►
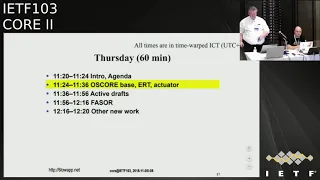
From YouTube: IETF103-CORE-20181108-1120
Description
CORE meeting session at IETF103
2018/11/08 1120
https://datatracker.ietf.org/meeting/103/proceedings/
A
A
C
B
Gonna
present
the
update
on
not
score,
so
the
status
is
that
we
are
in
version
15
that
was
submitted
in
August.
There's
one
discussed
left
from
acre
and
we
got
a
few
comments
from
him:
channeled
through
Alexey,
this
Sunday.
So
that's
what
we've
been
working
on
now.
Unfortunately,
it
got
congested
in
ad
space
on
the
way,
but
anyway
we
started
in
this
meeting
to
work
on
on
the
comment.
B
The
unprotected
message
fields
so,
as
you
remember,
we
introduced
an
appendix
need
to
handle
on
a
record
previous
comments
and
in
particular
the
four
is
looking
at.
If
you
like,
a
residual
risk
type
of
scenario
where
you
have
protected
the
message-
and
you
still
have
unprotected
message
fields
and
what's
the
consequence
of
that
so,
for
example,
out
there
code
can't
be
changed
so,
which
actually
is
it's
not
a
problem?
B
Because
our
code
is
a
dummy
code
and
the
inner
core
contains
the
the
actual
method
that
the
same
trend,
integrity,
detect
and
then
so
that
does
probably
here
misunderstanding.
Then
we
have
a
comment
related
to
proxy
operations.
That
proxies
are
allowed
to
change
things
like
like
options.
It
could
change
your
I
host,
your
report
and
scheme
and
so
on,
and
that
was
the
question
why
that
is
okay
and
that's
essentially
what
co-op
and
forward
proxies
are
allowed
to
do.
So.
B
That's
I
think
that
suppose
should
be
quite
easy
to
answer
as
well,
and
the
third
comment
related
to
messaging
layer.
So,
as
you
know,
our
score
is
not
protecting
messaging
layer.
It's
only
protecting
the
request,
response,
layer
and
rest
operations
and
that's
because
it
won't
application
layer
security
that
could
could
work
on
another
transport.
B
So
the
corporate
TCP
doesn't
have
a
messaging
layer,
so
that's
not
protected
by
an
explorer
and
then
we
can
protect
over
TCP
use,
Morse
code
and
again,
that's
also
I,
think
related
to
the
understanding
of
all
exactly
what
are
we
protecting
with
all
its
core?
So
we
had
a
meeting
with
actor
on
Monday
to
discuss
this
and
and
he's
missing
a
threat
model,
basically
framing
that
part,
so
the
what?
What
do
we
protect?
B
So
that's
the
proposal
for
resolving
these
comments
is
basically
make
a
few
minor
clarifications
on
these
points,
and
we
add
this
appendix
T,
which
is
a
threat
model,
and
we
have
time
to
do
that
based
on.
Why
should
we
have
done
that
and
based
on
one
RFC,
which
is
model
so
those
two
three
comments
and
then
was
a
forced
comment
which
related
to
which
was
actually
a
comment
from
Varga
one
Karkat
Bartek
Varga,
one
related
by
Edgar
and
Alexei,
and
arrived
on
Sunday,
which
was
about
storage
to
non-volatile
memory.
That
was
a
good
comment.
B
We
think
so
we
have
me
some
super
slide.
So
this
relates
to
how
we
handle
loss
of
mutable
security
context,
and
this
is
not
mandated
in
aw
score,
but
in
section
75
we
give
examples
of
how
you
could
use
non-volatile
memory,
in
particular
writing
sequence.
Numbers
to
non-volatile
memory.
There
is
a
simple
write
scheme
is
basically
saying
that
if
the
sequence
numbers
are
divided
about
by
K,
then
you
write
it
to
non-volatile
memory.
B
Then
you
do
the
operation
and
if
you
happen
to
reboot,
then
you
read
from
non-volatile
memory
and
you
add
the
interval
K
now.
The
issue
here
is
that
writing
to
non-volatile
memory
has
and
may
have
an
unpredictable
completion
time,
which
means
that
they
might
not
have
the
you
might
have
lost
this
right
operation
due
to
rebook,
and
the
proposal
is
also
indicated
by
acre-
is
that
you
look
at
other
ways
for
or
handling
lots
of
security
context,
and
there
are
various
ways
to
do
it.
So
the
proposal
is
that
we
expand
on
the
alternatives.
