
how
to
use
TLS,
which
requires
more
than
just
saying
you
only
use
TLS.
F
F
So
this
is
this
is
not
going
to
be
easy,
so
I
give
I,
give
my
personal
opinion
on
this
year,
so
the
person
TCP
convergence
layer
version,
4
draft-
has
a
bunch
of
extension
fields
and
given
that
we
are
trying
to
do
something
minimal,
that
I
felt
that
this
was
way
out
of
way
too
much.
Given
that
we
have
been
squeezing
bits
out
in
all
kinds
of
other
places,
so
I
don't
know
what
we
would
possibly
be
else.
F
Am
a
big
fan
of
protocol
designs
that
do
keep
extension
points
open
because
you
you,
you
really
screwed
when
you
when
you
lose
all
of
them,
but
maybe
we
don't
have
to
overdo
it
here
and
we
have
a
way
of
revving
the
entire
thing.
So
it's
I
I
wouldn't
consider
this
to
be
a
big
big
issue,
but
maybe
there's
a
way
we
can
have
on
each
of
these.
F
B
So
I
know
that
some
of
the
implementer,
in
fact
two
of
the
open
source
implementations,
one
from
Scott
and
one
from
I,
can't
remember
who,
but
it
from
the
hackathon
both
say:
oh
and
we
do
neighbor
discovery
and
neighbor
discoveries
undocumented
anywhere
and
I
can
see
neighbor
discovery
being
something
that
could
be
put
in
as
an
extension
into
a
CL.
So
I
think
that
might
be
a
use
case
for
an
extension.
We.
B
F
B
Say
that
that
might
off
the
top
of
my
head
be
an
example
of
an
extension,
so
I
say
that
I
think
extensions
could
exist
in
the
near
future.
The
16-bit
32-bit
field
question,
given
this
is
running
over
TCP
we're
expecting
this
on
a
ground
link
we're
not
talking
across
deep
space
or
across
complex
environments
and
wireless
networks,
and
things
like
that.
Are
we
really
do
we
really
care
about
an
extra
16
bits
in
the
link
field?
B
I
mean
I
knew
I
need
to
refer
back
to
the
draft,
but
if
you
don't
have
any
extensions,
you
don't
even
bother
writing
down
about
extensions.
Only
in
the
presence
of
an
extension
are
you
gonna
start
spending
these
16
bits
for
your
type
and
your
32
bits
for
your
extension
item
length
and
the
extra
24
bits
Oh.
Do
we
really
care
in
the.
B
F
Don't
really
think
that
you
would
really
care
if
you
can
leave
them
out
entirely
I
thought.
If
that
is,
if
there
by
default,
is
doable,
then
you
would
never
see
those
to
begin
with,
and
so
they
wouldn't
be
in
the
critical
path
and
they
wouldn't
be
showing
up
on
most
of
the
most
of
the
bundles.
So
that's
that's,
probably
just
going
to
be
fine
to
have
them.
It's
so
worthwhile
asking
the
question:
if
you
I
mean
usually
the
the
way
you
dimension
things
gives
you
an
indication
of
what
your
plans
are
right.
B
F
F
B
F
F
Originally,
we
had
a
separate
length
thing
that
was
prefixed
to
into
a
separate
discussion
or
a
separate
transmission
of
a
bundle,
because
we
couldn't
fit
this
in
otherwise
in
a
backward
compatible
fashion.
Now,
that's
that
split
into
two
pieces
was
preserved,
but
since
we
don't
have
to
be
backward
compatible
here,
it
might
be
just
simpler
to
have
this
all
in
one
thing
rather
than
having
to
individual
segments
that
follow
each
other,
because
you
need
a
more
complex
state
machine.
F
B
F
F
So
in
the
original
t,
CPC
of
version
three,
after
sending
a
session
to
her
message,
she
couldn't
send
any
more
data
so
that
this
would
actually
be
pushing
your
data
that
the
last
thing
you
would
receive
on
a
TCP
connection
would
be
the
term
which
meant
that
you
could
do
a
one-way,
closed
or
one
way
to
shut
down.
And
after
that,
if
you
may
continued
remaining
data
items
after
a
session
term
message,
I
was
wondering
why
an
implementation
would
send
a
session
term
message
before
that
and
then
making
everybody's
life
more
difficult.
F
I
would
my
take
on
this.
Was
let's
not
have
that?
Let's
keep
the
original
semantics
and
so
that
we
can
be
sure
that
when
I
receive
session
term
and
I
echo
session
term
I
have
received
all
the
data
and
I
can
I
can
close
the
connection.
That
seems
sensible,
because
then
we
don't
get
any
any
kernel
layer,
buffering
issues
or
whatever
seems
to
be
actually
a
minor
simplification,
but
I
don't,
but
but
but
I
missed
what
the
original
motivation
was.
When
this
came
up
and
so
I,
don't
I,
don't
I
don't
want
to.
B
Hey
Rick,
Taylor
again
and
I'm
looking
at
edge
because
he
was
sat
in
the
meeting
we
were
having
about
this.
This
was
a
offline
discussion.
Actually
I
seem
to
remember.
Somebody
started
down
this
line
of
thought
because
it
was
the
idea
where
you
have
a
pool
of
threads
that
are
all
streaming
bundles
simultaneously
and
one
of
the
threads
receives
an
interrupt
from
somewhere
to
say
you
all
need
to
hang
up
now.
B
B
F
D
Was
there
and
and
I
recall
when
some
of
this
was
update?
The
major
question
I
have
is
this
needs
to
be
well
explained
in
the
draft,
and
it
should
not
be
for
us
to
try
and
understand
and
reverse-engineer
the
reasoning
for
this.
If
it
is
not
there
in
the
draft
it,
it
needs
to
be.
If
the
draft
cannot
defend
this,
this
more
complex,
behavior
than
I
think
it
should
be
simplified.
F
F
Then
the
the
draft
actually
gotten
got
got,
got
a
bit
more
verbose
and
expose
was
explaining
more
terms,
not
not
all
of
some
of
these
terms,
I
think
we're
useful
for
illustrative
purposes.
I
suppose
this
is
the
second
bullet
on
that
slide
right
now,
but
they
aren't
used
later
on
so
this
this.
This
may
be
confusing
that
you
introduce
terminology,
and
then
you
don't
use
this
anymore
and.
F
Looking
at
how
people
read
specs
that
they
usually
get
more
tired
with
every
page,
usually
trying
to
save
the
page
is
worth
the
effort,
because
people
remain
more
attentive,
so
I'd
be
always
in
favor
of
having
something
shot.
But
I
don't
feel
strongly
here.
If
they're,
if
people
believe
there
is
used
and
III
don't
it
just
occurred
to
me
that
it
might
be
sometimes
more
confusing,
then
and
then
helpful,
but
I
see
the
good
intentions
that
that
are
beyond
that.
F
F
Having
listened
to
the
previous
conversation
about
these
simple
TCP
convergence
layer
and
we're
using
that
term,
now,
I'm
wondering
we
also
put
TLS
in
here
TLS
support
and
the
same
reasonings
that
we
put
forward
for
the
previous
discussion
for
not
having
TLS
would
apply
here
in
principle.
So
the
question
is:
what
got
us
actually
forced
to
add
TLS
to
this
I
think
it's
good
to
have
the
support
but
I'm
wondering
what
was
the
exact
trigger
if
everybody
anybody
remembers.