B
One
alternative
is
obviously
to
make
a
key
exchange
protocol,
which
would
happen
a
lot
overhead
and
require
good
random
number
generation,
and
another
example
is
that
you
involve
in
a
trusted
third
party
assisted
key
provisioning
like
like
one
of
the
age
profiles,
and
there
is
also
a
third
variant
where
you,
you
still
have
the
shared
key
available.
Although
the
context
is
not
it's
not
up
to
date,
so
you
could
use
the
shared
key
and
you
could
introduce
a
random
number
and
derive
in
your
context.
All
these
are
perfectly
fine
examples.
B
So
we'd,
like
you
added
those-
and
we
also
like
to
keep
the
case
of
storing
to
non-volatile
and
memory,
but
we
wanted.
We
will
emphasize
the
the
issues
and
update
the
right
scheme
so
that
we,
in
addition
to
adding
K,
we
also
add
some
upper
bound
for
completing
the
right.
So
that
means
additional
safeguard
against
reuse
of
sequence
numbers,
but
we
like
them
to
allow
the
application
to
decide,
because
in
some
devices,
handling
the
right
to
non-volatile
might
actually
be
more
secure
than
they're
lying
on
ran
around
a
number,
a
bad
random
number
generator.
A
B
Yes,
I
mean
this.
These
are
all
these
are
examples
and
the
application
has
to
decide
and
exactly
how
you
set
up.
As
you
know,
our
score
is
assumes
to
have
secured
keys
in
place
and
how
you
get.
Those
piece
in
place
is
supposed
Ella
gated
to
other
protocols
like
and
the
ACE
profile
in
our
score
or
like
ad
hoc
or
likes
another
okay,
so
that
that's
it
from
from
the
in
terms
of
comments.
We
have
we're
made
these
updates
as
proposed
here.
B
A
From
a
sharing
or
document
shepherding
perspective,
the
problem
really
is
that
that
we
are
giving
a
little
bit
of
you
that
this
document
is
unstable
because
we
are
generating
so
many
new
versions.
But
the
reason
is
that
we
get
the
comments
and
piecemeal
fashion
and
we
are
trying
to
react
to
each
of
these
and
now
that
that
doesn't
really
look
very
good.
It
requires
some
some
explanation
to
people
who
are
looking
at
this
process
and
asking:
why
do
we
need
ten
revisions
to
get
this
through?
The
iesg.
B
D
Know
from
Nokia
my
question
is
as
a
chair
of
BMS
II
working
group
from
Omaha.
We
have
quoted
this
41.1
specification
and
we
have
approved
that
likely
time
to
a
1.1,
I
hope
this
gets
completed
and
moves
to
the
next
stage
as
fast
as
possible,
because
I
thought
this
would
have
being
then
sometime
back.
B
You,
ladies
I,
try
to
use
them.
Well,
so
echo
request
tag
is
in
version
3.
We
have
updated
according
to
all
review
comments.
We
got.
We
got
really
good
comments
from
them,
so
we
think
this
is
ready
for
working
group.
Last
call
and
I
think
do
you
match
agreed
on
that,
so
there
is
a
normative
dependency
from
request
from
Proctor
state.
If
you
request
tag,
which
is
yet
another
reason
why
this
should
progress
you
want
to
take
that
separately,
should
I
go
on
to
actuators
I'm
done
with
requests,
are.
A
The
usual
quick
questions,
who
has
read
a
recent
version
or
take
a
requester
all
so
that
this
is
going
into
Gordon
last
call
now,
so
please
have
a
look
at
it
and
find
out
whether
there's
something
in
there
that
that
is
horribly
problem
before
we
issue
the
breaking
glass
cause.
So
this
is
the
time
to
actually
look
it
up.
Okay,.
B
This
is
really
quickly.
First
explanation
of
this
craft
is
so
a
cone
request.
I
go
to
separate
drafts,
having
separate
problem,
description
and
solutions.
We
took
the
solutions
and
put
in
the
draft
we
talked
about
recently,
and
this
draft
is
about
the
problem
statements
and
the
question
is:
what
was
the
working
group
want
us
to
do
with
it?
So
it's
an
informational
draft.
B
A
A
A
So
we
now
had
the
the
gong
show
of
active
draught
we're
going
to
go
to
half
dozen
active
drafts
quickly
hop
limit,
that's
something
that
we
owe
to
the
dots
people
we
promised.
We
would
solve
their
problem
for
them
and
there
is
a
working
group
document
that
has
been
around
for
a
couple
of
weeks.
That
was
discussed
at
interim
meetings
and
apparently
we
have
been
pretty
slow
to
relay
our
concerns
to
the
office.
A
So
right
now
there
are
still
some
clarifying
going
on
whether
the
concerns
are
actually
addressed
in
the
conduction
and
are
we
needed
ever
one
before
we
can
go
forward
in
the
spot,
so
just
to
remind
people.
This
gives
us
a
way
to
limit
the
number
of
hops
the
number
of
proxy
hops.
The
request
takes
from
the
client
to
the
origin
is
our.
E
Okay,
thank
you.
So
this
is
a
most
recently
out
of
the
suburban
top
line,
so
we're
now
at
version
with
zero,
zero.
Here's.
What
happened
on
updates
since
the
zero
three,
the
key
thing
was.
We
clarified
their
security
consideration
section
that
there,
even
though
you
are
able
to
address
outlaw
names
in
the
single
parts,
you
are
not
conceptual
reaching
to
different
resources.
That
was
very
prescient
hidden
in
there
in
the
earlier
version.
There
was
a
small
change.
E
We
did
there,
but
the
bigger
question
is:
do
we
want
to
do
new
media
types
or
or
not?
So,
as
a
crystal
pointed
out
in
his
review,
there
are
some
challenges
with
the
way
using
reusing
the
existing
sentinel
media
type,
even
though
the
current
way
of
reusing
that
maps
nicely
with
a
couple
of
different
operations
using
the
same
cinema
constructs.
E
However,
if
you
do
patch
or
if
you
do
fetch,
they
are
issued,
that
said
ml
RFC
said
you
must
have
the
value
of
those
records
and
what
we're
proposing
for
the
fetch
method
was
that
you
seem
to
keep
the
names.
So
we
had
a
conflict
on
how
you're,
using
they
send
no
current
media
type.
So
after
some
discussions
on
the
list
and
also
with
my
DM,
it
seems
to
be
appropriate
that
we
actually
do
have
different
media
type
or
veteran
patch.
So
then
we
don't
have
these
issues
of
being
fully
aligned.
E
With
the
existing
cinema
seminar
see,
we
are
still
using
the
same
constructions,
which
says
that
we
don't
have
this
issue
with
having
an,
for
example,
something
different
for
the
B
value
that
would
expect
otherwise.
So
the
proposal
here
is
that
we
would
go
back
to
media
for
new
media
types
and
key
questions.
E
D
E
E
Yes,
so
if
it
was
the
same,
immediate
Anthony
would
need
to
know
basically
also
the
method
that
it
was
used
in
order
to
be
able
to
interpret
later
on.
So
it's
a
separate
media
type.
Those
issues
go
away.
The
good
thing,
of
course,
would
have
been,
then
we
would
be
able
to
use
all
existing
media
types
as
such.
Now
we
have
the
register,
depending
how
many
we
end
up
with
two
or
for.
F
An
example
so
plus
one
for
the
different
media
types
and
also
over
the
question
of
you,
know,
trying
to
support
many
different
surahs
Asian
formats.
I
would
say,
like
you
knows,
stick
to
the
minimum
thing
that
works
and
then
you
know
stand
in
the
future.
If
someone
wants
that,
so
see,
bolos
really
really
a
great
way
to
encode
them.
The
daily
thing
everything
else
is.
D
Okay,
but
MCMAP
from
okay,
again
it
earlier
soon
as
well.
I
got
the
same
kind
of
discussion,
but
I
want
to
make
it
here
with
the
Seabourn,
so,
whatever
we
are
doing
in
terms
of
in
Nydia,
we
are
looking
at
things
what
is
needed
for
next
plus
two
years,
plus
three
years.
So
if
we
are
going
on
extending
and
supporting
legacy
formats,
content
types
or
whatever
it
may
be,
I
think
that's
not
the
right
way
to
go.
D
So
in
this
case,
he
bar
is
the
way
to
go
for
sure,
and
we
should
not
look
at
things
from
backward.
Similarly,
even
for
the
suit
I
had
the
same
commanded,
don't
look
for
legacy
stuff.
Look
for
what
is
going
to
be
produced
in
the
next
two
years,
which
may
not
even
be
the
same
boat
as
we're
looking
at
today,
what
kindness
is
carrying
it
on.
E
G
E
And
how
about
the
same
immediate
approve
it's
a
batch.
Is
there
a
reason
to
have
separate
for
those,
or
can
we
just
have
a
single
one?
That
is
for
both
action
touch?
We
were
all
we
almost
have
the
same
for
all
of
them,
so
having
a
single
one,
perfection
pack
seems
reasonable
unless
there's
something
we're
missing
here.
I
see
people
not
England
one
media
type
or
both
is
good.