B
Rica's
chair,
if
I
remember
correctly,
it
was
the
exact
counter-argument
to
Spencer's
point,
which
was:
we've
got
running
code.
It's
kind
of
running
on.
You
know
ISS
and
a
few
within
a
few
secure
boundaries,
and
it's
good
enough
just
for
now,
and
we
want
to
write
it
up
for
TCP
CL.
This
was
seen
as
a
as
a
gold
standard,
transit
grade
convergence
layer
and
therefore
yeah.
It
must
just
have
TLS
in
there
and
there's.
No,
no
one
raised
an
issue
with
it,
but
it
was.
It
was
the
different
to.
B
B
F
So
this
this
we,
we
probably
will
do
a
version
11
at
some
point.
We
would
hope
that
we
are
going
to
get
some
feedback
from
the
group
and
to
speaking
up
to
some
of
these
things.
The
discussion
on
the
mailing
list
was
reasonably
short-lived
and
there
was
a
flurry
of
messages,
but
then
things
died
down
again.
F
It's
hard
to
second-guess
would
would
be
the
right
choice
if
you
have
your
own,
but
if
somebody
gives
me,
if
gives
us
an
engineering
direction
we
should
follow,
then
we
can
surely
work
that
out.
If
we
are
supposed
to
set
this
direction
ourselves
and
we
have
disagreement
on
what
the
direction
should
be
and
then
it's
hard
to
come
up
with
something
we
can
always
try
to
compromise
on
this
point
or
that
point,
but
it'd
be
great
to
get
feedback
before
people
perceive
that
they
need.
A
A
F
B
B
B
Okay,
so,
as
Mark
alluded
to
and
following
on
from
now,
we've
heard
about
both
Ciel's
TCP
CL
has
been
a
long
time
to
get.
To
this
point,
there's
been
a
numerous
reasons,
some
of
it
because
of
a
one
of
those
classic
moments
of.
When
you
start
looking
into
a
protocol,
you
realize
that
there's
actually
a
fair
amount
of
complexity
in
something
that
sounds
so
simple
on
paper.
B
It
may
be
that
we're
trying
to
slightly
boil
the
ocean
in
places
and
we've
been
around
this
loop
several
times,
but
we
are
where
we
are,
but
we
need
to
get
it
finished.
So
the
policy
has
been
that
the
the
triumvirate
of
BP
Biss
BP
SEC
and
at
least
one
convergence
layer
must
be
ready
to
go
forward
together
to
the
iesg
s
so
that
we
can
not
only
define
how
a
bundle
is
defined.
We
can
secure
a
bundle
and
we
can
move
a
bundle
and
therefore
we
have
a
basic
ATM
protocol
stack.
B
Currently,
we
have
two
out
of
three,
so
the
there
is
some
urgency
to
have
a
convergence
layer
so
that
we
can
demonstrate
interoperability
and
everyone
could
go
and
test
that
their
lab
implementations
are
suitable
for
taking
on
to
the
next
step
or
or
running
it
live
as
they
see
fit.
So,
with
the
arrival
of
Scots
simplified
TCP
document,
does
that
buy
some
time
to
get
TC
PCL
really
good?
Is
it
and
I'm
not
waiting
any
of
these
statements?
Is
it
a
replacement
for
TC
PCL?
Is
it
interesting,
but
we've
got
TC
PCL?
B
F
One
guy
was
famous
for
quoting
saying
that
hard
plus
easy
is
harder
than
hard,
and
because
you
have
to
figure
out
how
to
do
optional
things
and
implementation,
you
need
to
figure
out
okay,
in
some
cases,
both
ways
you
need
to
have
fallback
ways,
and
so
so
this
gets
me
to
one
PI,
especially
this
fallback
part
gets
made.
One
thing
we
need
to
differentiate
between
the
two.
F
We
can,
of
course,
pick
different
port
numbers
and
say
we
are
going
to
have
one
port
number
for
this
version
and
one
port
number
for
that
version,
or
we
are
going
to
use
the
same
port,
but
then
we'll
need
to
have
a
magic
cookie
in
the
beginning.
That
allows
you
to
figure
out
which,
which
version
you
are
running.
F
If
but,
but
if
there
would
be
a
coexistence,
you
would
need
to
figure
out
how
that's
supposed
to
work.
We
would
just
need
to
have
a
way
of
differentiating
and
and
allowing
either
upgrading
or
whatever
and
and
understand
what
are
the
respective
spaces
that
these
respective
implementations
cover
and
then
go
back
to
the
question.
What
are
we
actually
needing
at
some
point
whenever
a
working
group
engineers,
something
we
sometimes
lose
sight
of,
what
our
requirements
are
and
maybe
double
check,
whether
the
space
covered
by
one
of
the
two
implementations
is
actually
off?
F
All
that
bears
the
risk
that
we
might
delay
both
in
the
end,
so
it
may
be
worthwhile
getting
I,
don't
think
tcp
ser
version
4.
Doesn't
it
doesn't
need
much
breathing
space
because
most
of
the
stuff
is
done.
There's
some
simplifications
where
there
were
some
fixes
now
put
into
the
latest
version,
so
one
can
probably
ship
this
at
some.
It's
a
lot,
not
true
distant
point
in
the
future
and
I'd
be
but
I
don't
mind
having
a
simpler
version
either.
G
G
So,
thank
you.
If
you're
talking
about
you
know
if
you're
talking
about
Rio,
we
pour
you
reusing
the
same
port
for
both
versions.
This
that
actually
turns
out
to
be
a
big
deal
to
the
people
who
do
port
reviews
in
Diana,
so
that
it
really
that's
not
the
only
possible
answer,
but
that
is
a
that
is
definitely
the
right
answer.
So
thinking
about
that
number
one
number
two-
and
this
is
I-
think
related
to
that
one
of
where
we
are
with
where
we
are
in
quick,
where
we
say
we
want
to
have
versioning.
G
But
that
means
you
have
to
have
two
versions
in
order
to
test
that.
Okay.
So
if
you
know
so,
if
the
answer
is
that
this
is
going
to
run
on
one
don't
want
protocol,
then
you're
going
to
be
do
as
part
of
your
as
part
of
your
support
for
two
testing.
Now
you'll
start
that,
but
you've
also
got
two
convergence
layers
fairly
quickly
that
you
can
test
both.
You
know
that
you
could
test
both
up
and
you
could
demonstrate
that
this
is
the
behavior
you're
looking
for
is
not
tied
to
one
particular
convergence
layer.
G
That
would
be.
That
would
be
helpful.
Also
so
I
think
there's
a
I
only
had
one
reason
to
say:
well,
I
was
gonna
say
that
I
think
you
just
gave
me
two
reasons.
Just
say
that
simple,
you
know
or
think
I'm
you
seeing
around
using
around
here
or
frequently
than
simple
these
days
is
probably
minimal.
If
that
helps
that
that
that
way
and
everybody
in
the
room
won't
twitchy
uncontrollably,
when
you
say
it,
every
time
like
we
all
are
now.
B
So
Rick
individual
I
wasn't
proposing
that
minimal,
TCP
and
TCP
CL
should
try
and
run
on
the
same
port
and
multiplex
I
mean.
Obviously
one
can
do
that
by
putting
a
cookie
on
the
front.