E
Okay,
then
the
other
issue.
Now
when
we
have
the
new
media
type,
how
do
we
do
a
deletion?
So
all
the
other
operations
are
quite
straightforward,
except
how
you
indicate
that
you
want
to
believe
a
record
from
a
patch
and
at
least
these
three
different
ways
are
our
options
for
us.
The
first
one
is
what
is
currently
in
the
draft,
so
you
will
indicate
a
that
value
is
now
that's
the
Chasen
merge,
but
spread
style
deleting
living
things
from
Jason
contract.
It
is
kind
of
clean.
E
There
is
an
issue
that
I
sent
an
RFC
said:
okay,
use
it
all
well,
instead
of
RFC
that
we
have
different
tax
for
different
kind
of
values,
and
now
you
would
have
a
be
used
to
have
only
both
now
we
could
also
have
a
no
it's
a
different
media
type.
So
it's
that
big,
an
issue,
but
some
parts
are,
could
be
confused,
an
alternative
that
that
Christian
was
proposed
in
his
review.
Was
this
video
equals
true
or
something
similar,
basically
a
flag
in
the
record?
E
The
cool
thing
about
this
is
that
it
doesn't
have
the
problems
of
variable
types.
On
the
other
hand,
this
we
could
buy
a
new
tag
on
another
big
cost
and
it's
slightly
more
verbose
in
Jason
cause.
You
actually
write
it
through
in
with
four
letters.
I
can
see,
bore.
Of
course,
it
becomes
pretty
compact
and
the
final
option
is
to
have
this
chasing
ax
type
of
arm
operations.
So
you
have
a
defining
operation
that
says
it
removed.
H
F
Yeah,
so
the
thing
is:
I
have
not
really
thought
about
how
this
fits
in
Sena.
Now
so
probably
some
of
the
things
that
I
might
say
they
will
not
accents
to
you.
But
I.
Look
this
to
the
point
of
view
of
kamae,
because
there
will
be
a
lot
of
things
in
fashion
patch
and
I
mean
he
considered
this
from
the
start,
and
then
there
we
did
it
with
the
node
so,
but
it
makes
sense
right.
F
It
I
mean
by
looking
at
the
scheme
and
I
think
it
was
really
clear
that
you
knew
that
whenever
you
get
to
know
them,
you
know
like
the
operation
was
removal
removal.
The
element
I
have
not
thought
about.
You
know
the
variable
things,
but
that
could
be
a
question
here
right,
but
you
know
maybe
one
thing
to
look
at.
Is
this
as
comidas
the
pageant
edge
and
they're
one
of
the
points
over
there
is
that
we
really.
We
also
said
that.
F
Okay,
we
need
to
have
two
media
types
just
so
that
we
differentiate
between
patch
and
patch,
because
the
structure
is
a
little
bit
different
of
the
payload.
That
goes
there,
because
the
operations
there
a
little
bit
different
but
then
I
mean,
as
I
said,
I
have
not
really
I
mean,
probably
have
much
more
feedback
on
on
that
point.
So
if
I
mean,
if
you
don't
risk
your
your
code,
you
know
just
by
some
chance
of
you
get
your
fetch
method
or
some
payload
get
gets
rather
to
the
patch
and
then
some
strange
stuff
happening.
F
E
F
Actually,
we
had
big
discussions
at
the
time
were
like
okay.
Do
we
go
with
everything
you
just
see,
bow
and
call
it
stuff?
And
then
we
look
at
the
method.
Is
it's
patch
patch
get
peep
toes
delete
and
then
on?
Based
on
that,
we
can
do
now.
We
can
infer
how
the
sea
were
structured,
so
that
was
like
the
one
end
of
the
spectrum
and
the
other
end
of
the
spectrum
was
okay.
We
have
to
mediate
at
for
every
for
every
type
of
payload
and
because
there
were
several
times
several
things
that
we
can
encode.
F
We
can
encode
individual
elements.
We
can
encode
collections
of
things,
we
can
encode
hatch
collection
and
you
know
how
do
you
form
the
fetching
of
things?
How
do
you
do
the
patching
of
things
and
then
actually
it
was
much
more
readable
with
having
several
media
types,
because
I
mean
at
least
in
the
Khmer.
Otherwise
it
was
like
okay.
Well,
in
this
case,
I
can
have
like
a
the
list.
F
F
E
E
E
A
K
So
if
people
be
able
to
get
into
the
review
cycle
again
and
up
true
in
the
interim
before
the
next
meeting,
they
can
see
on
this
one.
So
mixed
didn't
mean
yeah
dine
link.
So
basically,
recently
I've
done
a
reference.
Implementation
of
the
condition
will
observe
attributes
and
see,
and
also
they're,
learning,
interesting
learning
about
that,
and
it
turns
out
that
there's
really
it's
a
fide
logic
of
expression
and
also
there's
some
learning
from
developing
LCF
version
of
dine
link
and
with
OCFS
we're
not
using
the
conditional
observed
for
just
using
the
timing
pattern
itself.
K
So
I've
got
a
couple
of
sides
to
sort
of
some
examples:
the
next
one
being
the
next
one.
Okay,
so
basically
there's
this
is
the
C
code
that
just
two
pages
a
second
page,
next
yeah,
okay,
then
there's
some
definitions
and
then
a
couple
of
logic,
expressions
that
cover
scalars
strings
and
GUI,
and
so
on
take
a
look
at
that
that's
referenced
in
the
github
and
actually
in
the
current
draft.
Now
as
well,
let's
see
next
slide.
Please
yeah,
okay!
K
Christian
analysis
gave
us
in
the
feedback
that
you
know
we
looked
at
and
I
think
we
wanted
to
basically
do
that
and
then
provide
these
observe
attributes
in
the
example
document.
As
query
parameters
to
the
observe
request,
there
are
some
questions
and
issues
about
that,
but
looking
at
all
the
options
that
what
seems
to
make
the
most
sense
then
doing
that
we
could
structure
the
draft
where
we
introduced
the
observe,
attribute
and
then
talk
about
dyeing
links,
and
then
we
have
this
binding
table
implementation.
So
it
also
agrees
to
the
action
of
restructuring.
K
Okay,
next
slide,
please,
okay,
so
you
also
take
any
comments
and
questions
after
the
whole
and
so
pub/sub
not
a
whole
lot
of
changes
recently.
But
we've
got
some
some
good
feedback
from
from
Peter
stock
I
believe
and
we
want
to
track
what's
going
on
with
the
429,
although
I
think
that
things
are
looking
fine
for
that,
there's
no
big
deal.
We
wanted
to
get
some
implementation
experience
with
pub/sub
as
well
and
I
don't
want
to
maybe
set
up
an
interim.
K
The
mini
plugfest
and
I've
been
talking
with
Federico
at
interrupts
on
the
sort
of
GTN
modes.
We
might
need
to
do
that
and
so
I
I
don't
know
how
quickly
that
can
happen,
but
I
think
that's
that's
an
approach
to
getting
some
implementation
experience
and
I'm
going
to
produce
some
kind
of
implementation
of
them
and
we'll
see
how
that
goes.
Who.
K
L
K
L
K
Okay,
sort
of
looking
at
some
of
the
ways
of
using
Open,
VPN
and
also,
but
what
we
want
to
do
is
use
make
a
V,
Allen
and
sort
of
have
a
standard,
little
router
box
that
people
can.
You
can
do
that's
a
little
ambitious,
but
it
seems
like
that's
really
the
way
to
make
it
work
right
anyway,
separate
topic,
but
maybe
you
want
to
try
to
enable
that
by
the
way
yeah.
A
A
This
one
no
comment
no
no
come
on.
Thank
you.
Thank
you
Michael.
This
is
a
very
short
meeting,
sorry
for
rushing
you
through
this,
but
we
have
some
some
more
items
on
the
agenda.
The
next
item
we
have
is
a
congestion
control
and
while
a
PO
is
coming
through
the
front,
let
me
just
report
from
a
meeting
we
have
had
yesterday
between
the
two
groups
that
have
congestion
control
proposals
out
there
and,
as
I
said
on
the
Monday
meeting,
we
have
some
some
interesting
observations
about
the
the
cohort
document
and
we
had
different
understandings.
A
We
noticed
this
in
London
and
ran
out
of
time
resolving
this
in
Austria,
and
this
time
we
finally
made
it
and
by
nailing
it,
the
authors
of
the
Coco
draft
noticed
that
they
also
have
different
understandings
of
what's
in
that
past,
and
that,
of
course
puts
the
validity
of
the
simulation
sent
experiments
that
are
referenced
by
the
stuff
in
question.
So
for
us,
it's
back
to
the
drawing
board
and
I
have
asked
Maria.
M
Yes,
so
one
point
talk
about
this
new
consistent
control
proposal
called
fastener
and
it'll
be
out
there.
So
what
pass
or
tries
to
balance
between
between
there
are
this
two
contradictory
calls.
So
so
in
the
random
lost
case,
you
would
want
to
trick
at
the
RTO
very
fast
fast,
because
the
targets
are
not
lost
due
to
congestion
and
then
then,
in
case
of
conscious
and
you
need
to
slow
down
so
so
there
are.