I
believe
TCP
CL
already
has
a
an
equivalent
cookie
at
the
part
of
the
session.
Initialization
there's
a
unique
identifier:
you
can
you
can
spot
that
you're
there,
so
it
could
be
doable.
But
again
it
adds
complexity
to
simple
so
there's,
but
it
makes
getting
ports
easier.
B
So
those
there's
a
compromise
and
there's
something
for
the
group
and
it's
almost
admin
trivia,
but
it
is
relevant.
I
suppose,
following
on
point,
your
grade
raised
a
good
point
about
use
cases
that,
if
we're
going
to
have
to
CLS
that
look
actually
as
though
they
live
in
the
same
domain
loosely
there
needs
to
be
some
use
case
guidance
because
otherwise
say
I'm,
brand-new
academic
organization
or
company
who
goes
oh
I
need
a
CL
for
my
bundle.
B
G
G
And
Stephen
was
right
about
people
twitching
uncontrollably
when
you
say
I
application
applicability
statement.
If
you
want
to
see
people
twist,
Twitter
control
will
be
really
hard
say,
use
cases.
Don't
do
that
so
saying
it?
Where
is
this
applicable?
You
know
just
friendly
guidance
from
a
friend,
but.
A
Yeah,
when
we,
if
well,
we
need
to
know
one
TCP
layer
to
both,
which
one
one
point
might
be,
that
the
Spencer
was
saying
about.
Don't
don't
take
too
much
time
on
the
status
of
the
document,
but
it
might
be
a
case
where
simple
is
actually
experimental.
Therefore
you
know
you
know
right.
So
that
tells
you
know
this
is,
you
know,
doesn't
have
the
same
talking
spending
three
years
on
TCP
Co.
This
is
the
standard
track.
One
and
experimental
is
there.
You
can
use
it
and
then
I
think
we
send
the
right
message
so.
I
A
A
I
I
Secondly,
I
think
there
is
a
functional
difference
between
these
of
them.
If
I'm,
remembering
correctly
in
that,
even
though
reactive
fragmentation
is
not
a
thing
that
that's
in
the
current
ppthis,
if
I
remember
rightly,
it
still
is
a
thing,
and
you
could
only
do
that
with
the
TCP
CL
one.
You
couldn't
really
do
it
with
this.
The
new,
simpler
iteration,
because
you
don't
know
how
far
you've
got
yet
so
so
I
mean
there
is
a
functional
difference
between
them.
Yes,
TCP.
B
I
B
The
the
controi
Rick
Taylor
again
personally,
the
counter-argument
to
that
is
TCP
CL,
has
proven
to
be
more
complicated
to
get
finished
than
we
expected
and
we
might
be
falling
into
the
trap
of
oh.
It
looks
like
it
should
just
be
a
couple
of
weeks.
It's
just
a
few
few
hundred
words
change
and
we're
fine
yeah,
November
22nd
is
being
quoted,
but
I
mean
the
presence
of
minimal
TCP,
simple
TCP
by
TC
PCL
sometime
within
the
working
group,
to
really
get
right
and
iron
out
these
problems.
I
Point
I
was
the
only
one
makers
at
back
when
we
were
using
DT
and,
and
there
was
a
TCP
CL.
It
was
like
this.
It
was
very
hairy
and
crappy,
and
but
it
worked
and
nobody
cared
cuz
you're
generally
using
it.
Where,
once
you
had
a
contact,
keep
any
bandwidth
see
it.
So
as
long
as
it
works,
it
was
able
to
get
used
and.
B
I
So
my
point
was
that
if
there's,
if
somebody
has
shown
that
you
can
implement
and
use
the
TCP
CL
version,
4,
then
that'll
be
fine
in
almost
all
cases
and
so
I
don't
think
you
would
see
a
simpler
one
displacing
an
existing
implementation
if
the
implication
exists.
If
there
was
no
such
implementation,
then
maybe,
but
if
there
is,
then
you
just
configure
TCP
and
off
you
go.
A
A
F
As
this
one
is
awake
that
let
me
make
one
your
core,
let
me
make
one
quick
comment:
if
I'm
like
Scott,
simple
thing,
but
if
it
is
really
only
unidirectional
and
the
one
who
connects
sends,
then
then
this
isn't
applicable
to
the
terrestrial
version
of
DTN
at
all,
because
we
have
many
nuts
and
firewalls
who
won't
allow.
So
the
simple
version
is
not
an
option.
Okay,.
B
B
I
Stephen,
probably
just
this
may
have
been
what
you
said
right,
because
there
are
scenarios
where
what
you
exactly.
What
you
want
is
to
establish
an
outbound
TCP
session,
send
some
packets
and
then
put
her
off
like
lots
of
sensor
kind
of,
whereas
you,
if
you
want
an
actuator
or
if
you're,
then
you
need
to
more
complicated.
So.
B
This
is
this
again
is
the
applicability
statements
of
both
protocols.
One
is
yeah,
you
know
TC
BCL.
Before
has
all
those
properties
you
might
want
to
use
for
a
transit
network
where
you've
got
bi-directional
order.
I
get
the
transit
meant,
maybe
the
loosest
term,
but
sort
of
backbone,
ease
style.
Let's
shovel
packets,
on
big,
fast
pipes
and
simple
tcp
has
the
sensor
network
dial
up
occasionally
shovel
your
data
off.
Hang
up
the
you
know
it's
they
both
well.
E
One
other
thought
on
the
existence
of
the
code
is
that
we
do
end
up
I
think
with
certainly
with
bung
protocol.
We
ended
up
with
like
lots
of
different
implementations,
just
because
part
of
because
people
wanted
a
lots
of
different
implementations
for
various
reasons,
partly
because
we
really
use
different
languages
and
I
think
that
that
might
be
an
advantage
of
having
as
an
option
a
minimal
TCP
convergence
layer
that
anybody
who
wants
to
can
you
know
hack
together
in
an
afternoon
and
and
and
start
working
with
it,
and
and
they
can
do
it
in
Python.
E
A
B
I
B
Putting
T
Ric
here,
sorry
quickly
and
I,
know
Fred
is
in
the
queue
and
the
putting
TLS
Ian
is
actually
having
done
it
recently
to
a
TCP
protocol
is
actually
quite
simple.
It's
call
out
the
B
sip
and
there's
some
pretty
much
some
boilerplate
code
and
and
the
the
security
groups
will
hold
your
hand.
It's
not
hard
and
Fred
go
ahead.
I
just.
M
B
Rick
Taylor
answering
with
a
chair
hat
on
I,
think
the
presence
of
a
convergence
layer
really
helps.
We
don't
immediately
have
the
answer
of
whether
having
standards
track
documents
relying
on
having
a
canonical
reference
to
an
experimental
document,
I'm,
not
quite
sure,
that's
a
discussion
with
the
iesg
in
the
80s,
but
it
can
only
help.
D
Sorry,
a
brain-
and
this
is
similar
to
Fred's
question,
which
was
what
we
just
hummed
one-
was
working
group
adoption
of
those
documents,
but
the
question
behind
that
is
both
don't
need
to
be
finished,
to
put
BP
bills
forward.
You
know
and
and
in
fact
we
would
be
comfortable
with
either
of
them
and
whichever
one
could
be
done.
First,
I'm.
B
Rick
as
chair
I,
don't
a
first
office
mark
has
pushed
York
quite
hard
on
this.