M
You
need
to
do
both
ways
and
it's
hard
to
know
which
way
it
is,
and
we
realize
that
in
the
IOT
people's
composition,
mostly
this
expected
to
occur
when
you
have
very
large
number
of
devices.
So
so
we
wanted
to
test
test
its
at
scenarios,
and
this
is
the
way
we
can
came
across
these
problems
and
we
discovered
that
both
the
default
co-op
and
cocoa
have
had
some
issues
that
lead
to
congestion
collapse
collapse.
M
Despite
handling
the
conscious
of
well
it's.
It
is
also
able
to
and
of
the
random
lost
case,
so
you
don't
see
the
strengths
like
titles
at
all.
So
so,
what's
the
problem
with
or
problem
with
this
congestion
control
proposed
or
so
so,
there's.
First
of
all,
those
discounts
algorithm
for
TCP.
It
uses
exponential
back-off
and
keeps
the
back
of
RT
or
until
it
gets
an
onion,
because
RTD
sampled
and
on
the
other
hand,
we
have
this
cop
Co
efficient
control,
others
which
they
do
exponential
back-off.
And
there
is
this.
M
The
problem
show
up
when,
when
the
RTO
is
not
weak,
engine
like
it
comes
out
there
and
I
will
not
go
to
the
details,
because
how
how
to
how
this
is
manifested
in
the
devout
carbuncle
cards.
But
you
can
read
it
from
here
or
look
back
to
the
slides
and
tears
and
references
to
this
London
presentation
and
one
other
paper.
But
on
the
same
time
we
learnt
from
this
from
cocoa
and
effort
crop
that
it's,
it
is
cool
to
good
for
the
random
lost
case
to
actually
be
able
to
to
get
out
of
your
fast.
M
M
M
So
first
idea,
like
I,
said,
is
like
this
TCP
Artie
Artie
T
computation.
We
have
destroyed
the
small
modification
to
the
utilization
with
slowest
RTO
for
short
exchange.
We
have
the
disk
a
gator,
so
the
Alpha
T
bar
becomes
smaller.
So
if
you
are
sorted
chasing
helps
and
then
then
the
slow
RTO
is
analogous
to
this
consequently
skips
the
RTO
on
today
on
because
sample.
So
we
see
there's
this
figure.
M
M
So,
on
the
next
slide
slow
how
we
use
these.
So
we
add
additional
state,
so
normal
cars
only
has
these
two
states,
so
just
the
state
where
it's
music,
normal
transmission
and
then
the
second
state
this
which
is
using
using
the
longer
longer
RTO
but
in
fossil.
We
have
this
intermediate
state
state
where,
where
we
start
with
the
first
RTO
and
only
then
use
the
slow
our
deal
and
after
that,
we
again
can
use
the
fast
start
here,
because
we
her
handle
it
congestion.
M
If
there
was
was
such
already
quite
well
and
then
the
last
last
state
starts
with
slower
cue
in
order
to
ensure
that
we
can
always
need
to
take
a
oddity
measurement
and
these
state
transitions
or
shots
that
always
if
we
could
get
on
am
because
we
will
end
a
pact
that
is
passed
first
RTO
or
the
first
state,
which
is
using
only
first
diagnosis.
So
this
is
the
normal
RTO
back
of
service.
M
The
point
point
of
all
this
is
to
avoid
about
the
slow
about
using
slow,
RTOS
much
as
possible
because
it
has
inherent
cost.
If
you
need
to
actually
wait
for
that.
So
if
that
particular
pocket
for
which
you
have
are
armed
the
slow
RTO,
if
you
need
to
wait
for
that,
it
takes
a
lot
lot,
lots
of
time
and
in
random
random
closed
cases.
It's
of
course
not
very
nice,
wait!
Wait
because
the
pocket
was
not
lost
due
to
congestion.
M
So
when
we
send
retransmissions,
we
don't
know
which
of
those
request
copies
actually
trigger
the
acknowledgements.
So
with
this
using
this
option
or
other
entities,
the
option
can
be
ended
or
the
ordinal
number
of
the
transmission
can
be
angled
it
to
the
Tolkien,
since
it's
the
client
can
decide,
but
not
to
put
in
the
token.
So
it
has
this
possibility,
so
it
doesn't
need
to
always
use
this
option
it
doesn't
want.
M
M
For
Coco
we
have
disabled
aging
because
we
have
discovered
a
problem
problem
with
it,
and
it
was
is
up
like
this
floss.
This
has
been
reported
in
London,
so
you
can
probably
get
more
details
from
that
presentation.