We
may
well
get
TC
PCL
done
pretty
quickly.
I
think
we
could
get
minimal,
simple
tcp
CL
done
pretty
quickly
as
well
put
TLS
on
the
front
of
it.
We
could
probably
go
standards
track
or
whatever
the
is
G
teams
is
the
right
tag,
as
Spencer
pointed
out,
they
can
changed
it
change
it.
Oh,
we
might
be
able
to
get
both
done
quickly,
but
this
means
everyone
in
the
room
and
dialed
in
and
on.
B
The
mailing
list
needs
to
actually
help.
We
can't
just
sit
back
and
wait
for
the
wafer,
scott
yoak
and
brian
to
finish
this
and
demand
they
finished
it,
and
that
applies
to
me
as
well
as
to
you.
We
we've
got
help
with
this,
because
I
know
we're
all
keen
to
get
this
stuff
finished.
So,
let's
help
okay.
B
K
Hello,
my
name
is
wisdom.
I
work
for
a
company
called
red
mesh
on
the
we
are
doing.
There
is
really
TN.
Our
goal
is
mostly
to
connect
on
try
to
provide
service
to
underserved
communities
on.
We
are
doing
that
primarily
through
mesh
networks.
On
recently,
we
got
interested
into
the
DTN
because
of
the
ability
to
move
data
on
of
remote
outpost
stammering,
so
we
are
targeting
consumer
devices,
so
we
made
an
implementation
of
the
chain
on
Java.
K
K
It's
about
40
49
of
code,
three
megabytes
packaged
on
it
implements
as
of
November
2018
draft
IETF
VPN
is
11,
simple
TCP
that
Scot
center
a
few
month
ago
and
in
during
the
Academy
was
implemented
IPSec
with
a
minimum
in
Europe
like
Iran's,
and
the
draft
with
only
to
cipher
and
follow
encryption
on
one
for
the
integrity
which
are
part
of
the
implementation.
Now
the
code
is
public
and
available
on
the
following
address.
K
K
Overall,
it's
the
draft
is
pretty
clean.
It
was
very
easy
to
implement.
There
is
a
few
areas
which
made
the
implementation
slightly
difficult,
mostly
it's
not
for
what
the
draft
was
saying,
but
for
what
it
was
not
saying.
So
that's
mostly
the
storage
on
the
under
routing,
because
I
mean
I
had
to
travel
to
wrap
my
head
around
the
endpoint
ID.
What
exactly
does
that
covers?
Is
it
an
identifier?
Is
it
a
resource
location?
K
Is
it
a
root
on
I
understand
that
the
draft
makes
the
interpretation
of
the
EAD
fairly
flexible
for
the
use
cases
on
it's
both
an
endpoint
for
the
bundle,
but
it's
also
the
inductive
fire
of
the
note
that
hosts
the
service
so
so
yeah
we've
I
mean
we.
We
made
some
implementation
decision
which
are
present
on
the
you
have
any
question
or
critics
open
for
the
discussion
minor
problem
on
actual
design
of
the
draft.
There
is
not
really
a
problem,
but
comments
really
when
it
comes
to
parsing.
K
K
So
strings
should
probably
be
covering
everything
without
having
to
do
those
distinctions
and
I'm,
not
sure
the
value
of
having
integer
in
just
one
bytes,
as
opposed
to
a
string
which
takes
a
few
bytes
Maurice,
is
really
useful.
The
other
thing
was
the
notion
of
the
retention
constraints
since
the
since
the
RFC
doesn't
cover
anything
to
do
with
storage.
I
think
the
world
doesn't
even
mention
once
the
the
retention
constraints
is
mostly
informational,
so
there
is
no,
if
statement
in
a
draft
that
says,
if
retention
is
that
on
that,
then
we
do
something
differently.
K
K
So,
as
I
said,
an
eID
is
mostly
an
URI,
so
it
should
be
anything,
however,
for
when
it
comes
to
the
application
agent
registration,
we
decided
that,
since
the
service
is
osted
on
an
actual
host,
a
bundle
node,
we
would
just
happen.
The
whatever
is
the
strange
that
the
application
general
registers
to
to
the
to
the
DTN
idea
of
the
depend
or
not.
K
The
reason
is
because
if
we
were
to
allow
any
application
to
reduce
us
to
any
en
first
of
all,
we
would
be
some
problem
with
impersonation,
but
even
without
that,
that
means
it
wouldn't
work
until
we
develop
a
DTN
resolver
system
like
this
akin
to
a
DNS
root.
A
root
locator
on
having
having
the
service
binded
to
the
host
means
we
just
have
to
care
about
the
routine
on,
doesn't
have
to
care
about
resolving,
on
top
of
the
routine,
to
resolve
an
and
an
eID
to
an
actual
noted,
not
vocation.
K
Similarly,
since
each
uri
has
its
own
skin
on
skin
specific
part,
I
would
ring
how
exactly
are
we
supposed
to
process
a
new
array
which
we
don't
know
the
skin?
Let's
say
it's
got
a
specific
scheme.
Don't
want
to
come
on
like
what
do
we
do
with
that?
Should
we
try
to
match
it
to
the
longest
prefix
that
we
have
in
the
new
routing
table
that
we
have?
Should
we
delayed
it?
K
Should
we
stir
it
until
someone
talk
to
us
again,
I
believe
that's
out
of
scope
of
the
draft,
but
having
an
informational
draft
about
the
best
practice
would
be
interesting
because
when
it
comes
to
interweb
interoperability,
if
I
can't
expect
a
certain
behavior
when
I
send
a
bundle,
it
makes
that
behavior
unpredictable
next,
please.
So,
in
order
to
address
those
issues,
we
introduce
something.
We
call
this
convergence
layer,
adapter
specific
endpoint
ID,
which
is
a
way
to.
K
Meets
in
only
one
address
both
another
90
fire
on
route
location,
meaning
basically
an
interface
energy
fire.
So,
for
instance,
for
the
simple
TCP
that
we
implemented,
every
simple
TCP
channel
is
binded
to
a
unique
singleton,
a
ID.
So,
for
instance,
it
would
be
clas
DCP,
followed
by
the
IP
on
the
port's
it
chooses
for
the
communication
and
I
think
having
this
model
could
be
interesting
to
edit
as
a
draft
or
maybe
in
DPP's,
because
then
it
allows.
K
How
can
I
put
it
like,
for
instance,
we
just
use
about
stcp
vs.
DC
PCL
on
TLS
I
feel
that,
right
now,
a
CCP
is
pretty
good,
because
whether
we
are
running
sdcp,
oversecured
channel
with
TLS
or
whether
we
in
the
plane,
the
sdcp,
would
not
change.
It
would
be
the
same
way
to
move
bundle
from
one
point
to
another.
However,
where
this
decision
is
taken
to
open
a
TLS
circuit
or
a
TCP,
socket
I
think
it's
out
of
scope
of
the
protocol.
K
It's
something
that
that
should
be
done
within
like
the
peer
discovery
or
the
neighbor
discovery
on
linker
management,
but
it's
another
module
which
is
not
part
of
the
protocol
itself,
which
is
really
just
a
link.
Every
convergence
layer,
just
one
hop
link
on
the
security,
should
not
be
one
who
should
be
end-to-end
or
if
the
link
moves
over
the
Internet,
then
we
can
open
it
till
a
circuit,
but
that
doesn't
have
to
be
a
feature
of
the
actual
protocol
that
sends
the
vendor
on
right.
K
Now,
the
on
the
draft,
the
services
at
each
convergence
layer
should
offer
is
only
to
ascend
on
receive
bundles.
It
doesn't
say
anything
about.
If
the
application
agent
reduces
security,
then
every
link
on
the
way
should
be
secured,
or
so
until
until
the
services
of
the
channel
are
just
sending
on
receiving
vendor
I.
Don't
really
understand
in
the
need
to
add
a
neighbor
discovery,
wave
contact
either
serious
negotiation
with
some
negotiation.
So
that's
what
was
original
behind
the
implementation
of
TCP.
K
So
the
next
thing,
also
with
a
CLA
IDs,
is
that,
because
it's
an
ambiguous
on
binded
to
every
channel
uniquely,
it
can
also
be
used
to
proactively
open
the
channel.
So
when
I
receive
a
bender,
for
instance
in
in
Tara,
so
it's
a
name
of
the
implementation
if
I
receive
a
bundle
with
a
CLIA
IDs
or
any
edits
for
that
matter.
If
we
can
resolve
it
on
at
the
end,
we
end
with
a
CLIA
ID.
We
can.
We
can
proactively
open
sub
channel
using
the
basically
also
act
as
a
negotiation.
K
B
Sorry,
brick
personally
I'm
waiting
for
Scott
to
jump
in
on
this
I
think
Scott's
original
vision
and
it
may
not
have
been
Scott's
but
as
I
understood
it
when
I
first
started
getting
involved
with
DT
and
was
did
the
endpoint
identified
would
be
late
bound,
and
this
was
seen
as
a
very
positive
aspect.
So
I'm
wondering
and
I
like
where
you're
going
with
the
CLA
PID
but
I
think
it
adds
early
binding.
F
K
K
K
It
would
be
much
better
if
I
could,
just
in
the
in
the
Eid
select
IP
port
on
and
then
that
would
find
that
its
way
itself
next
slides
will
be
more
informational
because
yeah
next
one,
but
for
this
one
the
idea
was
just
maybe
we
could
just
add
a
new
service
to
a
convergence
layer,
whether
they're
just
sending
on
receiving
bandar.
Maybe
a
convergence
layer
should
should
also
state
what
is
the
CLA
idea
of
the
current
channel.
K
So
every
time
it
generally
is
opened
by
recommenders
layer,
it
should
provide
as
an
api,
the
IDS
of
the
room
you
appear
on.
If
the
channel
is
symmetrical,
it
should
also
provide
the
idea
of
the
local
peer
that
the
peers
can
use.
So
when
we
will
be
on
the
vendor.
Forwarding
algorithm
on
there
is
the
line
that
says
is
the
is
the
ID
local
so
having
this
ID
coming
from
the
Sierra
with
allows
for
feeling
I
mean
the
local
ID
stable
on
the
yeah.
K
I
K
B
Coding,
yes,
HTTP,
ipv6,
URL,
encoding
thing,
it's
just
call
out,
but
sorry
Rick,
jumping
in
the
queue
here,
I'm
totally
agreeing
with
you
here
Lucy.
If
it's
a
convert
this
slide
to,
if
it's
a
convergence
layer
service,
then
the
convergence
layer
can
hand
out
names
that
it
knows
how
to
parse.
So
you
know,
I
can
I
can
set
your
any
old,
random
blob
and
say
if
you
give
that
back
to
me,
I
know
what
that
means
and
you
don't
need
to
care.
But
it's
an
identifier
can.
K
You
move
up
just
a
second,
so
the
way
it
works
is
that
it's
very
it's
a
little
constraint,
but
if
it
starts
with
CLA,
then
you
have
pretty
much
like
a
normal
AG.
A
seal.
A
scheme
followed
by
a
specific
part
on
that
parser
or
cellular,
is
provided
also
at
the
service
of
the
convergence
layer.
So,
for
instance,
when
I
receive
a
bundle
with
a
CLIA
ID
I
will
try
to
find
a
congratulate
that
will
accept
this
ID
on.
If
it
does,
then
I
can
provide
basic
I
have
a
service.
K
Can
you
try
to
create
an
opportunity
with
that
ID
that
right
now
is
not
in
my
link
local
table
on
every
convergence
layer
that
receive
it.
If
it
recognizes
the
scheme,
then
it
tries
to
parse
the
simple
specific
part,
and
then
it
tries
to
to
create
the
connection
of
stcp
if
it
says
disappear,
disappear
disappear
on
that
is
configurable.
So
if
you
don't
want
people
to
abuse
this,
but
you
can
yeah,
let's
go.
E
E
There's
something
in
ion
now
called
a
convergence
layer
manager
that
read
stuff
out
of
the
queue
that
is
destined
for
node,
X
and
figures
out,
which
of
the
possible
multiple
convergence
layer
paths,
no
excuse
for
that
bundle
and
I
think
that's
ultimately,
a
useful
capability
and
and
and
I
think,
quite
desirably.
It
is
completely
buried.
Underneath
bundle.
Protocol
on
the
protocol
doesn't
see
or
know
or
care
anything
about
this.
It
is
the
convergence
layer,
the
sitting.
K
E
K
K
So
right
now,
the
forward
in
the
draft
I
mean
VP
VP
B's
draft.
There
is
only
one
rule
see
if
it's
local
deliver
locally,
if
it's
not
local,
select,
select
the
set
on
track
to
forward
otherwise
try
to
forward
later
when
the
opportunity
makes
it
happen,
so
I
would
be
in
favor
of
adding
two
new
rules.
That
would
be
look
if
it's
not
local.
Look
at
the
link.
Local
table
for
one
hop
direct
forwarding
if
the
Eid
is
a
link
is
a
CLA
ID.
Then
we
can
just
directly
direct
that
bundle
to
the
interface.
K
So
the
bundle
could
carry
its
own
forwarding
strategy,
for
instance,
if
it
wants
to
be
routed
using
the
GPS
of
the
phone.
So
we
are
using
phones
to
be
that's
the
goal.
We
want
phones
to
be
bundle
nodes,
so
there
is
a
lot
of
things
that
we
can,
how
it's
good
one.
So
if
we
have
a
path
which
is
made
of
predictable
nodes
like
a
purse,
freight
trains
buses
that
can,
that
is
like
the
satellites
kind
of
use
case.
It's
mostly
delay
that
you
are
dealing
with.
K
But
if
you
are
in
a
network
made
of
randomly
moving
nodes,
then
it
becomes
an
opportunistic
network
on
the
routing
strategy
is
very
application
dependent.
So
it
would
make
sense
that
each
bundle
could
carry
element
of
its
own
routing
strategy.
It
could
be
its
own
routing
table
if
it
only
wants
to
be
forwarded
through
trusted
nodes,
it
could
be
like
it
could
be
anything
a
geographical
that
down
and
then
extensible
modules.
So
that's
why
I
go
back
to
the
algorithm
step,
one!
It's
local
step,
two!
K
It's
link
local
step,
three
looking
in
the
routing
table,
otherwise
we
tried
to
sort
somehow
do
a
key
study
transfer
inside
the
bender
note
saying:
if
a
module
wants
to
take
care
of
the
routing
of
this
bender
then
take
it
on
that
would
be
I
would
imagine
directed
by
the
routing
block.