So
we
have
to
test
scenario.
So
we
have
this
heavy
congestion,
which
includes
also
buffaloed
quesiton,
and
we
have
best
it
up
to
400
power
potion
or
well,
it's
parallel
class.
We
call
a
flow
one.
One.
One
of
these
quiet,
quiet,
quiet
or
this
set
of
clients
is
perform,
perform
50
request
responses
in
total.
M
M
400
clients
and
infinite
buffer
the
base
RTT
will
be
like
10
10
seconds.
So
so,
if
it's
each
of
the
flows
or
each
of
the
clients,
I
have
a
just
just
one
pocket
in
flight,
they
started.
He
will
be
dislodge
so
and
then
then
there
other
cases,
this
random
losses
case
where
there
is
no
competition
and
parallel
clients
and
the
error
models
are
also
mentioned
there.
So
it's
quite
thirsty,
thirsty
element.
M
The
this
congestion
collapse
problems
is
sewn
sewn
with
a
purple,
co-op
and
cocoa,
and
because
fossil
is
able
to
handle
the
consistent
well
that
it
gets
much
better
performance,
and
this
problem
is
mostly
due
to
unnecessary
transmission.
So
so
the
Pissarro
logic
is
able
to
reduce
the
number
of
unnecessary
Francis's
very
dramatically.
M
M
M
Median
median
for
fossil
fossil
is
significantly
smaller,
smaller
than
their
falco
for
Coco
and
on
the
RTO
side
we
might
need
it's
probably
not
well
visible
in
this.
But
if
you
look
on
your
own
screen,
the
know
know
that
the
right
hand
side
figure,
so
so
the
initial
RTO
is
two
seconds
and
the
taste
oddity
for
this
case,
where
there
is
no
competition,
is
this
six
660,
milliseconds
and
yeah
fossils
able
to
lower
this,
even
though
there
are
only
very
very
few
few
request
responses
before
the
congestion
control
state
is
weathered.
M
C
M
M
Token
talk
at
Maryann's,
so
so
state
test
performance
because
it
can
immediately
always
learnt,
is
even
even
when
there
were
some
losses
to
to
link
errors
and
one
interesting
detail
from
coke
coke
wised
also
visit
Tokyo
Celtic
artists
actually
crow
because
they
went
there.
There
are
enough
enough
errors
or
enough
random
loss.
Is
the
peak
estimator
collects
this
noise
from
the
ambiguity
samples
so
so,
instead
of
converging
Thomas
the
reality,
it's
actually
increasing
it
and
in
fossil.
We
avoid
this,
because
there
is
this
fast
RT
always
only
update
it
on
onion
because
sample.
M
So
we
never
take
this
on,
because
samples
in
the
day
and
first
RTO
measurements
or
computation,
then
we
have
some
items
which
this
might
not
make
sense
to
you
unless
you
have
worked
more
to
the
motive
the
details
of
their
algorithm.
So
but
at
the
end
we
both
go
through
them
now
so
occasionally
stir
fast,
slow,
fast
state,
backup
services.
It
may
actually
be
more
accuracy
than
what
what
goes
on
in
in
the
first
state.
M
M
So
if
we,
if
the
consistent
case
will
be
handled
correctly,
it's
likely
effect
Steven
Pinker's
case
or
this
random
loss
case
performance
somewhat,
and
we
think
that
the
faster
ogron's
complexity
is
not
significantly
higher.
It
might
even
be
slightly
lower
than
what's
the
complexity
of
Coco
and
because
of
the
promising
results.
We
believe
that
would
be
beneficial
for
the
whole
ecosystem.
M
A
Already
over
our
time
and
instead
of
point,
I
have
to
make
sorry
so
look
at
the
slide
and
be
impressed.
So
this
is
interesting
stuff.
This
is
good
stuff
and
at
some
point
we
would
have
to
decide
whether
we
want
to
adopt
this
and
one
very
important
question
that
came
up
when
we
looked
at
this
is
there
is
an
Ikea
declaration
on
this.
A
So
generally,
this
is
the
second
IPR
declaration
we
had
in
this
working
group
and
this
Burger
has
been
around
for
a
while
generally,
we
do
not
discuss
any
patent
claims.
This
is
a
patent
application
at
the
moment
on
in
meetings
on
mailing
lists,
but
the
the
procedure
is
that
working
group
members
form
an
opinion
about
this
and
decide
whether
they
think
this
is
an
obstacle
to
working
group
adoption
or
not.
A
So
the
one
thing
that
might
happen
is
that
the
patent
claim
owner
chooses
to
speed
up
the
discussion
by
providing
more
information
right
now.