Otherwise
it
goes
into
cold
storage
on
so
that's
what
our
implication
doing.
Then
it
tries
to
create
an
opportunities
using
the
CLA.
It
isn't
the
forward
set
okay,
so.
B
Rick
Taylor's
speaking
personally,
I
understand
what
you're
talking
about
in
terms
of
having
a
bundle
carrying
a
routing
strategy.
I
was
waiting
for
some
of
the
older
IETF
errs
in
the
room
to
suddenly
jump
to
the
microphone
and
say
the
source
based
routing
is
has
proven
to
be
a
unwise
idea
in
some
circumstances
in
the
fixed
internet,
because
intermediate
nodes
often
have
a
better
idea
of
reality
than
the
sender,
so
yeah
I'm,
trying
to
think
of
the
right
word
says:
there's
always
traditionally
been
a
lot
of
pushback.
B
That
doesn't
mean
it's
not
a
good
idea
under
some
circumstances,
but
there
are,
there
are
dangers
there,
so,
whatever
handling
has
to
be
optional,
we
have
bundle
in
bundle,
be
less.
That's
quite
a
careful
use
case
of
tunneling
rather
than
the
sender
saying,
I
need
this
bundle
sent
by
this
path
to
the
endpoint.
This.
K
K
It
is
your
graphic,
it's
mostly
like
I'm.
My
experience
in
opportunistic
networks
is
that
the
routine
on
the
application
goes
hand
in
hand
yeah,
you
can't
have
you
can't
try
to
find
us
win
thousands
of
paper
on
each
of
them
addressing
a
specific
routine
issue
on
optimization.
You
can
have
a
epidemic
on
constrained,
epidemic
control,
epidemic,
random
epidemic,
and
then
you
have
the
cure,
forwarding
strategy,
geographical
routing,
but
at
the
end
it
boils
down
to
what
the
application
needs
on
on.
K
It
makes
sense
that
the
bundle
being
being
a
big
blob
of
data
that
doesn't
require
us
to
open
a
session,
because
it
contains
every
information
in
itself
make
sense
that
it
also.
It
may
also
contain
its
routing
strategy,
at
least
for
a
certain
portion
of
the
DTN
region,
which
might
be
challenging
yeah.
E
I
just
wanted
to
suggest
that
this
is
a
really
interesting
discussion
and
has
sort
of
been
going
on
for
about
15
years
and
I
think
we're
making
solid
progress
on
on
figuring
out
which
of
these
things
work
under
what
circumstances,
all
of
which
I'm
I'm
deeply
convinced
does
not
belong
in
the
bundle
protocol
specification.
It
belongs
in
in
other
documents,
because
there
are
volumes
right
there.
E
We
can
just
go
on
forever
talking
about
this
stuff
and
and
if
we
try
to
include
all
these
kinds
of
considerations
in
the
bundle
protocol
spec,
we
would
end
up
with
a
specification
that
nobody
would
be
able
to
lift
much
less
read
so
I
encourage
this
kind
of
thinking.
I.
Think
it's
great
I
think
the
you
know
discussing
the
options
for
things
that
may
resemble
source
path,
routing
or
maybe
not
example-
exactly
are
I
think.
E
B
Rick
with
the
chair
hat
on
following
on
from
that
I
I
agree
as
well:
I
I
think
Scott
and
the
working
group
spent
a
little
bit
of
time
making
sure
that,
for
example,
in
in
bundle
protocol
section
504
is
you
draw
out
here?
I
think
the
text
is
sufficiently
open
to
say.
The
forwarding
strategy
applies
to
stop
us
having
to
specify
in
the
bundle
protocol
spec
what
that
forwarding
strategy
will
be
but
pointing
to
where
it
is.
B
I
really
like
your
CLA
and
point
out
the
thing
I
think
that
would
be
a
really
interesting
document
to
write
up
and
I
would
include
the
link
local
one
hop
it
as
part
of
that
document
to
say
this
would
introduce
a
forwarding
strategy.
Ref
a
bundle
protocol,
section,
five
point
for
you:
if
you're
using
CLA
IDs,
then
this
could
be
a
step
there.
So
so
back
refer
back
point,
so
the
original
one
I
think
would
be
the
easiest.
We're
doing
it
right.
K
Yeah,
so
the
arena
hackathon
I
also
like
to
party
to
try
on
develop
the
VP
set,
which
I
mostly
did
so
again,
not
much
common.
The
draft
is
pretty
clean,
quite
easy
to
understand.
I
would
have
some
proposition,
though
I
feel
that
those
raft
were
developed.
Maybe
we
did
not
move
as
fast
as
PP
so
a
bit
independently,
because
there
are
some
things
that
I
found
a
bit
odd.
K
Why?
Why
do
we
have
integrity
in
the
ppb's
if
it's
covered
by
the
BP
SEC
I
feel
like
those
two
kind
of
it's?
Okay,
we
work
together,
but
it's
it's
twice
a
service.
Another
thing
was
when
in
basic
encryption
modifies
the
block
in
place,
meaning
that
when
you
need
to
parse
it,
if
you
don't
know
that
the
content
has
been
modified,
the
parser
will
throw
an
error
so
I
added
I
added
in
the
block
heater
I
added
a
little
a
flag
that
says
that
the
block
is
it
in
decrypted.
It
could
be.
K
If
you
want
to
be
generic,
we
could
just
say
the
block
has
been
modified
was
in
unintelligible,
so
don't
try
to
parse
it
until
until
it's
been
decrypted
in
the
abstract
security
block,
and
so
in
the
bp6
specification
there
was
a
lot
I
mean.
I
was
a
bit
confused
with
the
security
station
ID
on
actually
I
think
that
maybe
it's
a
mistake,
but
the
abstract
security
block
should
mention
cypher
suit
ID
rather
than
security
station.
D
Sorry
so
ed
brain,
if
you
implemented
this
with
the
security
Association
block-
that's
terrific,
because
we
just
had
put
that
together,
maybe
two
weeks
ago
or
just
right
before
the
end
and
we're
going
to
talk
about
that
sort
of
Nexus
a
b.p
sec
version.
Seven
was
the
sort
of
standard
version
we
had
taken
it
to
other
communities
for
feedback,
and
one
of
the
feedbacks
was
to
try
and
understand
this.
This
distinction
between
Cyprus
sweet
IDs
and
security
associations.
D
K
There
is
two
thing:
there
is
a
security
Association
block
which
mentions
security
station
ad
and
then
here
is
the
block,
integrity
and
confidentiality
which
both
derives
from
the
abstract
security
block,
which
mention
also
security.
Additionally,
but
I
think
what
it
mentions
release
they
first
say
for
asset
ID.
So.
K
Right,
ok,
so
that's
pretty
much
it
can
you
move
to
the
next
slide,
so
that's
information
photograph
that,
basically
that's
what
it
looks
like
right.
Now,
it's
a
fairly
modular
architecture,
so
every
red
blocks
on
the
Left
graph
would
use
that
can
be
loaded
on
runtime,
so
the
various
modules,
so
every
Canadian
Slayer
is
a
module.
So
a
module
is
just
an
program
that
include
the
API
and
then
you
can
do
pretty
much
everything.
So
every
conference
leader
is
a
module
routine.
K
So
because
we
have
this
notion
of
link
table
on
routing
table,
a
module
can
passively
feed
the
routing
table.