The
IPO
declaration
is
very
basic.
It's
essentially
the
information
that
you
have
to
give,
but
not
not
not
much
more,
but
sometimes
I
get
owners
choose
to
provide
more
information
to
make
it
easier
for
the
working
with
to
understand
the
impact
of
this
idea
declaration.
So
right
now,
it's
very
hard
to
understand,
because
the
actual
patent
application
probably
won't
be
published
before
January
2020.
A
A
A
More
about
that
point,
this
time
it
has
been
properly
cleared.
Everything
is
wonderful
point
of
view,
but
we
still
have
to
find
out
how
we
want
to
handle
this.
Thank
you
any
more
comments
on
this,
so
who
has
ever
read
any
congestion
control
document
that
was
owned
by
this
working
group.
Oh
wait!
A
few,
that's
good!
Okay!
So
maybe
those
of
you
who
have
done
that
please
have
a
look
at
this
and
form
your
opinion
on
whether
this
is
technically
good
and
form
your
opinion
on
whether
the
patent
stuff
is
an
impediment
or
not.
A
A
Most
of
you
will
think
that
scientists,
surgeons
in
this
universe
are
expressed
as
x.509
certificates.
So
if
you
go
to
a
random
sto,
which
one
do
we
take
care,
they
will
think
if
they
need
anything
that
is
signed.
This
takes
on
the
form
of
often
X
of
x.509
certificate,
and
that
was
probably
true
for
about
30
years,
but
it
no
longer
is
because
we
now
do
have
those
RFC's
that
tell
us
how
to
do
it
in
a
different
way.
A
Now
is
you
still
may
want
to
use
certificates
because
you
have
the
infrastructure
for
ending
them
and
so
on,
but
it's
important
to
note.
There
is
another
way
of
doing
that
and
there
is
a
document
that
has
been
submitted
under
the
name
of
this
working
group.
I
have
no
idea
whether
that's
actually
a
good
fit.
Let's
see,
Iran
has
another
document.
I
should
have
put
it
on
this
side.
Sorry
I'm
kidding,
can
you
just
say
the
draft
name.
It's
called
draft.
A
You
so
there
are
two
drops
out
there
taking
different
stances
on
this
problem,
so
the
Raza
draft
is
more
x.509
compatible.
This
draft
is
more
clean.
State
oriented,
have
a
look
at
those
and
see
whether
that
might
be
solving
your
signed,
clean
problem
that
you
thought
you
had
to
solve
it
with
experimented
a
bit.
N
B
So
I
mean
this
this
graph.
This
is
a
it's
a
profile
of
x.509,
but
it
can
still
be
parsed
right
by
the
back
end,
I
mean
it
can
still
be
generated
by
the
ca,
so
have
the
X
file
on
our
infrastructure
in
place
so
basically
take
an
x.509
certificate
and
you
could
put
the
front
end
which
converts
this
to
seaboard
you
transport
it
in
seaboard.
B
Then
you
have
to
do
in
the
device,
the
reverse
operation,
to
expand
it
into
x.509
again,
which
is
a
burden,
but
this
is
a
migration
path
to
have
a
format
which
could
be
natively
Seaborg
eventually,
and
it
also
offers
the
SI
CA
infrastructure
to
be
part
of
that
transition
path
from
X
5
minus
negative.
So
that's
a
purpose
and
the.
N
Think
again,
and
then
the
concise
identity
documents
we're
talking
about
here,
just
a
flavor
of
the
possibility,
how
to
package
assertions,
scientists,
surgeons
in
the
future.
There
are
other
objects,
testing
graphs
that
already
do
use
CW
T's
in
the
context
of
searching
something
about
the
device,
for
example,
or
something
else,
and
and
there
will
be-
there
will
be
multiple
flavors
of
this,
and
this
can
be.
We
will
be
built
on
each
other,
but
from
size
identities.
There's
a
identity
document
could
be
a
stage
that
we
arrive
at
and
therefore
workers
like
an
EXO.
A
But
more
about
this
might
be
happening
in
the
future
interim
of
this
book.
We
might
talk
about
this
in
ace
this
afternoon.
We
might
have
a
revival
of
the
cosy
working
group,
which
is
mainly
going
through
on
cosy
into
an
Internet
standard,
but
which
might
also
look
at
formats
that
make
use
of
cosy.
So
it's
up
tight,
but
not
quite
clear
where
this
will
be
done,
but
there
are
a
lot
of
people
who
want
this
done
and
so
I'm
quite
confident
that
it
will
be
done
and
with
that,
thank
you
all
for
sitting
here.