So
if
we
were
to
implement
the
profit
draft,
basically
what
we
do
that
it
would
have
its
own
its
own
chat
protocol
over
bundle.
It
would
probably
send
messages
to
a
degenerate,
slash
profit
and
then
they
would
feed
the
routing
table
using
their
own
strategy,
and
we
also
have
the
active
routing
protocols,
which
is
the
routing
block.
K
So
right
now,
there's
only
one.
It's
a
so
called
EDC
piece
for
liberty
and
client
protocol,
and
then
you
have
the
so.
The
connection
agent
will
which
marshal
the
services
of
the
convergence
layer
to
instantiate
channel
on
the
discovery
agent,
who
is
actually
taking
care
of
discovering
nodes
in
a
run
so
showing
the
IP
network
it
we
try
to
discover
its
IP
peers
on.
If
it
does
it
will
it
may
ask
the
connection
engine
to
create
a
connection.
So
that's
that's
in
this
co
agent.
K
That's
a
work
in
progress,
but
basically
I
wanted
to
do
a
small
bundle,
not
neighbor
discovery,
so
I
think
it
would
be
interesting
to
have
some
core
services.
I
mean
core
application
agent
that
provides
some
services
like
I
was
thinking
of
a
new
agent
that
would
put
everybody
received
into
into
the
trash,
so
that
could
be
useful
for
peeing
on
a
traceroute,
because
the
implementations
I've
seen
so
far.
K
They
when
we
implement
implement
an
actual
application
agents
that
should
send
on
receive
being
bundle
and
I
think
we
already
have
everything,
because
we
have
the
administration
records
that
can
say
when
there
was
forwarded
or
delivered.
But
what
to
do
with
that
vendor
that
we
received
by
default.
It
would
put
it
in
cash.
So
if
we
had
a
slash
Neal,
we
could
still
be
able
to
send
administrative
records
yet
no
need
to
spend
much
time
on
processing
the
Panda
and
the
hello
one
was
just
too
so.
K
B
A
A
B
B
D
My
name's
Edie,
brain
and
I
want
to
talk
about
the
bundle
protocol
security
specification,
so
this
had
gone
through
a
series
of
reviews.
It
was
put
into
working
group
last
call.
It
did
get
a
preliminary
security
ad
review
coming
out
of
the
preliminary
security
ad
review.
There
were
one
or
two
sort
of
minor
comments.
D
I
think
the
most
significant
comment
was
cleaning
up
some
of
the
language
to
require
that
our
confidentiality
suites
use
a
EAD
cipher
suites
that
we
always
have
a
signature
on
the
ciphertext
and
otherwise
to
just
make
sure
that
we
included
that
our
integrity
mechanisms
other
than
that
were
always
on
the
the
open,
plain
text.
If
we
were
just
providing
integrity
on
on
other
blocks,
just
a
small.
A
A
D
It
would
be
good
to
be
correct,
so
we
had
incorporated
all
of
that
feedback
and
we
were
taking
it
out
to
other
communities
for
review
another
one
of
those
communities
was
the
CC
SDS,
which
also
gave
it
a
security
review,
and
they
came
back
with
a
series
of
recommendations.
Most
of
them
were
specific
to
CC
SDS
and
would
not
apply
to
BP
sec.
We
just
a
few
weeks
ago
were
another
CC
SDS
meeting
and
they
had
another
set
of
recommendations,
and
we
wanted
to
talk
about
those
right.
One
of
those
recommendations
here
so
briefly,
yeah.
N
D
So,
at
the
last
IETF
we
asked
a
series
of
questions
as
to
whether
we
needed
to
make
any
changes
to
BP
sack.
One
of
them
did
we
need
additional
graphics
to
make
the
specification
clearer.
We
felt
the
answer
was
no.
It
was
good
to
hear
that
an
implementer
of
BP
sack
felt
that
the
spec
was
clear
and
easy
to
walk
through
as
well.
We
asked
the
question:
could
ciphers
weights
alter
the
size
of
the
target
lots
of
data
fields?
D
We
we
said
that,
yes,
that
is
allowed,
and
we
do
have
mechanisms
now
for
accomplishing
that
without
much
difficulty
do
do.
We
need
language
to
allow
cipher
suites
to
be
able
to
remove
blocks
from
a
bundle
we
said.
No,
that
could
be
something
that
is
in
cipher
suite
specific
implementations,
and
it
just
needs
to
not
be
precluded
by
the
specification.
D
It
doesn't
need
to
be
explicit
in
the
specification
and
then
finally,
there
was
some
question
as
to
do
you
want
the
specification
to
prevent
adding
a
b
c
b
and
a
bib
on
a
target
at
the
same
time,
because
no
one
would
ever
do
that
they
would
always
if
they
were
adding
encryption
at
the
time
a
bundle
was
created,
they
would
always
encrypt
and
then
have
an
integrity
signature
on
the
ciphertext
and
you
would
not
need
a
bib.
And
while
we
said
that
that
is
a
good
practice.
D
D
So
next
slide,
then,
when
we
went
to
see
CSDs
security
review,
there
were
additional
minor
comments.
Many
of
them
dealt
with
adding
additional
hooks
into
CCSD
s,
documents
for
cipher,
suite
selection
and
background
context,
material
and
how
this
would
be
used.
None
of
that
would
be
appropriate
in
the
VP,
sac
RFC
or
do
draft
document.
D
One
question
that
came
up
at
that
meeting
a
few
weeks
ago
was
whether
or
not
there
was
value
in
trying
to
talk
about
the
security
parameters
as
a
security
Association,
in
the
sense
that
bi,
B's
and
B
CBS,
instead
of
having
cipher
suite
identifiers
and
instead
of
having
cipher
suite
parameters,
would
simply
have
a
security
Association
identifier
and
it
would
be
presumed
that
either
out-of-band
or
using
some
other
mechanism
in
the
bundle.
You
would
be
able
to
define
what
exactly
that
security
Association
was.
D
We
were
not
convinced
at
the
time
that
that
was
the
correct
way
to
go
because
security
associations,
one
is
a
very
loaded
term,
and
it
does
imply
that
you
have
done
a
lot
of
back-to-back
negotiation
and
state
synchronization
that
you
cannot
do
in
a
DTN,
but
what
we,
what
we
decided
to
do
was
just
to
try
and
prototype
what
it
might
look
like
to
say.
Let's
create
a
a
draft
version
of
the
document
that
has
a
a
stab
at
security
associations
in
it.
D
If
we
don't
like
it
or
we
want
to
do
something
different,
it's
obviously
very
easy
to
correct
that.
So
what
we
did
was
we,
we
came
back
and
said
a
way
of
looking
at
this
is
to
say
that
right
now,
bib
and
BC
B
carry
cipher
suite,
identifying
information
and
parameter
information
with
it.
If
you
were
to
extract
that
information
away,
give
it
a
handle
and
then
call
that
handle
the
security
Association,
then
what
would
that
look
like?
D
B
B
When
IDI
was
talking
to
this
they're
talking
about
this
with
me
was
and
I
think
it's
the
same
comment
loosing
has,
which
is
there,
isn't
really
any
difference
between
a
cipher,
suite
ID
and
a
security
Association
ID?
If
you
think,
instead
of
a
cipher
suite
ID
being
the
identifier
of
the
cipher
suite,
you
are
using,
you
say
it's
just
the
identifier
of
the
way.
I
am
applying
security
to
this
block
and
it
can
either
be
in
line.
B
So
it
is
actually,
as
the
original
cipher
suite
ID
was
so
I'm
using
I'm,
putting
all
my
n-tuple
of
IV
and
salts
and
whatever
is
required,
including
the
identifier
of
the
cipher
suite
I'm
using
and
it's
all
in
line
in
the
block,
or
you
can
say
it's
a
reference
to
a
security
identifier
block.
So
you
have
the
the
proposal
of
the
security
associations
and
I
have
completely
forgotten.
The
third
example
sorry
miss.
B
Is
pre-placed
that
was
it,
it
was
for
people
who
wanted
to
say
I
actually
have
a
security,
Association
pre-configured
out-of-band
between
my
two
end
points
and
I
just
want
to
refer
to
it
by
an
ephemeral
identifier.
So
I
want
to
say
this
is
number
four
and
we
all
know
what
number
four
is,
but
no
one
else
does
and
all
I
have
to
send.
You
is
four
and
you
know
what
I
mean
and-and-and.
D
What
was
important
about
all
of
those
is
that
none
of
these
add
or
remove
particularly
technical
abilities
I,
could
have
a
cipher
suite,
ID,
seven
and
a
parameter
could
be
pony
and,
and
that
is
an
out-of-band
meaningful
thing
and
and
that's
the
same
as
saying
I
have
a
security
Association
of
three:
don't
worry
about
how
we
made
it
or
what
it
means.
The
the
the
thing
I
don't
like
about
this
approach
is
security.
Association
is
a
loaded
term.
D
There
may
be
value
in
the
size
compression
here
so
that
you
do
not
need
to
repeat
a
cipher
suite,
ID
and
cipher
suite
parameters,
one
way
of
handling
that
was
with
target
multiplicity,
so
maybe
there
is
a
significant
size
compression,
so
the
question,
and-
and
so
perhaps
we
comment
back
to
other
communities
looking
at
this
is
security.
Association
is
the
wrong
term,
maybe
handle
or
reference
or
something
like
that
is
a
better
term
but
term
aside.
D
Is
there
a
value
in
in
having
the
bi
B
and
the
BC
B
include
a
reference
to
cipher
materials
as
opposed
to
the
cipher
materials
themselves,
now
that
that
is
ultimately
a
relatively
small
change,
one
way
or
the
other,
and
and
arguably
it
doesn't
rise
to
great
significance
in
this,
but
it
is
sort
of
as
we
collect
subject
matter
expert
review
of
this.
That
becomes
the
latest
question.
Do
we
want
to
have
bibs
and
BC?
D
B's
include
some
kind
of
reference
which
can
be
a
reference
to
something
in
band
or
reference
to
something
out
of
band
rather
than
cipher,
suite
ID
and
cipher
suite
parameters,
or
would
we
say
cipher
suite
ID
can
itself
act
as
a
reference
to
something
in
band
or
something
out
of
band,
and
therefore
we
don't
need
something
new.
So.
B
Rick
again,
as
part
of
my
conversation
earlier
with
with
Ed
about
this
I
agreed
that
the
terminology
of
an
essay
is
so
loaded
with
IPSec.
You
know,
people
know
what
an
IPSec
essay
is
and
it
I'd
be.
Sec
relies
on
a
complete
end-to-end
connectivity
and
that
that
just
doesn't
exist
in
the
DTM.
So
we
should
not
use
the
word
security
association
equally.
If
we
are
to
introduce
the
idea
of
indirection
and
I
can
see
the
advantages
in
terms
of
compression
and
also
maintaining
the
idea
of
an
out-of-band
security
Association
in
quotes.
B
B
D
There
may
be
some
question
of
you,
then
assume
that
if
something
has
been
queued
for
days
or
weeks
and
when
it
gets
to
another
end-
and
it
says,
I
have
contacts
X
that
that
may
have
been,
you
know
expired
in
some
way,
whereas
if
you
say
I've
been
encrypted
with
a
certain
set
of
keys
and
so
on,
I
mean
keys
themselves
are
ephemeral.
It
may
not
be
a
difference
that
makes
a
difference.
It
is
another
ephemeral
thing
that
we
need
complete.
B
Agree
with
you,
but
I
don't
see
that
that's
a
problem
with
the
specification
if
people
wanted,
if
people
want
to
set
up
an
ephemeral
relationship
and
some
of
the
bundles
last
longer
than
the
ephemeral
relationship
exists,
then
and
I'm
looking
at
Stephan.
To
tell
me
that
we
ought
to
document
that
that
is
a
whole
you
can
fall
in,
but
that's
a
whole.
You
can
fall
in
because
you've
dug
it.
K
Speaking
just
a
little
remark,
I
seen
another
problem
in
orphan
in
the
encryption,
with
the
parameters
of
the
encryption
separating
these
two
in
in
context
rather
than
debating
its.
If
you
have
a
node
in
between
that
wants
to
check
it,
for
instance,
integrity,
and
it
doesn't
have
the
parameters
of
how
the
integrity
was
complete,
just
have
a
context
that
doesn't
have,
because
it
wasn't
part
of
the
trusted
parameter
as
the
nodes
and.
G
K
Can
do
it
and
we
can
forward
the
corrupted
when
there's,
even
though
Vic
would
be
able
to
check
for
integrity
on,
we
could
have
stopped
the
propagation
so
I
think
it's
interesting
to
this
approach
is,
if
I
understand
just
you
still
can
derive
the
parameter
of
the
encryption
on
the
integrity
using
at
the
security
station.
They
did
right,
it's
all,
embedded,
independent,
so
well,.
B
I
I
G
D
D
F
I
D
The
other
point
being
is
that
in
cases
where
all
the
cipher
suite
parameters
do
happen
to
line
up,
the
spec
allows
you
to
stack
security
results
in
the
one
block,
so
you're
not
having
multiple
blocks
in
that
case
anyway.
So
there's
no.
So
my
recommendation
is
we.
We
template
addthis
just
to
see
what
it
would
look
like.
I.
Think
we've
gotten
a
couple
of
examples
here
as
to
what
could
be
problems
with
that.
B
Hat
on
we're
under
a
lot
of
pressure
to
actually
get
documents
finished,
we
have
yet
to
finish
anything
and
I
know
we're
waiting
on
the
convergence
layers,
but
I
would
be
nervous
about
saying
well,
let's
rescind
BP
SEC,
with
some
exciting
new
ideas,
because
we've
come
up
with
them.
While
we
were
waiting
to
finish
it,
it
might
be
something
with
my
pragmatic
hat
on.
You
could
retrofit
this
by
introducing
a
new
cipher
suite
id
of,
and
now
we
do
in
Direction
blocks
into
somewhere
else.
I'd
like.
F
B
A
A
D
That
the
last
remark
was
this
was
a
comment
that
came
back
from
the
CC
SDS.
We
said
that
we
would
present
it.
We
thought
a
way
to
present.
It
would
be
to
come
up
with
the
draft.
So
if
anyone
wanted
to
read
it,
they
would
be
able
to
give
review.
You
have
read
it
and
and
gave
an
implementation
of
it
and
then
came
back
with
some
review.
So
in
that
sense
it
was
a
worthwhile
endeavor.
